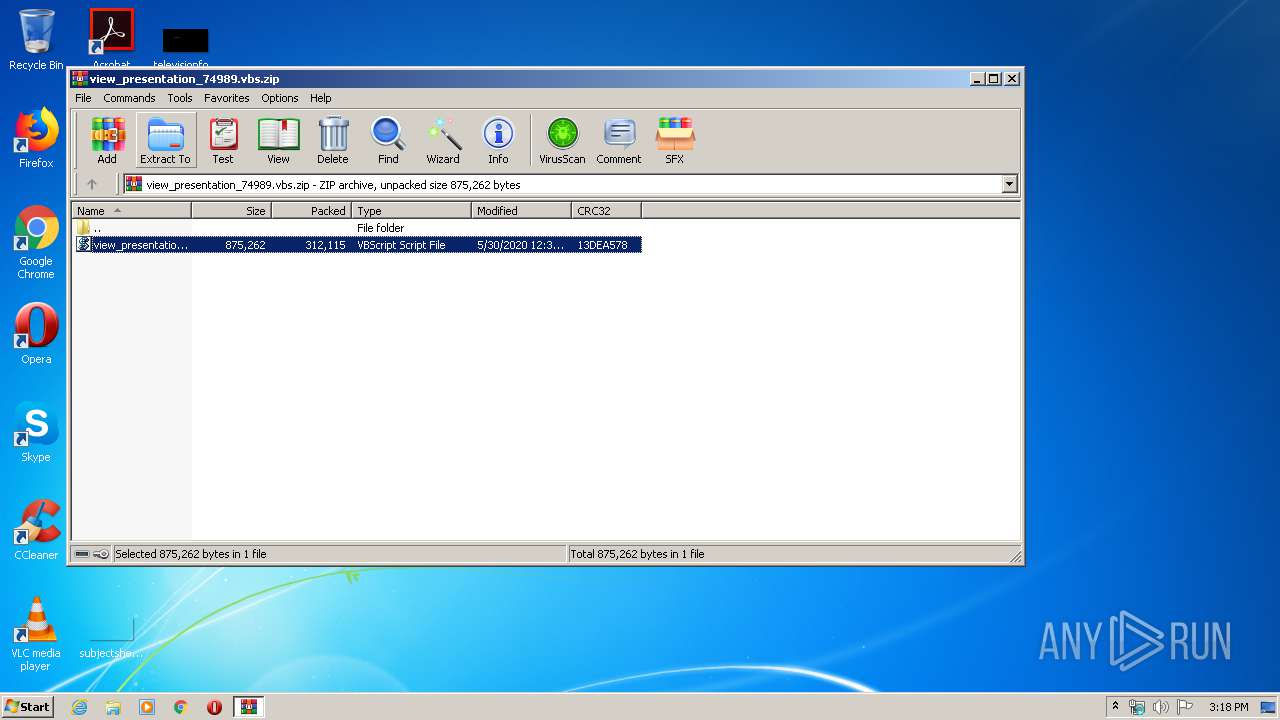
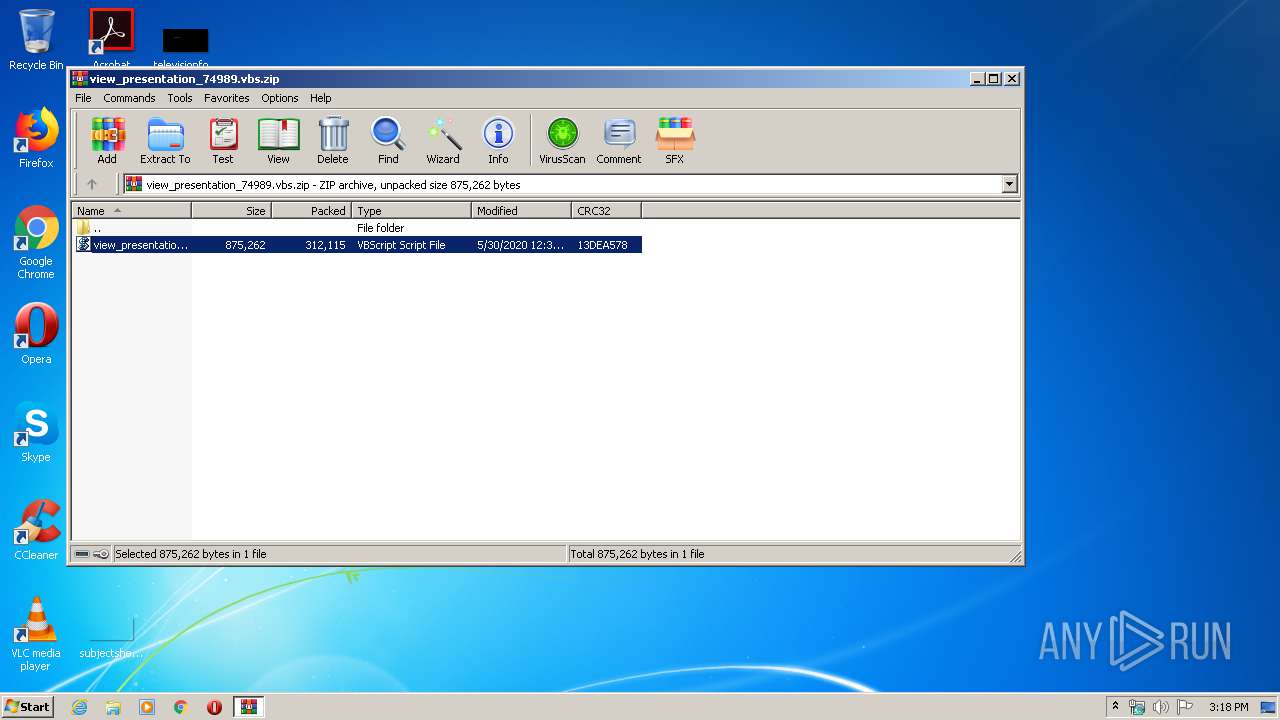
| File name: | view_presentation_74989.vbs.zip |
| Full analysis: | https://app.any.run/tasks/662a7665-1c54-4fe3-93b8-739399fe2672 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 14:18:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E8BC270FB095A01D84DE3489598E0FCC |
| SHA1: | F2C45260C075FF3C4CF19C5C0A38539765C44C04 |
| SHA256: | EBB98F65B1BC72FECF3B03CC83F2EFC847851C17E9D900A72EDEE10C60ED88AA |
| SSDEEP: | 6144:D56076RzNzh9wFK9Wp79ovgQbk4haE/A7onMLcB91Y14Lbt2rhbybeE:B7mzh9vYoYKk4haETnQubAsbD |
MALICIOUS
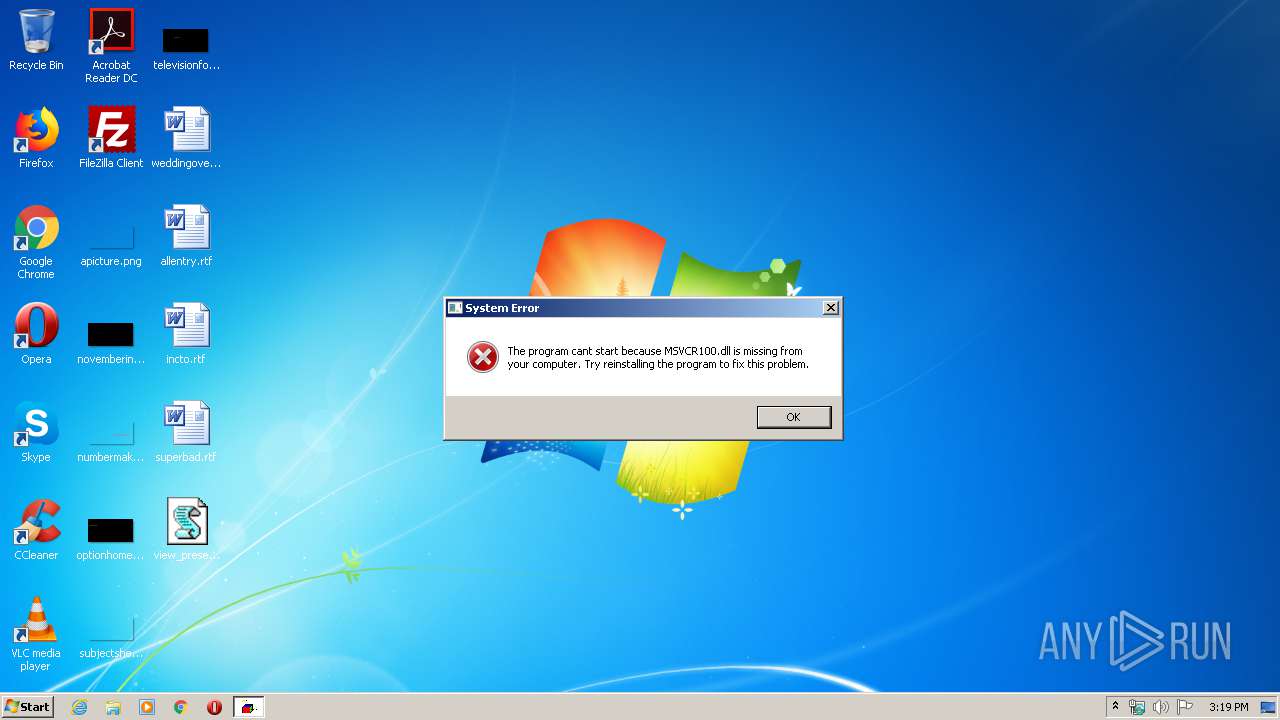
Application was dropped or rewritten from another process
- dad.cab (PID: 3828)
- dad.cab (PID: 2192)
Changes settings of System certificates
- WScript.exe (PID: 3552)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 3552)
Starts application with an unusual extension
- dad.cab (PID: 3828)
Executed via WMI
- dad.cab (PID: 3828)
Executed via COM
- iexplore.exe (PID: 2940)
Adds / modifies Windows certificates
- WScript.exe (PID: 3552)
INFO
Manual execution by user
- WScript.exe (PID: 3552)
Reads settings of System Certificates
- WScript.exe (PID: 3552)
Reads Internet Cache Settings
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 2940)
Changes internet zones settings
- iexplore.exe (PID: 2940)
Reads internet explorer settings
- iexplore.exe (PID: 2440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:05:30 13:38:24 |
| ZipCRC: | 0x13dea578 |
| ZipCompressedSize: | 312115 |
| ZipUncompressedSize: | 875262 |
| ZipFileName: | view_presentation_74989.vbs |
Total processes
44
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\Users\admin\AppData\Local\Temp\dad.cab | C:\Users\admin\AppData\Local\Temp\dad.cab | — | dad.cab | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
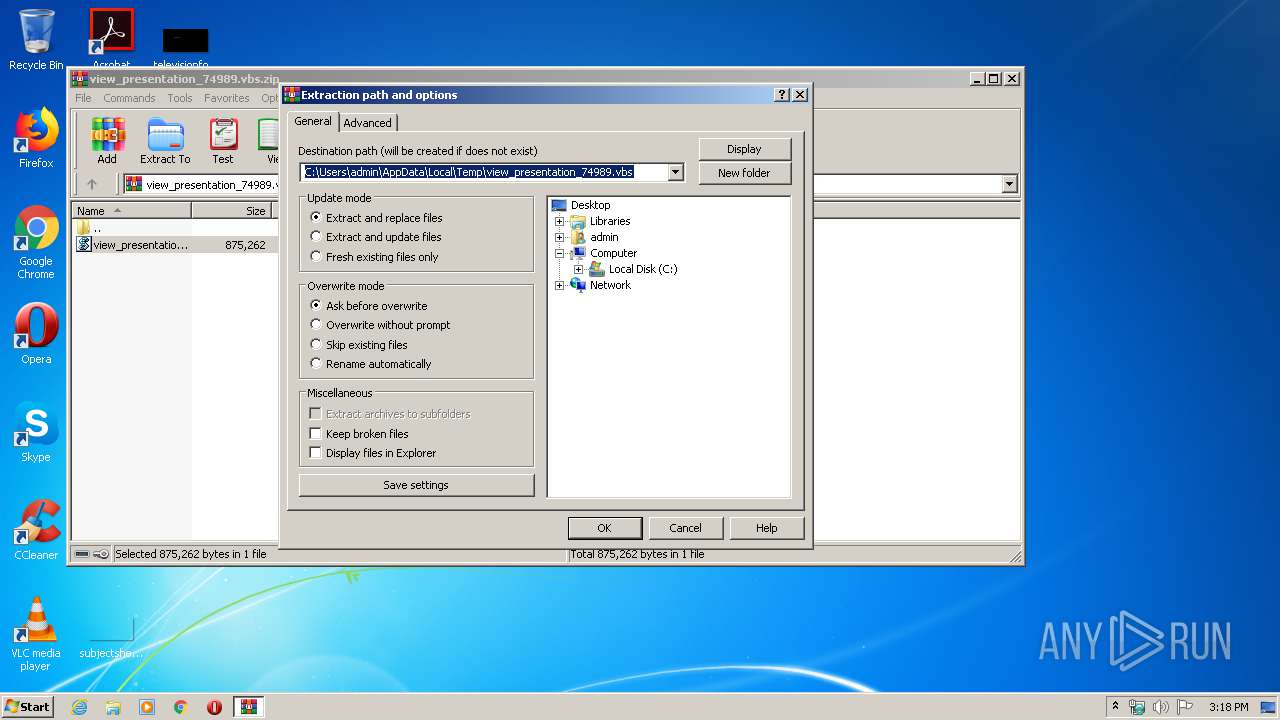
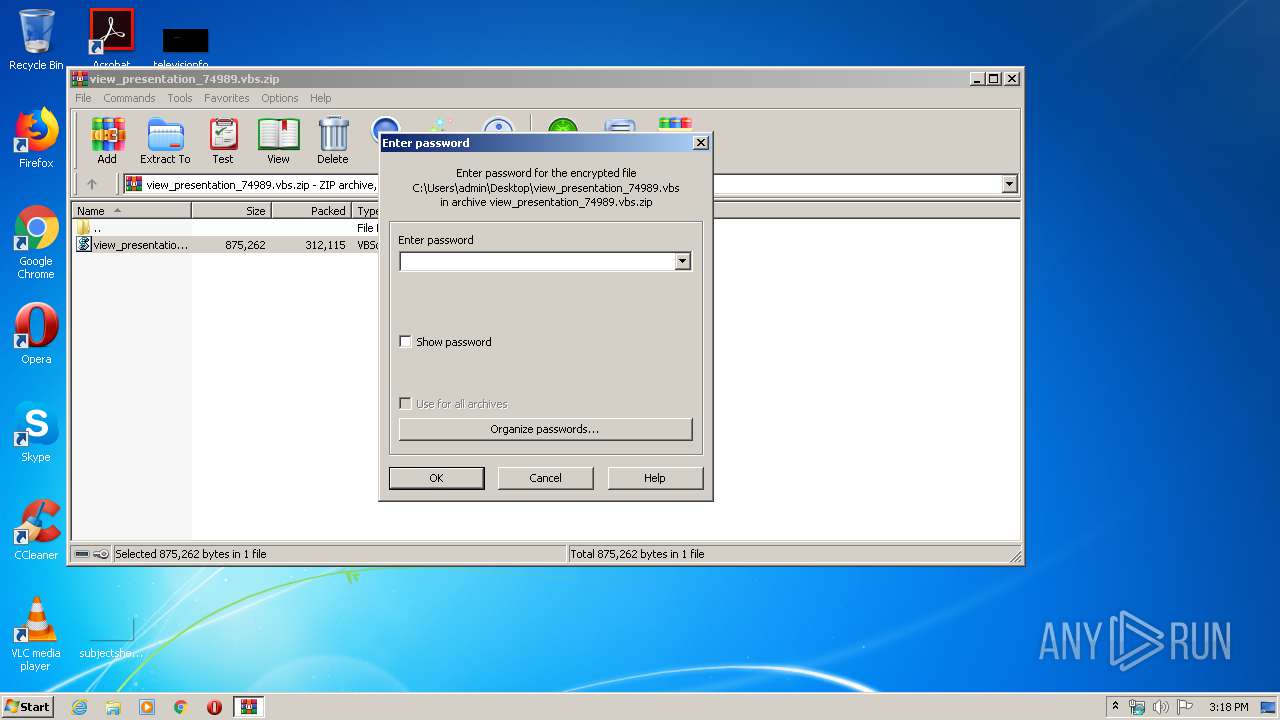
| 2436 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\view_presentation_74989.vbs.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2940 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3552 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\view_presentation_74989.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3828 | C:\Users\admin\AppData\Local\Temp\dad.cab | C:\Users\admin\AppData\Local\Temp\dad.cab | — | wmiprvse.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 724
Read events
1 072
Write events
2 455
Delete events
1 197
Modification events
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\view_presentation_74989.vbs.zip | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
Executable files
1
Suspicious files
2
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2E72E63745D1DCAB.TMP | — | |
MD5:— | SHA256:— | |||
| 3552 | WScript.exe | C:\Users\admin\AppData\Local\Temp\maternity.zip | compressed | |
MD5:— | SHA256:— | |||
| 3552 | WScript.exe | C:\Users\admin\AppData\Local\Temp\adobe.url | text | |
MD5:— | SHA256:— | |||
| 3552 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Segovia.mid | text | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\Desktop\view_presentation_74989.vbs | text | |
MD5:— | SHA256:— | |||
| 3552 | WScript.exe | C:\Users\admin\AppData\Local\Temp\dad.cab | executable | |
MD5:— | SHA256:— | |||
| 3552 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Caleb.m4 | text | |
MD5:— | SHA256:— | |||
| 3552 | WScript.exe | C:\Users\admin\AppData\Local\Temp\decay.tiff | text | |
MD5:— | SHA256:— | |||
| 2440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\errorPageStrings[1] | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2940 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2940 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3552 | WScript.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iplogger.org |
| shared |
fs.ramtool.at |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
3 ETPRO signatures available at the full report