| download: | electrum-3.2.2.exe |
| Full analysis: | https://app.any.run/tasks/7b47fc9e-df27-4637-999b-5873f5a96965 |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2018, 19:31:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B6D5D920150CD96BC8B5FE17D64C6AED |
| SHA1: | C52AB3C5C5D2BBDA8C2680C81A0620F762F83771 |
| SHA256: | EBC558C80086DD2D1396E055655B00CD76E32D1AEB24BAC2BADA1EFBF9A78B37 |
| SSDEEP: | 393216:qgoNPaR7Uwyw5nX/46cZRiCWvLnmZZ5H1sPUNr62oYaC9AxE8:qgsQ5ywt/cXO4vN+j7C96E8 |
MALICIOUS
Loads dropped or rewritten executable
- electrum-3.2.2.exe (PID: 3480)
SUSPICIOUS
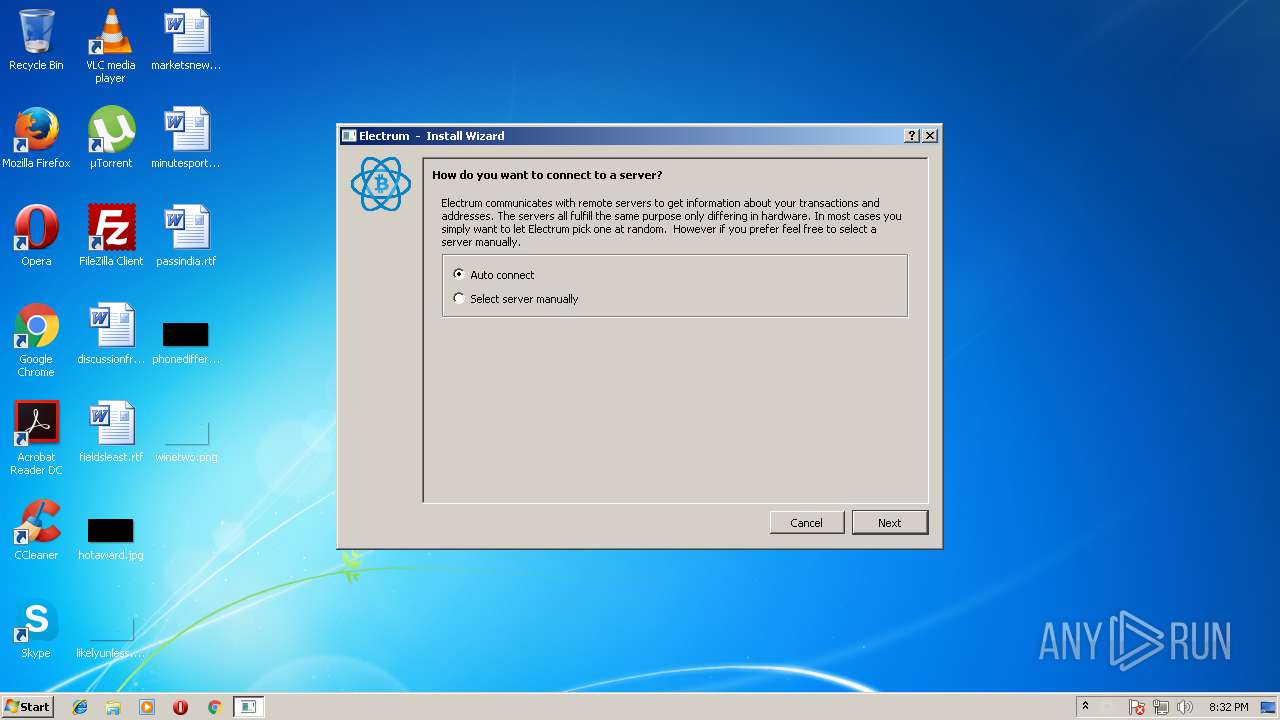
Application launched itself
- electrum-3.2.2.exe (PID: 2608)
Connects to unusual port
- electrum-3.2.2.exe (PID: 3480)
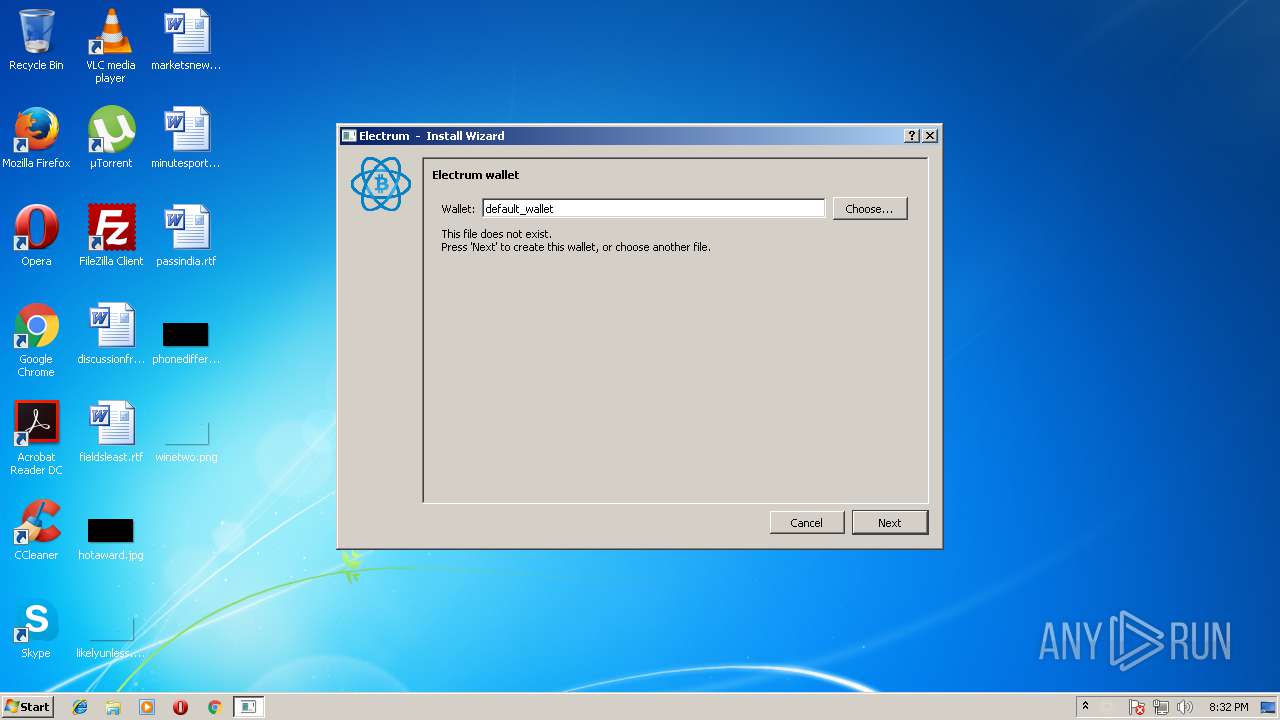
Creates files in the user directory
- electrum-3.2.2.exe (PID: 3480)
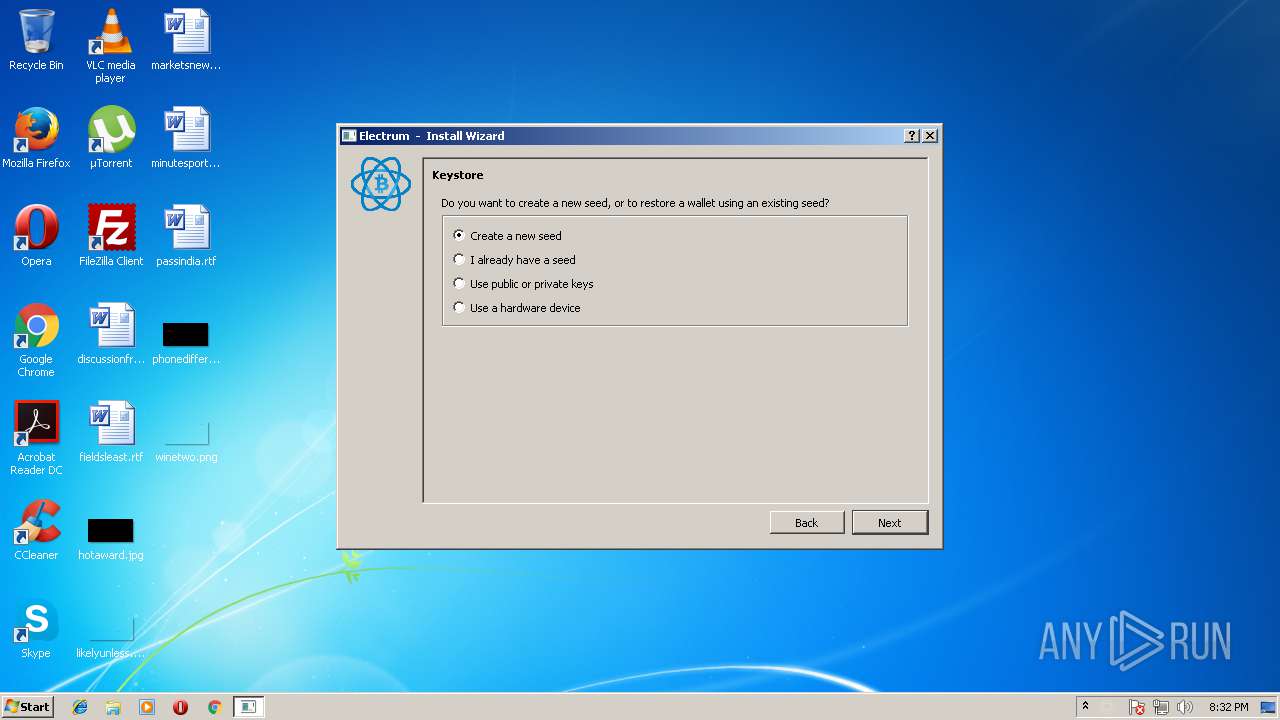
Executable content was dropped or overwritten
- electrum-3.2.2.exe (PID: 2608)
INFO
Reads settings of System Certificates
- electrum-3.2.2.exe (PID: 3480)
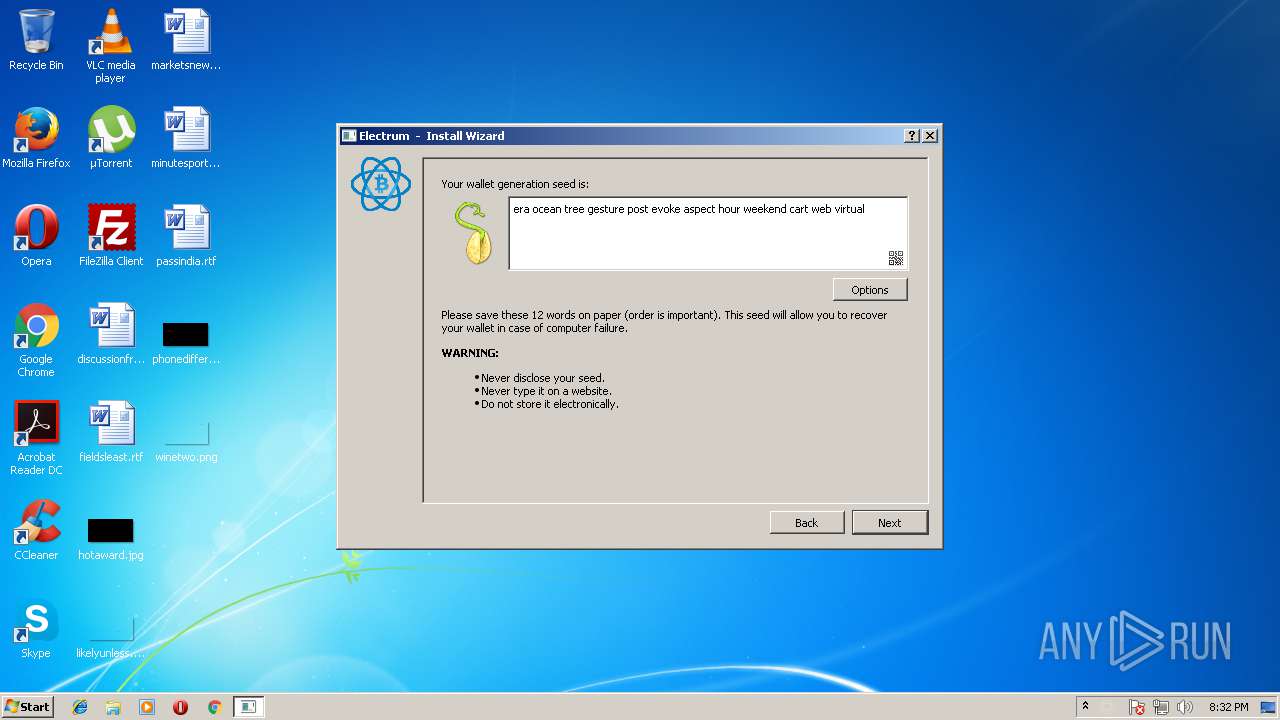
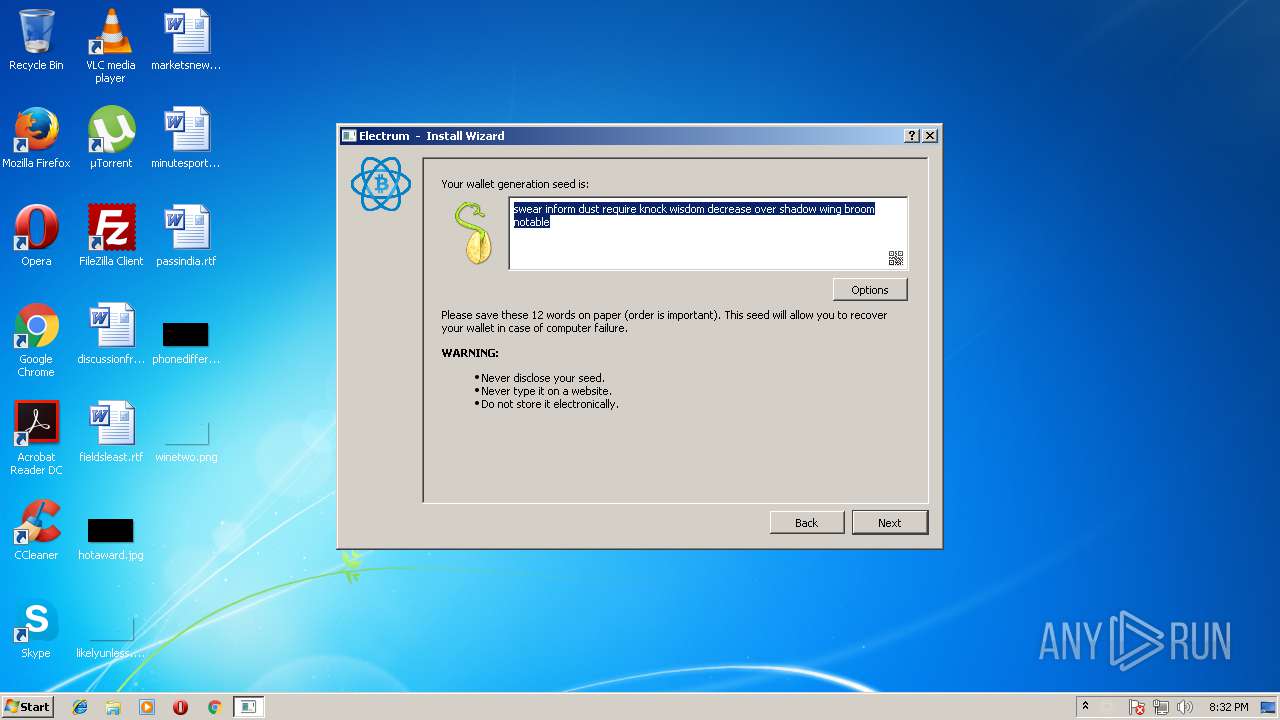
Dropped object may contain Bitcoin addresses
- electrum-3.2.2.exe (PID: 2608)
Dropped object may contain URL's
- electrum-3.2.2.exe (PID: 2608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x7873 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 107520 |
| CodeSize: | 125440 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2017:07:31 17:20:53+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Jul-2017 15:20:53 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 31-Jul-2017 15:20:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001E9D4 | 0x0001EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65368 |
.rdata | 0x00020000 | 0x0000B0C2 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.08353 |
.data | 0x0002C000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.93069 |
.gfids | 0x0003B000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.82553 |
.rsrc | 0x0003C000 | 0x0000D000 | 0x0000CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.159 |
.reloc | 0x00049000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.63681 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.90294 | 146 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 | 1.734 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 1.15935 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.17452 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.65167 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.47831 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.52336 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.66811 | 1640 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 2.80722 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 3.20642 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
34
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2608 | "C:\Users\admin\AppData\Local\Temp\electrum-3.2.2.exe" | C:\Users\admin\AppData\Local\Temp\electrum-3.2.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3480 | "C:\Users\admin\AppData\Local\Temp\electrum-3.2.2.exe" | C:\Users\admin\AppData\Local\Temp\electrum-3.2.2.exe | electrum-3.2.2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
246
Read events
246
Write events
0
Delete events
0
Modification events
Executable files
72
Suspicious files
1
Text files
122
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_Salsa20.cp35-win32.pyd | executable | |
MD5:2A5055C6420A61AB61215021E03E35A2 | SHA256:3B4034A5820789F2CF95F7D1A897506F192F947BBDCC29063D229CCAECE07FE4 | |||
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_raw_blowfish.cp35-win32.pyd | executable | |
MD5:A8AF77DC6220FFCF2CE587156C92C895 | SHA256:492D3578513D6909F789035F4A5E57FB610C8309DA8EAA9F2E9F9734EA386CEE | |||
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_ARC4.cp35-win32.pyd | executable | |
MD5:1E3057CCE21458FC4FD78829D653A63B | SHA256:99257DE88269000F1579945FC1B59A3598C84AD2285B6B91C732FBF933BE0224 | |||
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_raw_aes.cp35-win32.pyd | executable | |
MD5:9A3154EC289480E9DA0F9F61ABE5BE8B | SHA256:08B3CF0459A9A540EDAE163FD6B1791CAC07DD91226DA87CEA424BBC413AC854 | |||
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_raw_cast.cp35-win32.pyd | executable | |
MD5:CAE9BF8586B8AE02AE10980A6EEB8BC8 | SHA256:C2B27043DE869027830039AAF5A69E237404AF7729736E8F01BE42C5B4A808DD | |||
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_raw_arc2.cp35-win32.pyd | executable | |
MD5:79D38A6A61DBA2165F191A05BE7BD2CE | SHA256:98C71019461F56852EBA4A390A1FFDEF37DF7F22EBC3E81A9060B6E28E0F545D | |||
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_raw_aesni.cp35-win32.pyd | executable | |
MD5:7F46E7CA73FA4C753C9AB3B10410D5E3 | SHA256:F83813971AAC61D8C048BBCD46EF179A8C79F2E4DDE165FD550B570AC9AC8009 | |||
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_raw_cfb.cp35-win32.pyd | executable | |
MD5:912EE95EB10591A53125007BD8AE959C | SHA256:71AAF17F01EC2BADBD67EE526C2369300DFD028B74A352822A1FDAD019FB0FCC | |||
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_raw_cbc.cp35-win32.pyd | executable | |
MD5:22FB51A1EC7E7D0ACCBCBF1D03581E54 | SHA256:6985D882EA2852C721E5D6C1AD408AE2C99867B1316C2F7633A054CEECAFD259 | |||
| 2608 | electrum-3.2.2.exe | C:\Users\admin\AppData\Local\Temp\_MEI26082\Cryptodome\Cipher\_raw_ctr.cp35-win32.pyd | executable | |
MD5:4AEB30D1954B230EC32CE36F266019C0 | SHA256:2E94E1F111AFE0950BE85EB28CBF727313925F671446D94DF9429CDC5CA80740 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
36
DNS requests
16
Threats
12
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3480 | electrum-3.2.2.exe | 50.198.167.205:995 | btc.smsys.me | Comcast Cable Communications, LLC | US | unknown |
3480 | electrum-3.2.2.exe | 87.122.87.30:50002 | qmebr.spdns.org | 1&1 Versatel Deutschland GmbH | DE | unknown |
3480 | electrum-3.2.2.exe | 104.40.216.160:50002 | electrumx.westeurope.cloudapp.azure.com | Microsoft Corporation | NL | whitelisted |
3480 | electrum-3.2.2.exe | 84.200.105.74:50002 | daedalus.bauerj.eu | Accelerated IT Services GmbH | DE | unknown |
3480 | electrum-3.2.2.exe | 88.198.241.196:50002 | electrum.be | Hetzner Online GmbH | DE | unknown |
3480 | electrum-3.2.2.exe | 185.244.194.39:50002 | noserver4u.de | — | — | unknown |
3480 | electrum-3.2.2.exe | 208.110.73.107:50002 | us.electrum.be | WholeSale Internet, Inc. | US | unknown |
3480 | electrum-3.2.2.exe | 88.99.162.199:50002 | electrum.qtornado.com | Hetzner Online GmbH | DE | suspicious |
3480 | electrum-3.2.2.exe | 144.76.99.209:110 | ecdsa.net | Hetzner Online GmbH | DE | unknown |
3480 | electrum-3.2.2.exe | 78.46.103.75:443 | headers.electrum.org | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
btc.smsys.me |
| unknown |
qmebr.spdns.org |
| unknown |
electrumx.westeurope.cloudapp.azure.com |
| unknown |
daedalus.bauerj.eu |
| unknown |
electrum.be |
| malicious |
noserver4u.de |
| unknown |
us.electrum.be |
| unknown |
electrum.qtornado.com |
| suspicious |
ecdsa.net |
| unknown |
headers.electrum.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3480 | electrum-3.2.2.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 639 |
3480 | electrum-3.2.2.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3480 | electrum-3.2.2.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3480 | electrum-3.2.2.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3480 | electrum-3.2.2.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3480 | electrum-3.2.2.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3480 | electrum-3.2.2.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3480 | electrum-3.2.2.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3480 | electrum-3.2.2.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3480 | electrum-3.2.2.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |