| File name: | ebfc5467b571656fa637e3ba09cbbbeb85d5539467f13a5575cb3aa76720f7bc |
| Full analysis: | https://app.any.run/tasks/4124f60e-1a07-43de-a823-7ec7d5ec0169 |
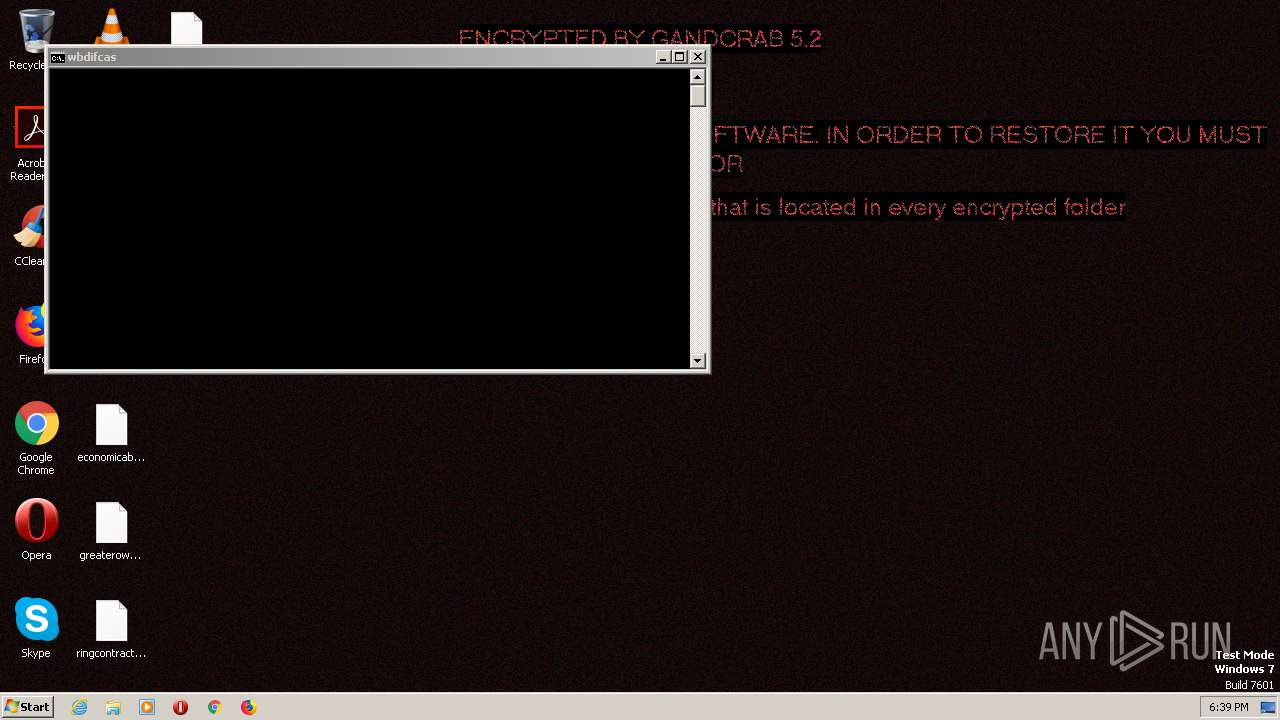
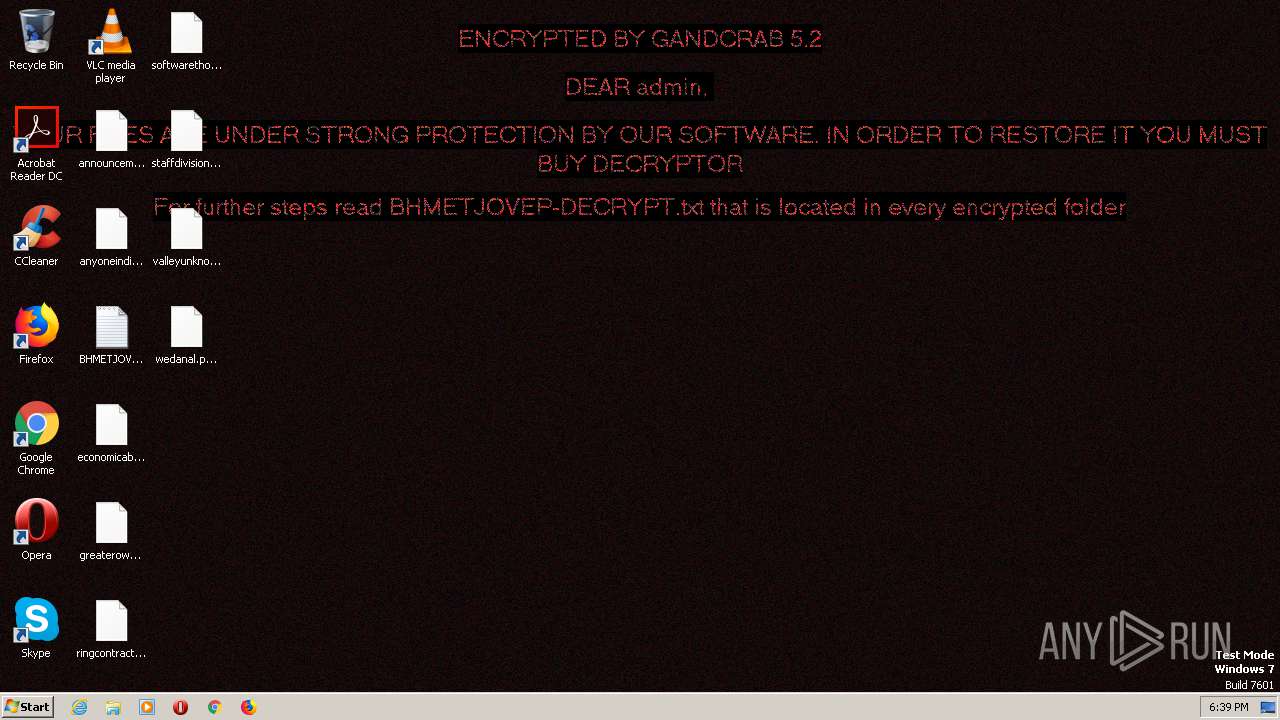
| Verdict: | Malicious activity |
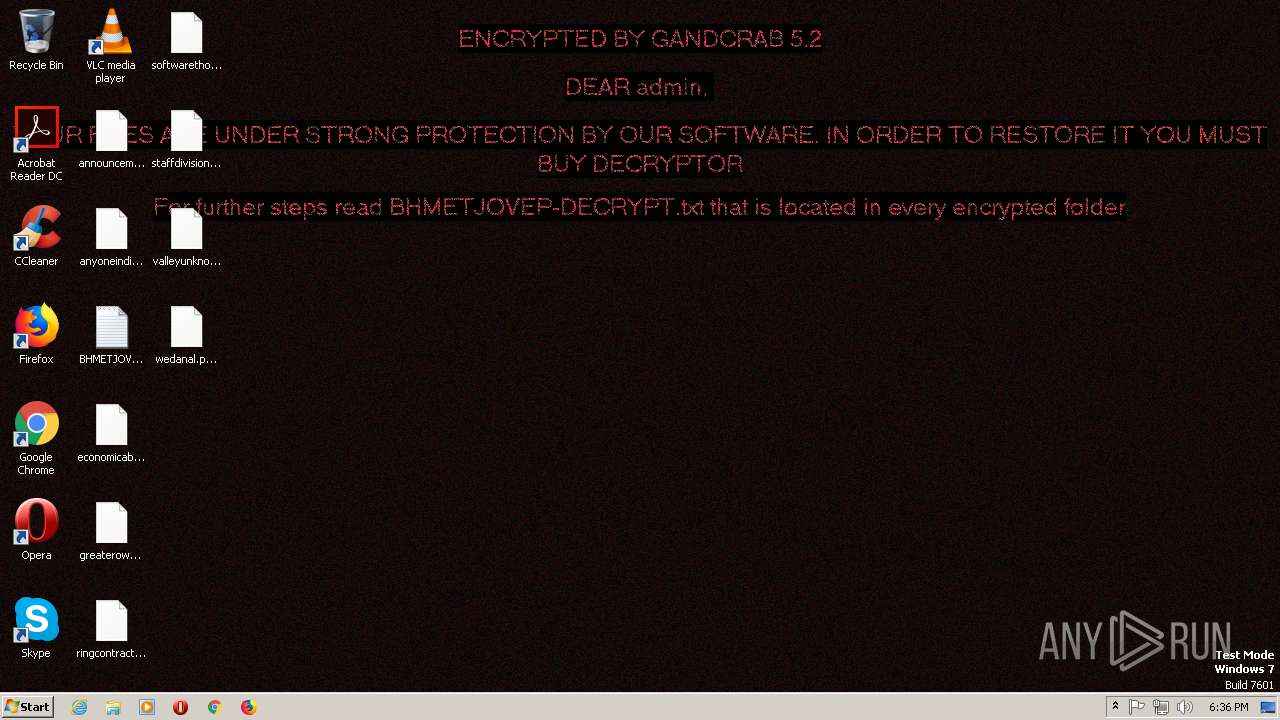
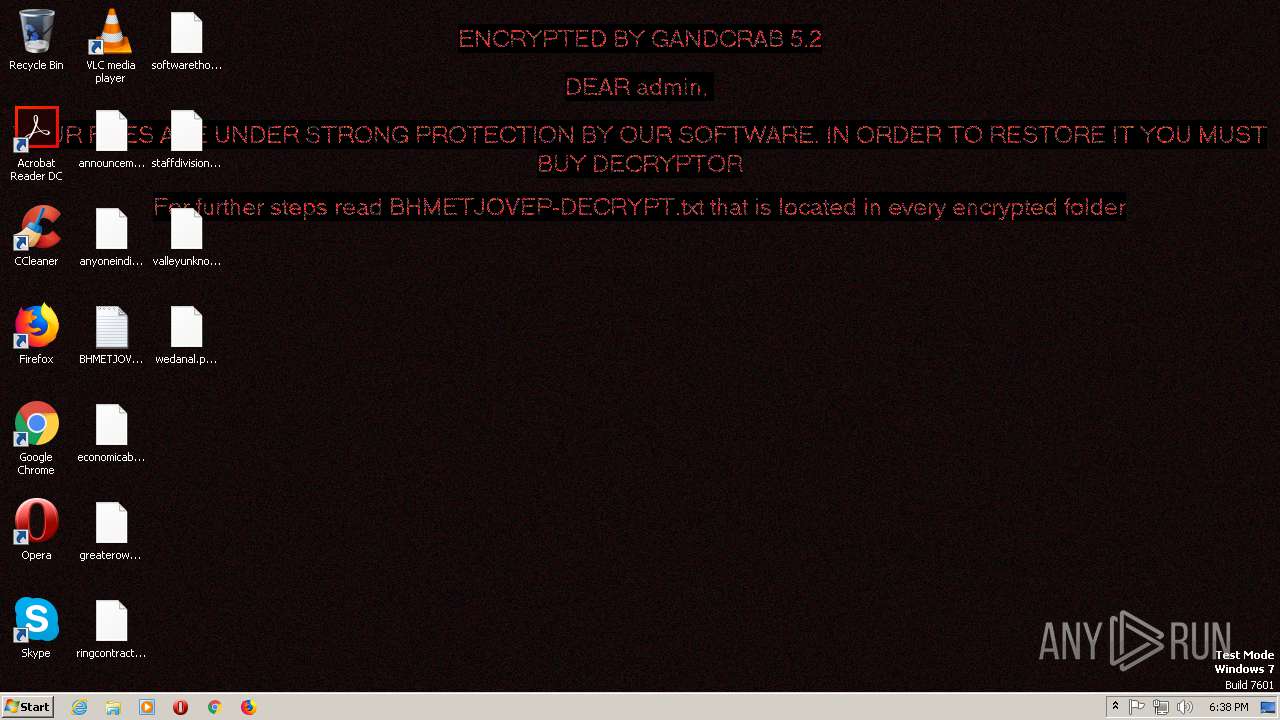
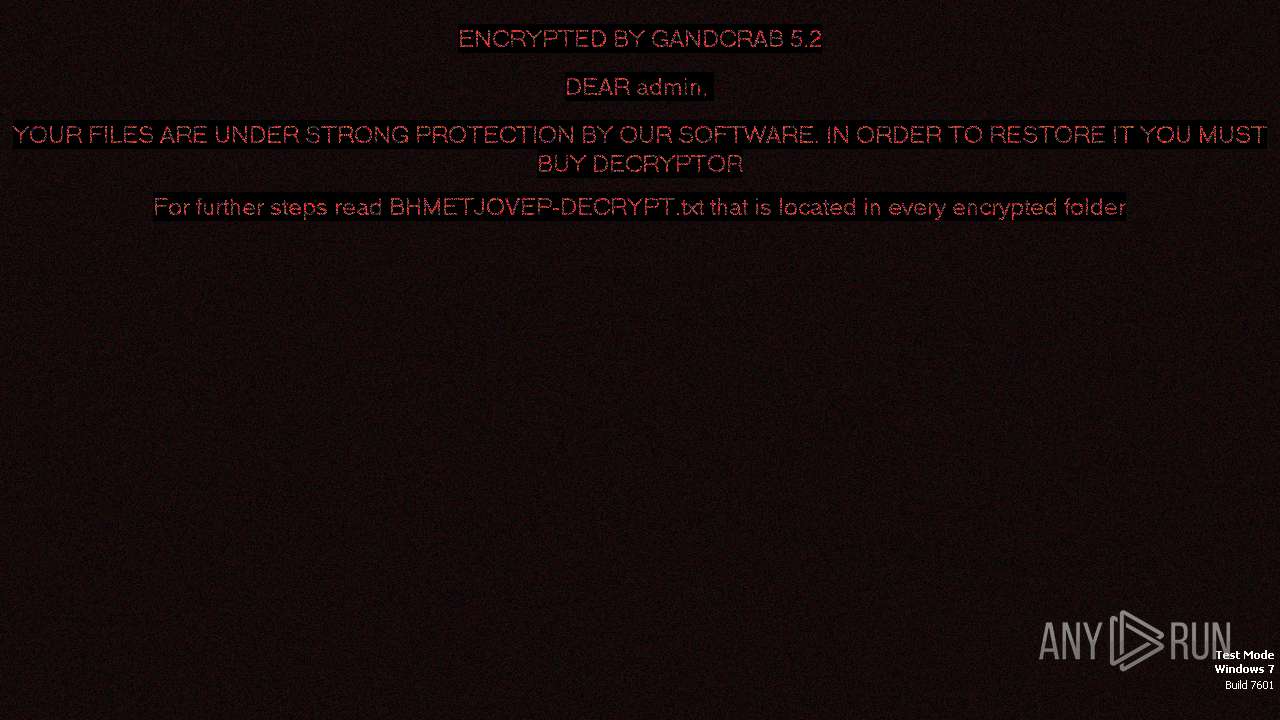
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | March 21, 2019, 18:34:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | C6B5114DA22B8B4AF660397326250B0C |
| SHA1: | 7918F8EC9E1853AEEE48356595D0DA3DB1AFFC20 |
| SHA256: | EBFC5467B571656FA637E3BA09CBBBEB85D5539467F13A5575CB3AA76720F7BC |
| SSDEEP: | 3072:YcLPYT1tUCA1E9rbuduhyeCnx+zilG+eUp5IAlImy2:uTLkE932uhydnOilUGa6zy2 |
MALICIOUS
Downloads executable files from the Internet
- explorer.exe (PID: 1868)
- tydkdukd.exe (PID: 3036)
Writes to a start menu file
- explorer.exe (PID: 1868)
- Explorer.EXE (PID: 1724)
Downloads executable files from IP
- explorer.exe (PID: 1868)
Connects to CnC server
- explorer.exe (PID: 1868)
- hygfh2.exe (PID: 2632)
- svchost.exe (PID: 2516)
- Explorer.EXE (PID: 1724)
Application was dropped or rewritten from another process
- 2A58.tmp.exe (PID: 2592)
- cbnjoyiv.exe (PID: 3000)
- 8DA7.tmp.exe (PID: 2272)
- tydkdukd.exe (PID: 2656)
- tydkdukd.exe (PID: 3036)
- hygfh2.exe (PID: 2632)
- cbnjoyiv.exe (PID: 1260)
Uses SVCHOST.EXE for hidden code execution
- cbnjoyiv.exe (PID: 3000)
- svchost.exe (PID: 2336)
Loads the Task Scheduler COM API
- explorer.exe (PID: 1868)
- Explorer.EXE (PID: 1724)
SMOKE was detected
- explorer.exe (PID: 1868)
- Explorer.EXE (PID: 1724)
TOFSEE was detected
- svchost.exe (PID: 2336)
Renames files like Ransomware
- hygfh2.exe (PID: 2632)
Writes file to Word startup folder
- hygfh2.exe (PID: 2632)
Loads dropped or rewritten executable
- tydkdukd.exe (PID: 3036)
Stealing of credential data
- tydkdukd.exe (PID: 3036)
Deletes shadow copies
- hygfh2.exe (PID: 2632)
Dropped file may contain instructions of ransomware
- hygfh2.exe (PID: 2632)
Looks like application has launched a miner
- svchost.exe (PID: 2336)
MINER was detected
- svchost.exe (PID: 2516)
GANDCRAB detected
- hygfh2.exe (PID: 2632)
SUSPICIOUS
Executable content was dropped or overwritten
- explorer.exe (PID: 1868)
- 2A58.tmp.exe (PID: 2592)
- cmd.exe (PID: 2796)
- 8DA7.tmp.exe (PID: 2272)
- tydkdukd.exe (PID: 3036)
Starts CMD.EXE for commands execution
- 2A58.tmp.exe (PID: 2592)
- Explorer.EXE (PID: 1724)
Reads the machine GUID from the registry
- explorer.exe (PID: 1868)
- netsh.exe (PID: 1740)
- SearchProtocolHost.exe (PID: 856)
- Explorer.EXE (PID: 1724)
Creates or modifies windows services
- svchost.exe (PID: 2336)
Creates files in the user directory
- explorer.exe (PID: 1868)
- Explorer.EXE (PID: 1724)
- hygfh2.exe (PID: 2632)
Uses NETSH.EXE for network configuration
- 2A58.tmp.exe (PID: 2592)
Creates files in the Windows directory
- svchost.exe (PID: 2336)
Executes scripts
- 8DA7.tmp.exe (PID: 2272)
Connects to unusual port
- svchost.exe (PID: 2336)
- svchost.exe (PID: 2516)
Starts SC.EXE for service management
- 2A58.tmp.exe (PID: 2592)
Connects to SMTP port
- svchost.exe (PID: 2336)
Application launched itself
- tydkdukd.exe (PID: 2656)
- ebfc5467b571656fa637e3ba09cbbbeb85d5539467f13a5575cb3aa76720f7bc.exe (PID: 856)
- svchost.exe (PID: 2336)
- htujvavg.exe (PID: 2112)
- htujvavg.exe (PID: 1000)
Creates files in the program directory
- hygfh2.exe (PID: 2632)
- tydkdukd.exe (PID: 3036)
INFO
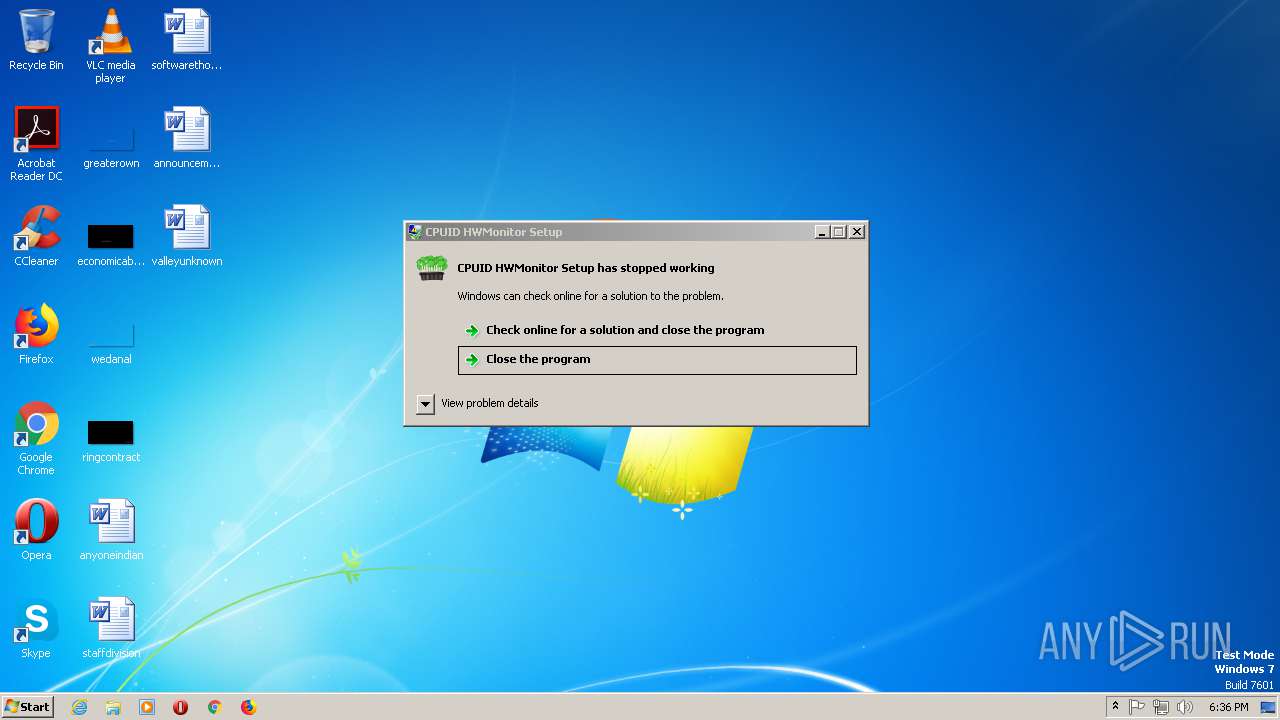
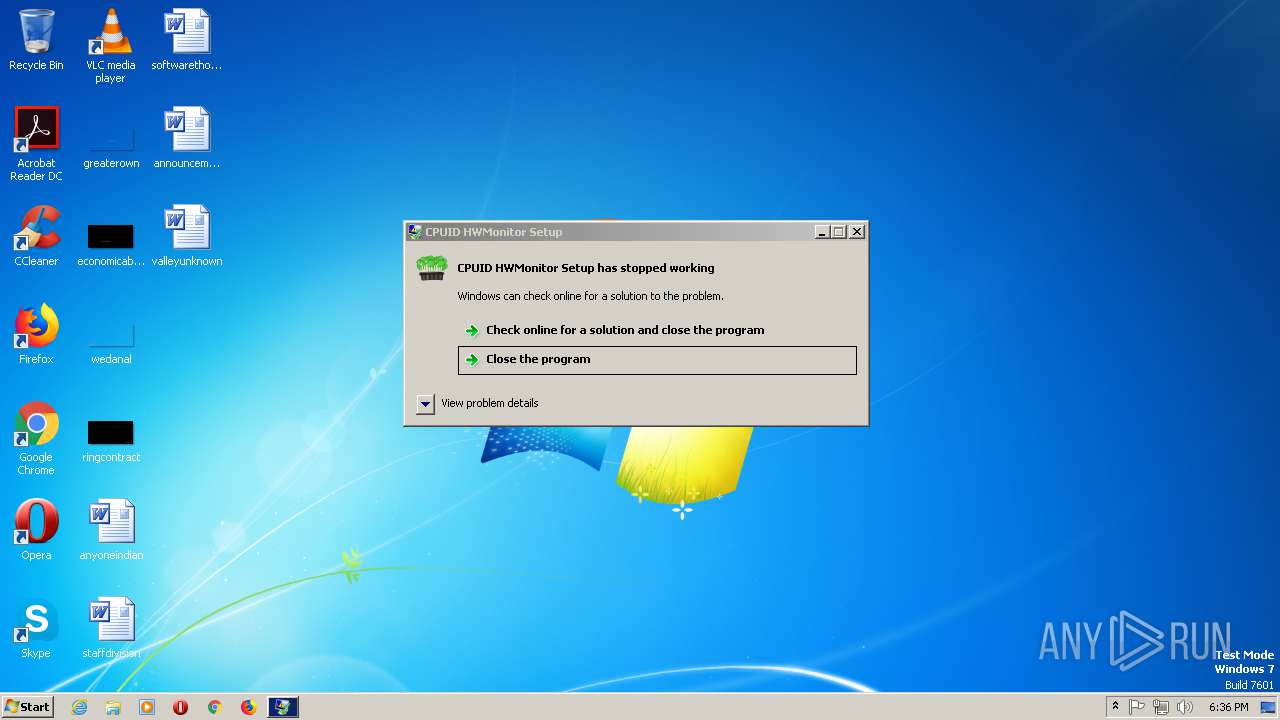
Application was crashed
- tydkdukd.exe (PID: 3036)
Dropped object may contain TOR URL's
- hygfh2.exe (PID: 2632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:03 21:16:31+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 114688 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | 176128 |
| EntryPoint: | 0x47bc0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 7.4.4.86 |
| ProductVersion: | 7.4.4.86 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Mar-2018 20:16:31 |
| Detected languages: |
|
| FileVersion: | 7.4.4.86 |
| ProductVersion: | 7.4.4.86 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 03-Mar-2018 20:16:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0002B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0002C000 | 0x0001C000 | 0x0001BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.81015 |
.rsrc | 0x00048000 | 0x0000E000 | 0x0000DC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.68191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.06974 | 328 | UNKNOWN | English - United States | RT_VERSION |
2 | 4.64991 | 9640 | UNKNOWN | Czech - Czech Republic | RT_ICON |
3 | 4.92413 | 4264 | UNKNOWN | Czech - Czech Republic | RT_ICON |
4 | 5.10708 | 1128 | UNKNOWN | Czech - Czech Republic | RT_ICON |
5 | 7.44038 | 3752 | UNKNOWN | Czech - Czech Republic | RT_ICON |
6 | 7.42768 | 2216 | UNKNOWN | Czech - Czech Republic | RT_ICON |
7 | 5.62408 | 68 | UNKNOWN | Czech - Czech Republic | RT_STRING |
8 | 5.38173 | 60 | UNKNOWN | Czech - Czech Republic | RT_STRING |
9 | 7.4895 | 9640 | UNKNOWN | Czech - Czech Republic | RT_ICON |
10 | 7.8447 | 4264 | UNKNOWN | Czech - Czech Republic | RT_ICON |
Imports
GDI32.dll |
KERNEL32.DLL |
MSIMG32.dll |
ole32.dll |
Total processes
123
Monitored processes
30
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | C:\Users\admin\AppData\Roaming\Microsoft\Windows\wbdifcas\htujvavg.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\wbdifcas\htujvavg.exe | — | htujvavg.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 776 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\sscc.vbs" | C:\Windows\SysWOW64\WScript.exe | 8DA7.tmp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 836 | sc create cgrlikha binPath= "C:\Windows\SysWOW64\cgrlikha\cbnjoyiv.exe /d\"C:\Users\admin\AppData\Local\Temp\2A58.tmp.exe\"" type= own start= auto DisplayName= "wifi support" | C:\Windows\system32\sc.exe | 2A58.tmp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 856 | "C:\Users\admin\AppData\Local\Temp\ebfc5467b571656fa637e3ba09cbbbeb85d5539467f13a5575cb3aa76720f7bc.exe" | C:\Users\admin\AppData\Local\Temp\ebfc5467b571656fa637e3ba09cbbbeb85d5539467f13a5575cb3aa76720f7bc.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 856 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe11_ Global\UsGthrCtrlFltPipeMssGthrPipe11 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.23930 (win7sp1_ldr.171011-1526) Modules
| |||||||||||||||
| 980 | "C:\Users\admin\AppData\Local\Temp\ebfc5467b571656fa637e3ba09cbbbeb85d5539467f13a5575cb3aa76720f7bc.exe" | C:\Users\admin\AppData\Local\Temp\ebfc5467b571656fa637e3ba09cbbbeb85d5539467f13a5575cb3aa76720f7bc.exe | — | ebfc5467b571656fa637e3ba09cbbbeb85d5539467f13a5575cb3aa76720f7bc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1000 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\wbdifcas\htujvavg.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\wbdifcas\htujvavg.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1260 | C:\Windows\SysWOW64\cgrlikha\cbnjoyiv.exe | C:\Windows\SysWOW64\cgrlikha\cbnjoyiv.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1344 | cmd /C mkdir C:\Windows\SysWOW64\cgrlikha\ | C:\Windows\system32\cmd.exe | 2A58.tmp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1404 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\SysWOW64\wbem\wmic.exe | — | hygfh2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 726
Read events
7 398
Write events
320
Delete events
8
Modification events
| (PID) Process: | (1868) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage\NewShortcuts |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1868) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage\NewShortcuts |
| Operation: | write | Name: | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\WinRAR\WinRAR.lnk |
Value: 1 | |||
| (PID) Process: | (1868) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage\NewShortcuts |
| Operation: | write | Name: | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\WinRAR\WinRAR.lnk |
Value: 1 | |||
| (PID) Process: | (2592) 2A58.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2592) 2A58.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2592) 2A58.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2592) 2A58.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1868) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\65\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1868) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\jhfn.rkr |
Value: 0000000000000000000000009C000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (1868) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000220000002F000000B5E50900040000000E000000B8E402007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000002E006500780065000000000000000000000000005867F4FBFE0700000000000000000000A400060000000000D8EBC90200000000010000000000000080E0C9020000000004FE5BFEFE07000080E0C902000000000000000000000000000000000000000022BBEAFF0000000080E0C90200000000A400060000000000A2100000000000004313B30300000000A400060000000000EFCBEAFF00000000A210000000000000000000000000000080E0C9020000000000000000000000000100000000000000D469F4FBFE070000040000000E0000000FE102007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018565CFEFE07000000000040FCA81A4100000040FCA81A4100000040FCA81A4100000040FCA81A4100000000000000002C5D5CFEFE0700000000000000000000885FA703000000003C9798FEFE070000885FA7030000000001000000040000000E000000B8E402007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000002E006500780065000000000000000000000000005867F4FBFE0700000000000000000000A400060000000000D8EBC90200000000010000000000000080E0C9020000000004FE5BFEFE07000080E0C902000000000000000000000000000000000000000022BBEAFF0000000080E0C90200000000A400060000000000A2100000000000004313B30300000000A400060000000000EFCBEAFF00000000A210000000000000000000000000000080E0C9020000000000000000000000000100000000000000D469F4FBFE070000040000000E0000000FE102007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018565CFEFE07000000000040FCA81A4100000040FCA81A4100000040FCA81A4100000040FCA81A4100000000000000002C5D5CFEFE0700000000000000000000885FA703000000003C9798FEFE070000885FA7030000000001000000040000000E000000B8E402007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000002E006500780065000000000000000000000000005867F4FBFE0700000000000000000000A400060000000000D8EBC90200000000010000000000000080E0C9020000000004FE5BFEFE07000080E0C902000000000000000000000000000000000000000022BBEAFF0000000080E0C90200000000A400060000000000A2100000000000004313B30300000000A400060000000000EFCBEAFF00000000A210000000000000000000000000000080E0C9020000000000000000000000000100000000000000D469F4FBFE070000040000000E0000000FE102007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018565CFEFE07000000000040FCA81A4100000040FCA81A4100000040FCA81A4100000040FCA81A4100000000000000002C5D5CFEFE0700000000000000000000885FA703000000003C9798FEFE070000885FA7030000000001000000 | |||
Executable files
19
Suspicious files
2 227
Text files
216
Unknown types
60
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1868 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\wbdifcas.lnk | — | |
MD5:— | SHA256:— | |||
| 2336 | svchost.exe | C:\Windows\SysWOW64\config\systemprofile:.repos | binary | |
MD5:— | SHA256:— | |||
| 2272 | 8DA7.tmp.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\sscc.vbs | text | |
MD5:— | SHA256:— | |||
| 1868 | explorer.exe | C:\Users\admin\AppData\Local\Temp\2A58.tmp.exe | executable | |
MD5:— | SHA256:— | |||
| 1868 | explorer.exe | C:\Users\admin\AppData\Local\Temp\8DA7.tmp.exe | executable | |
MD5:— | SHA256:— | |||
| 2632 | hygfh2.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 1868 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\wbdifcas\htujvavg.exe | executable | |
MD5:— | SHA256:— | |||
| 2796 | cmd.exe | C:\Windows\SysWOW64\cgrlikha\cbnjoyiv.exe | executable | |
MD5:— | SHA256:— | |||
| 2272 | 8DA7.tmp.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\celebrating-johann-sebastian-bach-5702425880035328.3-s.png | image | |
MD5:— | SHA256:— | |||
| 3036 | tydkdukd.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\freebl3[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
399
DNS requests
339
Threats
82
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1868 | explorer.exe | POST | 404 | 124.156.106.160:80 | http://vygxxhh.bit/2/ | CN | binary | 37 b | malicious |
1868 | explorer.exe | GET | 200 | 93.189.41.63:80 | http://93.189.41.63/2.php | RU | executable | 103 Kb | suspicious |
1868 | explorer.exe | POST | 404 | 124.156.106.160:80 | http://vygxxhh.bit/2/ | CN | html | 401 b | malicious |
1868 | explorer.exe | POST | 404 | 124.156.106.160:80 | http://vygxxhh.bit/2/ | CN | html | 401 b | malicious |
1868 | explorer.exe | POST | 404 | 124.156.106.160:80 | http://vygxxhh.bit/2/ | CN | html | 401 b | malicious |
1868 | explorer.exe | POST | 404 | 124.156.106.160:80 | http://vygxxhh.bit/2/ | CN | binary | 42 b | malicious |
1868 | explorer.exe | POST | 404 | 124.156.106.160:80 | http://vygxxhh.bit/2/ | CN | html | 401 b | malicious |
1868 | explorer.exe | POST | 404 | 124.156.106.160:80 | http://vygxxhh.bit/2/ | CN | html | 401 b | malicious |
1868 | explorer.exe | POST | 404 | 124.156.106.160:80 | http://vygxxhh.bit/2/ | CN | binary | 8 b | malicious |
1868 | explorer.exe | POST | 200 | 124.156.106.160:80 | http://vygxxhh.bit/2/ | CN | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1868 | explorer.exe | 124.156.106.160:80 | vygxxhh.bit | — | CN | suspicious |
2336 | svchost.exe | 104.47.54.36:25 | microsoft-com.mail.protection.outlook.com | Microsoft Corporation | US | unknown |
2336 | svchost.exe | 74.6.137.64:25 | mta6.am0.yahoodns.net | Yahoo! | US | unknown |
1868 | explorer.exe | 2.16.186.17:80 | www.msftncsi.com | Akamai International B.V. | — | whitelisted |
1868 | explorer.exe | 45.66.9.228:80 | — | — | — | suspicious |
1868 | explorer.exe | 58.251.121.110:53 | — | China Unicom Shenzen network | CN | malicious |
1868 | explorer.exe | 192.71.245.208:53 | — | Prometeus di Daniela Agro | IT | malicious |
3036 | tydkdukd.exe | 86.105.1.108:80 | google.ac.ug | Seflow S.N.C. Di Marco Brame' & C. | IT | malicious |
2336 | svchost.exe | 104.47.37.33:25 | hotmail-com.olc.protection.outlook.com | Microsoft Corporation | US | whitelisted |
2336 | svchost.exe | 212.227.15.10:25 | mx00.gmx.net | 1&1 Internet SE | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.msftncsi.com |
| whitelisted |
dvhwzq.ru |
| malicious |
hdxaet.ru |
| unknown |
vygxxhh.bit |
| malicious |
microsoft.com |
| whitelisted |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
yahoo.com |
| whitelisted |
mta6.am0.yahoodns.net |
| whitelisted |
iplogger.org |
| shared |
google.ac.ug |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1868 | explorer.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
1868 | explorer.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
1868 | explorer.exe | A Network Trojan was detected | ET TROJAN Sharik/Smoke CnC Beacon 12 |
1868 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32.Sharik/SmokeLoader 404 fake response |
1868 | explorer.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
1868 | explorer.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
1868 | explorer.exe | A Network Trojan was detected | ET TROJAN Sharik/Smoke CnC Beacon 12 |
1868 | explorer.exe | A Network Trojan was detected | ET TROJAN Sharik/Smoke Fake 404 Response with Payload Location |
1868 | explorer.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1868 | explorer.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
10 ETPRO signatures available at the full report
Process | Message |
|---|---|
tydkdukd.exe | User32.dll |
tydkdukd.exe | User32.dll |
tydkdukd.exe | User32.dll |
tydkdukd.exe | User32.dll |
tydkdukd.exe | User32.dll |
tydkdukd.exe | User32.dll |
tydkdukd.exe | User32.dll |
tydkdukd.exe | User32.dll |
tydkdukd.exe | User32.dll |
tydkdukd.exe | User32.dll |