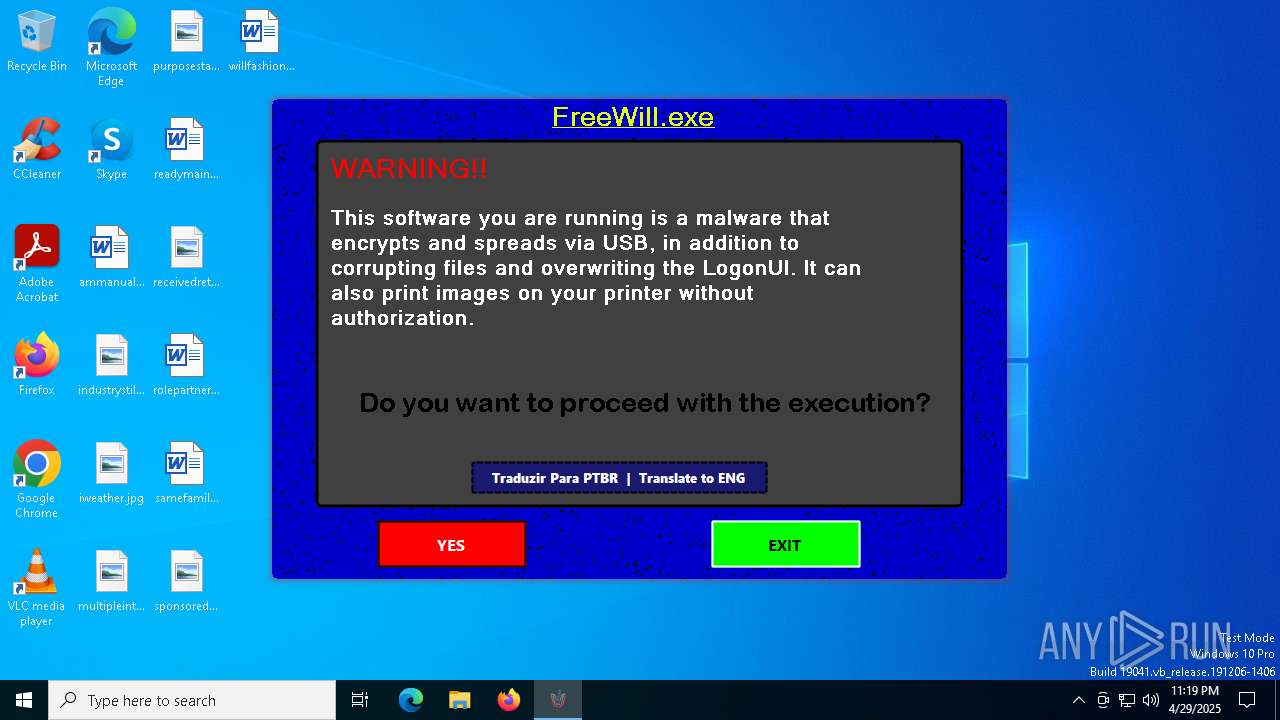
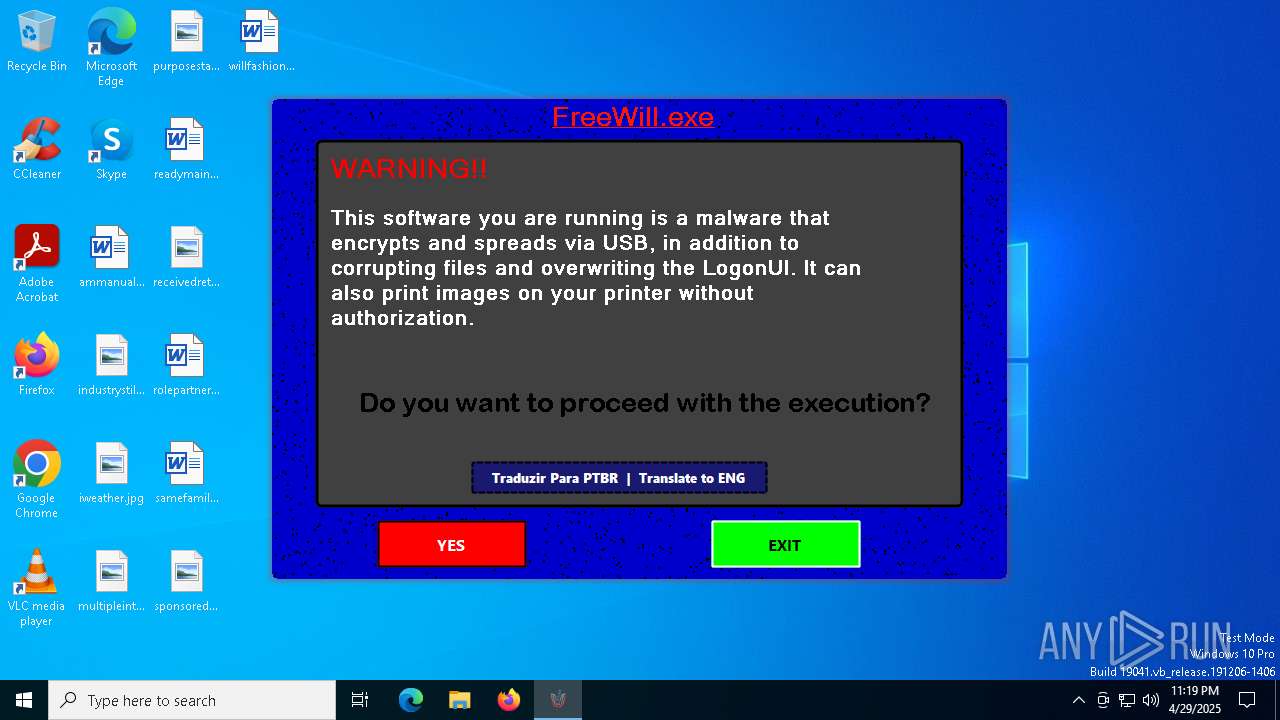
| File name: | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe |
| Full analysis: | https://app.any.run/tasks/5d9e6bc7-bd5e-4c46-9208-f95584f0d403 |
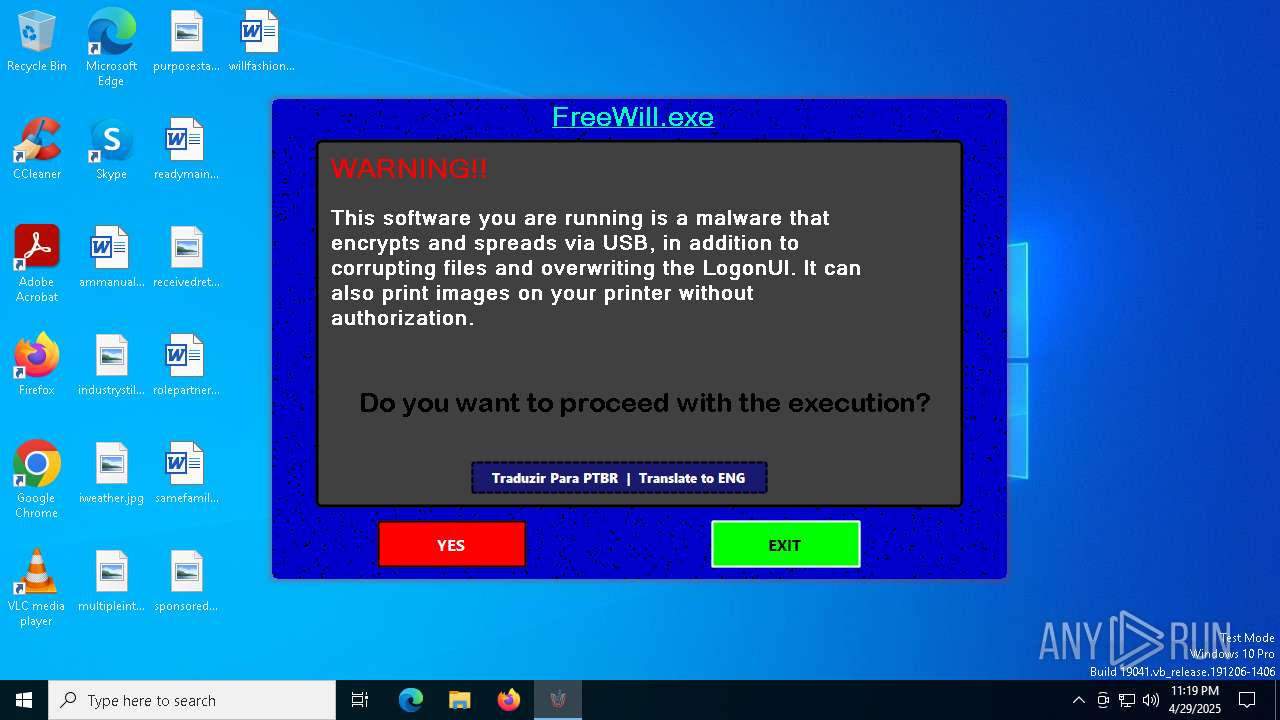
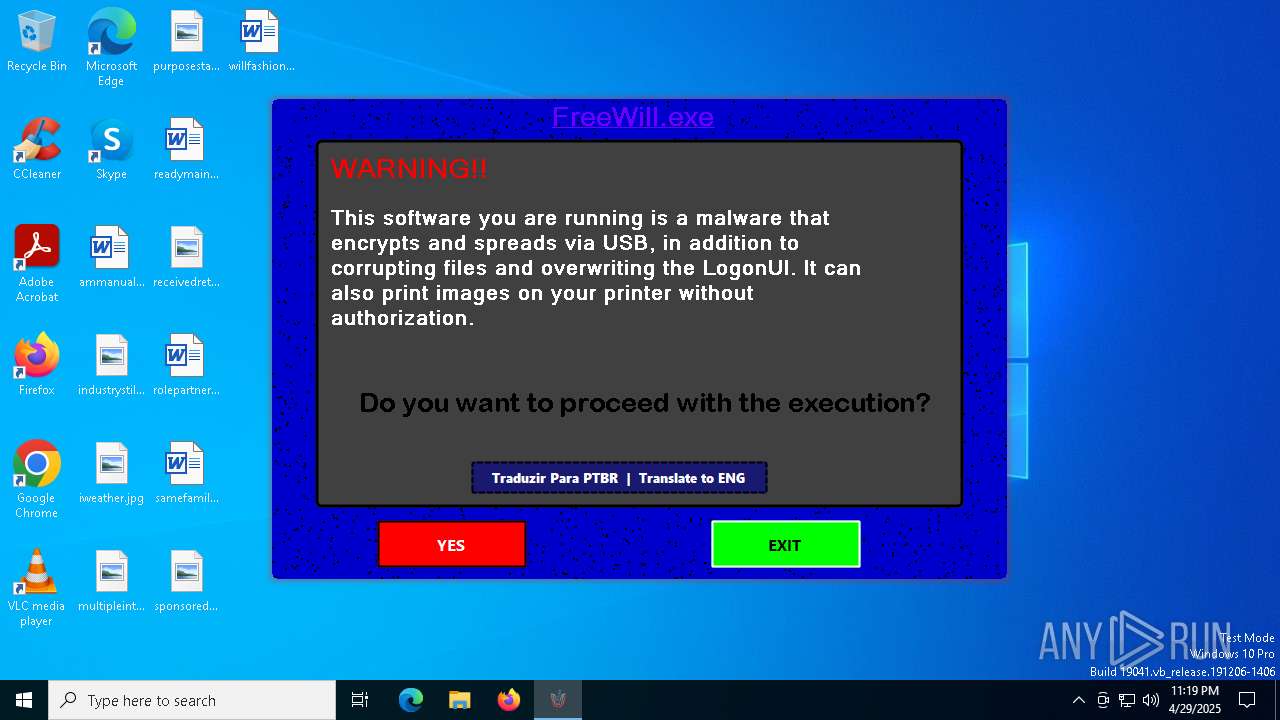
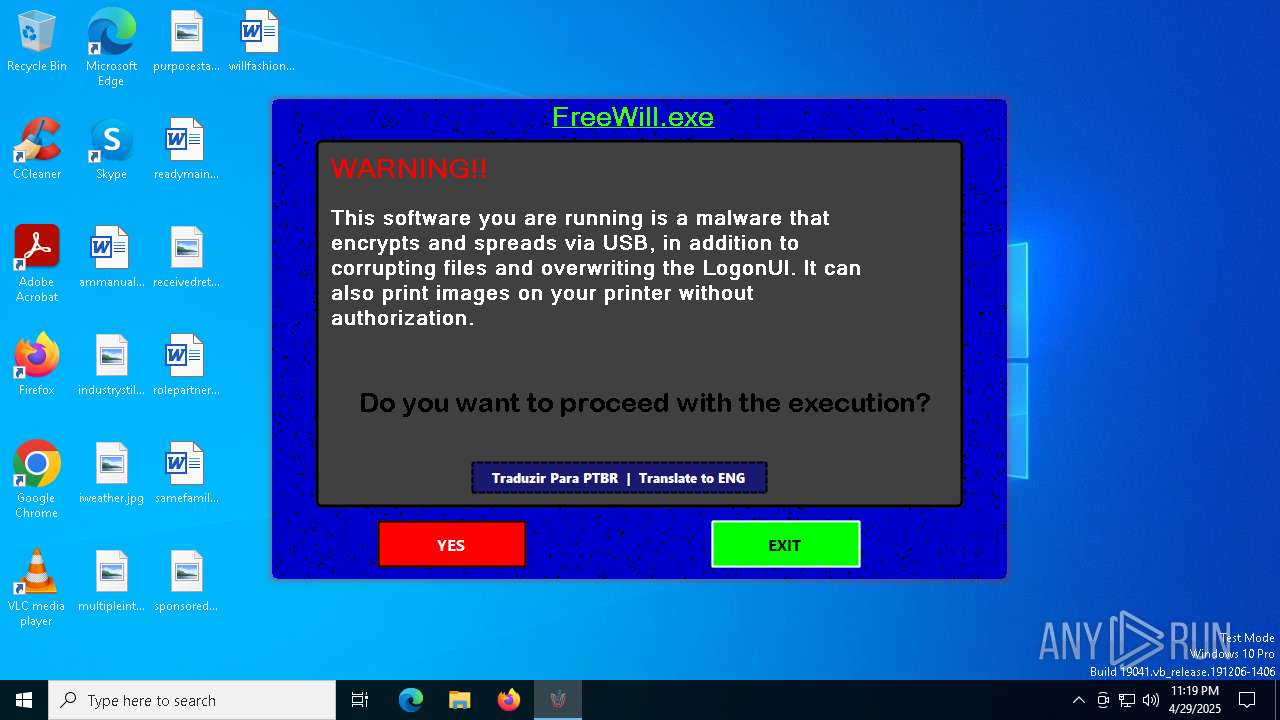
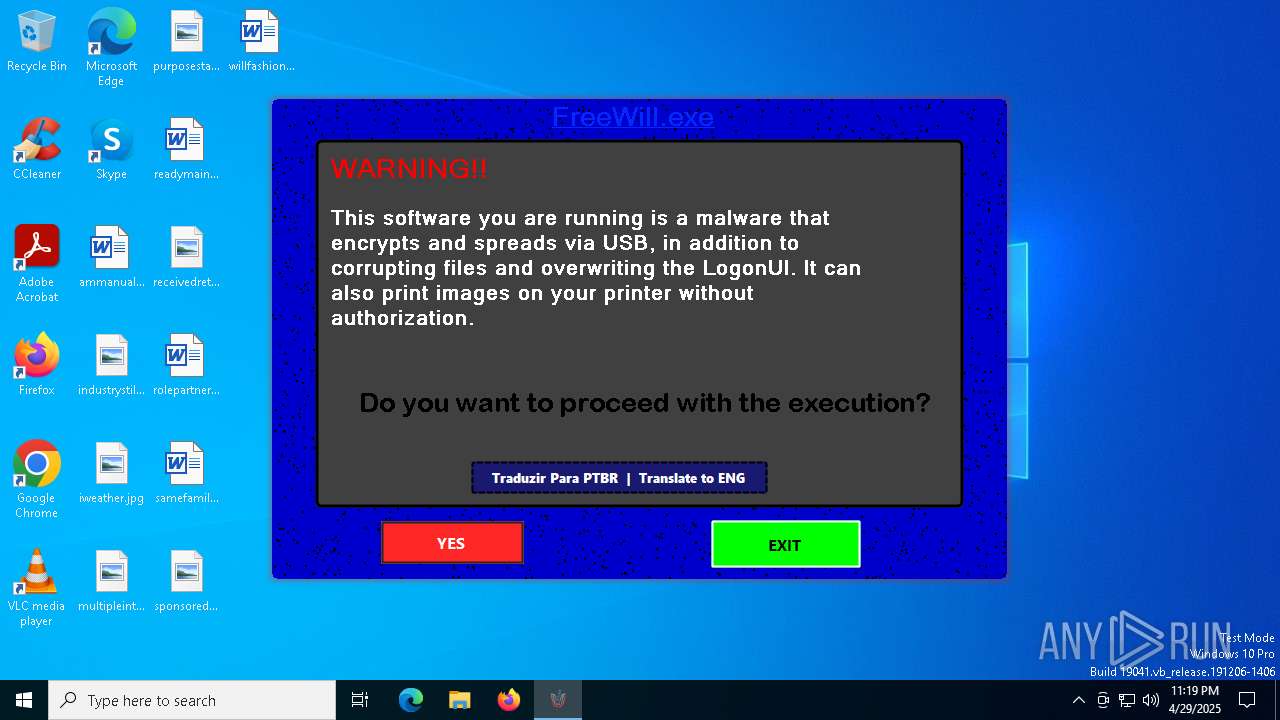
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 23:19:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 4318D93E4B3D3590F3B4C6C2CDD794F3 |
| SHA1: | 166C8A860D24671C6236944D32F5713A91449893 |
| SHA256: | EBBB8769086DCF3F7BDAF9366CF6A5AC4C5AC981E4BE3C69D08CE06FC80C2F28 |
| SSDEEP: | 98304:oluqhluqCrHjdyl+MW5Mq6X2kFIhDMlsUN0cPsZg5pyd4Ww2KZ2KGd/ezmcdrHjW:KQ |
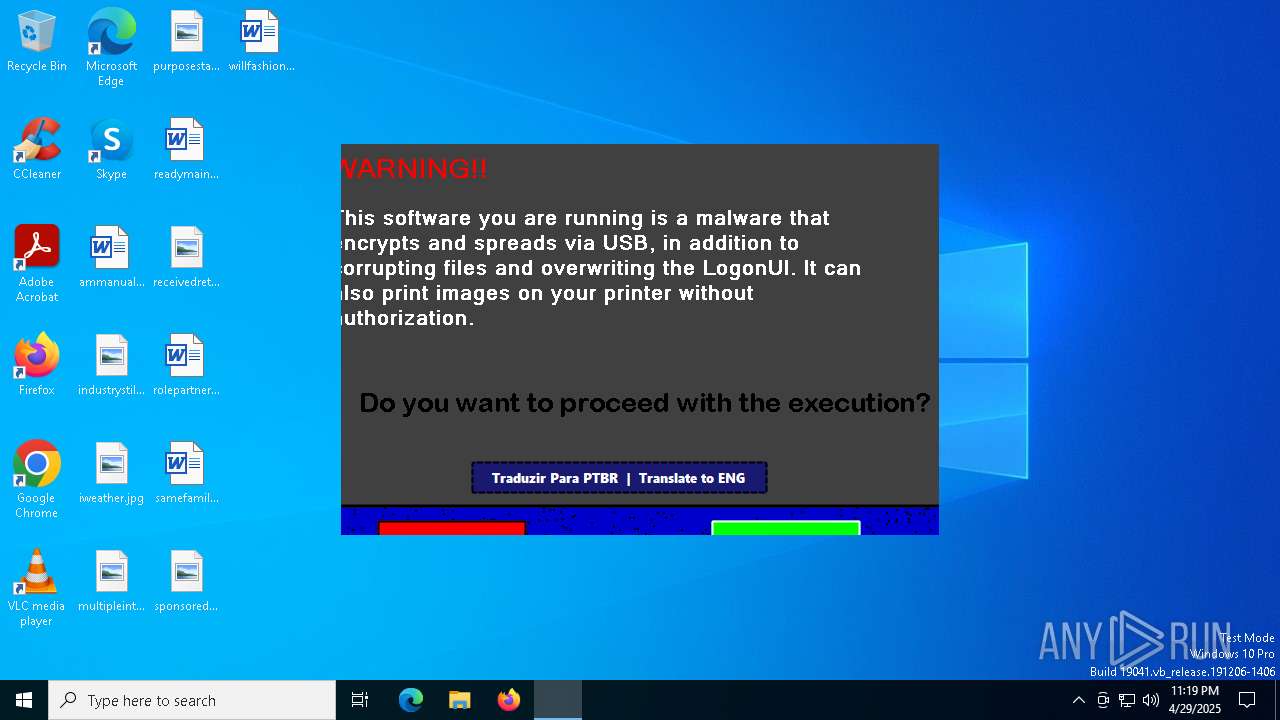
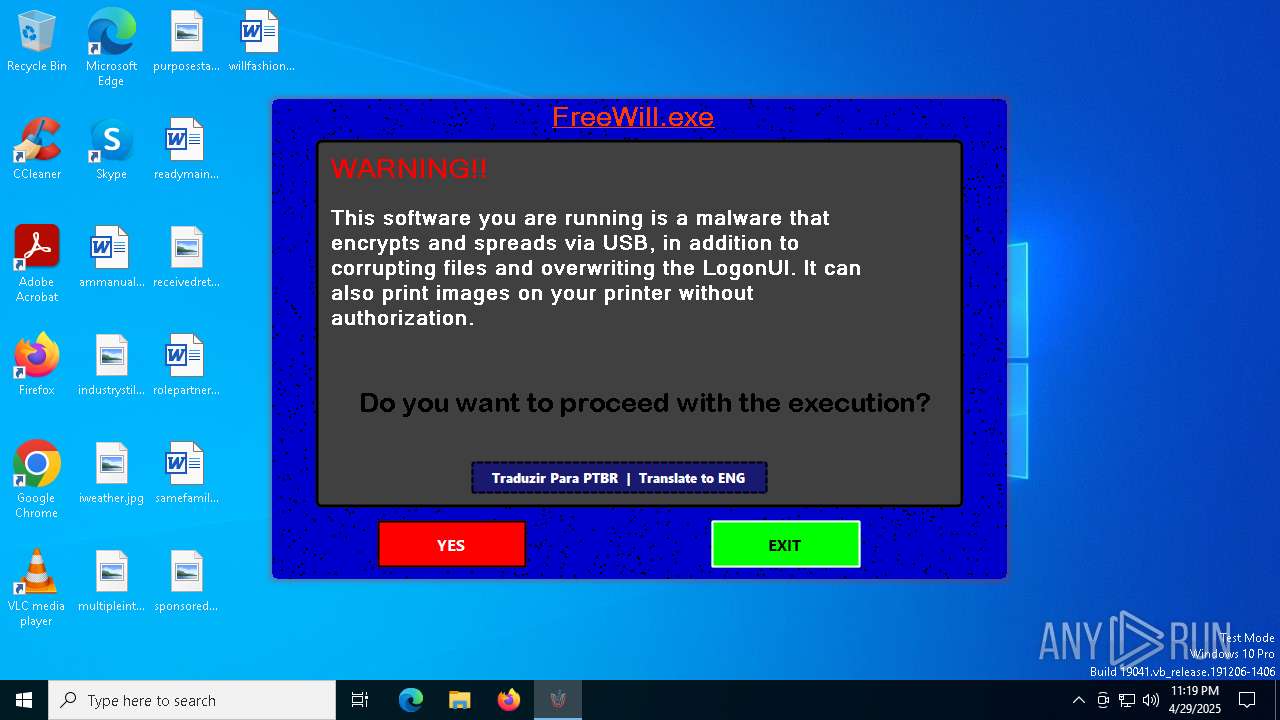
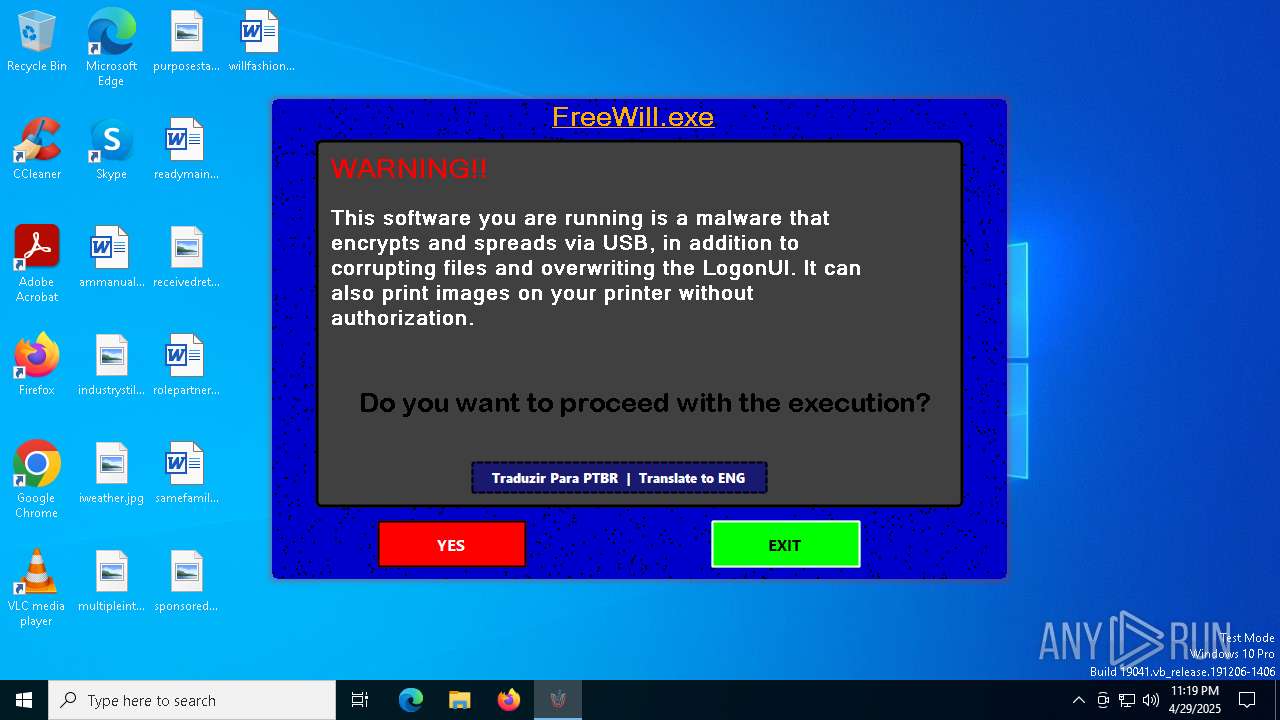
MALICIOUS
Changes the login/logoff helper path in the registry
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
UAC/LUA settings modification
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Disables task manager
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Disables the Command Prompt (cmd)
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
SUSPICIOUS
Executable content was dropped or overwritten
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
There is functionality for taking screenshot (YARA)
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Reads security settings of Internet Explorer
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
- ShellExperienceHost.exe (PID: 1324)
Reads the date of Windows installation
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 5260)
- cmd.exe (PID: 856)
Starts CMD.EXE for commands execution
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 6572)
- cmd.exe (PID: 2908)
The process checks if it is being run in the virtual environment
- icacls.exe (PID: 2320)
Process drops legitimate windows executable
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
INFO
Reads the computer name
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
- ShellExperienceHost.exe (PID: 1324)
Create files in a temporary directory
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Checks supported languages
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
- ShellExperienceHost.exe (PID: 1324)
Reads the machine GUID from the registry
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Confuser has been detected (YARA)
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Process checks computer location settings
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
The sample compiled with english language support
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Process checks whether UAC notifications are on
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Creates files or folders in the user directory
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Reads Environment values
- ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe (PID: 5972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2091:08:12 21:11:03+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 7190016 |
| InitializedDataSize: | 229376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6dd5ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
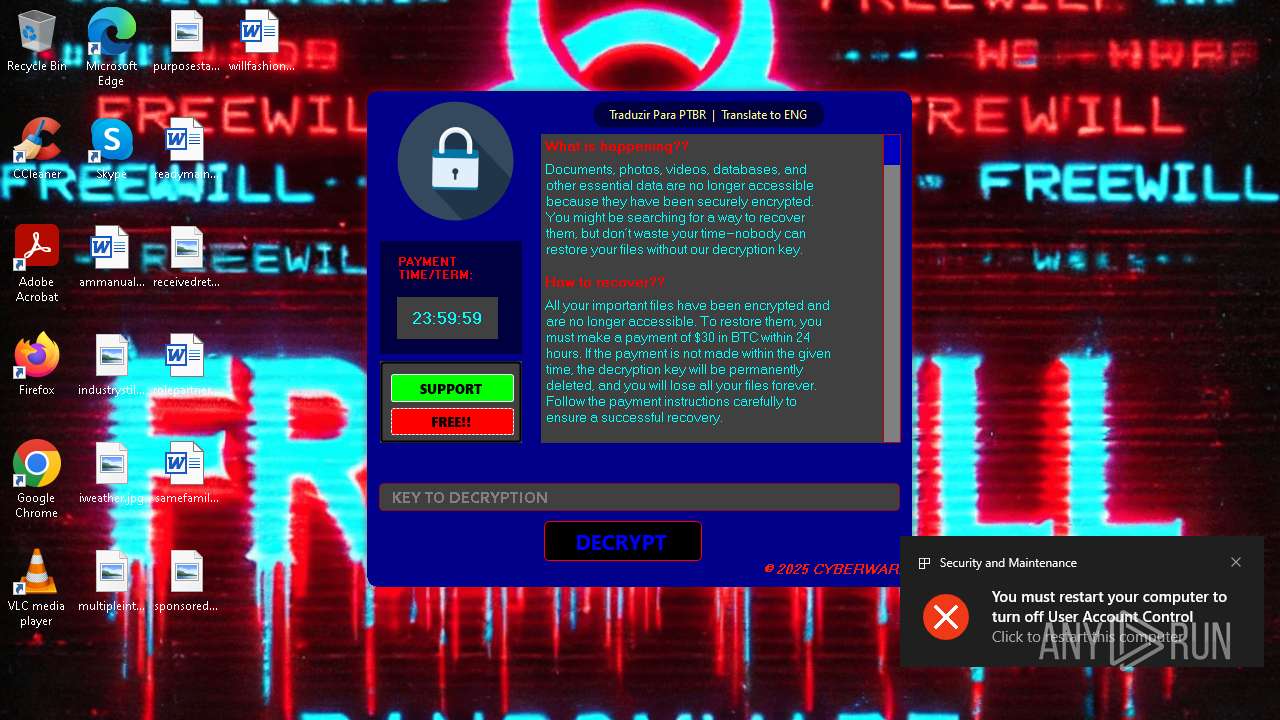
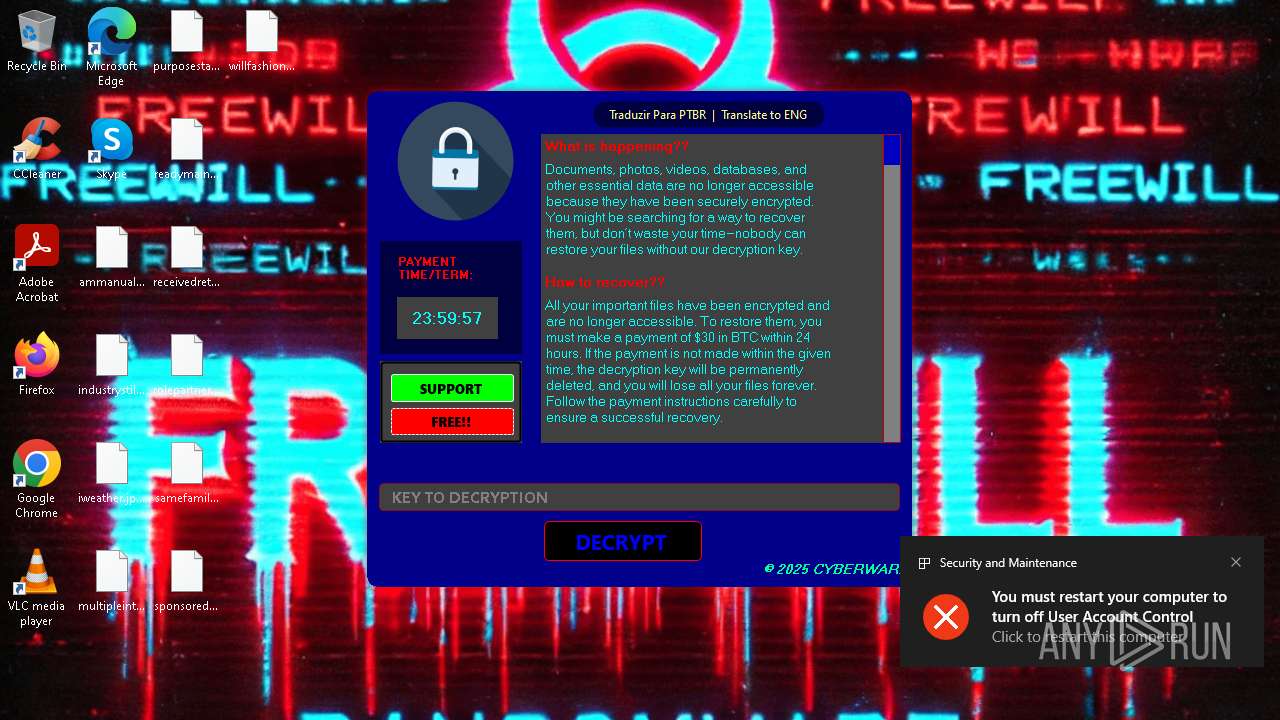
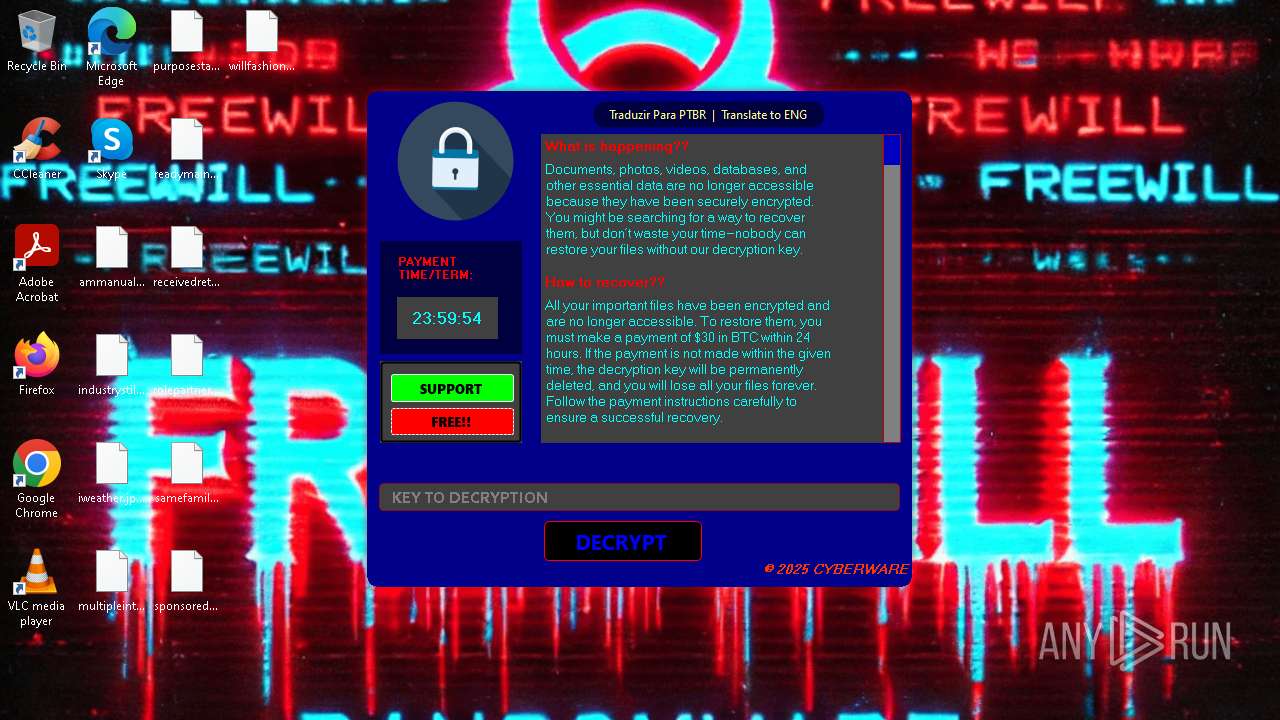
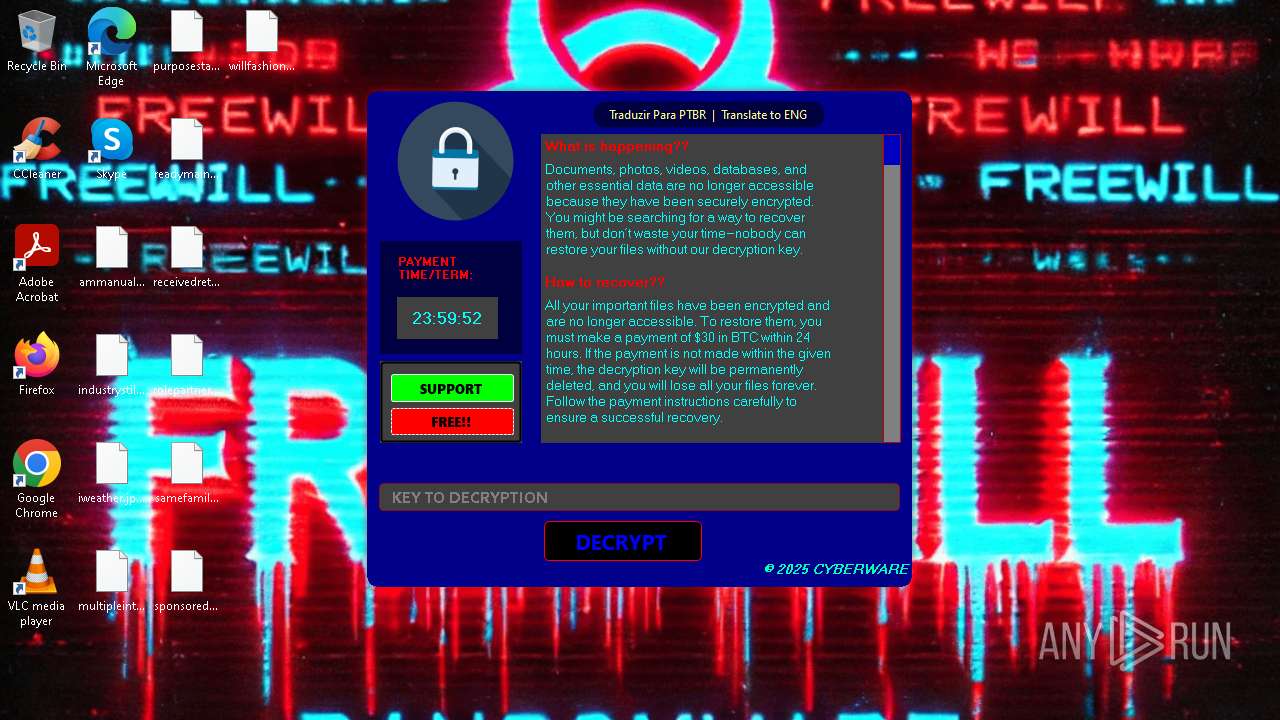
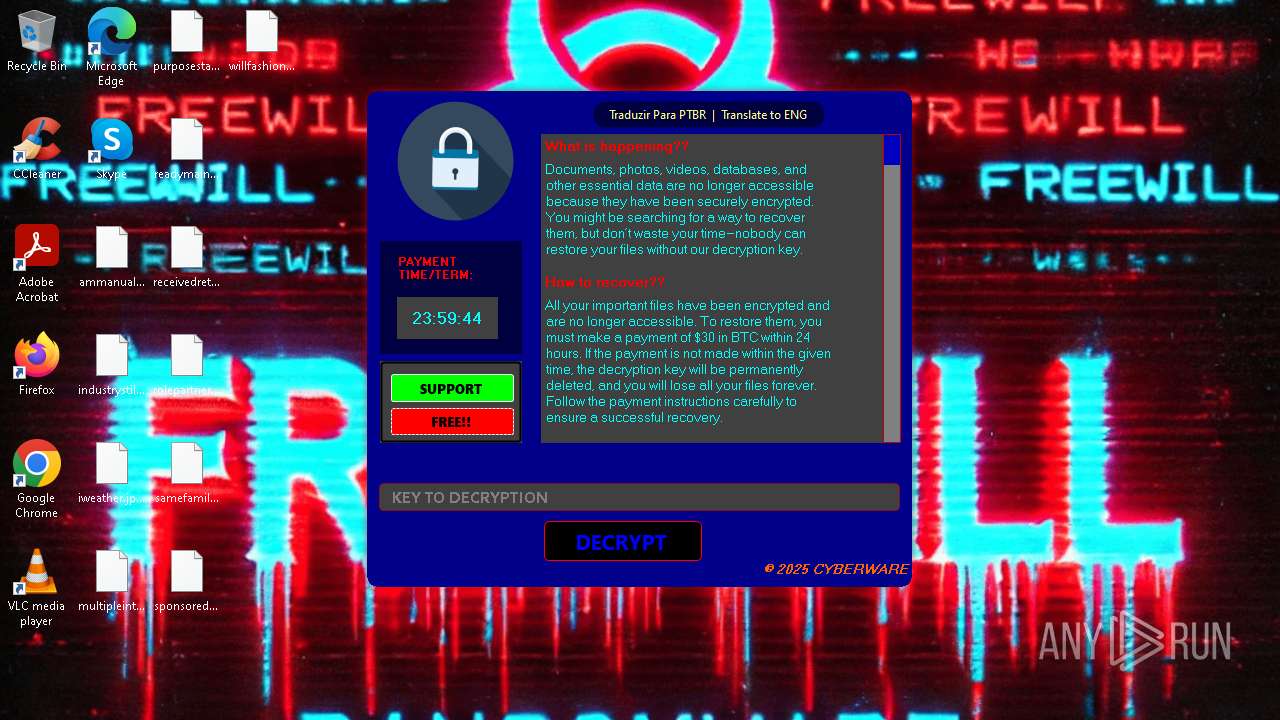
| Comments: | FreeWill |
| CompanyName: | CYBERWARE |
| FileDescription: | FreeWill |
| FileVersion: | 0.0.0.0 |
| InternalName: | FreeWill.exe |
| LegalCopyright: | Copyright © 2025 CYBERWARE |
| LegalTrademarks: | CYBERWARE |
| OriginalFileName: | FreeWill.exe |
| ProductName: | FreeWill |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
146
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Windows\System32\cmd.exe" /c takeown /f C:\WINDOWS\system32\LogonUI.exe /a | C:\Windows\System32\cmd.exe | — | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\AppData\Local\Temp\ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe" | C:\Users\admin\AppData\Local\Temp\ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | — | explorer.exe | |||||||||||
User: admin Company: CYBERWARE Integrity Level: MEDIUM Description: FreeWill Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1324 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | takeown /f C:\WINDOWS\system32\LogonUI.exe /a | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | icacls C:\WINDOWS\system32 /grant admin:F | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2908 | "C:\Windows\System32\cmd.exe" /c icacls C:\WINDOWS\system32\LogonUI.exe /grant %username%:F | C:\Windows\System32\cmd.exe | — | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4152 | icacls C:\WINDOWS\system32\LogonUI.exe /grant admin:F | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 604
Read events
6 596
Write events
8
Delete events
0
Modification events
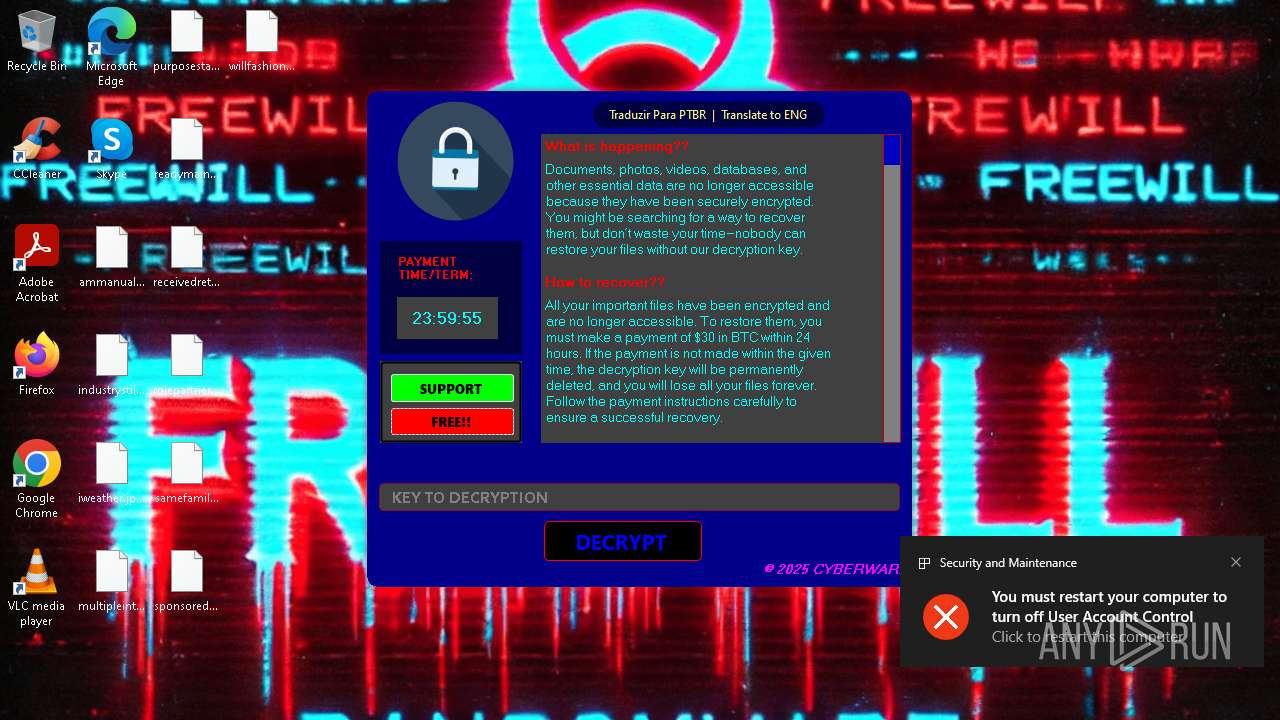
| (PID) Process: | (5972) ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (5972) ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 1 | |||
| (PID) Process: | (5972) ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | DisableCMD |
Value: 1 | |||
| (PID) Process: | (5972) ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe, FreeWill.exe | |||
| (PID) Process: | (5972) ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (1324) ShellExperienceHost.exe | Key: | \REGISTRY\A\{a3e6dfb9-7d0e-b9f9-da55-e69b59d05927}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D000000029C65335DB9DB01 | |||
| (PID) Process: | (5972) ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 8654110000000000 | |||
Executable files
9
Suspicious files
468
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Users\admin\Desktop\ammanual.rtf.FW | binary | |
MD5:B9308935A3597EDB79EB0285BA056B73 | SHA256:A943E3F8E94E656912CFE83E7F7CEE5902788D6901CC5A7298ECDB50750E459E | |||
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Users\admin\AppData\Local\Temp\TheBloop.wav | binary | |
MD5:95E02CB77FACB2CA242937A81B781D27 | SHA256:8E25111F9933E7D7AC3AD332976F217CEC37D8E17DA3DC0D8C0AA2F11D4EFF0F | |||
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Users\admin\AppData\Local\IconCache.db.FW | binary | |
MD5:DE5E5F03A0640999EB82A801A24DC570 | SHA256:29DCEB5F77385D768A50234213EBEB3F55FB2B6C37FC4EBA987A75A17A853AB0 | |||
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Windows\System32\FreeWill.exe | executable | |
MD5:4318D93E4B3D3590F3B4C6C2CDD794F3 | SHA256:EBBB8769086DCF3F7BDAF9366CF6A5AC4C5AC981E4BE3C69D08CE06FC80C2F28 | |||
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Windows\bootfcg.dat | executable | |
MD5:4318D93E4B3D3590F3B4C6C2CDD794F3 | SHA256:EBBB8769086DCF3F7BDAF9366CF6A5AC4C5AC981E4BE3C69D08CE06FC80C2F28 | |||
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Windows\System32\WindowsUpdateService.exe | executable | |
MD5:4318D93E4B3D3590F3B4C6C2CDD794F3 | SHA256:EBBB8769086DCF3F7BDAF9366CF6A5AC4C5AC981E4BE3C69D08CE06FC80C2F28 | |||
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Users\admin\AppData\Local\Temp\FreeWill_img.png | image | |
MD5:66EB581D01F02A72457458A477CF1E3D | SHA256:D32EAEDE73B3376F4B54CA1BB433DB86C8D9061659644B2FB87AA4C3C097BE90 | |||
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Users\admin\Pictures\batteryseptember.jpg.FW | binary | |
MD5:F4042F4E7DEEAEA98F6A4BC8380E4D12 | SHA256:250C3E125271FB9CE91208183551BB8B2931CAE31954FBBB87790BE8B3022675 | |||
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Windows\System32\LogonUITrue.exe | executable | |
MD5:893144FE49AA16124B5BD3034E79BBC6 | SHA256:CF01E46C146699F6C0E3DD447043F59BC9438DBBCB9563AF6C60EBC6D82727F2 | |||
| 5972 | ebbb8769086dcf3f7bdaf9366cf6a5ac4c5ac981e4be3c69d08ce06fc80c2f28.exe | C:\Users\admin\Downloads\advancedmr.png.FW | binary | |
MD5:8D0047DA8740C28B1A716DDB6B745BF0 | SHA256:5173FCDEDFF76E96B9710F877912783F78F39E5F7E23ED39CB18ECE3176DE662 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.124.11.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1052 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1052 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.124.11.17:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 104.119.109.218:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |