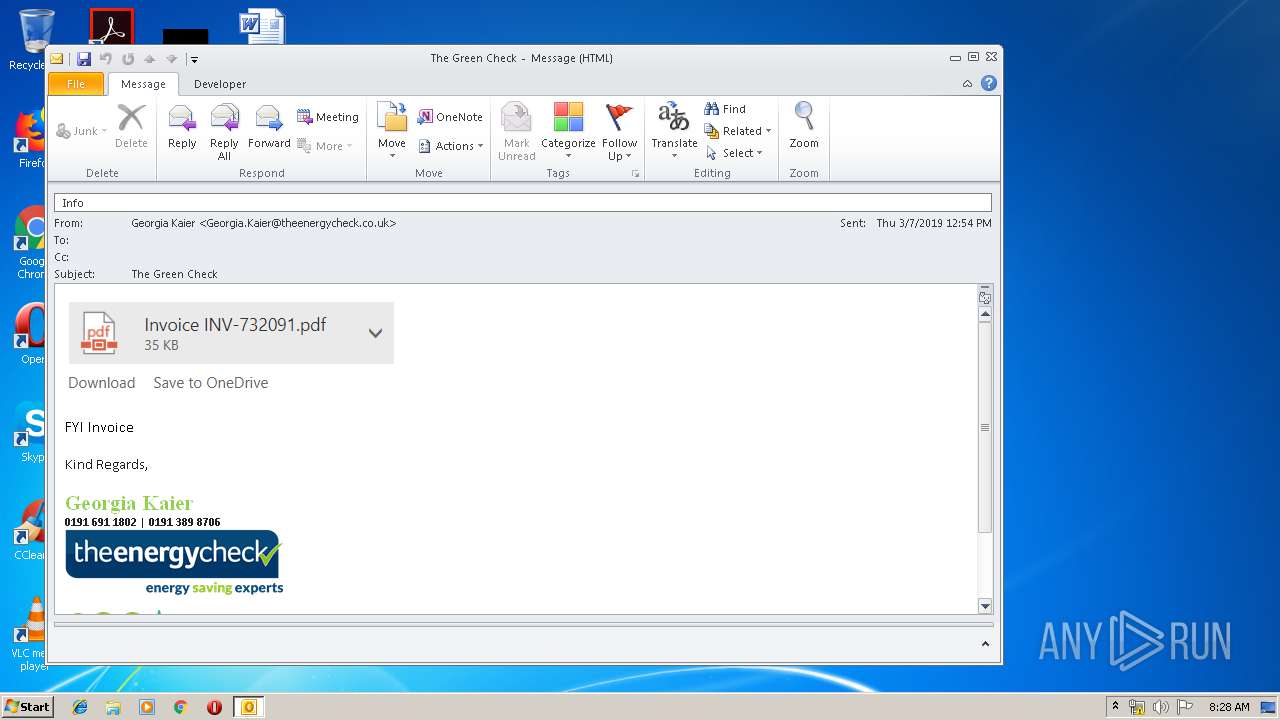
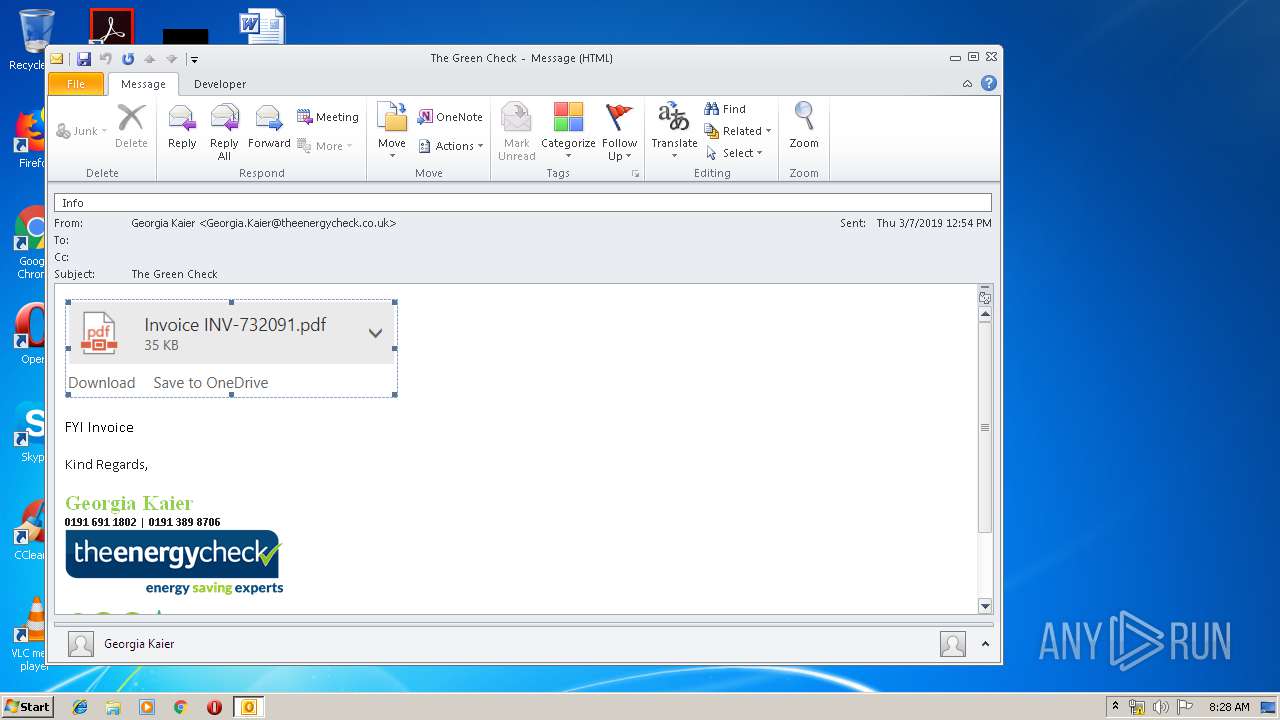
| File name: | The Green Check.msg |
| Full analysis: | https://app.any.run/tasks/107efc10-ef18-4b98-8255-c878274a130a |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 07:27:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | E83EA4C30573489796BE49F7418282E1 |
| SHA1: | 7D5F46672831F16A9AF125E6BDDCA28AF3B29FF5 |
| SHA256: | EC5C7990B8EA8F0699368CB84456E8360C9FF1F44453F89666665AF41A1D8530 |
| SSDEEP: | 1536:15g5UPAWLWFmJh11boqMnk32ySeJNSaUAwNB/wWLWGiB6nUhcZTkdrx36ebqafaL:35X1boqMnkmsUAwNtiB6nnOrx36ebJf |
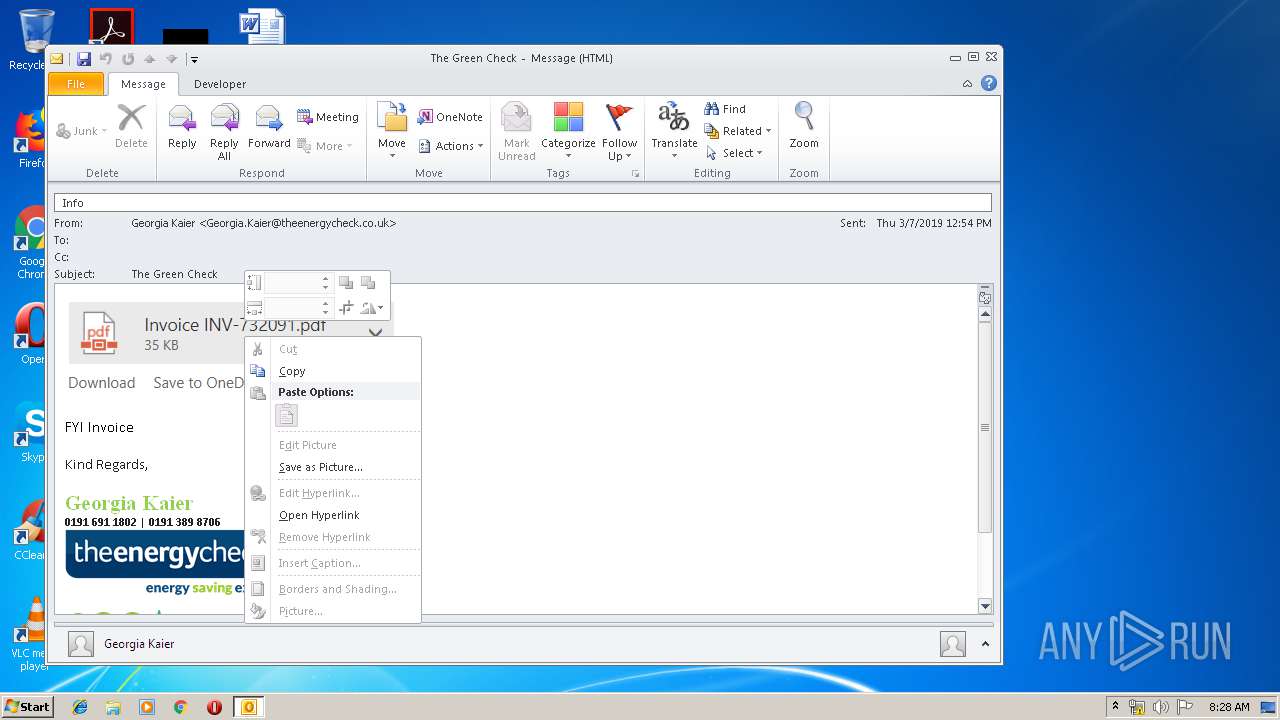
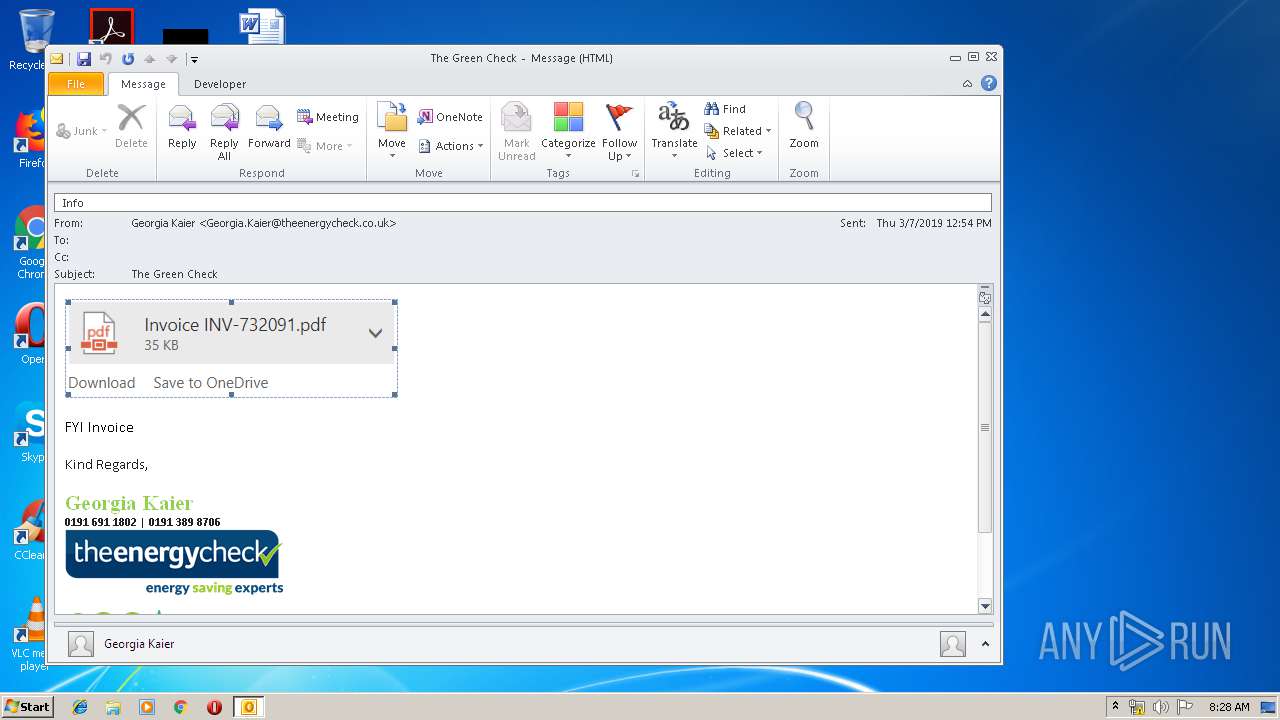
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2128)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2128)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2128)
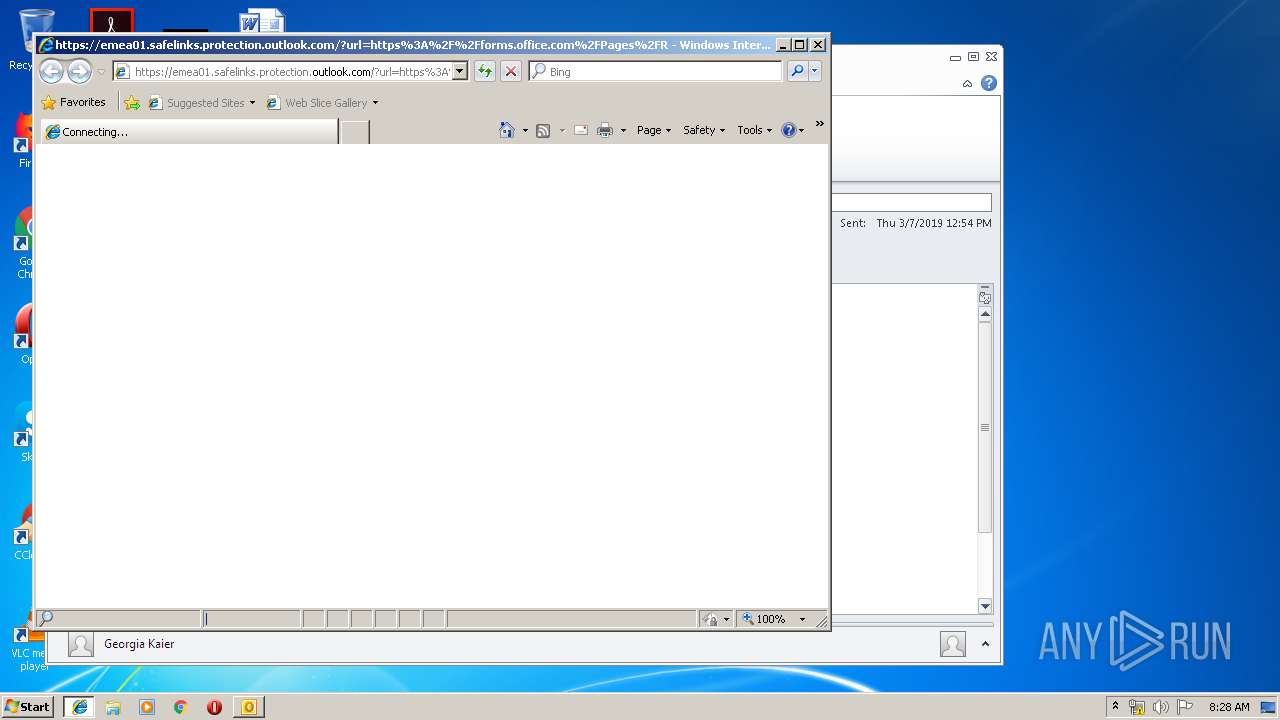
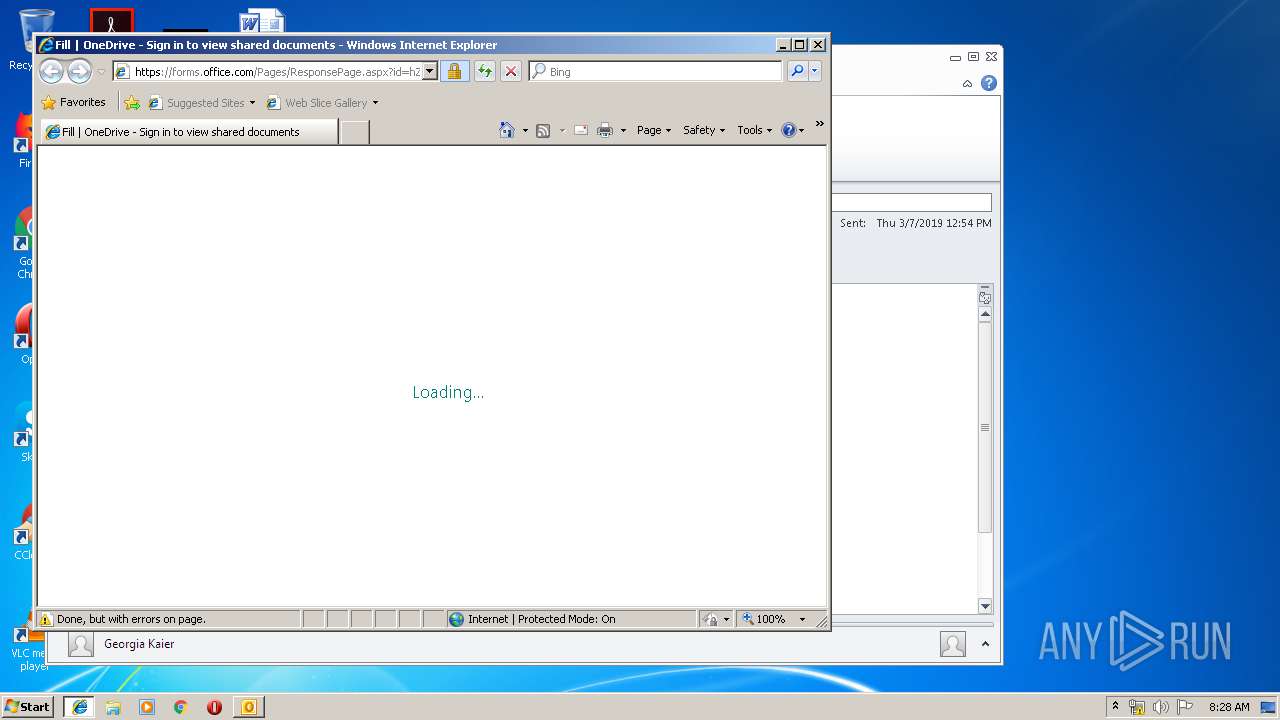
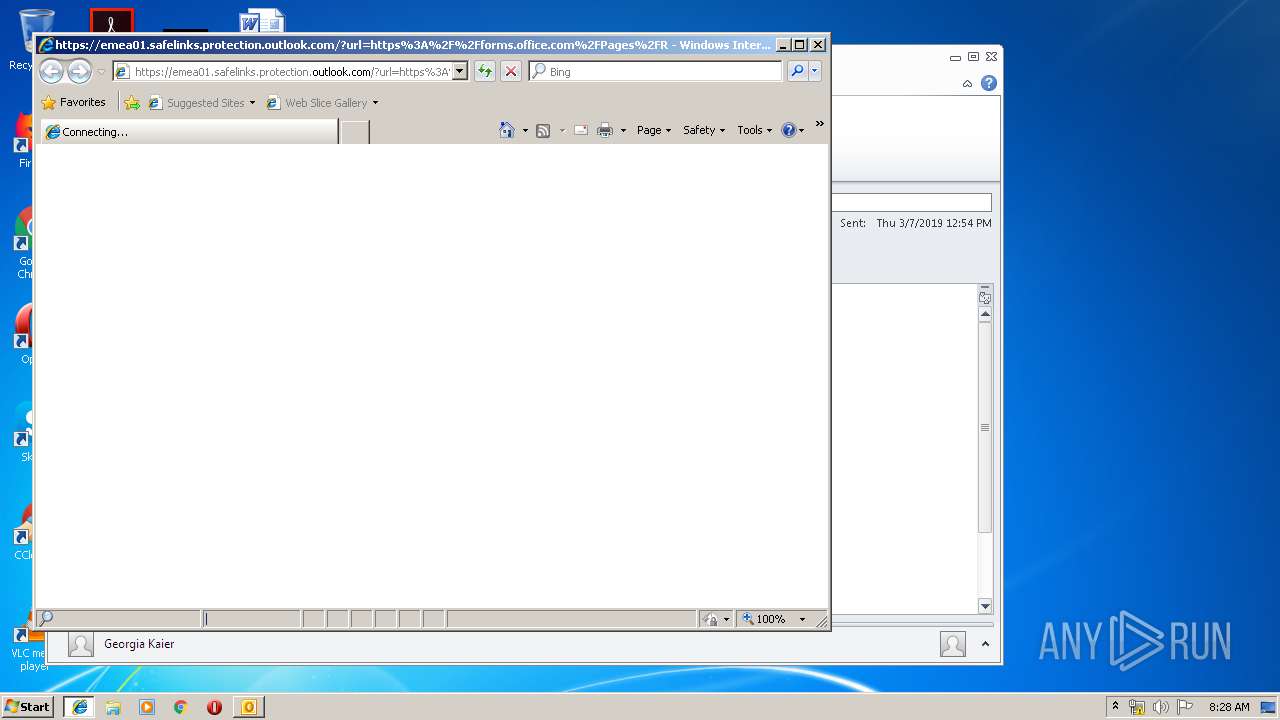
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2128)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2484)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3580)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 868)
- iexplore.exe (PID: 4088)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3580)
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 4088)
- iexplore.exe (PID: 3240)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2484)
- iexplore.exe (PID: 868)
Changes settings of System certificates
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 3240)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2128)
Application launched itself
- iexplore.exe (PID: 3240)
- chrome.exe (PID: 3644)
- iexplore.exe (PID: 2640)
Reads Internet Cache Settings
- iexplore.exe (PID: 4088)
- iexplore.exe (PID: 868)
Changes internet zones settings
- iexplore.exe (PID: 3240)
- iexplore.exe (PID: 2640)
Manual execution by user
- chrome.exe (PID: 3644)
Reads settings of System Certificates
- iexplore.exe (PID: 2640)
- chrome.exe (PID: 3644)
- iexplore.exe (PID: 3240)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 3240)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
60
Monitored processes
26
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,14388315340130669833,6274188756423030649,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11658210027538053520 --mojo-platform-channel-handle=4044 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2640 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,14388315340130669833,6274188756423030649,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11608487091767503755 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11608487091767503755 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,14388315340130669833,6274188756423030649,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16330134442150927211 --mojo-platform-channel-handle=4672 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,14388315340130669833,6274188756423030649,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12632274175828429980 --mojo-platform-channel-handle=4076 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,14388315340130669833,6274188756423030649,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3288111088979216900 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=928 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\The Green Check.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2484 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,14388315340130669833,6274188756423030649,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18128975967361938457 --mojo-platform-channel-handle=3996 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 210
Read events
1 596
Write events
584
Delete events
30
Modification events
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | 3q> |
Value: 33713E0050080000010000000000000000000000 | |||
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 500800004EDAED8FDD0ED50100000000 | |||
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220046400 | |||
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2128) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1320419349 | |||
Executable files
0
Suspicious files
69
Text files
163
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF123.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2128 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\14CC7A3A.dat | image | |
MD5:— | SHA256:— | |||
| 2128 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FFF4424C.dat | image | |
MD5:— | SHA256:— | |||
| 2128 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AFA52A79.dat | image | |
MD5:— | SHA256:— | |||
| 2128 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2128 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E0C3530E.dat | image | |
MD5:— | SHA256:— | |||
| 2128 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\76BF50F3.dat | image | |
MD5:— | SHA256:— | |||
| 2128 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\29B2EE58.dat | image | |
MD5:— | SHA256:— | |||
| 2640 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2128 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5960CBB7.dat | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
141
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2128 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3644 | chrome.exe | GET | 200 | 172.217.133.38:80 | http://r1---sn-hgn7rne7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=95.174.64.2&mm=28&mn=sn-hgn7rne7&ms=nvh&mt=1558337236&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
3644 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
3240 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2640 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2128 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
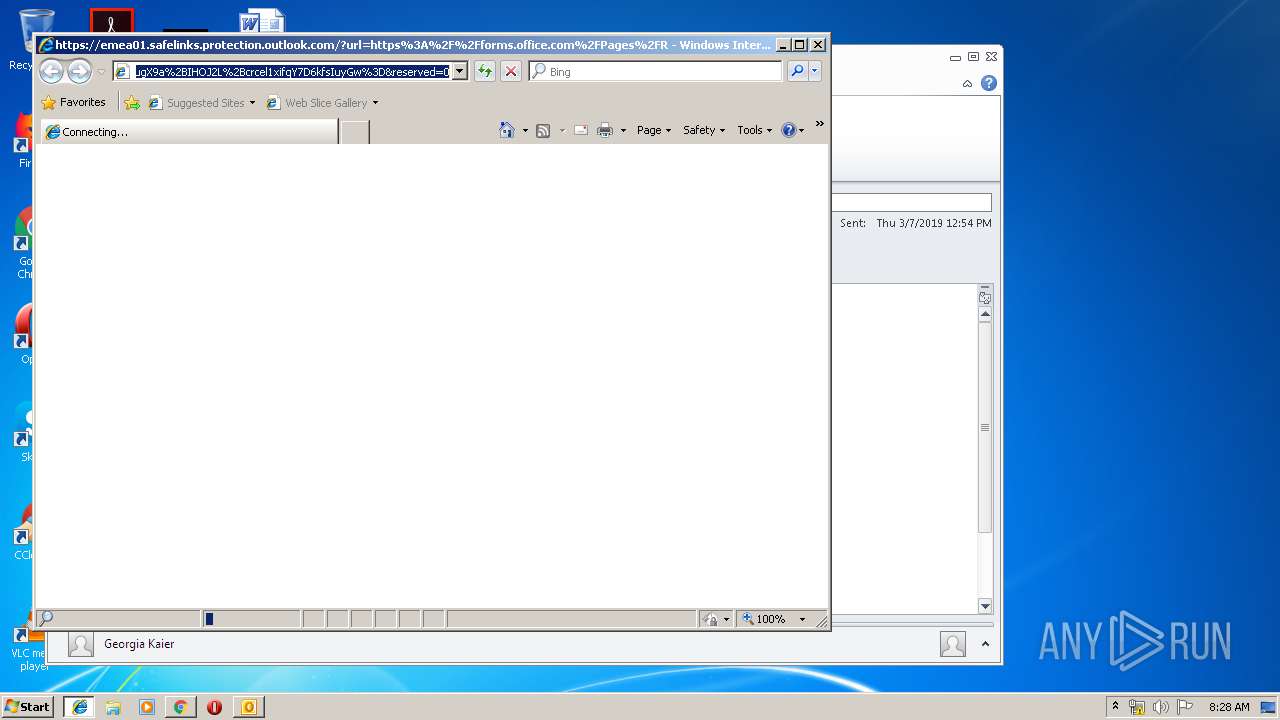
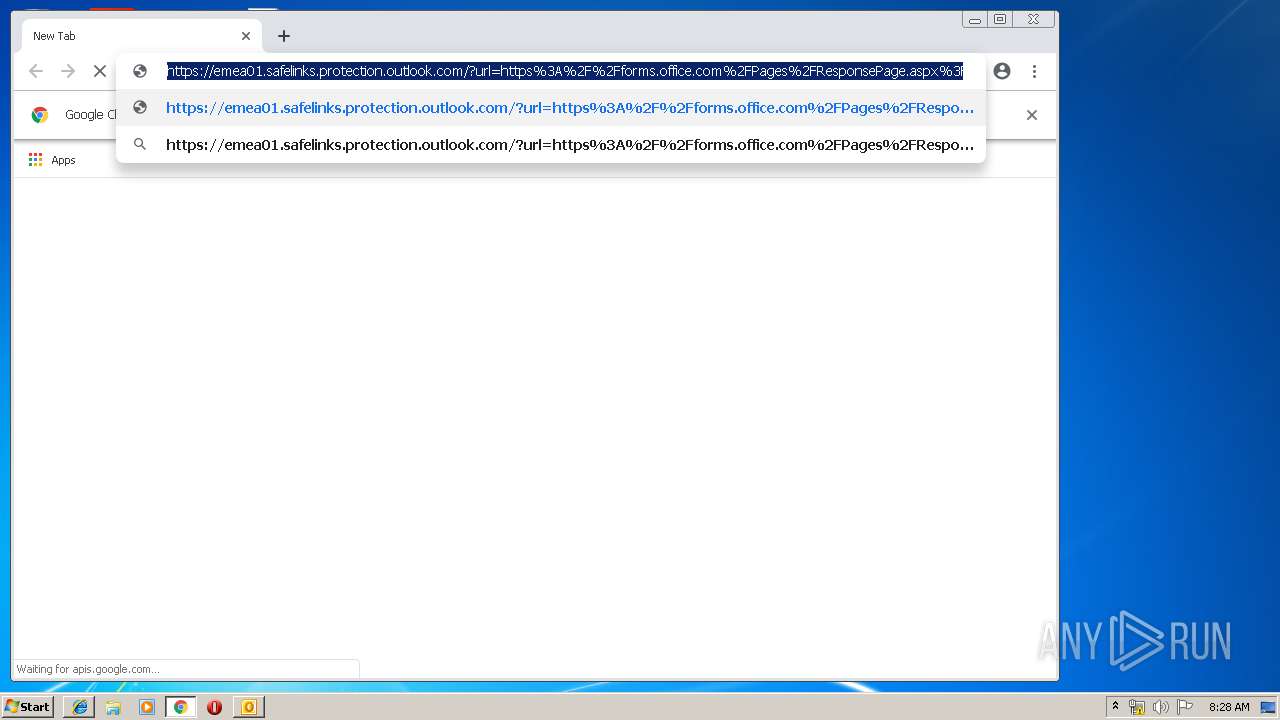
868 | iexplore.exe | 104.47.9.28:443 | emea01.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
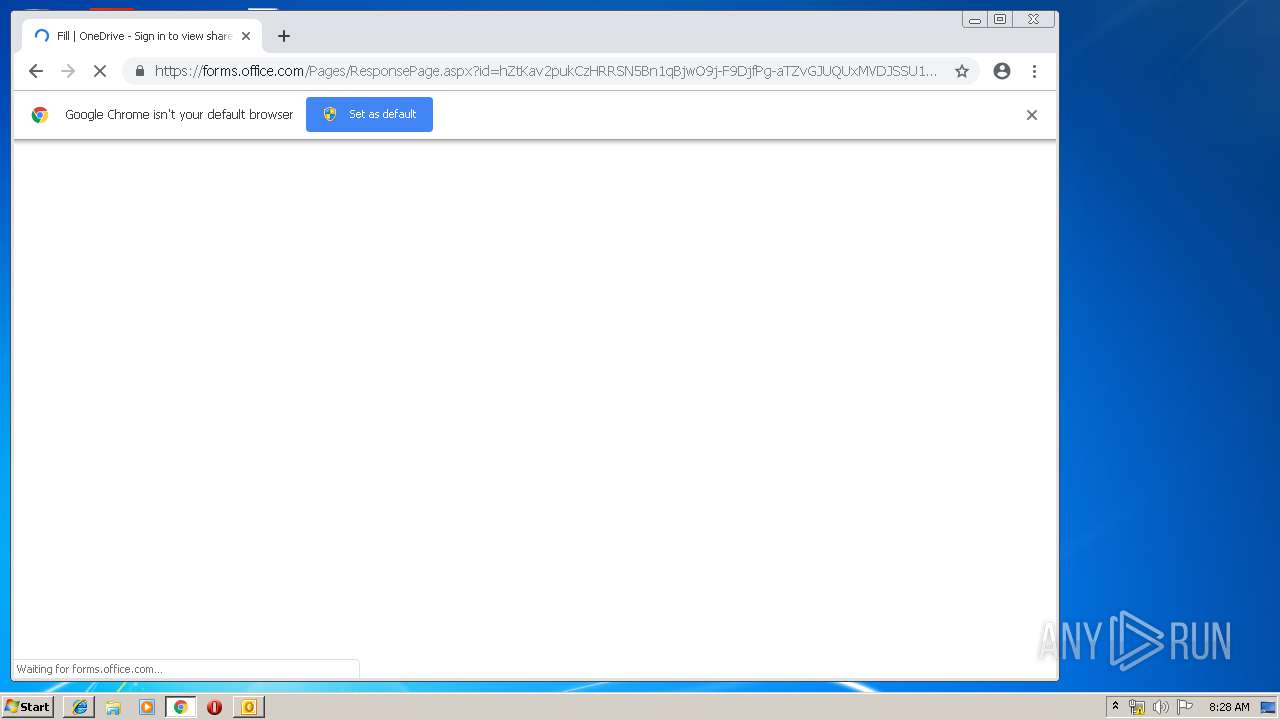
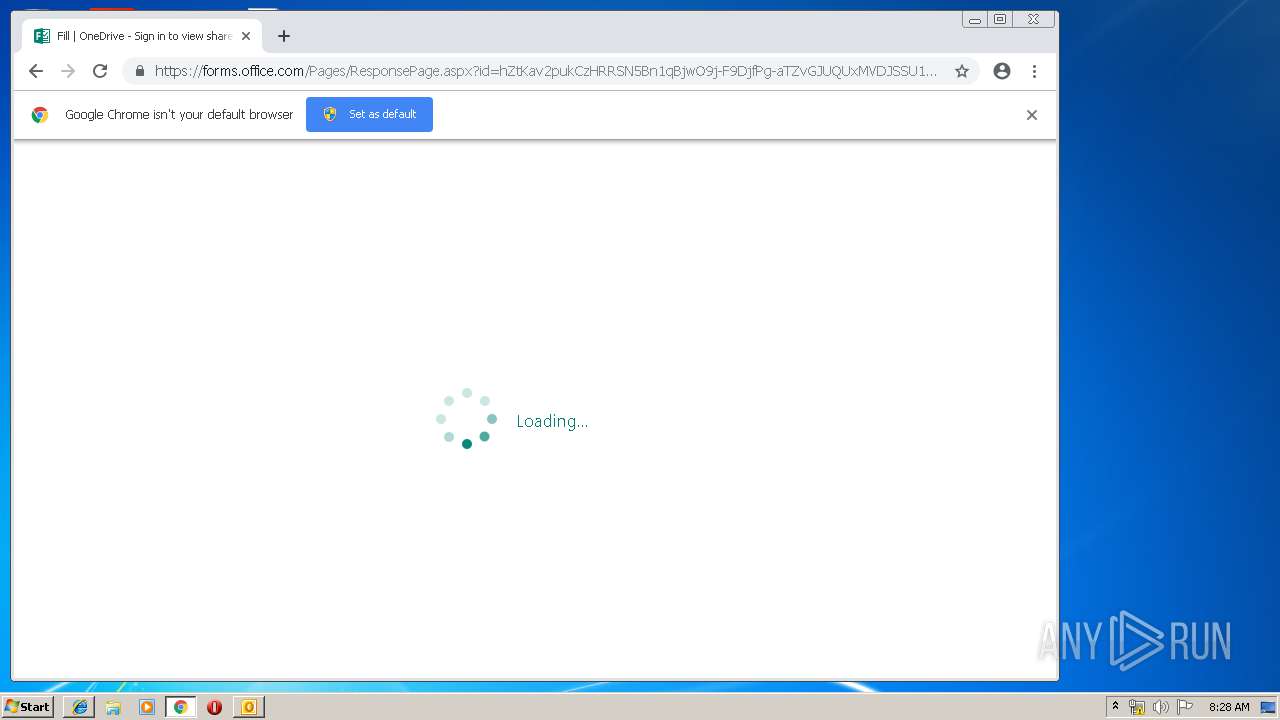
868 | iexplore.exe | 52.109.76.19:443 | forms.office.com | Microsoft Corporation | IE | whitelisted |
2640 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
868 | iexplore.exe | 152.199.19.160:443 | az725175.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
868 | iexplore.exe | 2.19.34.64:443 | static2.sharepointonline.com | Akamai International B.V. | — | whitelisted |
868 | iexplore.exe | 40.77.226.250:443 | web.vortex.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
— | — | 2.19.34.64:443 | static2.sharepointonline.com | Akamai International B.V. | — | whitelisted |
2640 | iexplore.exe | 52.109.76.19:443 | forms.office.com | Microsoft Corporation | IE | whitelisted |
4088 | iexplore.exe | 104.47.13.28:443 | emea01.safelinks.protection.outlook.com | Microsoft Corporation | FI | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
emea01.safelinks.protection.outlook.com |
| whitelisted |
www.bing.com |
| whitelisted |
forms.office.com |
| whitelisted |
az725175.vo.msecnd.net |
| whitelisted |
static2.sharepointonline.com |
| whitelisted |
web.vortex.data.microsoft.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |