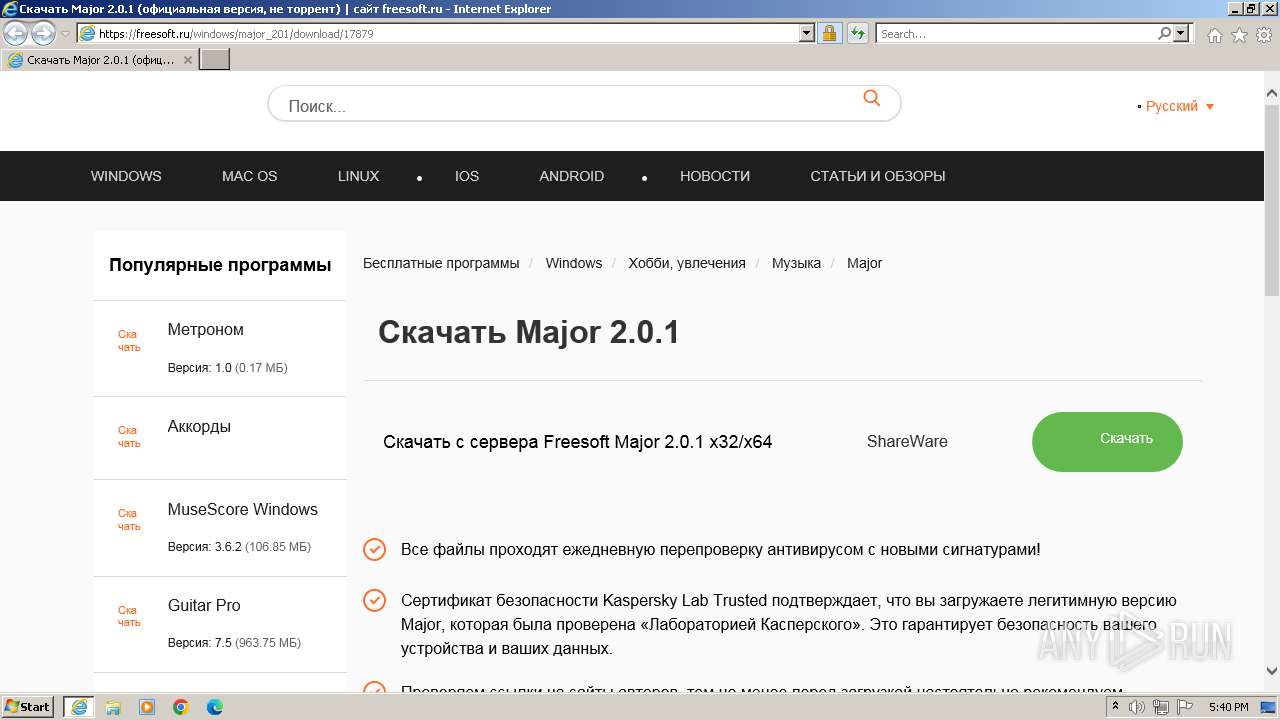
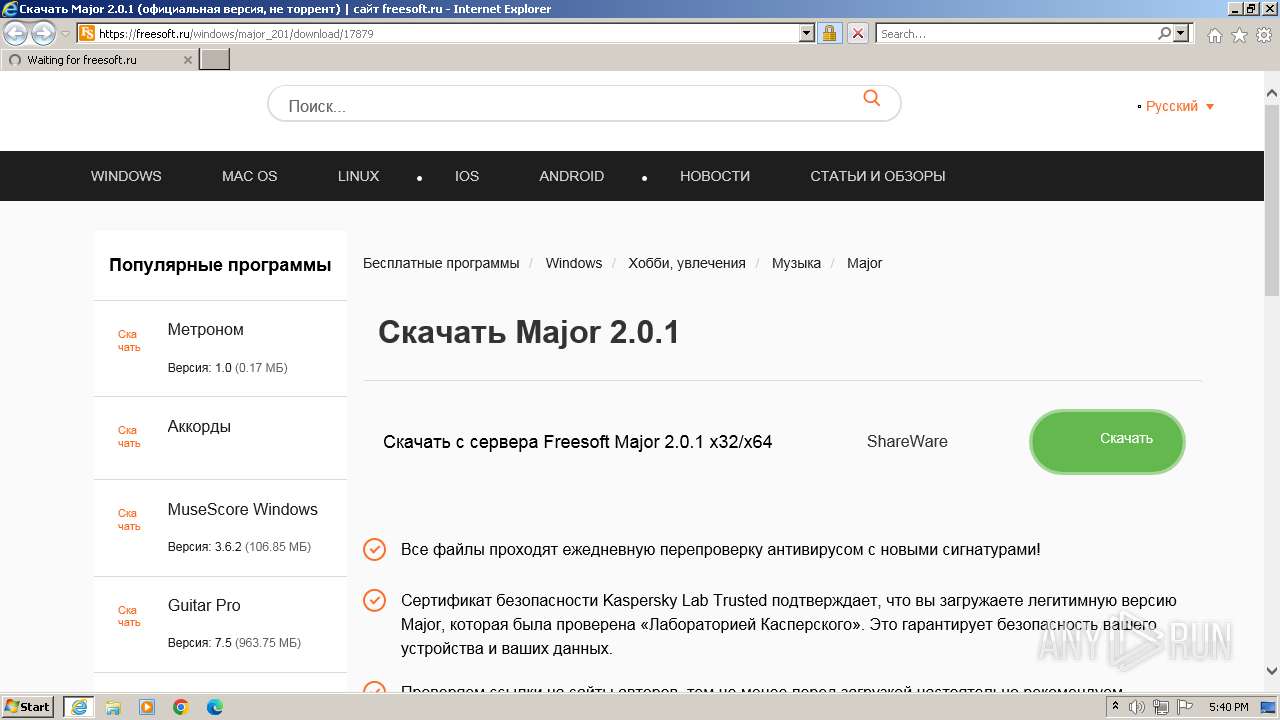
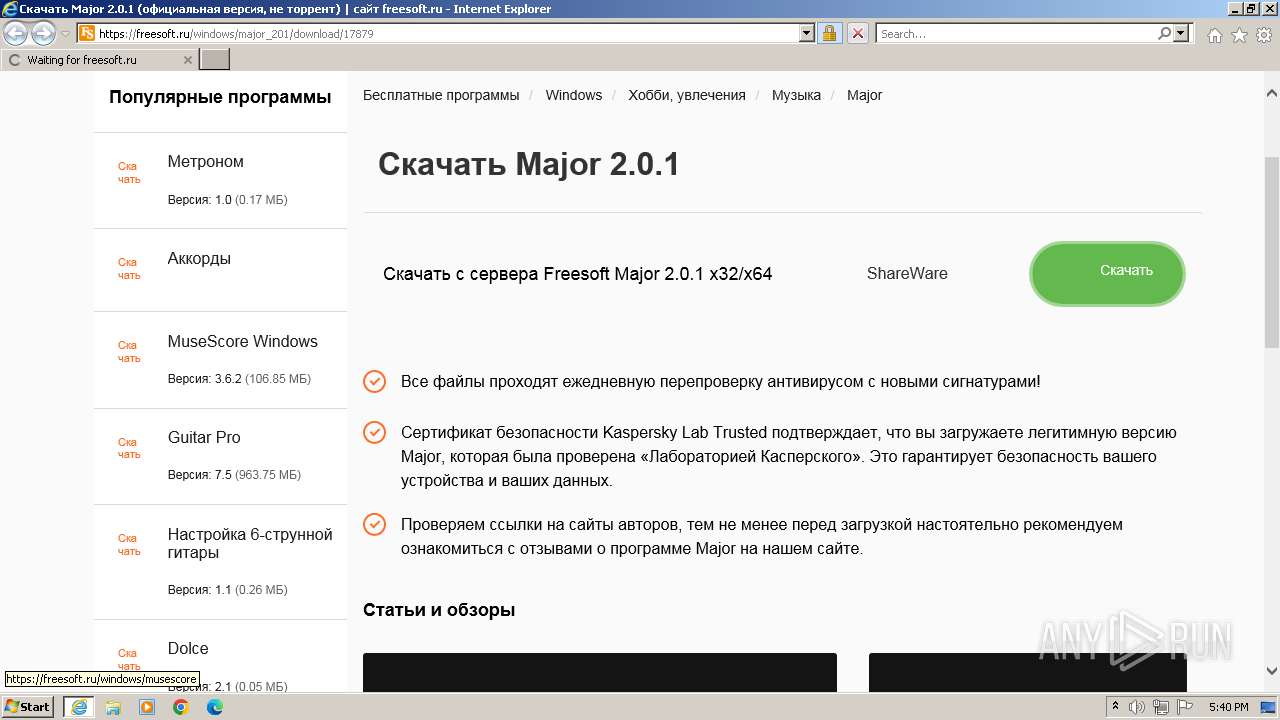
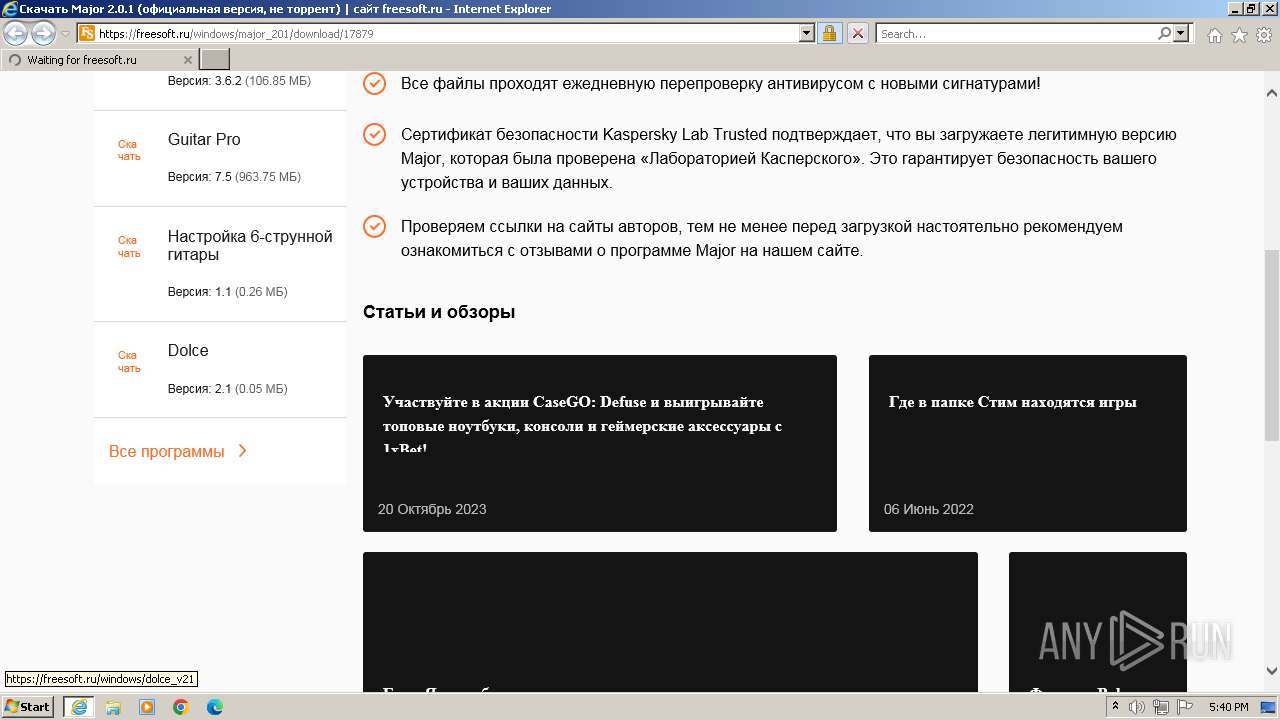
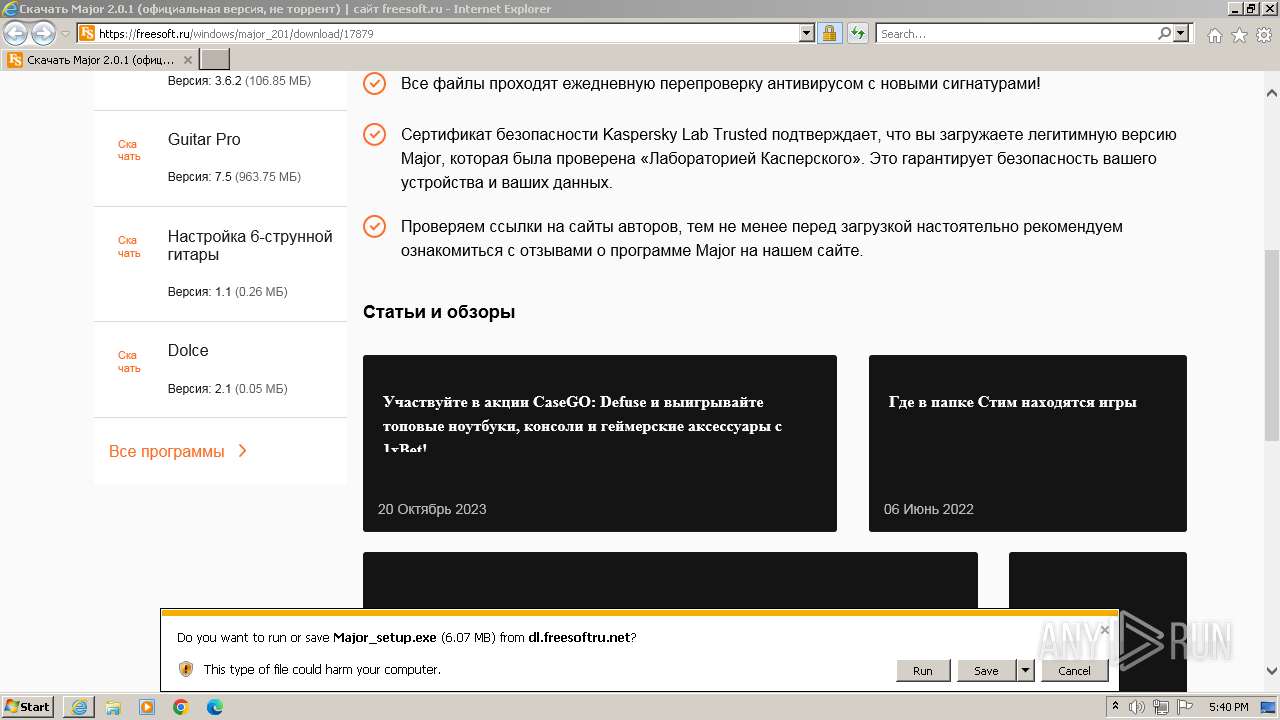
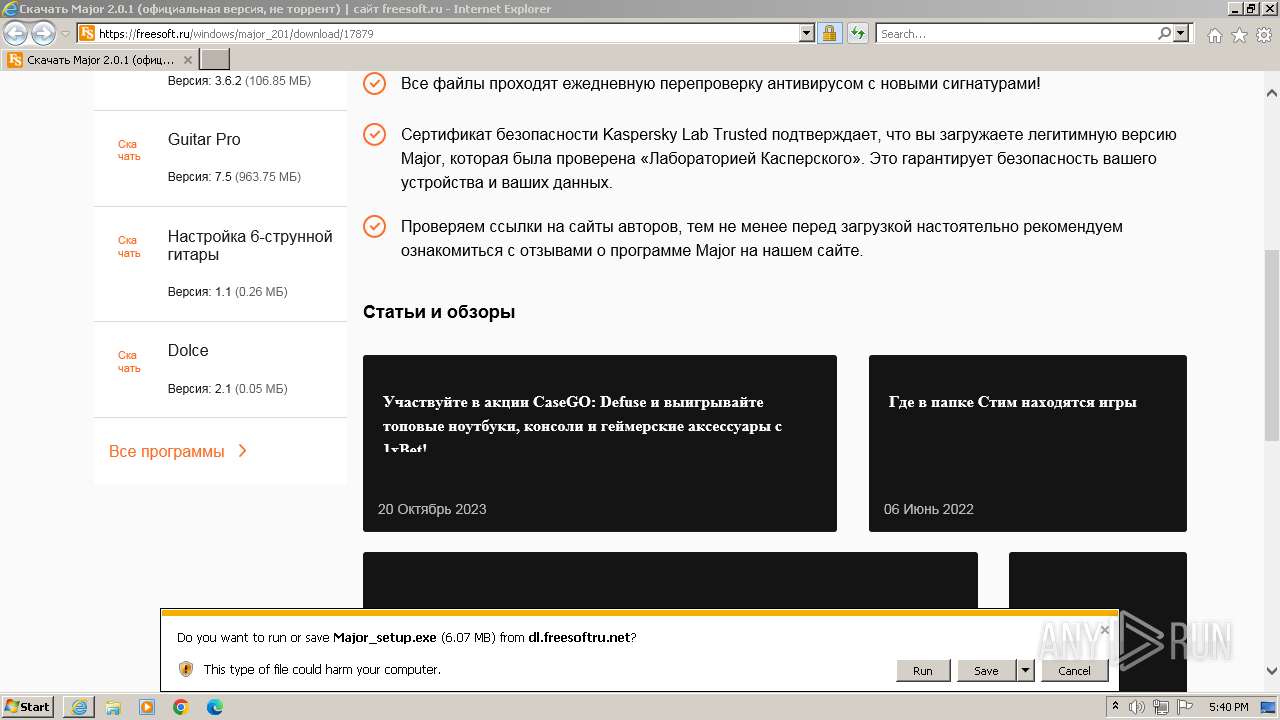
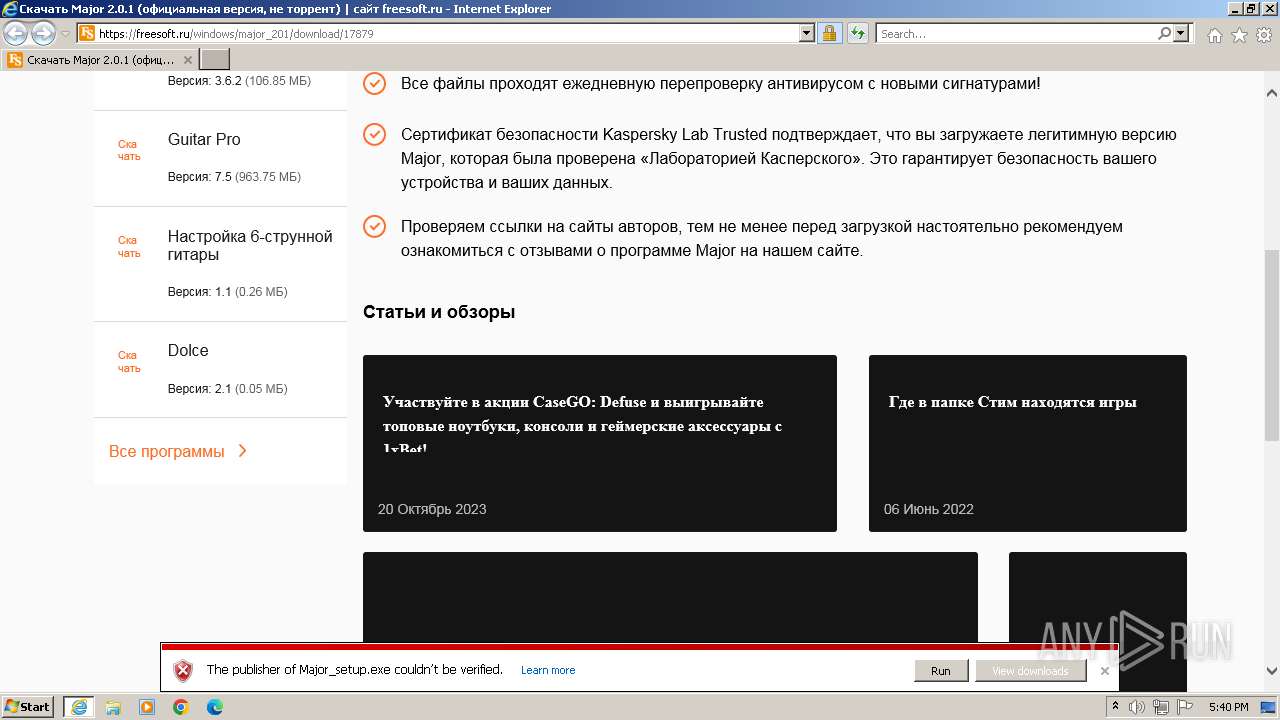
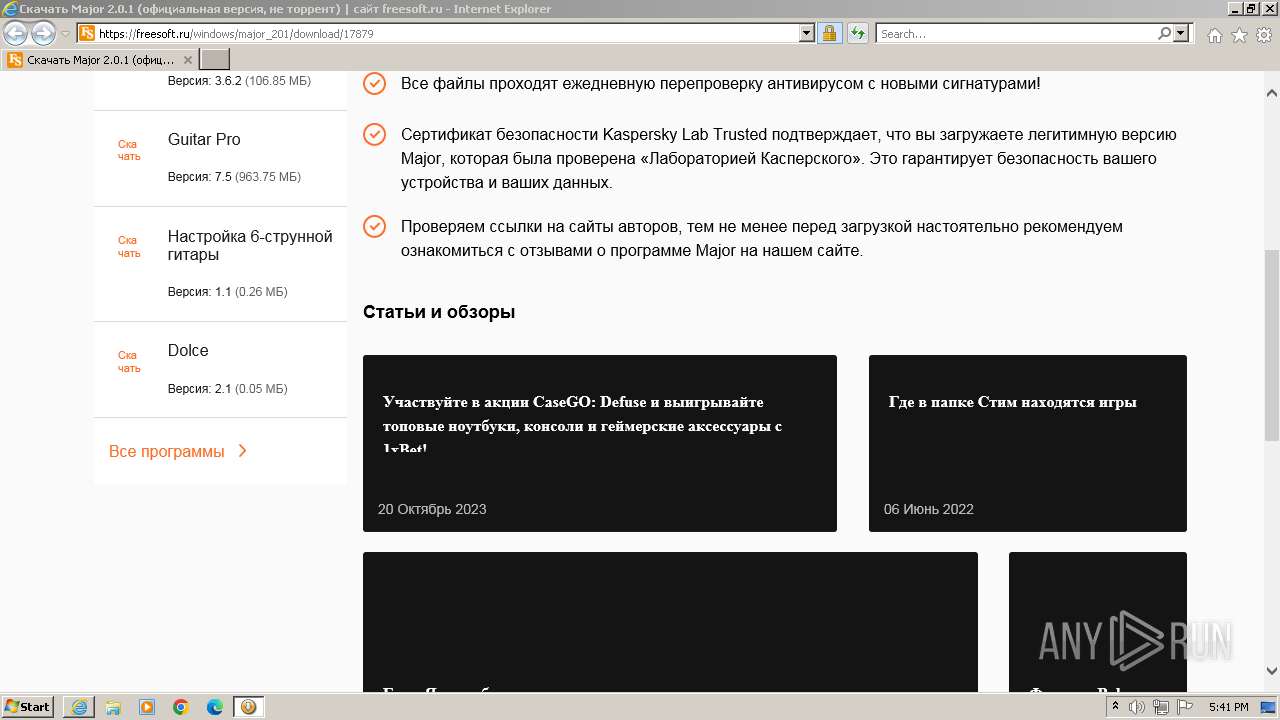
| URL: | https://freesoft.ru/windows/major_201/download/17879 |
| Full analysis: | https://app.any.run/tasks/fe4508f2-53d6-44d4-a675-3381c7bad772 |
| Verdict: | Malicious activity |
| Analysis date: | October 26, 2023, 16:39:54 |
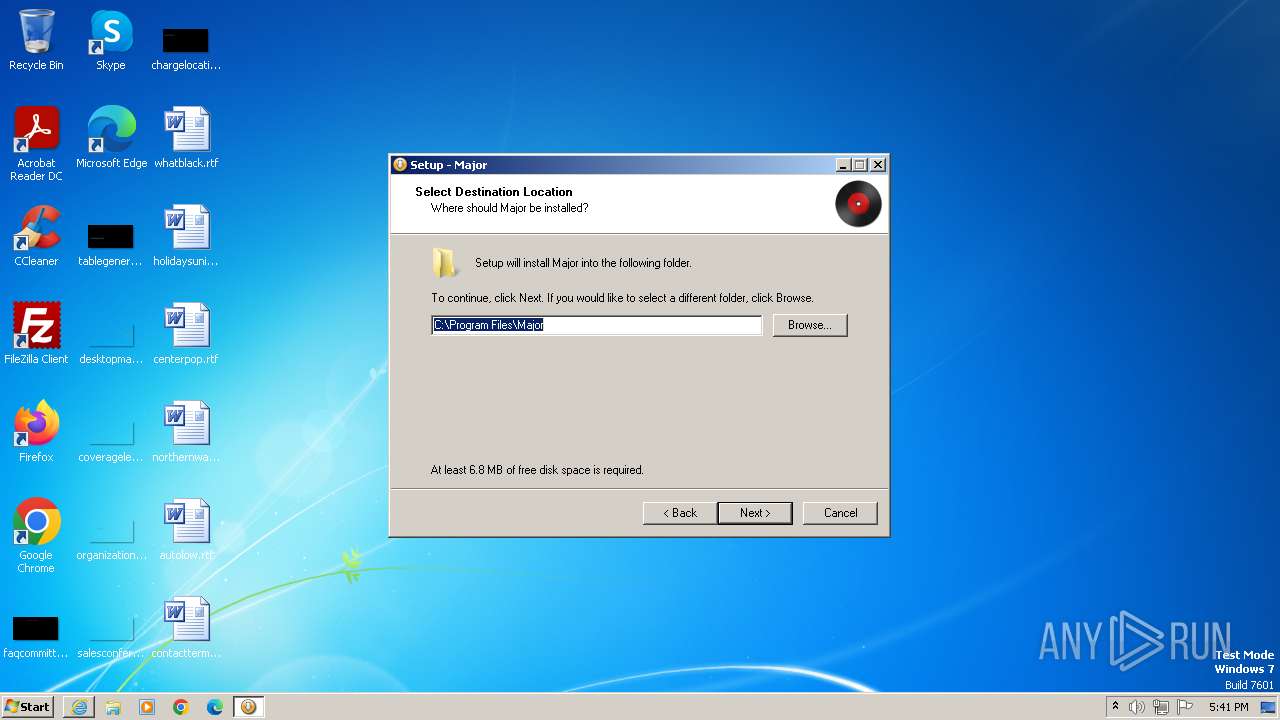
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 480B756D66E9EE773752205EB6AADCB2E318F738 |
| SHA256: | EC15347B4169415C44A6331EF88502C6CB0F4727F5BBDC1A1875A12F40D9617B |
| SSDEEP: | 3:N8iKNrSKBIwFUBLUuv:2iKsz6uv |
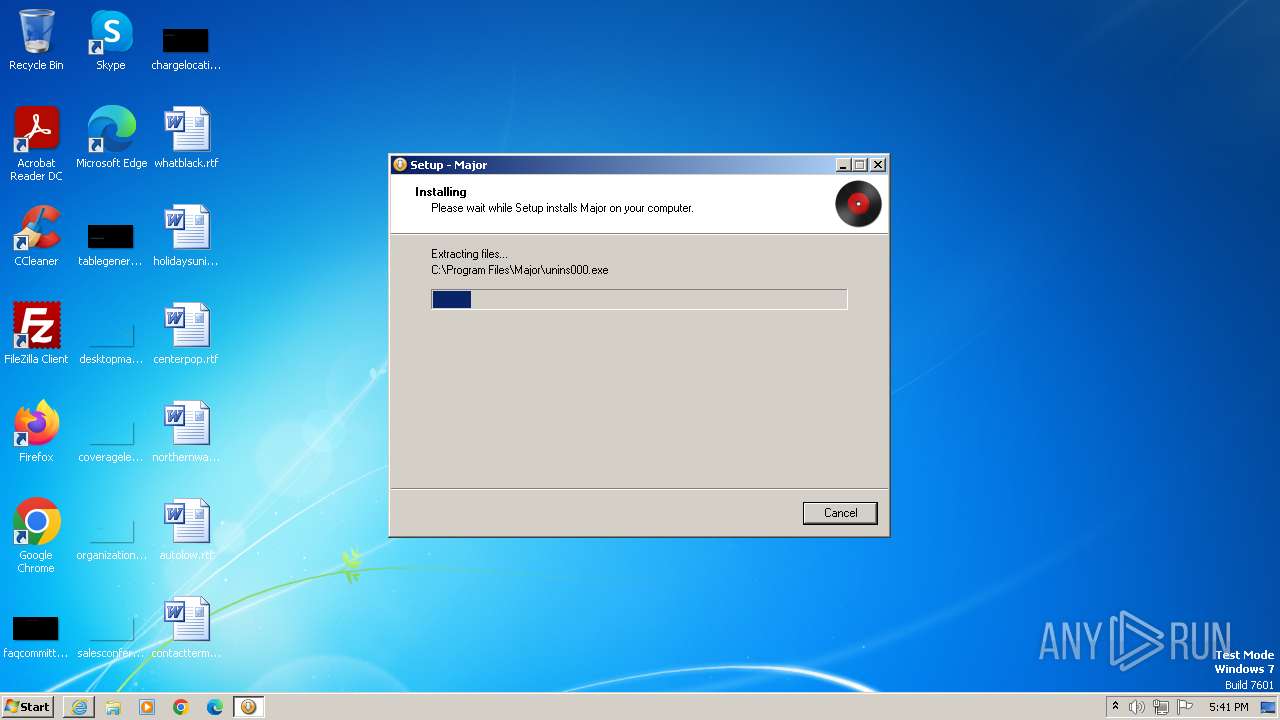
MALICIOUS
Application was dropped or rewritten from another process
- Major_setup.exe (PID: 3860)
- Major_setup.exe (PID: 4076)
- Major.exe (PID: 3000)
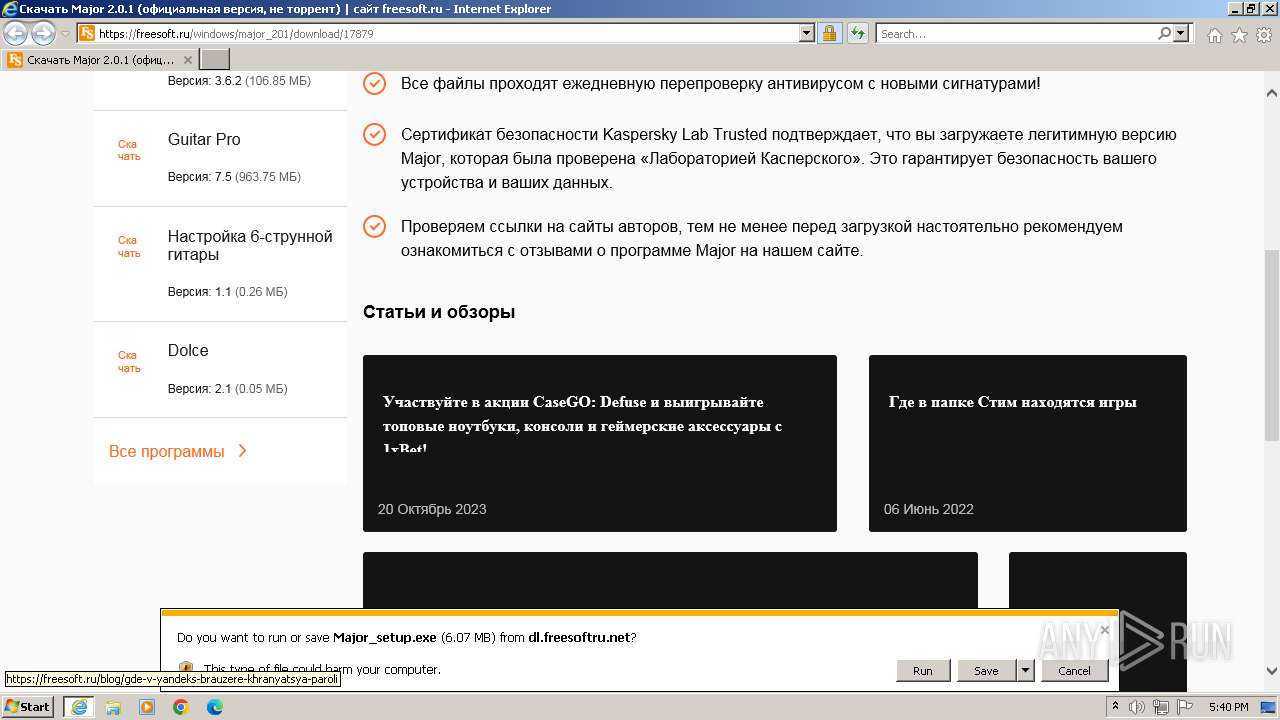
Drops the executable file immediately after the start
- Major_setup.exe (PID: 3860)
- is-O72GU.tmp (PID: 2448)
Loads dropped or rewritten executable
- is-O72GU.tmp (PID: 2448)
- Major.exe (PID: 3000)
SUSPICIOUS
Reads the Windows owner or organization settings
- is-O72GU.tmp (PID: 2448)
Process drops legitimate windows executable
- is-O72GU.tmp (PID: 2448)
INFO
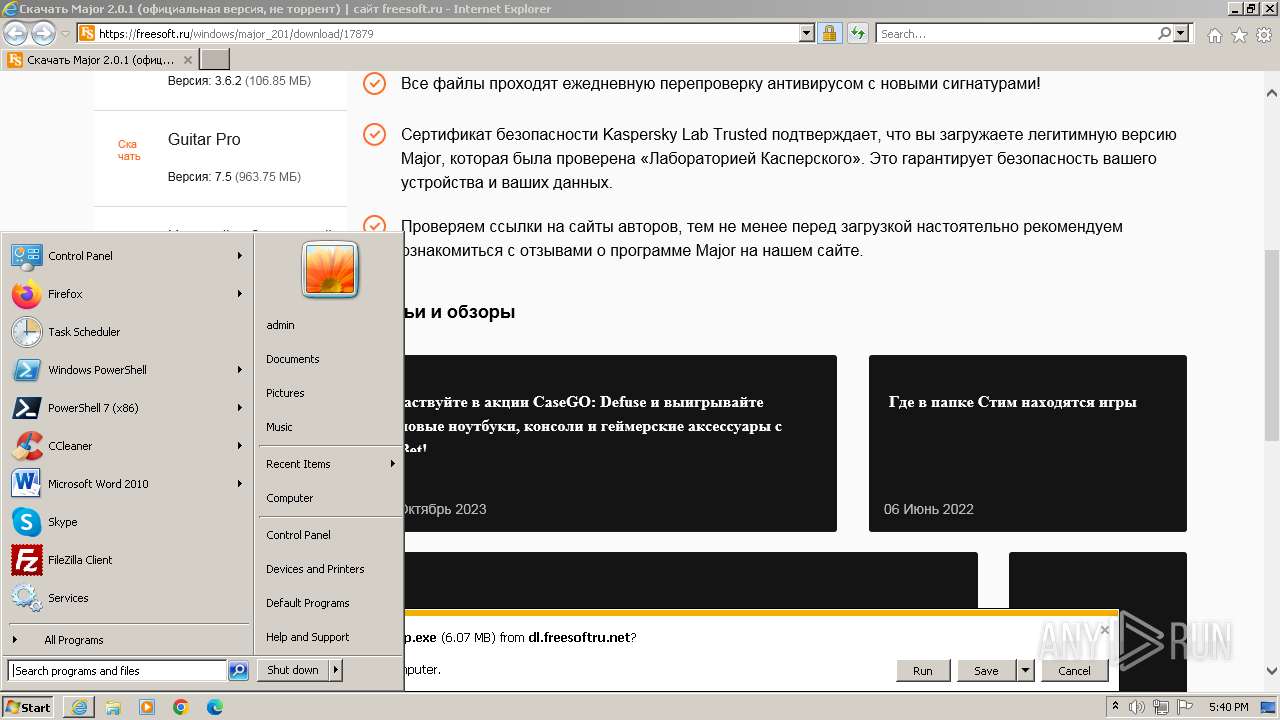
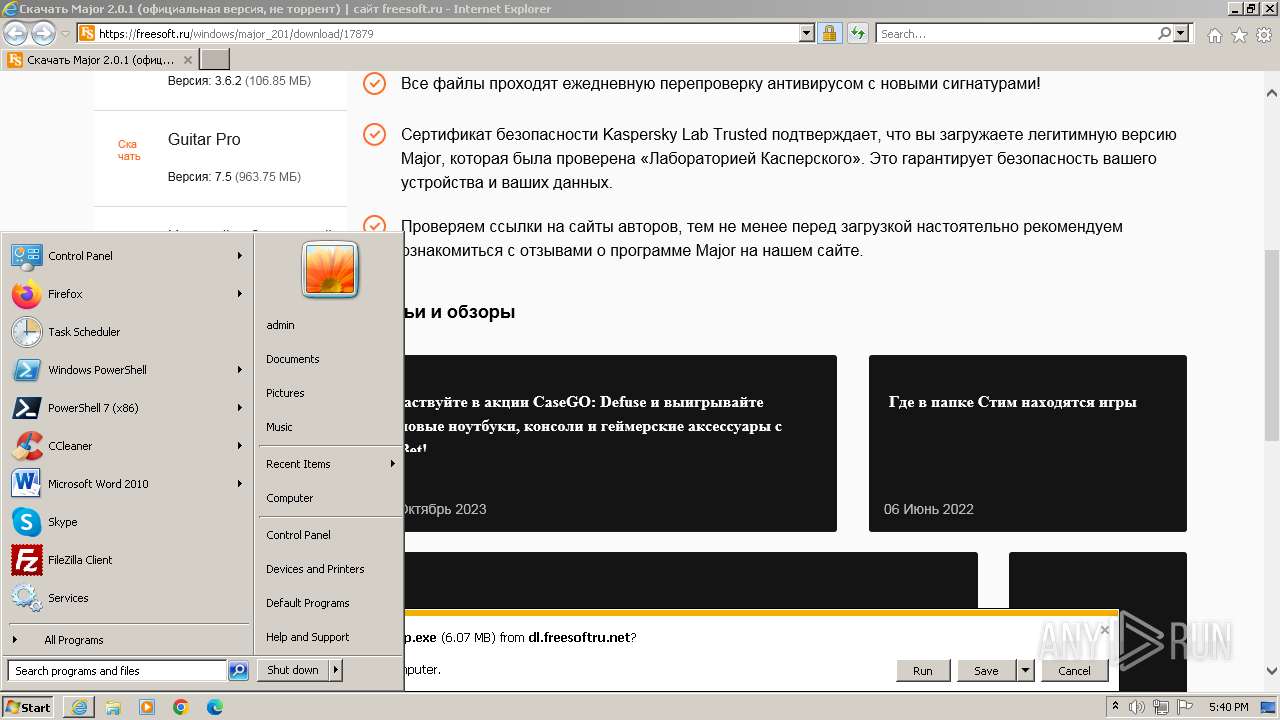
Application launched itself
- iexplore.exe (PID: 3580)
Checks supported languages
- Major_setup.exe (PID: 3860)
- is-O72GU.tmp (PID: 2448)
- Major.exe (PID: 3000)
Drops the executable file immediately after the start
- iexplore.exe (PID: 3404)
- iexplore.exe (PID: 3580)
Create files in a temporary directory
- is-O72GU.tmp (PID: 2448)
- Major_setup.exe (PID: 3860)
- Major.exe (PID: 3000)
The process uses the downloaded file
- iexplore.exe (PID: 3580)
Reads the computer name
- is-O72GU.tmp (PID: 2448)
- Major.exe (PID: 3000)
Application was dropped or rewritten from another process
- is-O72GU.tmp (PID: 2448)
Creates files in the program directory
- is-O72GU.tmp (PID: 2448)
- Major.exe (PID: 3000)
Reads the machine GUID from the registry
- Major.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
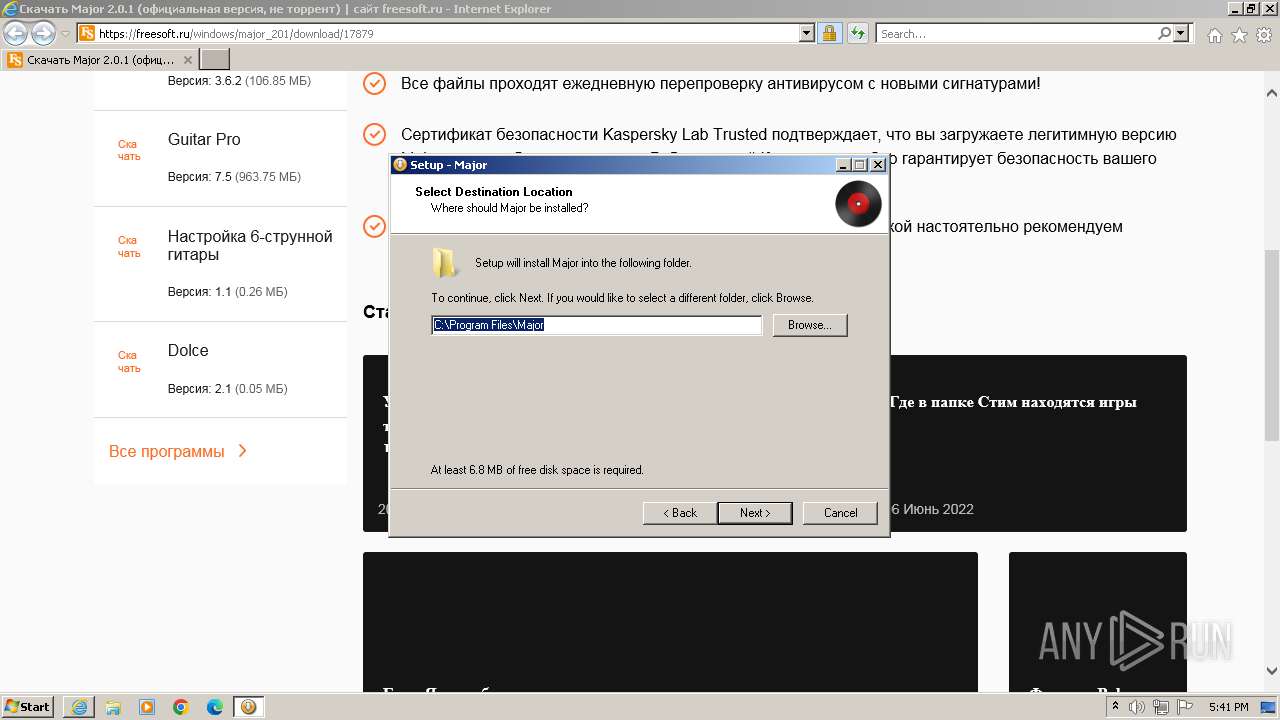
| 2448 | "C:\Users\admin\AppData\Local\Temp\is-OPR0R.tmp\is-O72GU.tmp" /SL4 $A01D4 "C:\Users\admin\Downloads\Major_setup.exe" 6130902 72192 | C:\Users\admin\AppData\Local\Temp\is-OPR0R.tmp\is-O72GU.tmp | — | Major_setup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.34.0.0 Modules
| |||||||||||||||
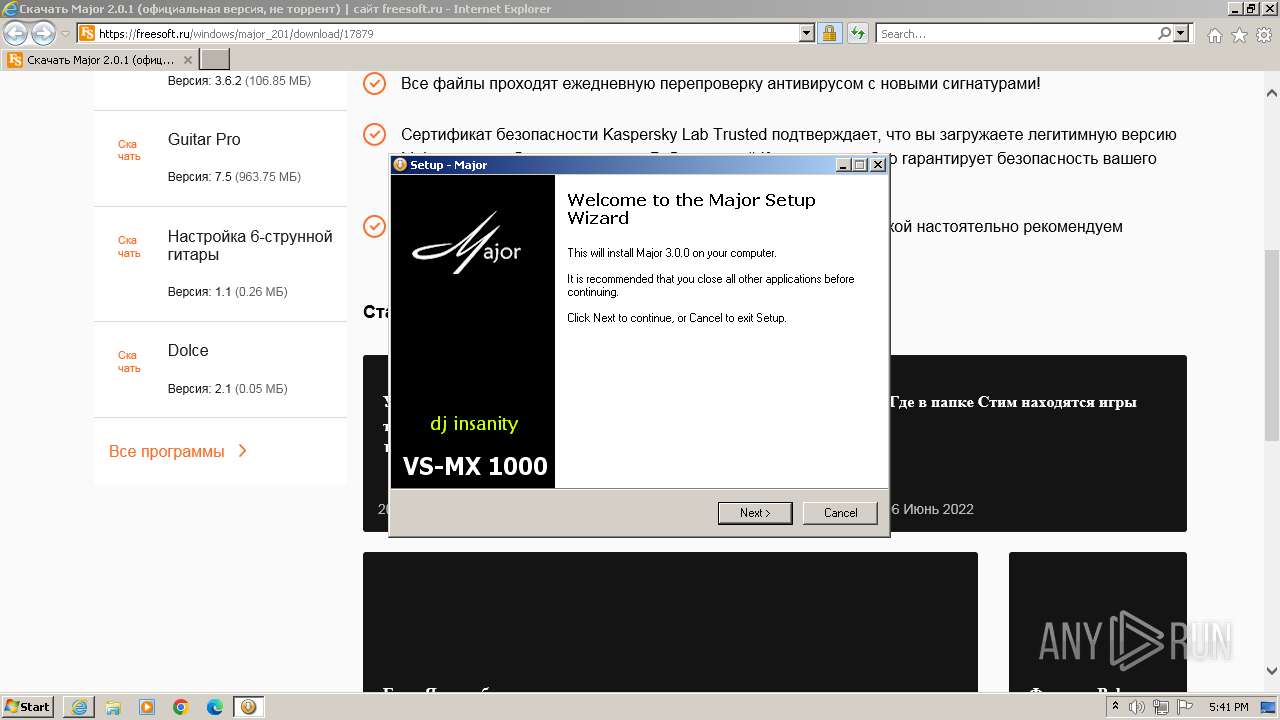
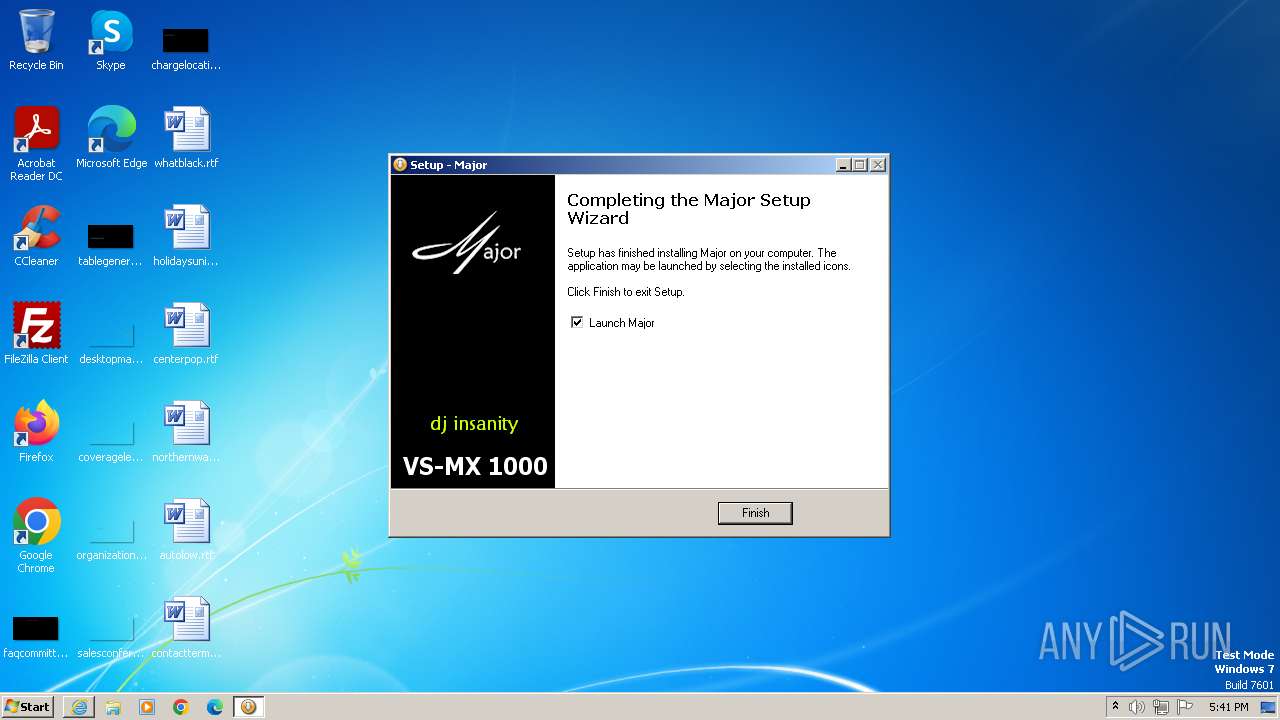
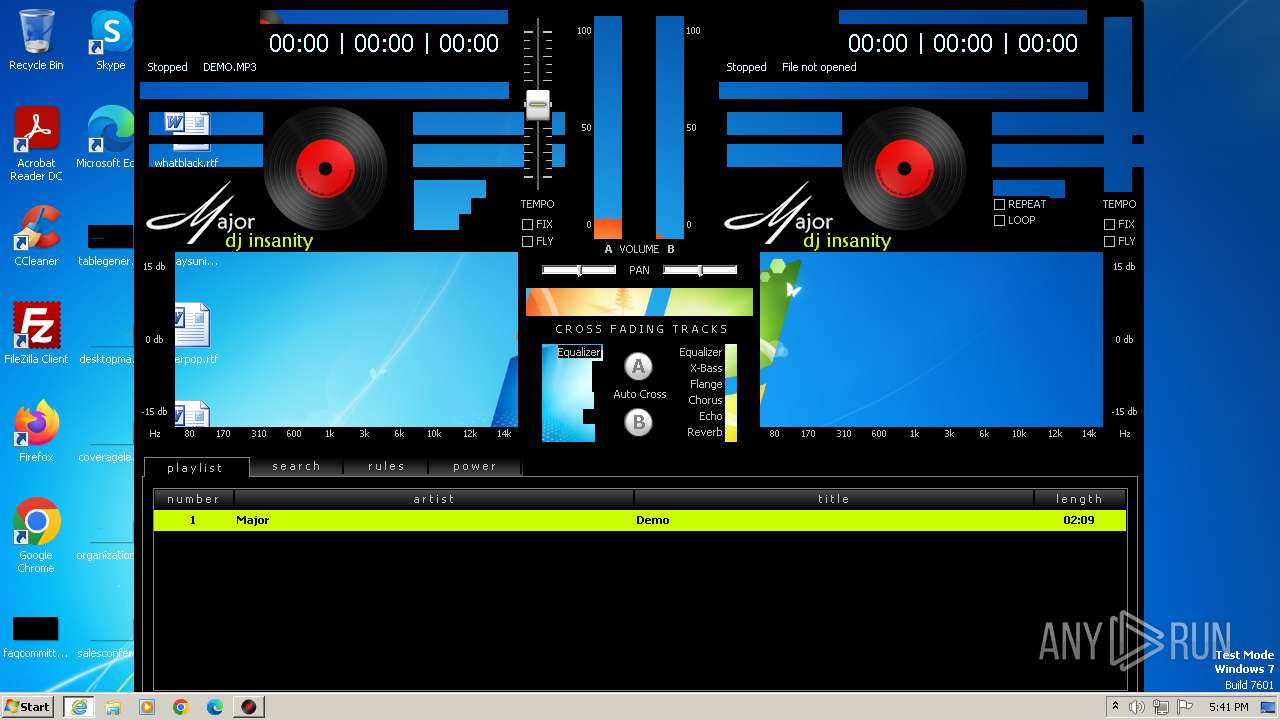
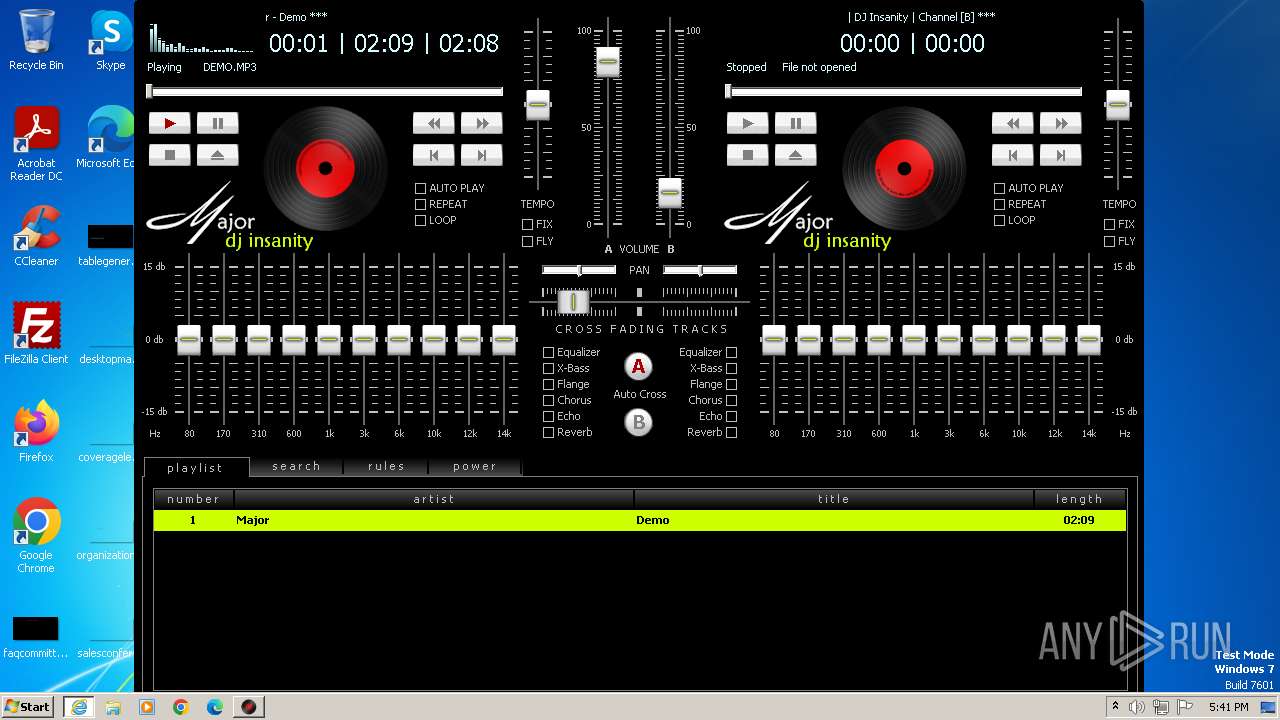
| 3000 | "C:\Program Files\Major\Major.exe" | C:\Program Files\Major\Major.exe | — | is-O72GU.tmp | |||||||||||
User: admin Company: PROSELF Integrity Level: HIGH Description: DJ Insanity Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 3404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3580 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3580 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://freesoft.ru/windows/major_201/download/17879" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3860 | "C:\Users\admin\Downloads\Major_setup.exe" | C:\Users\admin\Downloads\Major_setup.exe | iexplore.exe | ||||||||||||
User: admin Company: PROSELF Integrity Level: HIGH Description: Major Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 4076 | "C:\Users\admin\Downloads\Major_setup.exe" | C:\Users\admin\Downloads\Major_setup.exe | — | iexplore.exe | |||||||||||
User: admin Company: PROSELF Integrity Level: MEDIUM Description: Major Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
Total events
19 477
Read events
19 399
Write events
74
Delete events
4
Modification events
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
38
Suspicious files
55
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarBCA8.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:DEC6BBE308EB44937F77160A25EE32DB | SHA256:68A71DE28F488586C2B169F4652347E0A1FD632D48A6D6725393607BFA18BC7E | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabBCA7.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\waiting-page[1].css | text | |
MD5:C065E84864A1A8BA22A5788EC3A28E82 | SHA256:C875F140D9278C780C7034951BEA1DE4297E16CD95B18F445DDC97185C8D87C3 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:D3AF216FDD9B2BFCC0C6C46DC2C7B0C8 | SHA256:DD3612F4E2E3C3D8E67F9A2DC78E63A5B60D30C8F984FC94EBB7E5F7A2F8DE30 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:07613A5EC39B6D58555F416B3FBF5356 | SHA256:107BAEAF6D6AA78E2D39E95FAE13265D7EC92AF8947BD6ADDF1AF82D21D0C4B3 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabBCD7.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:D33114A48AB07830BEBC1443BD16908C | SHA256:BD744AE0152174A32936831FEF2BBBA81A26BBF53207A242BFA78A589C444748 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
39
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3580 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
3580 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
3404 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ab6c62e3d2bbc5b0 | unknown | compressed | 61.6 Kb | unknown |
3404 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?060020e49c501eb3 | unknown | compressed | 4.66 Kb | unknown |
3404 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3404 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7147a541e8aecbd1 | unknown | compressed | 61.6 Kb | unknown |
3404 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
3404 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
3404 | iexplore.exe | GET | 200 | 172.217.17.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3404 | iexplore.exe | GET | 200 | 172.217.17.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3404 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3404 | iexplore.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3404 | iexplore.exe | 142.251.141.40:443 | www.googletagmanager.com | GOOGLE | US | unknown |
3404 | iexplore.exe | 104.18.214.59:443 | cdn.onesignal.com | CLOUDFLARENET | — | unknown |
3404 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3404 | iexplore.exe | 88.212.201.198:443 | counter.yadro.ru | United Network LLC | RU | unknown |
3404 | iexplore.exe | 172.217.17.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3404 | iexplore.exe | 146.75.122.133:80 | ocsp.globalsign.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
mc.webvisor.org |
| whitelisted |
newrrb.bid |
| whitelisted |
counter.yandro.ru |
| unknown |
mc.yandex.ru |
| whitelisted |