| File name: | DriveEncryptor.bat |
| Full analysis: | https://app.any.run/tasks/7b8ff92d-4f0e-48a4-a09b-4d1fd3b5c4ba |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2026, 21:48:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-script.python |
| File info: | Python script, Unicode text, UTF-8 text executable, with very long lines (347) |
| MD5: | B8F24E5972172FE4DFA5032B737D34F9 |
| SHA1: | FEF3F3129C0E331049BA0F4E990BAF4E80878AA1 |
| SHA256: | EBEB8B7AC294D4BD11A5B357160A3409E9689DFADAD09B8C9A080044D9549A15 |
| SSDEEP: | 192:C/ADzl0zVt22FI+o7whmU7uwsQvaVYv2Yepwu+ICyPi:Qw0jI+oEP7gQva1pn+Iy |
MALICIOUS
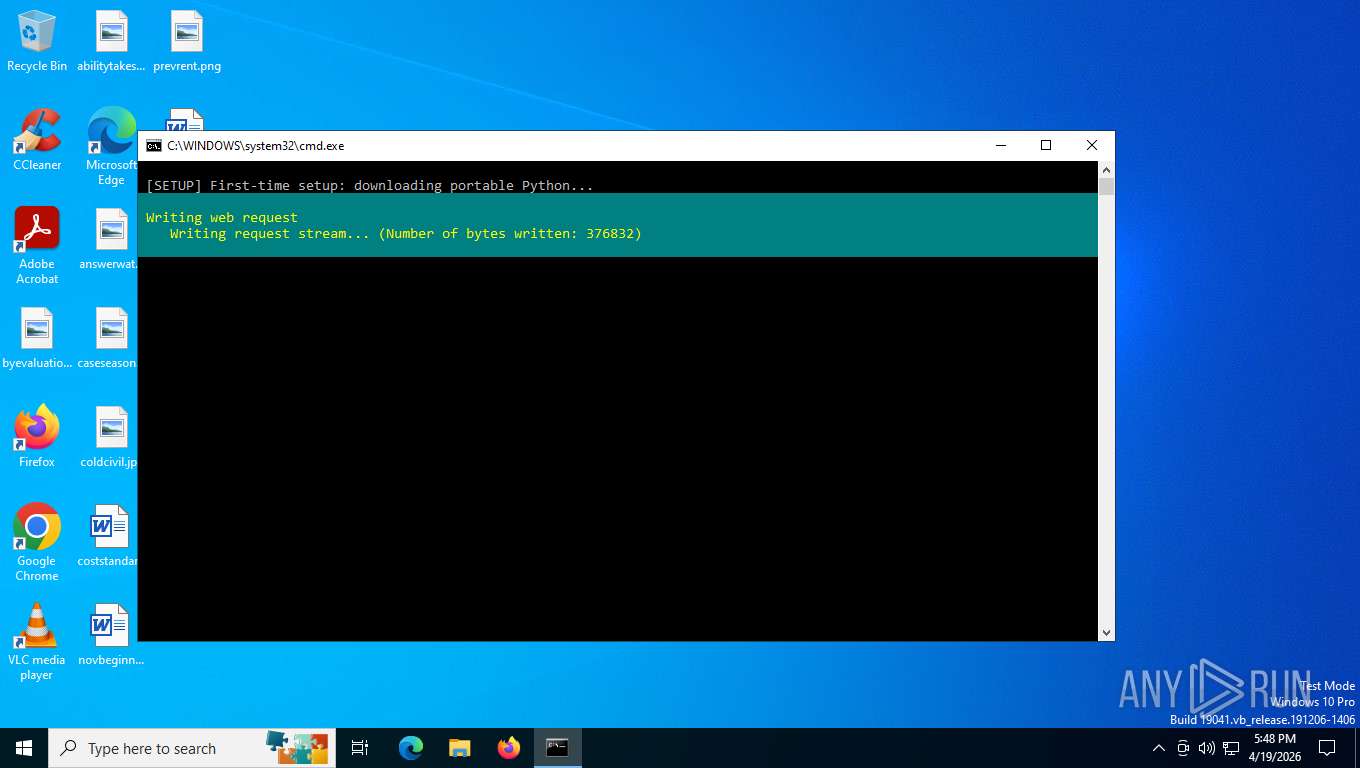
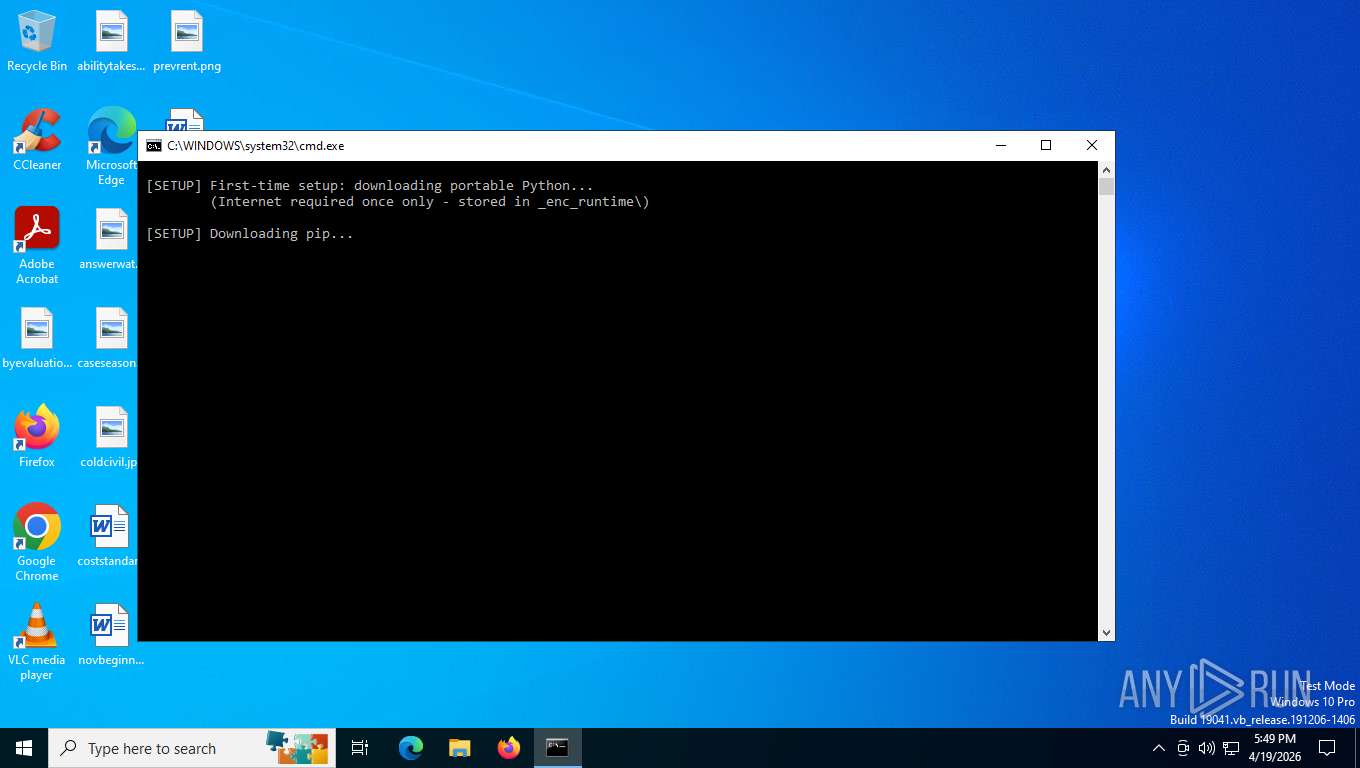
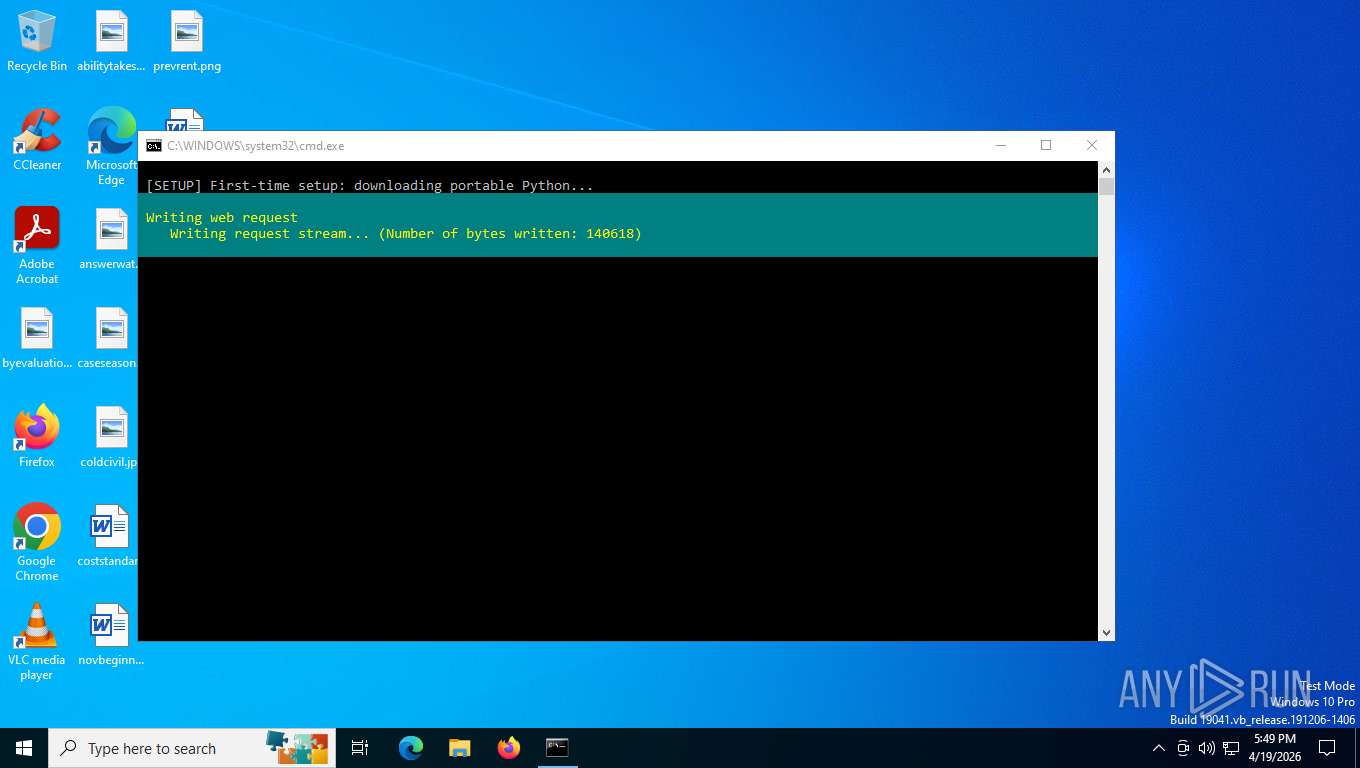
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 4692)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4692)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 6228)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4692)
Bypass execution policy to execute commands
- powershell.exe (PID: 1296)
- powershell.exe (PID: 2456)
- powershell.exe (PID: 2880)
- powershell.exe (PID: 7420)
- powershell.exe (PID: 2032)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4692)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4692)
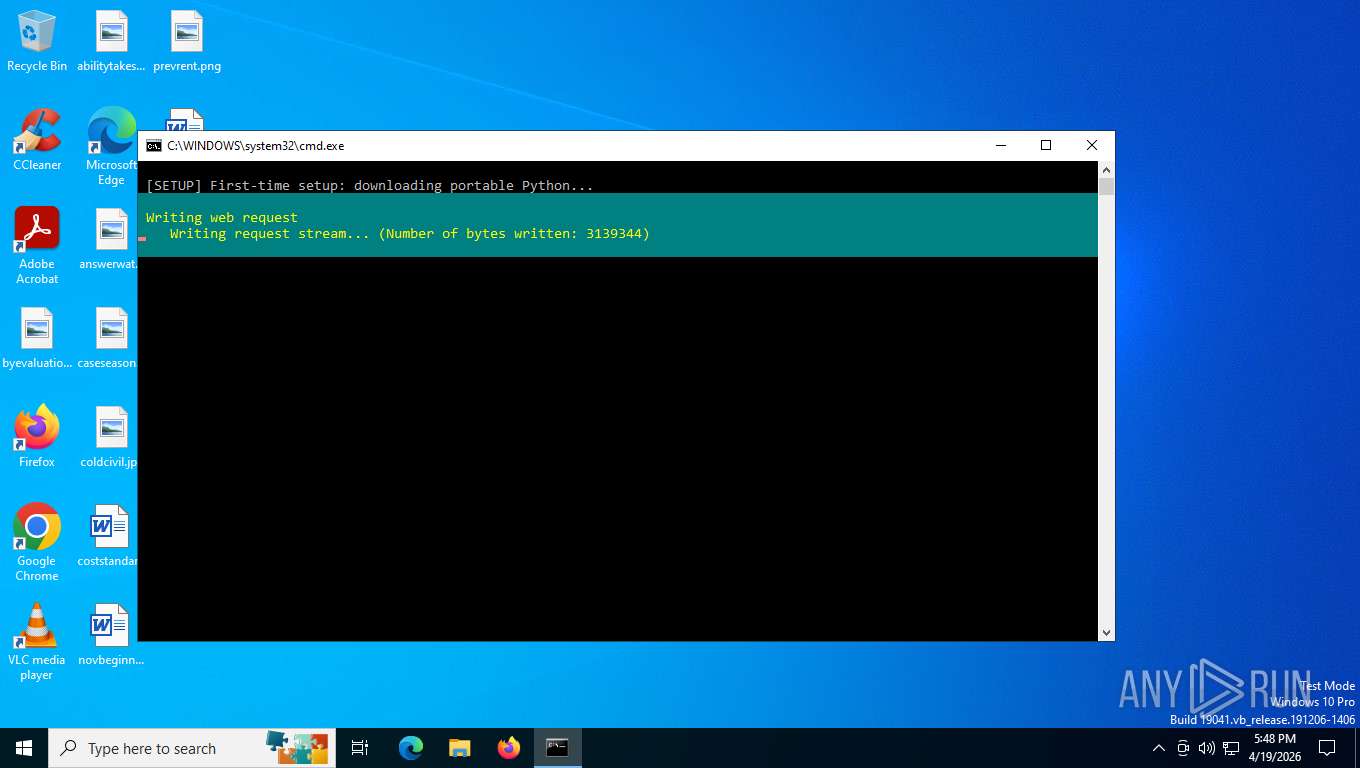
Downloads file from URI via Powershell
- powershell.exe (PID: 2456)
- powershell.exe (PID: 7420)
The process drops C-runtime libraries
- powershell.exe (PID: 2456)
- powershell.exe (PID: 2880)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 2880)
Executable content was dropped or overwritten
- powershell.exe (PID: 2880)
- python.exe (PID: 8072)
- python.exe (PID: 6628)
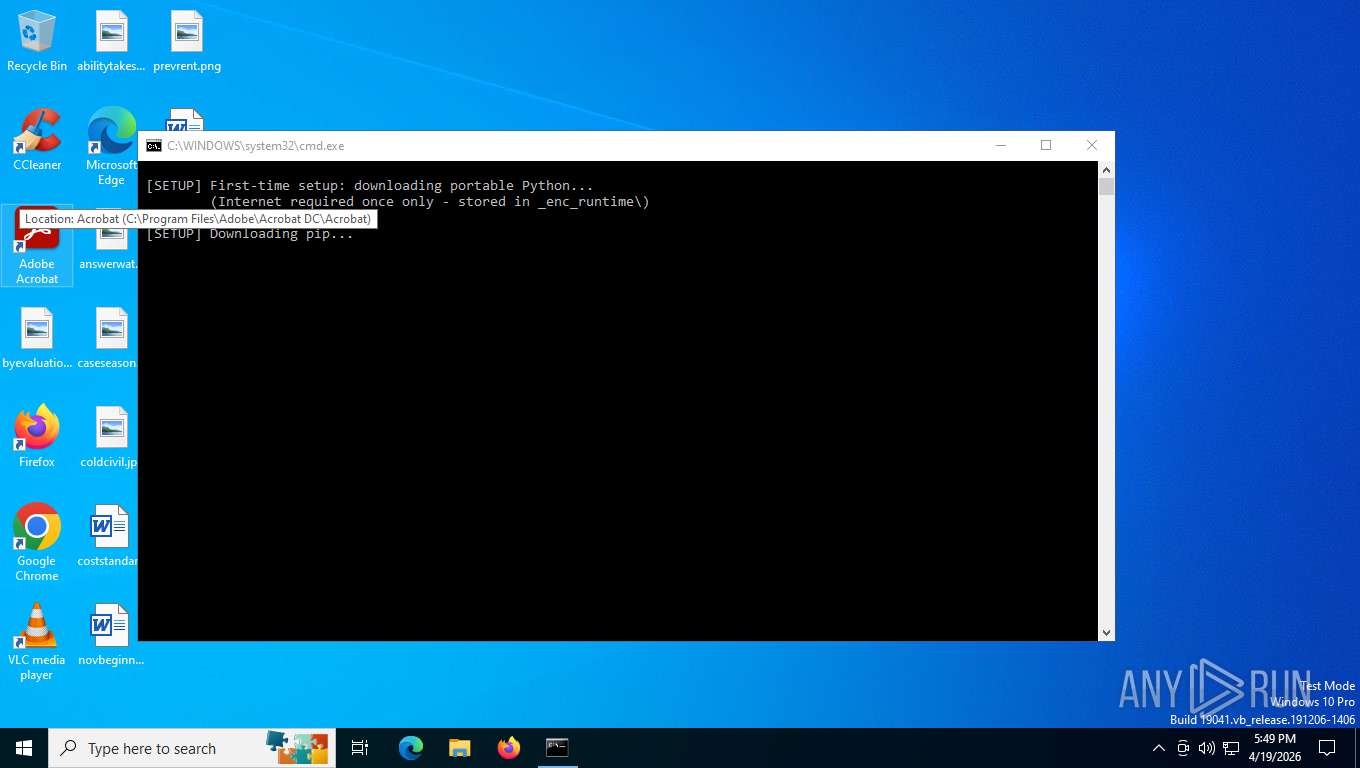
Process drops python dynamic module
- powershell.exe (PID: 2880)
- python.exe (PID: 6628)
Loads Python modules
- python.exe (PID: 8072)
- python.exe (PID: 6628)
- python.exe (PID: 1980)
The executable file from the user directory is run by the CMD process
- python.exe (PID: 8072)
- pip.exe (PID: 1140)
- python.exe (PID: 1980)
INFO
The sample compiled with english language support
- powershell.exe (PID: 2456)
- powershell.exe (PID: 2880)
- python.exe (PID: 8072)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2880)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2880)
Using PowerShell for ZIP File Operations
- powershell.exe (PID: 2880)
Checks supported languages
- python.exe (PID: 8072)
- pip.exe (PID: 1140)
- python.exe (PID: 6628)
- python.exe (PID: 1980)
Create files in a temporary directory
- python.exe (PID: 8072)
- python.exe (PID: 6628)
Drops encrypted JS script (Microsoft Script Encoder)
- python.exe (PID: 8072)
- python.exe (PID: 6628)
Reads the computer name
- python.exe (PID: 8072)
- python.exe (PID: 6628)
Checks operating system version
- python.exe (PID: 8072)
- python.exe (PID: 6628)
Python executable
- python.exe (PID: 8072)
- python.exe (PID: 6628)
- python.exe (PID: 1980)
Reads the machine GUID from the registry
- python.exe (PID: 8072)
- python.exe (PID: 6628)
Creates files or folders in the user directory
- python.exe (PID: 8072)
- python.exe (PID: 6628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
153
Monitored processes
13
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1140 | "C:\Users\admin\AppData\Local\Temp\_enc_runtime\Scripts\pip.exe" install cryptography --quiet --no-warn-script-location | C:\Users\admin\AppData\Local\Temp\_enc_runtime\Scripts\pip.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1296 | powershell -NoProfile -ExecutionPolicy Bypass -Command "$lines = Get-Content -LiteralPath 'C:\Users\admin\AppData\Local\Temp\DriveEncryptor.bat'; $idx = 0; for ($i = 0; $i -lt $lines.Count; $i++) { if ($lines[$i] -eq ':PYTHON_SOURCE:') { $idx = $i + 1; break } }; $py = $lines[$idx..($lines.Count - 1)] -join [Environment]::NewLine; Set-Content -LiteralPath 'C:\Users\admin\AppData\Local\Temp\drive_enc_tmp.py' -Value $py -Encoding UTF8" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1980 | "C:\Users\admin\AppData\Local\Temp\_enc_runtime\python.exe" "C:\Users\admin\AppData\Local\Temp\drive_enc_tmp.py" | C:\Users\admin\AppData\Local\Temp\_enc_runtime\python.exe | — | cmd.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 2 Version: 3.11.9 Modules
| |||||||||||||||
| 2032 | powershell -NoProfile -ExecutionPolicy Bypass -Command "$pth = Get-ChildItem 'C:\Users\admin\AppData\Local\Temp\_enc_runtime' -Filter 'python*._pth' | Select-Object -First 1; (Get-Content $pth.FullName) -replace '#import site','import site' | Set-Content $pth.FullName" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
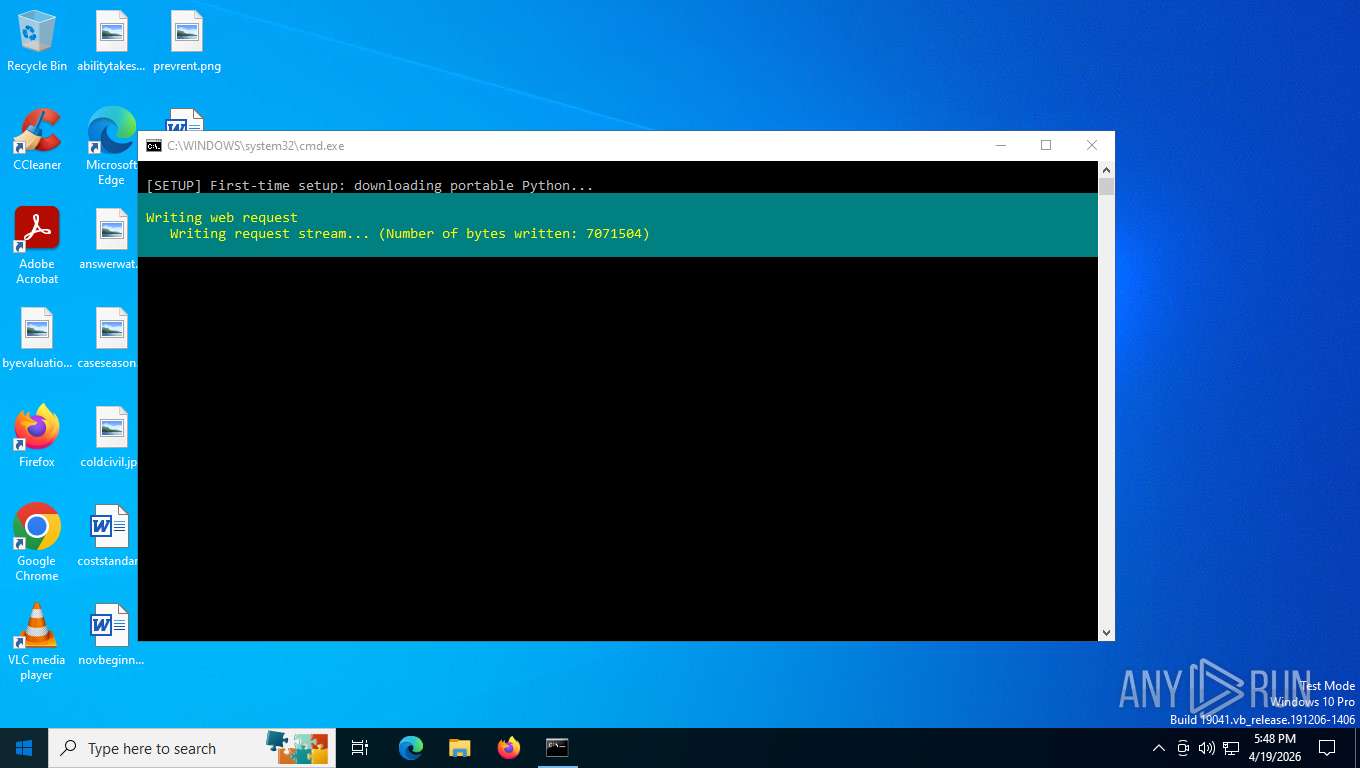
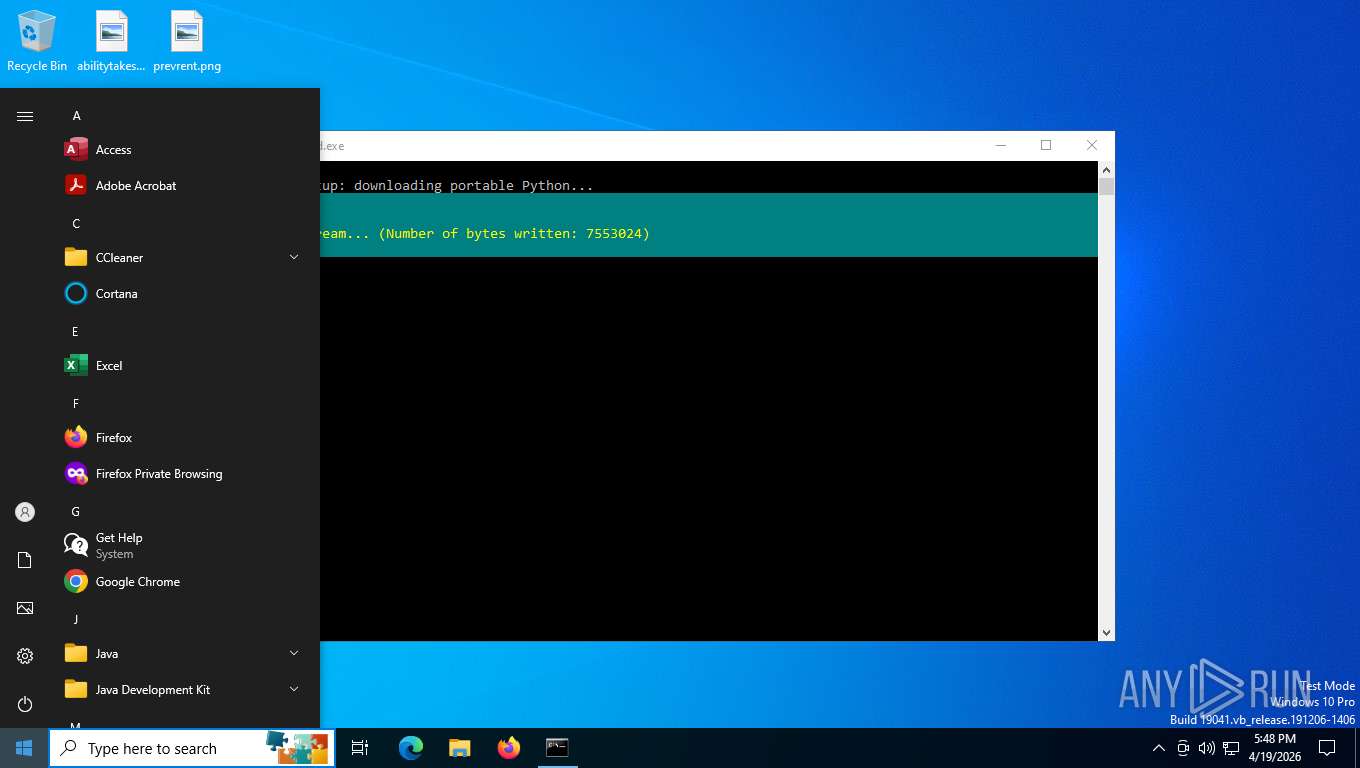
| 2456 | powershell -NoProfile -ExecutionPolicy Bypass -Command "Invoke-WebRequest -Uri 'https://www.python.org/ftp/python/3.11.9/python-3.11.9-embed-amd64.zip' -OutFile 'C:\Users\admin\AppData\Local\Temp\py_embed.zip' -UseBasicParsing" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2880 | powershell -NoProfile -ExecutionPolicy Bypass -Command "Expand-Archive -Path 'C:\Users\admin\AppData\Local\Temp\py_embed.zip' -DestinationPath 'C:\Users\admin\AppData\Local\Temp\_enc_runtime' -Force" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4692 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\DriveEncryptor.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6228 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6628 | "C:\Users\admin\AppData\Local\Temp\_enc_runtime\python.exe" "C:\Users\admin\AppData\Local\Temp\_enc_runtime\Scripts\pip.exe" install cryptography --quiet --no-warn-script-location | C:\Users\admin\AppData\Local\Temp\_enc_runtime\python.exe | pip.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.11.9 Modules
| |||||||||||||||
| 7096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 757
Read events
32 757
Write events
0
Delete events
0
Modification events
Executable files
46
Suspicious files
1 693
Text files
1 074
Unknown types
159
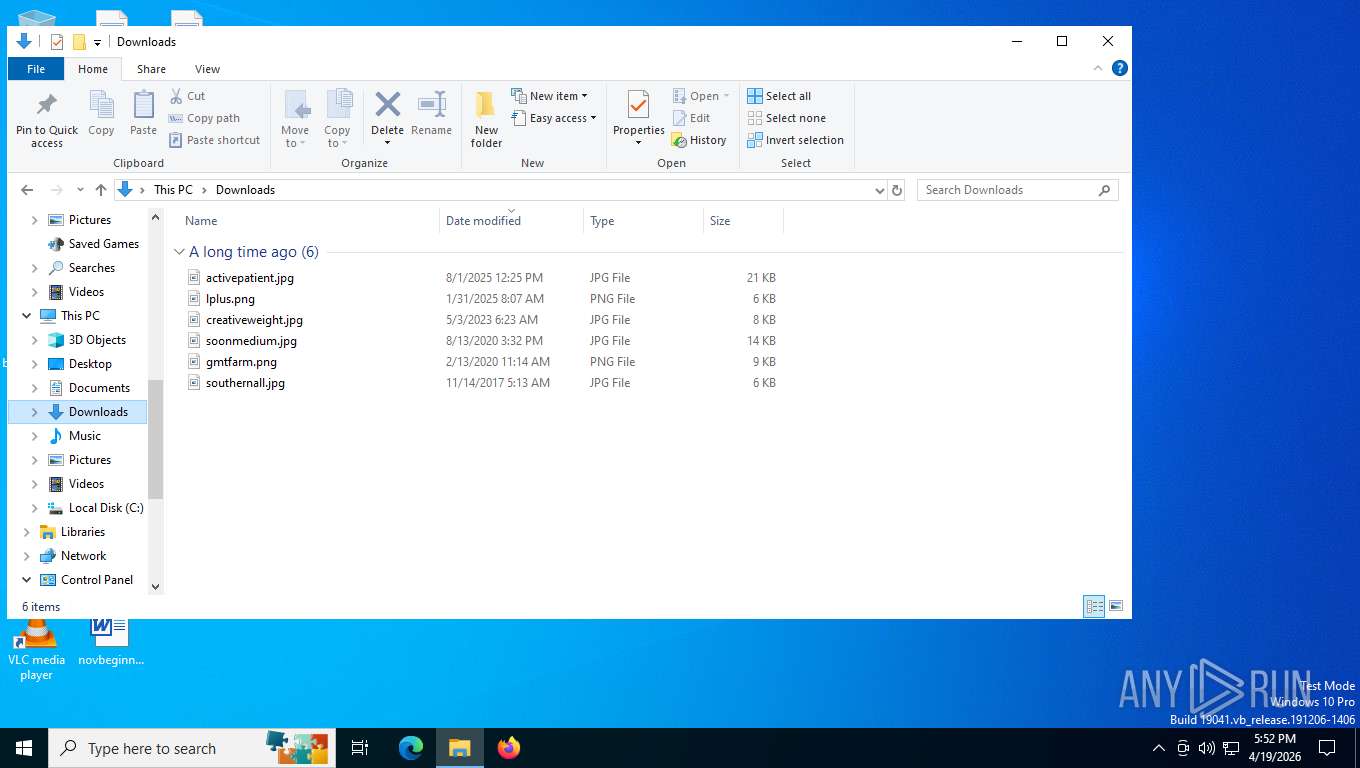
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:E64B12A6A1C1FB03DD84805641DD595A | SHA256:2268D7DBC37DD31CDC1208793F0B0D40F4A6B7A733028B919D9723E22CEE6991 | |||
| 1296 | powershell.exe | C:\Users\admin\AppData\Local\Temp\drive_enc_tmp.py | text | |
MD5:6D39ACB351595C0B419F1767DED97F99 | SHA256:A91D9C66A92BCCE36AE68265EBA3B5066BB6DF405003ACDC10B92541B42DDA00 | |||
| 2880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\_enc_runtime\python.exe | executable | |
MD5:36C241133B4DBB462E256E1F71FD3978 | SHA256:5F7B89A612C9B8AF1D6456CDFCD1DBE5CA630849E79AEBCED9BEE9A6694952EC | |||
| 1296 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_aqzkatm2.bjl.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1296 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cp3eyu12.rea.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2456 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0iwzit0q.fzm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_u3yle3qr.aql.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\_enc_runtime\pythonw.exe | executable | |
MD5:B7FB4DD9BCDF787D4C1995037257984B | SHA256:D5355E1DE2A5195DCCB1BA524B146AA7705BE71AF18D876819756838251B37B3 | |||
| 2880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\_enc_runtime\python3.dll | executable | |
MD5:7E07C63636A01DF77CD31CFCA9A5C745 | SHA256:DB84BC052CFB121FE4DB36242BA5F1D2C031B600EF5D8D752CF25B7C02B6BAC6 | |||
| 2456 | powershell.exe | C:\Users\admin\AppData\Local\Temp\py_embed.zip | compressed | |
MD5:6D9AA08531D48FCC261BA667E2DF17C4 | SHA256:009D6BF7E3B2DDCA3D784FA09F90FE54336D5B60F0E0F305C37F400BF83CFD3B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
41
DNS requests
30
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5532 | SearchApp.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 314 b | whitelisted |
680 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
2456 | powershell.exe | GET | 200 | 167.82.48.223:443 | https://www.python.org/ftp/python/3.11.9/python-3.11.9-embed-amd64.zip | US | compressed | 5.00 Mb | unknown |
5316 | svchost.exe | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
5316 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
1108 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
680 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2456 | powershell.exe | 167.82.48.223:443 | www.python.org | FASTLY | US | whitelisted |
3428 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5316 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5316 | svchost.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
680 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.python.org |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
680 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2456 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2232 | svchost.exe | Misc activity | ET FILE_SHARING File Hosting Service Domain Domain in DNS Lookup (files .pythonhosted .org) |
8072 | python.exe | Misc activity | ET INFO Observed File Hosting Service Domain (files .pythonhosted .org in TLS SNI) |
7420 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2232 | svchost.exe | Misc activity | ET FILE_SHARING File Hosting Service Domain Domain in DNS Lookup (files .pythonhosted .org) |
6628 | python.exe | Misc activity | ET INFO Observed File Hosting Service Domain (files .pythonhosted .org in TLS SNI) |