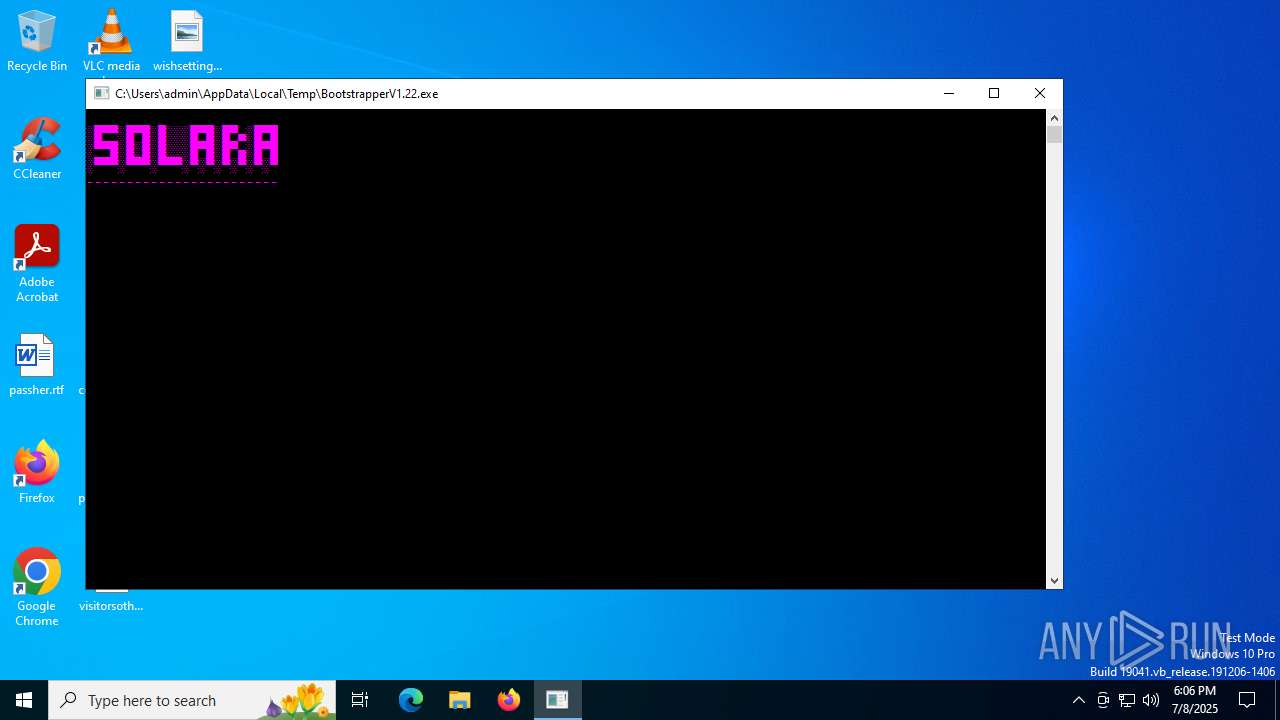
| File name: | BootstrapperV1.22.exe |
| Full analysis: | https://app.any.run/tasks/f05e131d-84ca-4ae5-9ace-071fe3583b32 |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 18:06:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A4DCF20B82896BE94EB538260C5FB93 |
| SHA1: | 21F232C2FD8132F8677E53258562AD98B455E679 |
| SHA256: | EBBCB489171ABFCFCE56554DBAEACD22A15838391CBC7C756DB02995129DEF5A |
| SSDEEP: | 6144:LQ3tXkS2NIikH1izJZ3e82Zavp/ijHrGEW1IhThuENaDffKTghOpDozwKdVuaQ:LiMIikViCocauhu6TghOpDkwKdw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- BootstrapperV1.22.exe (PID: 3908)
Uses WMIC.EXE to obtain information about the network interface controller
- cmd.exe (PID: 7160)
Reads the date of Windows installation
- BootstrapperV1.22.exe (PID: 3908)
Reads security settings of Internet Explorer
- BootstrapperV1.22.exe (PID: 3908)
- BootstrapperV2.23.exe (PID: 6388)
- MicrosoftEdgeUpdate.exe (PID: 4236)
Executable content was dropped or overwritten
- BootstrapperV1.22.exe (PID: 3908)
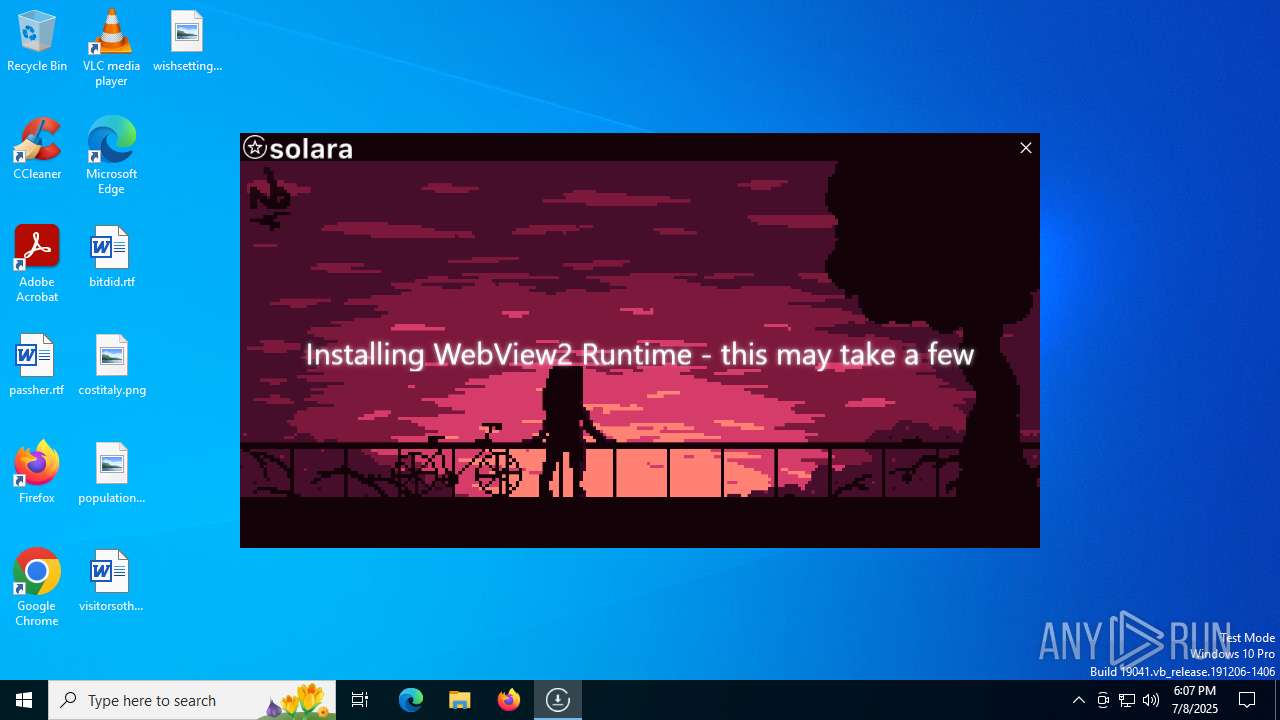
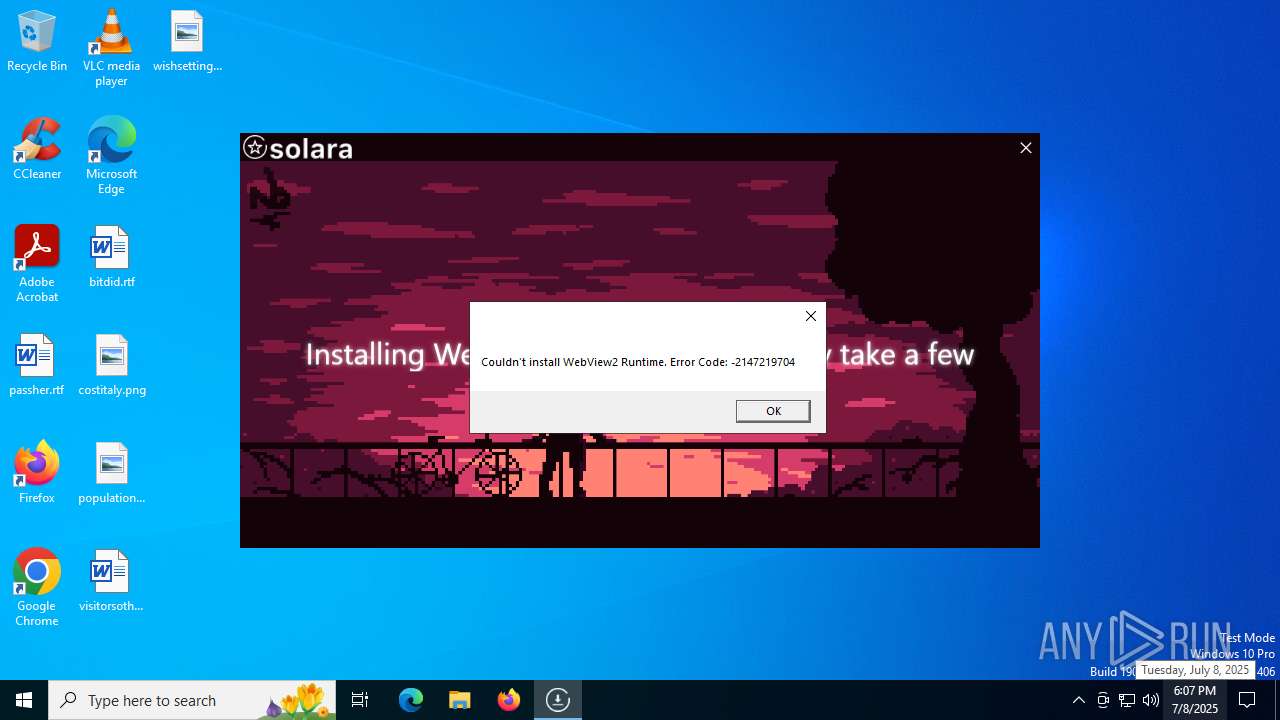
- MicrosoftEdgeWebview2Setup.exe (PID: 7020)
- BootstrapperV2.23.exe (PID: 6388)
Process drops legitimate windows executable
- MicrosoftEdgeWebview2Setup.exe (PID: 7020)
- BootstrapperV2.23.exe (PID: 6388)
- MicrosoftEdgeUpdate.exe (PID: 4236)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 7020)
- MicrosoftEdgeUpdate.exe (PID: 4236)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 4236)
INFO
Checks supported languages
- BootstrapperV1.22.exe (PID: 3908)
- BootstrapperV2.23.exe (PID: 6388)
- MicrosoftEdgeWebview2Setup.exe (PID: 7020)
- MicrosoftEdgeUpdate.exe (PID: 4236)
Reads the computer name
- BootstrapperV1.22.exe (PID: 3908)
- BootstrapperV2.23.exe (PID: 6388)
- MicrosoftEdgeUpdate.exe (PID: 4236)
Reads the machine GUID from the registry
- BootstrapperV1.22.exe (PID: 3908)
- BootstrapperV2.23.exe (PID: 6388)
Checks proxy server information
- BootstrapperV1.22.exe (PID: 3908)
- BootstrapperV2.23.exe (PID: 6388)
- MicrosoftEdgeUpdate.exe (PID: 4236)
- wermgr.exe (PID: 3924)
Disables trace logs
- BootstrapperV1.22.exe (PID: 3908)
- BootstrapperV2.23.exe (PID: 6388)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1512)
Reads Environment values
- BootstrapperV1.22.exe (PID: 3908)
- BootstrapperV2.23.exe (PID: 6388)
- MicrosoftEdgeUpdate.exe (PID: 4236)
Reads the software policy settings
- BootstrapperV1.22.exe (PID: 3908)
- BootstrapperV2.23.exe (PID: 6388)
- wermgr.exe (PID: 3924)
- MicrosoftEdgeUpdate.exe (PID: 4236)
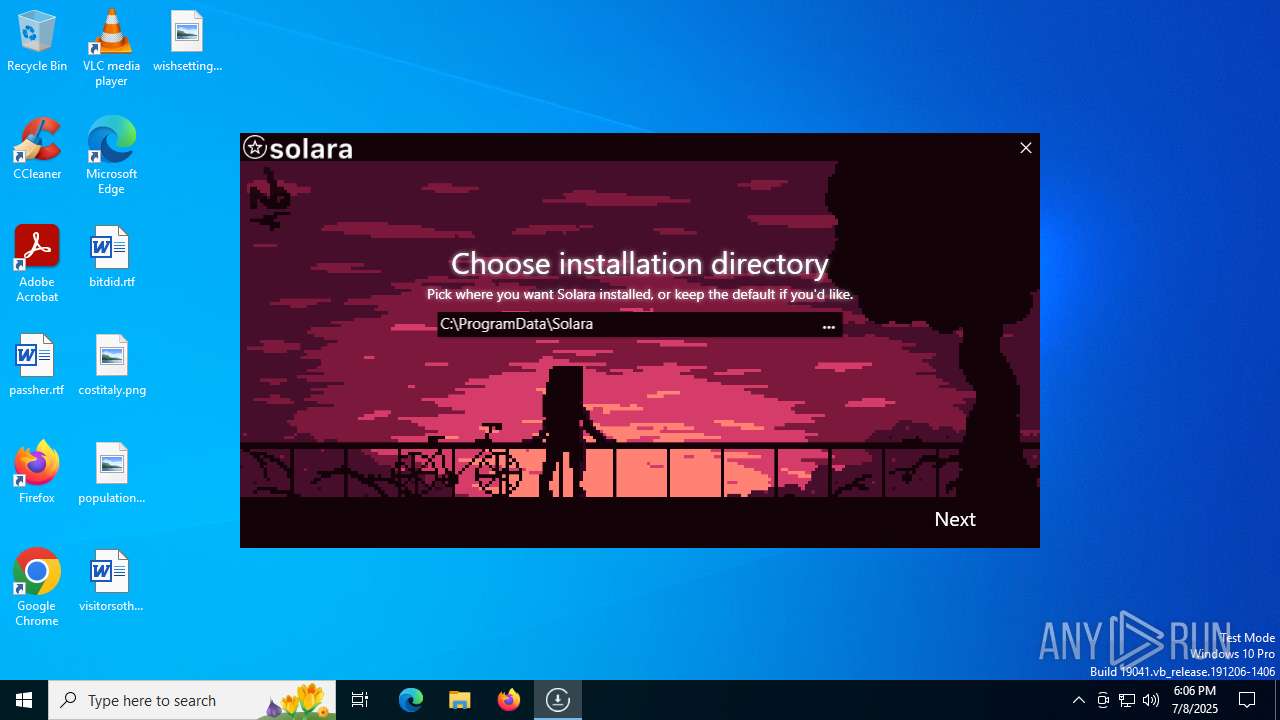
Create files in a temporary directory
- BootstrapperV1.22.exe (PID: 3908)
- BootstrapperV2.23.exe (PID: 6388)
Process checks computer location settings
- BootstrapperV1.22.exe (PID: 3908)
- MicrosoftEdgeUpdate.exe (PID: 4236)
Creates files in the program directory
- BootstrapperV2.23.exe (PID: 6388)
- MicrosoftEdgeWebview2Setup.exe (PID: 7020)
The sample compiled with english language support
- BootstrapperV2.23.exe (PID: 6388)
- MicrosoftEdgeWebview2Setup.exe (PID: 7020)
- MicrosoftEdgeUpdate.exe (PID: 4236)
Checks if a key exists in the options dictionary (POWERSHELL)
- BootstrapperV2.23.exe (PID: 6388)
Creates files or folders in the user directory
- wermgr.exe (PID: 3924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:10:04 22:29:32+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 816640 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc949a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
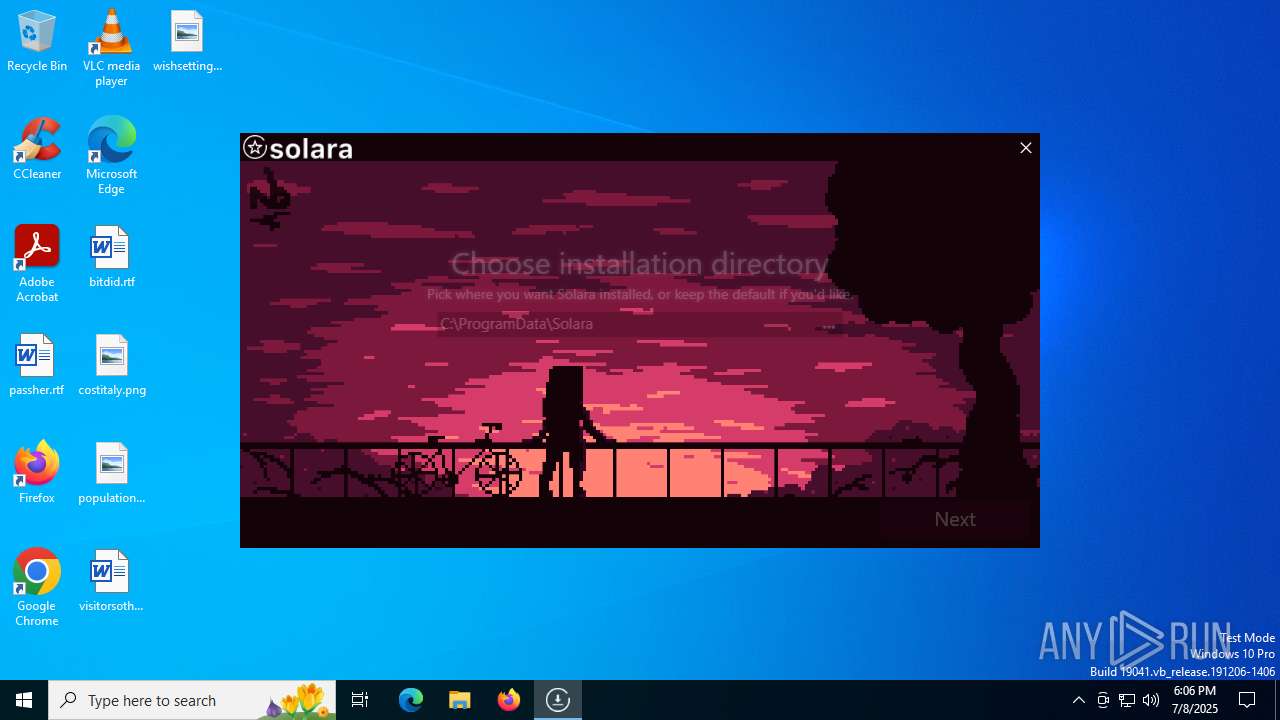
| FileDescription: | SolaraBootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | SolaraBootstrapper.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | SolaraBootstrapper.exe |
| ProductName: | SolaraBootstrapper |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
149
Monitored processes
11
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | BootstrapperV1.22.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | wmic nicconfig where (IPEnabled=TRUE) call SetDNSServerSearchOrder ("1.1.1.1", "1.0.0.1") | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3908 | "C:\Users\admin\AppData\Local\Temp\BootstrapperV1.22.exe" | C:\Users\admin\AppData\Local\Temp\BootstrapperV1.22.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SolaraBootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3924 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "4236" "1848" "1876" "1700" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\SysWOW64\wermgr.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4236 | "C:\Program Files (x86)\Microsoft\Temp\EUBE9D.tmp\MicrosoftEdgeUpdate.exe" /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Program Files (x86)\Microsoft\Temp\EUBE9D.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Exit code: 2147747592 Version: 1.3.195.61 Modules
| |||||||||||||||
| 4692 | "C:\Users\admin\AppData\Local\Temp\BootstrapperV1.22.exe" | C:\Users\admin\AppData\Local\Temp\BootstrapperV1.22.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SolaraBootstrapper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5496 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6388 | "C:\Users\admin\AppData\Local\Temp\BootstrapperV2.23.exe" --oldBootstrapper "C:\Users\admin\AppData\Local\Temp\BootstrapperV1.22.exe" --isUpdate true | C:\Users\admin\AppData\Local\Temp\BootstrapperV2.23.exe | BootstrapperV1.22.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Bootstrapper Version: 1.0.0.0 Modules
| |||||||||||||||
| 7020 | "C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe" /silent /install | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | — | BootstrapperV2.23.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Setup Exit code: 2147747592 Version: 1.3.195.61 Modules
| |||||||||||||||
Total events
13 732
Read events
13 670
Write events
60
Delete events
2
Modification events
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (3908) BootstrapperV1.22.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperV1_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
202
Suspicious files
4
Text files
7
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3908 | BootstrapperV1.22.exe | C:\Users\admin\AppData\Local\Temp\DISCORD | binary | |
MD5:43151972F36B756BB89CE08B7B8E1023 | SHA256:ABE3C8428FA463FEF24F4BD5280910E5C2CCB7ABCCE86E9EBBD93C6538DC0479 | |||
| 6388 | BootstrapperV2.23.exe | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | executable | |
MD5:5424BAC02DB3D21E75C21FF2049CD04F | SHA256:3C60FDBD71B468CF52FDE6F780740A910C9D190E7023B1AC1217D427D794CCB1 | |||
| 7020 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EUBE9D.tmp\MicrosoftEdgeUpdateOnDemand.exe | executable | |
MD5:B552E2C44C71C93E4AAE5411357BDE40 | SHA256:C6EA70D4372A37A6EE06B35C1F6E1B2668B39005FC2D71347BF6FD3BF680B316 | |||
| 3908 | BootstrapperV1.22.exe | C:\Users\admin\AppData\Local\Temp\BootstrapperV2.23.exe | executable | |
MD5:1974506038C5934399DE3C2F6C7544DE | SHA256:5BCC68604C4C4ADD6D592E0455156024E52FF10F9F06DAA1F543B005D7C2A53F | |||
| 6388 | BootstrapperV2.23.exe | C:\Users\admin\AppData\Local\Temp\CONFIG | binary | |
MD5:0284FA0391784125AD3B12BE8C92C6AE | SHA256:789075B8C810F2B63F86DD1F8B7BE836178AC679A32F2CB2376E013BC78C68C0 | |||
| 7020 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EUBE9D.tmp\MicrosoftEdgeUpdateComRegisterShell64.exe | executable | |
MD5:D65C7E1B579CD5ABA05D65D5FF0002AD | SHA256:5F2A785AEA8F1EAFD0B473722C95B1178A684734DA79BE28D3A445470F810062 | |||
| 6388 | BootstrapperV2.23.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ldqjjbe3.zva.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6388 | BootstrapperV2.23.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vvbh4to1.pre.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7020 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EUBE9D.tmp\MicrosoftEdgeUpdate.exe | executable | |
MD5:570D4E78E4EF679C9435247685F8A8D3 | SHA256:5CDF1C3C7F72120CA88145D38E48C9E1E6A6BD4EF43021193FD76D98D2F05496 | |||
| 7020 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EUBE9D.tmp\psuser.dll | executable | |
MD5:FBD300ADF6F745FEA1B8760ABC0EAE5A | SHA256:B0CEDF9965122280DF5E86955761ED5BACEA0A612412479786F075DEFBB82CE1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
33
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2524 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1328 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1328 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3924 | wermgr.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3924 | wermgr.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2200 | svchost.exe | 224.0.0.251:5353 | — | — | — | unknown |
2200 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1268 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3908 | BootstrapperV1.22.exe | 104.21.93.27:443 | getsolara.dev | CLOUDFLARENET | — | unknown |
2524 | svchost.exe | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
getsolara.dev |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO Packed Executable Download |