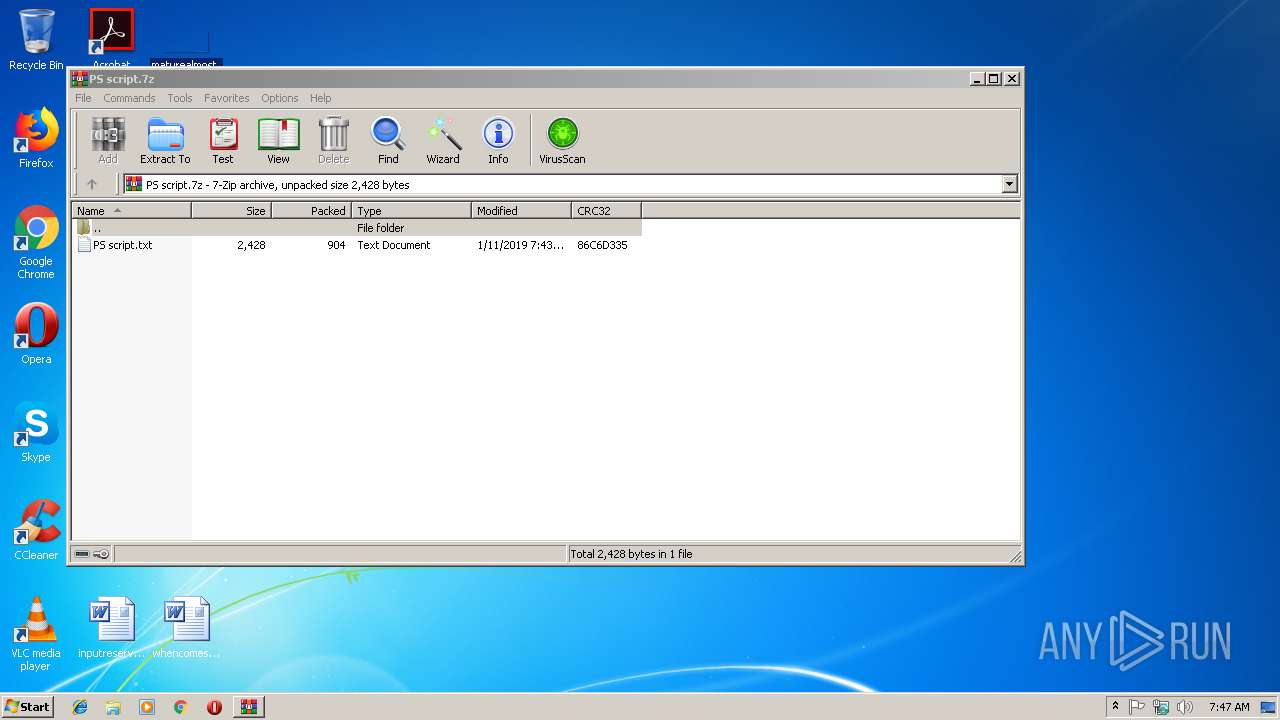
| File name: | PS script.7z |
| Full analysis: | https://app.any.run/tasks/4ea2f1d1-dc8a-48db-9cf5-32bcc2492163 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 07:47:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | FFD8F6B05881D8E9A4EFC21A6A3161FE |
| SHA1: | 06AA24C98EFA4C5AA676A3B8A895A1D423A8987D |
| SHA256: | EC2390FC9399A87C9626E78935095AEDC6F9C78DEB1A9FD20CB134A74BDDFA42 |
| SSDEEP: | 24:2AH++lO4+uMMF4e4p6kLQXeqWrgCqWS5vlWSus:2NRBuyQXeb0CzZs |
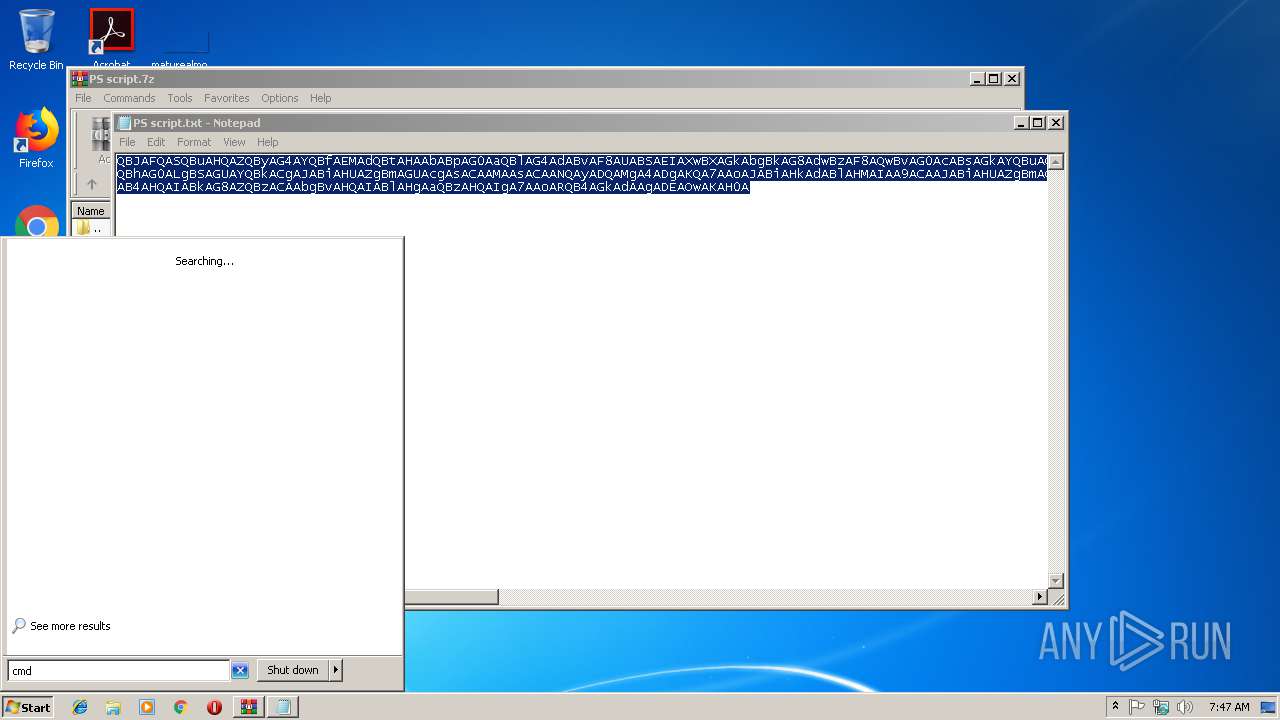
MALICIOUS
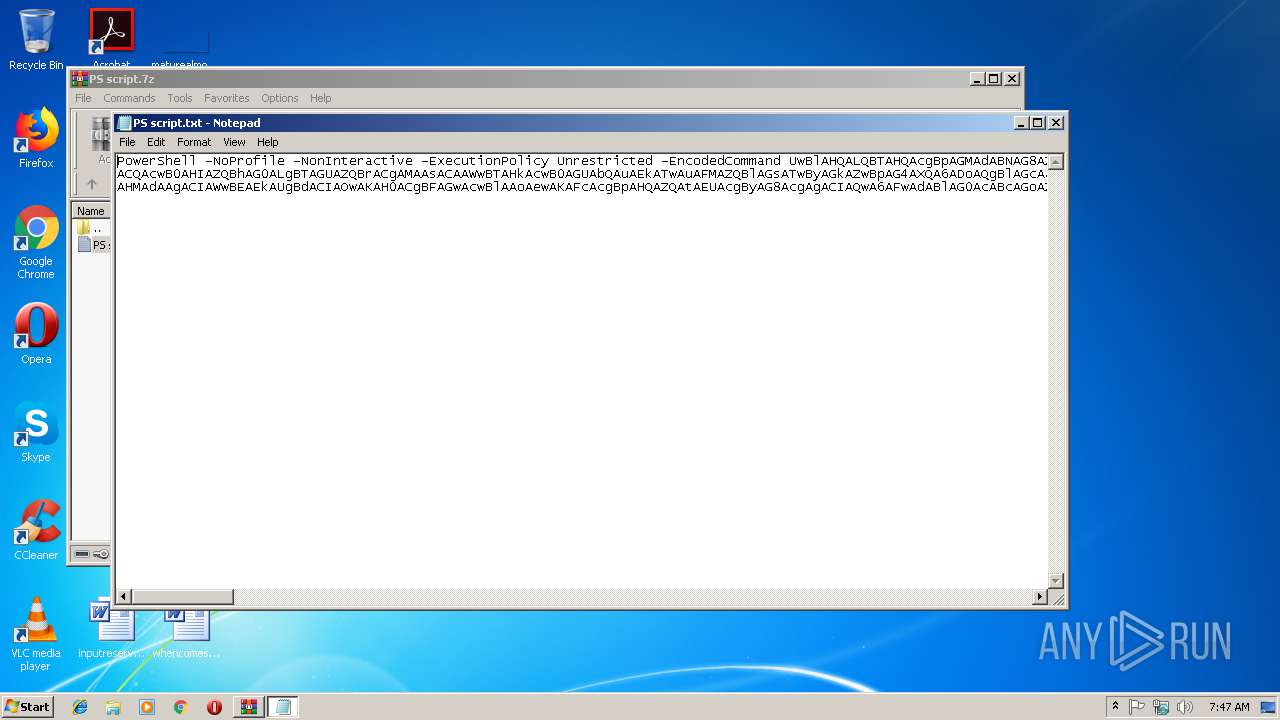
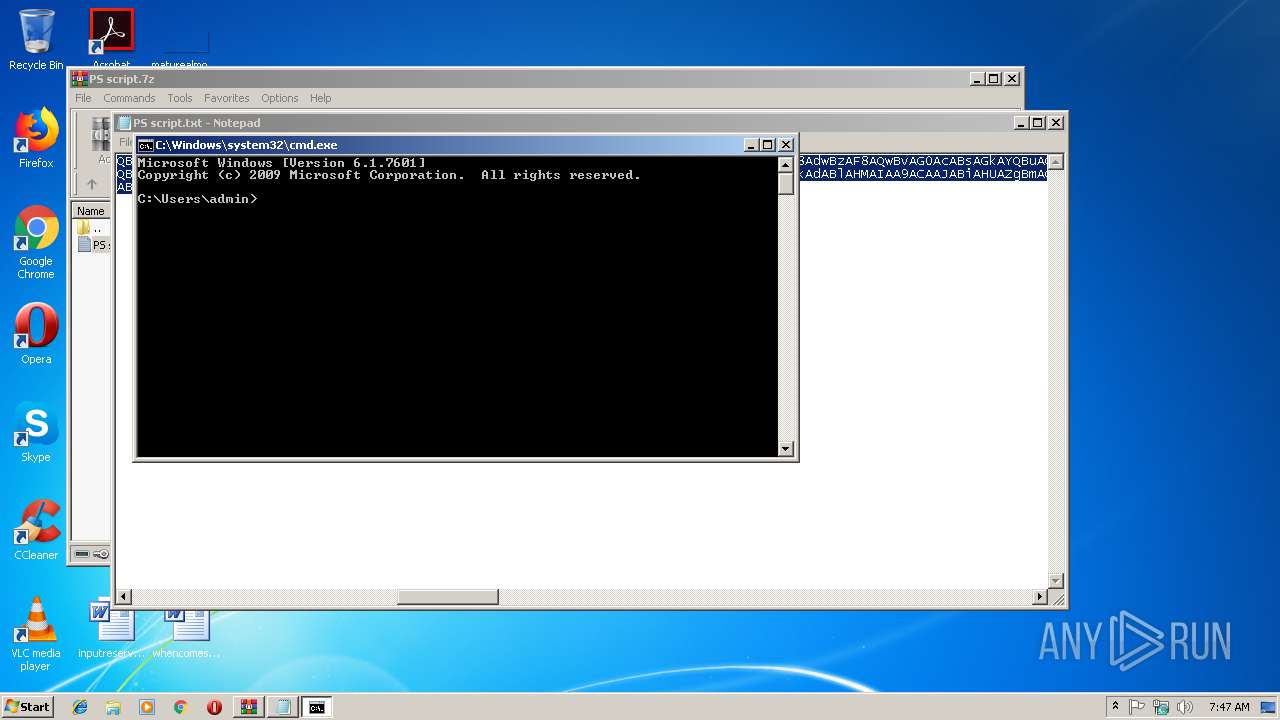
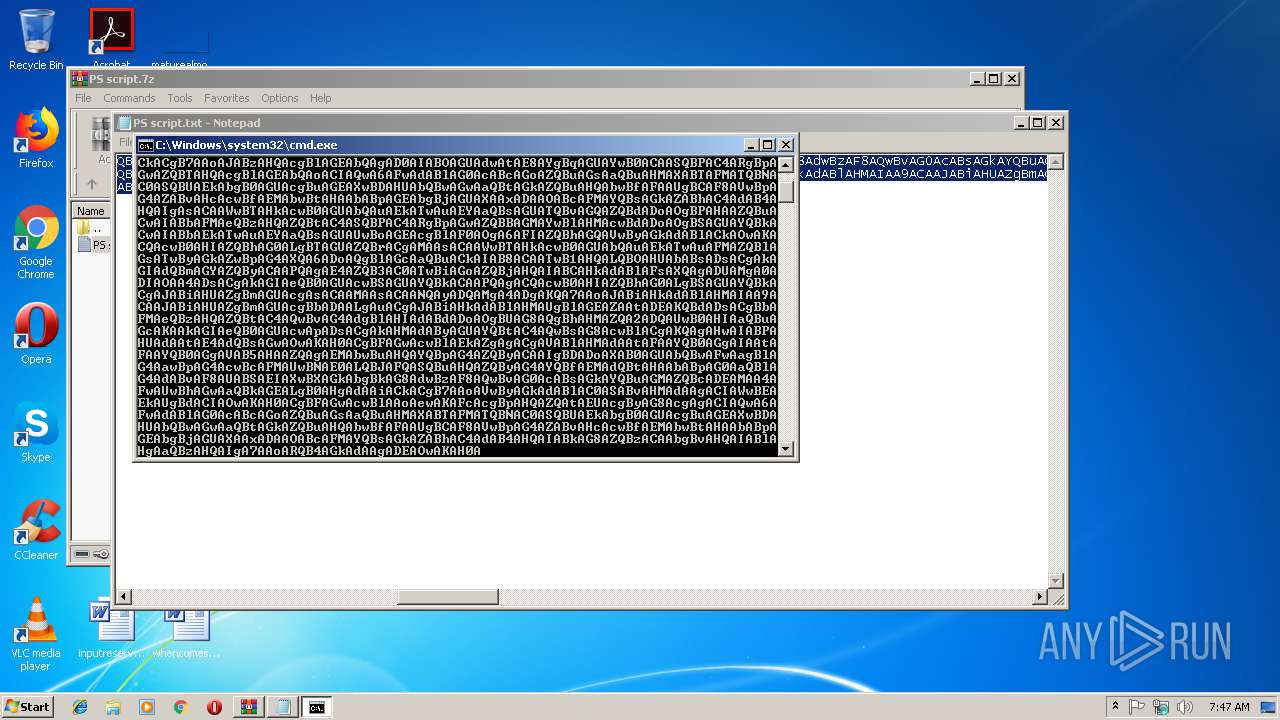
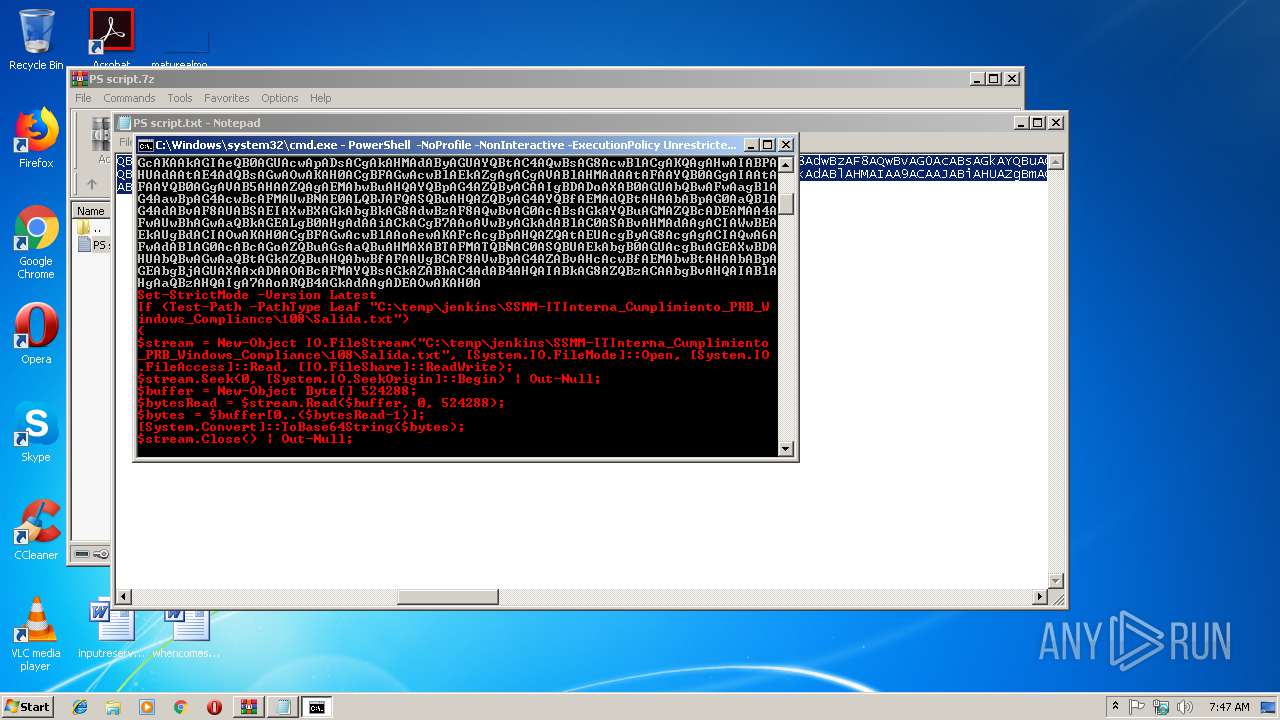
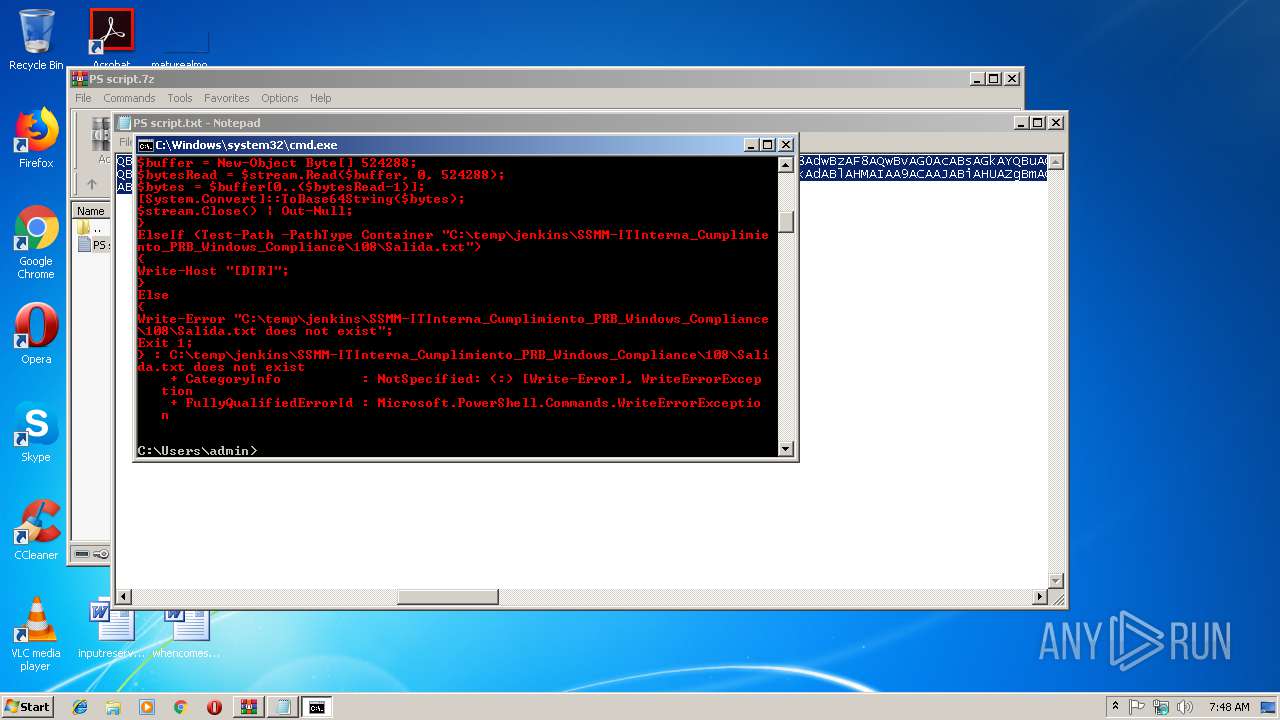
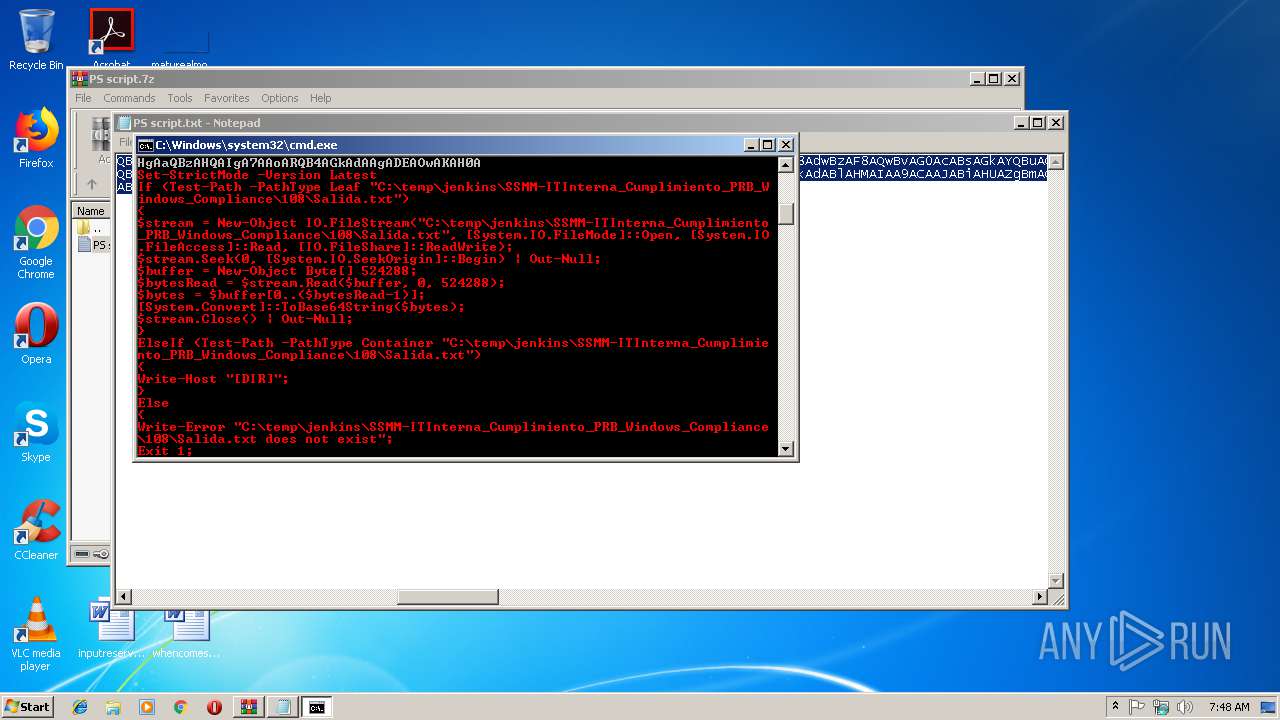
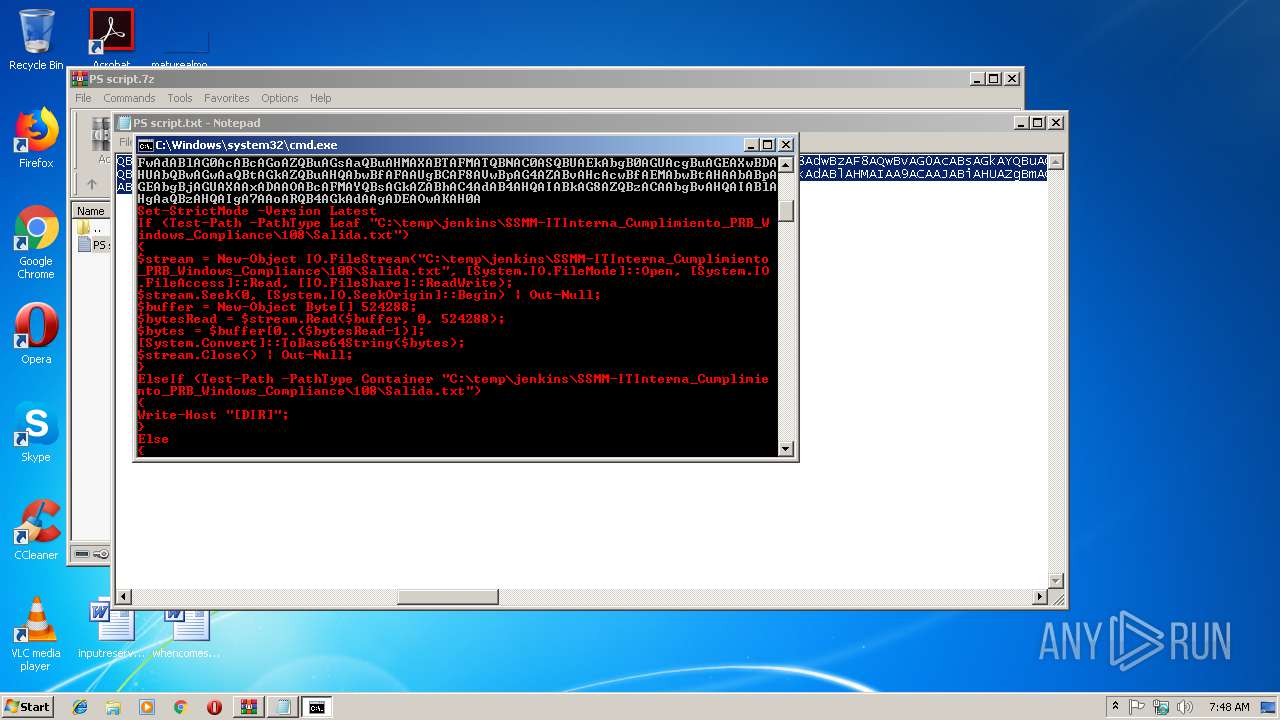
Executes PowerShell scripts
- cmd.exe (PID: 3804)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3056)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
34
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
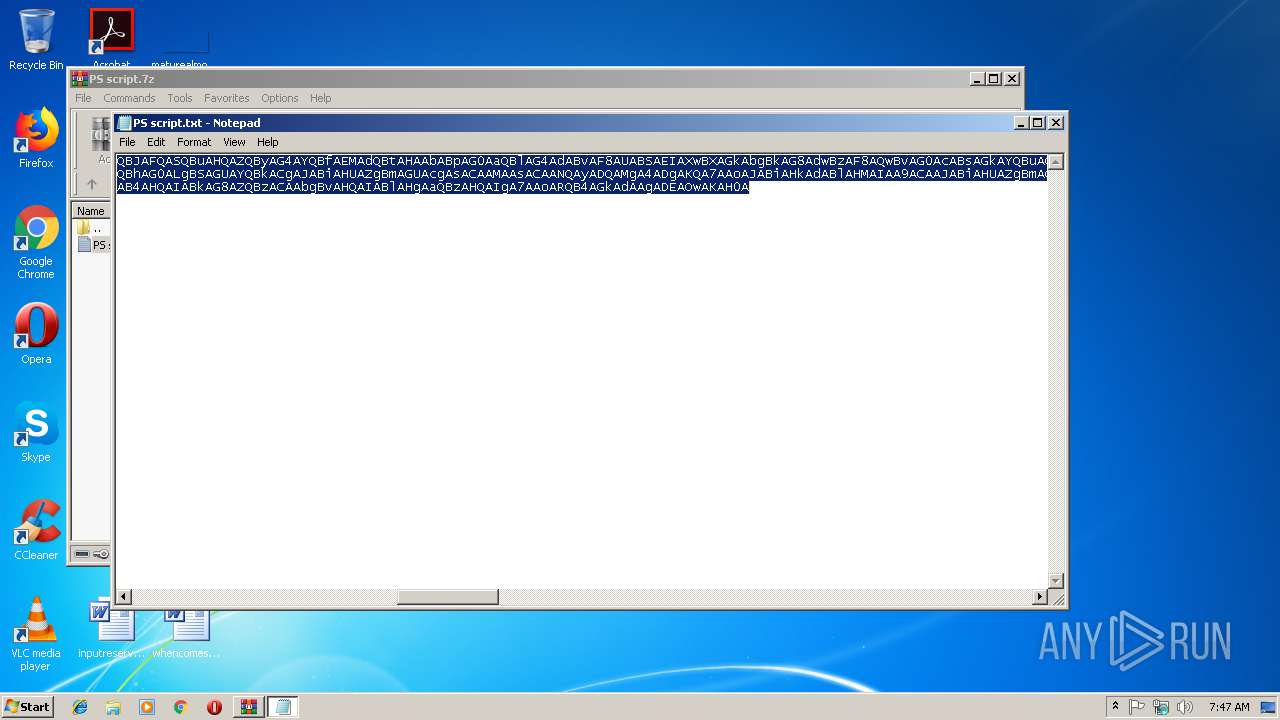
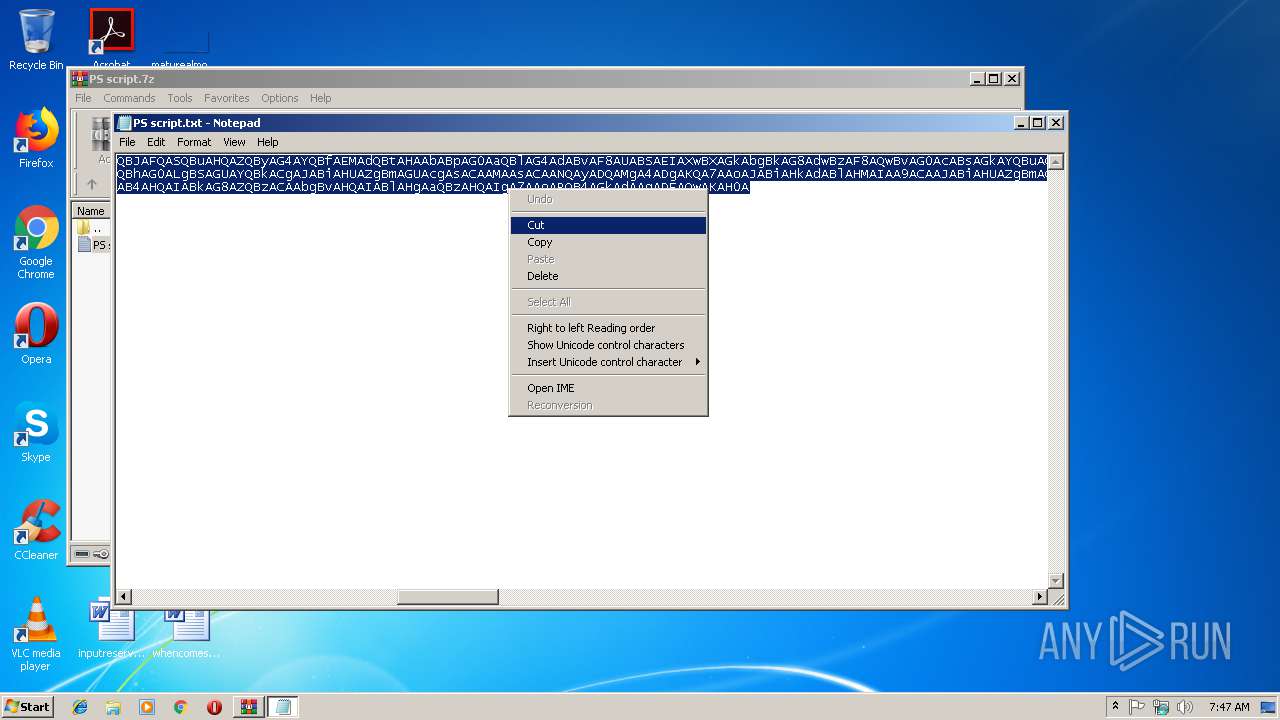
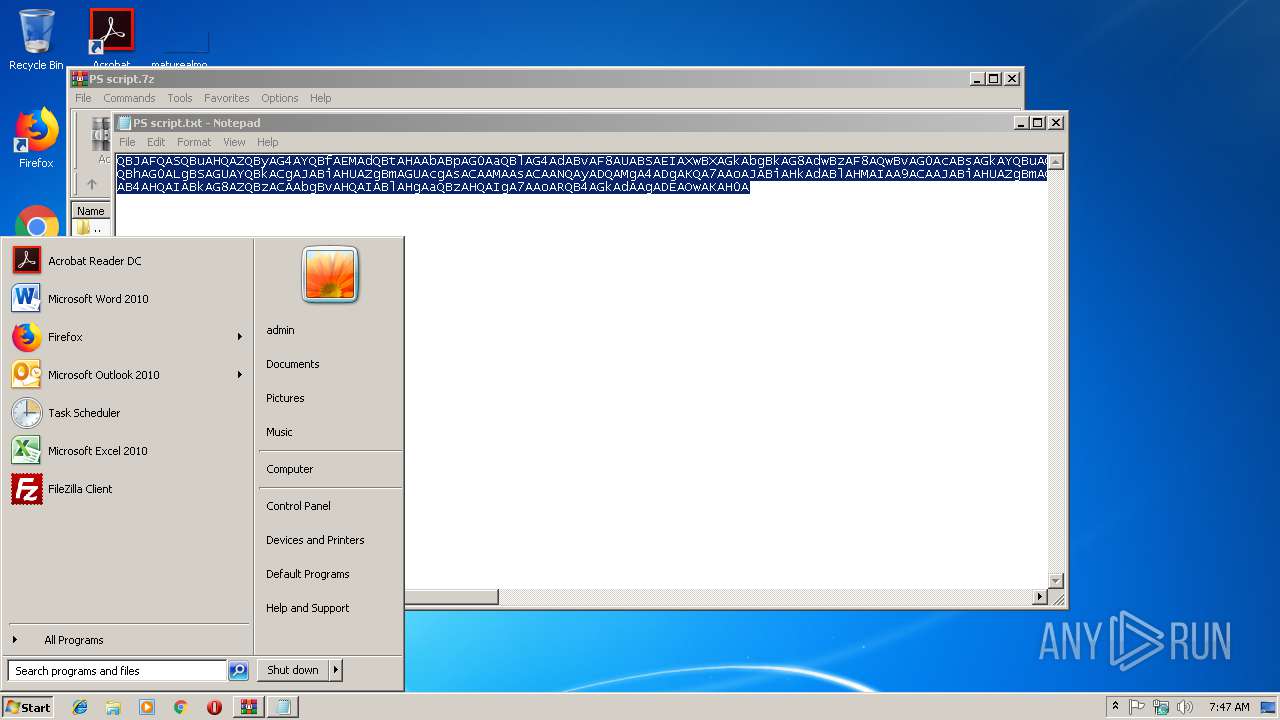
| 2616 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa2988.35809\PS script.txt | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2988 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\PS script.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
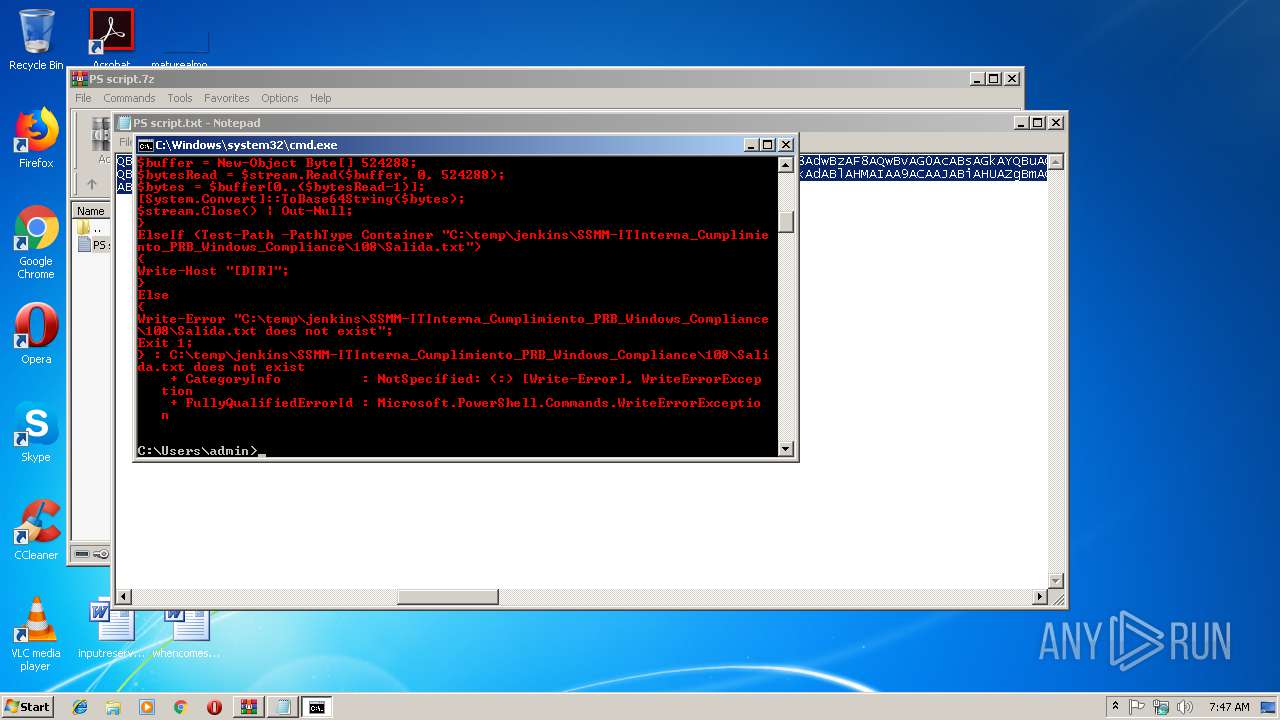
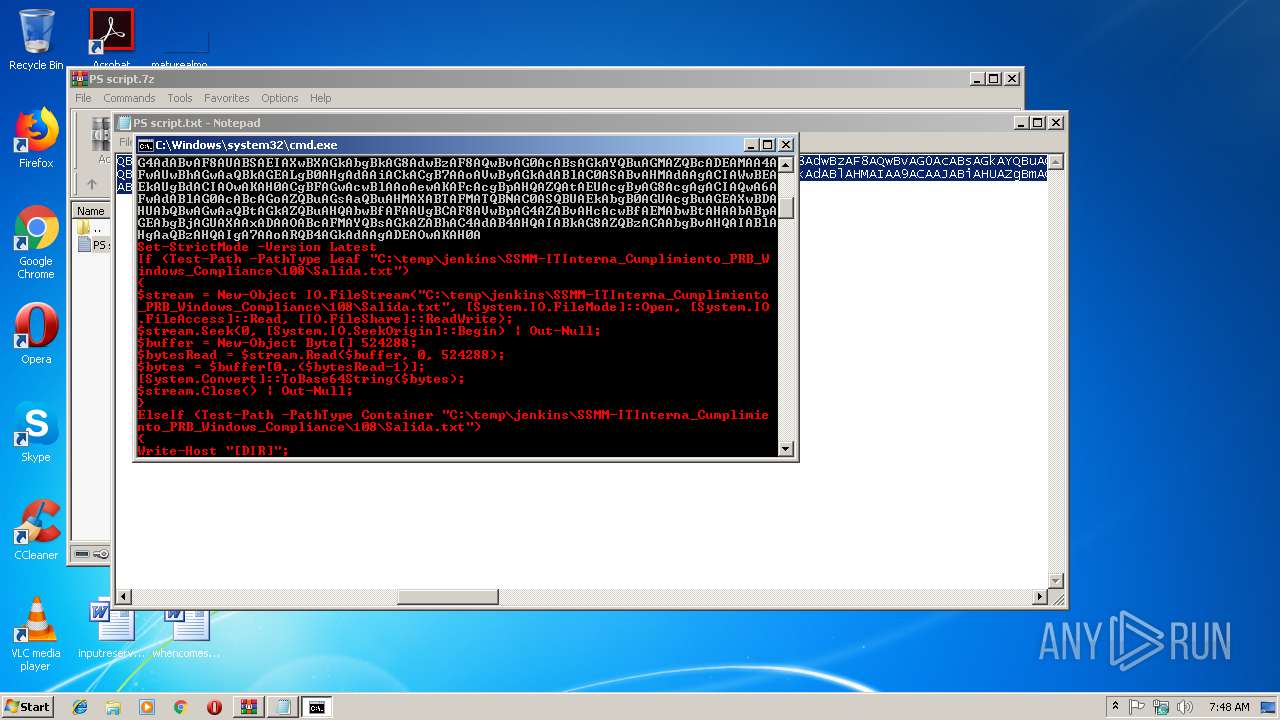
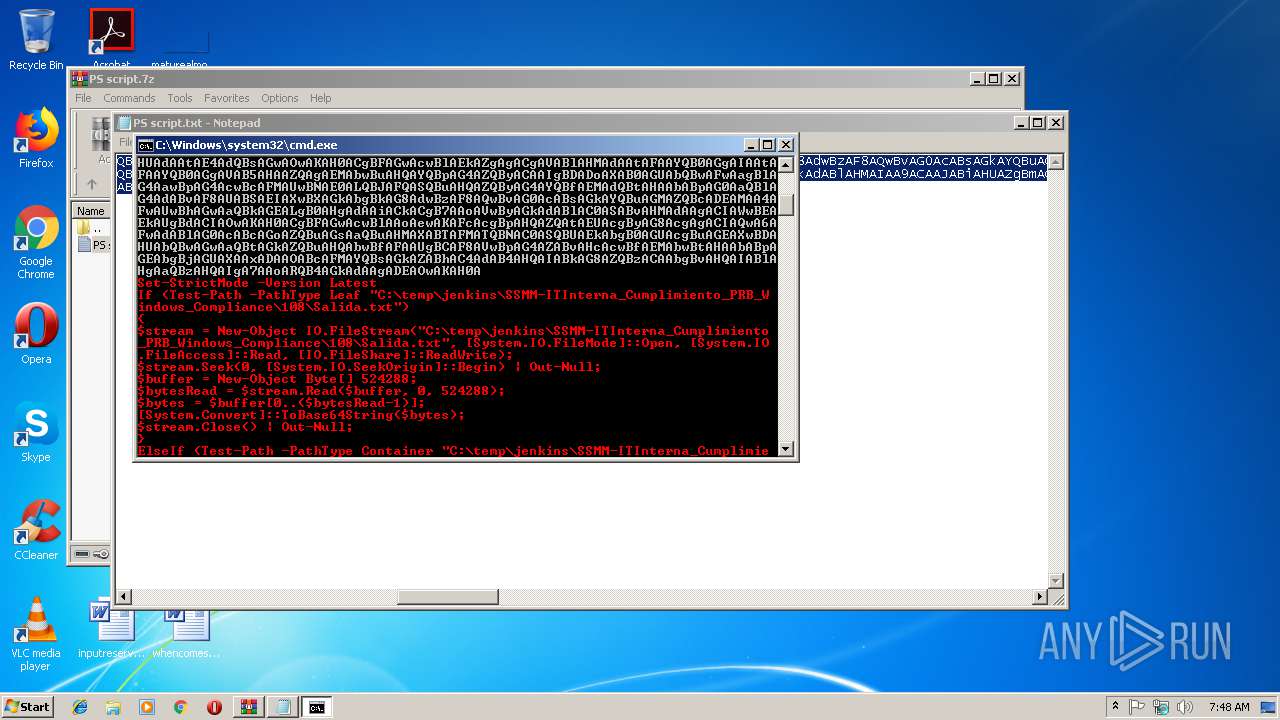
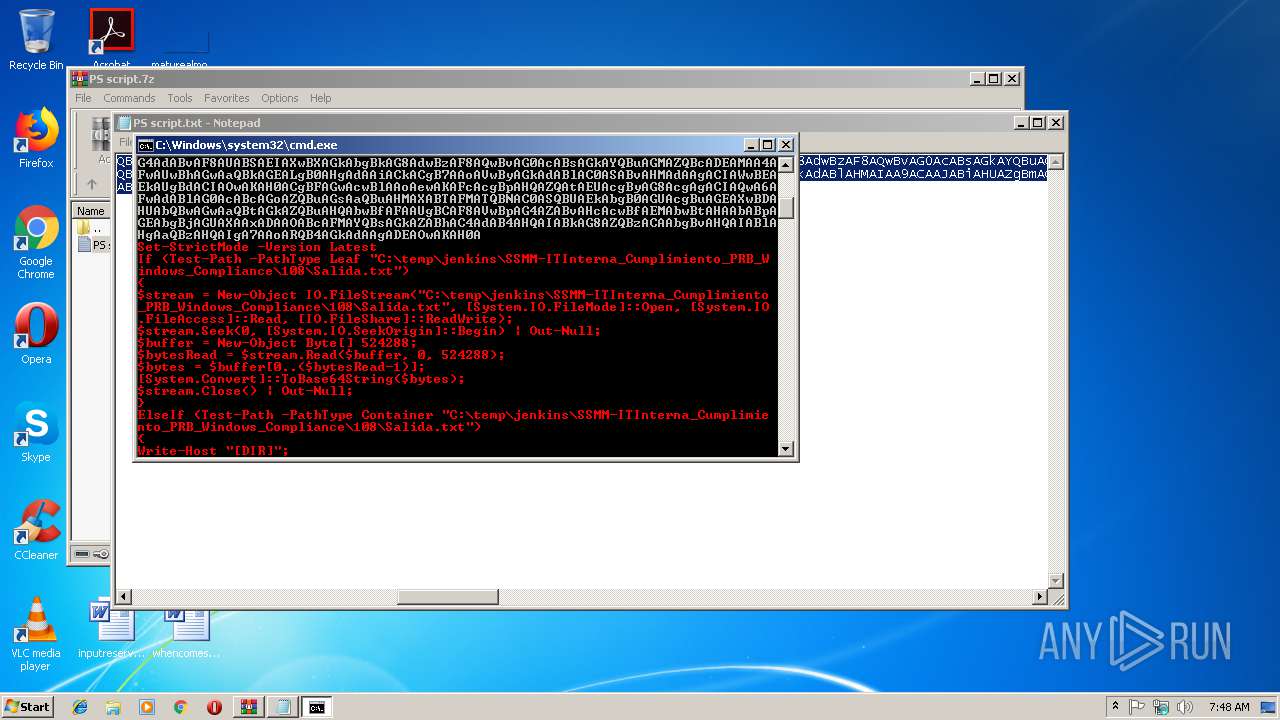
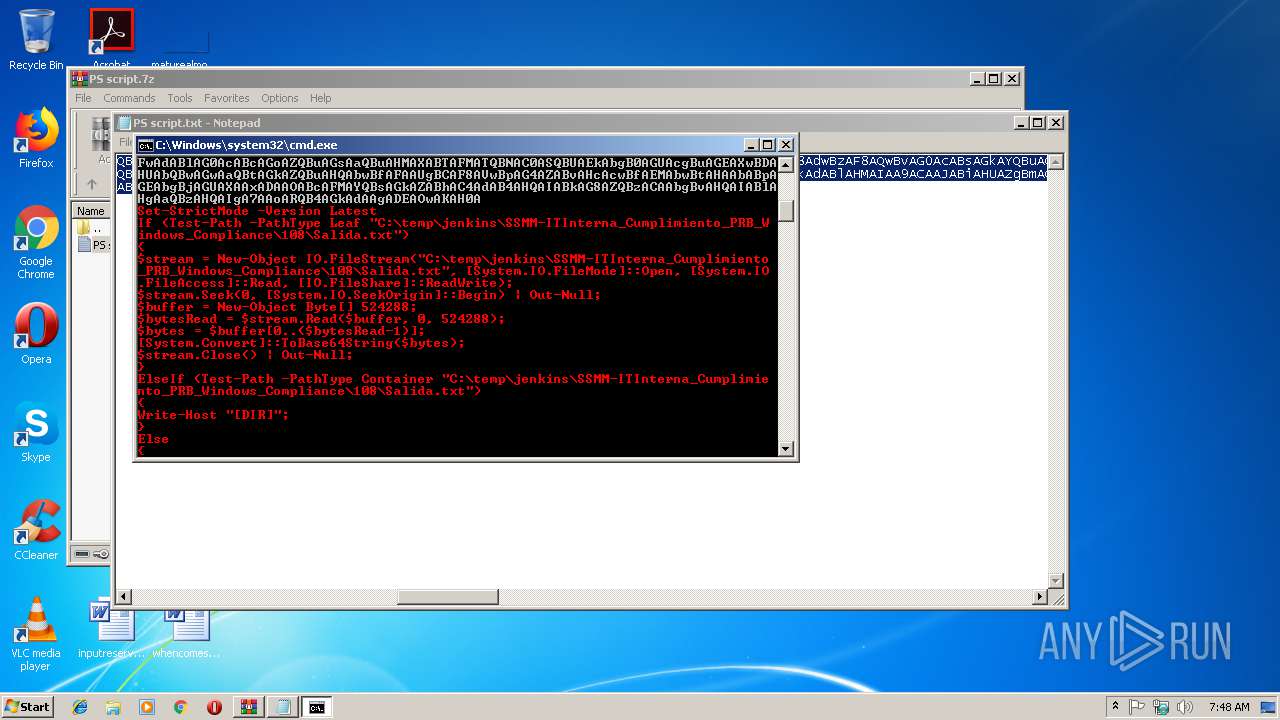
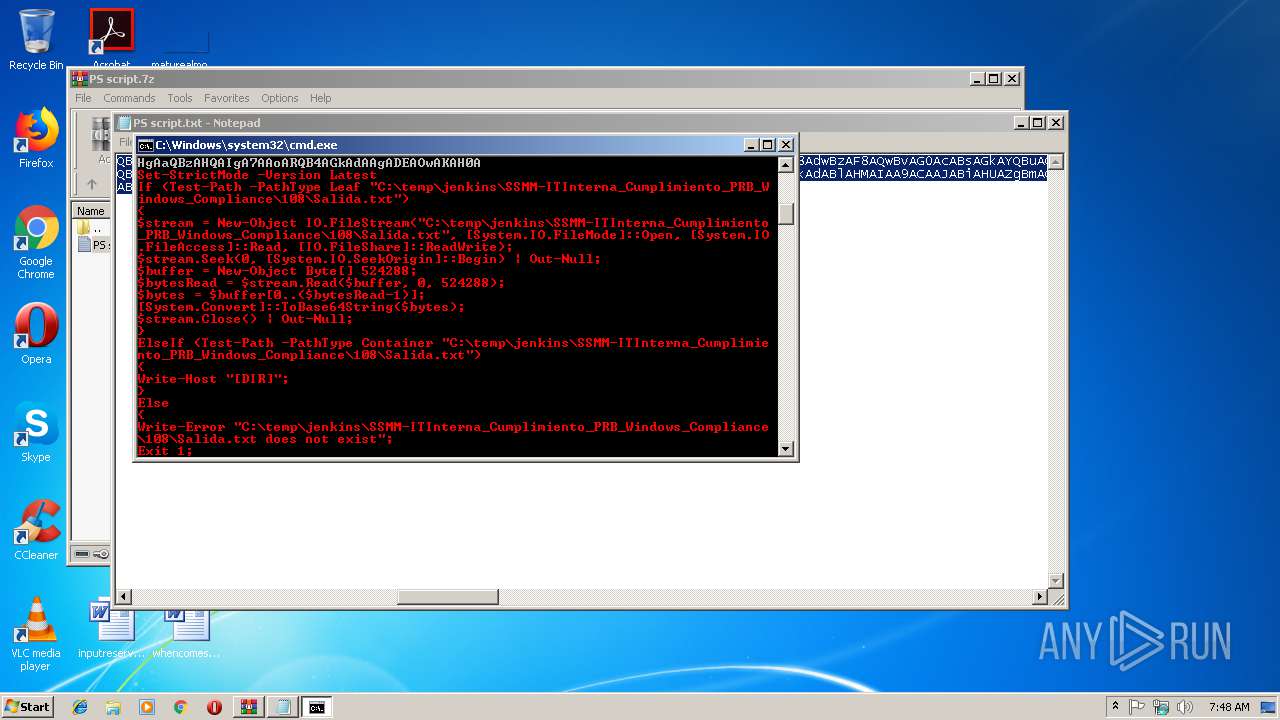
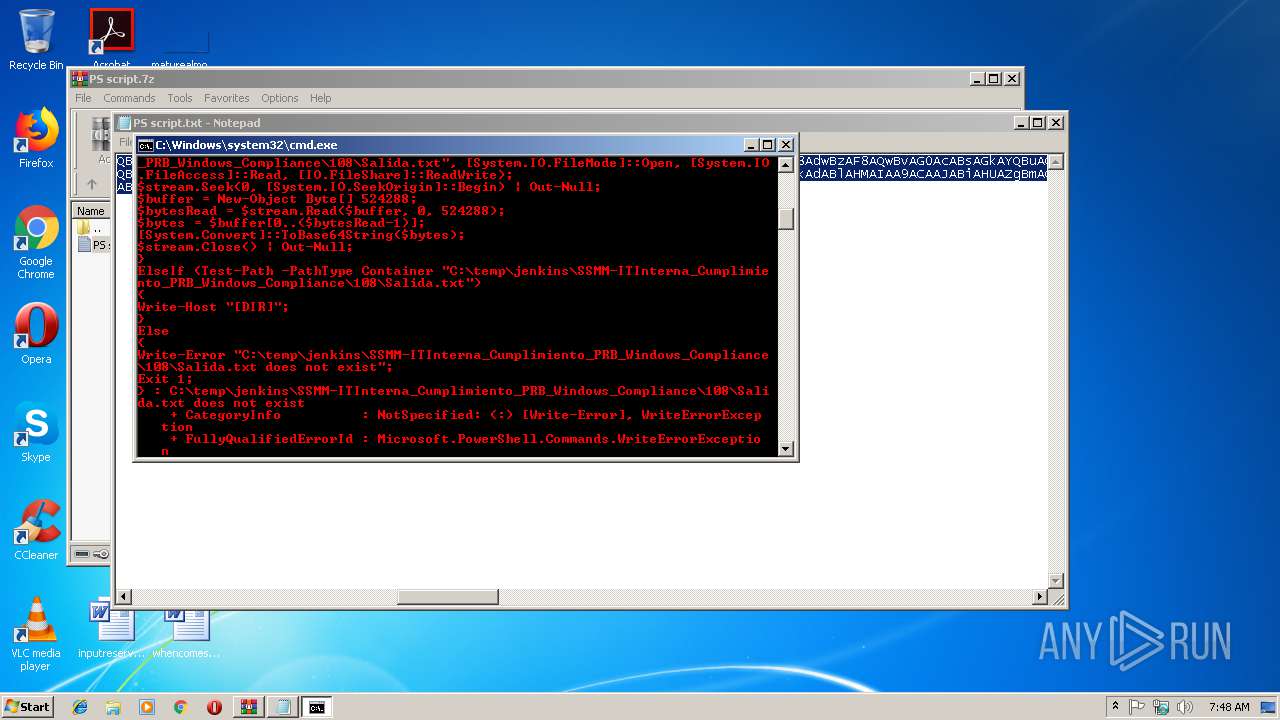
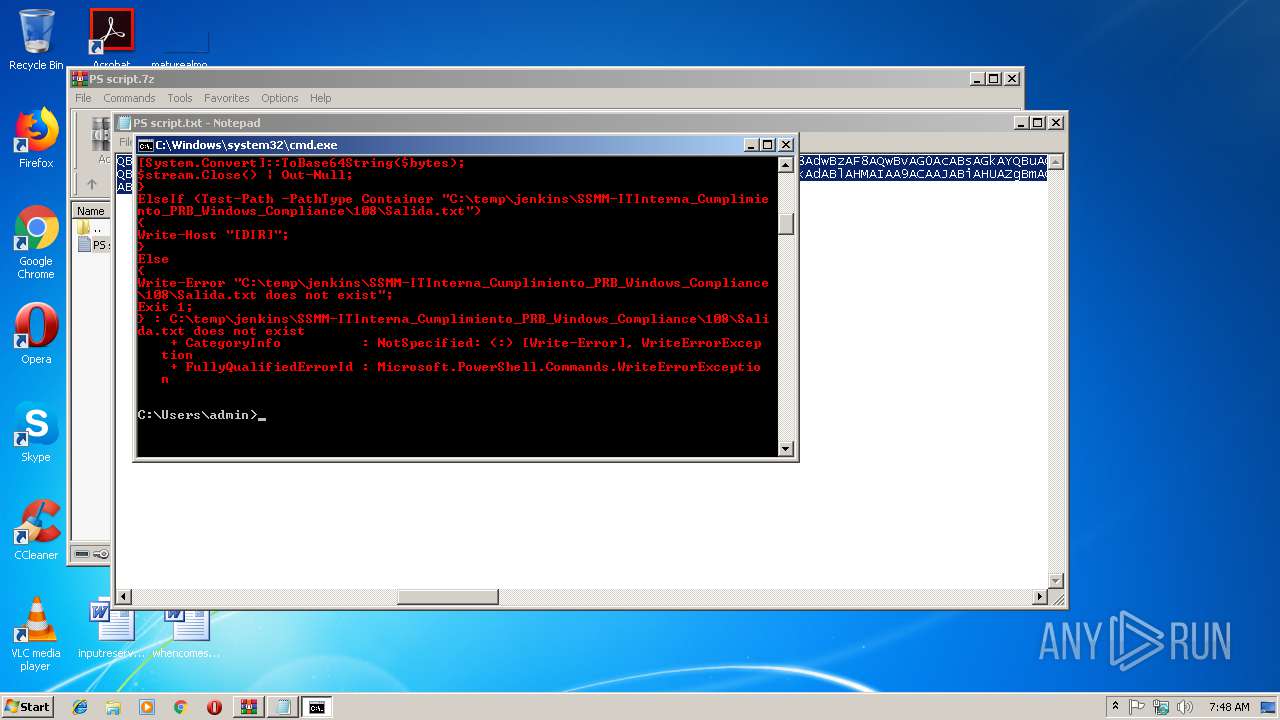
| 3056 | PowerShell -NoProfile -NonInteractive -ExecutionPolicy Unrestricted -EncodedCommand UwBlAHQALQBTAHQAcgBpAGMAdABNAG8AZABlACAALQBWAGUAcgBzAGkAbwBuACAATABhAHQAZQBzAHQACgBJAGYAIAAoAFQAZQBzAHQALQBQAGEAdABoACAALQBQAGEAdABoAFQAeQBwAGUAIABMAGUAYQBmACAAIgBDADoAXAB0AGUAbQBwAFwAagBlAG4AawBpAG4AcwBcAFMAUwBNAE0ALQBJAFQASQBuAHQAZQByAG4AYQBfAEMAdQBtAHAAbABpAG0AaQBlAG4AdABvAF8AUABSAEIAXwBXAGkAbgBkAG8AdwBzAF8AQwBvAG0AcABsAGkAYQBuAGMAZQBcADEAMAA4AFwAUwBhAGwAaQBkAGEALgB0AHgAdAAiACkACgB7AAoAJABzAHQAcgBlAGEAbQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAASQBPAC4ARgBpAGwAZQBTAHQAcgBlAGEAbQAoACIAQwA6AFwAdABlAG0AcABcAGoAZQBuAGsAaQBuAHMAXABTAFMATQBNAC0ASQBUAEkAbgB0AGUAcgBuAGEAXwBDAHUAbQBwAGwAaQBtAGkAZQBuAHQAbwBfAFAAUgBCAF8AVwBpAG4AZABvAHcAcwBfAEMAbwBtAHAAbABpAGEAbgBjAGUAXAAxADAAOABcAFMAYQBsAGkAZABhAC4AdAB4AHQAIgAsACAAWwBTAHkAcwB0AGUAbQAuAEkATwAuAEYAaQBsAGUATQBvAGQAZQBdADoAOgBPAHAAZQBuACwAIABbAFMAeQBzAHQAZQBtAC4ASQBPAC4ARgBpAGwAZQBBAGMAYwBlAHMAcwBdADoAOgBSAGUAYQBkACwAIABbAEkATwAuAEYAaQBsAGUAUwBoAGEAcgBlAF0AOgA6AFIAZQBhAGQAVwByAGkAdABlACkAOwAKACQAcwB0AHIAZQBhAG0ALgBTAGUAZQBrACgAMAAsACAAWwBTAHkAcwB0AGUAbQAuAEkATwAuAFMAZQBlAGsATwByAGkAZwBpAG4AXQA6ADoAQgBlAGcAaQBuACkAIAB8ACAATwB1AHQALQBOAHUAbABsADsACgAkAGIAdQBmAGYAZQByACAAPQAgAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABCAHkAdABlAFsAXQAgADUAMgA0ADIAOAA4ADsACgAkAGIAeQB0AGUAcwBSAGUAYQBkACAAPQAgACQAcwB0AHIAZQBhAG0ALgBSAGUAYQBkACgAJABiAHUAZgBmAGUAcgAsACAAMAAsACAANQAyADQAMgA4ADgAKQA7AAoAJABiAHkAdABlAHMAIAA9ACAAJABiAHUAZgBmAGUAcgBbADAALgAuACgAJABiAHkAdABlAHMAUgBlAGEAZAAtADEAKQBdADsACgBbAFMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBUAG8AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGIAeQB0AGUAcwApADsACgAkAHMAdAByAGUAYQBtAC4AQwBsAG8AcwBlACgAKQAgAHwAIABPAHUAdAAtAE4AdQBsAGwAOwAKAH0ACgBFAGwAcwBlAEkAZgAgACgAVABlAHMAdAAtAFAAYQB0AGgAIAAtAFAAYQB0AGgAVAB5AHAAZQAgAEMAbwBuAHQAYQBpAG4AZQByACAAIgBDADoAXAB0AGUAbQBwAFwAagBlAG4AawBpAG4AcwBcAFMAUwBNAE0ALQBJAFQASQBuAHQAZQByAG4AYQBfAEMAdQBtAHAAbABpAG0AaQBlAG4AdABvAF8AUABSAEIAXwBXAGkAbgBkAG8AdwBzAF8AQwBvAG0AcABsAGkAYQBuAGMAZQBcADEAMAA4AFwAUwBhAGwAaQBkAGEALgB0AHgAdAAiACkACgB7AAoAVwByAGkAdABlAC0ASABvAHMAdAAgACIAWwBEAEkAUgBdACIAOwAKAH0ACgBFAGwAcwBlAAoAewAKAFcAcgBpAHQAZQAtAEUAcgByAG8AcgAgACIAQwA6AFwAdABlAG0AcABcAGoAZQBuAGsAaQBuAHMAXABTAFMATQBNAC0ASQBUAEkAbgB0AGUAcgBuAGEAXwBDAHUAbQBwAGwAaQBtAGkAZQBuAHQAbwBfAFAAUgBCAF8AVwBpAG4AZABvAHcAcwBfAEMAbwBtAHAAbABpAGEAbgBjAGUAXAAxADAAOABcAFMAYQBsAGkAZABhAC4AdAB4AHQAIABkAG8AZQBzACAAbgBvAHQAIABlAHgAaQBzAHQAIgA7AAoARQB4AGkAdAAgADEAOwAKAH0A | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3804 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
683
Read events
619
Write events
64
Delete events
0
Modification events
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PS script.7z | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3056) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RW4Z9GYAAK7SDTFD291F.temp | — | |
MD5:— | SHA256:— | |||
| 2988 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2988.35809\PS script.txt | text | |
MD5:— | SHA256:— | |||
| 3056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF21538e.TMP | binary | |
MD5:— | SHA256:— | |||
| 3056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report