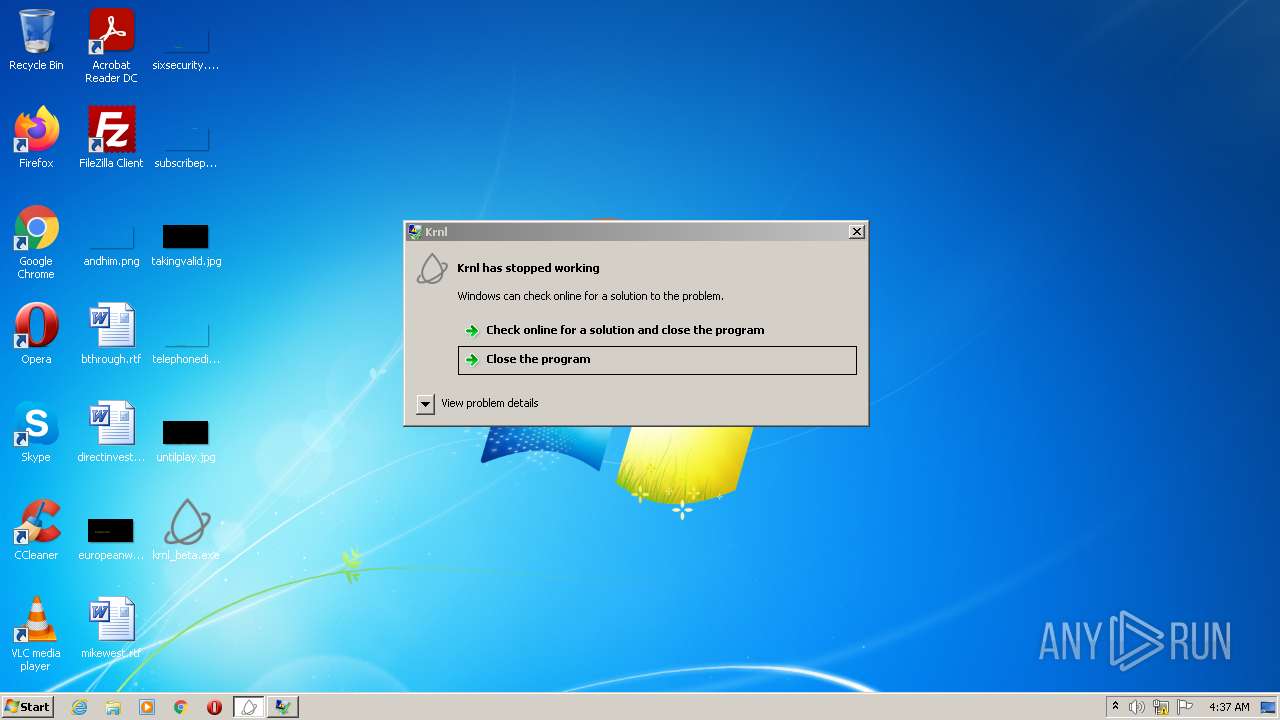
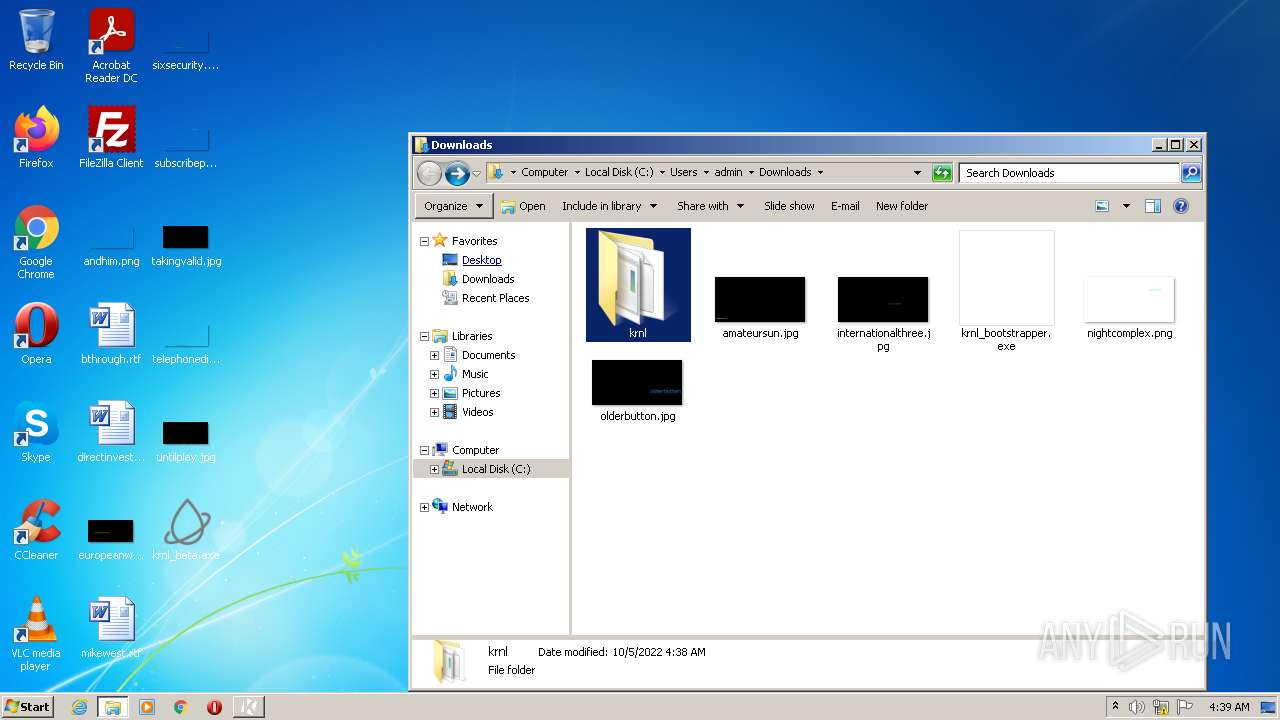
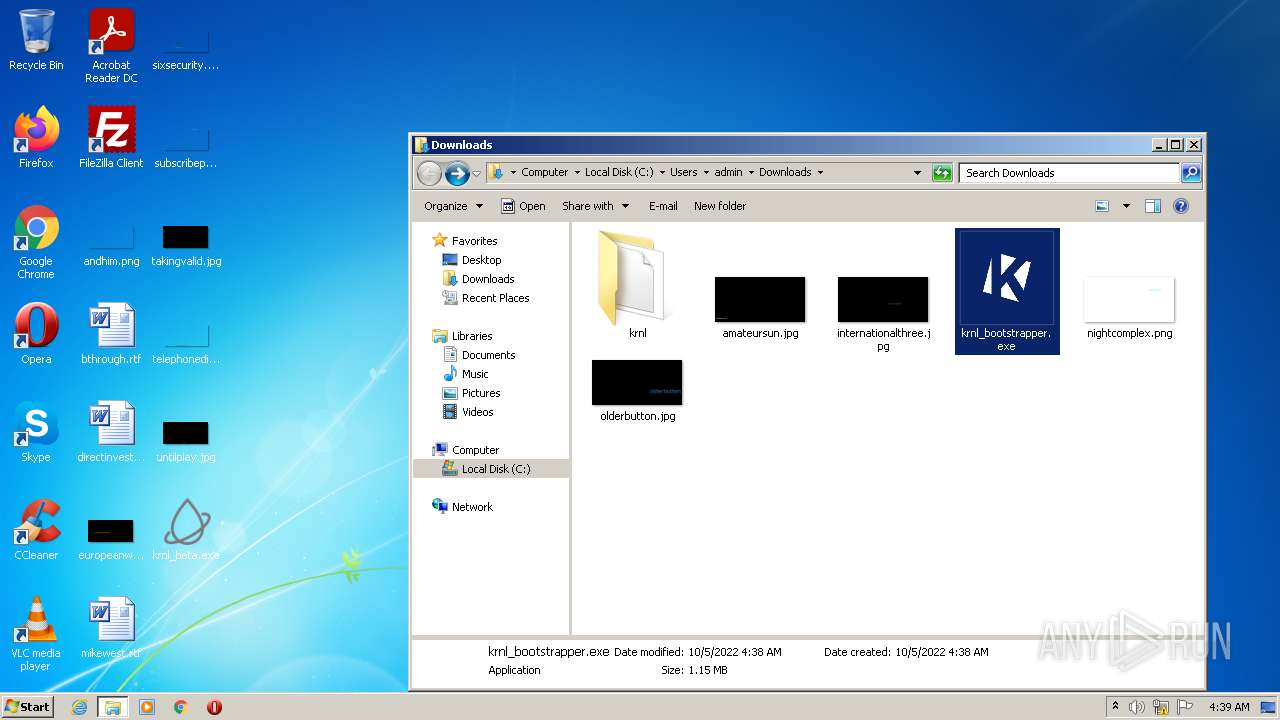
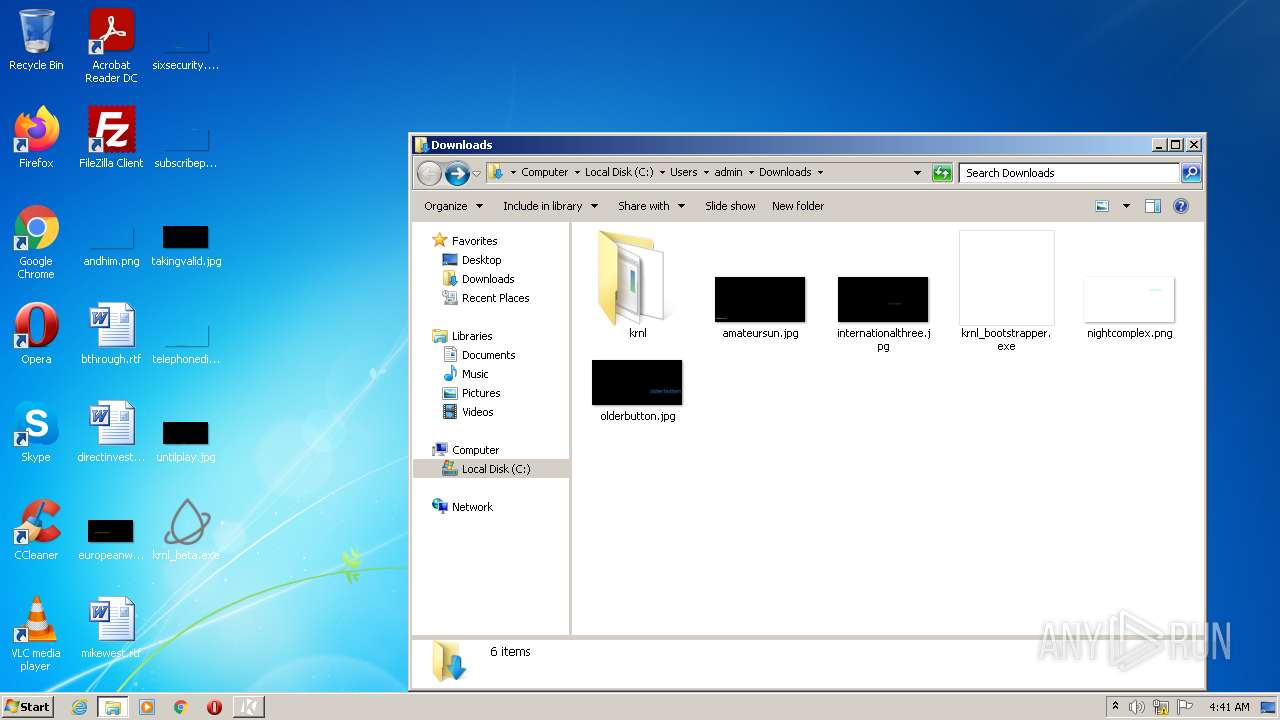
| File name: | krnl_beta.exe |
| Full analysis: | https://app.any.run/tasks/07247d56-3e46-4f2c-8e14-ea643349257e |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 03:37:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 3701DC535FB395D6A1FB557A3AEEC5E9 |
| SHA1: | EF517659229DDC6ECFC02481C3953AC9322DAE35 |
| SHA256: | EC6DF713446A8DD5EFB376FBB7B444ED7E09F5CDD98C0494999B64AF2E2D5537 |
| SSDEEP: | 49152:+P1uB0SVp4+KSxyrRUzS65+x+rnxYr9PC:+Pk0ST4+RgRUzS65+x1ZPC |
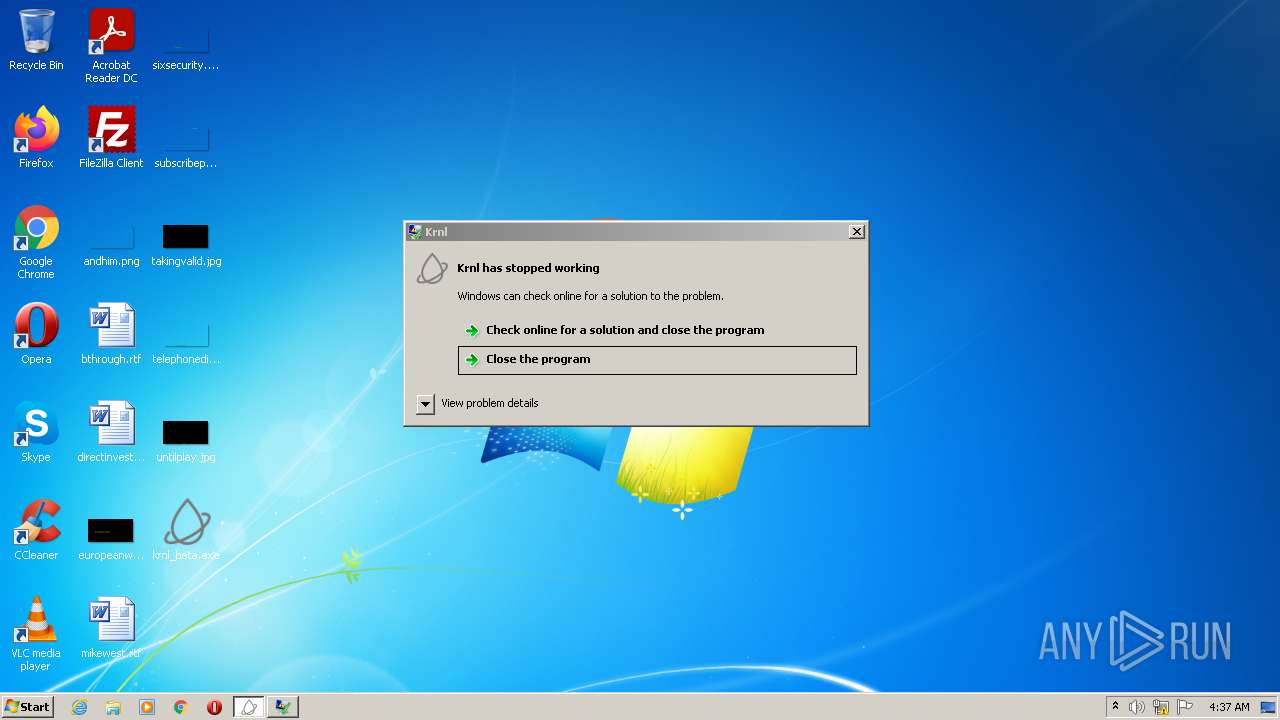
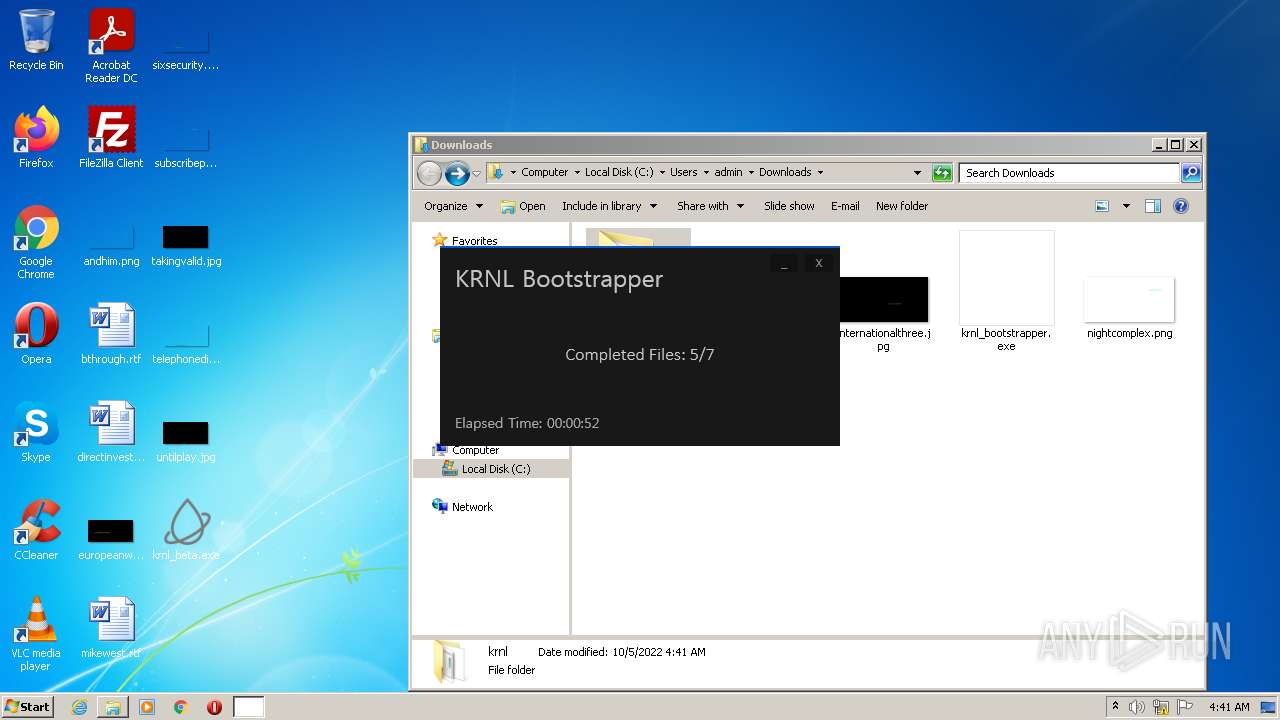
MALICIOUS
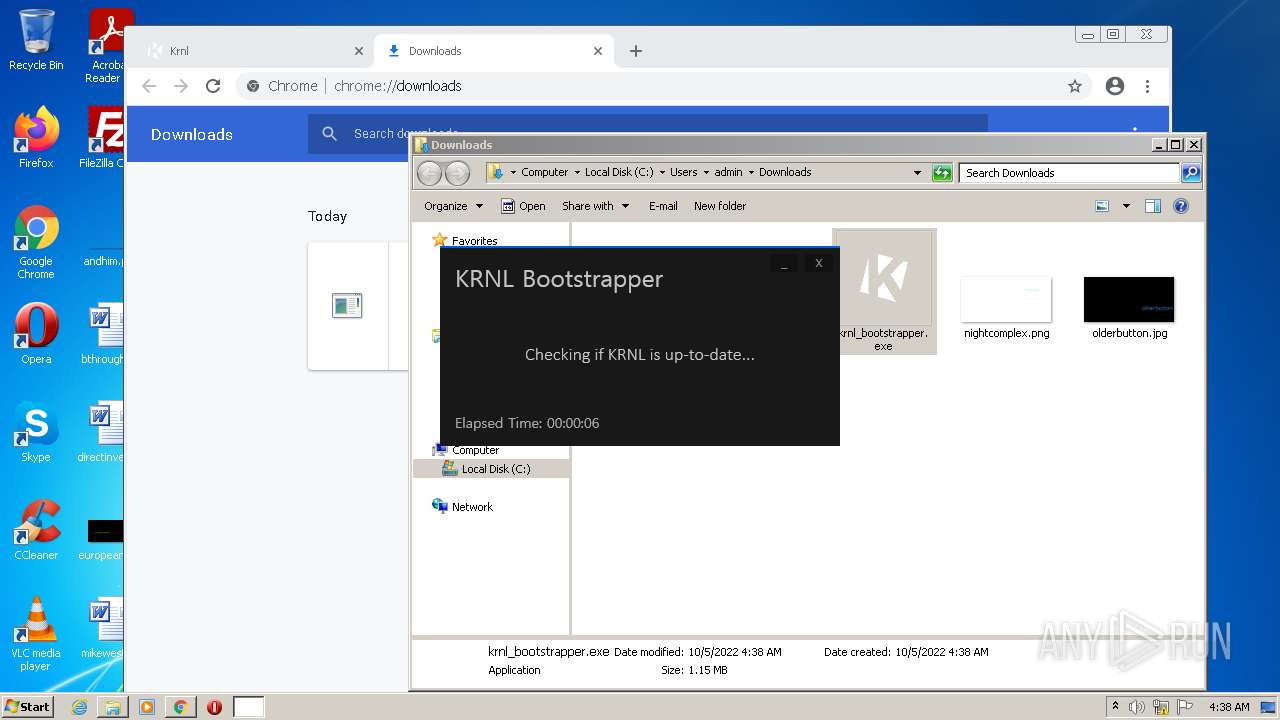
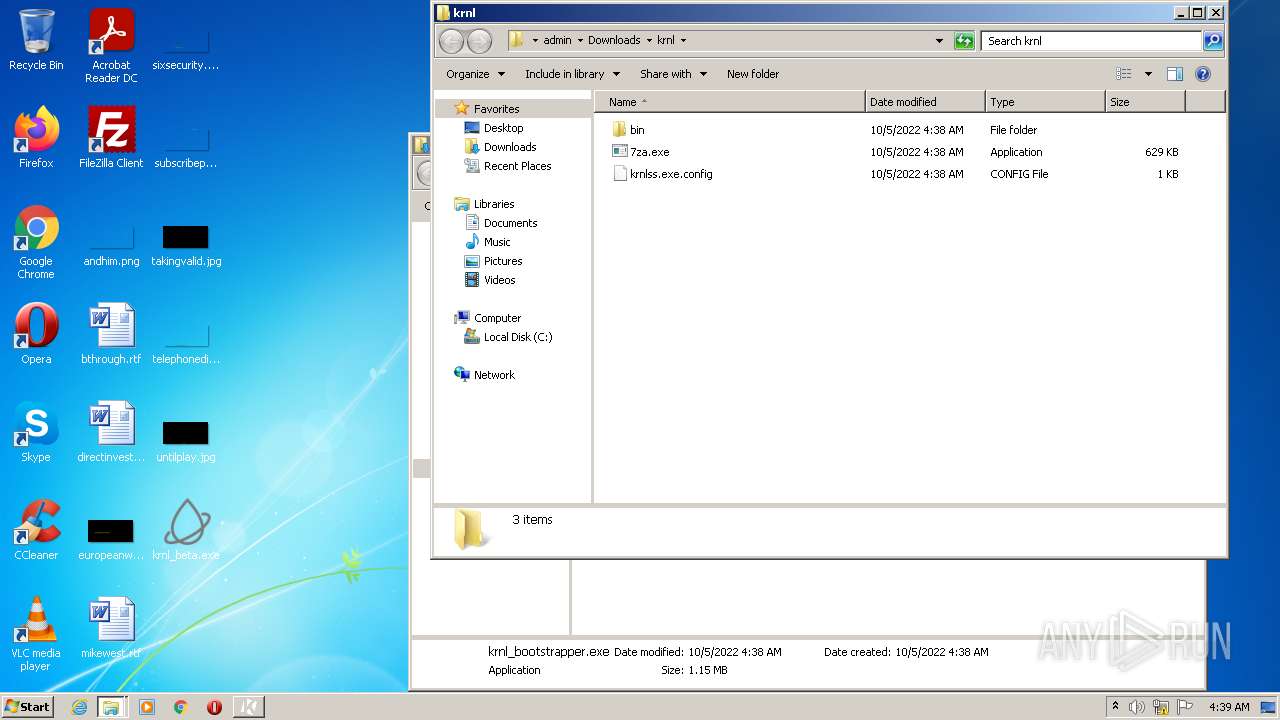
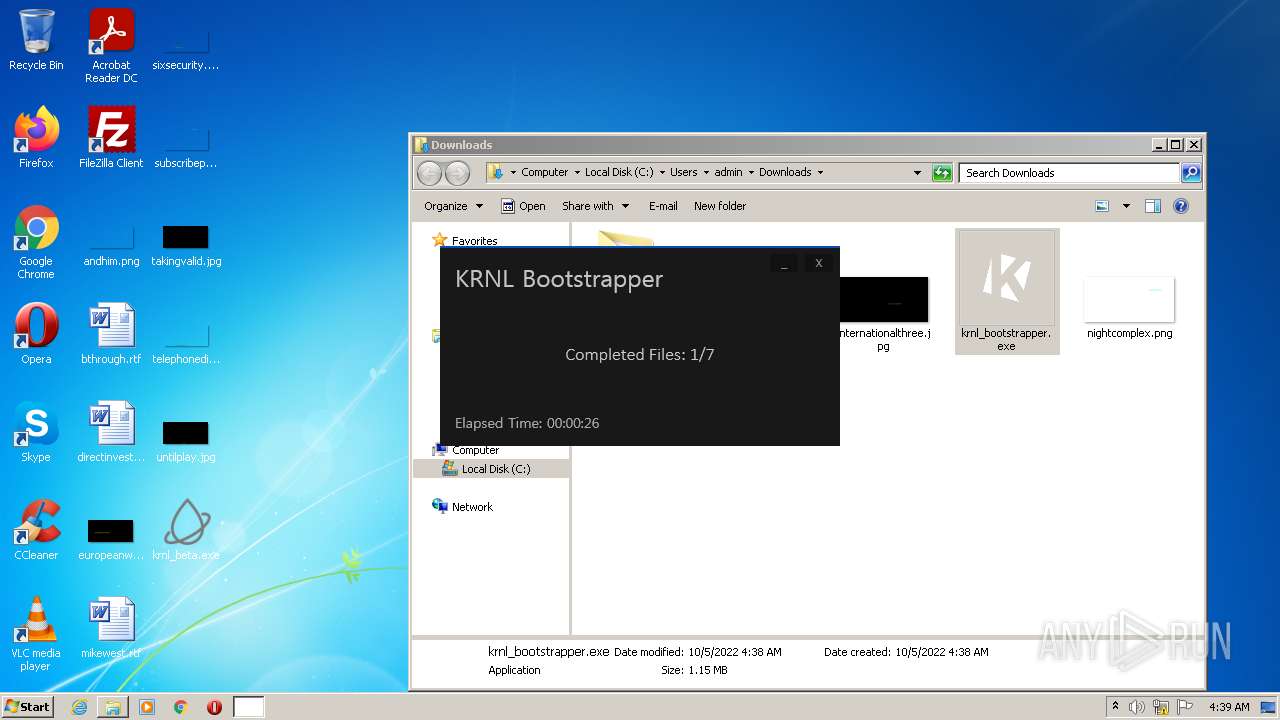
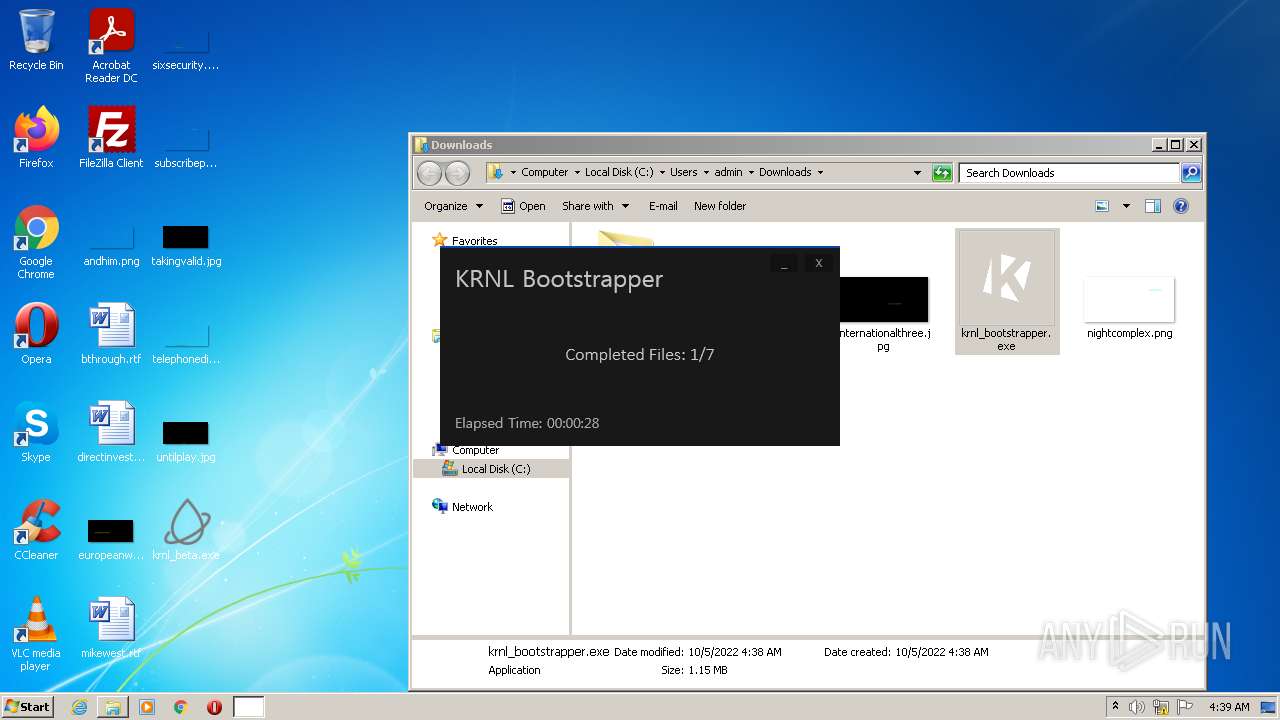
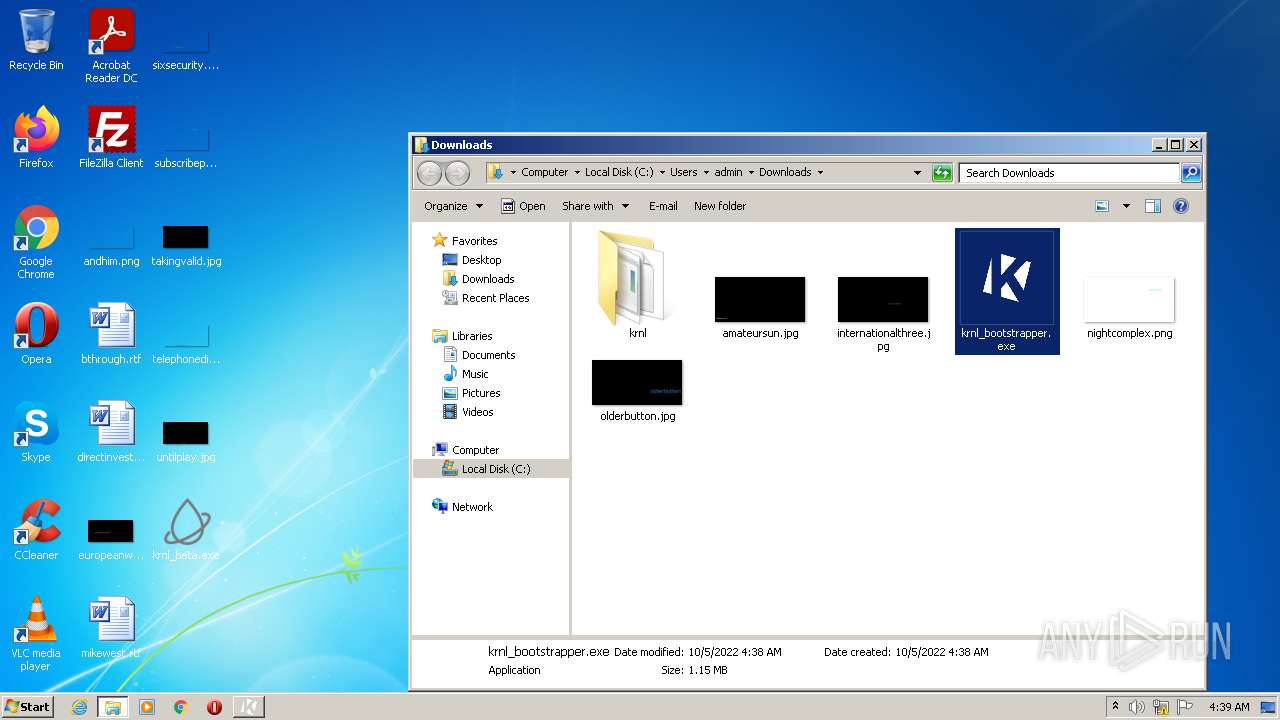
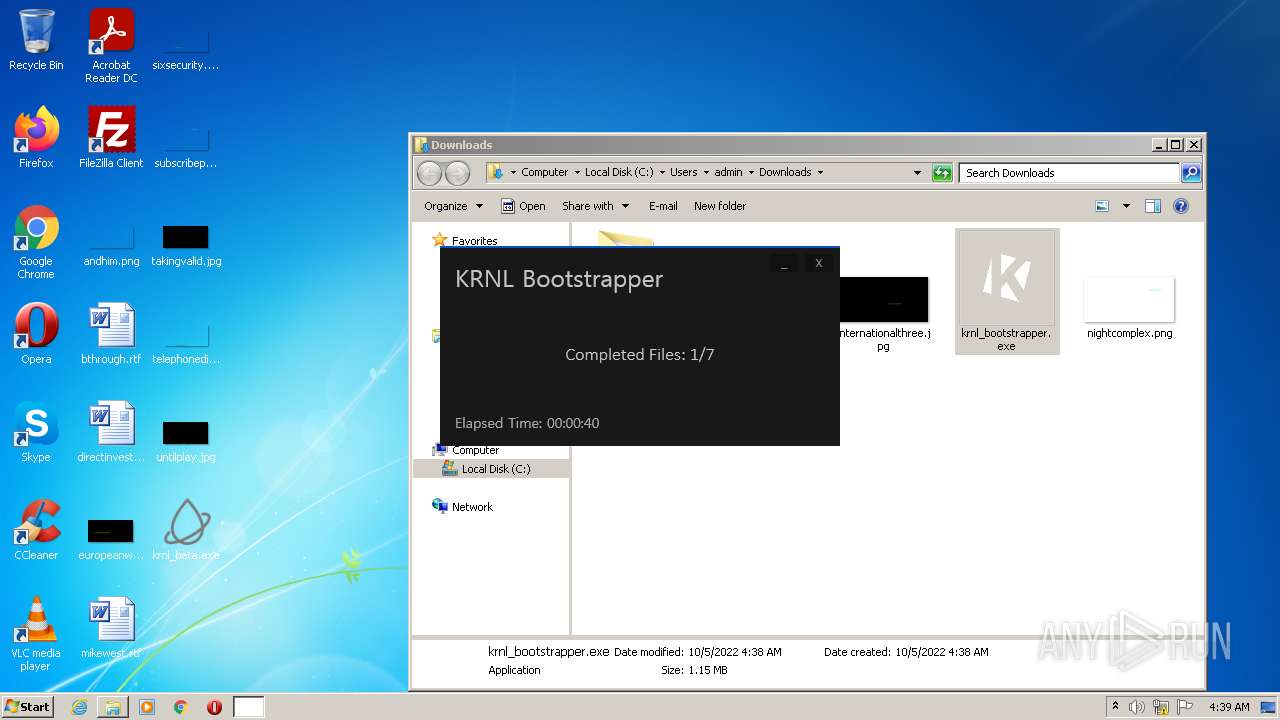
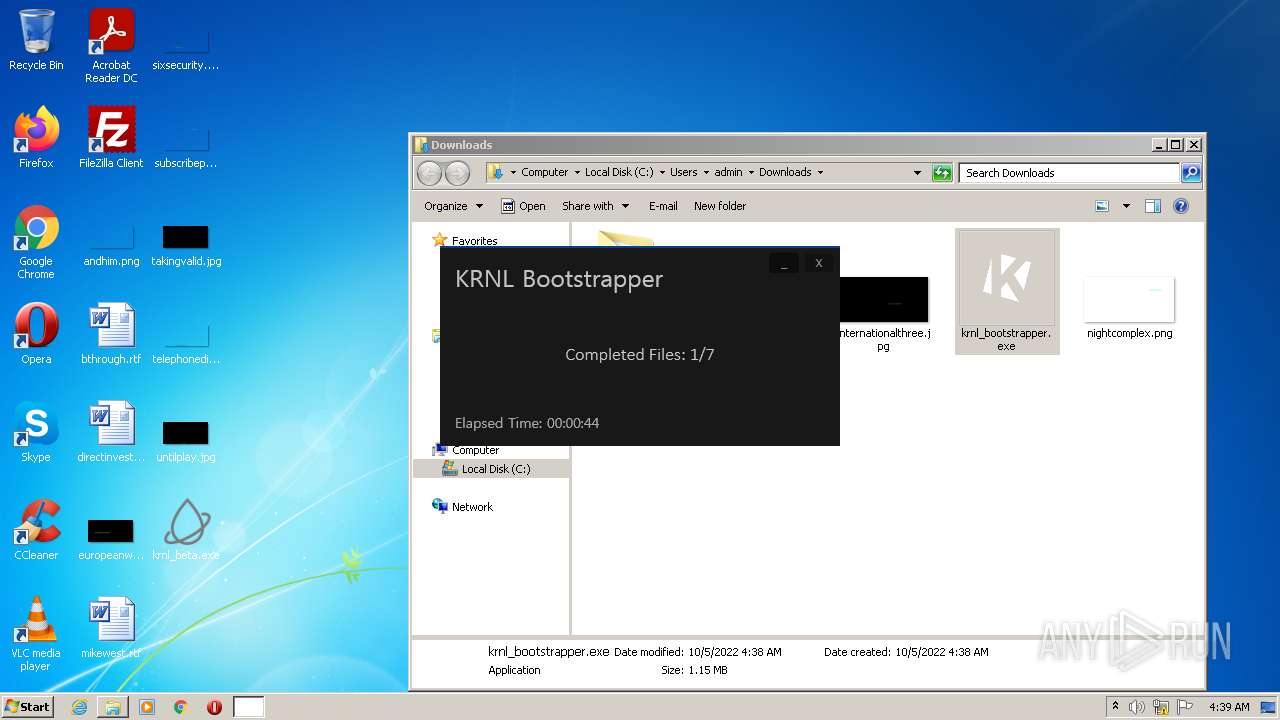
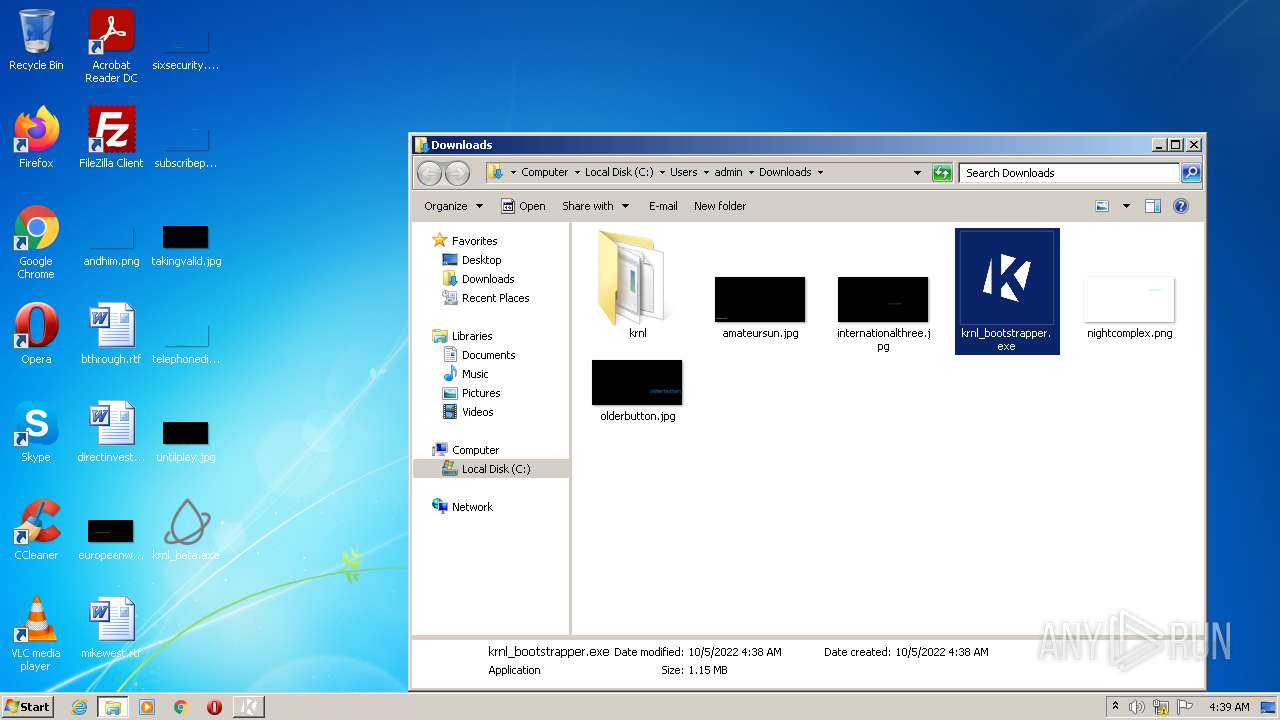
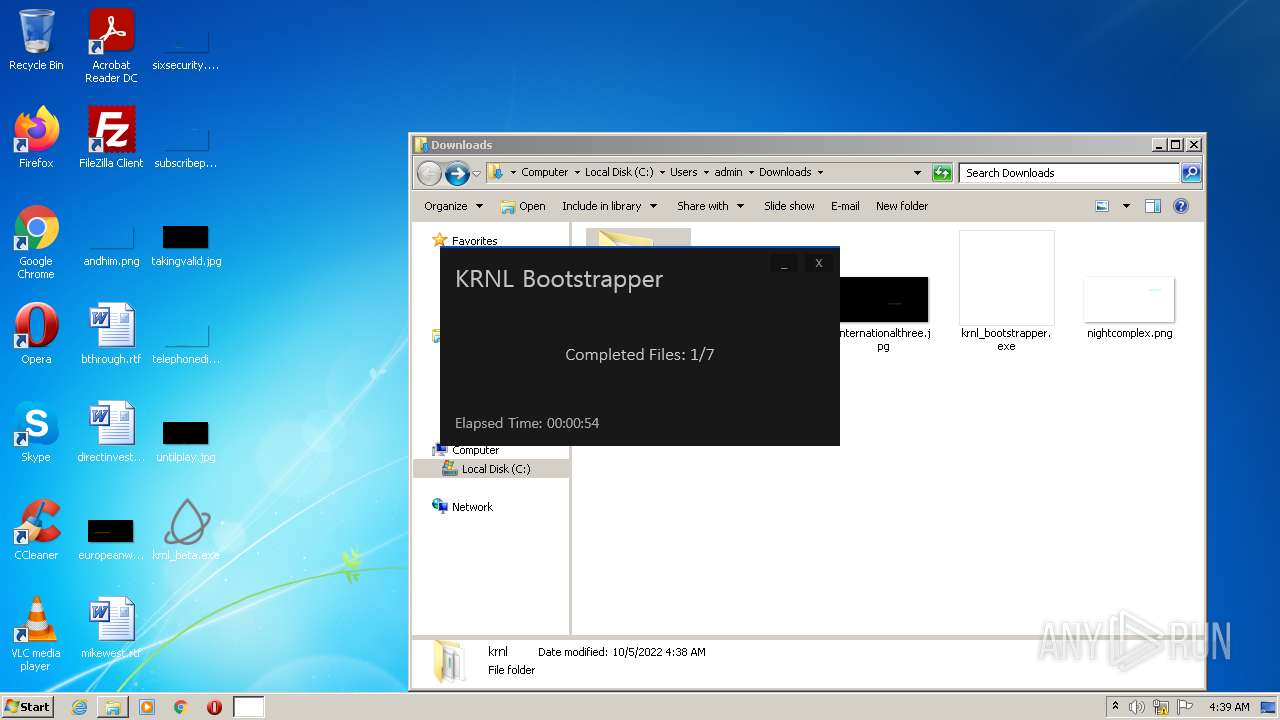
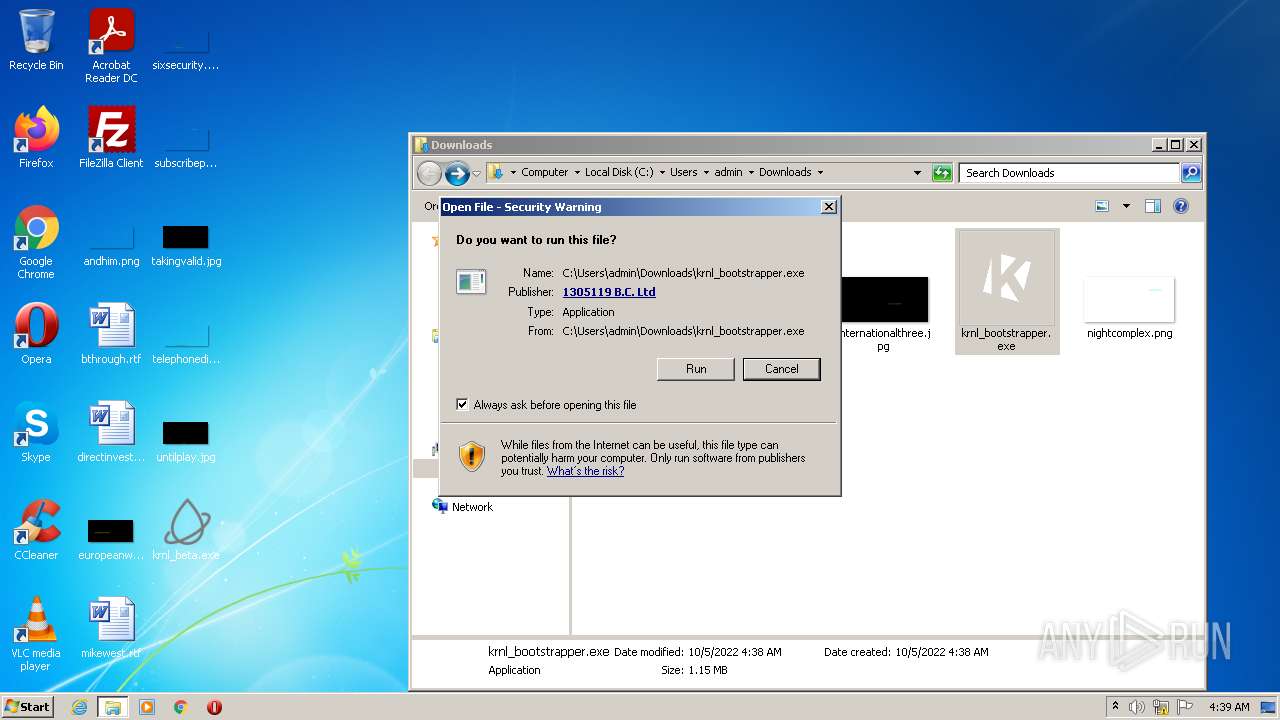
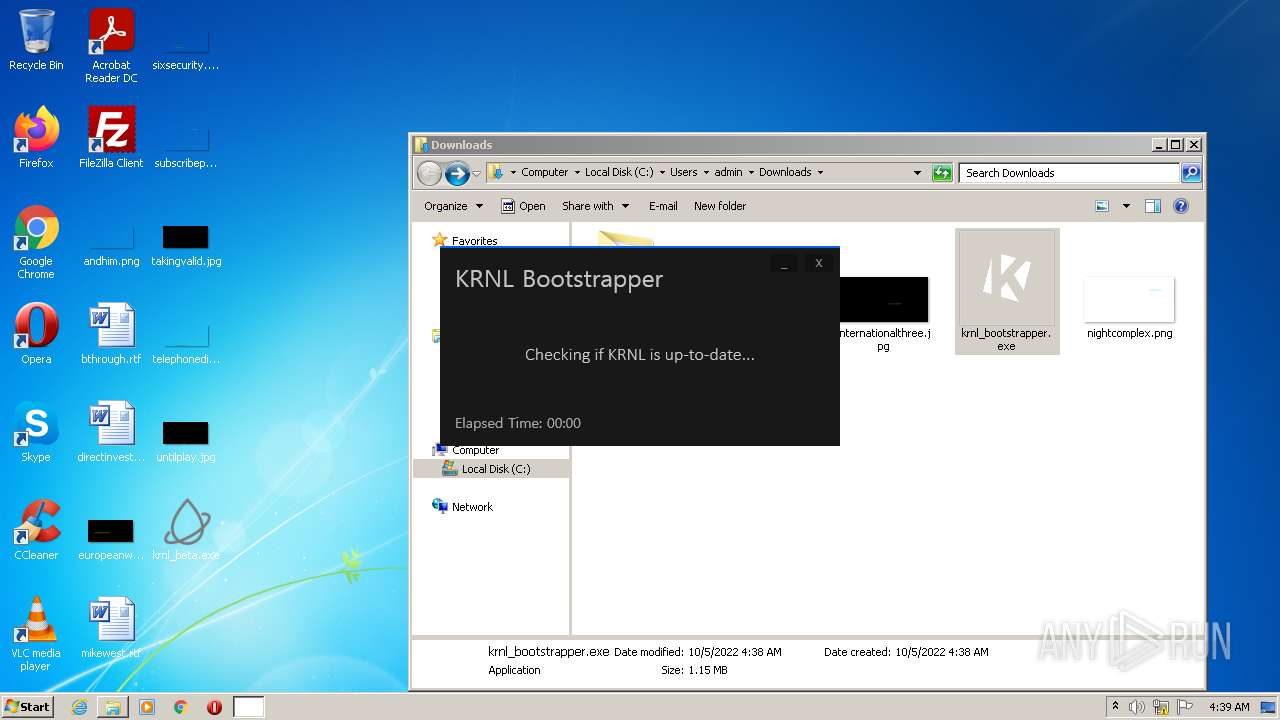
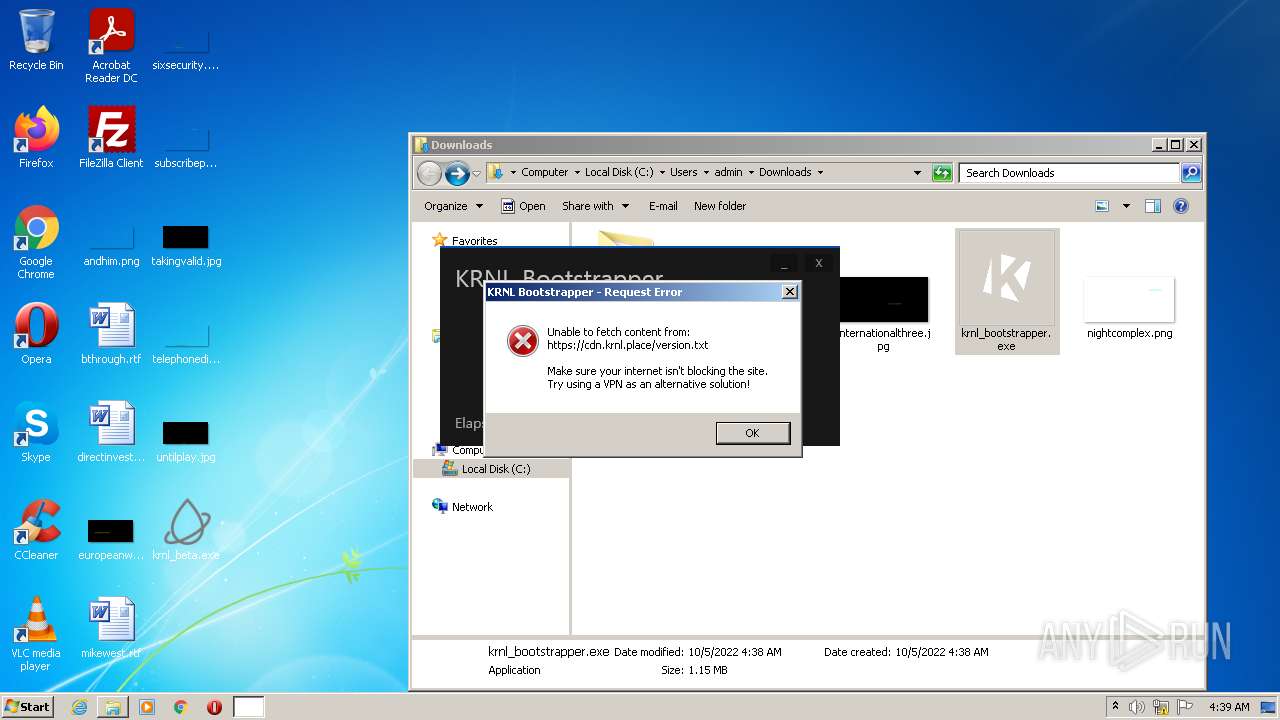
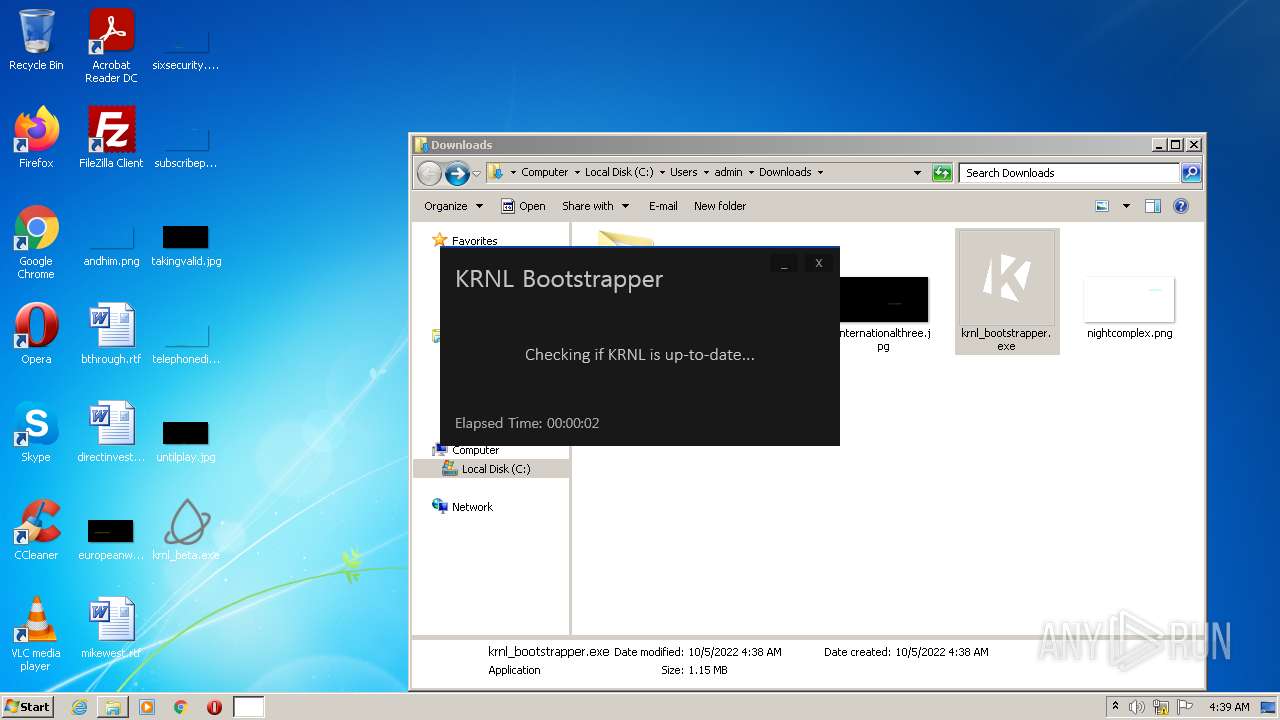
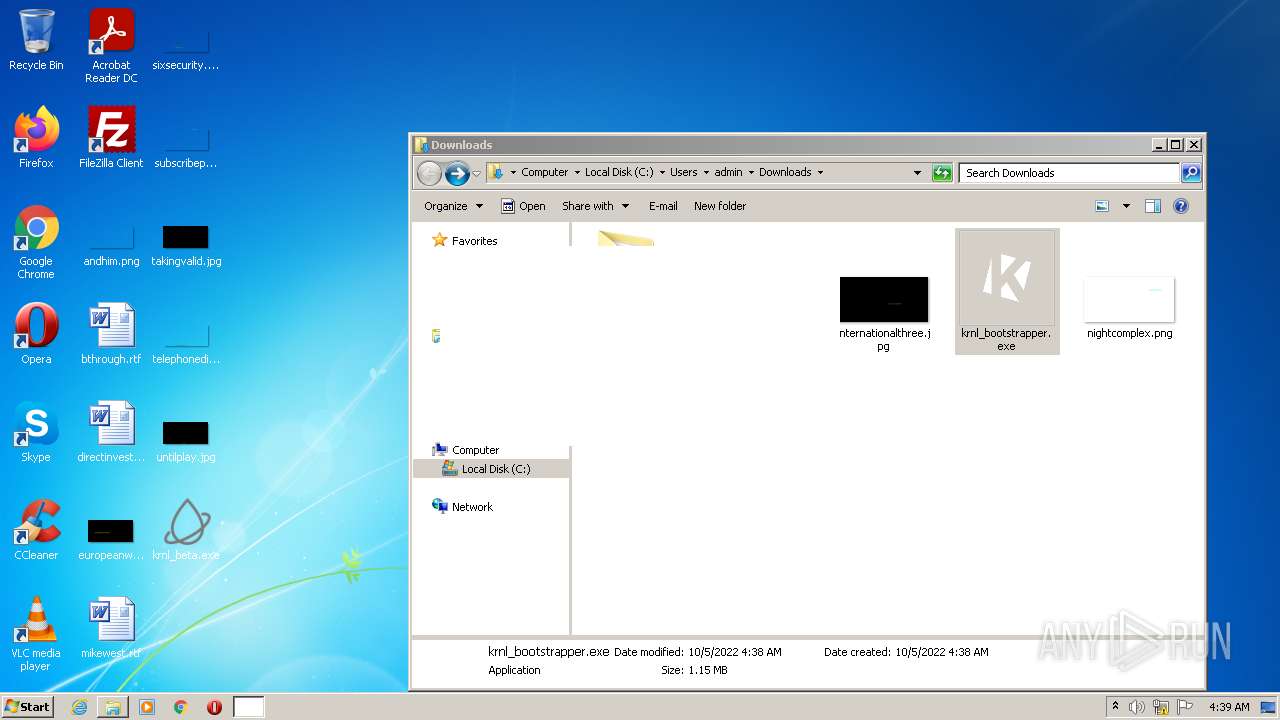
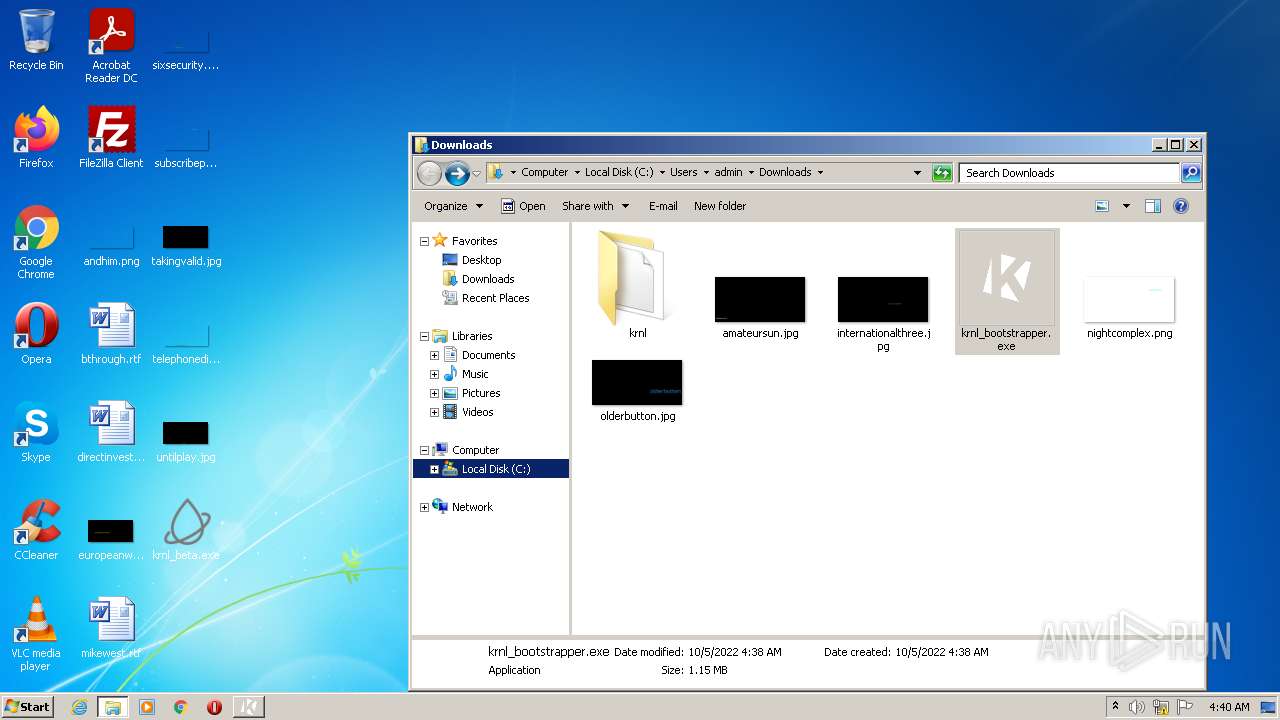
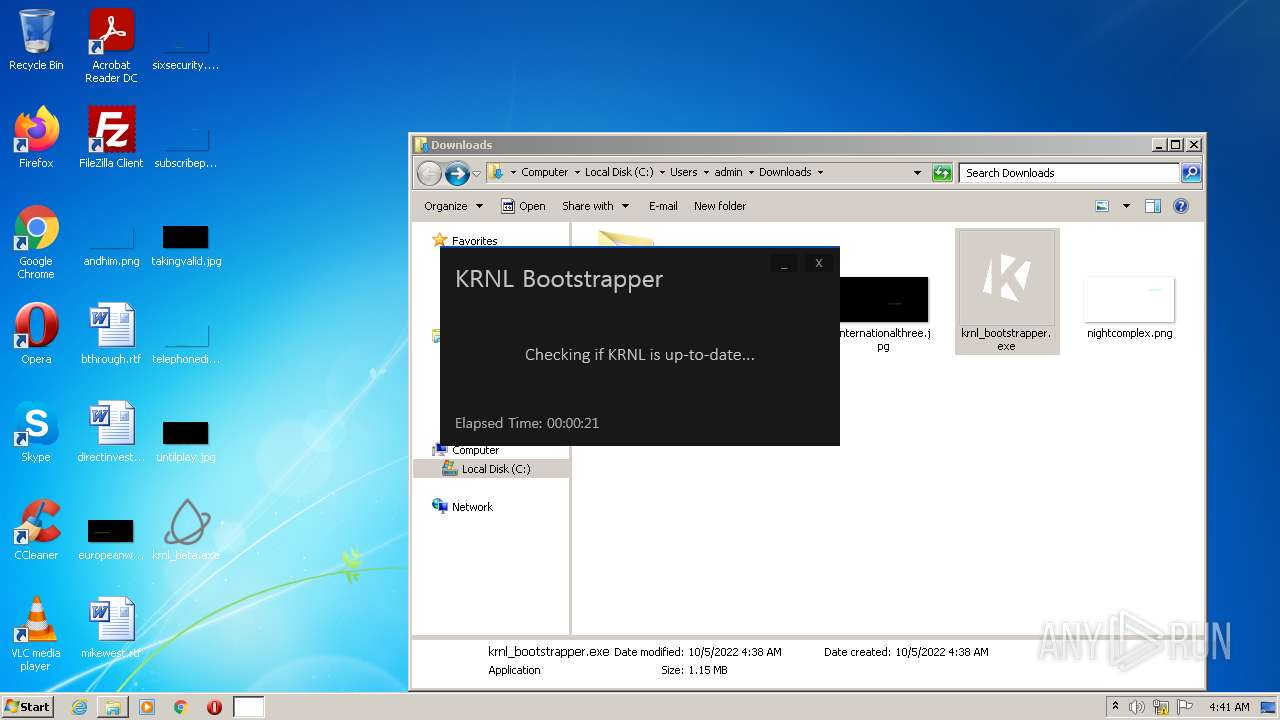
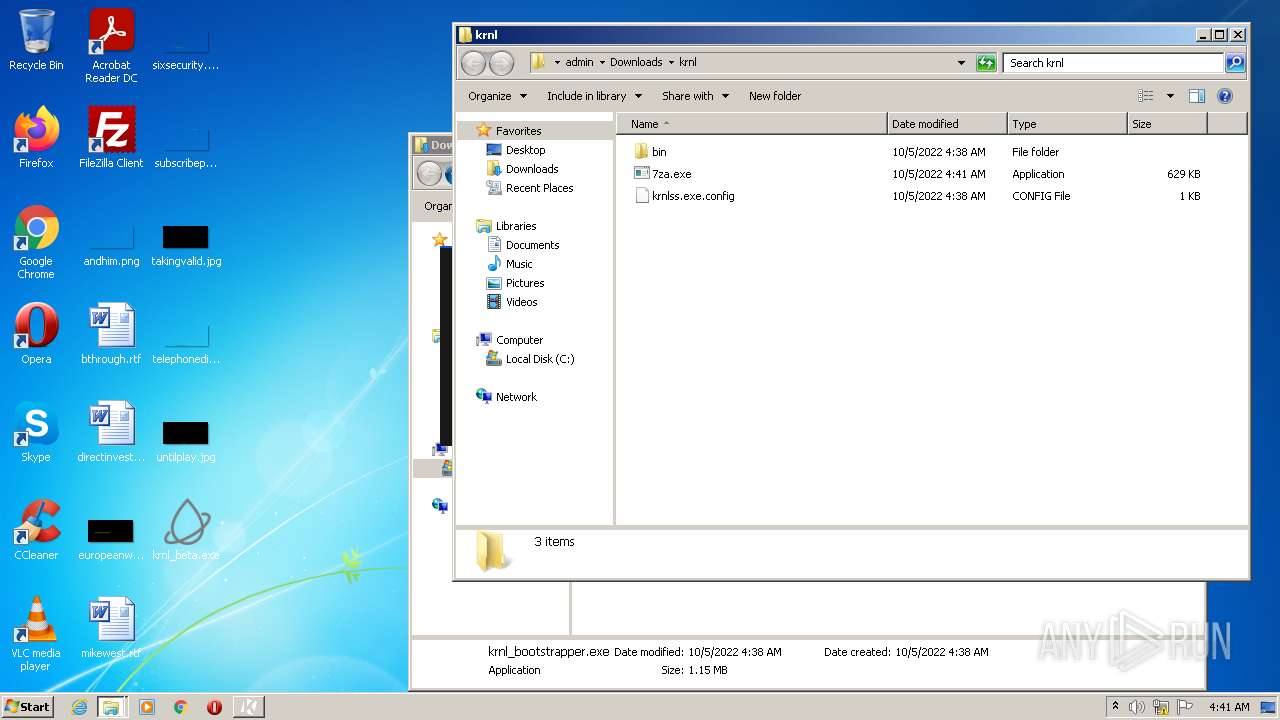
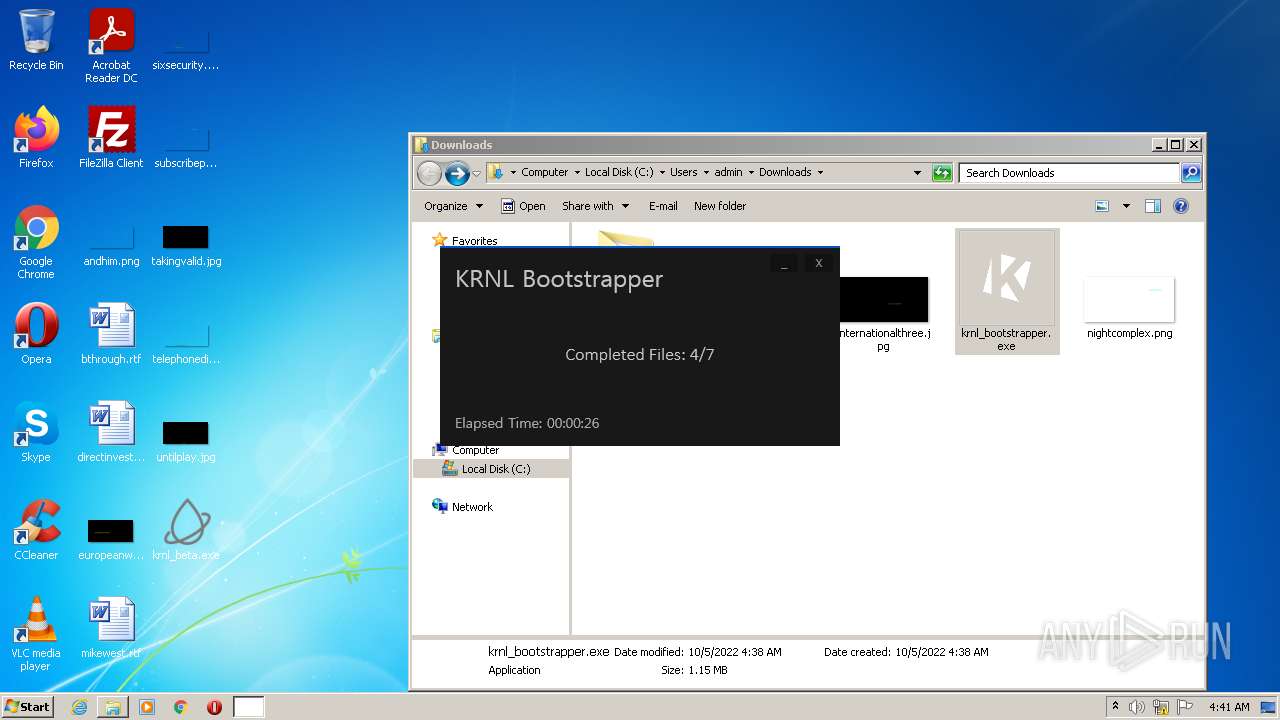
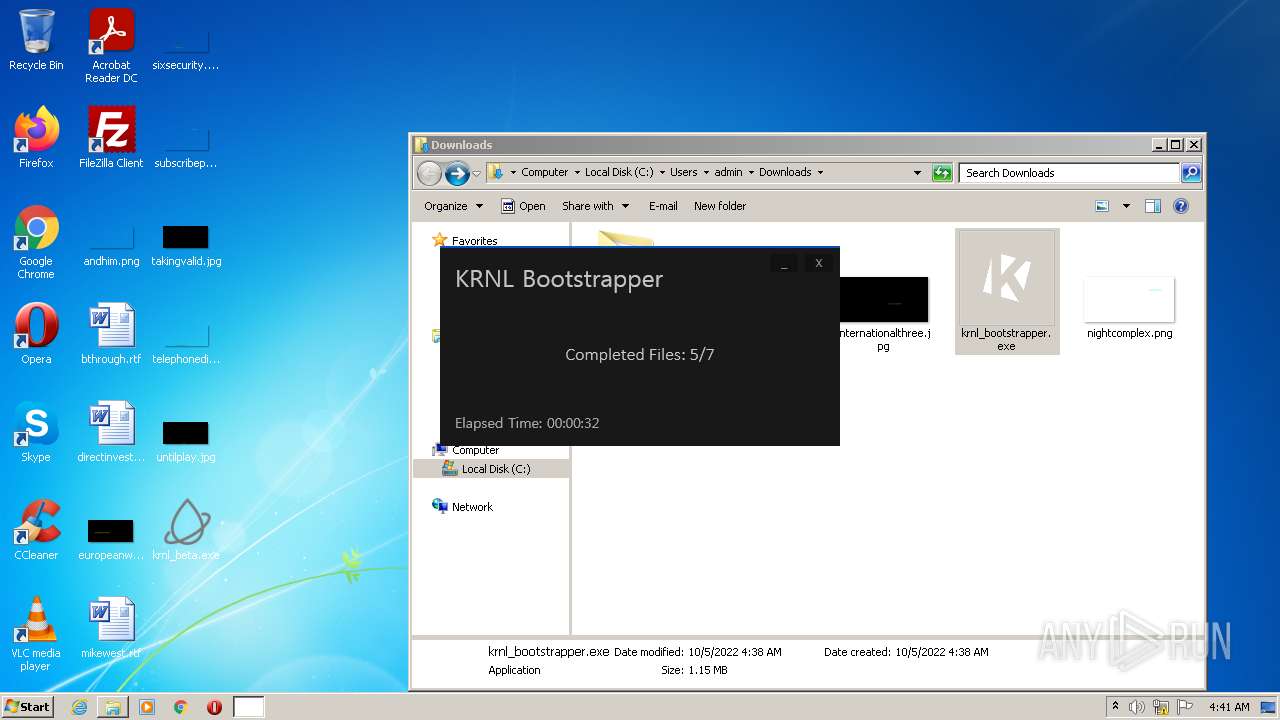
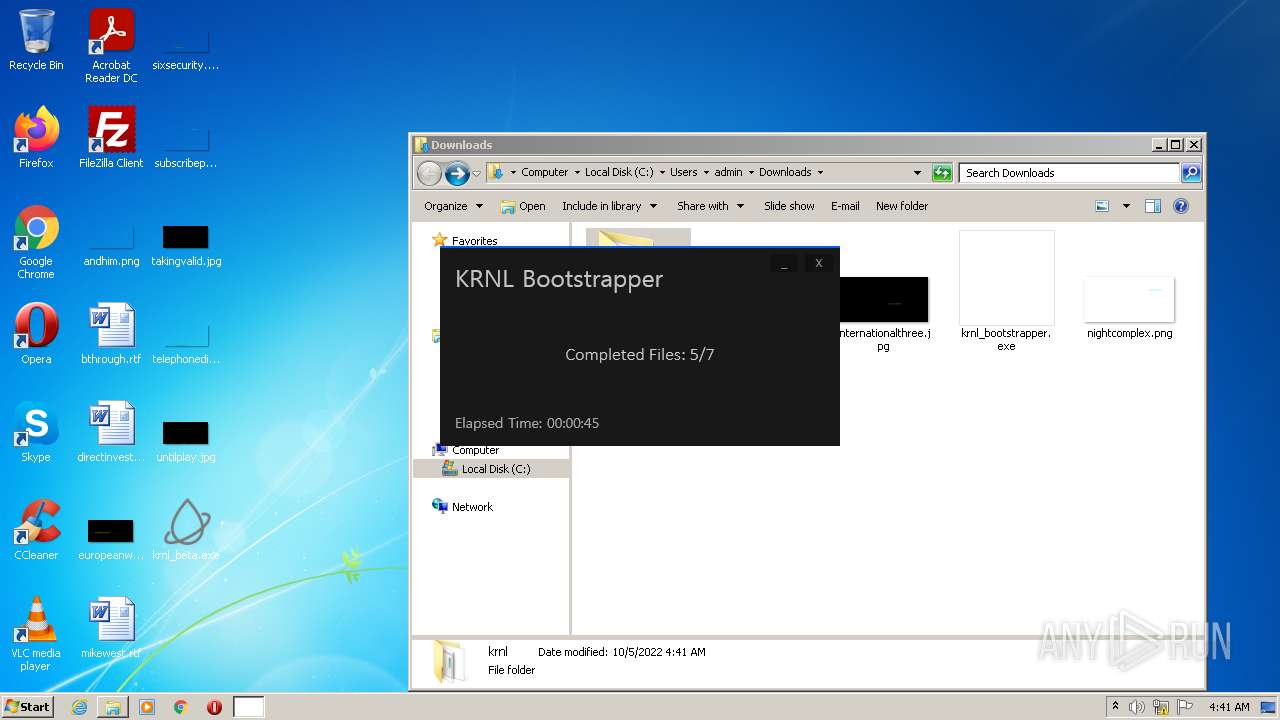
Application was dropped or rewritten from another process
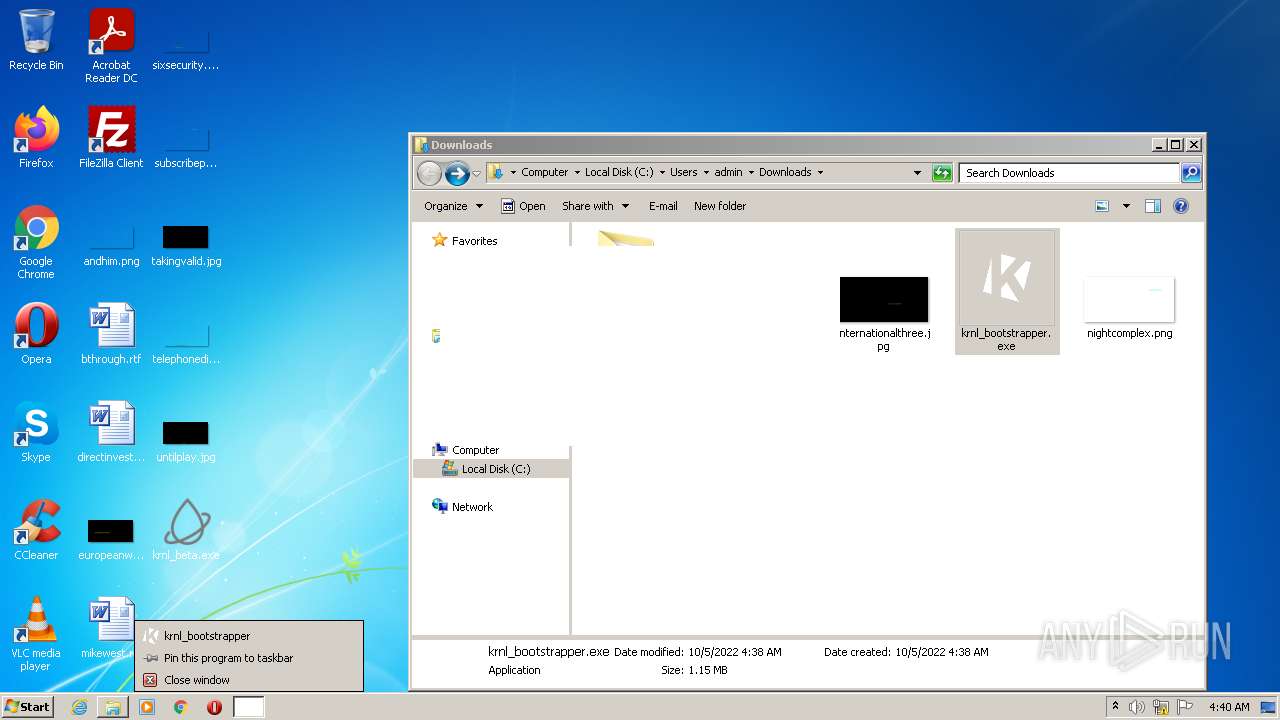
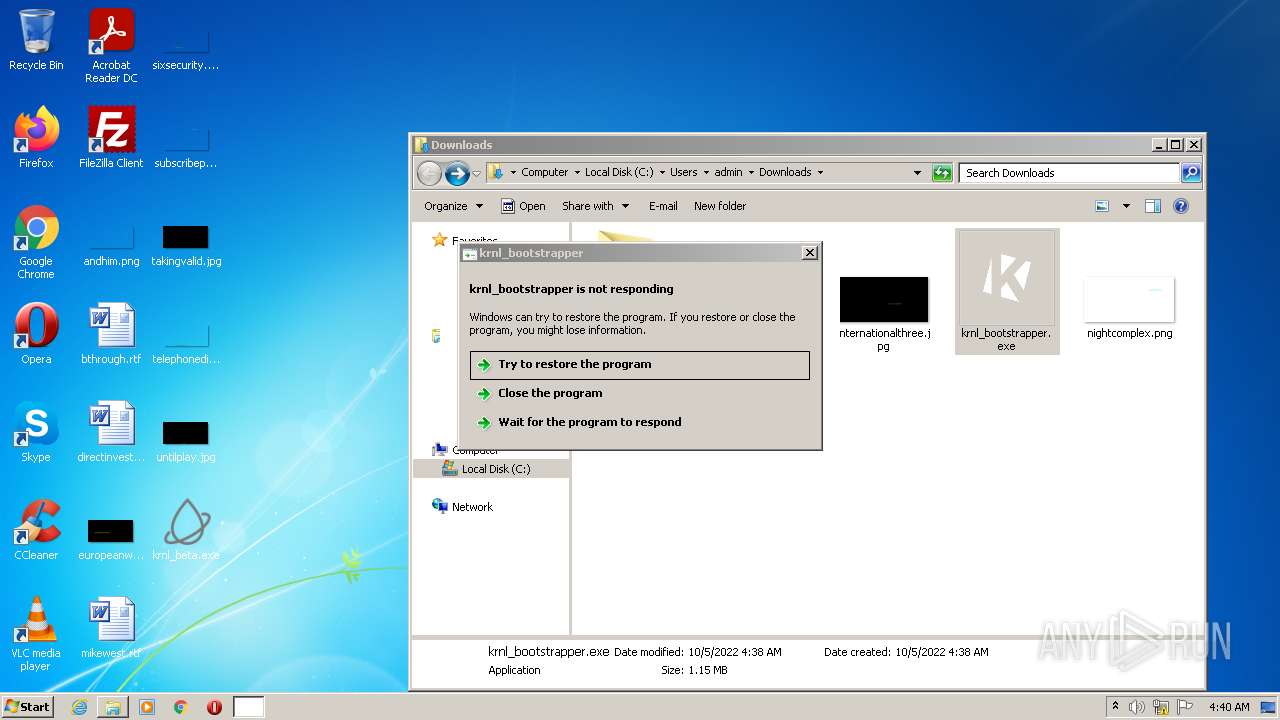
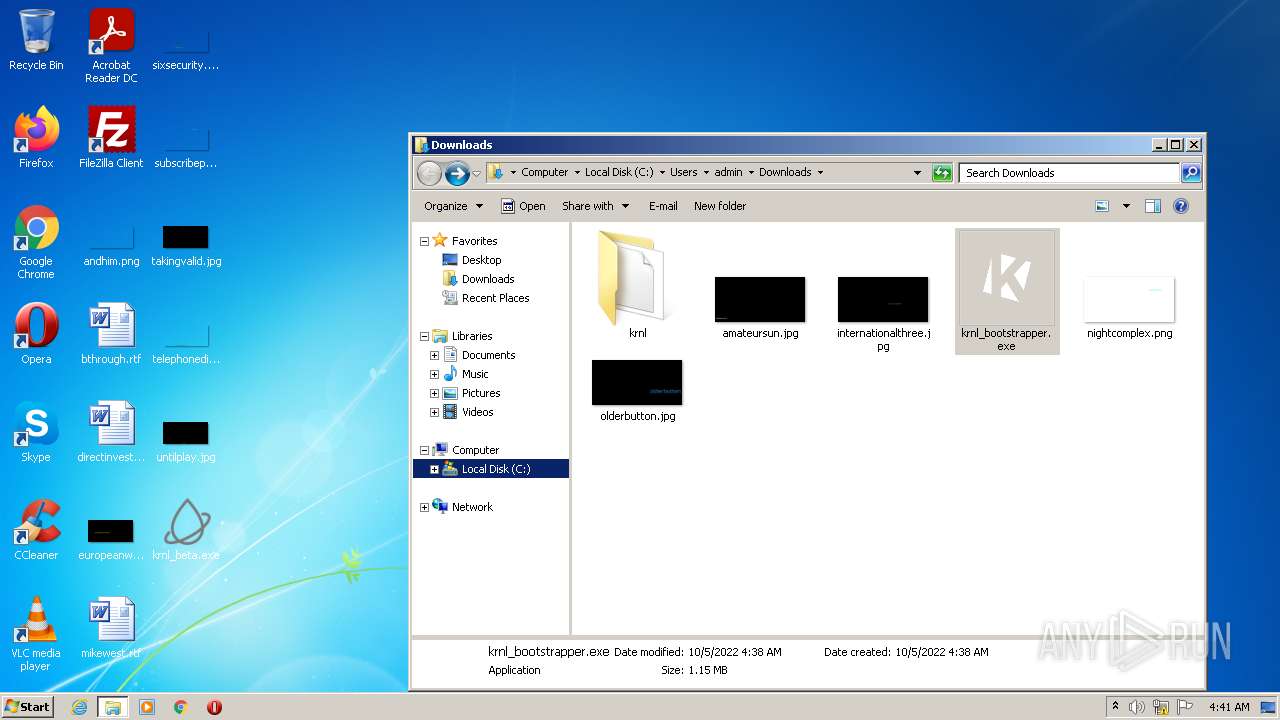
- krnl_bootstrapper.exe (PID: 2120)
- krnl_bootstrapper.exe (PID: 3068)
- krnl_bootstrapper.exe (PID: 320)
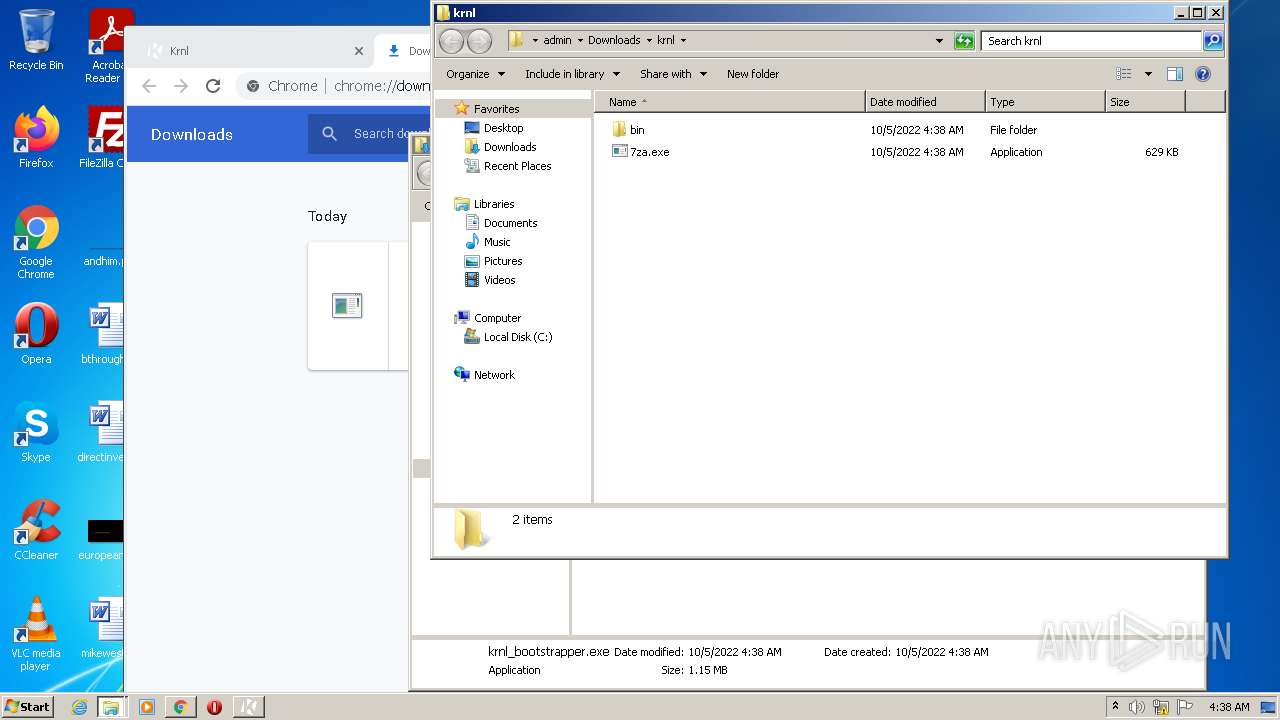
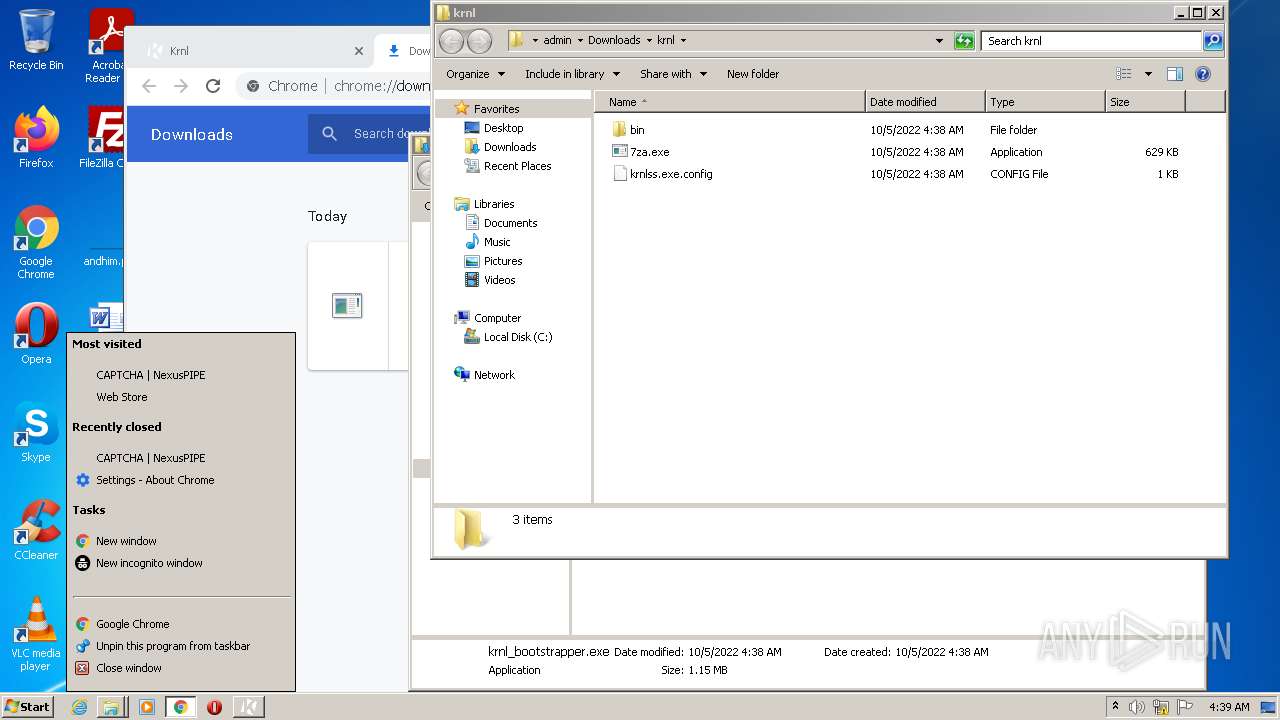
- 7za.exe (PID: 2032)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 884)
SUSPICIOUS
Reads the computer name
- krnl_beta.exe (PID: 3396)
- krnl_beta.exe (PID: 3020)
- krnl_bootstrapper.exe (PID: 3068)
- krnl_bootstrapper.exe (PID: 2120)
- 7za.exe (PID: 2032)
- krnl_bootstrapper.exe (PID: 320)
Checks supported languages
- krnl_beta.exe (PID: 3396)
- krnl_beta.exe (PID: 3020)
- krnl_bootstrapper.exe (PID: 3068)
- krnl_bootstrapper.exe (PID: 2120)
- krnl_bootstrapper.exe (PID: 320)
- 7za.exe (PID: 2032)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2592)
Reads Environment values
- krnl_bootstrapper.exe (PID: 3068)
- krnl_bootstrapper.exe (PID: 2120)
- krnl_bootstrapper.exe (PID: 320)
INFO
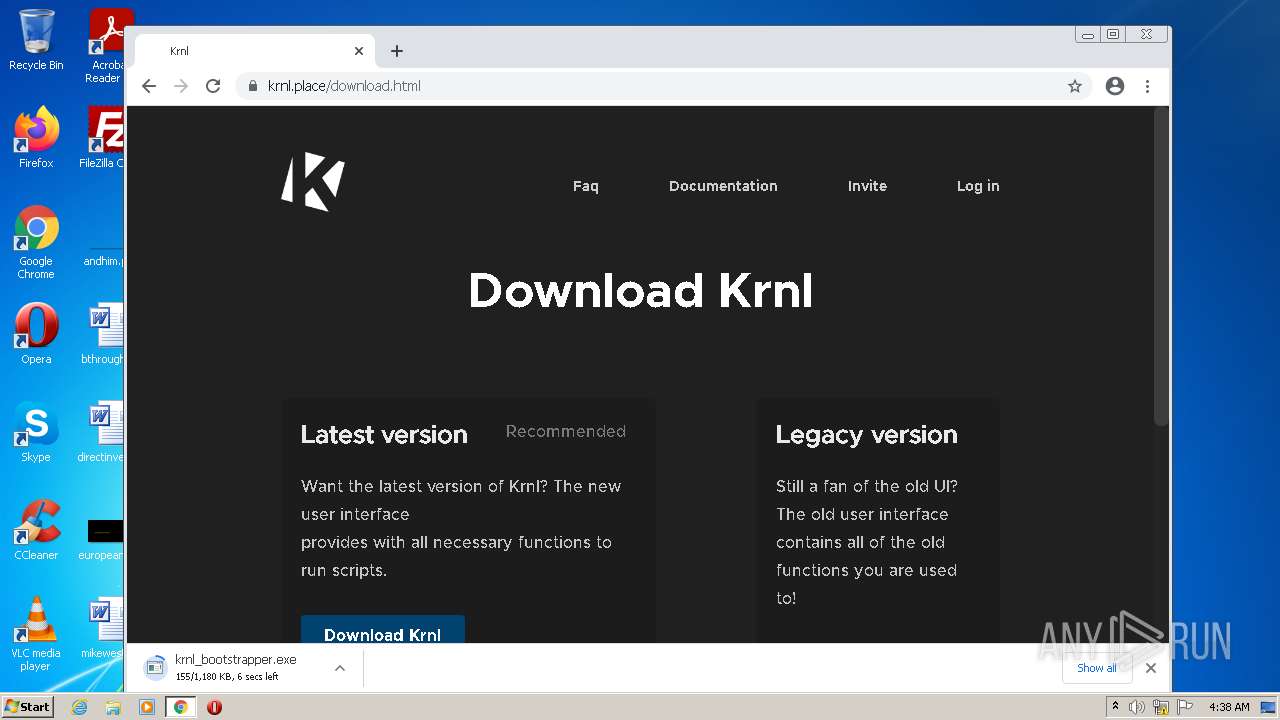
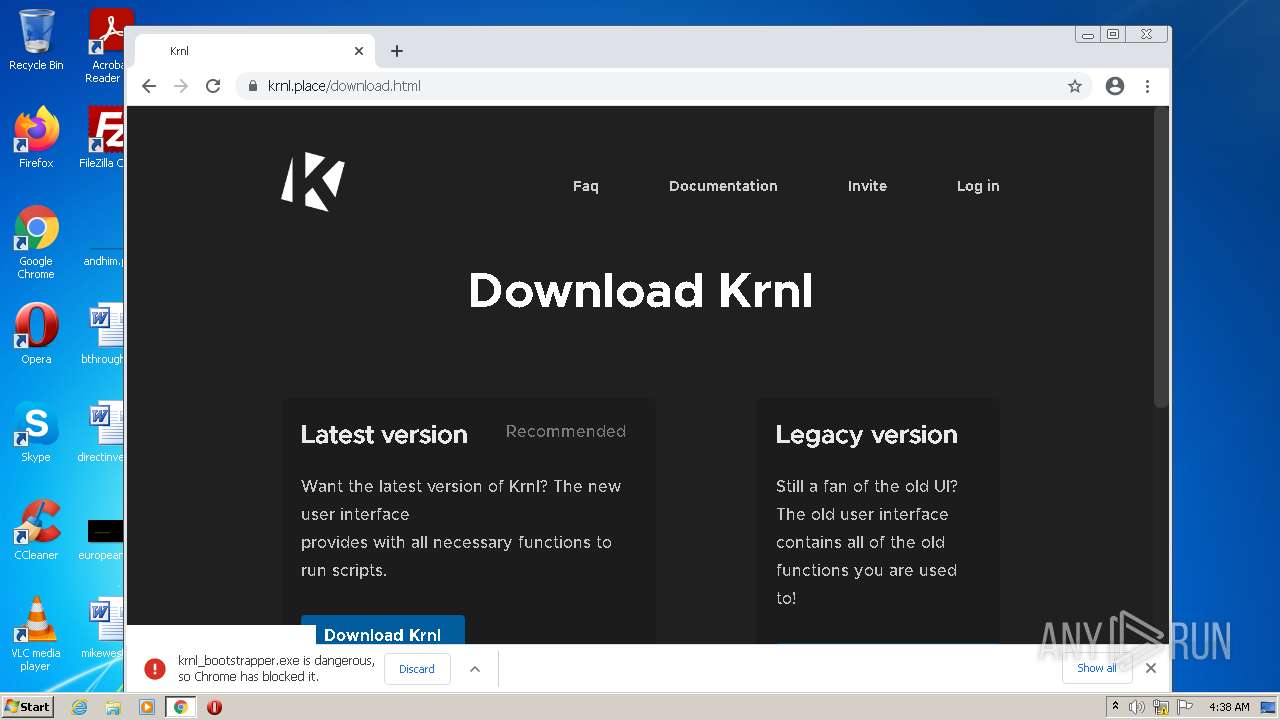
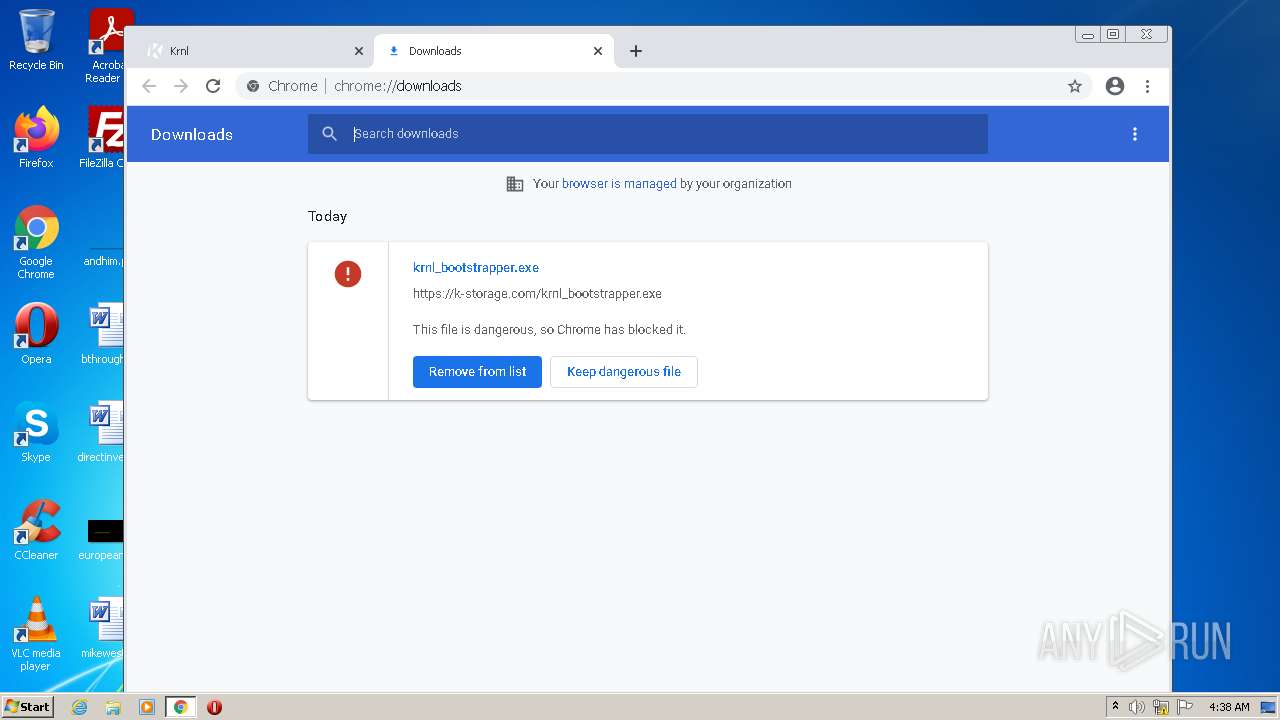
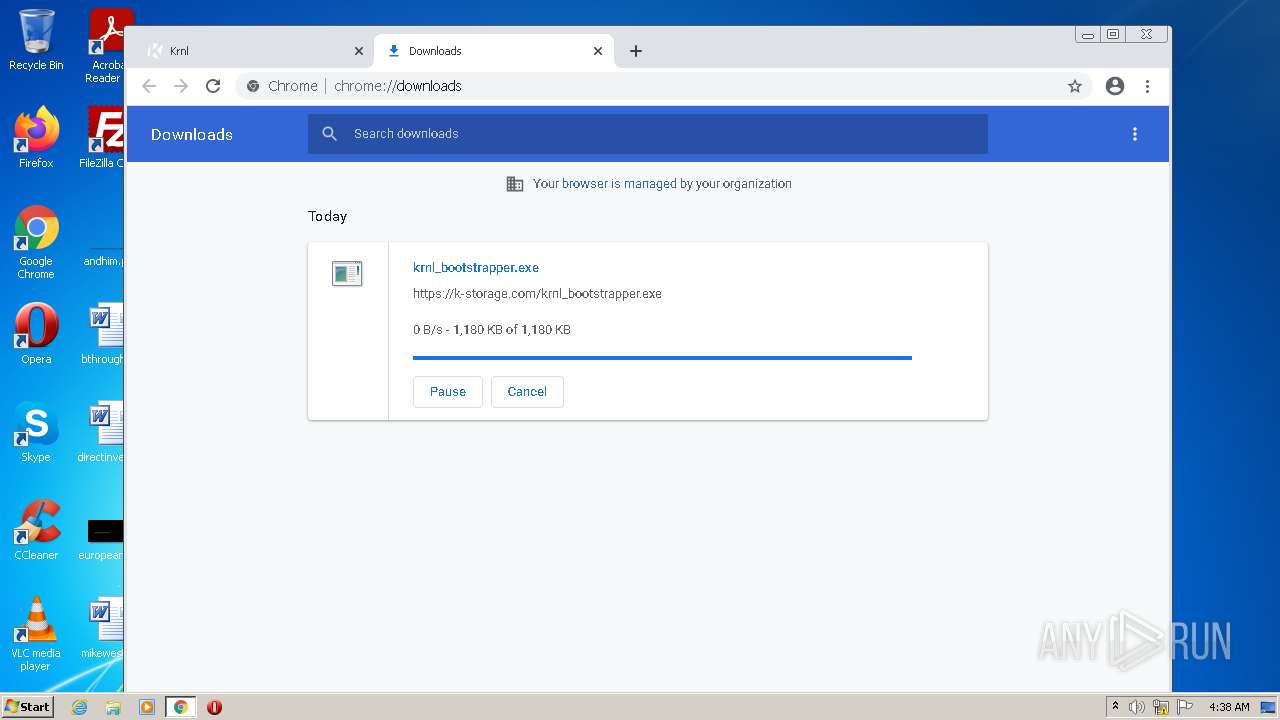
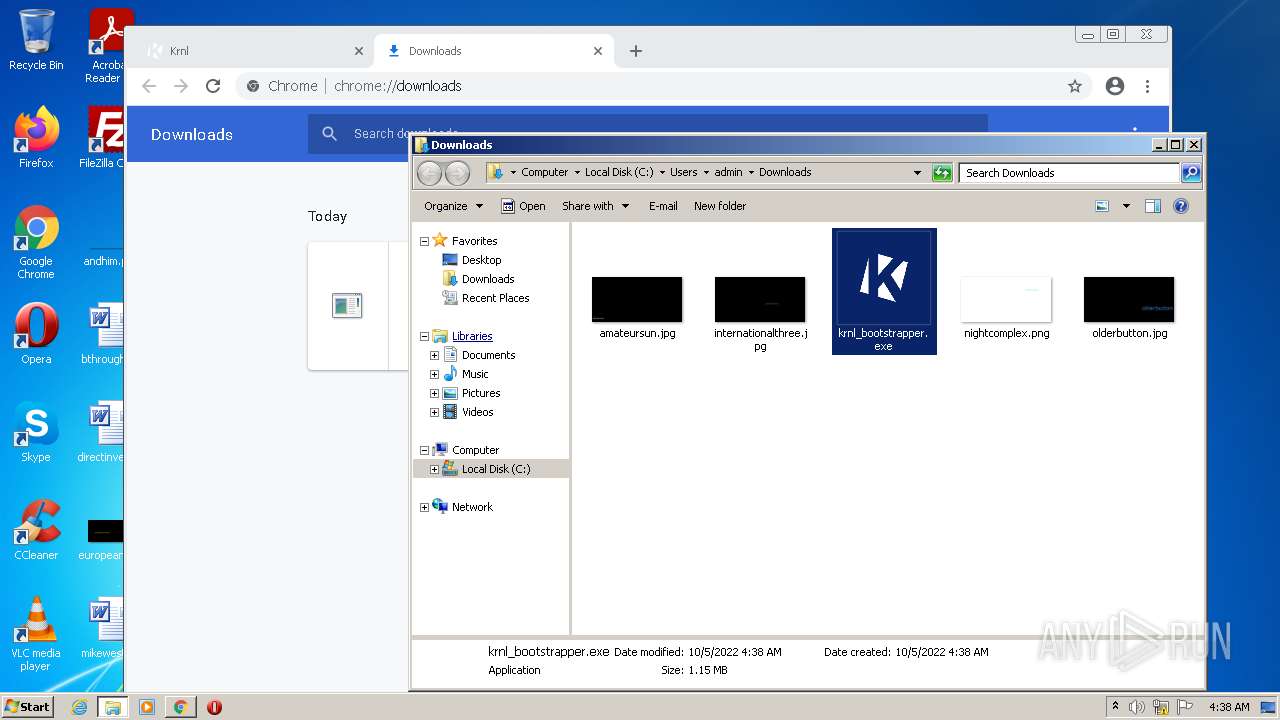
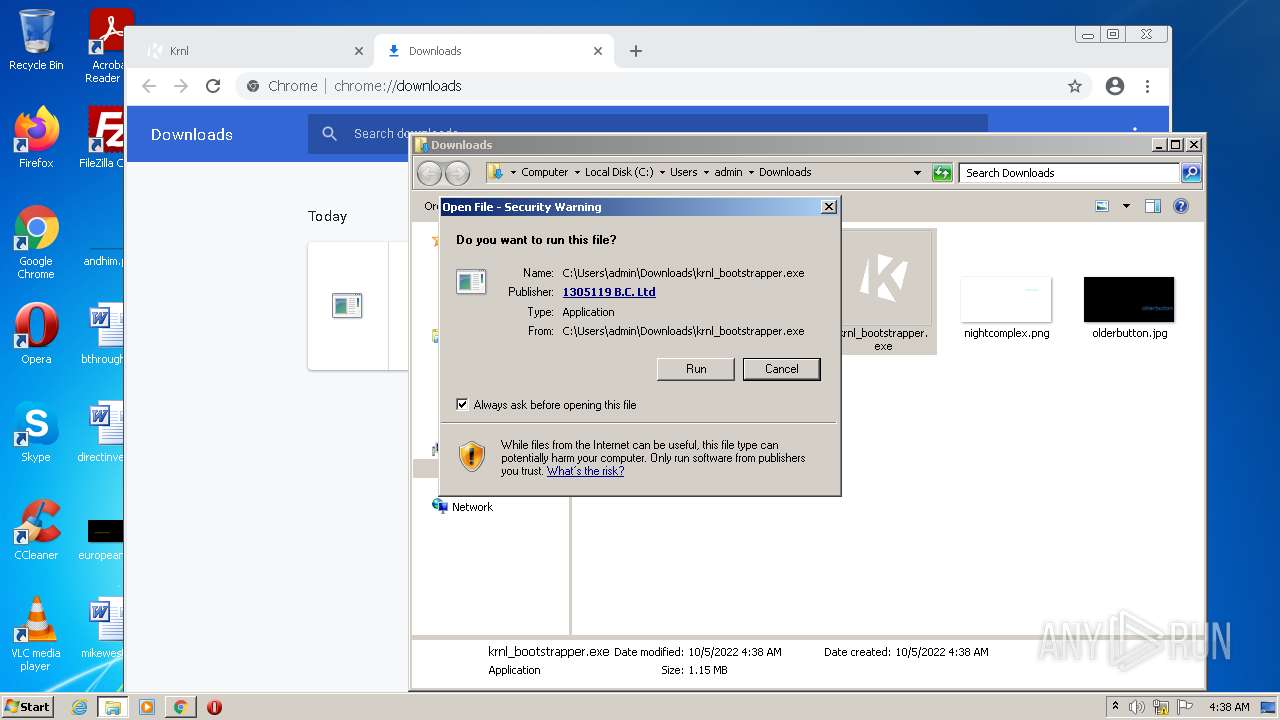
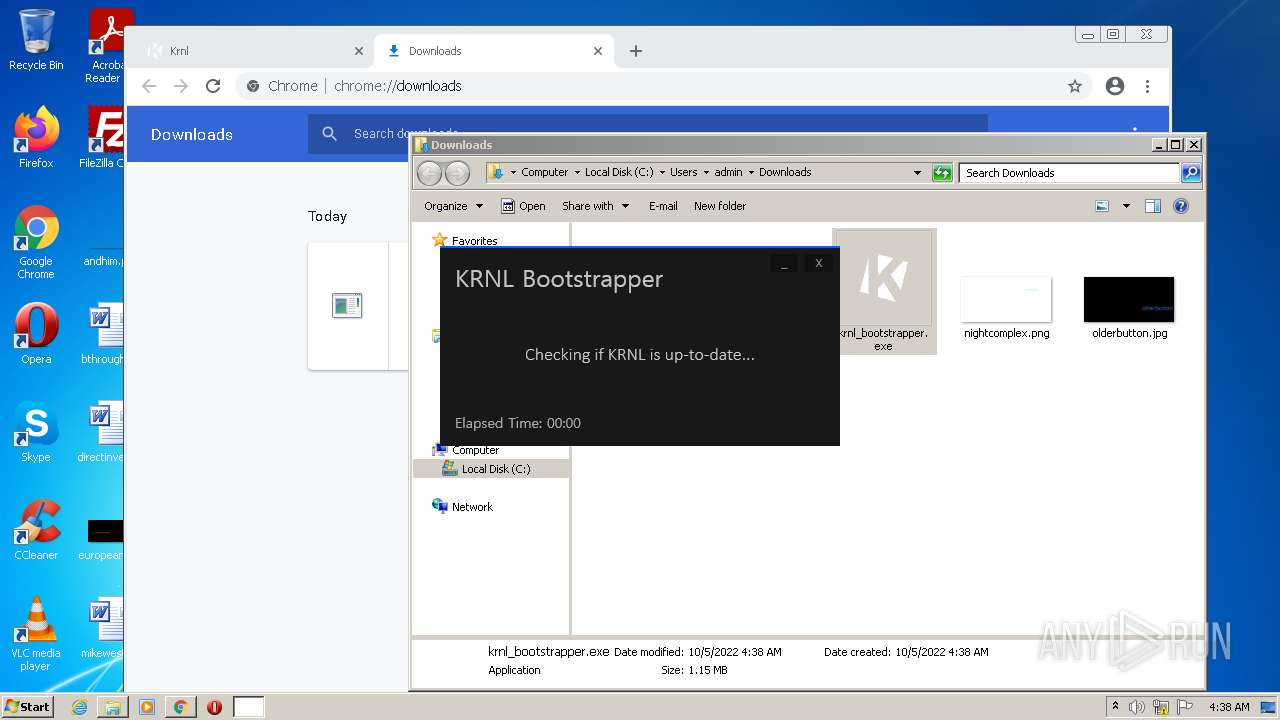
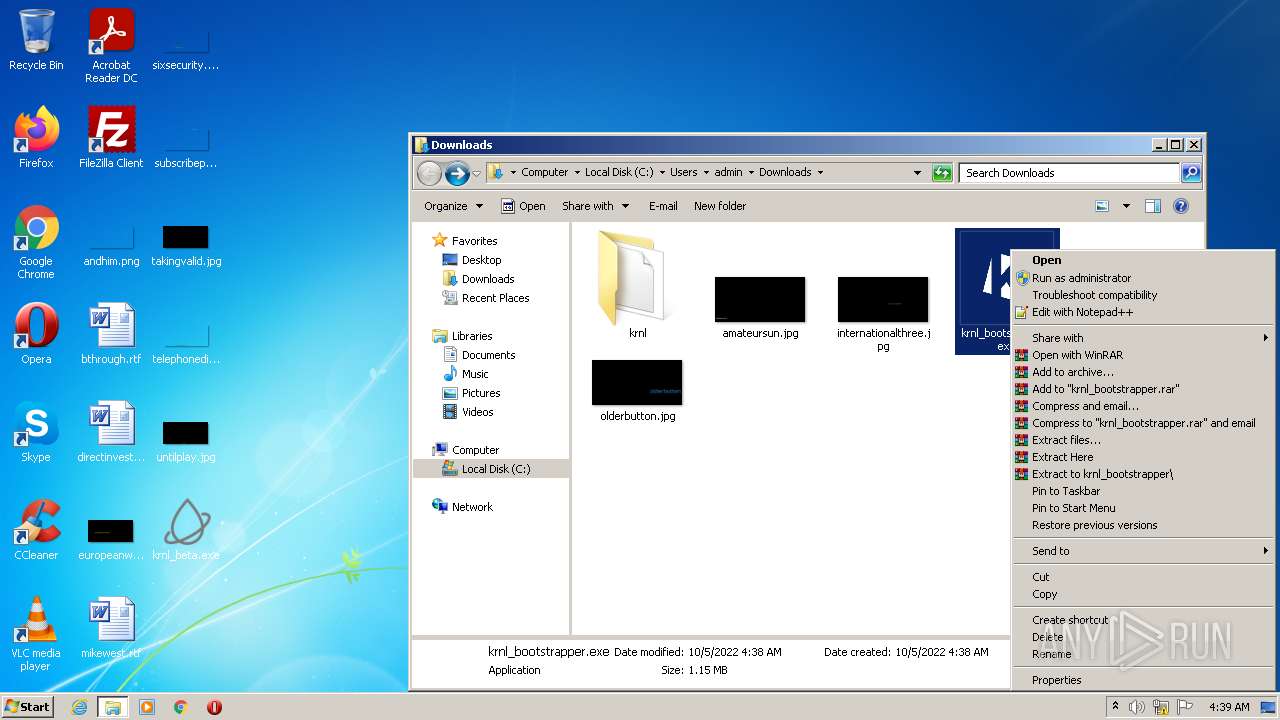
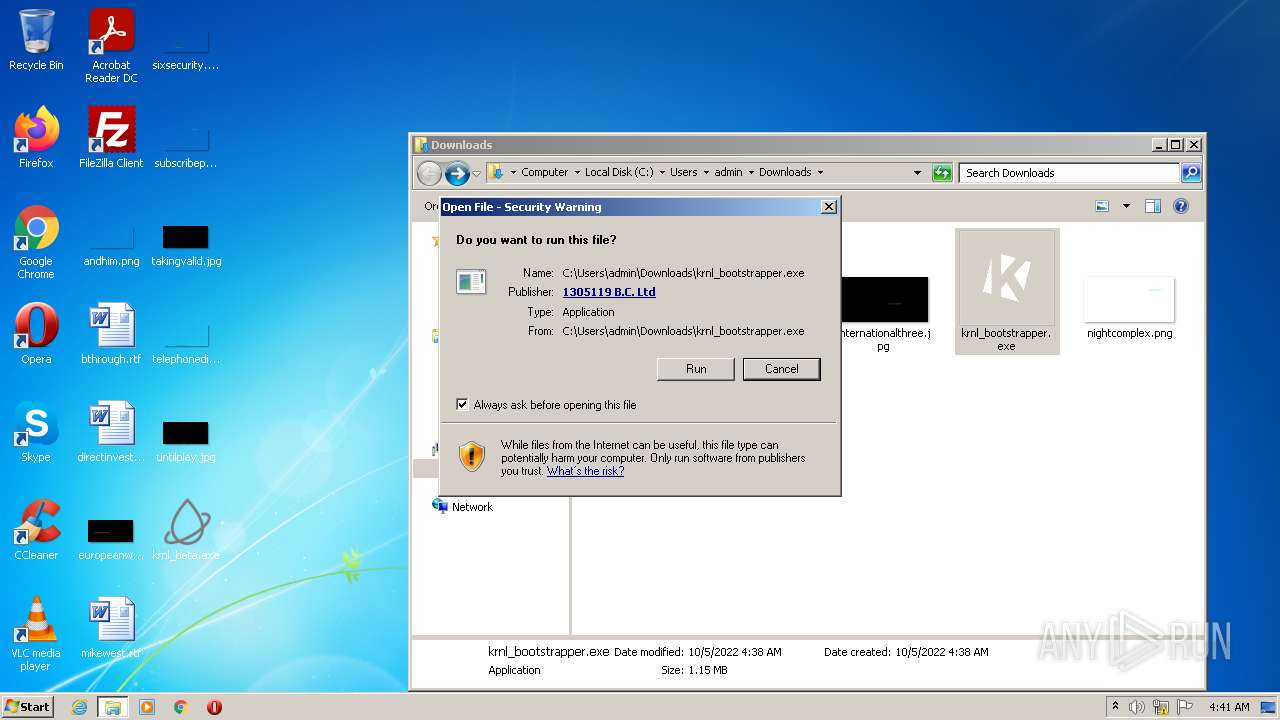
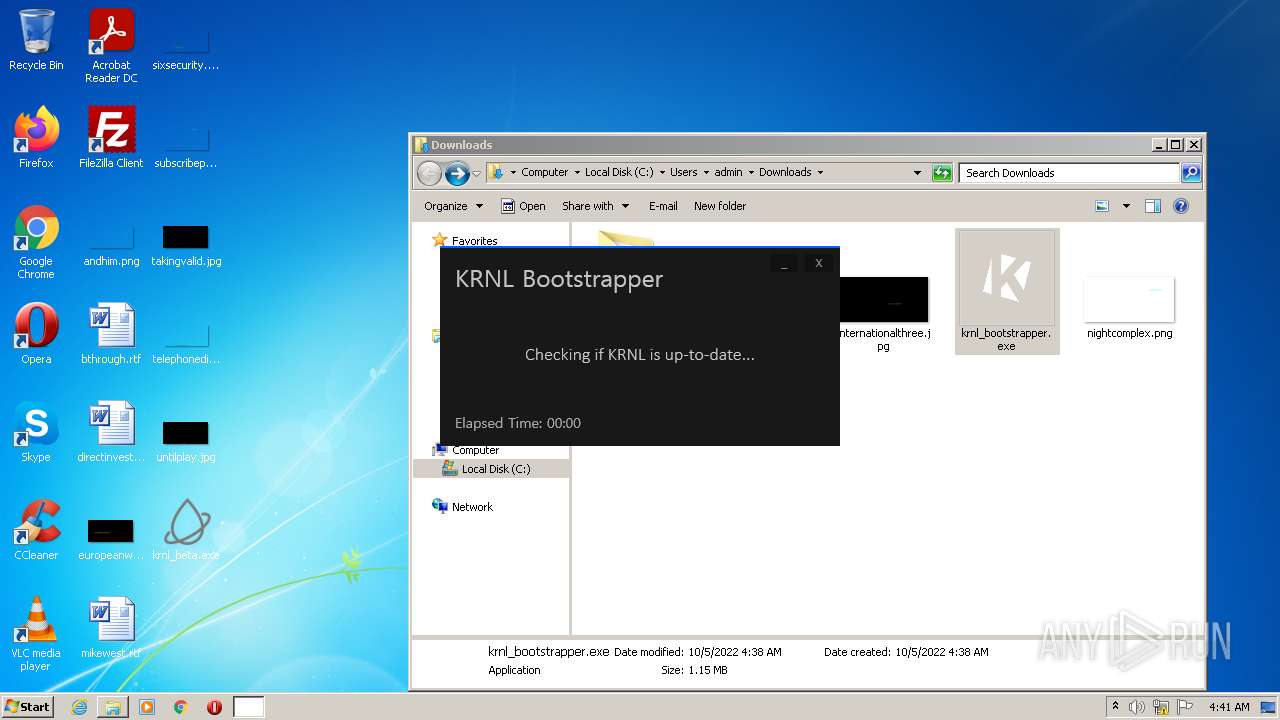
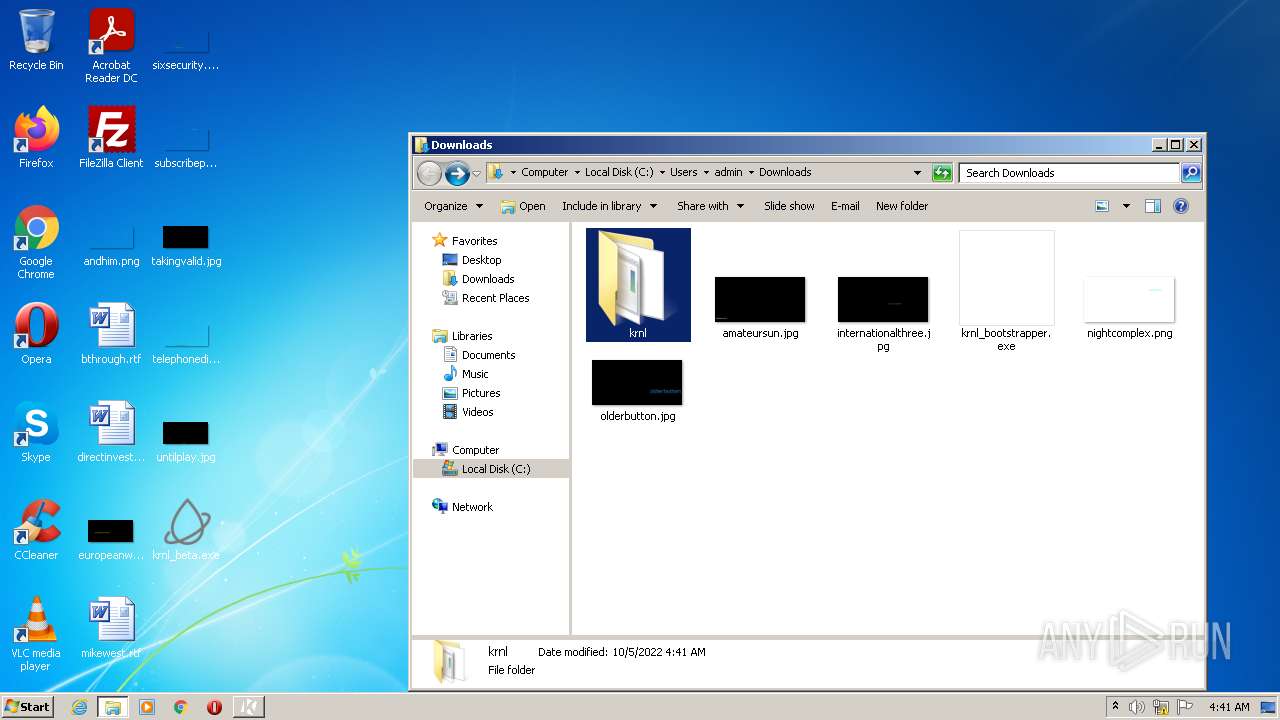
Manual execution by user
- chrome.exe (PID: 2592)
- krnl_beta.exe (PID: 3020)
- krnl_bootstrapper.exe (PID: 3068)
- krnl_bootstrapper.exe (PID: 2120)
- krnl_bootstrapper.exe (PID: 320)
Reads the computer name
- WISPTIS.EXE (PID: 2404)
- chrome.exe (PID: 2592)
- chrome.exe (PID: 328)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 2908)
- SearchProtocolHost.exe (PID: 884)
Checks supported languages
- chrome.exe (PID: 1148)
- chrome.exe (PID: 3224)
- WISPTIS.EXE (PID: 2404)
- chrome.exe (PID: 2592)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 328)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 3992)
- chrome.exe (PID: 576)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 3760)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 3424)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 884)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 2620)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 1112)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3112)
- SearchProtocolHost.exe (PID: 884)
Application launched itself
- chrome.exe (PID: 2592)
Reads the hosts file
- chrome.exe (PID: 2592)
- chrome.exe (PID: 3224)
Changes default file association
- chrome.exe (PID: 2592)
Reads settings of System Certificates
- chrome.exe (PID: 3224)
- chrome.exe (PID: 2592)
- krnl_bootstrapper.exe (PID: 3068)
- krnl_bootstrapper.exe (PID: 2120)
- krnl_bootstrapper.exe (PID: 320)
Creates files in the user directory
- chrome.exe (PID: 2592)
Checks Windows Trust Settings
- chrome.exe (PID: 2592)
Reads the date of Windows installation
- chrome.exe (PID: 3068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2076-Jan-07 21:18:28 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Krnl |
| FileVersion: | 1.0.0.0 |
| InternalName: | Krnl.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | Krnl.exe |
| ProductName: | Krnl |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2076-Jan-07 21:18:28 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 1806700 | 1806848 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.81062 |
.rsrc | 1818624 | 108360 | 108544 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.85821 |
.reloc | 1933312 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.91469 | 6870 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 2.09038 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.35895 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.53434 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.677 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 2.76097 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 (#2) | 3.22386 | 764 | UNKNOWN | UNKNOWN | RT_VERSION |
1 (#3) | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
99
Monitored processes
42
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Users\admin\Downloads\krnl_bootstrapper.exe" | C:\Users\admin\Downloads\krnl_bootstrapper.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: krnl_bootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,967300164983211675,6512726424102222271,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,967300164983211675,6512726424102222271,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,967300164983211675,6512726424102222271,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4136 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 884 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1036,967300164983211675,6512726424102222271,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2776 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f53d988,0x6f53d998,0x6f53d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,967300164983211675,6512726424102222271,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
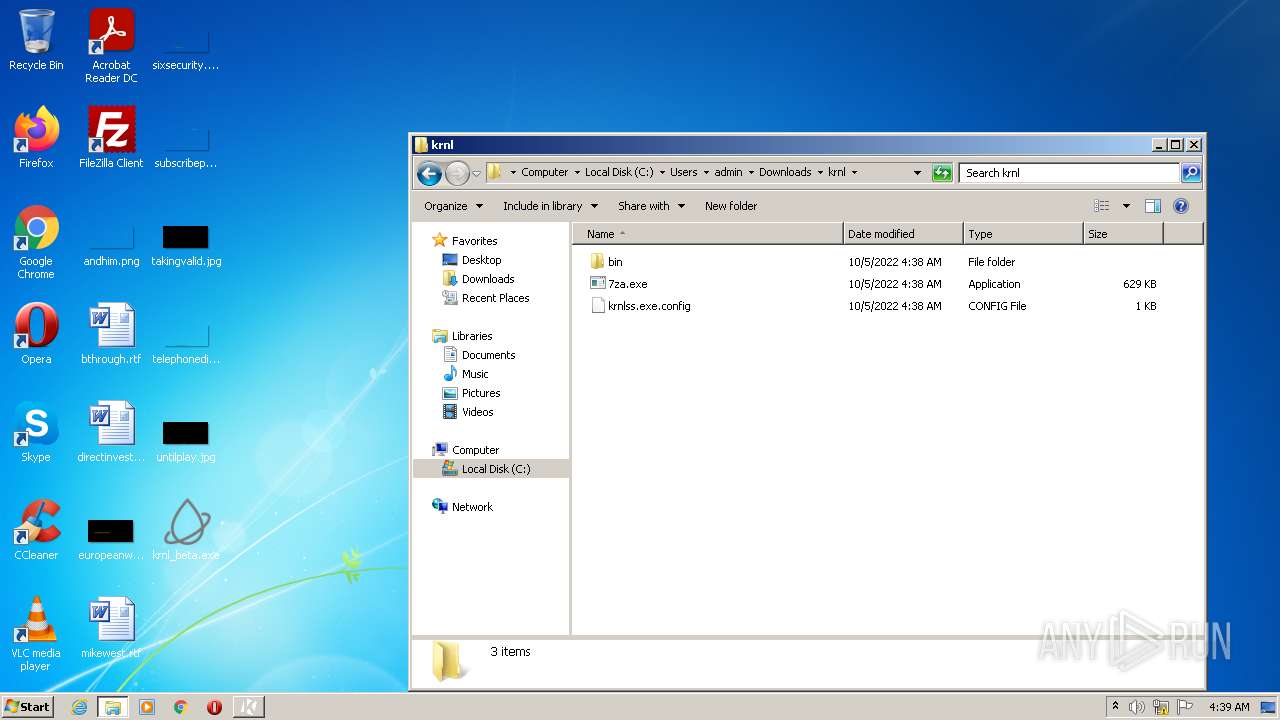
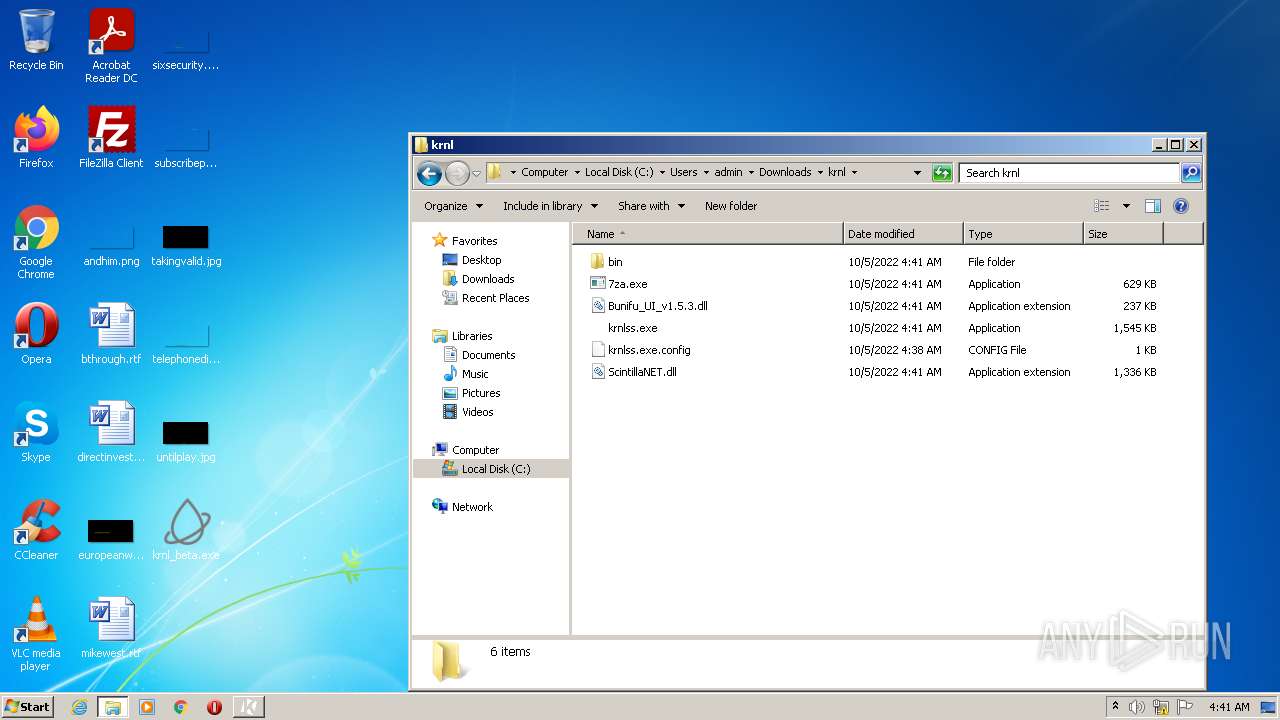
| 2032 | "C:\Users\admin\Downloads\krnl\7za.exe" x "C:\Users\admin\Downloads\krnl\bin\Monaco.zip" -o"C:\Users\admin\Downloads\krnl\bin" -aoa -bsp1 | C:\Users\admin\Downloads\krnl\7za.exe | — | krnl_bootstrapper.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 15.14 Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\Downloads\krnl_bootstrapper.exe" | C:\Users\admin\Downloads\krnl_bootstrapper.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: krnl_bootstrapper Exit code: 3489660927 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
25 498
Read events
25 198
Write events
293
Delete events
7
Modification events
| (PID) Process: | (3396) krnl_beta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: krnl_beta.exe | |||
| (PID) Process: | (3396) krnl_beta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3396) krnl_beta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3396) krnl_beta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3396) krnl_beta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2404) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: WISPTIS.EXE | |||
| (PID) Process: | (2404) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\Touch |
| Operation: | write | Name: | TouchGate |
Value: 1 | |||
| (PID) Process: | (2404) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\MultiTouch |
| Operation: | write | Name: | MultiTouchEnabled |
Value: 1 | |||
| (PID) Process: | (2404) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\Pen\SysEventParameters |
| Operation: | write | Name: | FlickMode |
Value: 1 | |||
| (PID) Process: | (2404) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\Pen\SysEventParameters |
| Operation: | write | Name: | TouchFlickTolerance |
Value: 50 | |||
Executable files
10
Suspicious files
145
Text files
171
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633CFC07-A20.pma | — | |
MD5:— | SHA256:— | |||
| 1148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\92ce7c6d-cef0-46a9-80c7-0f43c5a8ea72.tmp | text | |
MD5:— | SHA256:— | |||
| 3224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d1110e75-b7d3-44cb-9483-b641b6f4eb01.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF127065.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF126f3d.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
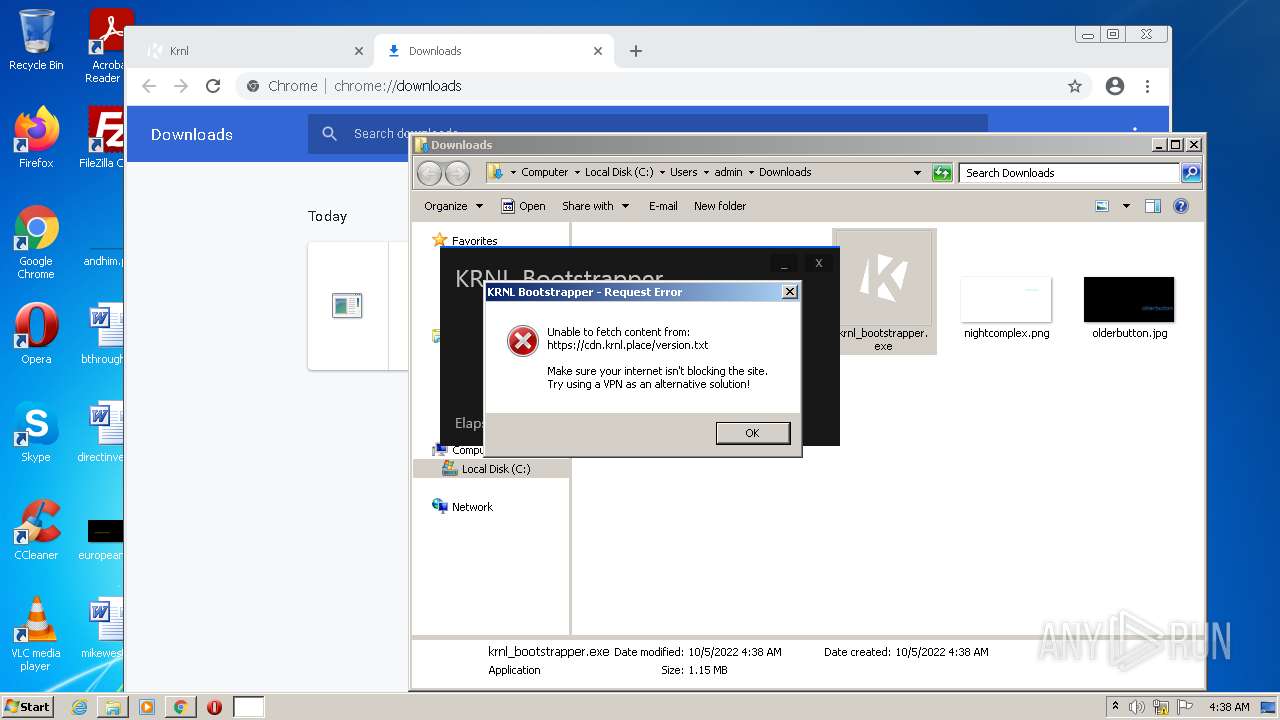
HTTP(S) requests
6
TCP/UDP connections
80
DNS requests
33
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
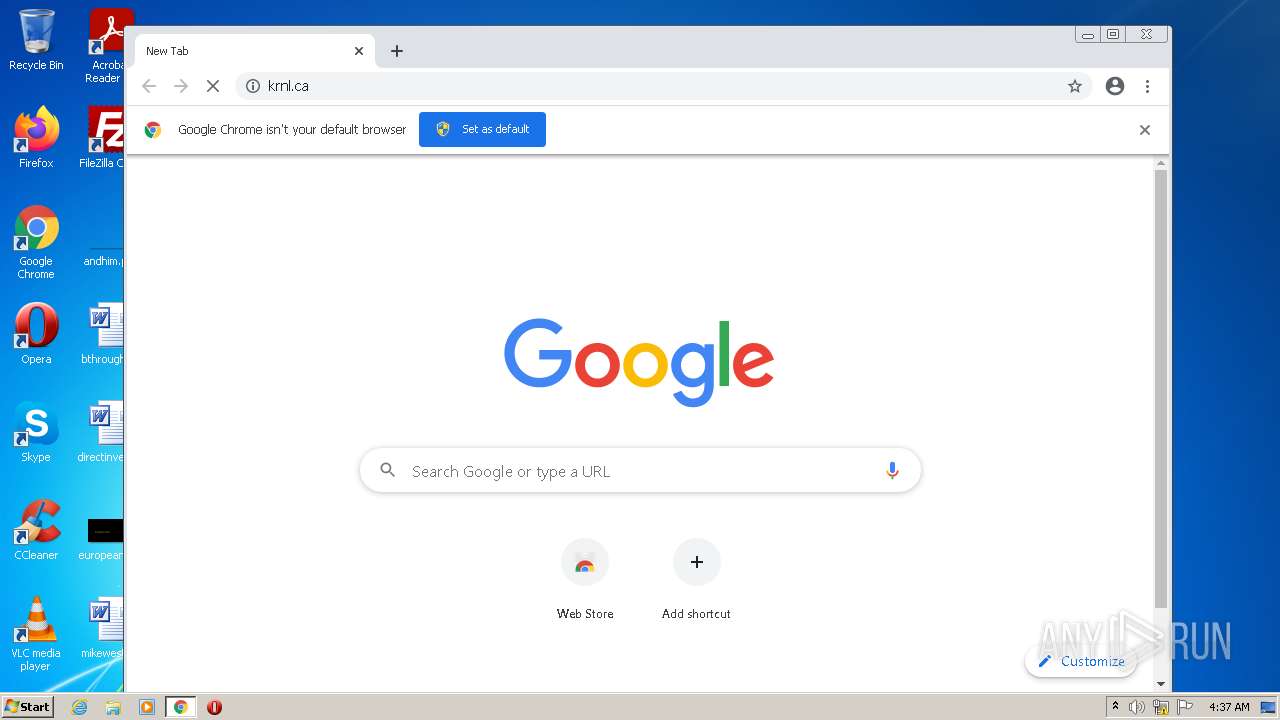
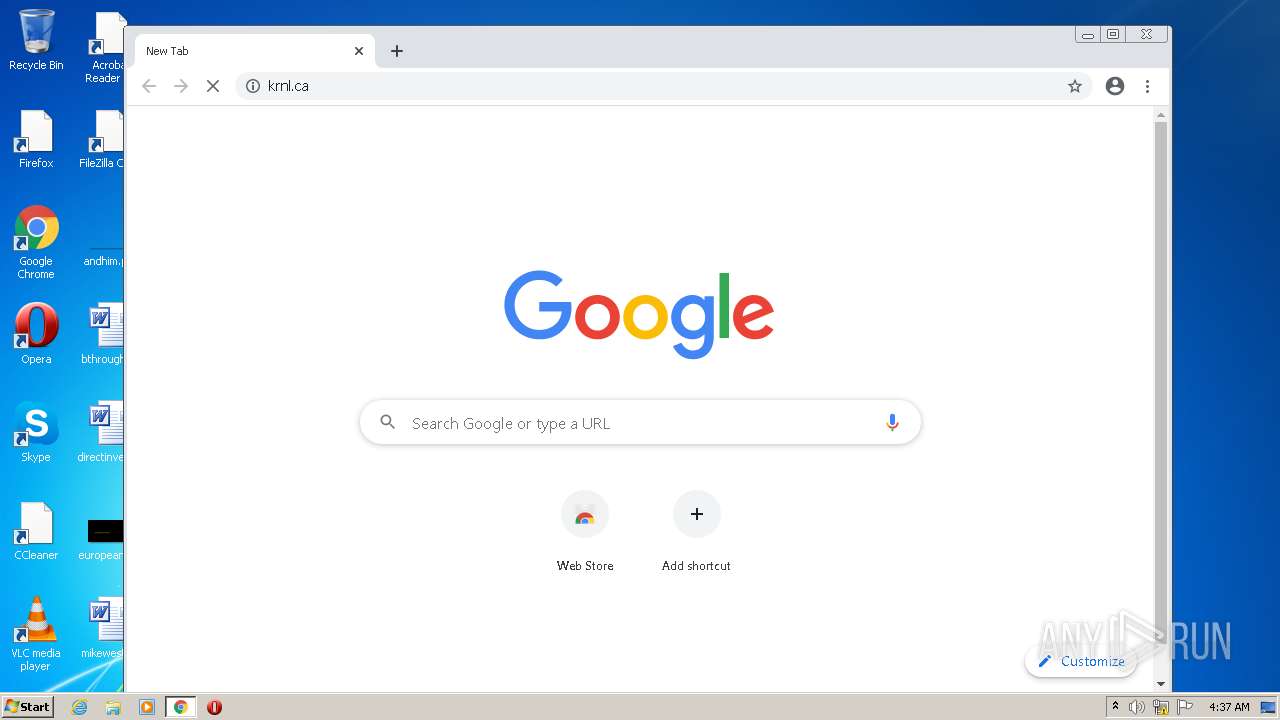
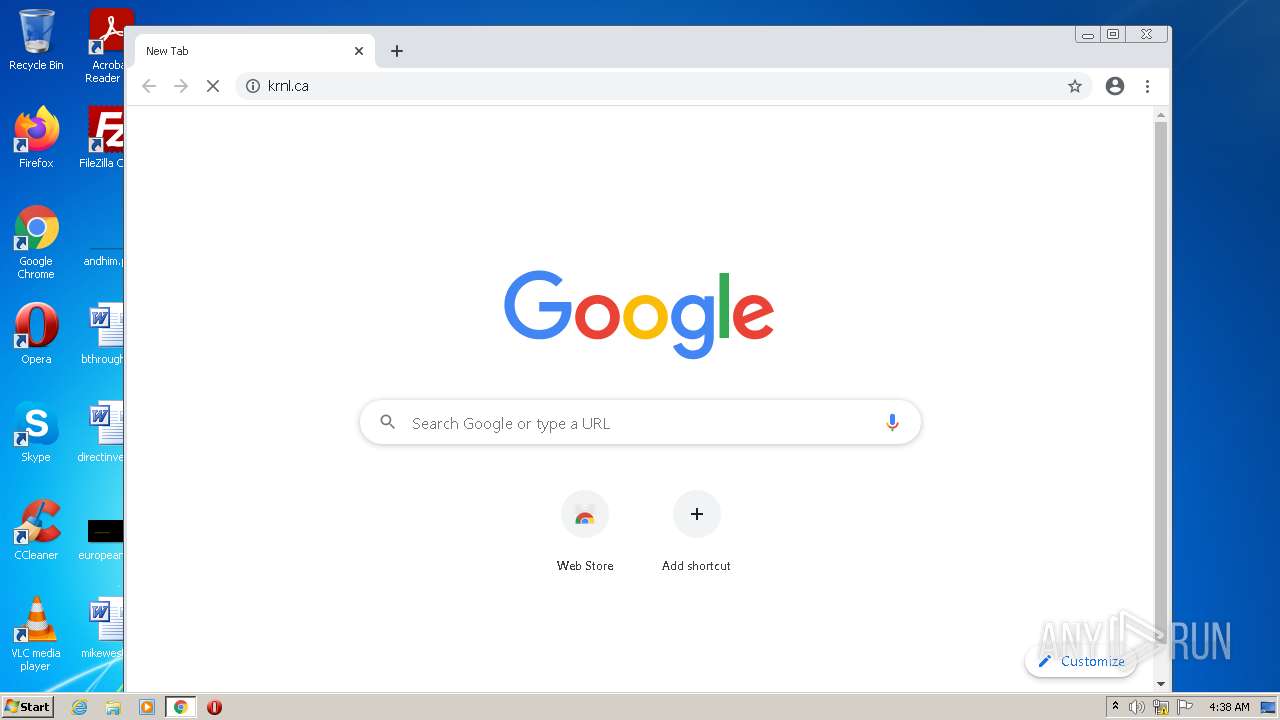
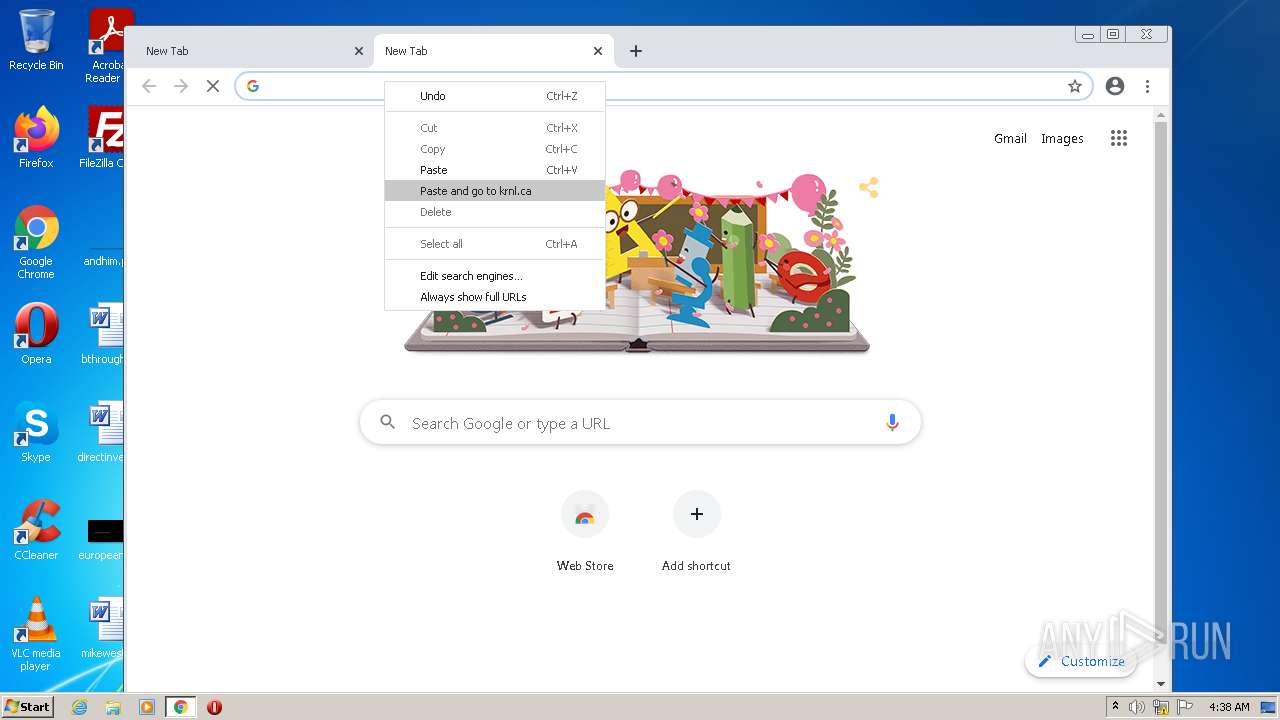
3224 | chrome.exe | GET | 301 | 188.114.97.3:80 | http://krnl.ca/ | US | — | — | malicious |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
924 | svchost.exe | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | — | — | whitelisted |
3224 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?26da7ca901186e10 | US | compressed | 60.9 Kb | whitelisted |
924 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | crx | 2.81 Kb | whitelisted |
3224 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3224 | chrome.exe | 142.250.186.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
3224 | chrome.exe | 216.58.212.132:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
3224 | chrome.exe | 142.250.186.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3224 | chrome.exe | 172.217.16.206:443 | apis.google.com | GOOGLE | US | whitelisted |
3224 | chrome.exe | 142.250.186.131:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3224 | chrome.exe | 162.159.133.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
3224 | chrome.exe | 104.18.114.97:443 | ipv4.icanhazip.com | CLOUDFLARENET | — | malicious |
3224 | chrome.exe | 142.250.186.99:443 | update.googleapis.com | GOOGLE | US | whitelisted |
3224 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
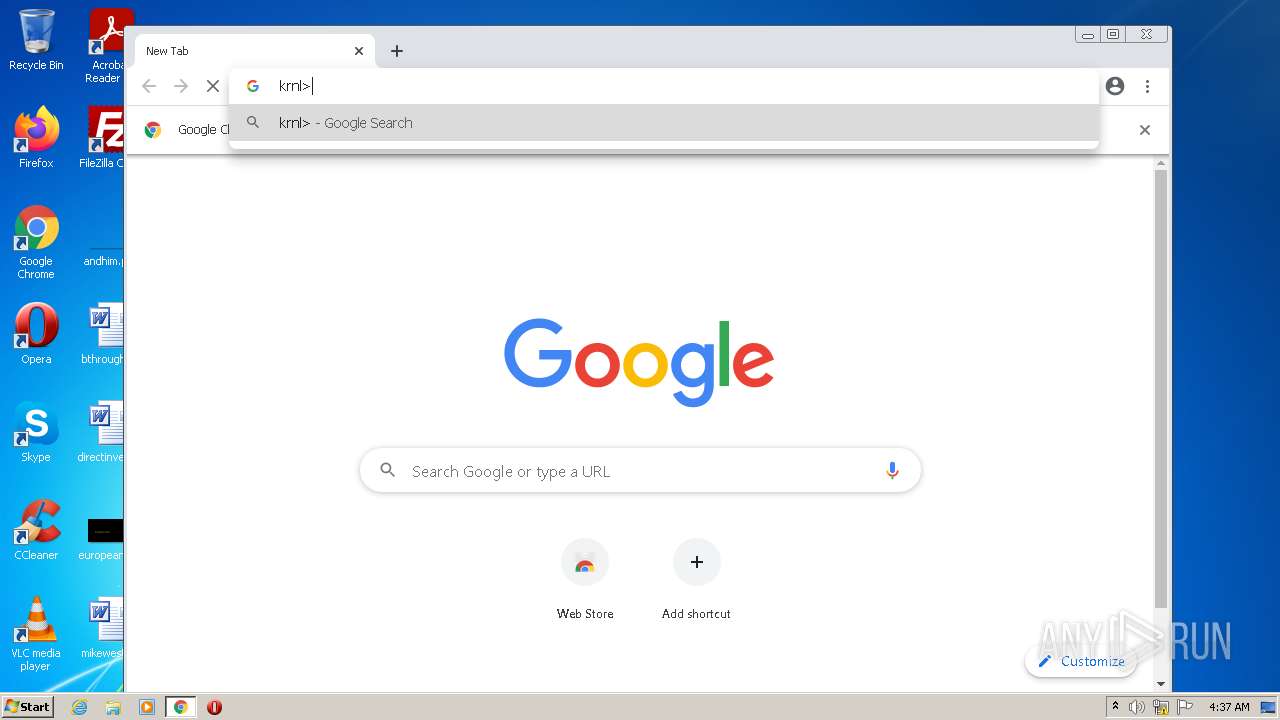
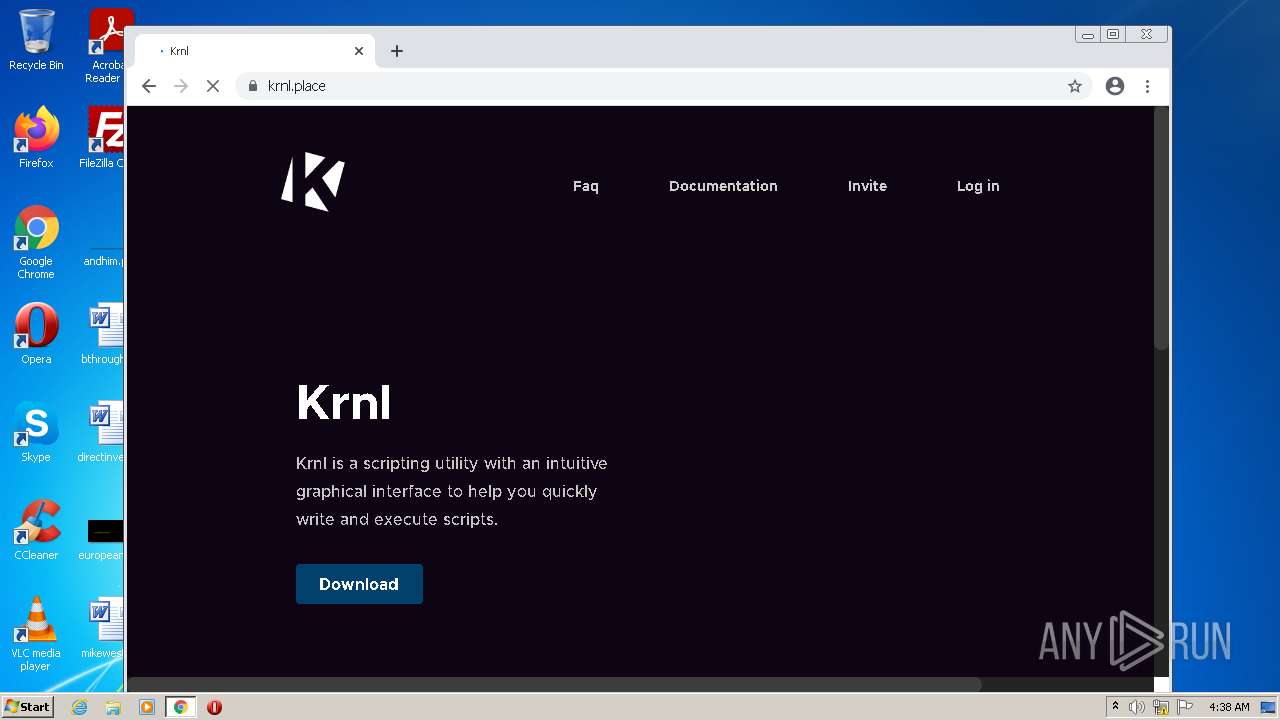
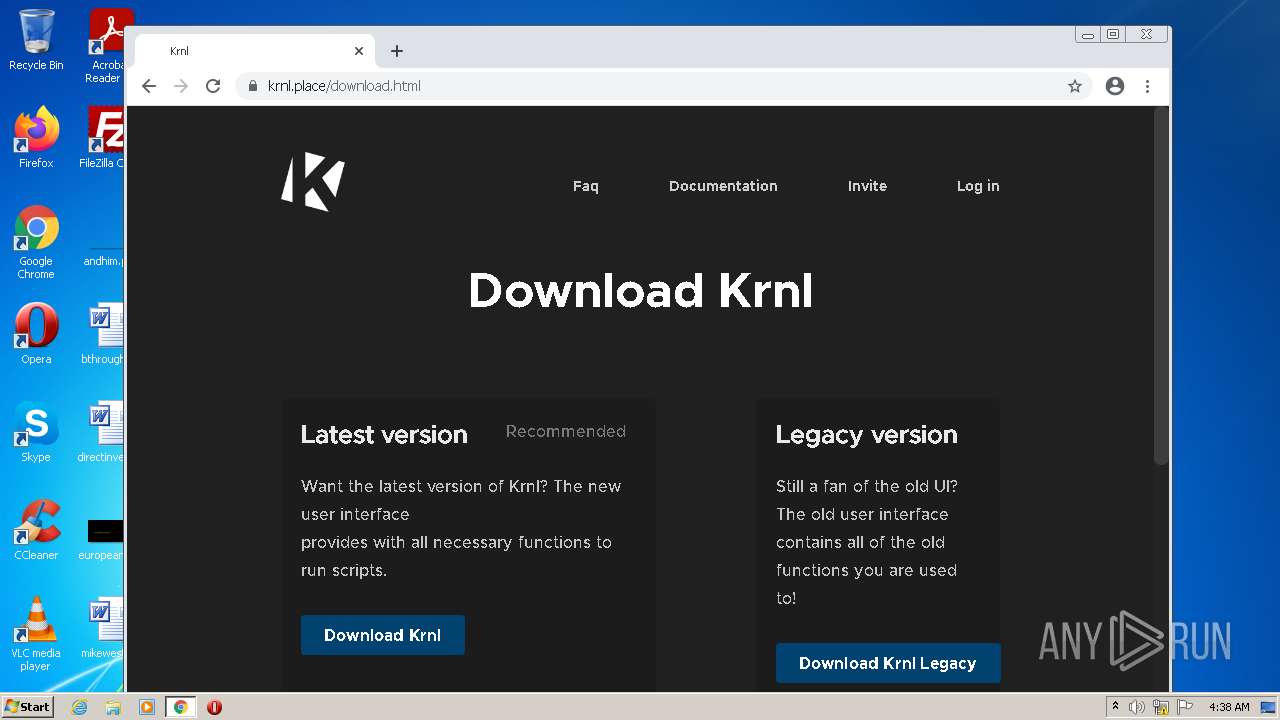
krnl.ca |
| malicious |
ssl.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
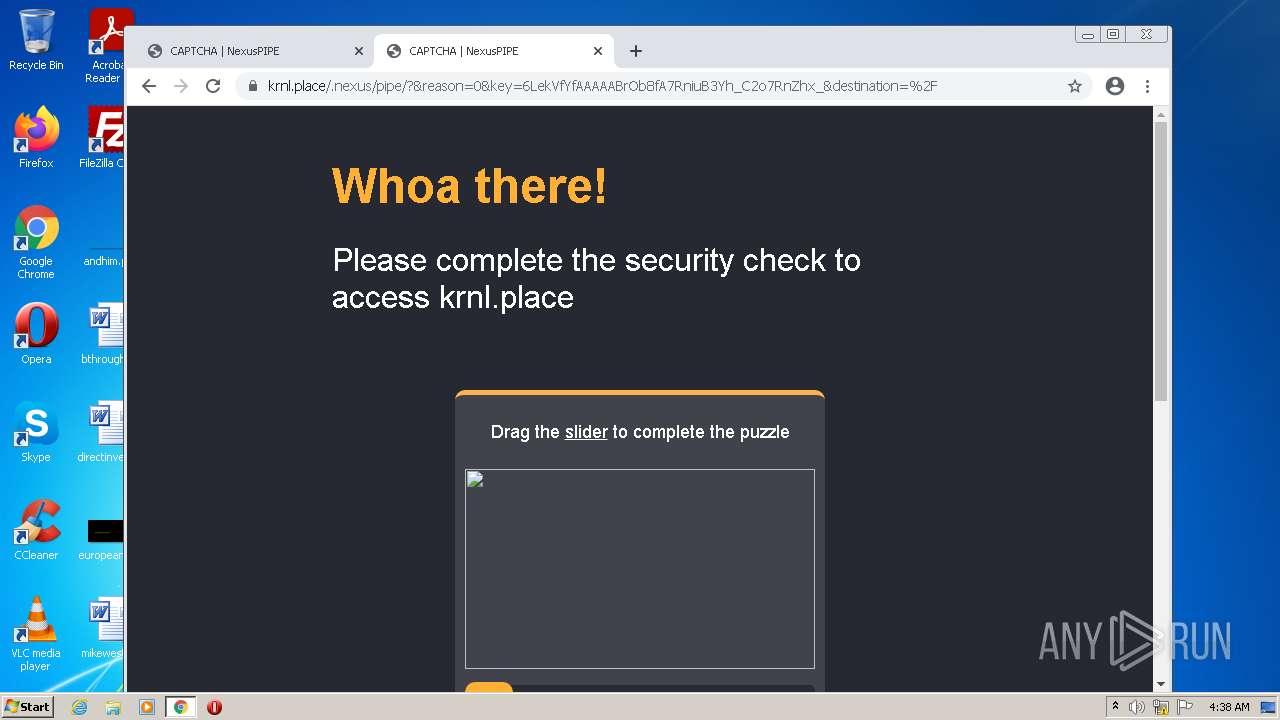
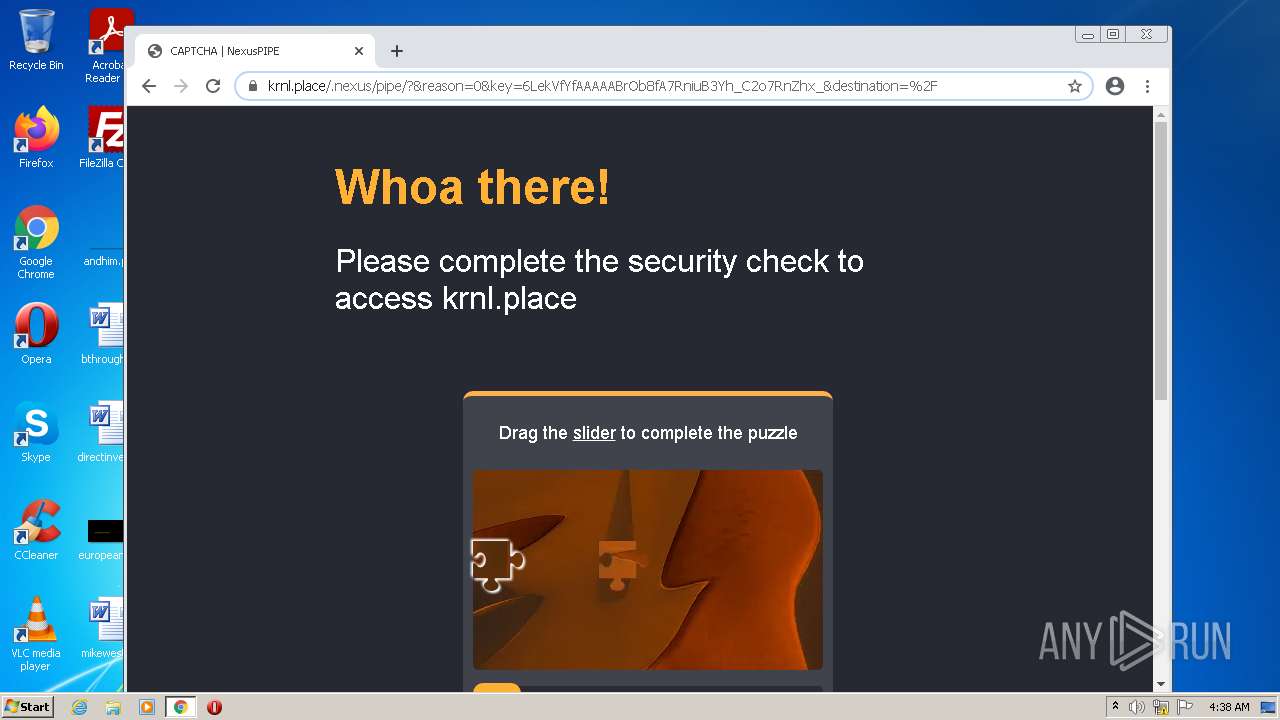
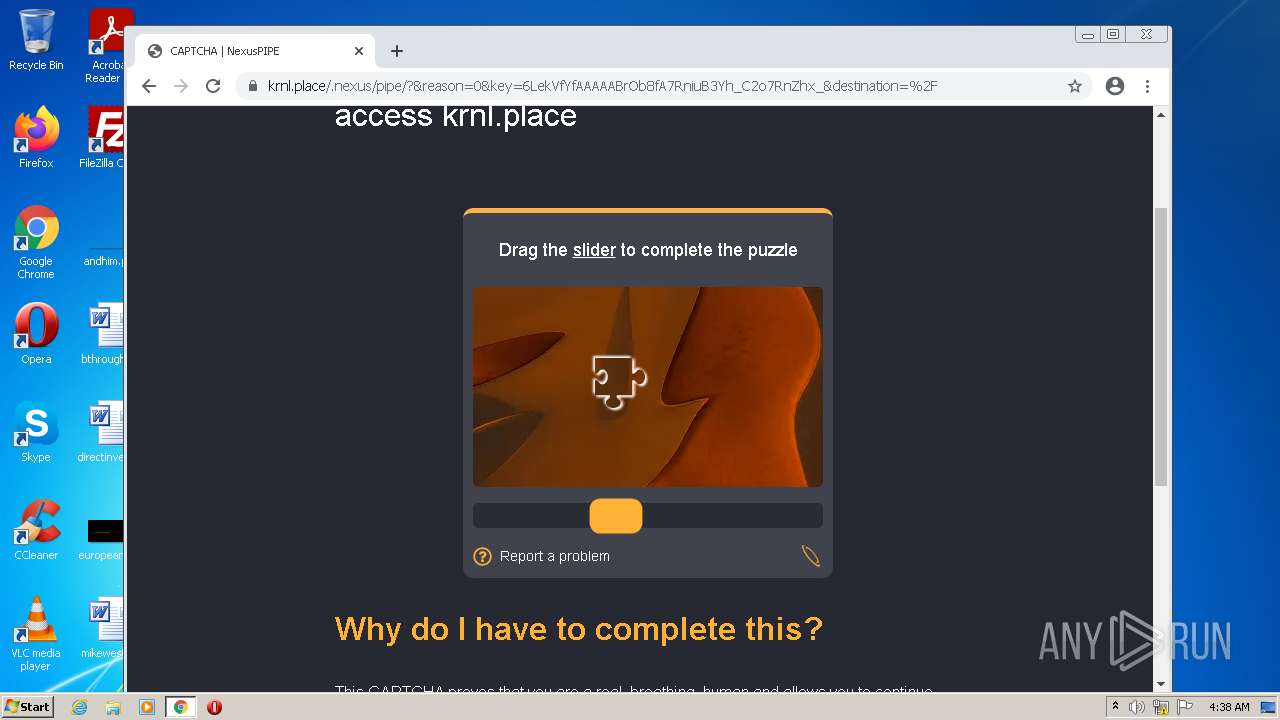
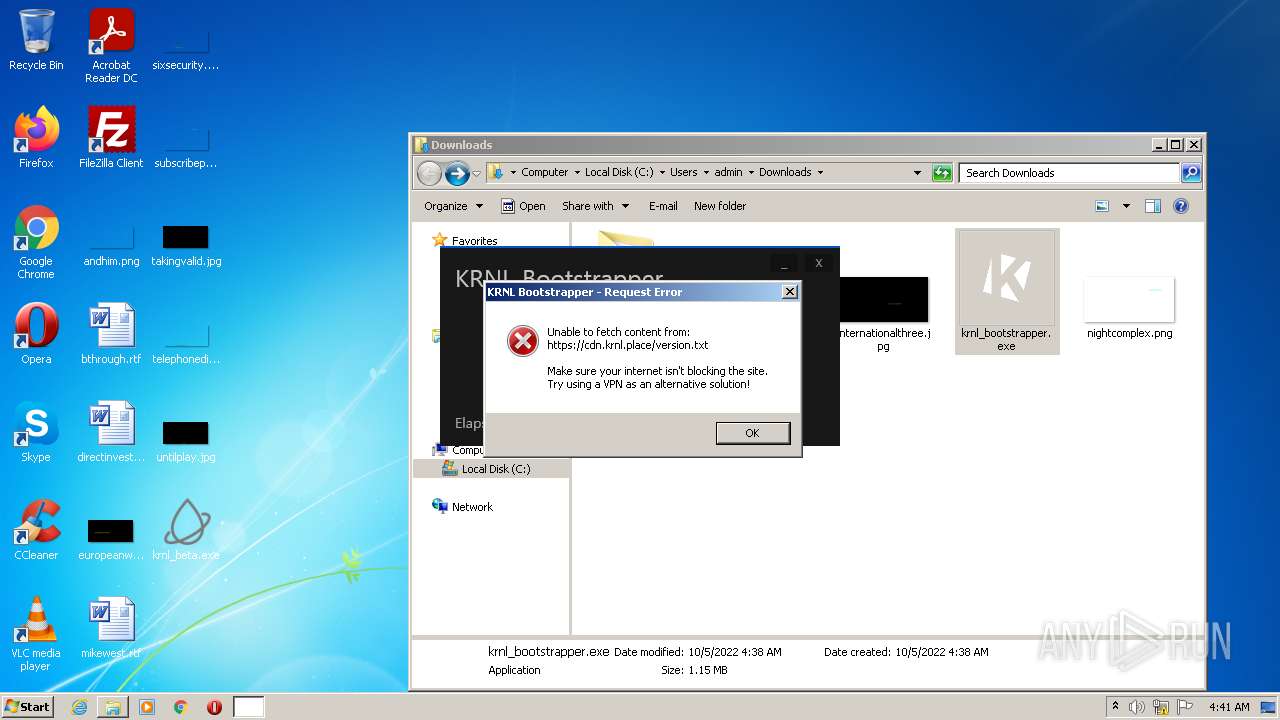
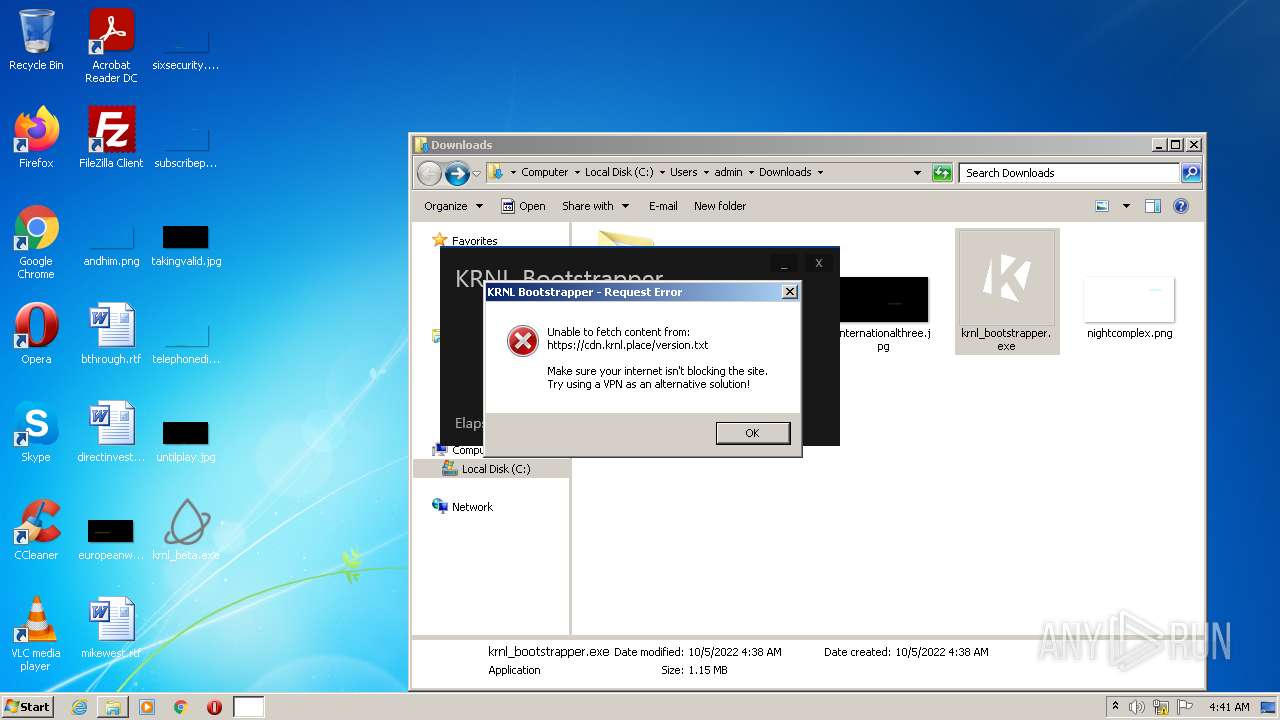
krnl.place |
| suspicious |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
3224 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |