| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/a0d0ff84-a47c-4ec6-8b41-8feae40b2568 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 23:07:28 |
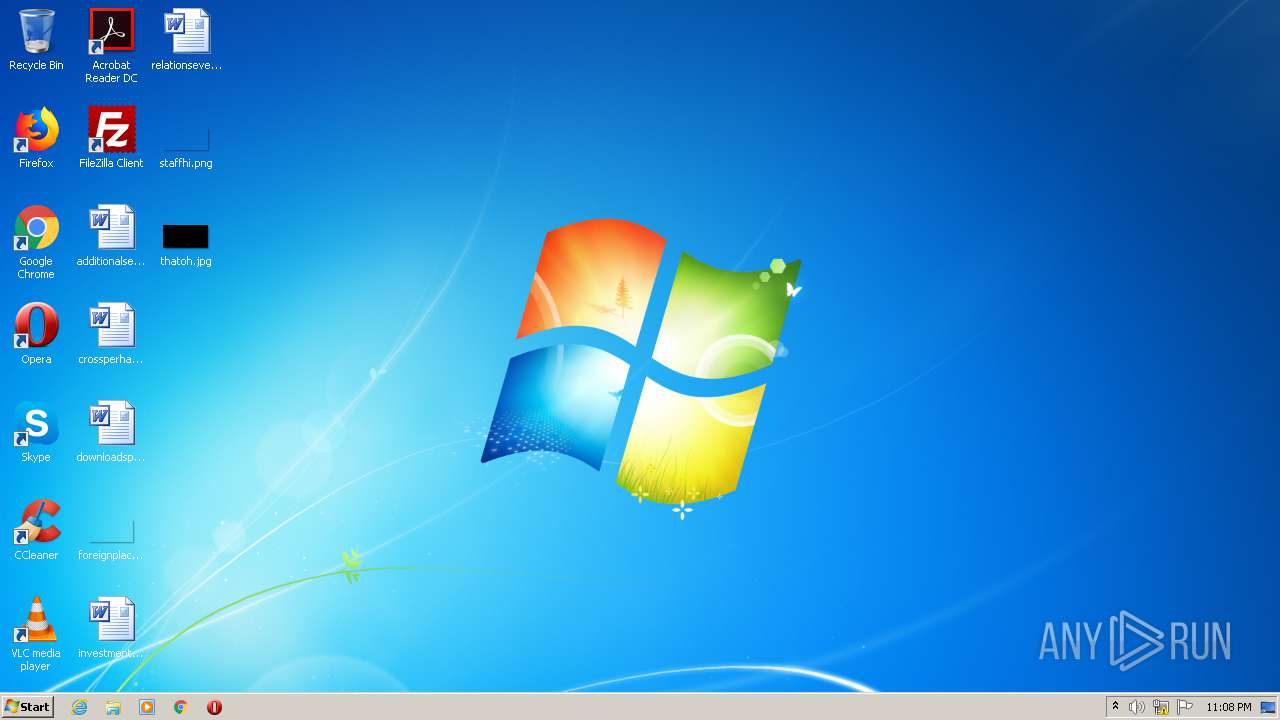
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BFACC36C3A7BA82C2F28F870A3FE5651 |
| SHA1: | F553D7E9ADCD7EBAE440BDA9B0BD1CCEE0A8CE94 |
| SHA256: | EC815652769B8547A36D6D50145B36DA5688184F4148A64FAEEE41E4C93D053E |
| SSDEEP: | 98304:JtWNRQJfjNiBJ3f4UXkxk+y0WjX/juAKC0pFY4JhJFUqMIbH2Re1o:sRagXvNkgPjXLuhC0JJfpn2RT |
MALICIOUS
Drops executable file immediately after starts
- setup.exe (PID: 2572)
- setup.exe.tmp (PID: 4084)
- setup.exe.tmp (PID: 2964)
SUSPICIOUS
Drops a file with too old compile date
- setup.exe (PID: 3036)
- setup.exe (PID: 2572)
- setup.exe.tmp (PID: 4084)
- setup.exe.tmp (PID: 2964)
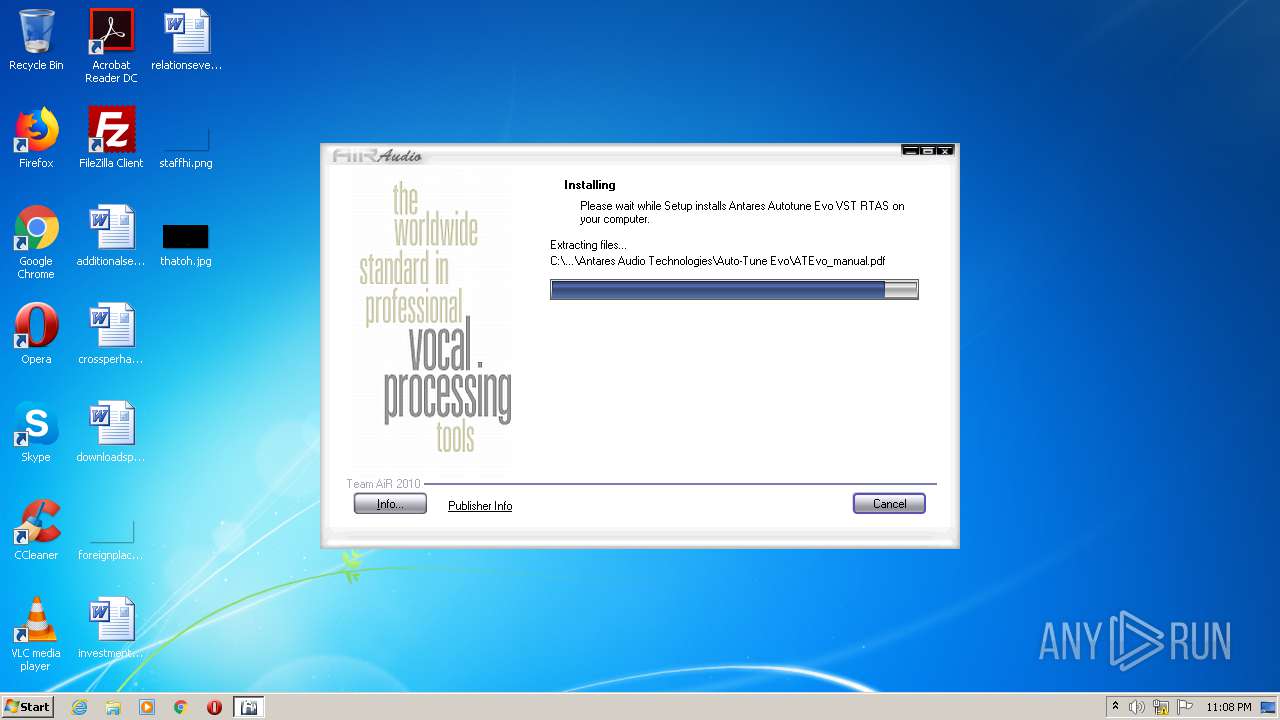
Executable content was dropped or overwritten
- setup.exe (PID: 2572)
- setup.exe.tmp (PID: 4084)
- setup.exe.tmp (PID: 2964)
- setup.exe (PID: 3036)
Creates files in the user directory
- setup.exe.tmp (PID: 2964)
Creates a directory in Program Files
- setup.exe.tmp (PID: 2964)
Drops a file that was compiled in debug mode
- setup.exe.tmp (PID: 2964)
Creates files in the Windows directory
- setup.exe.tmp (PID: 2964)
INFO
Application was dropped or rewritten from another process
- setup.exe.tmp (PID: 4084)
- setup.exe.tmp (PID: 2964)
Loads dropped or rewritten executable
- setup.exe.tmp (PID: 2964)
- setup.exe.tmp (PID: 4084)
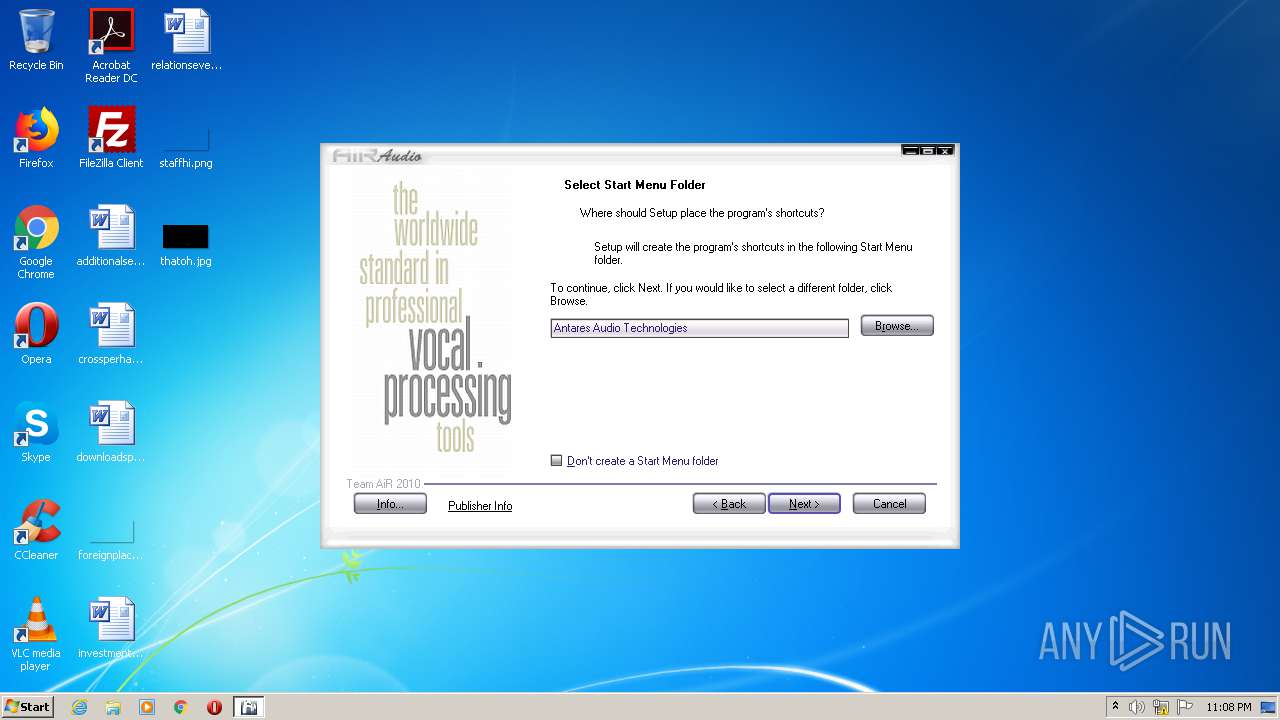
Creates a software uninstall entry
- setup.exe.tmp (PID: 2964)
Creates files in the program directory
- setup.exe.tmp (PID: 2964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 72704 |
| InitializedDataSize: | 30720 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12348 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.9.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | This installation was built with AiR FE. |
| CompanyName: | |
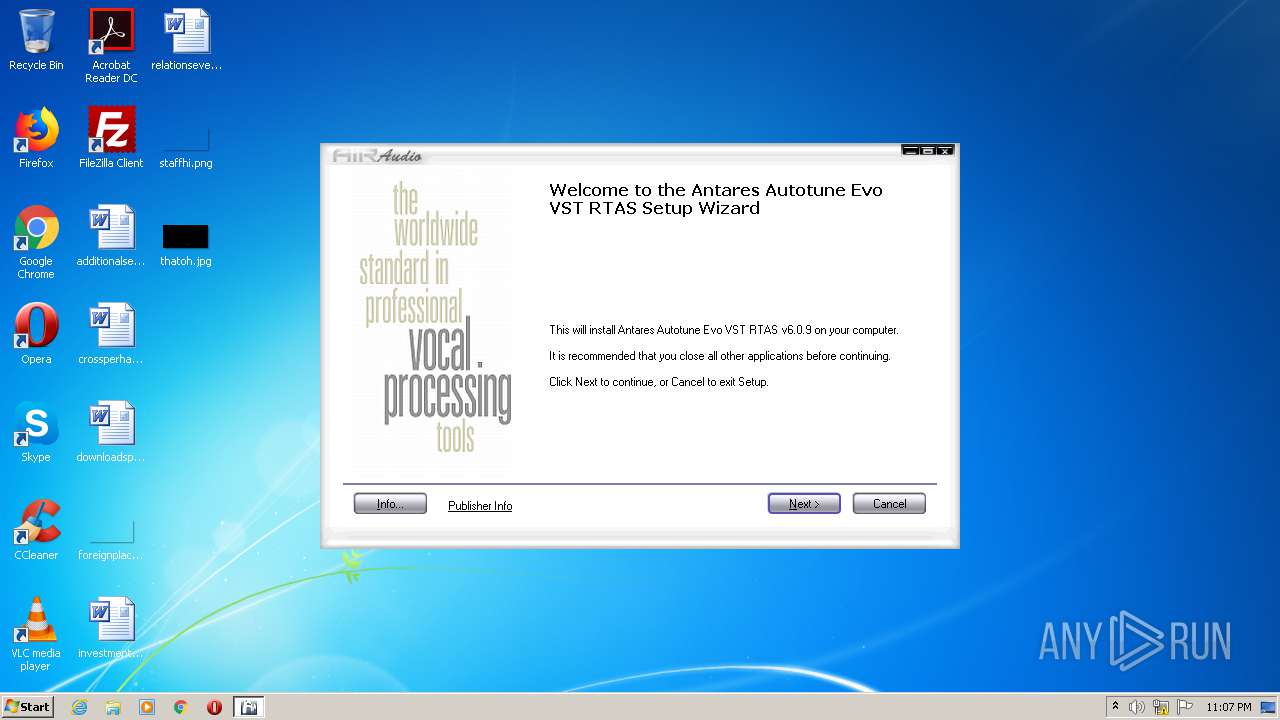
| FileDescription: | Antares Autotune Evo VST RTAS Setup |
| FileVersion: | 6.0.9.0 |
| LegalCopyright: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with AiR FE. |
| CompanyName: | - |
| FileDescription: | Antares Autotune Evo VST RTAS Setup |
| FileVersion: | 6.0.9.0 |
| LegalCopyright: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00010EC4 | 0x00011000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51747 |
.itext | 0x00012000 | 0x00000A68 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.65251 |
.data | 0x00013000 | 0x00000D10 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.52201 |
.bss | 0x00014000 | 0x00003BB8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00018000 | 0x00000EE2 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.77881 |
.tls | 0x00019000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001A000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.reloc | 0x0001B000 | 0x00001568 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.61169 |
.rsrc | 0x0001D000 | 0x00004130 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.37261 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94378 | 1150 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4091 | 2.8508 | 144 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.36848 | 196 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.38569 | 304 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.27129 | 964 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34727 | 812 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4096 | 3.29535 | 640 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11111 | 4.61354 | 44 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.22647 | 344 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
42
Monitored processes
4
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
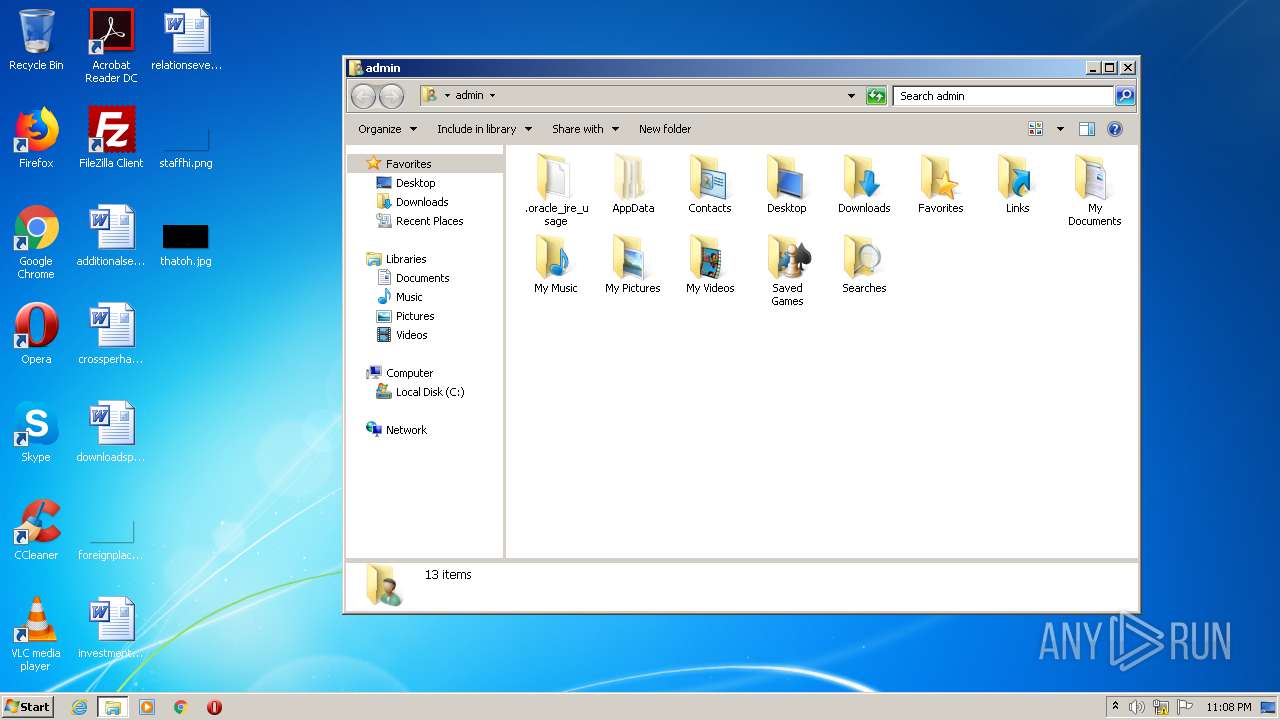
| 2572 | "C:\Users\admin\Downloads\setup.exe" /SPAWNWND=$5013E /NOTIFYWND=$50138 | C:\Users\admin\Downloads\setup.exe | setup.exe.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Antares Autotune Evo VST RTAS Setup Exit code: 0 Version: 6.0.9.0 Modules
| |||||||||||||||
| 2964 | "C:\Users\admin\AppData\Local\Temp\is-269QI.tmp\setup.exe.tmp" /SL5="$6013A,4131844,104448,C:\Users\admin\Downloads\setup.exe" /SPAWNWND=$5013E /NOTIFYWND=$50138 | C:\Users\admin\AppData\Local\Temp\is-269QI.tmp\setup.exe.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.48.0.0 Modules
| |||||||||||||||
| 3036 | "C:\Users\admin\Downloads\setup.exe" | C:\Users\admin\Downloads\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Antares Autotune Evo VST RTAS Setup Exit code: 0 Version: 6.0.9.0 Modules
| |||||||||||||||
| 4084 | "C:\Users\admin\AppData\Local\Temp\is-V5T1Q.tmp\setup.exe.tmp" /SL5="$50138,4131844,104448,C:\Users\admin\Downloads\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-V5T1Q.tmp\setup.exe.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.48.0.0 Modules
| |||||||||||||||
Total events
699
Read events
683
Write events
16
Delete events
0
Modification events
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.2.0 | |||
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Antares Audio Technologies | |||
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Antares Audio Technologies\ | |||
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Antares Audio Technologies | |||
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | Inno Setup: Setup Type |
Value: full | |||
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | Inno Setup: Selected Components |
Value: main,vst | |||
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Components |
Value: rtas | |||
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | DisplayName |
Value: Antares Autotune Evo VST RTAS v6.0.9 | |||
| (PID) Process: | (2964) setup.exe.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Antares Autotune Evo VST RTAS_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: D:\InnoFE\GFX\AiR.ico | |||
Executable files
13
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | setup.exe.tmp | C:\Program Files\Antares Audio Technologies\Uninstall\is-BK7DG.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | setup.exe.tmp | C:\Program Files\Antares Audio Technologies\Uninstall\RCX7A27.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | setup.exe.tmp | C:\Program Files\Steinberg\VstPlugins\is-TOU96.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | setup.exe.tmp | C:\Users\admin\AppData\Roaming\Antares\is-2THIQ.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | setup.exe.tmp | C:\Users\admin\AppData\Roaming\Antares\is-4SUV9.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | setup.exe.tmp | C:\Windows\system32\is-58AAT.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | setup.exe.tmp | C:\Windows\system32\is-0TL78.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | setup.exe.tmp | C:\Program Files\Antares Audio Technologies\Auto-Tune Evo\is-51E08.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | setup.exe.tmp | C:\Program Files\Antares Audio Technologies\Auto-Tune Evo\ATEvo_manual.pdf | — | |
MD5:— | SHA256:— | |||
| 4084 | setup.exe.tmp | C:\Users\admin\AppData\Local\Temp\tmpMM18D9E0.tmp | executable | |
MD5:0BE4A226874ECCB9F8BFE3D8DCED0C09 | SHA256:D98CD5D6ED9C4A95701684AA83777CEFD5D8096E14C836493F67159D68161C01 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report