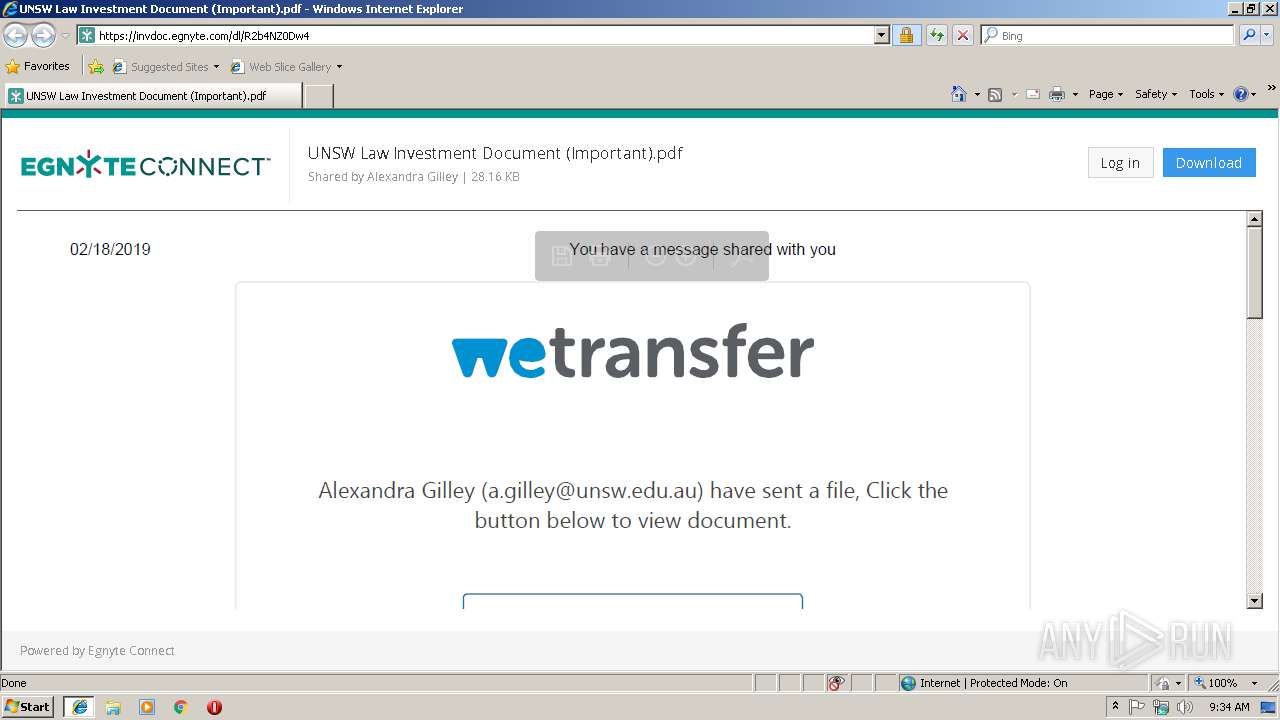
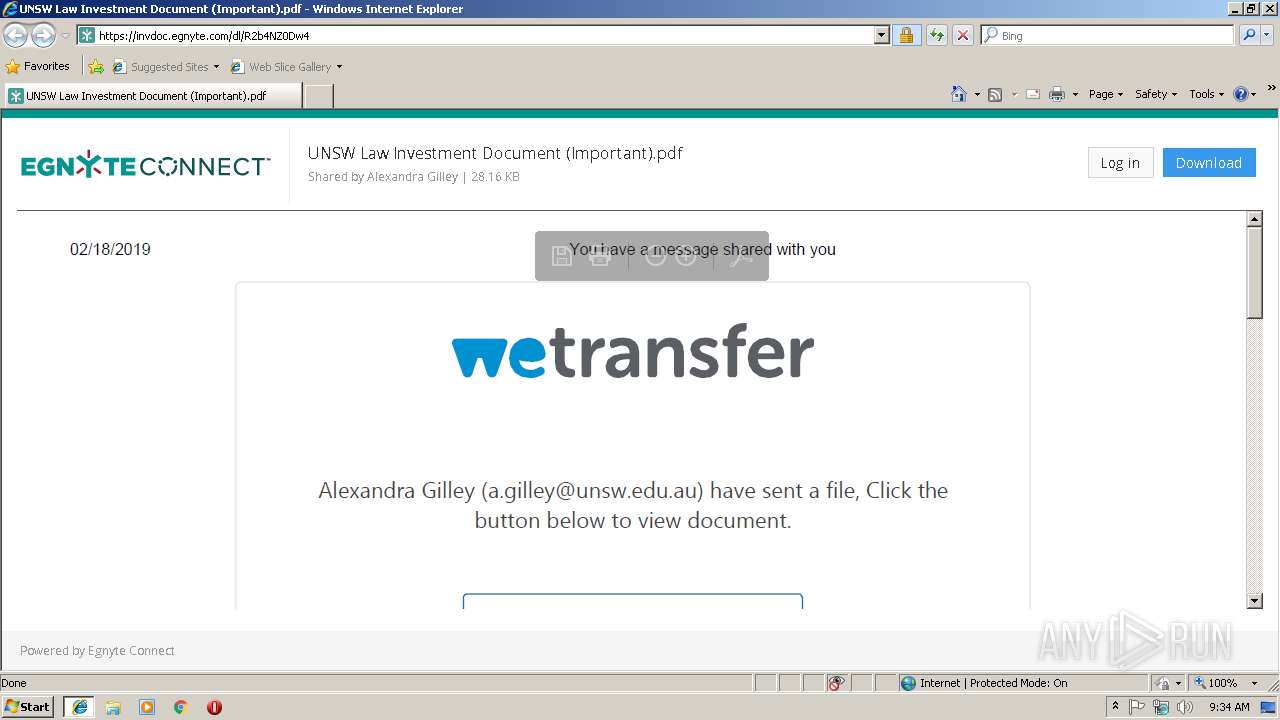
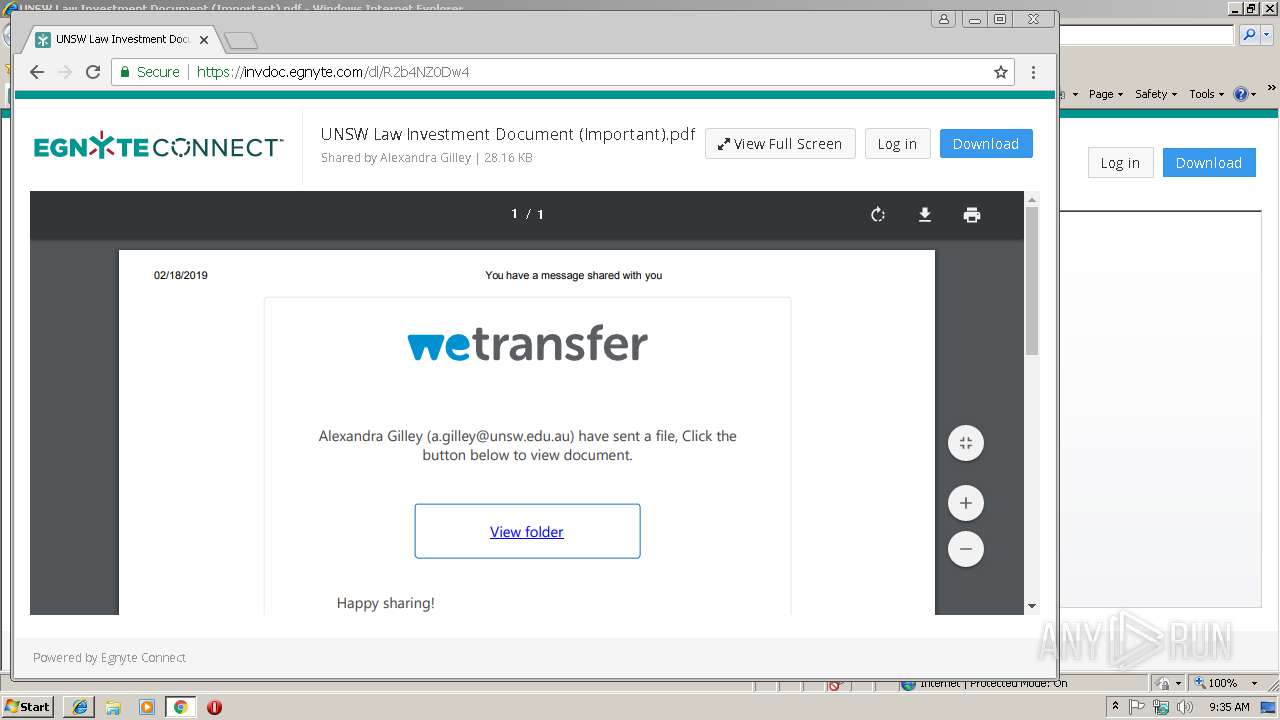
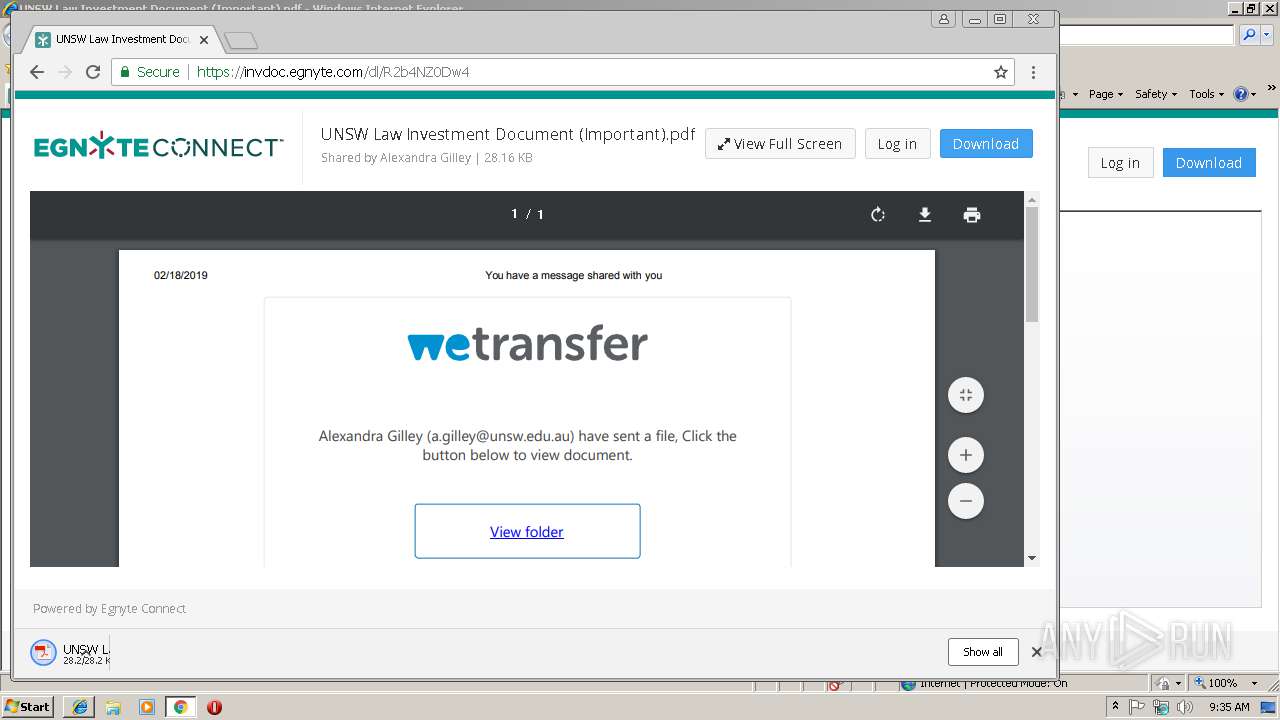
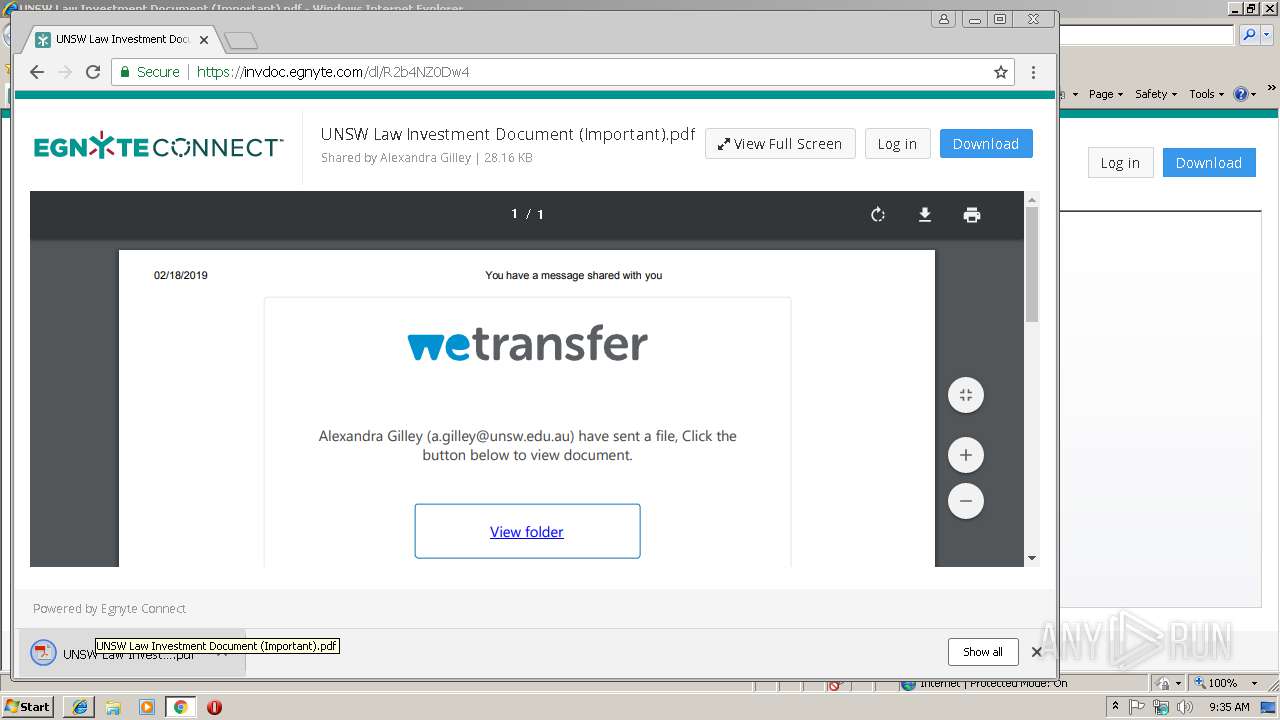
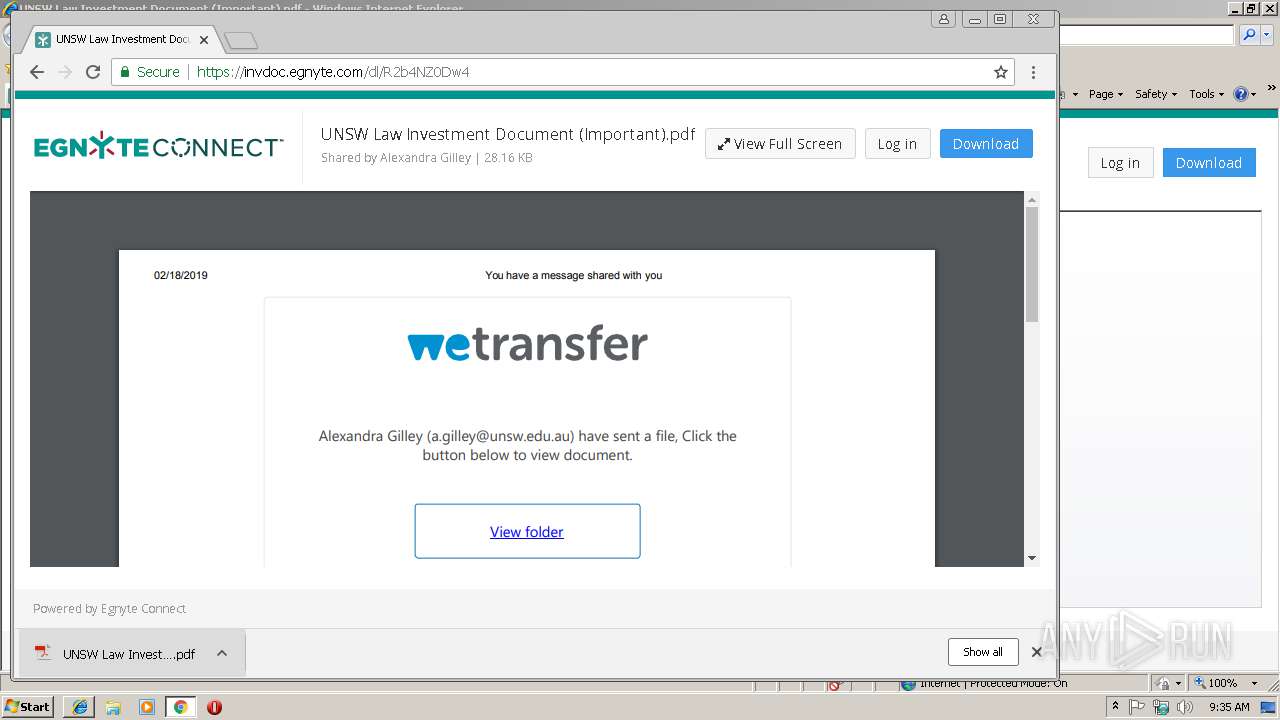
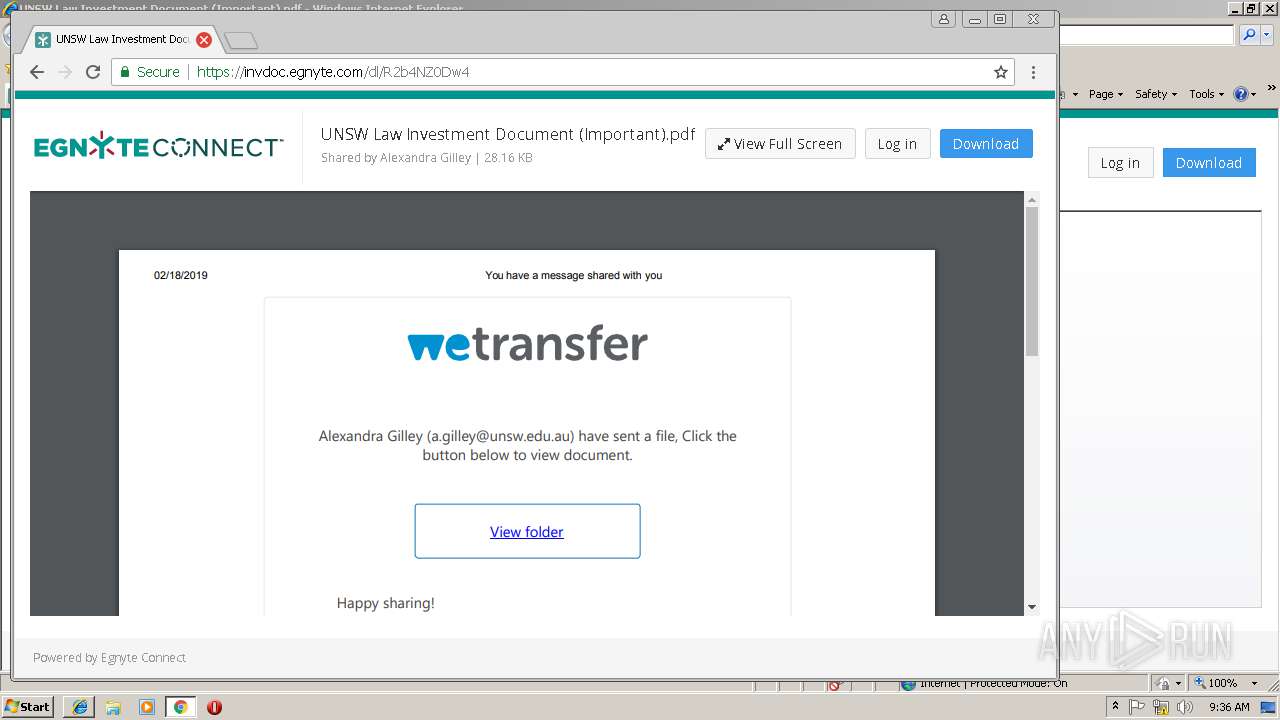
| URL: | https://invdoc.egnyte.com/dl/R2b4NZ0Dw4 |
| Full analysis: | https://app.any.run/tasks/0e896271-fb75-4873-a3b4-60e91c8502e1 |
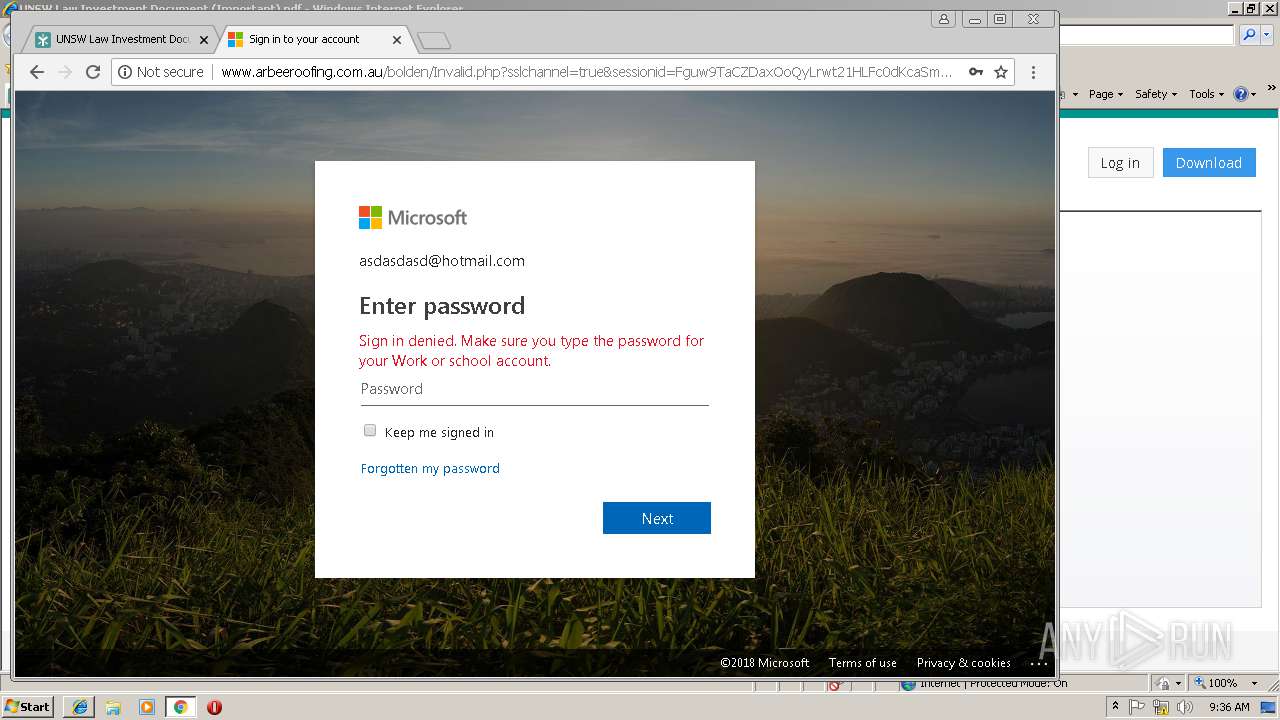
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 09:34:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8770F8C9155B90E8788ED1C34233E584 |
| SHA1: | 9513649A2B7B79327FD7A76ADEBDBD4D0BE63690 |
| SHA256: | EBEAC7F43906A07F06D53105E19B9C9915F3985B33572749453C3D04341633F3 |
| SSDEEP: | 3:N8ObLvxJ2H4:2ObaH4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3108)
- iexplore.exe (PID: 2956)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2596)
- iexplore.exe (PID: 3108)
- AcroRd32.exe (PID: 2216)
- iexplore.exe (PID: 2956)
Application launched itself
- AcroRd32.exe (PID: 2216)
- chrome.exe (PID: 2832)
Reads settings of System Certificates
- iexplore.exe (PID: 2956)
- chrome.exe (PID: 2832)
Reads internet explorer settings
- iexplore.exe (PID: 3108)
Changes internet zones settings
- iexplore.exe (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,16654425210609852955,14458137759534587774,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=80A7D5F94C7A615A3D6CD4B22E8B4F5D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=80A7D5F94C7A615A3D6CD4B22E8B4F5D --renderer-client-id=6 --mojo-platform-channel-handle=3780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,16654425210609852955,14458137759534587774,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=28997F89441DB85785E10076FEC6DDB8 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=28997F89441DB85785E10076FEC6DDB8 --renderer-client-id=12 --mojo-platform-channel-handle=4744 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3108 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,16654425210609852955,14458137759534587774,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=7BC6D3D814979CB6930ECB1502E4B222 --mojo-platform-channel-handle=4752 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3108 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | iexplore.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,16654425210609852955,14458137759534587774,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C0A765896EC40F18ECEB8D7386A38463 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C0A765896EC40F18ECEB8D7386A38463 --renderer-client-id=13 --mojo-platform-channel-handle=5116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,16654425210609852955,14458137759534587774,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=02EFD838A513D33A65F92C4BB228767F --mojo-platform-channel-handle=1480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2596 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,16654425210609852955,14458137759534587774,131072 --enable-features=PasswordImport --service-pipe-token=031F765CDD56177E968FD0EA5DE5CCFB --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=031F765CDD56177E968FD0EA5DE5CCFB --renderer-client-id=5 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=948,16654425210609852955,14458137759534587774,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=761505635B10D799AB27052F6A7E26E5 --mojo-platform-channel-handle=4324 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 300
Read events
1 122
Write events
171
Delete events
7
Modification events
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {61934833-3360-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307020001001200090022001B007601 | |||
Executable files
0
Suspicious files
91
Text files
168
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\R2b4NZ0Dw4[1].txt | — | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\jquery-1.7.2[1].js | text | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\font-awesome.min[1].css | text | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\BaseUtilities[1].js | text | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@egnyte[1].txt | text | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\swfobject_src[1].js | text | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ba-debug.min[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
71
DNS requests
33
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
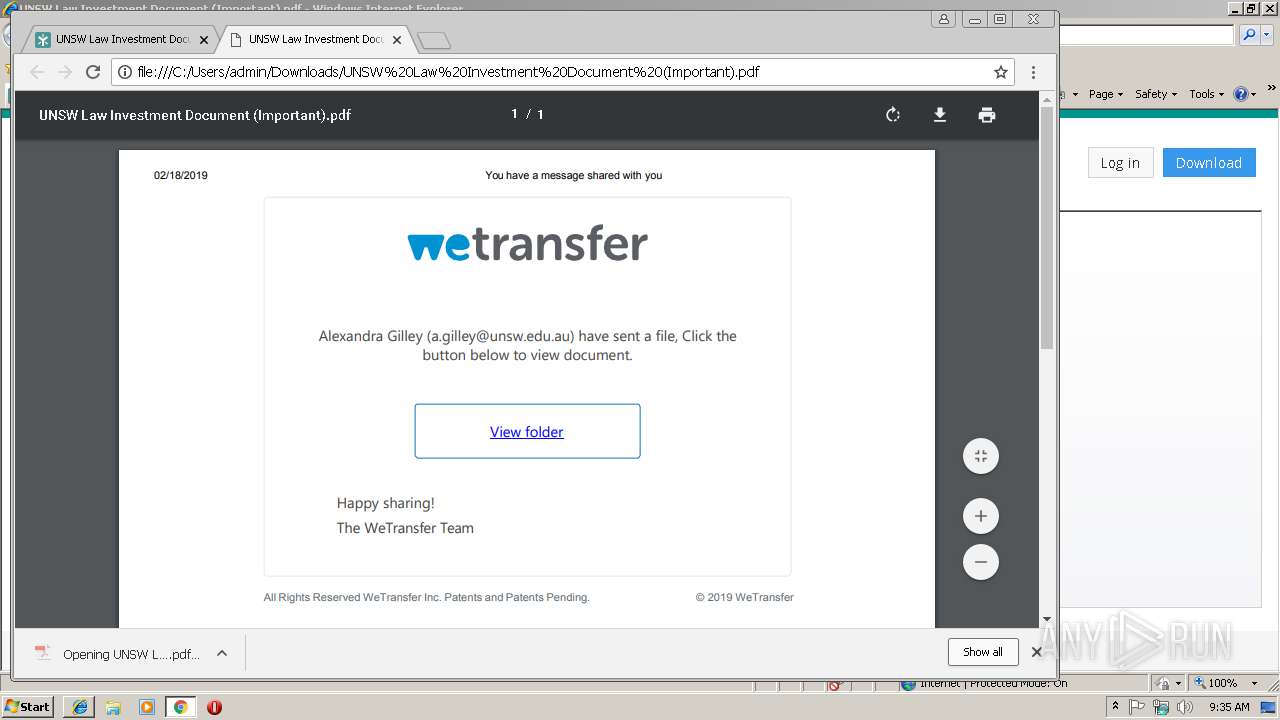
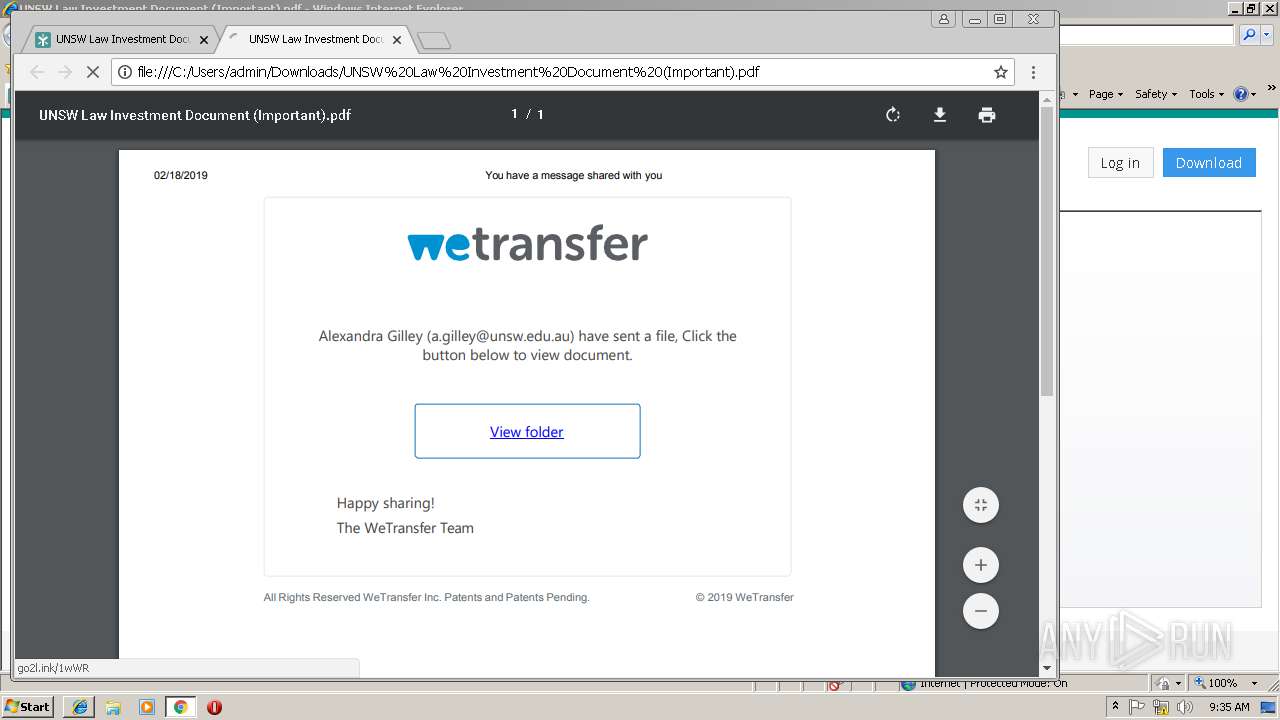
3108 | iexplore.exe | GET | — | 184.168.131.241:80 | http://go2l.ink/1wWR | US | — | — | shared |
2832 | chrome.exe | GET | 302 | 184.168.131.241:80 | http://go2l.ink/1wWR | US | — | — | shared |
2216 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/282_15_23_20070.zip | unknown | — | — | whitelisted |
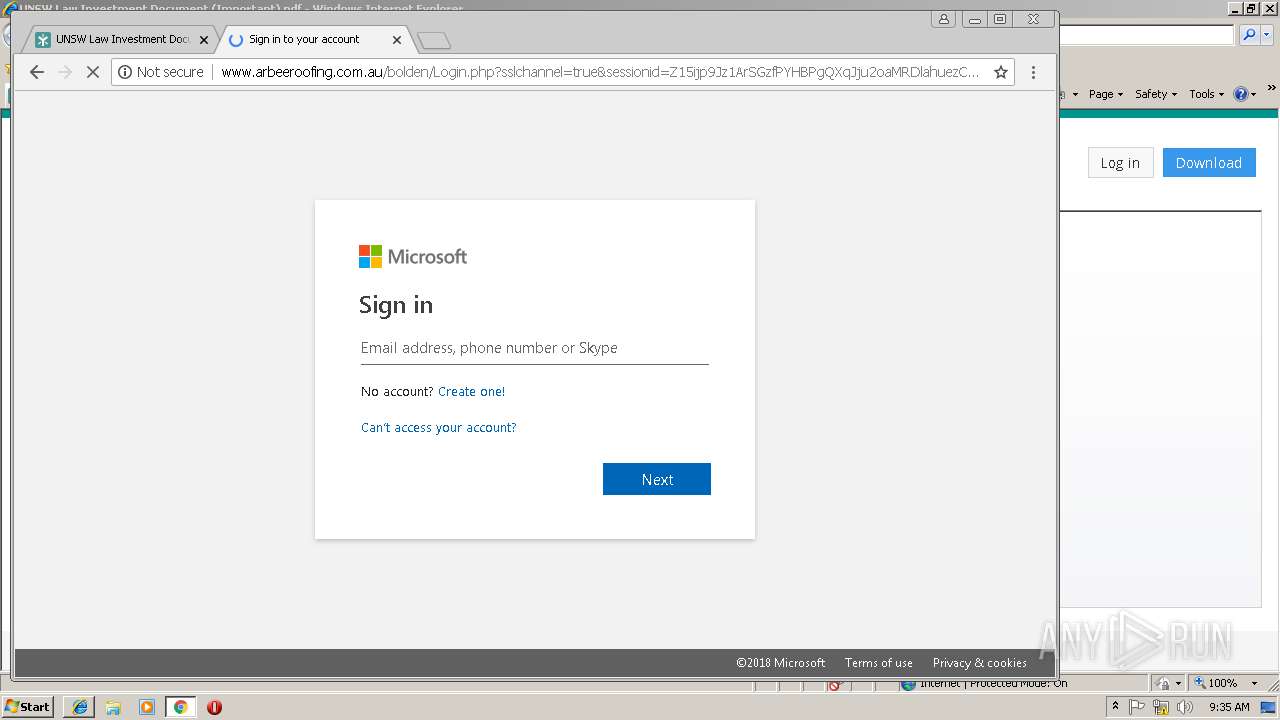
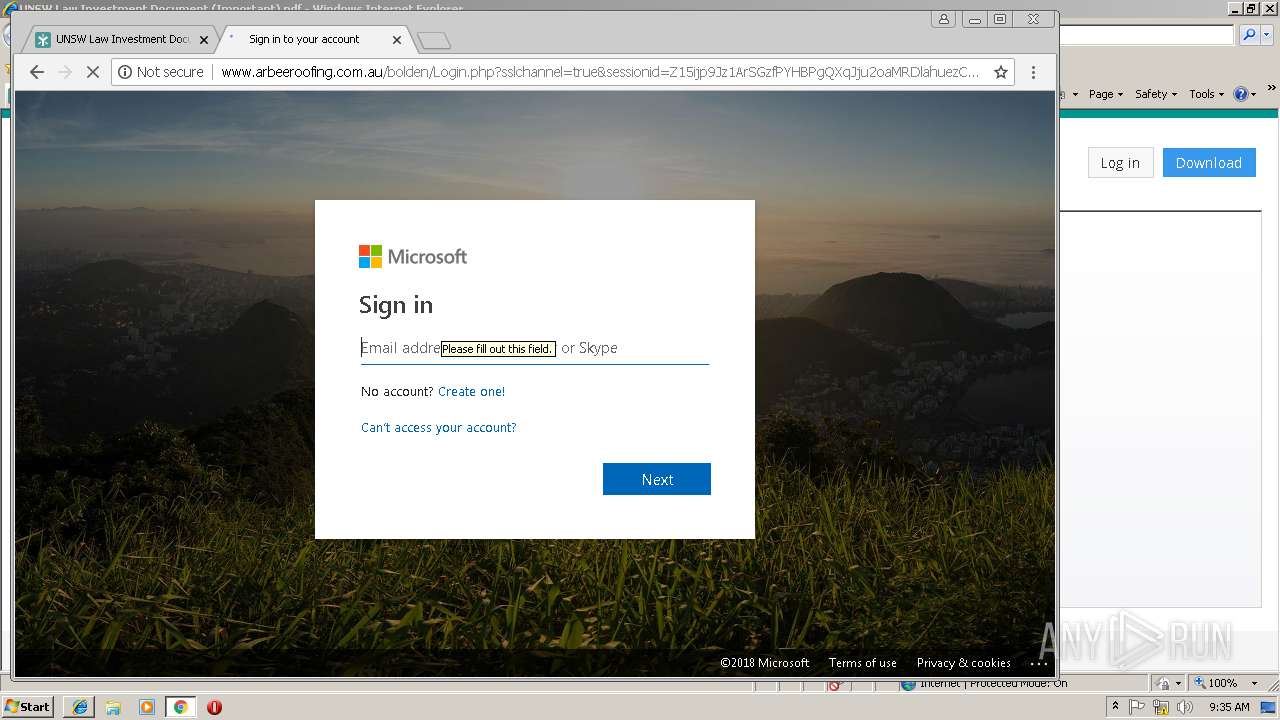
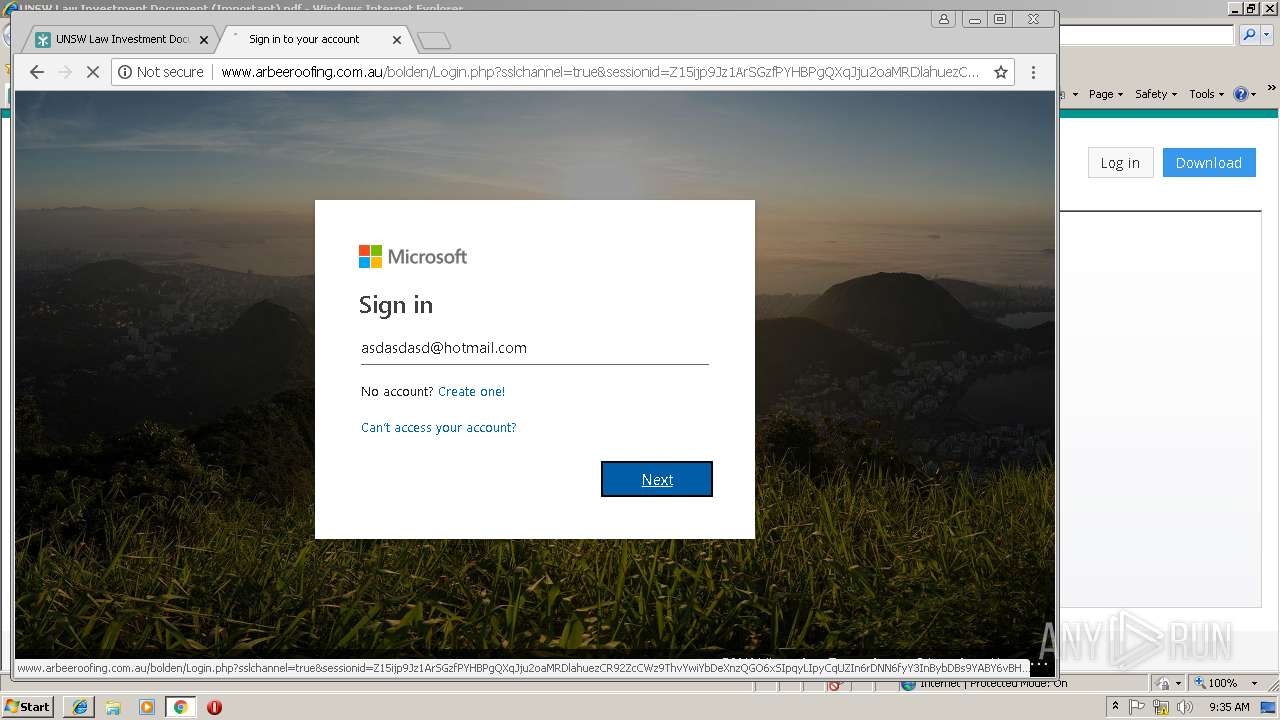
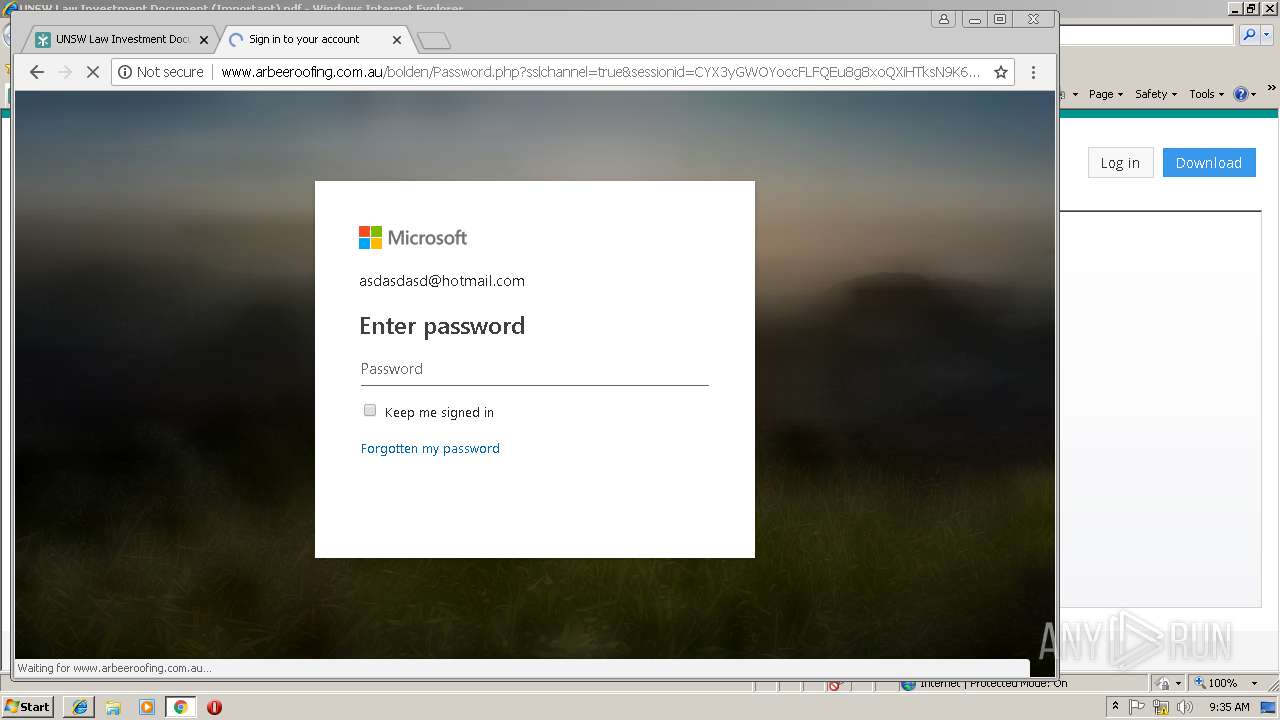
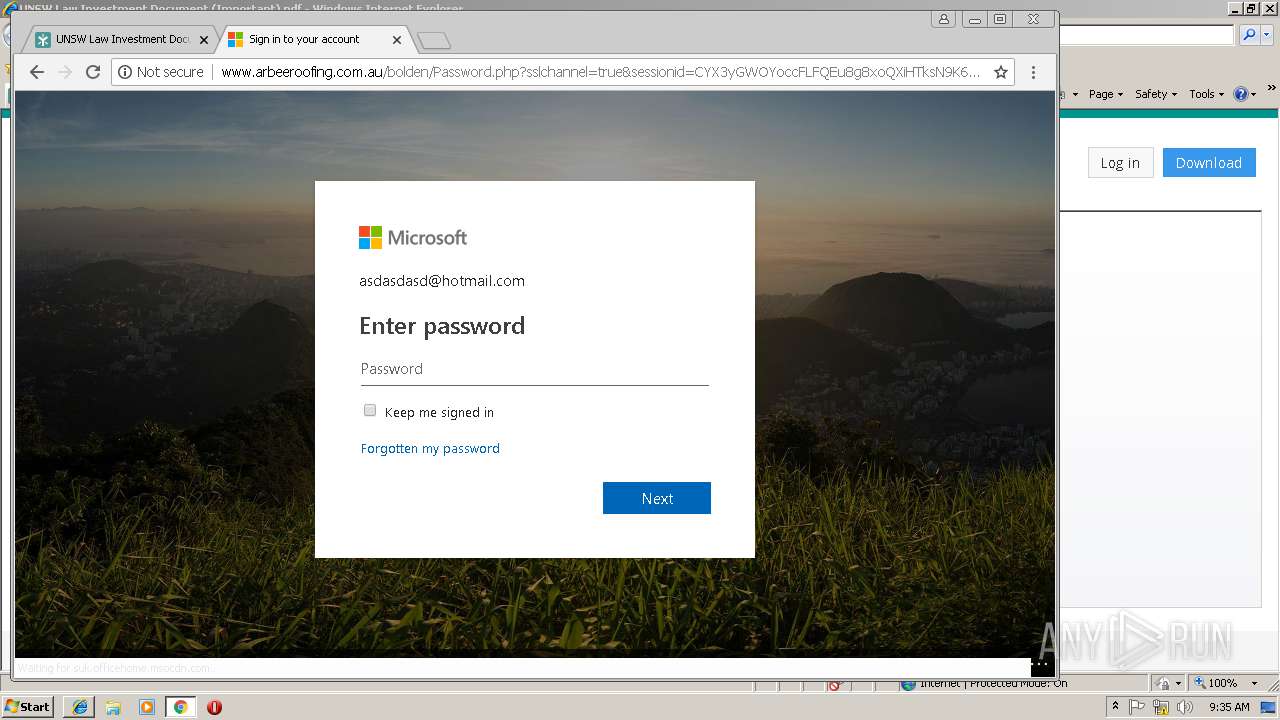
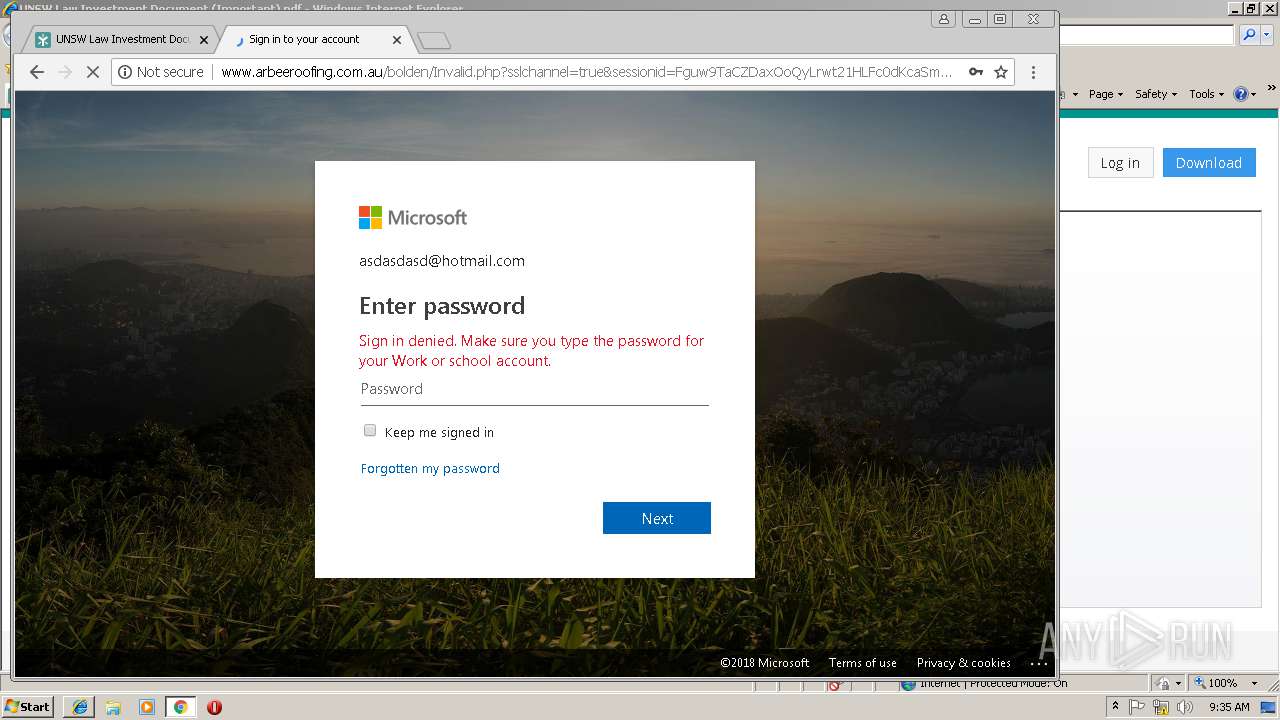
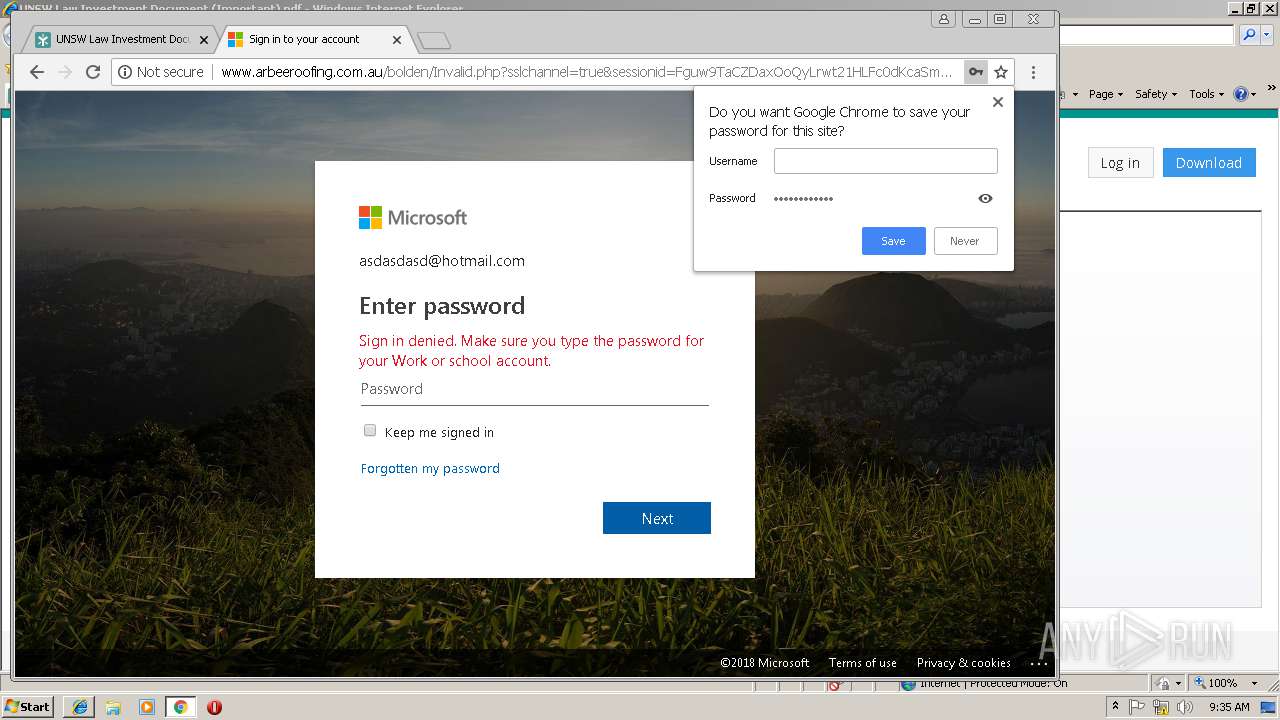
2832 | chrome.exe | GET | 200 | 27.121.64.87:80 | http://www.arbeeroofing.com.au/bolden/assets/files/prefetch_data/share.htm | AU | html | 291 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 27.121.64.87:80 | http://www.arbeeroofing.com.au/bolden/Login.php?sslchannel=true&sessionid=Z15ijp9Jz1ArSGzfPYHBPgQXqJju2oaMRDlahuezCR92ZcCWz9ThvYwiYbDeXnzQGO6xSIpqyLIpyCqUZIn6rDNN6fyY3InBybDBs9YABY6vBHceQsEYoVqfMLvKNE5CgB | AU | html | 20.4 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 27.121.64.87:80 | http://www.arbeeroofing.com.au/bolden/ | AU | html | 254 b | suspicious |
2832 | chrome.exe | GET | 200 | 27.121.64.87:80 | http://www.arbeeroofing.com.au/bolden/assets/files/prefetch.htm | AU | html | 2.56 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 27.121.64.87:80 | http://www.arbeeroofing.com.au/bolden/assets/files/converged.css | AU | text | 99.8 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 27.121.64.87:80 | http://www.arbeeroofing.com.au/bolden/assets/files/prefetch_data/prefetch.htm | AU | html | 3.23 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 27.121.64.87:80 | http://www.arbeeroofing.com.au/bolden/assets/files/prefetch_data/staticStylesFluent.css | AU | text | 41.4 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3108 | iexplore.exe | 208.83.110.20:443 | invdoc.egnyte.com | Bloomip Inc. | US | unknown |
2956 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3108 | iexplore.exe | 216.58.210.8:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
2956 | iexplore.exe | 208.83.110.20:443 | invdoc.egnyte.com | Bloomip Inc. | US | unknown |
3108 | iexplore.exe | 151.101.2.110:443 | js-agent.newrelic.com | Fastly | US | suspicious |
3108 | iexplore.exe | 162.247.242.20:443 | bam.nr-data.net | New Relic | US | whitelisted |
3108 | iexplore.exe | 130.211.5.208:443 | cdn.mxpnl.com | Google Inc. | US | whitelisted |
3108 | iexplore.exe | 130.211.34.183:443 | api.mixpanel.com | Google Inc. | US | whitelisted |
2216 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
3108 | iexplore.exe | 184.168.131.241:80 | go2l.ink | GoDaddy.com, LLC | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
invdoc.egnyte.com |
| unknown |
ssl.google-analytics.com |
| whitelisted |
js-agent.newrelic.com |
| whitelisted |
bam.nr-data.net |
| whitelisted |
cdn.mxpnl.com |
| whitelisted |
api.mixpanel.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
go2l.ink |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2832 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
2832 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
3 ETPRO signatures available at the full report