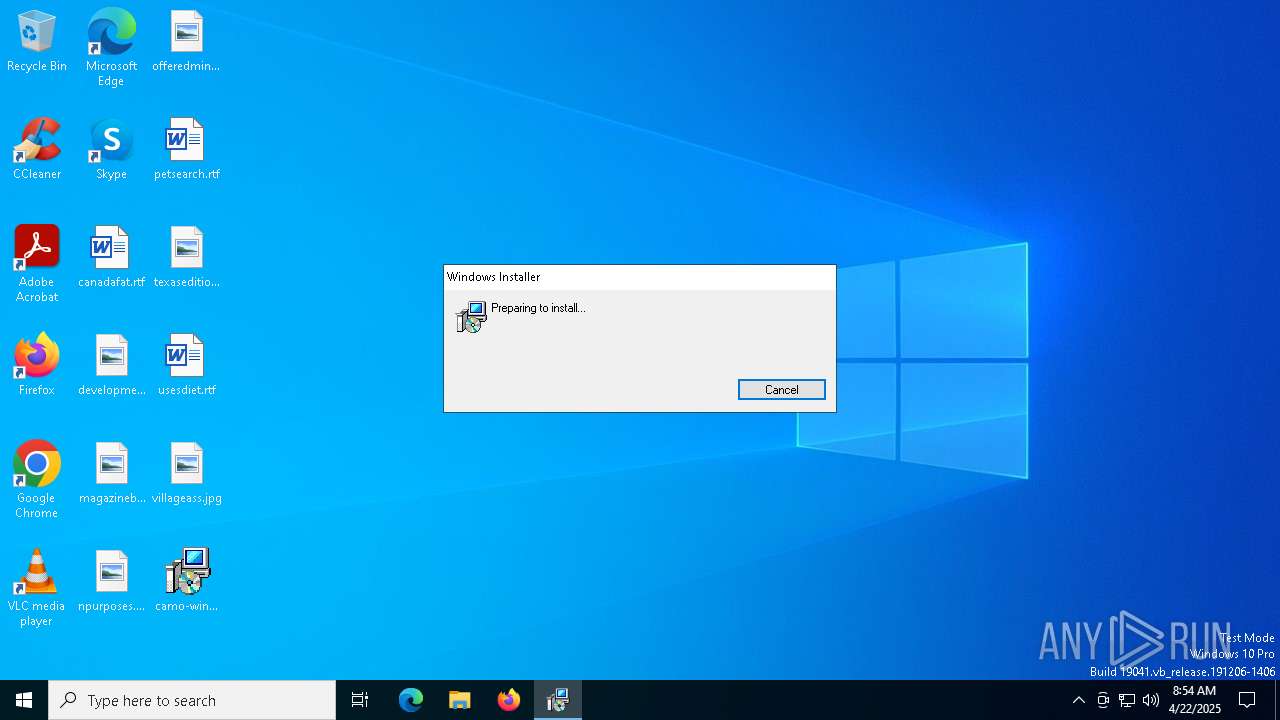
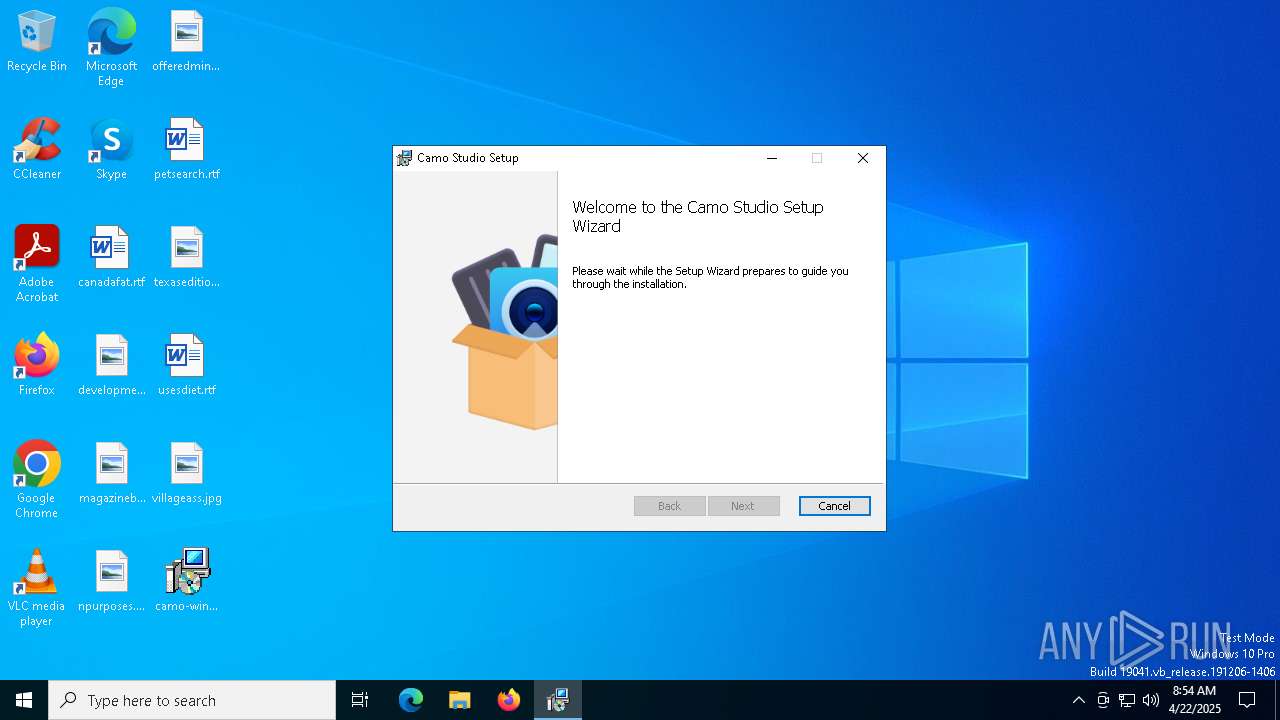
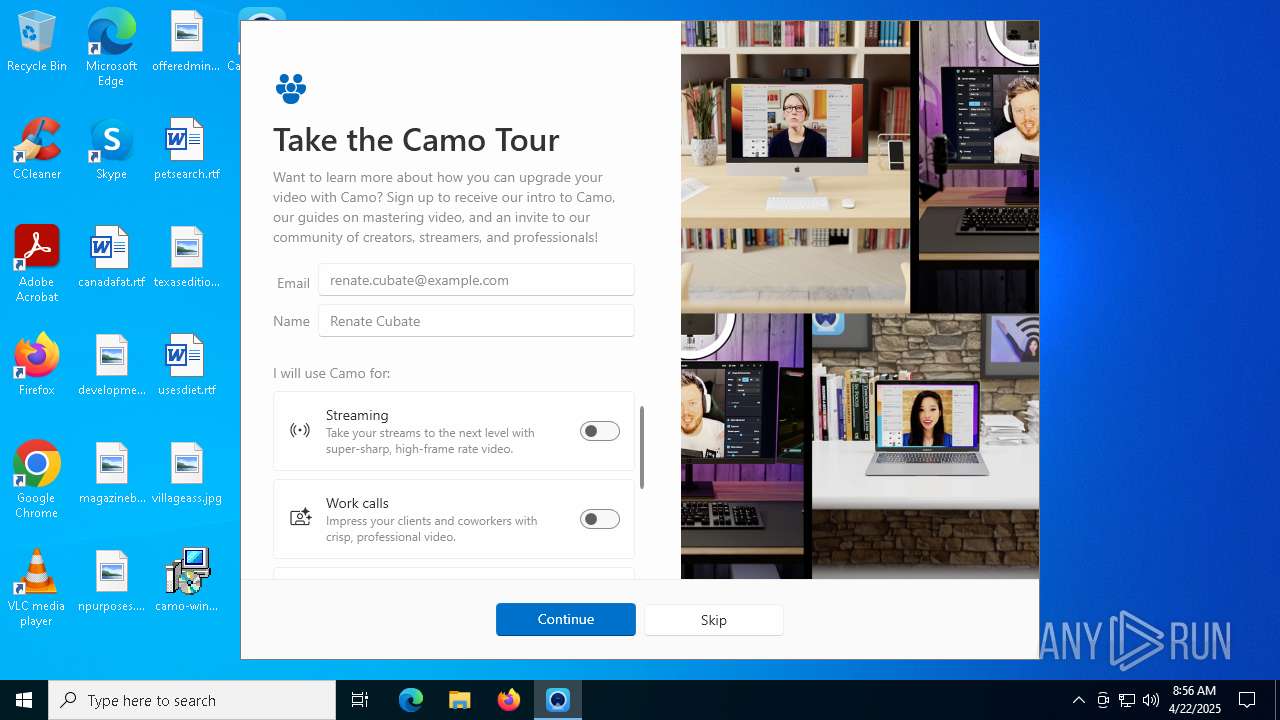
| File name: | camo-windows-latest.msi |
| Full analysis: | https://app.any.run/tasks/617387a1-4ae7-4c28-8c29-fe92273d9daf |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2025, 08:53:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
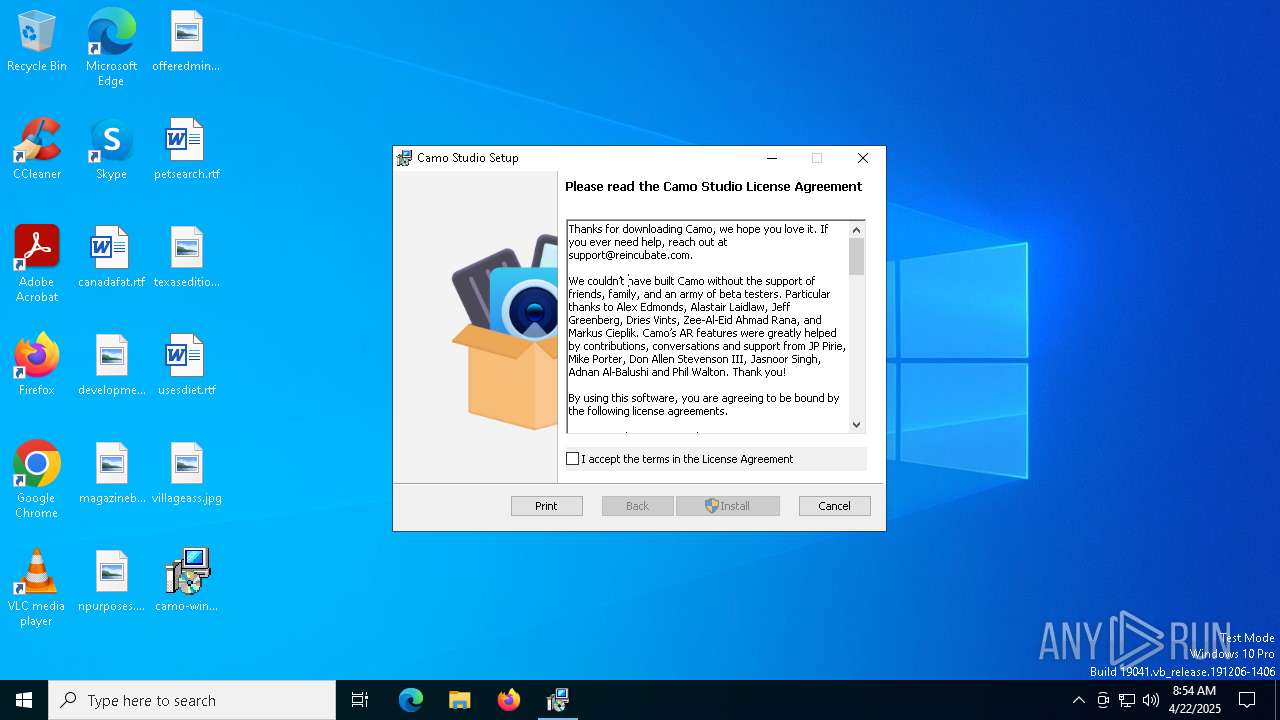
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Camo Studio, Author: Reincubate, Keywords: Installer, Comments: This installer database contains the logic and data required to install Camo Studio., Template: x64;1033, Revision Number: {B25F06D3-BD77-4512-89F2-4A214AFFE23F}, Create Time/Date: Thu Aug 22 11:40:46 2024, Last Saved Time/Date: Thu Aug 22 11:40:46 2024, Number of Pages: 301, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | 074B1221CA4AD9DF3B879301566580F0 |
| SHA1: | 281870DD4D92ECFDFB9CBA9D0FB5073271E8618E |
| SHA256: | EC9F46ED21A05F05DFDDC12D07AEEE653F3972217D58282E8DEA878905BCAEA3 |
| SSDEEP: | 786432:VjS21e+mbBjUEggoIDxWqSXzOx9LbsOv7Lg/+YF8pRJ/pg:VjSg6rggrxWF8JbsOv7Lg/DF8pRhpg |
MALICIOUS
No malicious indicators.SUSPICIOUS
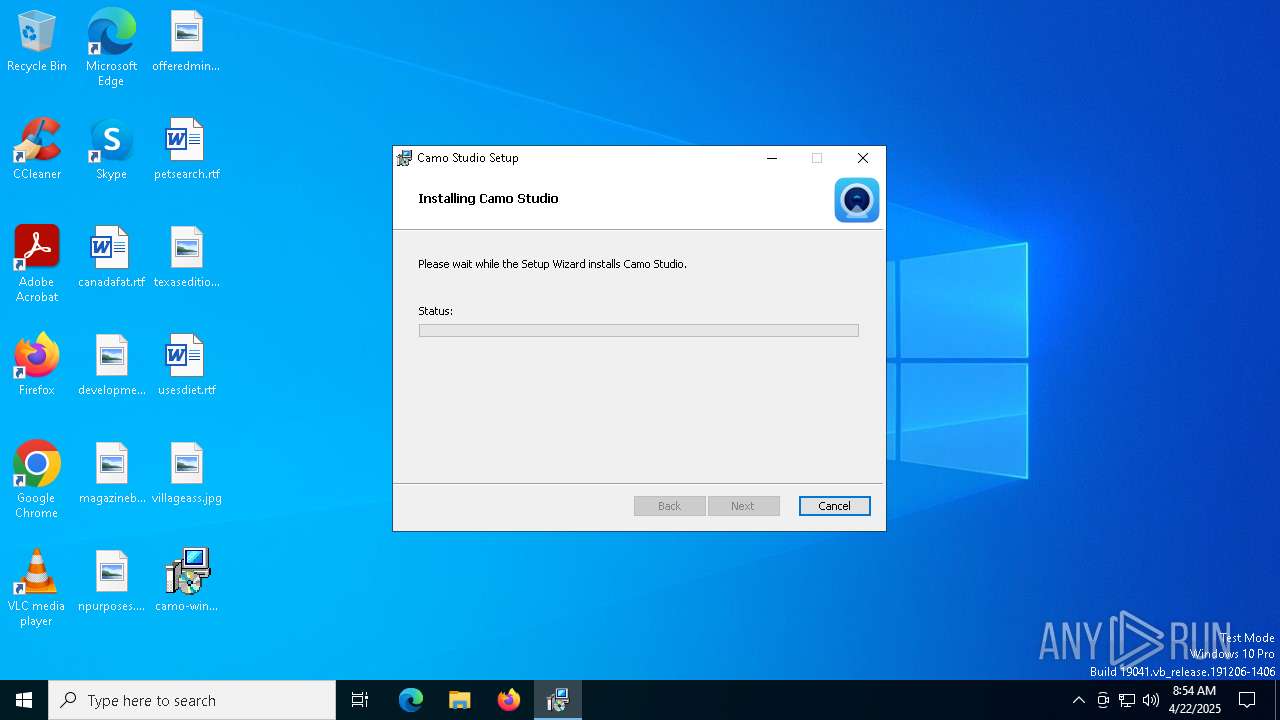
Process drops legitimate windows executable
- msiexec.exe (PID: 7432)
- msiexec.exe (PID: 7580)
The process drops C-runtime libraries
- msiexec.exe (PID: 7432)
- msiexec.exe (PID: 7580)
Executable content was dropped or overwritten
- rundll32.exe (PID: 7744)
- rundll32.exe (PID: 3888)
- rundll32.exe (PID: 1096)
- drvinst.exe (PID: 4724)
- rundll32.exe (PID: 5588)
- drvinst.exe (PID: 6656)
- drvinst.exe (PID: 1804)
Executes as Windows Service
- VSSVC.exe (PID: 7824)
- CamoService.exe (PID: 4244)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7580)
Application launched itself
- msiexec.exe (PID: 7580)
- adb.exe (PID: 7668)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 7580)
- drvinst.exe (PID: 4724)
- drvinst.exe (PID: 6656)
- drvinst.exe (PID: 1804)
The process creates files with name similar to system file names
- msiexec.exe (PID: 7580)
Creates files in the driver directory
- drvinst.exe (PID: 4724)
- CamoDriverInstaller.exe (PID: 4464)
- drvinst.exe (PID: 6656)
- drvinst.exe (PID: 1804)
Creates or modifies Windows services
- drvinst.exe (PID: 5956)
- drvinst.exe (PID: 1804)
Creates/Modifies COM task schedule object
- drvinst.exe (PID: 5956)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7704)
- CamoStudio.exe (PID: 5360)
Reads the date of Windows installation
- CamoStudio.exe (PID: 5360)
INFO
Creates files or folders in the user directory
- msiexec.exe (PID: 7432)
- CamoStudio.exe (PID: 5360)
Checks supported languages
- msiexec.exe (PID: 7580)
- msiexec.exe (PID: 7704)
- msiexec.exe (PID: 4880)
- msiexec.exe (PID: 920)
- msiexec.exe (PID: 5984)
- CamoDriverInstaller.exe (PID: 4464)
- drvinst.exe (PID: 4724)
- drvinst.exe (PID: 5956)
- CamoAudioDriverInstaller.exe (PID: 1324)
- drvinst.exe (PID: 6656)
- drvinst.exe (PID: 1804)
- msiexec.exe (PID: 4336)
- CamoService.exe (PID: 4244)
- CamoStudio.exe (PID: 5360)
- adb.exe (PID: 7668)
- adb.exe (PID: 2344)
- adb.exe (PID: 5132)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7432)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7432)
- msiexec.exe (PID: 7580)
Reads the software policy settings
- msiexec.exe (PID: 7432)
- msiexec.exe (PID: 7580)
- CamoDriverInstaller.exe (PID: 4464)
- CamoAudioDriverInstaller.exe (PID: 1324)
- drvinst.exe (PID: 4724)
- drvinst.exe (PID: 6656)
- CamoStudio.exe (PID: 5360)
- slui.exe (PID: 1088)
Reads the computer name
- msiexec.exe (PID: 7704)
- msiexec.exe (PID: 7580)
- msiexec.exe (PID: 4880)
- msiexec.exe (PID: 920)
- msiexec.exe (PID: 5984)
- CamoDriverInstaller.exe (PID: 4464)
- drvinst.exe (PID: 4724)
- drvinst.exe (PID: 5956)
- CamoAudioDriverInstaller.exe (PID: 1324)
- drvinst.exe (PID: 6656)
- drvinst.exe (PID: 1804)
- msiexec.exe (PID: 4336)
- CamoService.exe (PID: 4244)
- CamoStudio.exe (PID: 5360)
- adb.exe (PID: 5132)
Create files in a temporary directory
- rundll32.exe (PID: 7744)
- rundll32.exe (PID: 3888)
- adb.exe (PID: 5132)
The sample compiled with english language support
- msiexec.exe (PID: 7432)
- msiexec.exe (PID: 7580)
- drvinst.exe (PID: 4724)
Checks proxy server information
- msiexec.exe (PID: 7432)
- CamoStudio.exe (PID: 5360)
- slui.exe (PID: 1088)
Manages system restore points
- SrTasks.exe (PID: 6476)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7580)
- CamoDriverInstaller.exe (PID: 4464)
- drvinst.exe (PID: 4724)
- CamoAudioDriverInstaller.exe (PID: 1324)
- drvinst.exe (PID: 6656)
- CamoService.exe (PID: 4244)
- CamoStudio.exe (PID: 5360)
Reads Environment values
- CamoService.exe (PID: 4244)
- CamoStudio.exe (PID: 5360)
Creates a software uninstall entry
- msiexec.exe (PID: 7580)
Process checks computer location settings
- msiexec.exe (PID: 7704)
- CamoStudio.exe (PID: 5360)
Disables trace logs
- CamoStudio.exe (PID: 5360)
Creates files in the program directory
- CamoStudio.exe (PID: 5360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Camo Studio |
| Author: | Reincubate |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Camo Studio. |
| Template: | x64;1033 |
| RevisionNumber: | {B25F06D3-BD77-4512-89F2-4A214AFFE23F} |
| CreateDate: | 2024:08:22 11:40:46 |
| ModifyDate: | 2024:08:22 11:40:46 |
| Pages: | 301 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
Total processes
157
Monitored processes
28
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | C:\Windows\System32\MsiExec.exe -Embedding 52BE7A8CDDC8CE6F5435CEADAFFE9E31 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | rundll32.exe "C:\WINDOWS\Installer\MSID71A.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1169437 69 CamoStudio.Setup.CustomActions!CamoStudio.Setup.CustomActions.CustomActions.InstallVideoDriver | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Camo Studio\vac\CamoAudioDriverInstaller.exe" -q -l -m -h "Root\{e070661c-ac3f-4aae-aa3f-7d4e8ded5142}\0000" -i "Camo_e070661c-ac3f-4aae-aa3f-7d4e8ded5142" "C:\Program Files (x86)\Camo Studio\vac\vacrnckd.inf" | C:\Program Files (x86)\Camo Studio\vac\CamoAudioDriverInstaller.exe | — | rundll32.exe | |||||||||||
User: SYSTEM Company: Reincubate Integrity Level: SYSTEM Description: Camo Audio Driver Installer Exit code: 0 Version: 1.14.0.1 Modules
| |||||||||||||||
| 1804 | DrvInst.exe "2" "11" "ROOT\{E070661C-AC3F-4AAE-AA3F-7D4E8DED5142}\0000" "C:\WINDOWS\INF\oem6.inf" "oem6.inf:a52522ad0c48fa1f:DevInst:4.70.1.13063:camo_e070661c-ac3f-4aae-aa3f-7d4e8ded5142," "49474d123" "00000000000001E4" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2344 | "C:\Program Files (x86)\Camo Studio\Adb/adb.exe" version | C:\Program Files (x86)\Camo Studio\Adb\adb.exe | — | CamoStudio.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3888 | rundll32.exe "C:\WINDOWS\Installer\MSIAEBB.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1158906 2 CamoStudio.Setup.CustomActions!CamoStudio.Setup.CustomActions.CustomActions.CheckStoreInstall | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4244 | "C:\Program Files (x86)\Camo Studio\Service\CamoService.exe" | C:\Program Files (x86)\Camo Studio\Service\CamoService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Reincubate Integrity Level: SYSTEM Description: Camo Helper Service Version: 1.0.0.0 Modules
| |||||||||||||||
| 4336 | C:\Windows\System32\MsiExec.exe -Embedding 7241230FEF6578855379108BA6C42F69 E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4464 | "C:\Program Files (x86)\Camo Studio\camodriver\CamoDriverInstaller.exe" camo_install "C:\Program Files (x86)\Camo Studio\camodriver\camodriver.inf" | C:\Program Files (x86)\Camo Studio\camodriver\CamoDriverInstaller.exe | — | rundll32.exe | |||||||||||
User: SYSTEM Company: Reincubate Integrity Level: SYSTEM Description: Camo Driver Installer Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
Total events
38 125
Read events
36 364
Write events
1 731
Delete events
30
Modification events
| (PID) Process: | (7580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000D735BC2E64B3DB019C1D0000801E0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000D735BC2E64B3DB019C1D0000801E0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000FFD4162F64B3DB019C1D0000801E0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000E28A1B2F64B3DB019C1D0000801E0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000FB0B122F64B3DB019C1D0000801E0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000FB0B122F64B3DB019C1D0000801E0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (7580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000032C9922F64B3DB019C1D0000801E0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7824) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 480000000000000022E0A52F64B3DB01901E0000841F0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7824) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 480000000000000022E0A52F64B3DB01901E0000B01E0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
163
Suspicious files
48
Text files
34
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7580 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7580 | msiexec.exe | C:\Windows\Installer\118f0e.msi | — | |
MD5:— | SHA256:— | |||
| 7580 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:837076F63C1F5A08AD4748FC9CAA3C72 | SHA256:1E0494C44B5597FA31AEC7EF9F9D8ED6A844A6E422A7DDADB317C7C04FB21AEF | |||
| 7432 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_A784AE3E993E9BBF7162E8F9F9758D3D | binary | |
MD5:B7277E81D1DC8754435B848CC695306B | SHA256:338E9DBCA824D26EAC3A376D81DFF7CBB6894B8A9EF9AD8EC7AC1F50947AE11A | |||
| 7432 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A1D627669EFC8CD4F21BCF387D97F9B5_F9A93C85B285B385A1E5B6C51945DC2B | binary | |
MD5:AD912DDE57E60C478F7DB52CED9CE79D | SHA256:6BC27CEF8EE390804A2F933C18A3A238330CCA14082979DB15C2F64FDD0813CA | |||
| 7432 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI1922.tmp | executable | |
MD5:E7CE04593534BCBB1028367130992B43 | SHA256:65318A5C7FFF1372D85208EA39FB1B7B9AF5BC26738E53FB03C580BF6DC0461C | |||
| 7744 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\SFXCA8581BF6C1C40C5BBEEBA74402F51DC3D\WixToolset.Dtf.WindowsInstaller.dll | executable | |
MD5:195E24CE1176FCF271B12C208638A6F9 | SHA256:04FF498139C67CCCB791CE0A6A2DC38792149FA94516736689BC224F026BDE35 | |||
| 7744 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\SFXCA8581BF6C1C40C5BBEEBA74402F51DC3D\CustomAction.config | xml | |
MD5:6783A127A0B3B68B67462DDE8CDB6912 | SHA256:1DEBB93E37806158F6BBA132157967AC70146319E565524B314C870FD249C5EF | |||
| 7744 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\SFXCA8581BF6C1C40C5BBEEBA74402F51DC3D\CamoStudio.Setup.CustomActions.dll | executable | |
MD5:F571C1AF255C98415CEAB82F4C475B15 | SHA256:EC6CF4FF79E5D4C2E35A09850E0B81913AF1E2554192C769A265FD539F7B6E95 | |||
| 3888 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\SFXCAE6997CC27B4CD00BFE1DE1F9C243703C\CamoStudio.Setup.CustomActions.dll | executable | |
MD5:F571C1AF255C98415CEAB82F4C475B15 | SHA256:EC6CF4FF79E5D4C2E35A09850E0B81913AF1E2554192C769A265FD539F7B6E95 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
71
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 40.126.32.68:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.160.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.160.65:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | — | — | whitelisted |
— | — | POST | 400 | 20.190.160.132:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.160.17:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.32.72:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.32.68:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
7432 | msiexec.exe | GET | 200 | 146.75.122.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEQCBTkIXoSl%2F7VrM1Bf4ka11 | US | binary | 1.67 Kb | whitelisted |
— | — | GET | 304 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | unknown |
7432 | msiexec.exe | GET | 200 | 146.75.122.133:80 | http://ocsp.globalsign.com/gsgccr45codesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLuA3ygnKW%2F7xuSx%2F09F%2BhHVuEUQQU2rONwCSQo2t30wygWd0hZ2R2C3gCDEKYmMEQ4EUewESZxg%3D%3D | US | binary | 1.64 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
— | — | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7432 | msiexec.exe | 146.75.122.133:80 | ocsp.globalsign.com | FASTLY | US | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7908 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7908 | SIHClient.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
7908 | SIHClient.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |