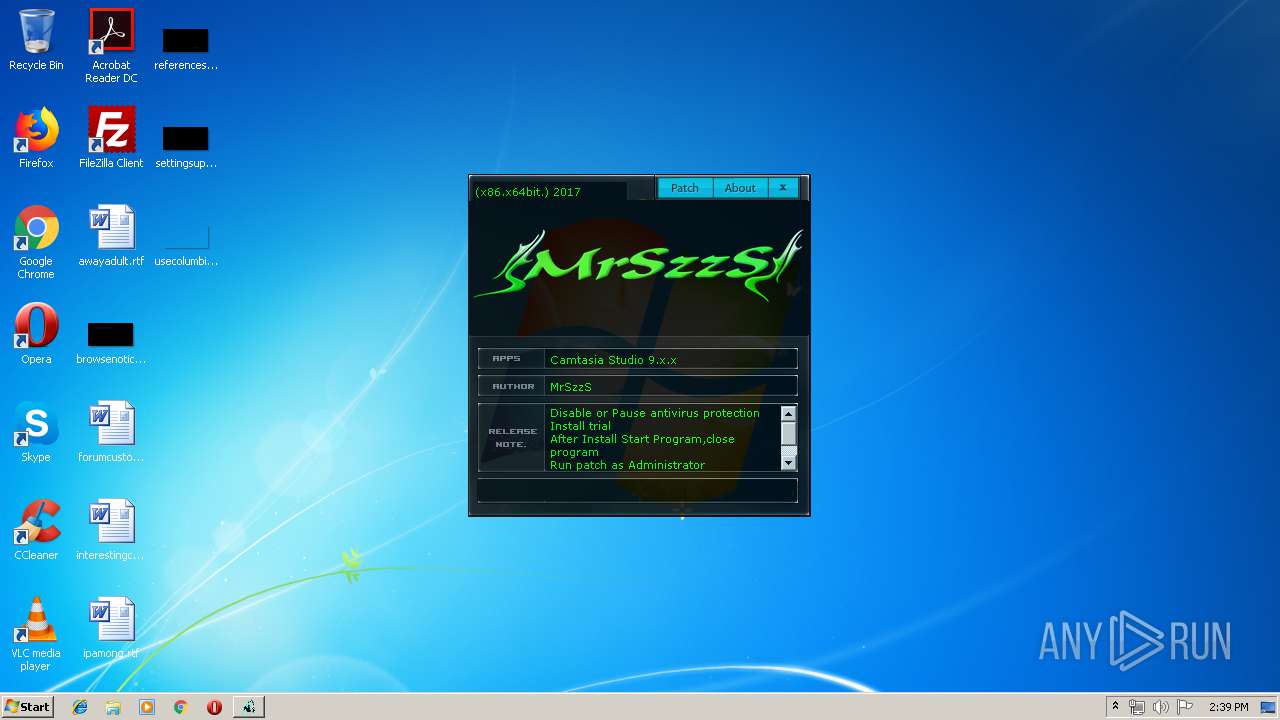
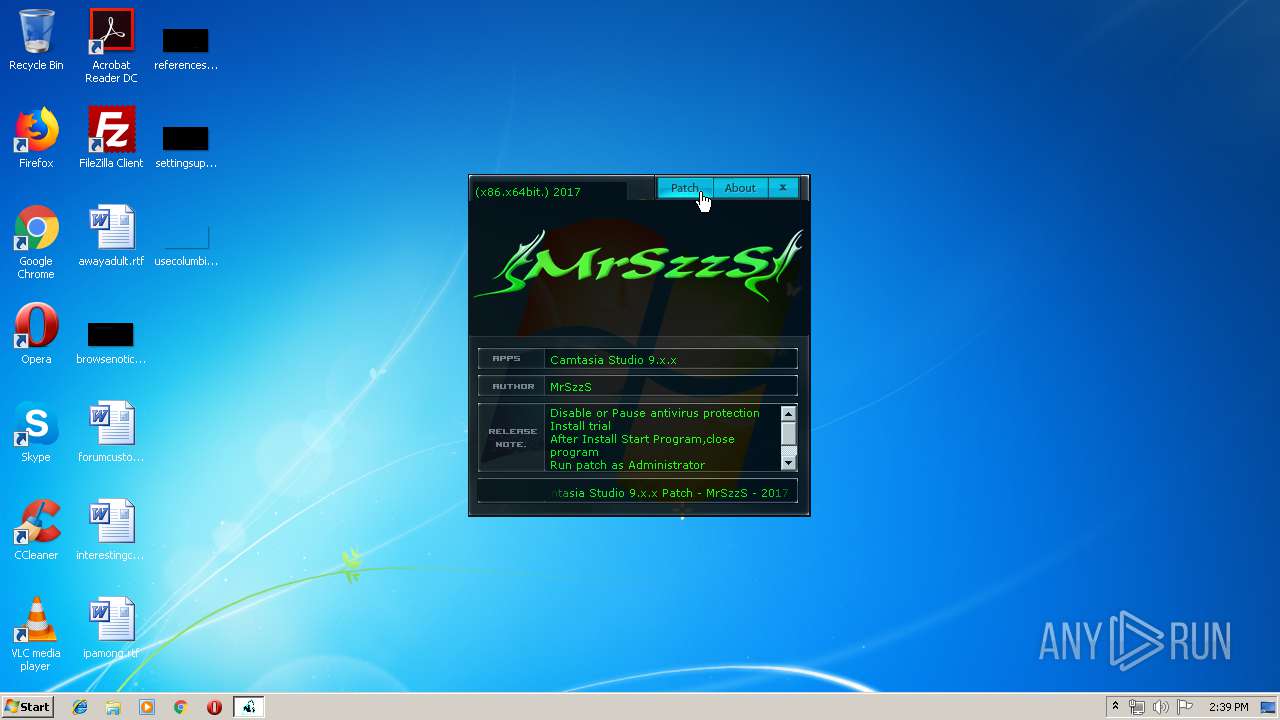
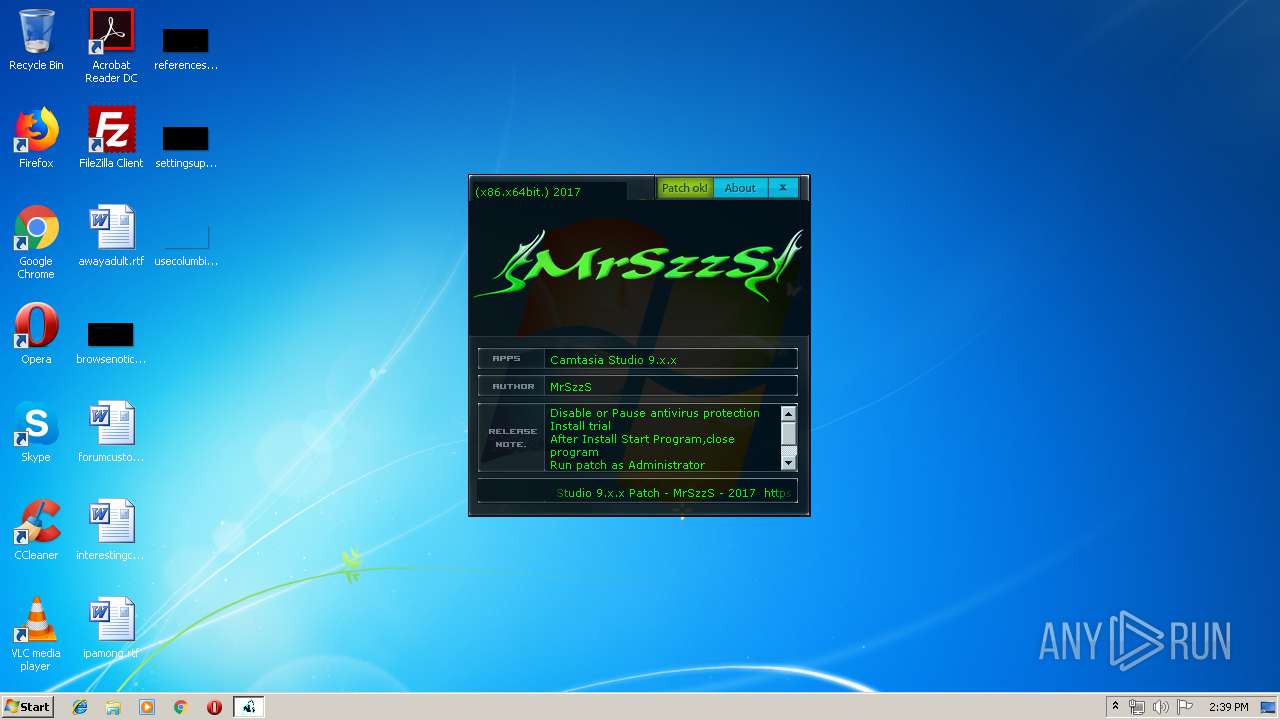
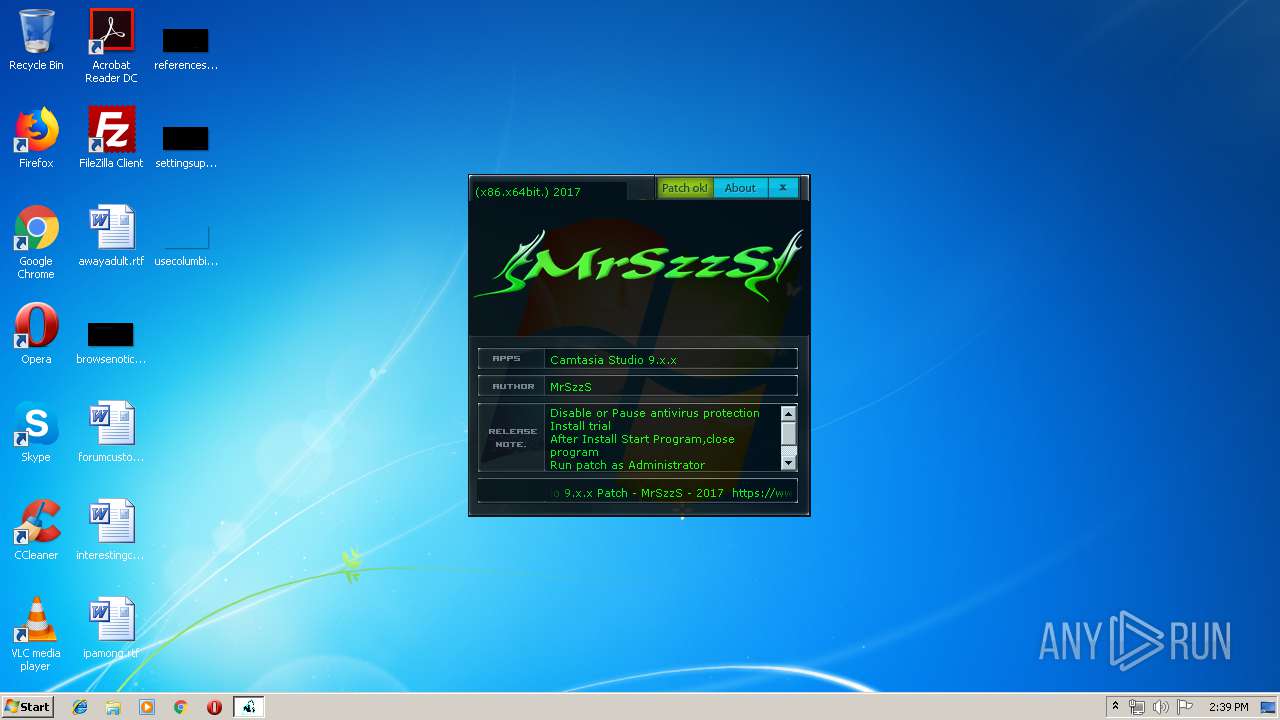
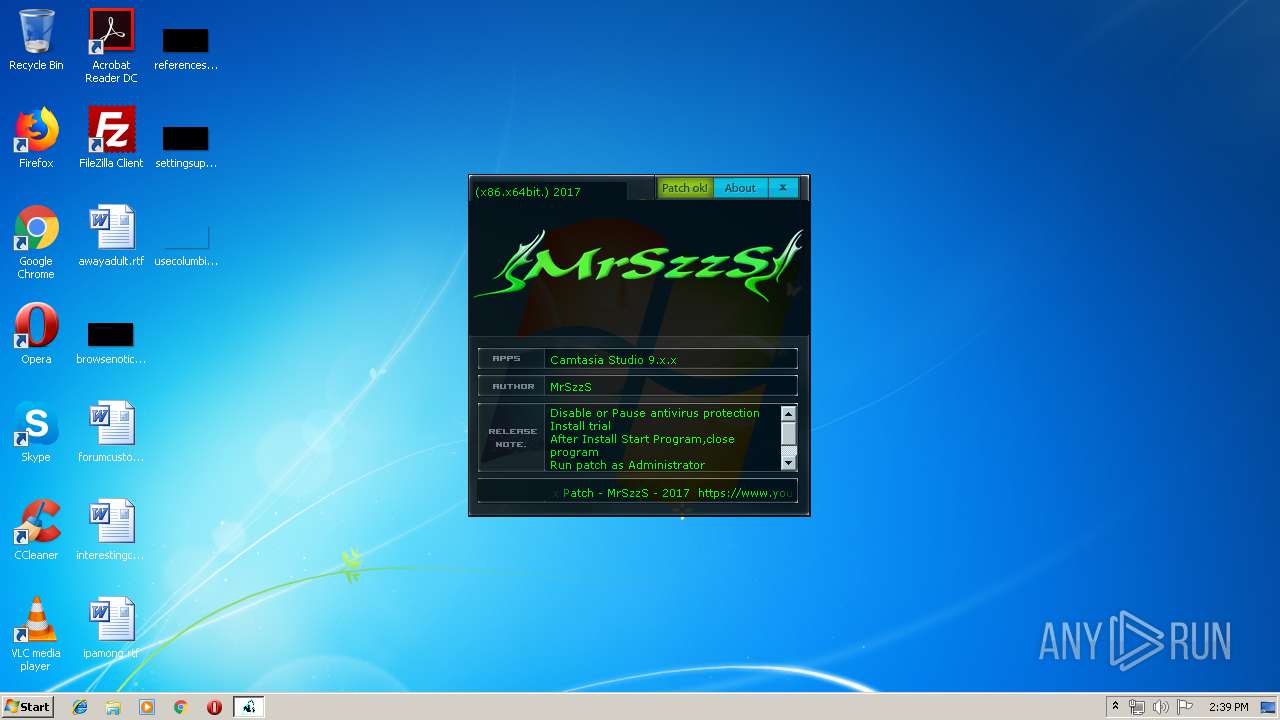
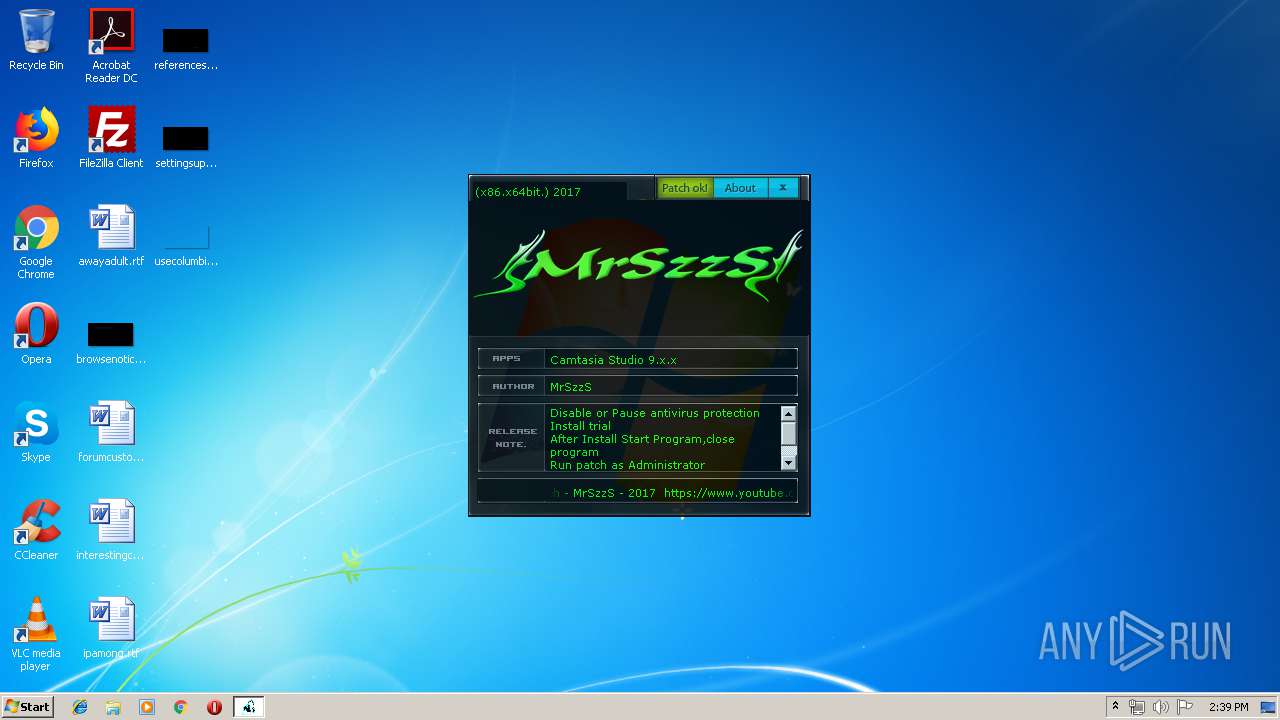
| File name: | Crack.exe |
| Full analysis: | https://app.any.run/tasks/78b36bdd-c8eb-4443-ab62-112cf274ab6f |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 13:39:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 184B306698F4FE3C202277460964999E |
| SHA1: | 5C0B95A30A8E0DE9D8AE0A0C75174546081A04C4 |
| SHA256: | EBB5CF6F5852FE46343924782BCD048D0281903D01B97D0E7879B2893E65409B |
| SSDEEP: | 24576:+i510GDqzJVC/zG9IpA7dPteM9JSCf/mXj:BHqFVC/zUIpA7xtHjf0j |
MALICIOUS
Loads dropped or rewritten executable
- Crack.exe (PID: 404)
SUSPICIOUS
Executable content was dropped or overwritten
- Crack.exe (PID: 404)
Creates files in the program directory
- Crack.exe (PID: 404)
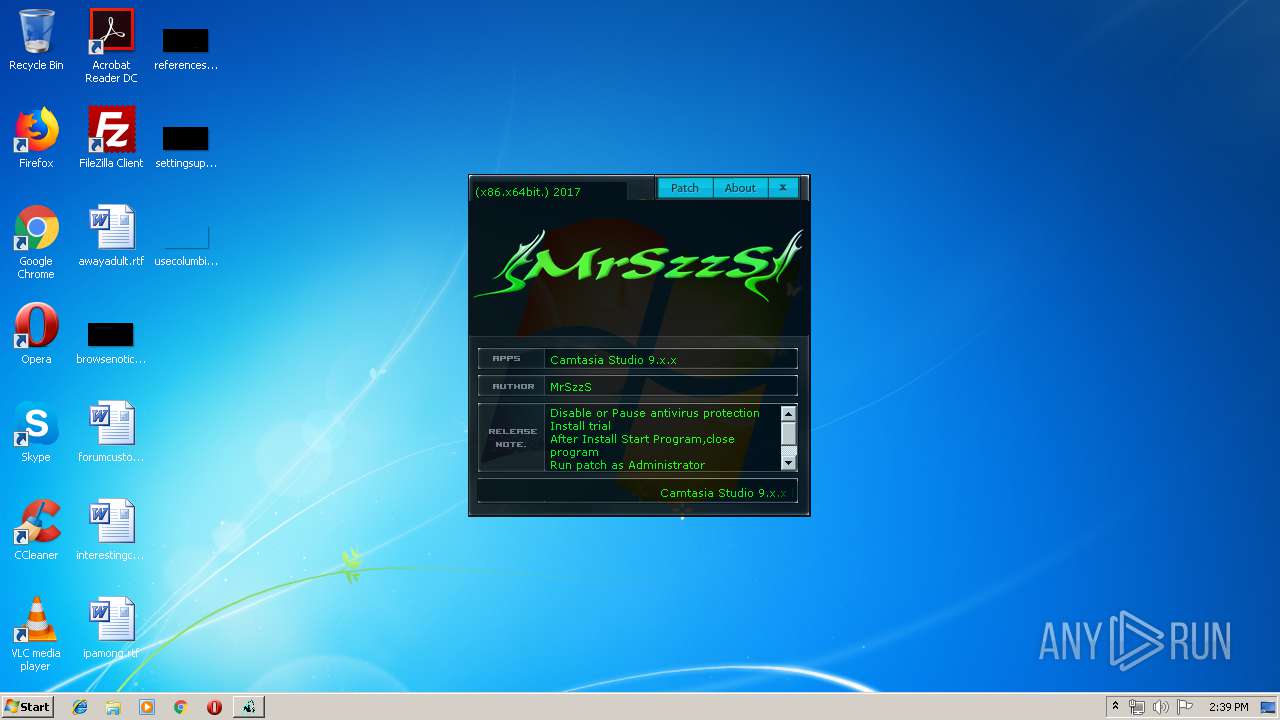
Starts CMD.EXE for commands execution
- Crack.exe (PID: 404)
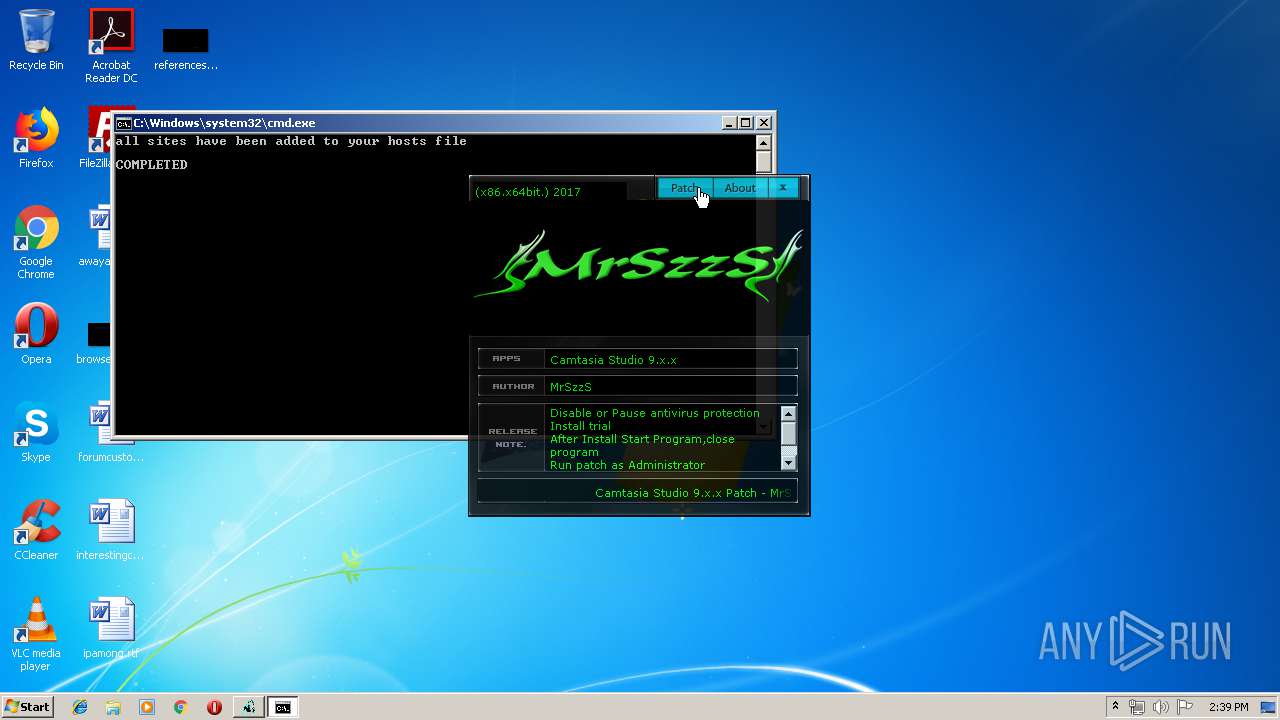
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 2588)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2588)
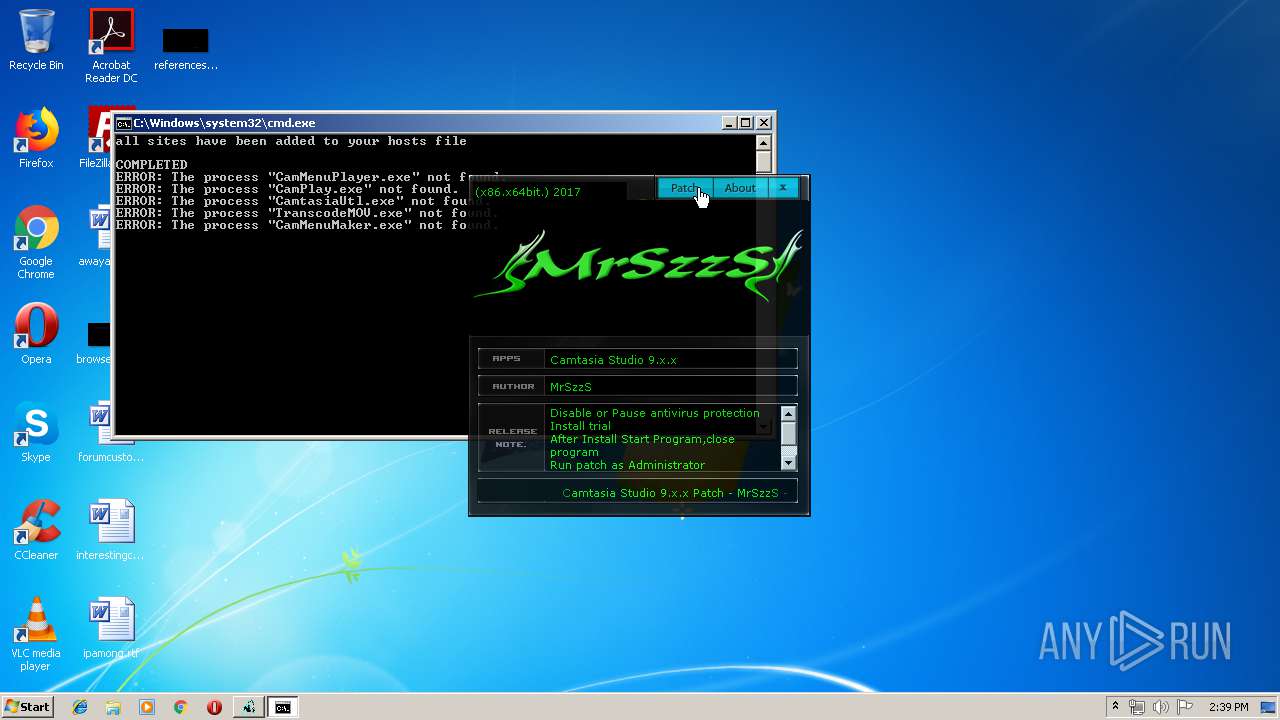
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2588)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:05:02 19:50:41+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 798208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-May-2012 17:50:41 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-May-2012 17:50:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x000C2678 | 0x000C2800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.9918 |
.reloc | 0x000C7000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
500 | 1.91924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
DLL | 7.99975 | 785408 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
Total processes
52
Monitored processes
15
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | taskkill /IM CamtasiaStudio.exe /F | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 404 | "C:\Users\admin\AppData\Local\Temp\Crack.exe" | C:\Users\admin\AppData\Local\Temp\Crack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225547 Modules
| |||||||||||||||
| 764 | taskkill /IM CamMenuMaker.exe /F | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 972 | taskkill /IM CamMenuPlayer.exe /F | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | "C:\Windows\regedit.exe" /s "C:\Users\admin\AppData\Local\Temp\\regpatch.reg" | C:\Windows\regedit.exe | — | Crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Users\admin\AppData\Local\Temp\Crack.exe" | C:\Users\admin\AppData\Local\Temp\Crack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2452 | attrib -r C:\Windows\system32\drivers\etc\hosts | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | taskkill /IM CamPlay.exe /F | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | cmd /c "C:\Program Files\TechSmith\Camtasia 9\2016 host.bat" | C:\Windows\system32\cmd.exe | — | Crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2644 | attrib +r C:\Windows\system32\drivers\etc\hosts | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
121
Read events
107
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | RegisteredTo |
Value: MrSzzS | |||
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | RegistrationKey |
Value: VVDCC3CHDCWVCZJ2DMCSP78RA | |||
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | ValidationData1 |
Value: /m`'A]Zkw6~%.zMr | |||
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | ValidationData3 |
Value: 1 | |||
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | ValidationData2 |
Value: 1 | |||
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | RegisteredTo |
Value: MrSzzS | |||
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | RegistrationKey |
Value: VVDCC3CHDCWVCZJ2DMCSP78RA | |||
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | ValidationData1 |
Value: /m`'A]Zkw6~%.zMr | |||
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | ValidationData3 |
Value: 1 | |||
| (PID) Process: | (2240) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TechSmith\Camtasia Studio\9.0 |
| Operation: | write | Name: | ValidationData2 |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2588 | cmd.exe | C:\Windows\system32\drivers\etc\hosts | text | |
MD5:— | SHA256:— | |||
| 404 | Crack.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:E233D698FB6DBEC8D082B610E8251853 | SHA256:E889217FB3DFD04CDF955AB96475A20282DD9A1E69CFFB227B9BE891E9FA195D | |||
| 404 | Crack.exe | C:\ProgramData\TechSmith\Camtasia Studio 9\RegInfo.ini | text | |
MD5:024A1DEA738B17665D07091C11C94B93 | SHA256:C4DA3C70F20A087C4C57BF10E9F65D711E3E55EB23EDFBC691BEC39C6E42FFC5 | |||
| 404 | Crack.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:780D14604D49E3C634200C523DEF8351 | SHA256:844EB66A10B848D3A71A8C63C35F0A01550A46D2FF8503E2CA8947978B03B4D2 | |||
| 404 | Crack.exe | C:\Users\admin\AppData\Local\Temp\regpatch.reg | text | |
MD5:A8564EB132D384AC2D62086044102F3F | SHA256:87E918EB1AB45E3698139BE80116A3449B85A0E6D467F501B0AB207E3AE94458 | |||
| 404 | Crack.exe | C:\Program Files\TechSmith\Camtasia 9\2016 host.bat | text | |
MD5:05298357041AB9226092B2EB395C9C61 | SHA256:91ED2111500A83FF21D8D2F7978A6CD601DEEDB3921F15CDCC23F2F0BDF5E083 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report