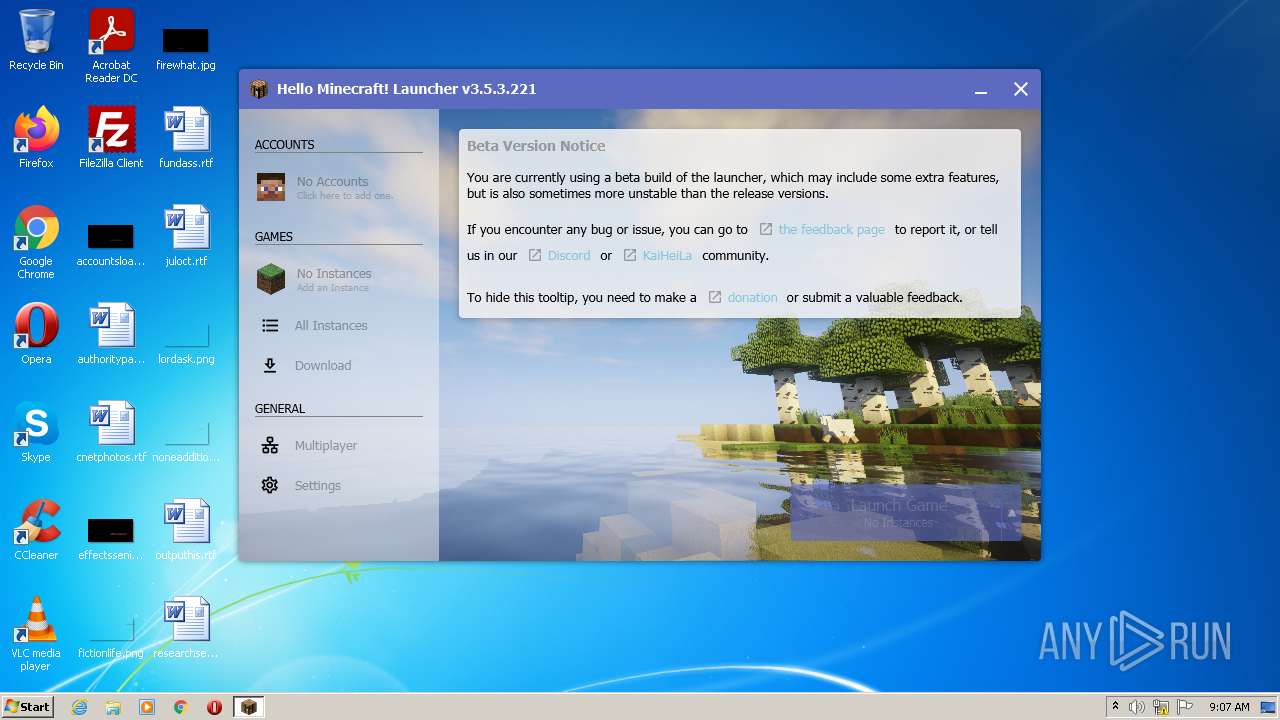
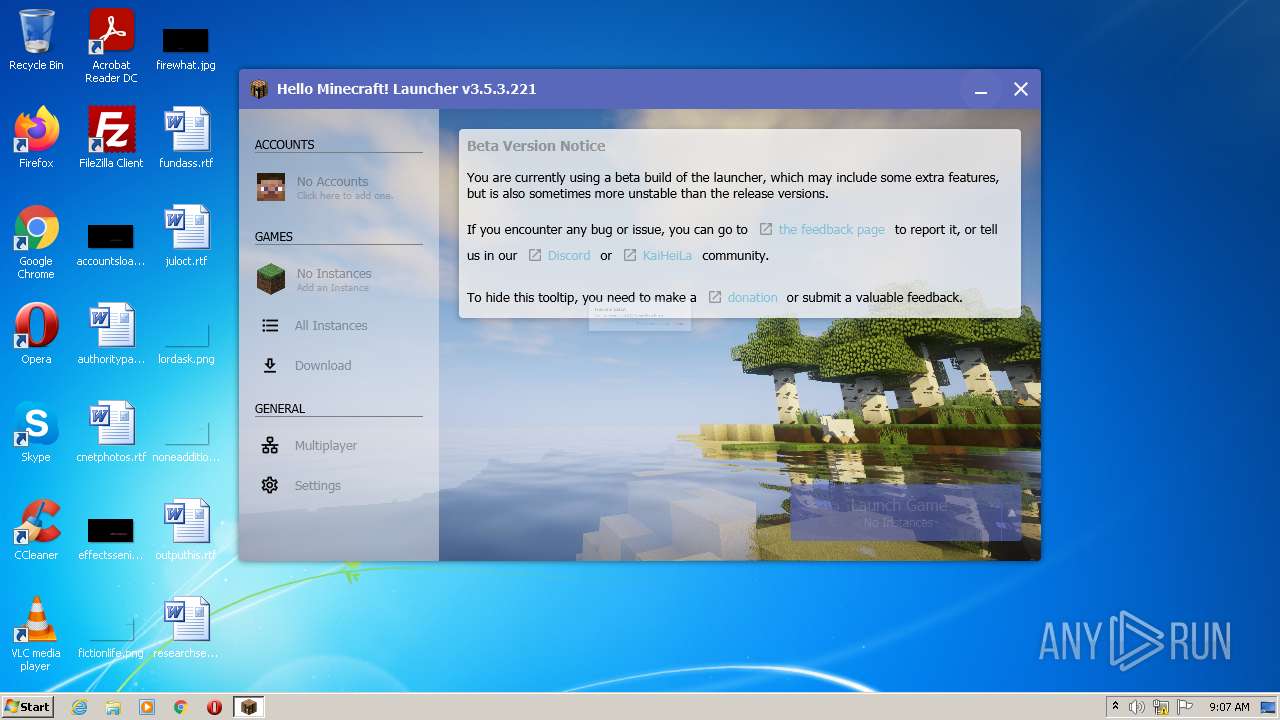
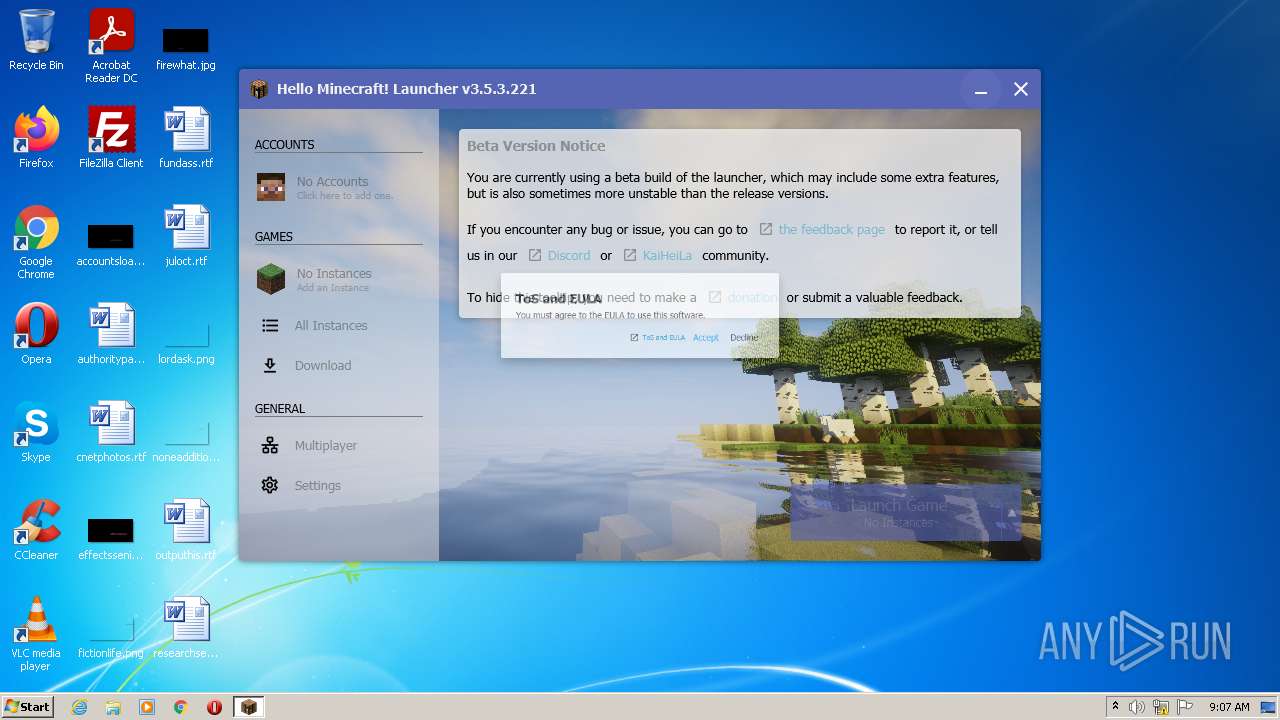
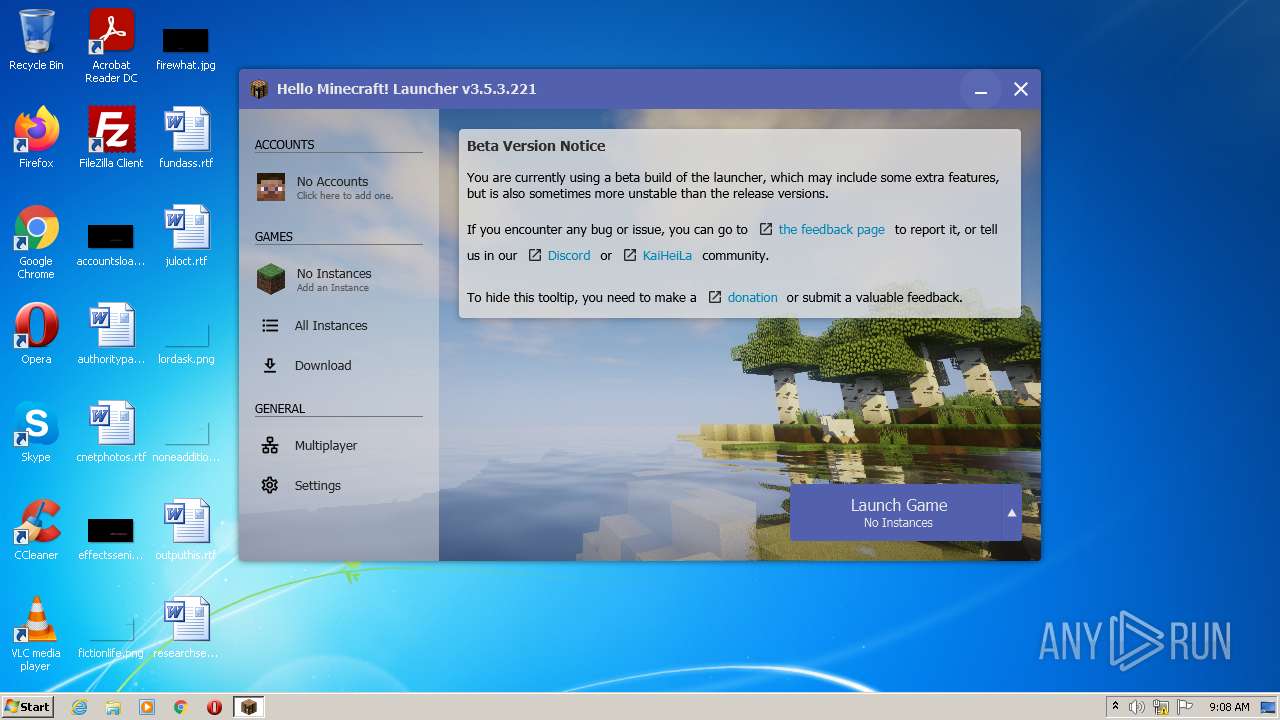
| download: | HMCL-3.5.3.221.exe |
| Full analysis: | https://app.any.run/tasks/620fa8c9-3a83-46fa-b1e7-16991d6f3c67 |
| Verdict: | Suspicious activity |
| Analysis date: | July 27, 2022, 08:07:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C05F0B6300D2D9C5EB552186191C01F1 |
| SHA1: | 8D317F51709F7C4ABC9F12E75D79A84AD8760049 |
| SHA256: | EC9DB614C849A315F20B1E43AEBC5E7ADFAB5F3A7AD6DA04A9886BD6E82F28A5 |
| SSDEEP: | 98304:dJYgE/OWIMBz4eHBq4pU/f4x4z4Id/X2W:NEGnMB8eHBqRoqz4I9X2W |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- HMCL-3.5.3.221.exe (PID: 2872)
- javaw.exe (PID: 3172)
- cmd.exe (PID: 3556)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 2300)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 3184)
- cmd.exe (PID: 3496)
- cmd.exe (PID: 1860)
- java.exe (PID: 2444)
Check for Java to be installed
- HMCL-3.5.3.221.exe (PID: 2872)
- java.exe (PID: 2444)
Creates files in the program directory
- javaw.exe (PID: 3172)
Reads the computer name
- javaw.exe (PID: 3172)
INFO
Checks supported languages
- icacls.exe (PID: 2268)
- reg.exe (PID: 3292)
- reg.exe (PID: 2584)
- reg.exe (PID: 1312)
- reg.exe (PID: 3044)
- reg.exe (PID: 1656)
- reg.exe (PID: 3440)
- reg.exe (PID: 1536)
Reads the computer name
- icacls.exe (PID: 2268)
Check for Java to be installed
- reg.exe (PID: 3292)
- reg.exe (PID: 2584)
- reg.exe (PID: 3044)
- reg.exe (PID: 1312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 3.5.0.0 |
|---|---|
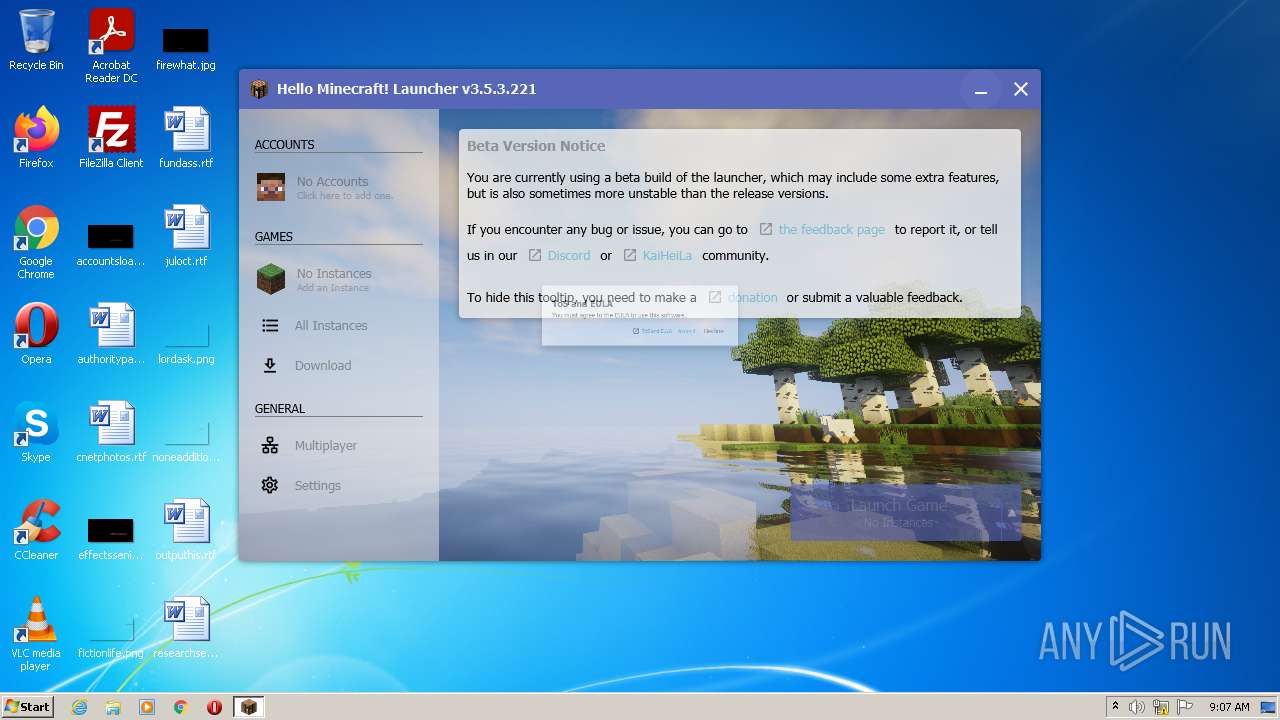
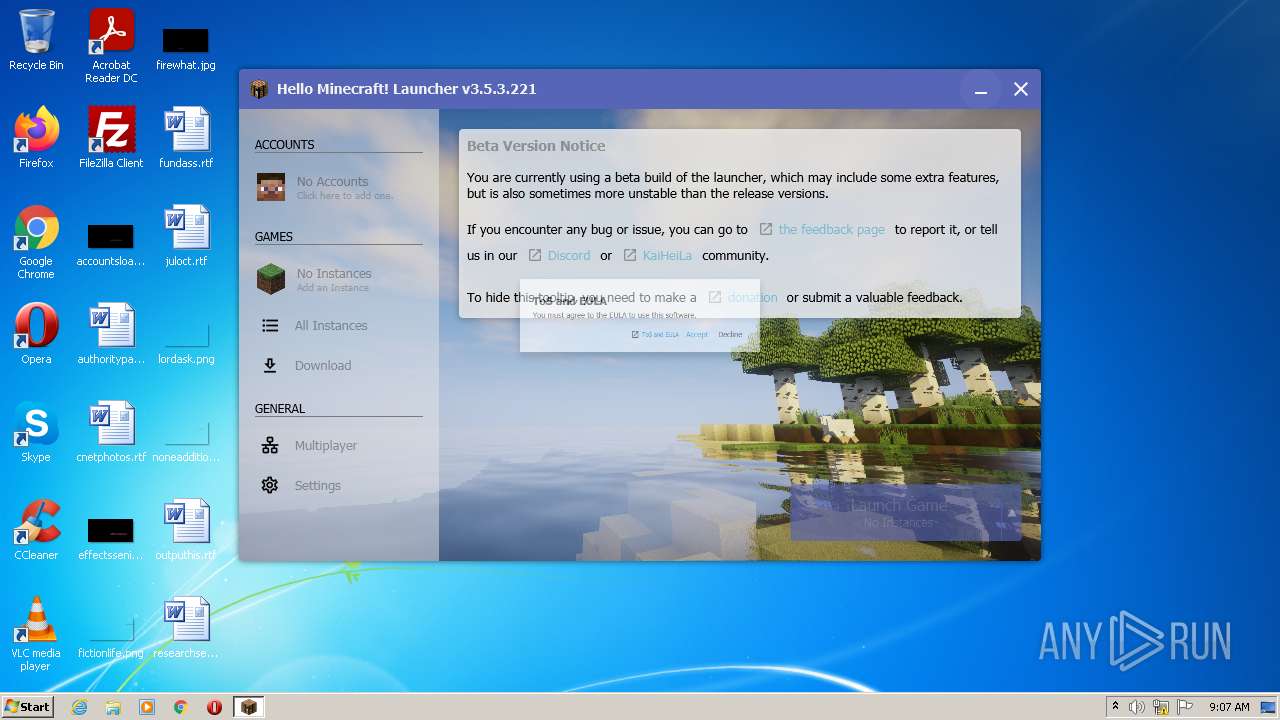
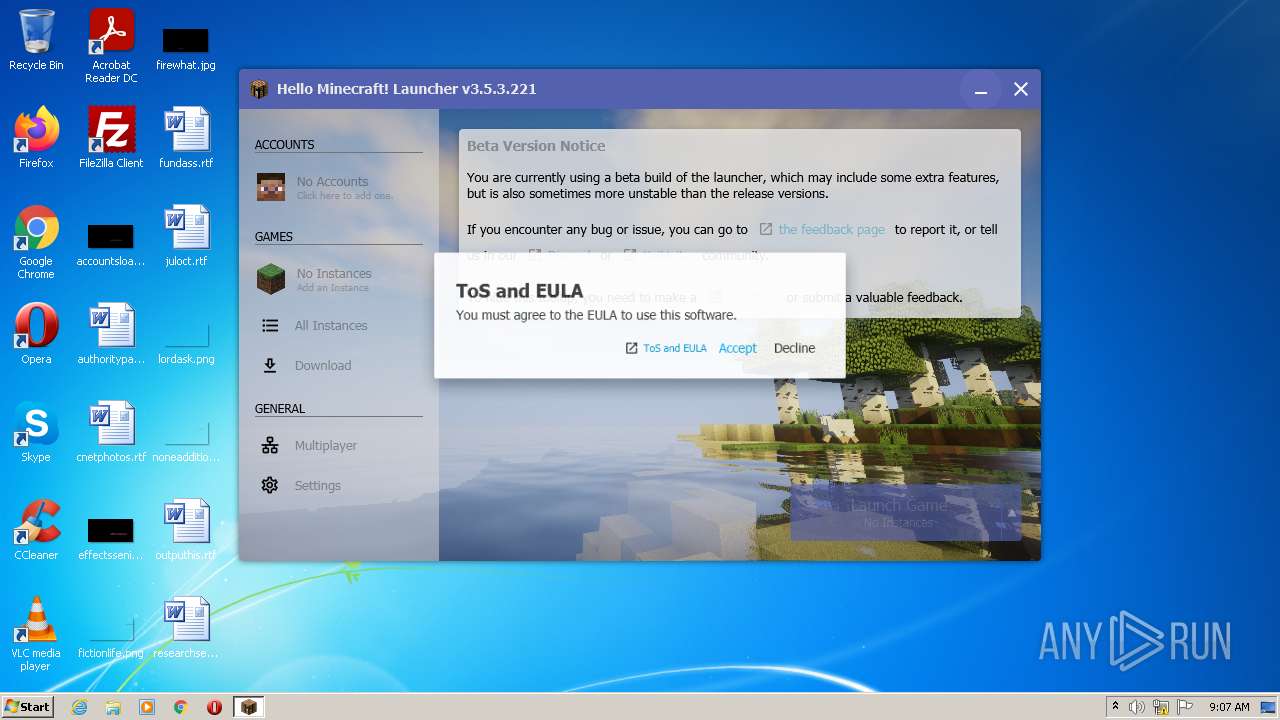
| ProductName: | Hello Minecraft! Launcher |
| OriginalFileName: | HMCL.exe |
| LegalCopyright: | Copyright (C) 2021 huangyuhui |
| InternalName: | HMCL.exe |
| FileVersion: | 3.5.0.0 |
| FileDescription: | Hello Minecraft! Launcher For Windows |
| CompanyName: | huanghongxun |
| CharacterSet: | Unicode |
| LanguageCode: | Chinese (Simplified) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.4.0.0 |
| FileVersionNumber: | 3.4.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x3aa4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 51712 |
| CodeSize: | 58880 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2022:05:22 08:29:13+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-May-2022 06:29:13 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | huanghongxun |
| FileDescription: | Hello Minecraft! Launcher For Windows |
| FileVersion: | 3.5.0.0 |
| InternalName: | HMCL.exe |
| LegalCopyright: | Copyright (C) 2021 huangyuhui |
| OriginalFilename: | HMCL.exe |
| ProductName: | Hello Minecraft! Launcher |
| ProductVersion: | 3.5.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 22-May-2022 06:29:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000E5D2 | 0x0000E600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5809 |
.rdata | 0x00010000 | 0x00006A18 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75863 |
.data | 0x00017000 | 0x000013E8 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.34673 |
.rsrc | 0x00019000 | 0x000037B0 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.95529 |
.reloc | 0x0001D000 | 0x000010A8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.32613 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
7 | 1.22202 | 48 | UNKNOWN | Chinese - PRC | RT_STRING |
107 | 1.7815 | 20 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
109 | 1.79879 | 16 | UNKNOWN | Chinese - PRC | RT_ACCELERATOR |
160 | 5.5016 | 8193 | UNKNOWN | Chinese - PRC | RT_RCDATA |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
AmdPowerXpressRequestHighPerformance | 1 | 0x0001779C |
NvOptimusEnablement | 2 | 0x000177A0 |
Total processes
61
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1312 | reg query "HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Runtime Environment\1.8.0_271" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | reg query HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\JDK\ | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1656 | reg query "HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Development Kit\\" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | cmd /c reg query HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\JDK\ | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1876 | cmd /c reg query "HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Runtime Environment\1.8.0_271" /v JavaHome | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2136 | cmd /c reg query "HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Runtime Environment\\" | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2268 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | cmd /c reg query "HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Runtime Environment\1.8" | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Common Files\Oracle\Java\javapath_target_52116515\java.exe" -XshowSettings:properties -version | C:\Program Files\Common Files\Oracle\Java\javapath_target_52116515\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2476 | cmd /c reg query "HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Runtime Environment\1.8.0_271" | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 082
Read events
1 081
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3172) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
0
Suspicious files
2
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3172 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 3172 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio414654768504801290.tmp | image | |
MD5:27BE3561F3E037E28D3D0D1376783A4B | SHA256:28695CA7DD6A76904512F904F99BAFC0BDEE1F51A28D6CB7C7ADE8BEDBF3C8A4 | |||
| 3172 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio2524746325444176098.tmp | image | |
MD5:607A88E778A05A24FD3DFBE4BFE43346 | SHA256:F6C0B9ED9A81AA63D9D1EAE474A0536CA0BE964F74DBDB0276965DEF44897EFA | |||
| 3172 | javaw.exe | C:\Users\admin\AppData\Local\Temp\hmcl.json | text | |
MD5:1C6D2429BA0355DEFCC1CE9ACB4B9AA3 | SHA256:DBC24B3F82ECDAE04671776FA2B9602081E33E29DDD2DA81B10D014DDD919869 | |||
| 3172 | javaw.exe | C:\Users\admin\AppData\Local\Temp\.hmcl.json.tmp | text | |
MD5:1C6D2429BA0355DEFCC1CE9ACB4B9AA3 | SHA256:DBC24B3F82ECDAE04671776FA2B9602081E33E29DDD2DA81B10D014DDD919869 | |||
| 3172 | javaw.exe | C:\Users\admin\AppData\Roaming\.hmcl\config.json | binary | |
MD5:60371DADBCDEC30F2440D49C3BEFA6F1 | SHA256:995F01C10E89C4CF03EBAFFA121D82B107001780DE74BDDF7FBBE55B8EF07567 | |||
| 3172 | javaw.exe | C:\Users\admin\AppData\Local\Temp\hmcl6875305718134964503.css | text | |
MD5:13271139EFB2F595DDBEEDC4A6341BB4 | SHA256:E8C5A38D76362FD38B1B93FAFA000BD9AE1927F5B19BC5AF256B74616279B4C6 | |||
| 3172 | javaw.exe | C:\Users\admin\AppData\Roaming\.hmcl\.config.json.tmp | binary | |
MD5:60371DADBCDEC30F2440D49C3BEFA6F1 | SHA256:995F01C10E89C4CF03EBAFFA121D82B107001780DE74BDDF7FBBE55B8EF07567 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3172 | javaw.exe | 1.117.239.163:443 | hmcl.huangyuhui.net | — | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hmcl.huangyuhui.net |
| suspicious |
dns.msftncsi.com |
| shared |