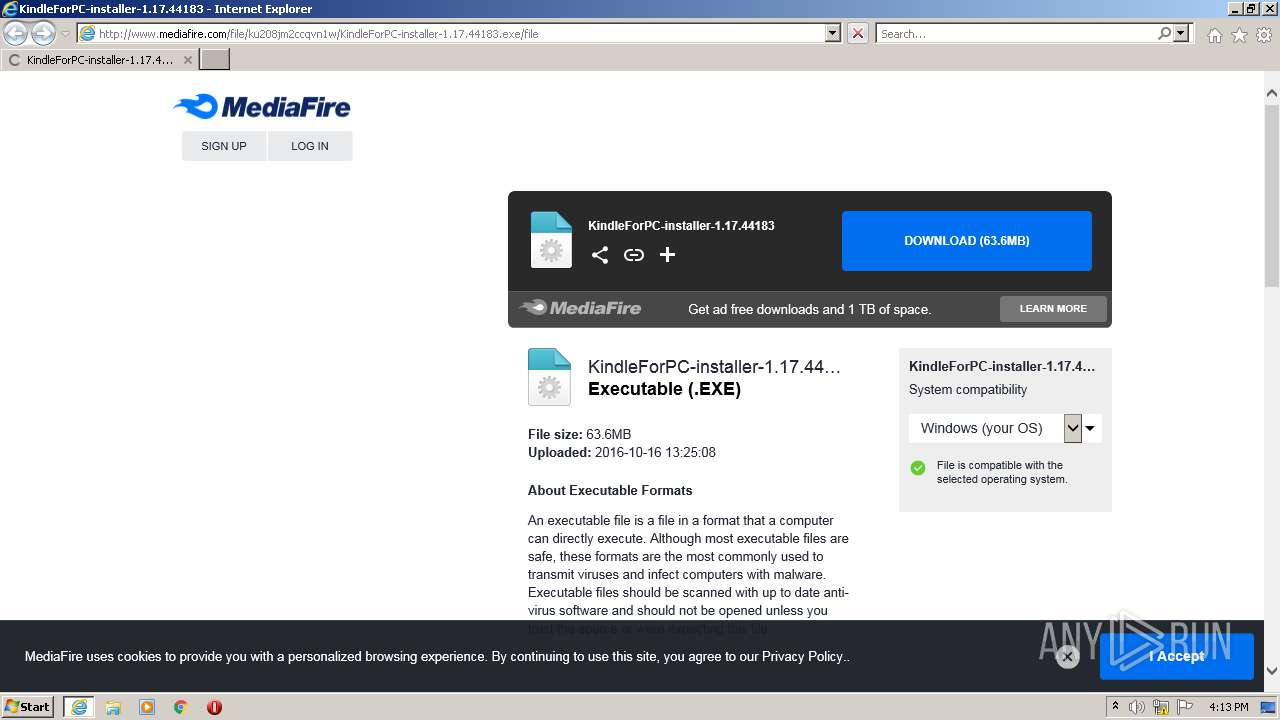
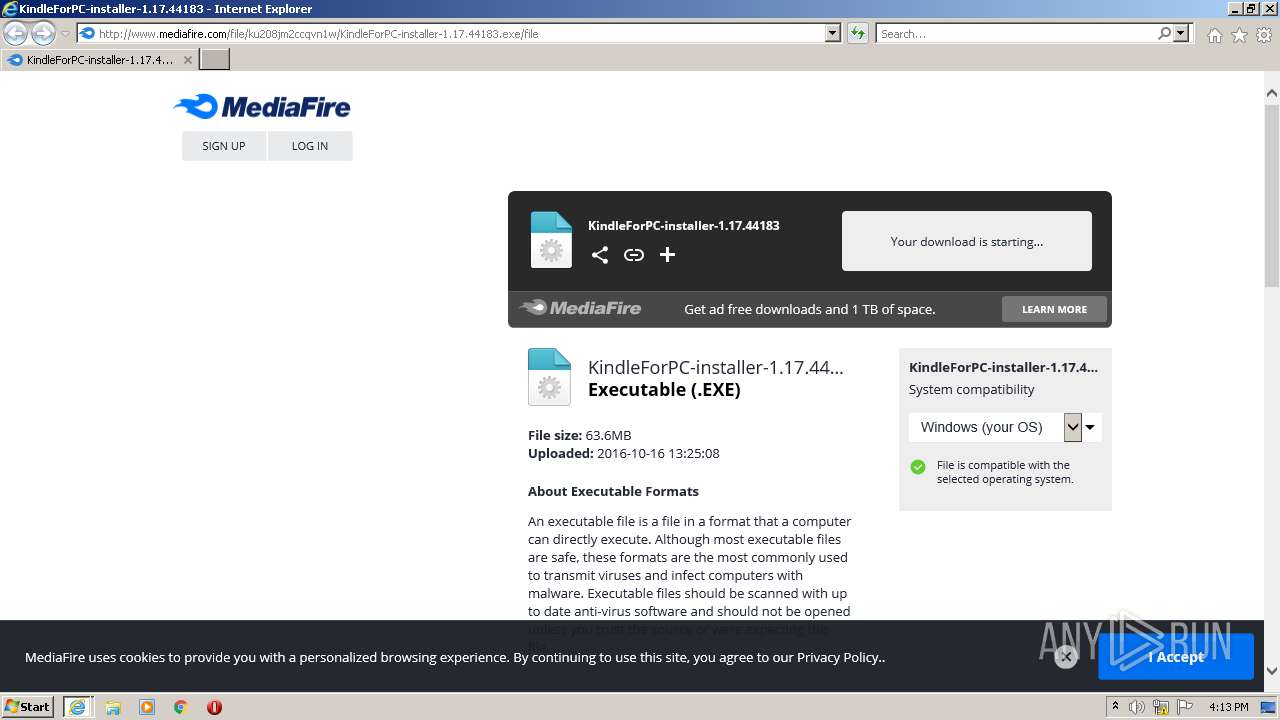
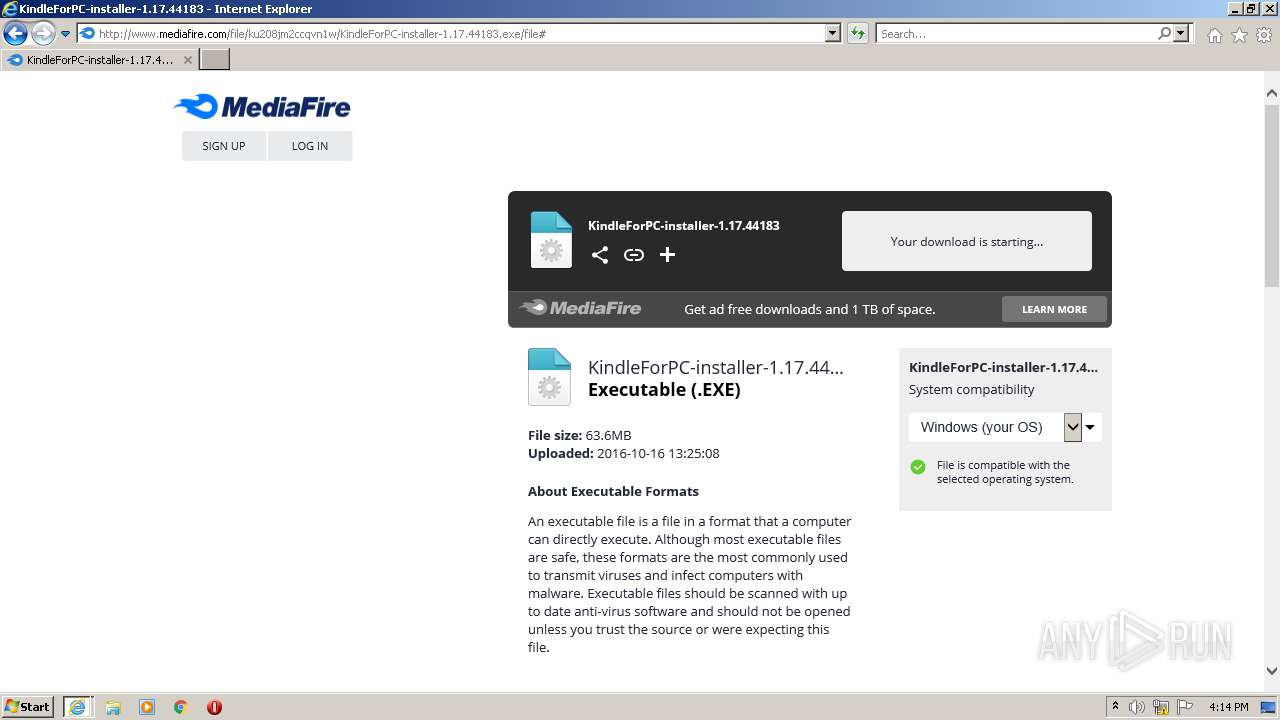
| URL: | http://www.mediafire.com/file/ku208jm2ccqvn1w/KindleForPC-installer-1.17.44183.exe/file |
| Full analysis: | https://app.any.run/tasks/38c0b454-def4-4386-9f51-91a658fd2697 |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2021, 15:13:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CDB7B7FDE4E7B6488F6E598D1902FC92 |
| SHA1: | 5705C73B4C3F7BEDE1E39A6B736B847A824C484E |
| SHA256: | EC999D2E7278B4F6EE42D330CCB53708FE6124AE3B1300E39F6F896D83EEDBAB |
| SSDEEP: | 3:N1KJS4w3eGUoHl1KIVL8XIScBdAfA:Cc4w3eGDl1KUwXl0dAo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 3960)
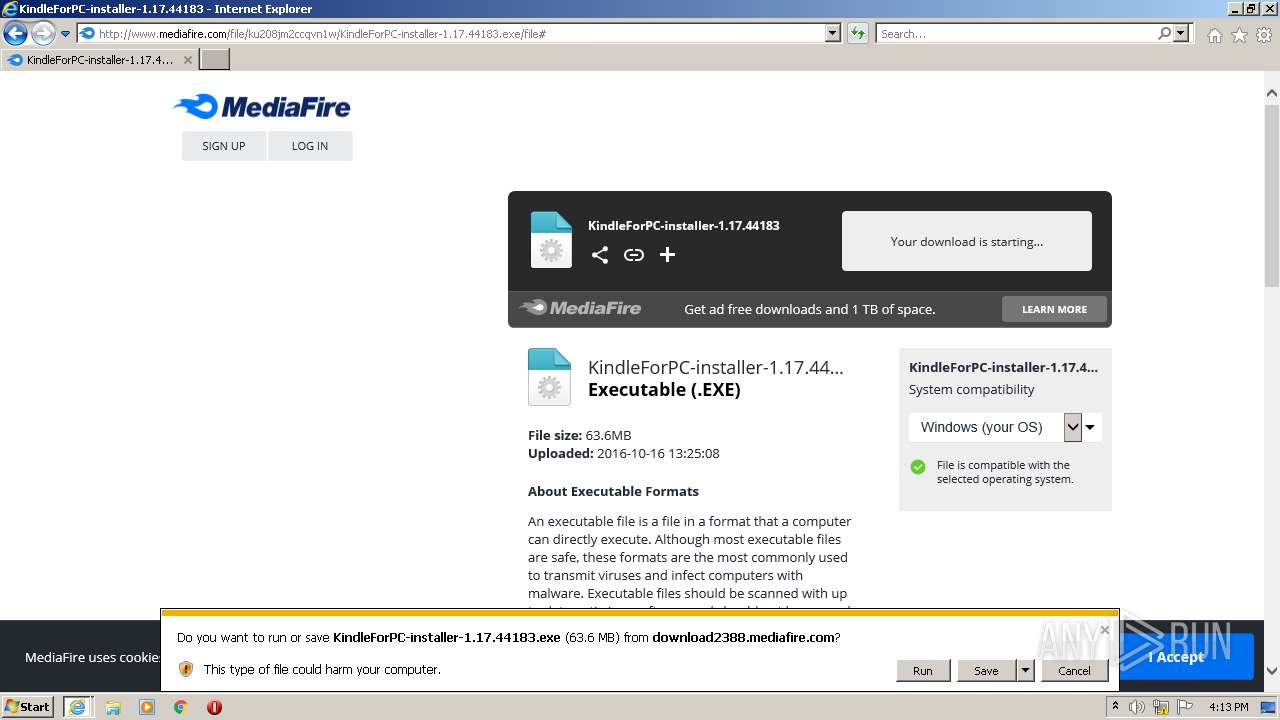
Executable content was dropped or overwritten
- iexplore.exe (PID: 3004)
Drops a file with too old compile date
- iexplore.exe (PID: 3004)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2800)
Checks supported languages
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 3960)
Creates files in the user directory
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 3960)
Checks Windows Trust Settings
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 3960)
- iexplore.exe (PID: 3004)
Reads the computer name
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 3960)
Application launched itself
- iexplore.exe (PID: 2800)
Reads settings of System Certificates
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 3960)
- iexplore.exe (PID: 2800)
Reads internet explorer settings
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 3960)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
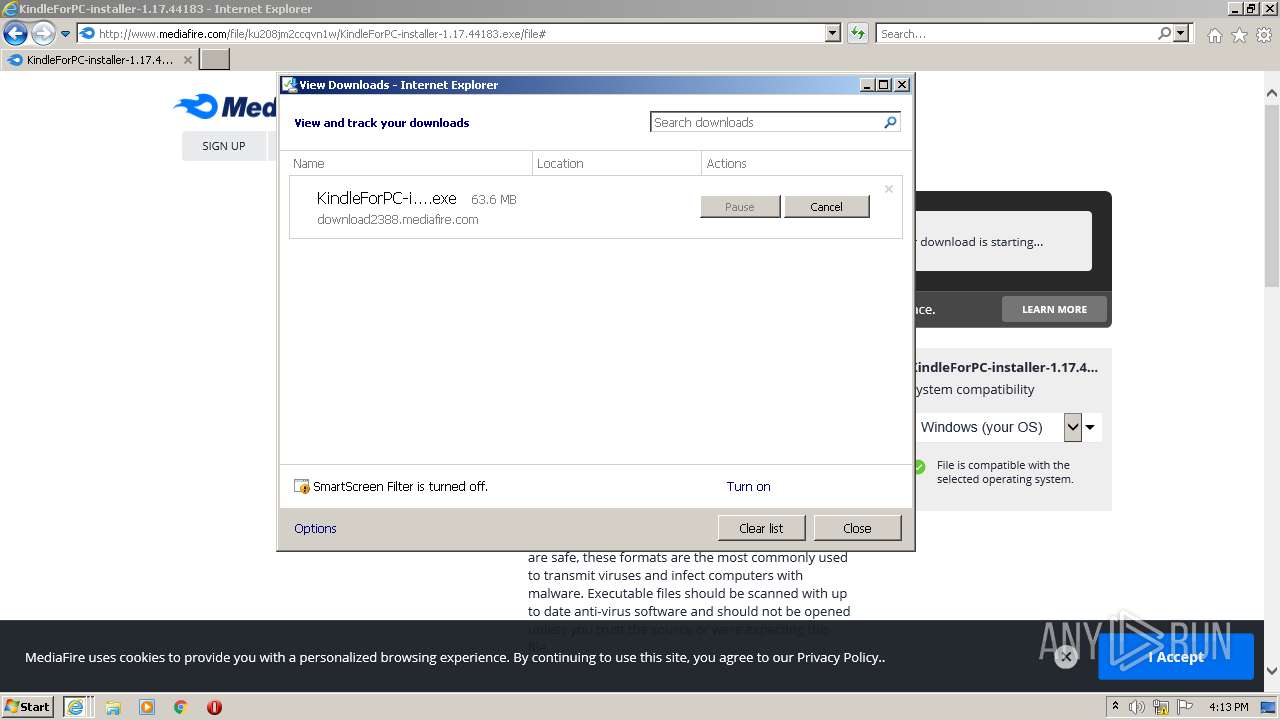
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2800 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.mediafire.com/file/ku208jm2ccqvn1w/KindleForPC-installer-1.17.44183.exe/file" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2800 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3960 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2800 CREDAT:3740944 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
25 295
Read events
25 107
Write events
188
Delete events
0
Modification events
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30896962 | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30896962 | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
26
Text files
122
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JCXUZ5G9.txt | text | |
MD5:— | SHA256:— | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\AYV9E34C.txt | text | |
MD5:— | SHA256:— | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2WBK7Z8R.txt | text | |
MD5:— | SHA256:— | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\f[1].txt | text | |
MD5:— | SHA256:— | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\file[1].htm | html | |
MD5:— | SHA256:— | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WGEE7QR5.txt | text | |
MD5:— | SHA256:— | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\mf_logo_full_color[1].svg | image | |
MD5:B3BB5BF9102F80054D199F293046DB84 | SHA256:8539C91AE0A82F8CAB27D481EA38AC4E66D1E5B36701FE295BCBA4399B9255BD | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\dl_promo_logo[1].png | image | |
MD5:6C600D768576CAC11D18FBFCACE25277 | SHA256:174D0CE23DDAA3923575AF7A8E047E1DBF75199EBEE7DF1ACA5E5713C4A1DD62 | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\footerIcons[1].png | image | |
MD5:E0ABC4FEA89D2C5153B73CD02AC5BA13 | SHA256:F917A9105C311331B1D40F4D2BDBF11233C1C465616C1A9C46232F451463B061 | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\check_circle_green[1].svg | image | |
MD5:6C560D3B737954CBF3BFC2B909448443 | SHA256:03C8D2DC7D985C3004FF2CD6D8148DD03560F37ED15EFDF6C2D7F4D771D0E599 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
121
DNS requests
42
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
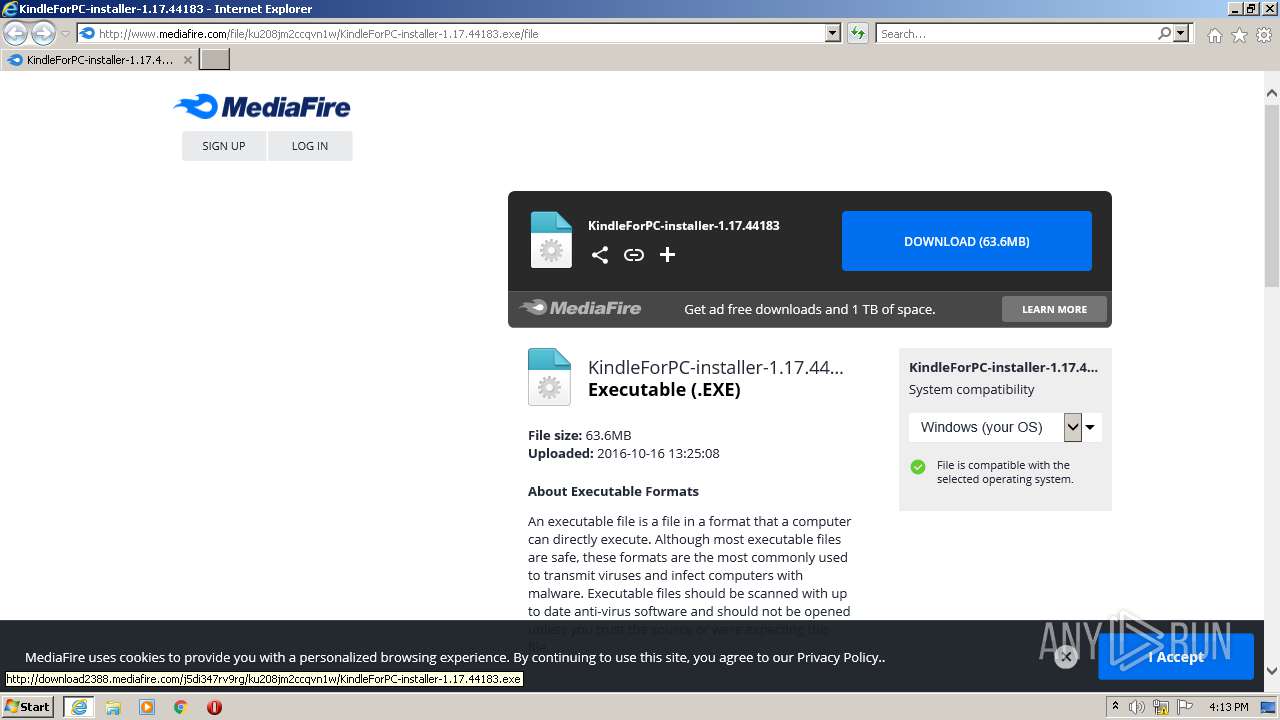
3004 | iexplore.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.10 Kb | shared |
3004 | iexplore.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/file/ku208jm2ccqvn1w/KindleForPC-installer-1.17.44183.exe/file | US | html | 81.6 Kb | shared |
3004 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3004 | iexplore.exe | GET | 200 | 142.250.186.78:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 3.76 Kb | whitelisted |
3004 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3004 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEEv1fo69oyETBQAAAACH6kw%3D | US | der | 471 b | whitelisted |
3004 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3004 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3004 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 727 b | whitelisted |
3004 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/download/social/fb_16x16.png | US | image | 181 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | iexplore.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3004 | iexplore.exe | 104.16.95.65:443 | static.cloudflareinsights.com | Cloudflare Inc | US | shared |
— | — | 104.16.95.65:443 | static.cloudflareinsights.com | Cloudflare Inc | US | shared |
3004 | iexplore.exe | 142.250.186.170:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3004 | iexplore.exe | 104.19.214.37:443 | cdn.otnolatrnup.com | Cloudflare Inc | US | shared |
3004 | iexplore.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3004 | iexplore.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | Microsoft Corporation | US | whitelisted |
3004 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3004 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3004 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
c.aaxads.com |
| whitelisted |
cdn.otnolatrnup.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
static.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3004 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3004 | iexplore.exe | Misc activity | ET INFO EXE - Served Attached HTTP |