| File name: | SAB.3.0.bat |
| Full analysis: | https://app.any.run/tasks/7857c424-dc5e-4bbe-818c-e39f8661d70c |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 02:44:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 988DB6360E6886AF17FCA78DB05183BF |
| SHA1: | A42682EC1493F5C96DA2FF5E35B39D7163A16F28 |
| SHA256: | EBAED86D3022F0540D3CE0ED25B86CAD430CED6A9404083042403BB12E0A63AC |
| SSDEEP: | 48:yutJjHjKNljukmtp6bDohSz+zcEPAEAiHin:TtNkQKbSzcEYEs |
MALICIOUS
Create files in the Startup directory
- cmd.exe (PID: 3888)
- cmd.exe (PID: 23788)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3888)
- cmd.exe (PID: 2044)
- cmd.exe (PID: 5444)
- cmd.exe (PID: 1652)
- cmd.exe (PID: 5924)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 1932)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 4856)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7668)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 4168)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8408)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 8644)
- cmd.exe (PID: 8776)
- cmd.exe (PID: 8892)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 9124)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 9528)
- cmd.exe (PID: 9268)
- cmd.exe (PID: 9404)
- cmd.exe (PID: 9644)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 9912)
- cmd.exe (PID: 10028)
- cmd.exe (PID: 10176)
- cmd.exe (PID: 9876)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 10320)
- cmd.exe (PID: 10708)
- cmd.exe (PID: 10852)
- cmd.exe (PID: 10556)
- cmd.exe (PID: 11072)
- cmd.exe (PID: 11192)
- cmd.exe (PID: 11304)
- cmd.exe (PID: 10948)
- cmd.exe (PID: 11452)
- cmd.exe (PID: 11624)
- cmd.exe (PID: 11948)
- cmd.exe (PID: 11748)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 12232)
- cmd.exe (PID: 12728)
- cmd.exe (PID: 12808)
- cmd.exe (PID: 12932)
- cmd.exe (PID: 13204)
- cmd.exe (PID: 13368)
- cmd.exe (PID: 13524)
- cmd.exe (PID: 13828)
- cmd.exe (PID: 13664)
- cmd.exe (PID: 14136)
- cmd.exe (PID: 14304)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 14024)
- cmd.exe (PID: 14496)
- cmd.exe (PID: 14628)
- cmd.exe (PID: 14788)
- cmd.exe (PID: 15052)
- cmd.exe (PID: 15152)
- cmd.exe (PID: 15292)
- cmd.exe (PID: 14892)
- cmd.exe (PID: 15464)
- cmd.exe (PID: 15616)
- cmd.exe (PID: 15728)
- cmd.exe (PID: 15188)
- cmd.exe (PID: 15828)
- cmd.exe (PID: 16008)
- cmd.exe (PID: 16224)
- cmd.exe (PID: 15840)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 16480)
- cmd.exe (PID: 16748)
- cmd.exe (PID: 16904)
- cmd.exe (PID: 17044)
- cmd.exe (PID: 17176)
- cmd.exe (PID: 17312)
- cmd.exe (PID: 16776)
- cmd.exe (PID: 17468)
- cmd.exe (PID: 17724)
- cmd.exe (PID: 17884)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 18016)
- cmd.exe (PID: 18292)
- cmd.exe (PID: 17640)
- cmd.exe (PID: 18584)
- cmd.exe (PID: 18728)
- cmd.exe (PID: 18912)
- cmd.exe (PID: 13932)
- cmd.exe (PID: 19268)
- cmd.exe (PID: 18436)
- cmd.exe (PID: 19092)
- cmd.exe (PID: 17704)
- cmd.exe (PID: 19532)
- cmd.exe (PID: 19656)
- cmd.exe (PID: 18776)
- cmd.exe (PID: 19964)
- cmd.exe (PID: 20212)
- cmd.exe (PID: 20436)
- cmd.exe (PID: 19828)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 20548)
- cmd.exe (PID: 19992)
- cmd.exe (PID: 20864)
- cmd.exe (PID: 21104)
- cmd.exe (PID: 21176)
- cmd.exe (PID: 21384)
- cmd.exe (PID: 20712)
- cmd.exe (PID: 9760)
- cmd.exe (PID: 21508)
- cmd.exe (PID: 21784)
- cmd.exe (PID: 22092)
- cmd.exe (PID: 22392)
- cmd.exe (PID: 22220)
- cmd.exe (PID: 23008)
- cmd.exe (PID: 21900)
- cmd.exe (PID: 23140)
- cmd.exe (PID: 23428)
- cmd.exe (PID: 16136)
- cmd.exe (PID: 23632)
- cmd.exe (PID: 23788)
- cmd.exe (PID: 24092)
- cmd.exe (PID: 24420)
- cmd.exe (PID: 15560)
- cmd.exe (PID: 24320)
- cmd.exe (PID: 24208)
- cmd.exe (PID: 24676)
- cmd.exe (PID: 25072)
- cmd.exe (PID: 24896)
- cmd.exe (PID: 25252)
- cmd.exe (PID: 25444)
- cmd.exe (PID: 22696)
- cmd.exe (PID: 16716)
- cmd.exe (PID: 22944)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 3092)
- cmd.exe (PID: 25612)
- cmd.exe (PID: 25856)
- cmd.exe (PID: 25984)
- cmd.exe (PID: 26220)
- cmd.exe (PID: 26464)
- cmd.exe (PID: 18508)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 23936)
- cmd.exe (PID: 8484)
- cmd.exe (PID: 23292)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 10920)
- cmd.exe (PID: 10540)
- cmd.exe (PID: 12004)
- cmd.exe (PID: 26708)
- cmd.exe (PID: 27020)
- cmd.exe (PID: 27400)
- cmd.exe (PID: 11932)
- cmd.exe (PID: 13500)
- cmd.exe (PID: 14040)
- cmd.exe (PID: 27616)
- cmd.exe (PID: 13272)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 15148)
- cmd.exe (PID: 27664)
- cmd.exe (PID: 27792)
- cmd.exe (PID: 15596)
- cmd.exe (PID: 17232)
- cmd.exe (PID: 27956)
- cmd.exe (PID: 28328)
- cmd.exe (PID: 28500)
- cmd.exe (PID: 28420)
- cmd.exe (PID: 18908)
- cmd.exe (PID: 19616)
- cmd.exe (PID: 28592)
- cmd.exe (PID: 20980)
- cmd.exe (PID: 19064)
- cmd.exe (PID: 20304)
- cmd.exe (PID: 28856)
- cmd.exe (PID: 29040)
- cmd.exe (PID: 29144)
- cmd.exe (PID: 28988)
- cmd.exe (PID: 29376)
- cmd.exe (PID: 29584)
- cmd.exe (PID: 29492)
- cmd.exe (PID: 25504)
- cmd.exe (PID: 30028)
- cmd.exe (PID: 29760)
- cmd.exe (PID: 30476)
- cmd.exe (PID: 30628)
- cmd.exe (PID: 30696)
- cmd.exe (PID: 30356)
- cmd.exe (PID: 15460)
- cmd.exe (PID: 24520)
- cmd.exe (PID: 22700)
- cmd.exe (PID: 23868)
- cmd.exe (PID: 12000)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 22872)
- cmd.exe (PID: 30772)
- cmd.exe (PID: 31556)
- cmd.exe (PID: 30988)
- cmd.exe (PID: 31668)
- cmd.exe (PID: 31348)
- cmd.exe (PID: 31680)
- cmd.exe (PID: 31084)
- cmd.exe (PID: 22908)
- cmd.exe (PID: 21092)
- cmd.exe (PID: 30236)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 15004)
- cmd.exe (PID: 31792)
- cmd.exe (PID: 32012)
- cmd.exe (PID: 32172)
- cmd.exe (PID: 31924)
- cmd.exe (PID: 32372)
Application launched itself
- cmd.exe (PID: 3888)
- cmd.exe (PID: 5444)
- cmd.exe (PID: 2044)
- cmd.exe (PID: 1652)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 5924)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 1932)
- cmd.exe (PID: 4856)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7668)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 4168)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8408)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 8644)
- cmd.exe (PID: 8892)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 9124)
- cmd.exe (PID: 8776)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 9528)
- cmd.exe (PID: 9268)
- cmd.exe (PID: 9644)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 9912)
- cmd.exe (PID: 10028)
- cmd.exe (PID: 9404)
- cmd.exe (PID: 10176)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 9876)
- cmd.exe (PID: 10320)
- cmd.exe (PID: 10556)
- cmd.exe (PID: 10708)
- cmd.exe (PID: 10852)
- cmd.exe (PID: 10948)
- cmd.exe (PID: 11192)
- cmd.exe (PID: 11072)
- cmd.exe (PID: 11304)
- cmd.exe (PID: 11452)
- cmd.exe (PID: 11624)
- cmd.exe (PID: 11748)
- cmd.exe (PID: 11948)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 12232)
- cmd.exe (PID: 12728)
- cmd.exe (PID: 12932)
- cmd.exe (PID: 13368)
- cmd.exe (PID: 13204)
- cmd.exe (PID: 12808)
- cmd.exe (PID: 13524)
- cmd.exe (PID: 13664)
- cmd.exe (PID: 13828)
- cmd.exe (PID: 14024)
- cmd.exe (PID: 14304)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 14136)
- cmd.exe (PID: 14496)
- cmd.exe (PID: 14628)
- cmd.exe (PID: 14788)
- cmd.exe (PID: 14892)
- cmd.exe (PID: 15052)
- cmd.exe (PID: 15152)
- cmd.exe (PID: 15292)
- cmd.exe (PID: 15188)
- cmd.exe (PID: 15464)
- cmd.exe (PID: 15616)
- cmd.exe (PID: 15728)
- cmd.exe (PID: 15828)
- cmd.exe (PID: 16008)
- cmd.exe (PID: 16224)
- cmd.exe (PID: 15840)
- cmd.exe (PID: 16480)
- cmd.exe (PID: 16748)
- cmd.exe (PID: 16904)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 17176)
- cmd.exe (PID: 17312)
- cmd.exe (PID: 16776)
- cmd.exe (PID: 17044)
- cmd.exe (PID: 17468)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 17724)
- cmd.exe (PID: 17884)
- cmd.exe (PID: 18016)
- cmd.exe (PID: 18292)
- cmd.exe (PID: 17640)
- cmd.exe (PID: 18584)
- cmd.exe (PID: 18728)
- cmd.exe (PID: 18912)
- cmd.exe (PID: 13932)
- cmd.exe (PID: 19092)
- cmd.exe (PID: 19268)
- cmd.exe (PID: 18436)
- cmd.exe (PID: 17704)
- cmd.exe (PID: 19656)
- cmd.exe (PID: 19532)
- cmd.exe (PID: 18776)
- cmd.exe (PID: 19828)
- cmd.exe (PID: 19964)
- cmd.exe (PID: 20212)
- cmd.exe (PID: 20436)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 19992)
- cmd.exe (PID: 20548)
- cmd.exe (PID: 20712)
- cmd.exe (PID: 20864)
- cmd.exe (PID: 21104)
- cmd.exe (PID: 21176)
- cmd.exe (PID: 9760)
- cmd.exe (PID: 21784)
- cmd.exe (PID: 21508)
- cmd.exe (PID: 21384)
- cmd.exe (PID: 22092)
- cmd.exe (PID: 22220)
- cmd.exe (PID: 22392)
- cmd.exe (PID: 21900)
- cmd.exe (PID: 23008)
- cmd.exe (PID: 23140)
- cmd.exe (PID: 23428)
- cmd.exe (PID: 23632)
- cmd.exe (PID: 23788)
- cmd.exe (PID: 24092)
- cmd.exe (PID: 16136)
- cmd.exe (PID: 24208)
- cmd.exe (PID: 24420)
- cmd.exe (PID: 15560)
- cmd.exe (PID: 24320)
- cmd.exe (PID: 24676)
- cmd.exe (PID: 24896)
- cmd.exe (PID: 25072)
- cmd.exe (PID: 25252)
- cmd.exe (PID: 25444)
- cmd.exe (PID: 22696)
- cmd.exe (PID: 16716)
- cmd.exe (PID: 22944)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 3092)
- cmd.exe (PID: 25612)
- cmd.exe (PID: 25856)
- cmd.exe (PID: 25984)
- cmd.exe (PID: 26220)
- cmd.exe (PID: 26464)
- cmd.exe (PID: 18508)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 23936)
- cmd.exe (PID: 8484)
- cmd.exe (PID: 23292)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 10540)
- cmd.exe (PID: 10920)
- cmd.exe (PID: 12004)
- cmd.exe (PID: 26708)
- cmd.exe (PID: 27020)
- cmd.exe (PID: 27400)
- cmd.exe (PID: 11932)
- cmd.exe (PID: 13500)
- cmd.exe (PID: 14040)
- cmd.exe (PID: 27616)
- cmd.exe (PID: 13272)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 15596)
- cmd.exe (PID: 15148)
- cmd.exe (PID: 27664)
- cmd.exe (PID: 27792)
- cmd.exe (PID: 28500)
- cmd.exe (PID: 17232)
- cmd.exe (PID: 27956)
- cmd.exe (PID: 28328)
- cmd.exe (PID: 28420)
- cmd.exe (PID: 18908)
- cmd.exe (PID: 19616)
- cmd.exe (PID: 20980)
- cmd.exe (PID: 28592)
- cmd.exe (PID: 19064)
- cmd.exe (PID: 20304)
- cmd.exe (PID: 28856)
- cmd.exe (PID: 29144)
- cmd.exe (PID: 29040)
- cmd.exe (PID: 29376)
- cmd.exe (PID: 29584)
- cmd.exe (PID: 28988)
- cmd.exe (PID: 29492)
- cmd.exe (PID: 29760)
- cmd.exe (PID: 30028)
- cmd.exe (PID: 25504)
- cmd.exe (PID: 30356)
- cmd.exe (PID: 30476)
- cmd.exe (PID: 30628)
- cmd.exe (PID: 30696)
- cmd.exe (PID: 24520)
- cmd.exe (PID: 22700)
- cmd.exe (PID: 23868)
- cmd.exe (PID: 15460)
- cmd.exe (PID: 22872)
- cmd.exe (PID: 12000)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 30988)
- cmd.exe (PID: 31556)
- cmd.exe (PID: 31668)
- cmd.exe (PID: 30772)
- cmd.exe (PID: 31348)
- cmd.exe (PID: 31680)
- cmd.exe (PID: 31084)
- cmd.exe (PID: 30236)
- cmd.exe (PID: 21092)
- cmd.exe (PID: 22908)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 15004)
- cmd.exe (PID: 31792)
- cmd.exe (PID: 32012)
- cmd.exe (PID: 32172)
- cmd.exe (PID: 31924)
- cmd.exe (PID: 32372)
Executes JavaScript directly as a command
- cmd.exe (PID: 2044)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 5444)
- cmd.exe (PID: 1652)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 5924)
- cmd.exe (PID: 1932)
- cmd.exe (PID: 4856)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7668)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 4168)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8408)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 8644)
- cmd.exe (PID: 8776)
- cmd.exe (PID: 8892)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 9124)
- cmd.exe (PID: 9268)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 9404)
- cmd.exe (PID: 9528)
- cmd.exe (PID: 9644)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 9912)
- cmd.exe (PID: 10176)
- cmd.exe (PID: 9876)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 10028)
- cmd.exe (PID: 10320)
- cmd.exe (PID: 10556)
- cmd.exe (PID: 10708)
- cmd.exe (PID: 10852)
- cmd.exe (PID: 10948)
- cmd.exe (PID: 11072)
- cmd.exe (PID: 11192)
- cmd.exe (PID: 11624)
- cmd.exe (PID: 11304)
- cmd.exe (PID: 11452)
- cmd.exe (PID: 11748)
- cmd.exe (PID: 12232)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 11948)
- cmd.exe (PID: 12932)
- cmd.exe (PID: 13204)
- cmd.exe (PID: 12808)
- cmd.exe (PID: 13368)
- cmd.exe (PID: 12728)
- cmd.exe (PID: 13524)
- cmd.exe (PID: 13664)
- cmd.exe (PID: 13828)
- cmd.exe (PID: 14136)
- cmd.exe (PID: 14304)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 14024)
- cmd.exe (PID: 14628)
- cmd.exe (PID: 14788)
- cmd.exe (PID: 14496)
- cmd.exe (PID: 15052)
- cmd.exe (PID: 15152)
- cmd.exe (PID: 15292)
- cmd.exe (PID: 14892)
- cmd.exe (PID: 15188)
- cmd.exe (PID: 15464)
- cmd.exe (PID: 15616)
- cmd.exe (PID: 15728)
- cmd.exe (PID: 15828)
- cmd.exe (PID: 16224)
- cmd.exe (PID: 16008)
- cmd.exe (PID: 15840)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 16480)
- cmd.exe (PID: 16748)
- cmd.exe (PID: 16904)
- cmd.exe (PID: 17044)
- cmd.exe (PID: 17176)
- cmd.exe (PID: 17312)
- cmd.exe (PID: 17468)
- cmd.exe (PID: 17724)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 16776)
- cmd.exe (PID: 18016)
- cmd.exe (PID: 17640)
- cmd.exe (PID: 18292)
- cmd.exe (PID: 17884)
- cmd.exe (PID: 18584)
- cmd.exe (PID: 18728)
- cmd.exe (PID: 13932)
- cmd.exe (PID: 19092)
- cmd.exe (PID: 19268)
- cmd.exe (PID: 18912)
- cmd.exe (PID: 18776)
- cmd.exe (PID: 17704)
- cmd.exe (PID: 19532)
- cmd.exe (PID: 18436)
- cmd.exe (PID: 19656)
- cmd.exe (PID: 19828)
- cmd.exe (PID: 19964)
- cmd.exe (PID: 20212)
- cmd.exe (PID: 20436)
- cmd.exe (PID: 19992)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 20548)
- cmd.exe (PID: 20864)
- cmd.exe (PID: 21104)
- cmd.exe (PID: 20712)
- cmd.exe (PID: 21384)
- cmd.exe (PID: 21176)
- cmd.exe (PID: 9760)
- cmd.exe (PID: 21508)
- cmd.exe (PID: 21784)
- cmd.exe (PID: 21900)
- cmd.exe (PID: 22092)
- cmd.exe (PID: 22220)
- cmd.exe (PID: 22392)
- cmd.exe (PID: 23008)
- cmd.exe (PID: 23140)
- cmd.exe (PID: 23428)
- cmd.exe (PID: 23788)
- cmd.exe (PID: 24092)
- cmd.exe (PID: 16136)
- cmd.exe (PID: 23632)
- cmd.exe (PID: 24208)
- cmd.exe (PID: 24420)
- cmd.exe (PID: 15560)
- cmd.exe (PID: 24320)
- cmd.exe (PID: 25252)
- cmd.exe (PID: 24896)
- cmd.exe (PID: 25072)
- cmd.exe (PID: 24676)
- cmd.exe (PID: 25444)
- cmd.exe (PID: 22696)
- cmd.exe (PID: 16716)
- cmd.exe (PID: 3092)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 22944)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 25612)
- cmd.exe (PID: 25856)
- cmd.exe (PID: 26464)
- cmd.exe (PID: 18508)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 25984)
- cmd.exe (PID: 26220)
- cmd.exe (PID: 23936)
- cmd.exe (PID: 8484)
- cmd.exe (PID: 23292)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 10540)
- cmd.exe (PID: 12004)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 10920)
- cmd.exe (PID: 26708)
- cmd.exe (PID: 27020)
- cmd.exe (PID: 27616)
- cmd.exe (PID: 11932)
- cmd.exe (PID: 13500)
- cmd.exe (PID: 27400)
- cmd.exe (PID: 14040)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 13272)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 15596)
- cmd.exe (PID: 15148)
- cmd.exe (PID: 27664)
- cmd.exe (PID: 27792)
- cmd.exe (PID: 28328)
- cmd.exe (PID: 28500)
- cmd.exe (PID: 17232)
- cmd.exe (PID: 28420)
- cmd.exe (PID: 18908)
- cmd.exe (PID: 19616)
- cmd.exe (PID: 27956)
- cmd.exe (PID: 28592)
- cmd.exe (PID: 20980)
- cmd.exe (PID: 20304)
- cmd.exe (PID: 28856)
- cmd.exe (PID: 29040)
- cmd.exe (PID: 29144)
- cmd.exe (PID: 19064)
- cmd.exe (PID: 29376)
- cmd.exe (PID: 28988)
- cmd.exe (PID: 29584)
- cmd.exe (PID: 29492)
- cmd.exe (PID: 29760)
- cmd.exe (PID: 30028)
- cmd.exe (PID: 25504)
- cmd.exe (PID: 30356)
- cmd.exe (PID: 30476)
- cmd.exe (PID: 30628)
- cmd.exe (PID: 24520)
- cmd.exe (PID: 15460)
- cmd.exe (PID: 22700)
- cmd.exe (PID: 30696)
- cmd.exe (PID: 22872)
- cmd.exe (PID: 12000)
- cmd.exe (PID: 23868)
- cmd.exe (PID: 30772)
- cmd.exe (PID: 30988)
- cmd.exe (PID: 31556)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 31668)
- cmd.exe (PID: 31348)
- cmd.exe (PID: 31680)
- cmd.exe (PID: 31084)
- cmd.exe (PID: 22908)
- cmd.exe (PID: 30236)
- cmd.exe (PID: 15004)
- cmd.exe (PID: 21092)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 31792)
- cmd.exe (PID: 31924)
- cmd.exe (PID: 32172)
- cmd.exe (PID: 32012)
- cmd.exe (PID: 32372)
Executing commands from a ".bat" file
- cmd.exe (PID: 3888)
- cmd.exe (PID: 2044)
- cmd.exe (PID: 1652)
- cmd.exe (PID: 5444)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 5924)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 4856)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 1932)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7668)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4168)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 8408)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 8644)
- cmd.exe (PID: 8892)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 9124)
- cmd.exe (PID: 8776)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 9268)
- cmd.exe (PID: 9404)
- cmd.exe (PID: 9528)
- cmd.exe (PID: 9644)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 9912)
- cmd.exe (PID: 10028)
- cmd.exe (PID: 10176)
- cmd.exe (PID: 9876)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 10320)
- cmd.exe (PID: 10708)
- cmd.exe (PID: 10852)
- cmd.exe (PID: 10948)
- cmd.exe (PID: 10556)
- cmd.exe (PID: 11072)
- cmd.exe (PID: 11304)
- cmd.exe (PID: 11192)
- cmd.exe (PID: 11452)
- cmd.exe (PID: 11748)
- cmd.exe (PID: 11948)
- cmd.exe (PID: 11624)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 12232)
- cmd.exe (PID: 12728)
- cmd.exe (PID: 13204)
- cmd.exe (PID: 12808)
- cmd.exe (PID: 13368)
- cmd.exe (PID: 12932)
- cmd.exe (PID: 13524)
- cmd.exe (PID: 13664)
- cmd.exe (PID: 13828)
- cmd.exe (PID: 14136)
- cmd.exe (PID: 14304)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 14024)
- cmd.exe (PID: 14628)
- cmd.exe (PID: 14788)
- cmd.exe (PID: 14496)
- cmd.exe (PID: 15152)
- cmd.exe (PID: 15292)
- cmd.exe (PID: 14892)
- cmd.exe (PID: 15052)
- cmd.exe (PID: 15464)
- cmd.exe (PID: 15616)
- cmd.exe (PID: 15828)
- cmd.exe (PID: 15728)
- cmd.exe (PID: 15188)
- cmd.exe (PID: 16008)
- cmd.exe (PID: 16224)
- cmd.exe (PID: 15840)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 16480)
- cmd.exe (PID: 16904)
- cmd.exe (PID: 16748)
- cmd.exe (PID: 17044)
- cmd.exe (PID: 17176)
- cmd.exe (PID: 17312)
- cmd.exe (PID: 16776)
- cmd.exe (PID: 17468)
- cmd.exe (PID: 17724)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 17884)
- cmd.exe (PID: 18016)
- cmd.exe (PID: 18292)
- cmd.exe (PID: 13932)
- cmd.exe (PID: 17640)
- cmd.exe (PID: 18584)
- cmd.exe (PID: 18728)
- cmd.exe (PID: 18912)
- cmd.exe (PID: 19268)
- cmd.exe (PID: 18436)
- cmd.exe (PID: 19092)
- cmd.exe (PID: 17704)
- cmd.exe (PID: 19532)
- cmd.exe (PID: 19656)
- cmd.exe (PID: 18776)
- cmd.exe (PID: 19828)
- cmd.exe (PID: 19964)
- cmd.exe (PID: 20212)
- cmd.exe (PID: 20436)
- cmd.exe (PID: 19992)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 20548)
- cmd.exe (PID: 20712)
- cmd.exe (PID: 20864)
- cmd.exe (PID: 21104)
- cmd.exe (PID: 21176)
- cmd.exe (PID: 21384)
- cmd.exe (PID: 9760)
- cmd.exe (PID: 21508)
- cmd.exe (PID: 21784)
- cmd.exe (PID: 21900)
- cmd.exe (PID: 22092)
- cmd.exe (PID: 22220)
- cmd.exe (PID: 22392)
- cmd.exe (PID: 23428)
- cmd.exe (PID: 23140)
- cmd.exe (PID: 16136)
- cmd.exe (PID: 23008)
- cmd.exe (PID: 23788)
- cmd.exe (PID: 23632)
- cmd.exe (PID: 24092)
- cmd.exe (PID: 24208)
- cmd.exe (PID: 24420)
- cmd.exe (PID: 15560)
- cmd.exe (PID: 24320)
- cmd.exe (PID: 24676)
- cmd.exe (PID: 24896)
- cmd.exe (PID: 25072)
- cmd.exe (PID: 25252)
- cmd.exe (PID: 16716)
- cmd.exe (PID: 22696)
- cmd.exe (PID: 22944)
- cmd.exe (PID: 25444)
- cmd.exe (PID: 3092)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 25612)
- cmd.exe (PID: 25856)
- cmd.exe (PID: 25984)
- cmd.exe (PID: 18508)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 26220)
- cmd.exe (PID: 26464)
- cmd.exe (PID: 23936)
- cmd.exe (PID: 8484)
- cmd.exe (PID: 23292)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 10540)
- cmd.exe (PID: 10920)
- cmd.exe (PID: 12004)
- cmd.exe (PID: 27020)
- cmd.exe (PID: 27400)
- cmd.exe (PID: 26708)
- cmd.exe (PID: 13500)
- cmd.exe (PID: 11932)
- cmd.exe (PID: 14040)
- cmd.exe (PID: 27616)
- cmd.exe (PID: 13272)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 15596)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 27664)
- cmd.exe (PID: 27792)
- cmd.exe (PID: 15148)
- cmd.exe (PID: 28328)
- cmd.exe (PID: 28500)
- cmd.exe (PID: 17232)
- cmd.exe (PID: 18908)
- cmd.exe (PID: 19616)
- cmd.exe (PID: 27956)
- cmd.exe (PID: 28420)
- cmd.exe (PID: 28592)
- cmd.exe (PID: 20980)
- cmd.exe (PID: 19064)
- cmd.exe (PID: 20304)
- cmd.exe (PID: 29040)
- cmd.exe (PID: 29144)
- cmd.exe (PID: 28856)
- cmd.exe (PID: 29584)
- cmd.exe (PID: 28988)
- cmd.exe (PID: 25504)
- cmd.exe (PID: 29376)
- cmd.exe (PID: 29492)
- cmd.exe (PID: 29760)
- cmd.exe (PID: 30028)
- cmd.exe (PID: 30356)
- cmd.exe (PID: 30628)
- cmd.exe (PID: 30696)
- cmd.exe (PID: 30476)
- cmd.exe (PID: 15460)
- cmd.exe (PID: 22700)
- cmd.exe (PID: 23868)
- cmd.exe (PID: 24520)
- cmd.exe (PID: 22872)
- cmd.exe (PID: 12000)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 30772)
- cmd.exe (PID: 30988)
- cmd.exe (PID: 31556)
- cmd.exe (PID: 31668)
- cmd.exe (PID: 31680)
- cmd.exe (PID: 31084)
- cmd.exe (PID: 31348)
- cmd.exe (PID: 22908)
- cmd.exe (PID: 21092)
- cmd.exe (PID: 30236)
- cmd.exe (PID: 31792)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 15004)
- cmd.exe (PID: 32012)
- cmd.exe (PID: 32172)
- cmd.exe (PID: 31924)
- cmd.exe (PID: 32372)
INFO
Launching a file from the Startup directory
- cmd.exe (PID: 3888)
- cmd.exe (PID: 23788)
Reads Internet Explorer settings
- mshta.exe (PID: 1496)
- mshta.exe (PID: 6148)
- mshta.exe (PID: 3924)
- mshta.exe (PID: 4644)
- mshta.exe (PID: 2448)
- mshta.exe (PID: 6868)
- mshta.exe (PID: 7180)
- mshta.exe (PID: 7324)
- mshta.exe (PID: 7424)
- mshta.exe (PID: 3832)
- mshta.exe (PID: 7512)
- mshta.exe (PID: 7648)
- mshta.exe (PID: 7768)
- mshta.exe (PID: 7892)
- mshta.exe (PID: 8172)
- mshta.exe (PID: 8136)
- mshta.exe (PID: 6232)
- mshta.exe (PID: 8168)
- mshta.exe (PID: 8280)
- mshta.exe (PID: 8392)
- mshta.exe (PID: 8536)
- mshta.exe (PID: 8628)
- mshta.exe (PID: 8752)
- mshta.exe (PID: 2228)
- mshta.exe (PID: 8872)
- mshta.exe (PID: 8976)
- mshta.exe (PID: 9088)
- mshta.exe (PID: 9276)
- mshta.exe (PID: 9380)
- mshta.exe (PID: 9508)
- mshta.exe (PID: 9752)
- mshta.exe (PID: 10008)
- mshta.exe (PID: 9892)
- mshta.exe (PID: 9628)
- mshta.exe (PID: 5764)
- mshta.exe (PID: 10304)
- mshta.exe (PID: 10112)
- mshta.exe (PID: 10116)
- mshta.exe (PID: 10656)
- mshta.exe (PID: 10780)
- mshta.exe (PID: 10928)
- mshta.exe (PID: 10528)
- mshta.exe (PID: 11056)
- mshta.exe (PID: 11184)
- mshta.exe (PID: 11276)
- mshta.exe (PID: 11840)
- mshta.exe (PID: 11728)
- mshta.exe (PID: 11432)
- mshta.exe (PID: 11564)
- mshta.exe (PID: 12048)
- mshta.exe (PID: 12240)
- mshta.exe (PID: 12864)
- mshta.exe (PID: 12984)
- mshta.exe (PID: 13264)
- mshta.exe (PID: 13300)
- mshta.exe (PID: 13336)
- mshta.exe (PID: 13484)
- mshta.exe (PID: 13612)
- mshta.exe (PID: 13800)
- mshta.exe (PID: 13936)
- mshta.exe (PID: 14272)
- mshta.exe (PID: 13776)
- mshta.exe (PID: 14460)
- mshta.exe (PID: 14076)
- mshta.exe (PID: 14596)
- mshta.exe (PID: 14700)
- mshta.exe (PID: 14852)
- mshta.exe (PID: 14992)
- mshta.exe (PID: 15124)
- mshta.exe (PID: 14936)
- mshta.exe (PID: 15260)
- mshta.exe (PID: 15544)
- mshta.exe (PID: 15440)
- mshta.exe (PID: 15700)
- mshta.exe (PID: 15844)
- mshta.exe (PID: 15924)
- mshta.exe (PID: 16148)
- mshta.exe (PID: 6140)
- mshta.exe (PID: 16232)
- mshta.exe (PID: 16488)
- mshta.exe (PID: 16848)
- mshta.exe (PID: 16792)
- mshta.exe (PID: 17008)
- mshta.exe (PID: 17140)
- mshta.exe (PID: 17272)
- mshta.exe (PID: 16396)
- mshta.exe (PID: 17440)
- mshta.exe (PID: 17716)
- mshta.exe (PID: 17812)
- mshta.exe (PID: 17556)
- mshta.exe (PID: 18416)
- mshta.exe (PID: 18044)
- mshta.exe (PID: 17992)
- mshta.exe (PID: 18196)
- mshta.exe (PID: 18716)
- mshta.exe (PID: 18888)
- mshta.exe (PID: 18572)
- mshta.exe (PID: 19172)
- mshta.exe (PID: 19436)
- mshta.exe (PID: 18764)
- mshta.exe (PID: 19136)
- mshta.exe (PID: 7756)
- mshta.exe (PID: 19488)
- mshta.exe (PID: 19628)
- mshta.exe (PID: 19908)
- mshta.exe (PID: 20100)
- mshta.exe (PID: 20316)
- mshta.exe (PID: 19772)
- mshta.exe (PID: 2148)
- mshta.exe (PID: 19772)
- mshta.exe (PID: 20532)
- mshta.exe (PID: 20668)
- mshta.exe (PID: 20816)
- mshta.exe (PID: 20912)
- mshta.exe (PID: 21184)
- mshta.exe (PID: 21368)
- mshta.exe (PID: 20572)
- mshta.exe (PID: 21408)
- mshta.exe (PID: 21652)
- mshta.exe (PID: 21880)
- mshta.exe (PID: 22040)
- mshta.exe (PID: 22328)
- mshta.exe (PID: 22460)
- mshta.exe (PID: 22184)
- mshta.exe (PID: 23184)
- mshta.exe (PID: 23416)
- mshta.exe (PID: 2272)
- mshta.exe (PID: 22604)
- mshta.exe (PID: 23700)
- mshta.exe (PID: 23840)
- mshta.exe (PID: 24156)
- mshta.exe (PID: 24316)
- mshta.exe (PID: 23812)
- mshta.exe (PID: 4156)
- mshta.exe (PID: 24608)
- mshta.exe (PID: 24888)
- mshta.exe (PID: 25128)
- mshta.exe (PID: 25332)
- mshta.exe (PID: 24988)
- mshta.exe (PID: 22676)
- mshta.exe (PID: 25212)
- mshta.exe (PID: 25512)
- mshta.exe (PID: 20932)
- mshta.exe (PID: 4684)
- mshta.exe (PID: 7332)
- mshta.exe (PID: 5340)
- mshta.exe (PID: 24020)
- mshta.exe (PID: 25976)
- mshta.exe (PID: 26044)
- mshta.exe (PID: 25808)
- mshta.exe (PID: 26564)
- mshta.exe (PID: 19524)
- mshta.exe (PID: 25640)
- mshta.exe (PID: 26496)
- mshta.exe (PID: 9056)
- mshta.exe (PID: 9764)
- mshta.exe (PID: 10144)
- mshta.exe (PID: 26228)
- mshta.exe (PID: 10516)
- mshta.exe (PID: 10788)
- mshta.exe (PID: 11656)
- mshta.exe (PID: 26836)
- mshta.exe (PID: 26904)
- mshta.exe (PID: 27312)
- mshta.exe (PID: 12056)
- mshta.exe (PID: 13308)
- mshta.exe (PID: 6308)
- mshta.exe (PID: 12720)
- mshta.exe (PID: 1268)
- mshta.exe (PID: 14476)
- mshta.exe (PID: 15500)
- mshta.exe (PID: 16140)
- mshta.exe (PID: 9296)
- mshta.exe (PID: 16412)
- mshta.exe (PID: 27736)
- mshta.exe (PID: 27924)
- mshta.exe (PID: 28424)
- mshta.exe (PID: 28588)
- mshta.exe (PID: 25040)
- mshta.exe (PID: 18308)
- mshta.exe (PID: 6216)
- mshta.exe (PID: 19860)
- mshta.exe (PID: 18564)
- mshta.exe (PID: 19208)
- mshta.exe (PID: 26432)
- mshta.exe (PID: 20896)
- mshta.exe (PID: 29100)
- mshta.exe (PID: 29252)
- mshta.exe (PID: 28760)
- mshta.exe (PID: 28936)
- mshta.exe (PID: 21664)
- mshta.exe (PID: 28940)
- mshta.exe (PID: 29428)
- mshta.exe (PID: 29712)
- mshta.exe (PID: 29840)
- mshta.exe (PID: 30156)
- mshta.exe (PID: 29516)
- mshta.exe (PID: 30432)
- mshta.exe (PID: 30580)
- mshta.exe (PID: 29788)
- mshta.exe (PID: 23660)
- mshta.exe (PID: 24388)
- mshta.exe (PID: 24408)
- mshta.exe (PID: 7280)
- mshta.exe (PID: 23696)
- mshta.exe (PID: 25568)
- mshta.exe (PID: 7616)
- mshta.exe (PID: 13280)
- mshta.exe (PID: 31628)
- mshta.exe (PID: 25028)
- mshta.exe (PID: 30832)
- mshta.exe (PID: 31080)
- mshta.exe (PID: 31464)
- mshta.exe (PID: 31224)
- mshta.exe (PID: 26724)
- mshta.exe (PID: 26020)
- mshta.exe (PID: 11644)
- mshta.exe (PID: 13912)
- mshta.exe (PID: 27600)
- mshta.exe (PID: 15564)
- mshta.exe (PID: 31840)
- mshta.exe (PID: 31976)
- mshta.exe (PID: 32248)
- mshta.exe (PID: 32444)
- mshta.exe (PID: 32108)
- mshta.exe (PID: 32612)
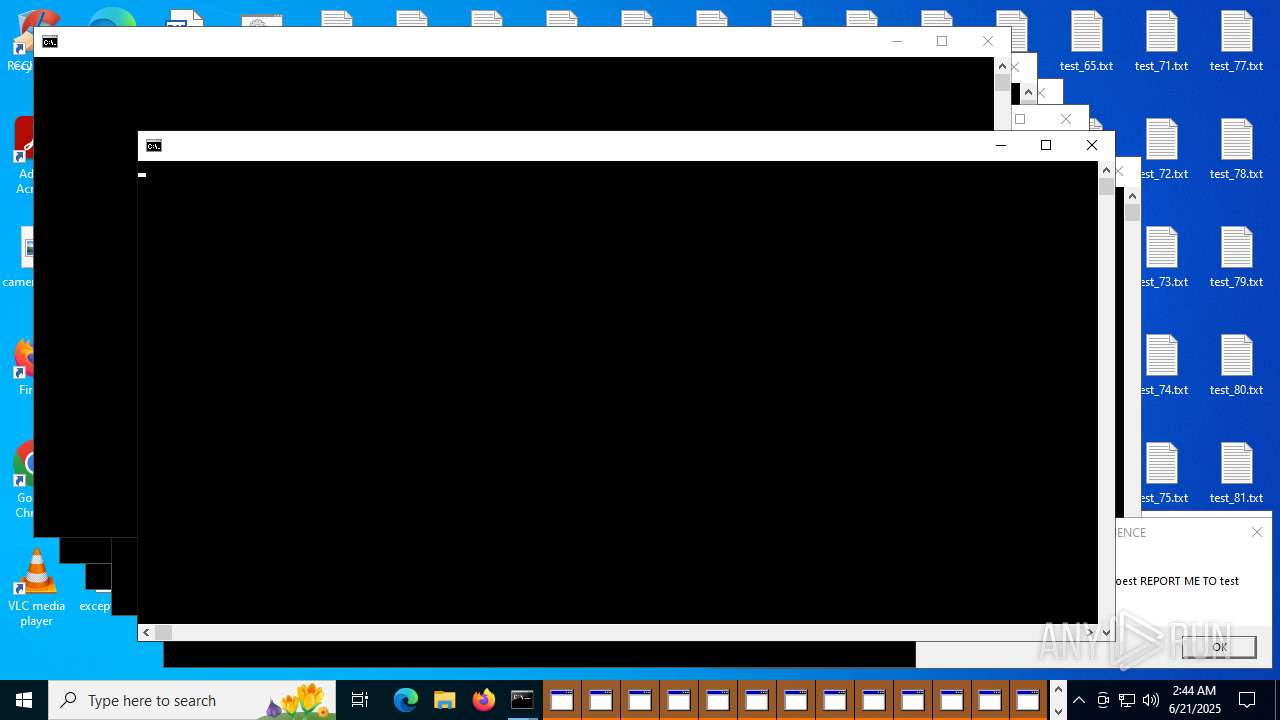
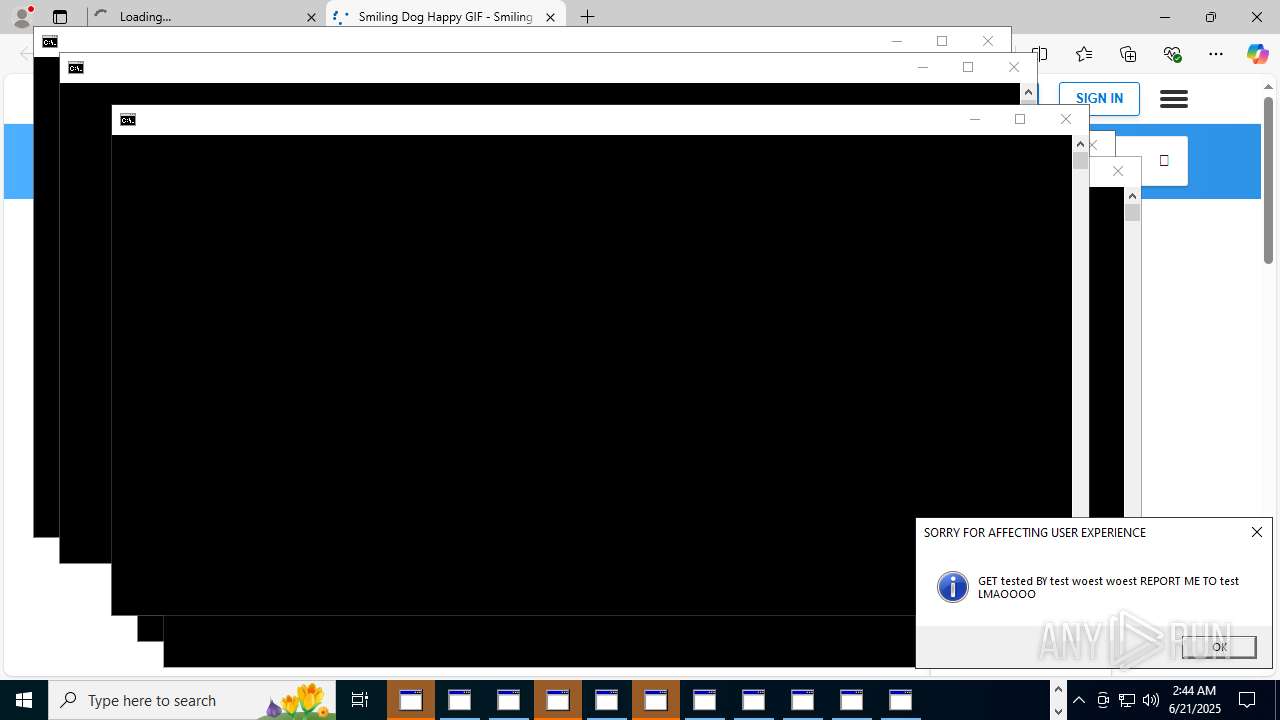
Manual execution by a user
- cmd.exe (PID: 7988)
Application launched itself
- msedge.exe (PID: 10400)
Checks proxy server information
- slui.exe (PID: 23524)
Reads the software policy settings
- slui.exe (PID: 23524)
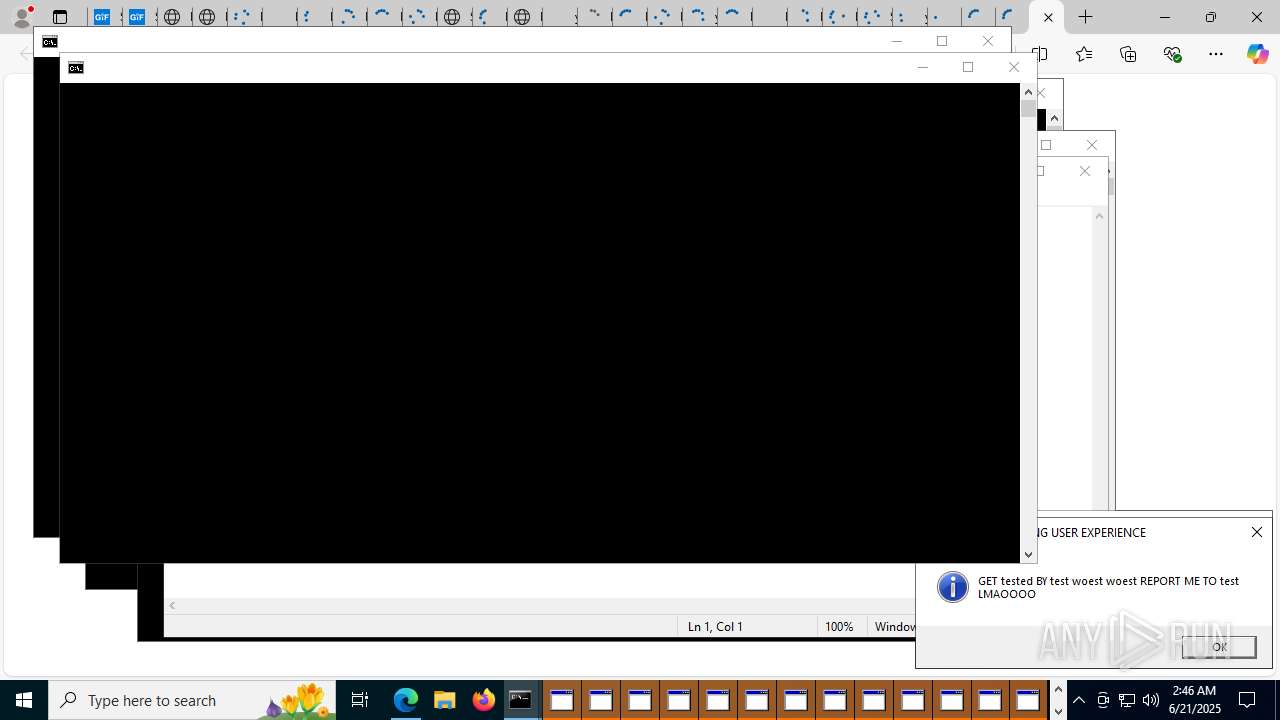
Reads security settings of Internet Explorer
- notepad.exe (PID: 13192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
960
Monitored processes
826
Malicious processes
223
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
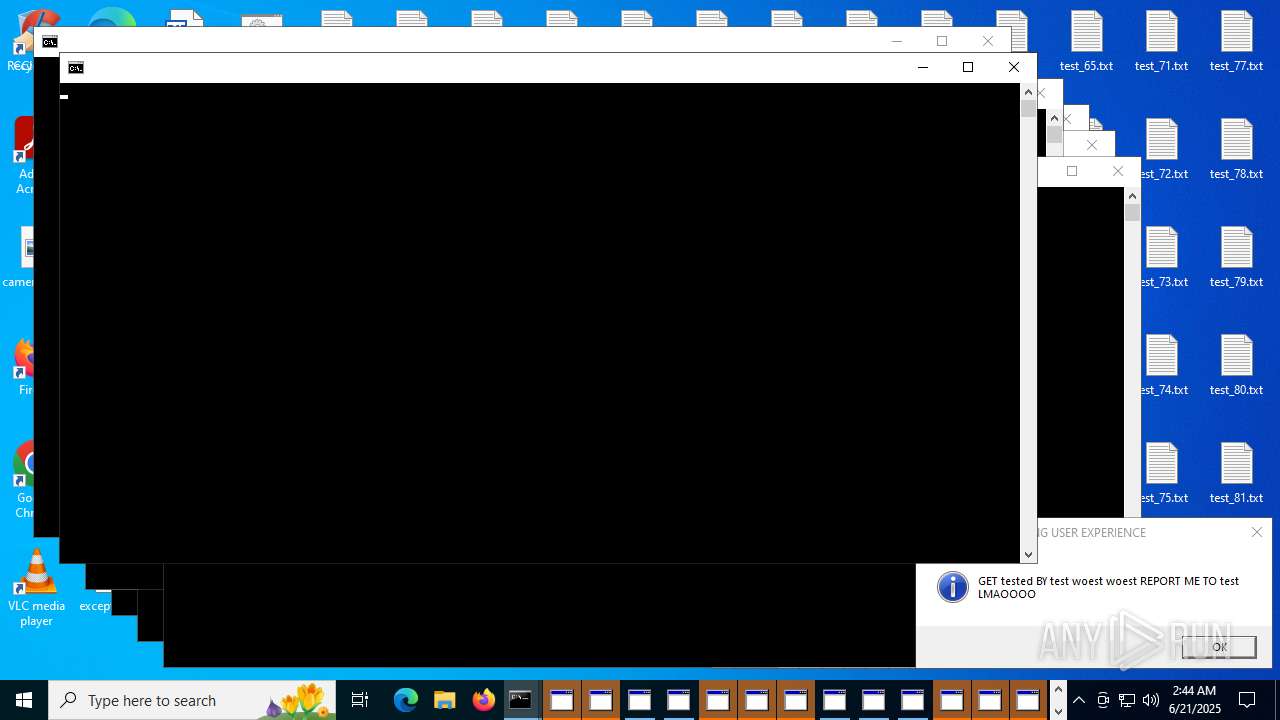
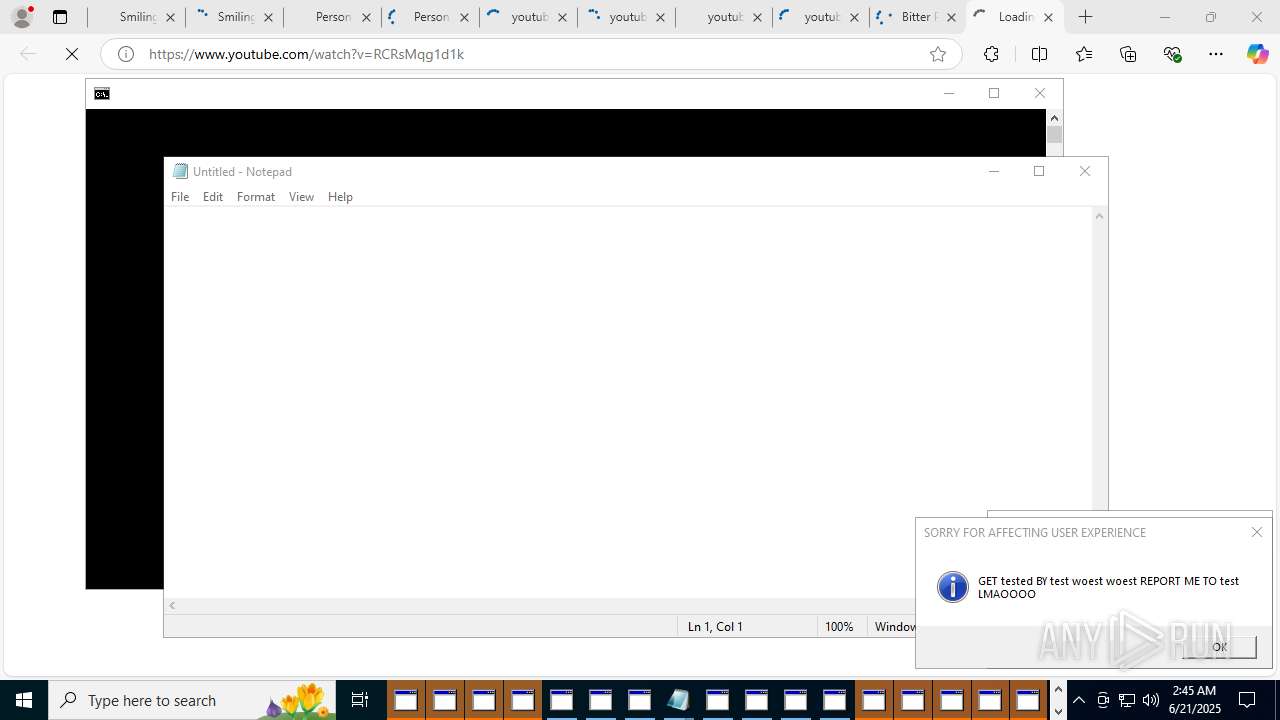
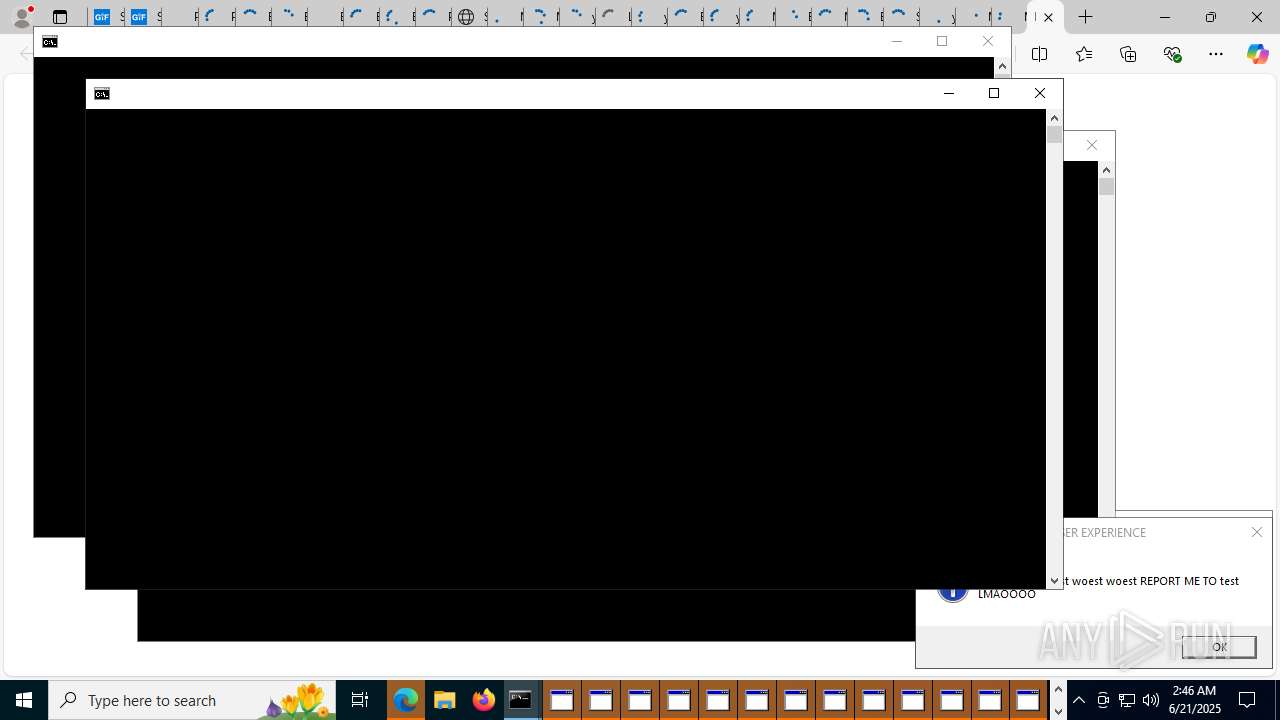
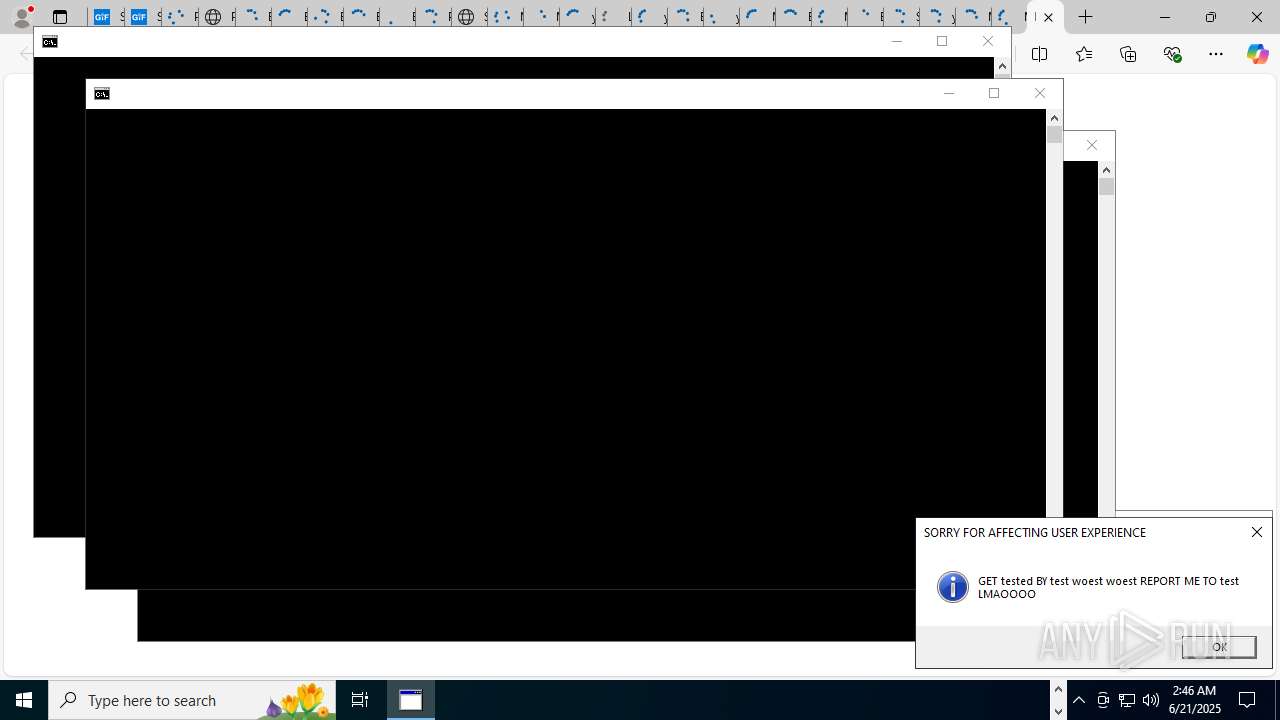
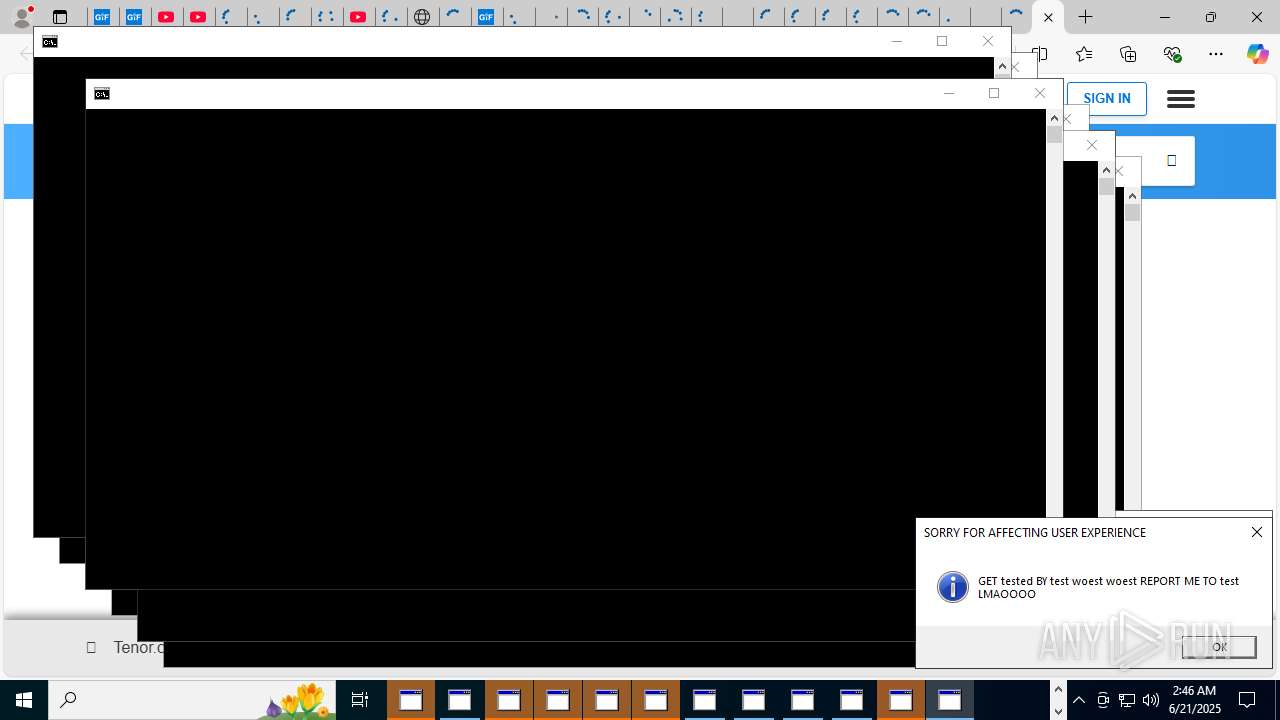
| 1268 | mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('GET tested BY test woest woest REPORT ME TO test LMAOOOO', 0, 'SORRY FOR AFFECTING USER EXPERIENCE', 64);close();" | C:\Windows\System32\mshta.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | C:\WINDOWS\system32\cmd.exe /K "copy_26477.bat" 17200000 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1496 | mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('GET tested BY test woest woest REPORT ME TO test LMAOOOO', 0, 'SORRY FOR AFFECTING USER EXPERIENCE', 64);close();" | C:\Windows\System32\mshta.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2576,i,5043542526679007172,9099923300496658962,262144 --variations-seed-version --mojo-platform-channel-handle=2572 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1652 | C:\WINDOWS\system32\cmd.exe /K "copy_19095.bat" 300000 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | notepad "" | C:\Windows\System32\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
89 286
Read events
88 777
Write events
509
Delete events
0
Modification events
| (PID) Process: | (10008) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (10008) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (10008) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (9784) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (9784) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (9784) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (9784) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (10400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (10400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (10400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
9
Suspicious files
343
Text files
633
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | cmd.exe | C:\Users\admin\Desktop\test_2.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 3888 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MyAutoStart.bat | text | |
MD5:988DB6360E6886AF17FCA78DB05183BF | SHA256:EBAED86D3022F0540D3CE0ED25B86CAD430CED6A9404083042403BB12E0A63AC | |||
| 3888 | cmd.exe | C:\Users\admin\Desktop\test_6.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 3888 | cmd.exe | C:\Users\admin\Desktop\test_11.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 3888 | cmd.exe | C:\Users\admin\Desktop\test_1.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 3888 | cmd.exe | C:\Users\admin\Desktop\test_7.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 3888 | cmd.exe | C:\Users\admin\Desktop\test_3.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 3888 | cmd.exe | C:\Users\admin\Desktop\test_8.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 3888 | cmd.exe | C:\Users\admin\Desktop\test_14.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 3888 | cmd.exe | C:\Users\admin\Desktop\test_9.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
793
TCP/UDP connections
423
DNS requests
169
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.131:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.68:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.68:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.131:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.131:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | GET | 200 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=51&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1750473883&lafgdate=0 | unknown | binary | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3396 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
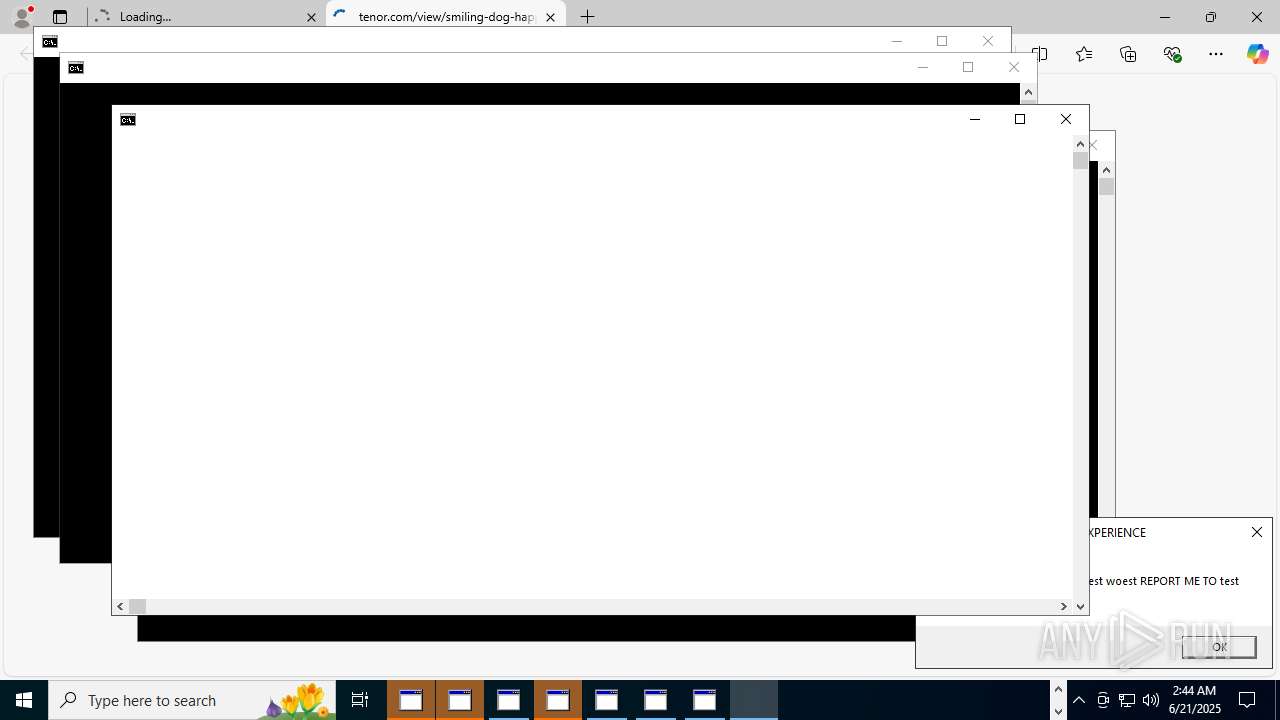
tenor.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
11448 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
11448 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
11448 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
11448 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |