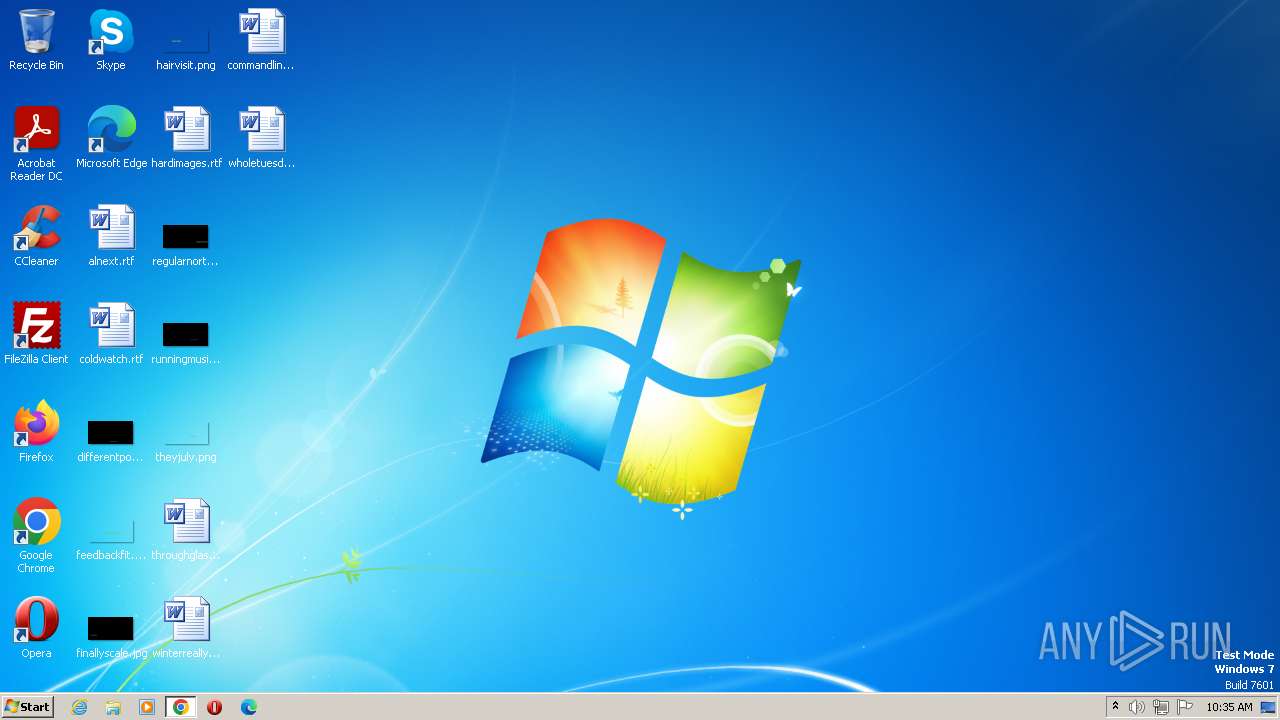
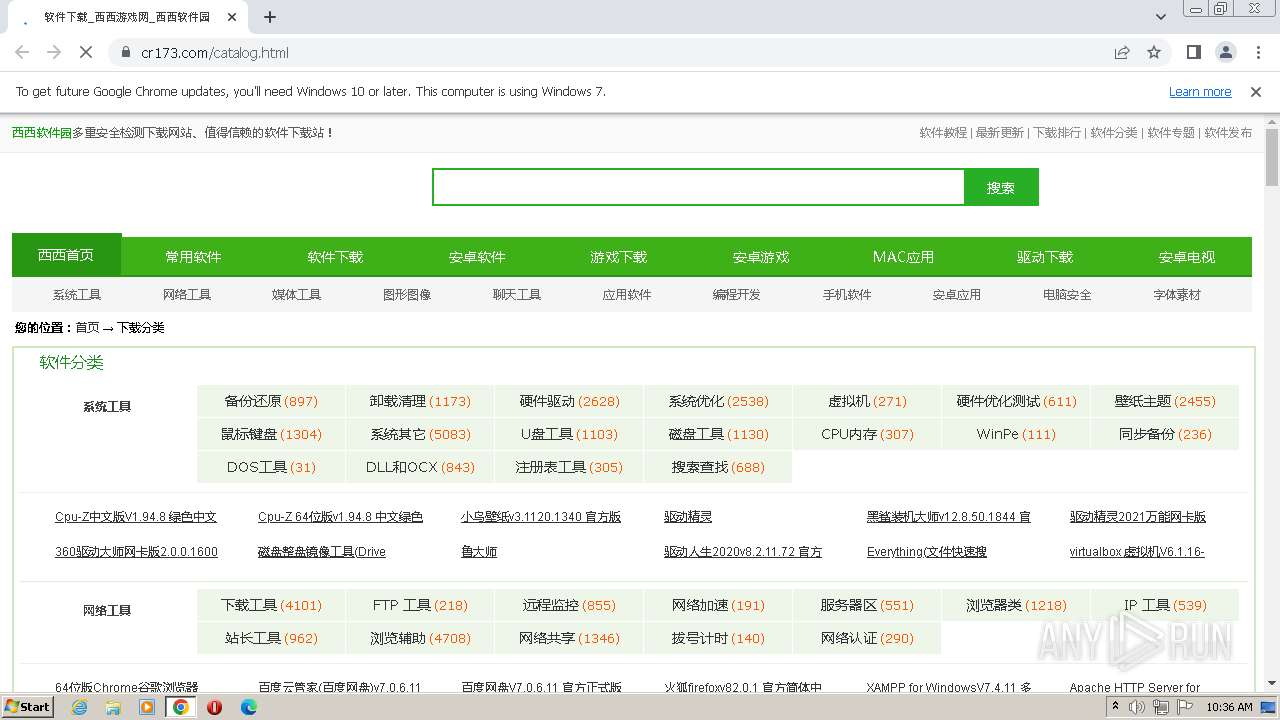
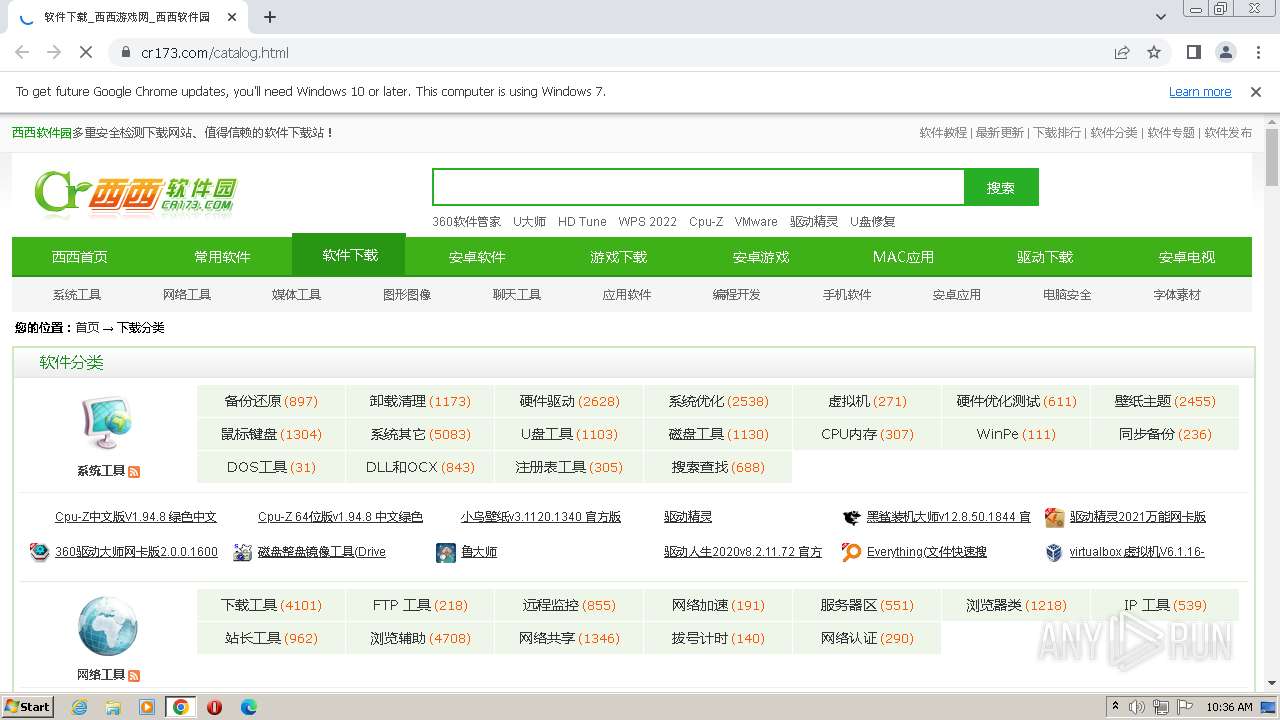
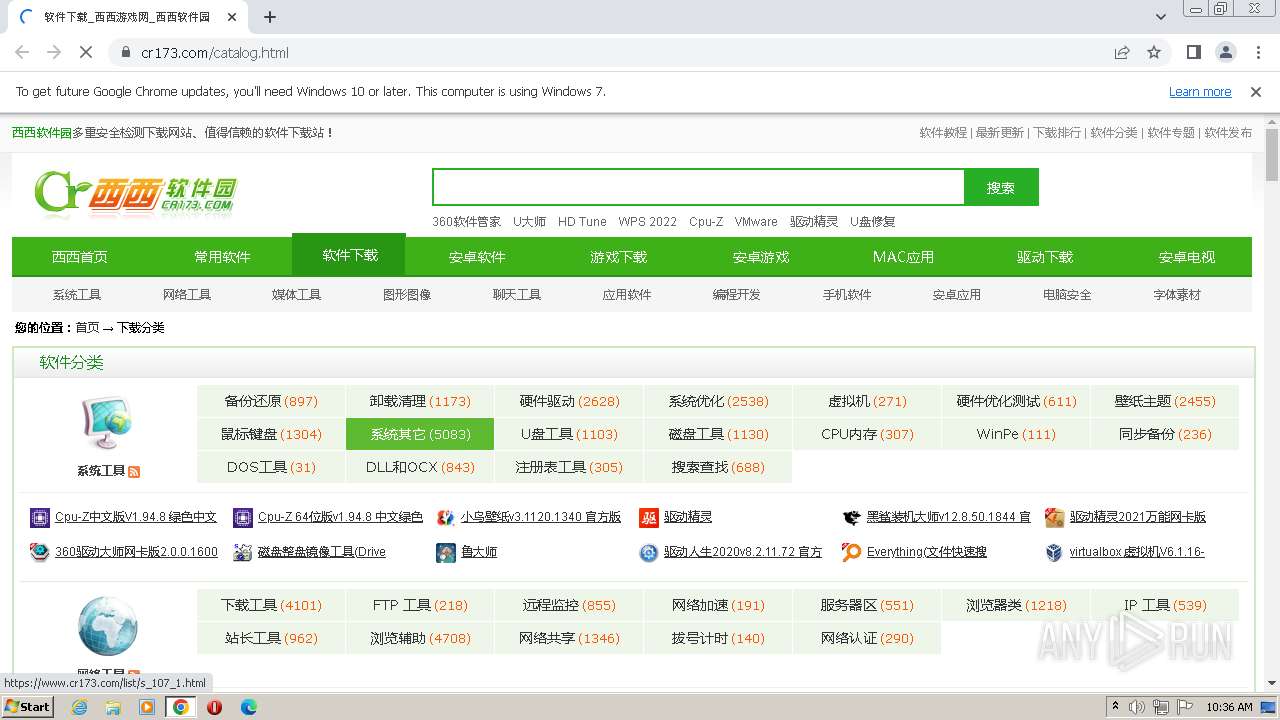
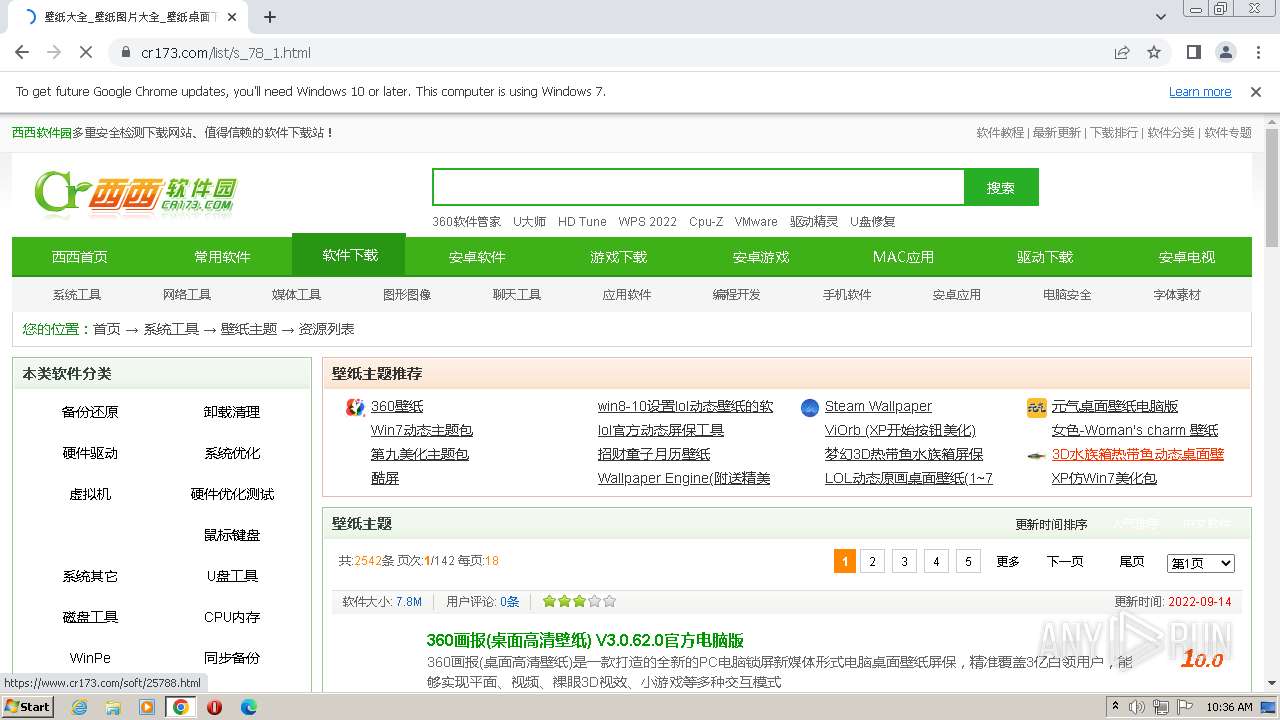
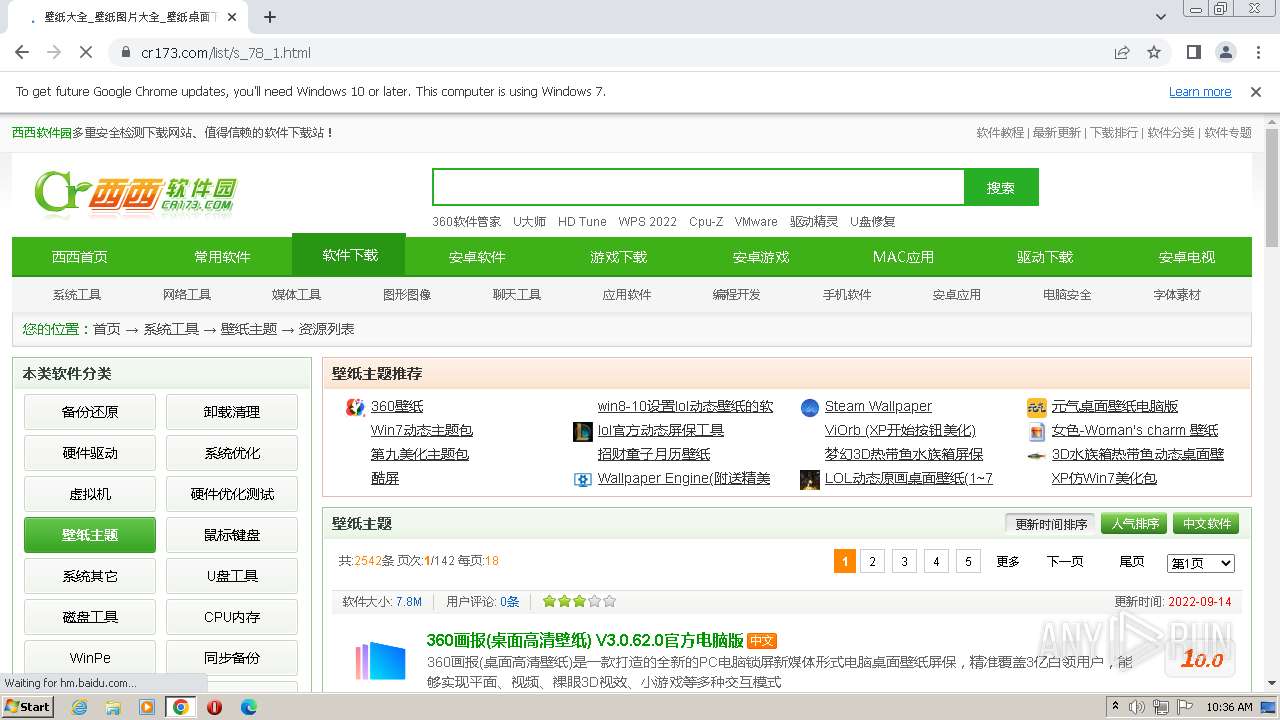
| URL: | https://www.cr173.com/catalog.html |
| Full analysis: | https://app.any.run/tasks/44eef3f9-dcbe-41dc-8dd5-27a10063fefb |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2023, 09:35:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BB525B2D1F20F1F817CA6CF7179D34C5 |
| SHA1: | 2CA2704F5277C41028C2D34DE9826F2DFF2BCE39 |
| SHA256: | EC1A35050D13773342F5D924F5603614877656C84FBECF2FCEF3BA41672EE8CE |
| SSDEEP: | 3:N8DSLqKIKTxC5Gn:2OLOM |
MALICIOUS
Application was dropped or rewritten from another process
- SearchEngine.exe (PID: 2236)
- SearchEngine.exe (PID: 1892)
- SearchEngine.exe (PID: 3912)
- SearchEngine.exe (PID: 2368)
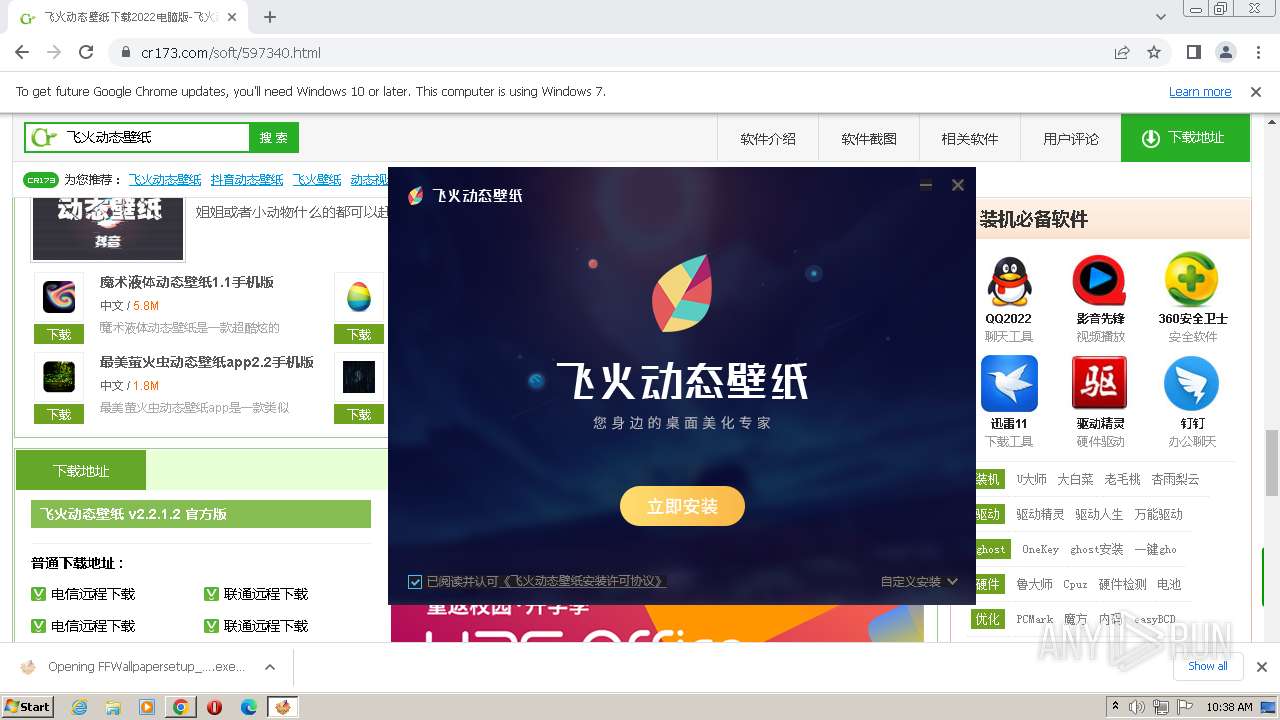
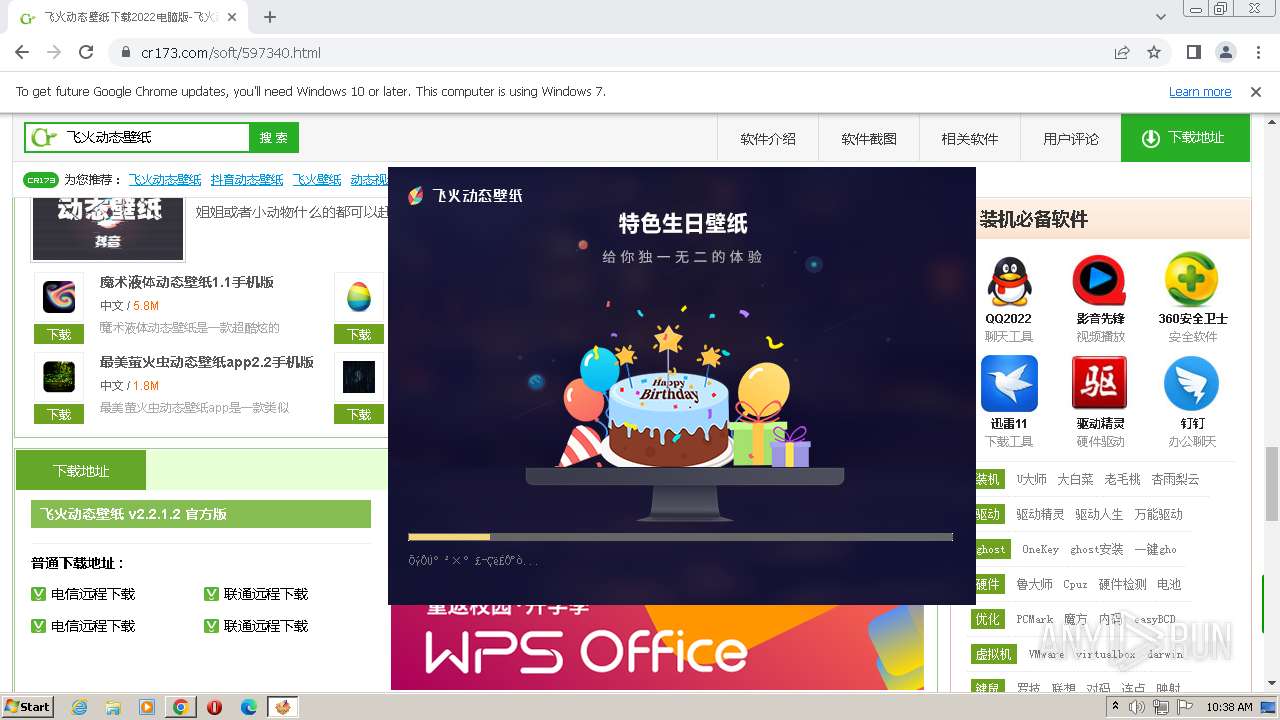
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
- FFWallpaper.exe (PID: 1692)
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 3244)
- ffloader.exe (PID: 2316)
- fhsearch.exe (PID: 912)
- ffauclt.exe (PID: 652)
- ffauclt.exe (PID: 3920)
Loads dropped or rewritten executable
- FFWallpaper.exe (PID: 1692)
- fhsearch.exe (PID: 912)
- ffauclt.exe (PID: 3920)
SUSPICIOUS
Reads the Internet Settings
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
- FFWallpaper.exe (PID: 1692)
- ffloader.exe (PID: 2316)
- ffauclt.exe (PID: 3920)
- ffauclt.exe (PID: 652)
The process creates files with name similar to system file names
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Executable content was dropped or overwritten
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Reads Microsoft Outlook installation path
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Reads Internet Explorer settings
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Executes as Windows Service
- SearchEngine.exe (PID: 1892)
Loads DLL from Mozilla Firefox
- default-browser-agent.exe (PID: 2972)
The process executes via Task Scheduler
- default-browser-agent.exe (PID: 2972)
Reads security settings of Internet Explorer
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Reads settings of System Certificates
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Checks Windows Trust Settings
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Adds/modifies Windows certificates
- chrome.exe (PID: 1532)
Process requests binary or script from the Internet
- ffauclt.exe (PID: 652)
INFO
The process uses the downloaded file
- chrome.exe (PID: 320)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 1532)
- chrome.exe (PID: 1016)
Application launched itself
- chrome.exe (PID: 1532)
Checks supported languages
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
- SearchEngine.exe (PID: 3912)
- SearchEngine.exe (PID: 2236)
- SearchEngine.exe (PID: 1892)
- default-browser-agent.exe (PID: 2972)
- SearchEngine.exe (PID: 2368)
- ffloader.exe (PID: 2316)
- FFWallpaper.exe (PID: 1692)
- fhsearch.exe (PID: 912)
- ffauclt.exe (PID: 3920)
- ffauclt.exe (PID: 652)
Executable content was dropped or overwritten
- chrome.exe (PID: 1532)
- chrome.exe (PID: 1760)
Reads the computer name
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
- SearchEngine.exe (PID: 3912)
- SearchEngine.exe (PID: 2236)
- SearchEngine.exe (PID: 1892)
- SearchEngine.exe (PID: 2368)
- FFWallpaper.exe (PID: 1692)
- ffloader.exe (PID: 2316)
- ffauclt.exe (PID: 3920)
- ffauclt.exe (PID: 652)
Checks proxy server information
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
- ffauclt.exe (PID: 3920)
- ffauclt.exe (PID: 652)
The process checks LSA protection
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
- ffloader.exe (PID: 2316)
- FFWallpaper.exe (PID: 1692)
- ffauclt.exe (PID: 3920)
- ffauclt.exe (PID: 652)
Create files in a temporary directory
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Reads the machine GUID from the registry
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
- ffauclt.exe (PID: 3920)
- ffauclt.exe (PID: 652)
Creates files or folders in the user directory
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
- FFWallpaper.exe (PID: 1692)
- SearchEngine.exe (PID: 2236)
- ffloader.exe (PID: 2316)
- ffauclt.exe (PID: 3920)
- ffauclt.exe (PID: 652)
Reads Environment values
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Creates files in the program directory
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Process checks are UAC notifies on
- ffloader.exe (PID: 2316)
Loads dropped or rewritten executable
- FFWallpapersetup_guanwang_2.2.1.2.exe (PID: 2328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
47
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3192 --field-trial-handle=1156,i,779568134362049450,6347461389188942676,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3244 --field-trial-handle=1156,i,779568134362049450,6347461389188942676,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 652 | "C:\Users\admin\AppData\Roaming\FFWallpaper\ffauclt.exe" -d -fs -fu -i ffwpconfig.ini | C:\Users\admin\AppData\Roaming\FFWallpaper\ffauclt.exe | ffloader.exe | ||||||||||||
User: admin Company: 合肥诺拉网络科技有限公司 Integrity Level: MEDIUM Description: 合肥诺拉网络自动更新程序 Exit code: 0 Version: 2.0.0.6 Modules
| |||||||||||||||
| 912 | "C:\Users\admin\AppData\Roaming\FFWallpaper\plugins\fhsearch\fhsearch.exe" -qt | C:\Users\admin\AppData\Roaming\FFWallpaper\plugins\fhsearch\fhsearch.exe | FFWallpaper.exe | ||||||||||||
User: admin Company: 合肥诺拉网络科技有限公司 Integrity Level: HIGH Description: fhsearch Exit code: 0 Version: 1.0.2.8260 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=3276 --field-trial-handle=1156,i,779568134362049450,6347461389188942676,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2032 --field-trial-handle=1156,i,779568134362049450,6347461389188942676,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2088 --field-trial-handle=1156,i,779568134362049450,6347461389188942676,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3508 --field-trial-handle=1156,i,779568134362049450,6347461389188942676,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3608 --field-trial-handle=1156,i,779568134362049450,6347461389188942676,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3804 --field-trial-handle=1156,i,779568134362049450,6347461389188942676,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
17 047
Read events
16 803
Write events
244
Delete events
0
Modification events
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
83
Suspicious files
401
Text files
664
Unknown types
151
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF109ffb.TMP | — | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7954e56e-46b6-4acc-ba47-5c44ca37a2e6.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:7C1C23F006788D107F8A01B852CC6701 | SHA256:9FA4E627077EDCBEC8AAA1ED2DD5538E630790893F88F02F1E9CC863E6A27848 | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_model_metadata_store\LOG.old~RF10c073.TMP | — | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_model_metadata_store\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_hint_cache_store\LOG.old~RF10c073.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
183
TCP/UDP connections
241
DNS requests
49
Threats
140
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acfrxel7rbjfr2oo2pzgxizks4eq_403/lmelglejhemejginpboagddgdfbepgmp_403_all_ZZ_acs5nbh2ktbkojmgdvvippsdbkka.crx3 | US | — | — | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acu5uq6ixeyjjhlczndqjljh4kna_117.0.5912.0/jamhcnnkihinmdlkakkaopbjbbcngflc_117.0.5912.0_all_acatj65nftfngtrqhdl3zkoqz42a.crx3 | US | binary | 1010 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acfrxel7rbjfr2oo2pzgxizks4eq_403/lmelglejhemejginpboagddgdfbepgmp_403_all_ZZ_acs5nbh2ktbkojmgdvvippsdbkka.crx3 | US | binary | 6.29 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 5.56 Kb | whitelisted |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 1.01 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 44.6 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 1.42 Mb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 90.3 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 22.1 Kb | whitelisted |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acu5uq6ixeyjjhlczndqjljh4kna_117.0.5912.0/jamhcnnkihinmdlkakkaopbjbbcngflc_117.0.5912.0_all_acatj65nftfngtrqhdl3zkoqz42a.crx3 | US | binary | 5.46 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1084 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1532 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3352 | chrome.exe | 142.250.181.237:443 | accounts.google.com | GOOGLE | US | suspicious |
2720 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3352 | chrome.exe | 222.73.33.249:443 | www.cr173.com | China Telecom Group | CN | suspicious |
3352 | chrome.exe | 172.217.18.4:443 | www.google.com | — | — | whitelisted |
1532 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3352 | chrome.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cr173.com |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
p.e5n.com |
| malicious |
safebrowsing.googleapis.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
hm.baidu.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3920 | ffauclt.exe | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
3920 | ffauclt.exe | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
652 | ffauclt.exe | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
— | — | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
652 | ffauclt.exe | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
652 | ffauclt.exe | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
652 | ffauclt.exe | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
652 | ffauclt.exe | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
652 | ffauclt.exe | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
652 | ffauclt.exe | A Network Trojan was detected | ET HUNTING Suspicious User-Agent Containing .exe |
Process | Message |
|---|---|
FFWallpaper.exe | |
FFWallpaper.exe | 2023/07/27 10:39:29.362 1692 1880 *** >>>>>>>>>>>> SESSION START: DBG_LEVEL:30 >>>>>>>>>>>>
|
ffloader.exe | |
ffloader.exe | 2023/07/27 10:39:29.440 2316 === >>>>>>>>>>>> SESSION START: DBG_LEVEL:31 >>>>>>>>>>>>
|
ffloader.exe | 2023/07/27 10:39:29.456 2316 *** RetryTimer: 0
|
ffloader.exe | 2023/07/27 10:39:29.456 2316 *** StartProcess: C:\Users\admin\AppData\Roaming\FFWallpaper\ffauclt.exe -f -i ffwpconfig.ini
|
FFWallpaper.exe | 2023/07/27 10:39:29.487 1692 1880 === <<<<<<<<<<<< SESSION FINISH: DBG_LEVEL:30 <<<<<<<<<<<<
|
fhsearch.exe | ??dll |
fhsearch.exe | ??dll |
ffauclt.exe | |