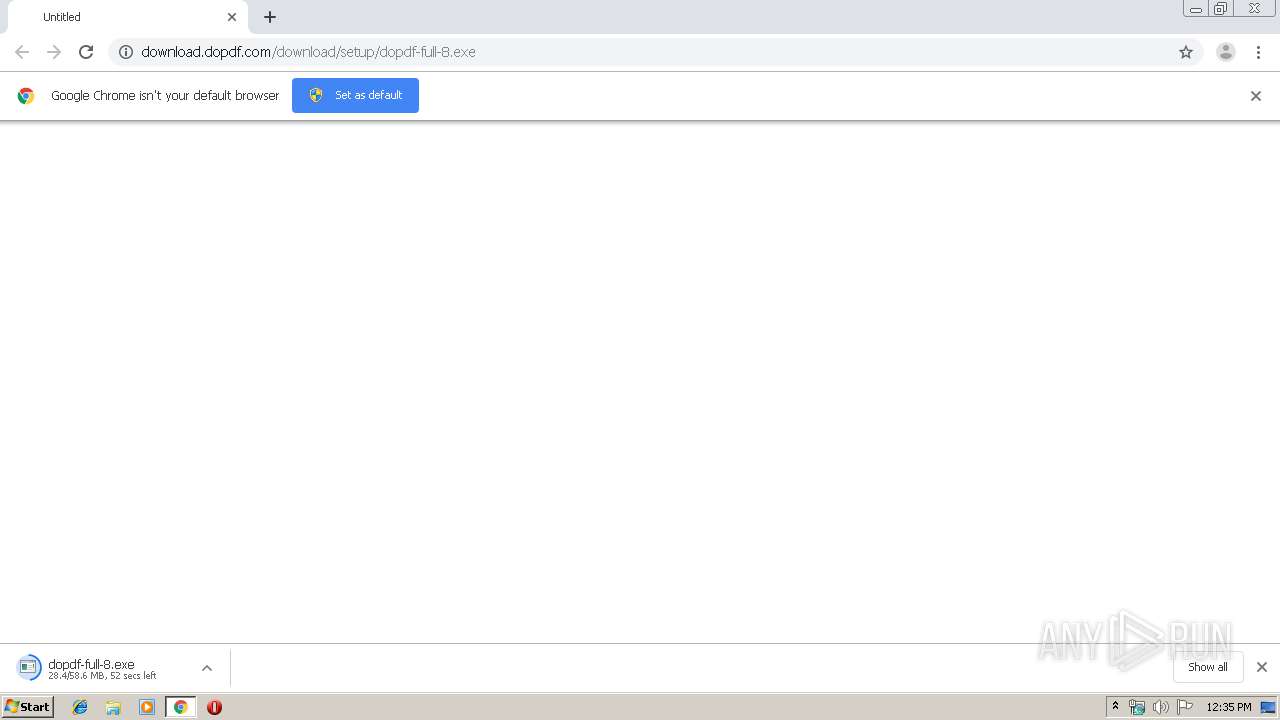
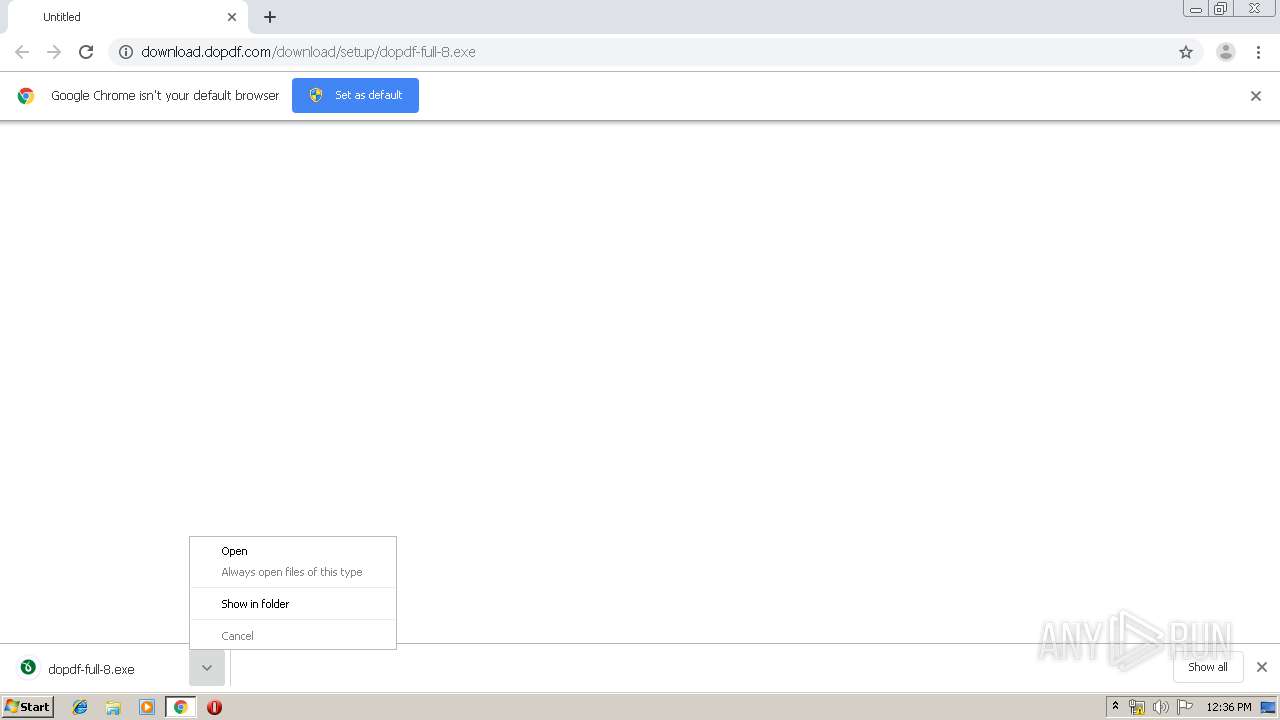
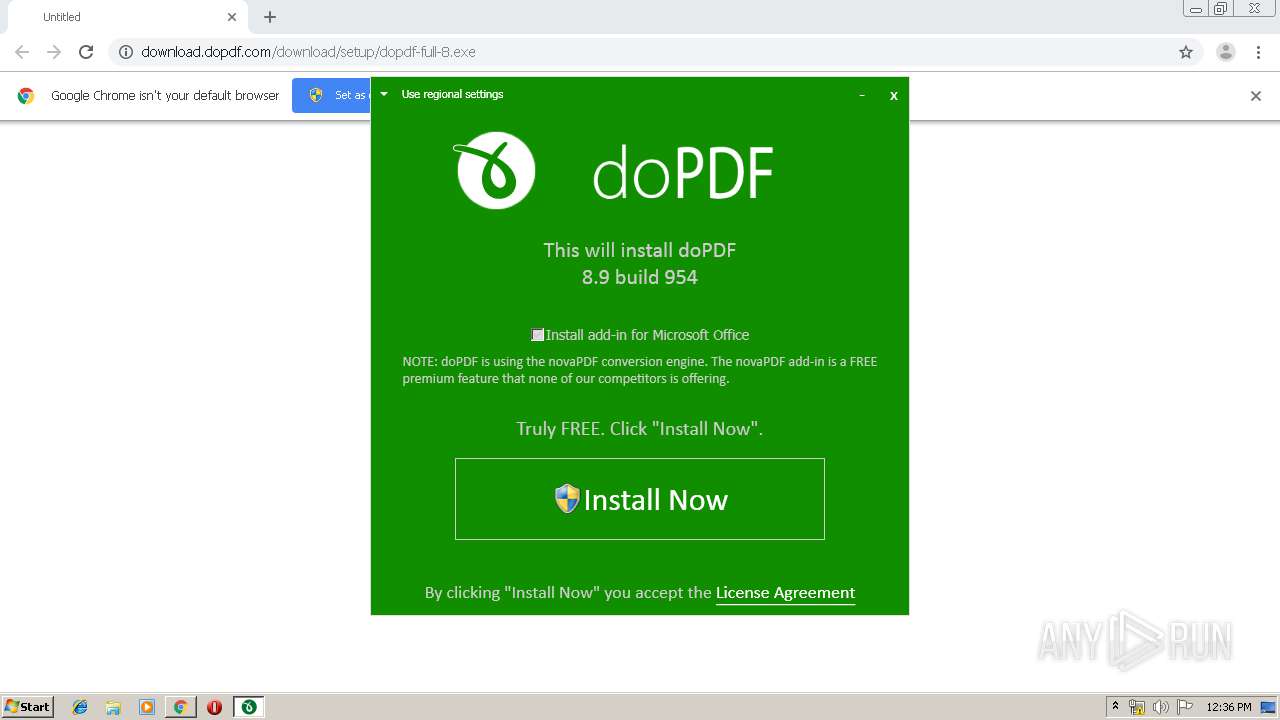
| URL: | http://download.dopdf.com/download/setup/dopdf-full-8.exe |
| Full analysis: | https://app.any.run/tasks/c2d13d84-631c-4a82-899f-fabeec37e7f8 |
| Verdict: | Malicious activity |
| Analysis date: | September 02, 2019, 11:34:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B39826609E910808AC8826D3A508038D |
| SHA1: | 5D938078A69CC410F5046661A777AD6C5CD54A35 |
| SHA256: | EB947AB101B4ADE3E1E347D4F30503C5DA8A124CADE0CB673C9B55A15D772BDD |
| SSDEEP: | 3:N1KaKEloDt8LxQg8VC0IyAn:Ca5et8t0VCxyA |
MALICIOUS
Application was dropped or rewritten from another process
- dopdf-full-8.exe (PID: 2696)
- dopdf-full-8.exe (PID: 3920)
- novapdf.exe (PID: 3632)
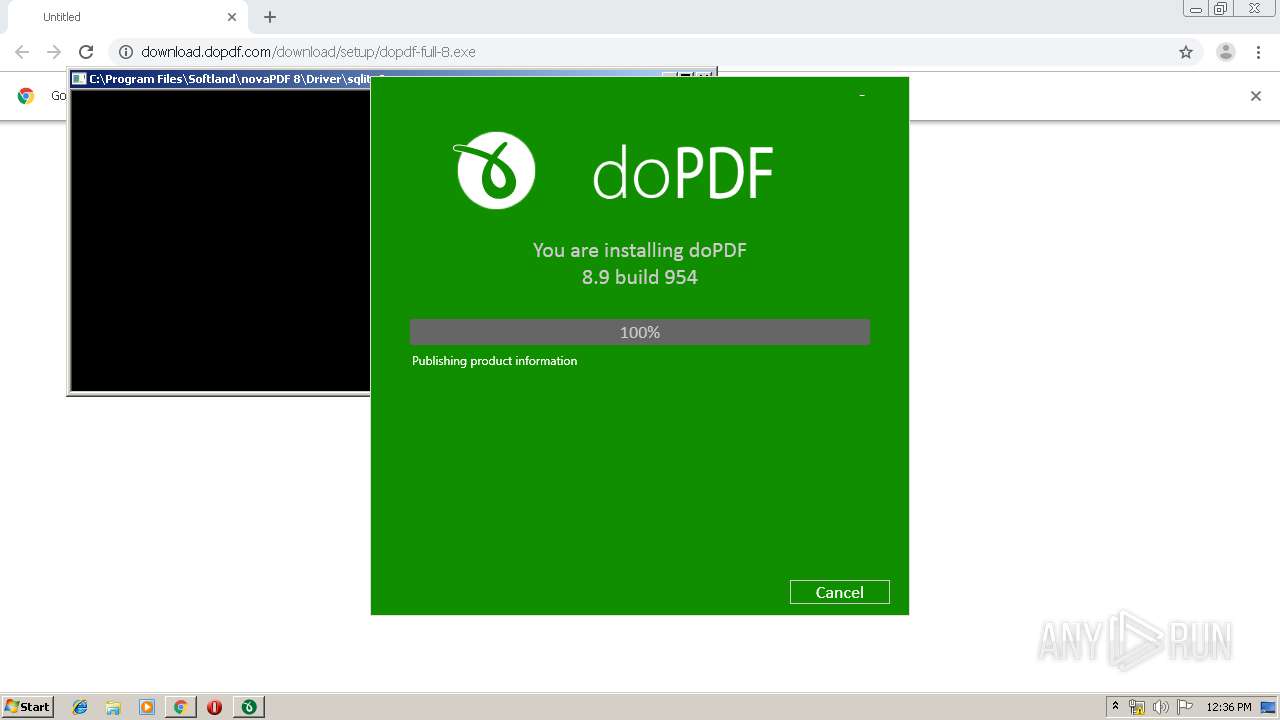
- sqlite3.exe (PID: 4000)
- sqlite3.exe (PID: 3304)
- sqlite3.exe (PID: 3448)
- novapdfs.exe (PID: 4076)
- Startup.exe (PID: 1680)
Loads dropped or rewritten executable
- dopdf-full-8.exe (PID: 3920)
- MsiExec.exe (PID: 3536)
- spoolsv.exe (PID: 1204)
- novapdfs.exe (PID: 4076)
- spoolsv.exe (PID: 2088)
- spoolsv.exe (PID: 3744)
- Startup.exe (PID: 1680)
Changes settings of System certificates
- msiexec.exe (PID: 2292)
Changes the autorun value in the registry
- novapdf.exe (PID: 3632)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1220)
Uses Task Scheduler to run other applications
- msiexec.exe (PID: 2292)
SUSPICIOUS
Executable content was dropped or overwritten
- dopdf-full-8.exe (PID: 3920)
- chrome.exe (PID: 3568)
- dopdf-full-8.exe (PID: 2696)
- rundll32.exe (PID: 3764)
- novapdf.exe (PID: 3632)
- rundll32.exe (PID: 4056)
- msiexec.exe (PID: 2292)
- spoolsv.exe (PID: 1204)
Reads Environment values
- dopdf-full-8.exe (PID: 3920)
- novapdfs.exe (PID: 4076)
- Startup.exe (PID: 1680)
Starts itself from another location
- dopdf-full-8.exe (PID: 3920)
Executed as Windows Service
- vssvc.exe (PID: 4084)
- novapdfs.exe (PID: 4076)
- spoolsv.exe (PID: 2088)
- spoolsv.exe (PID: 3744)
Creates a software uninstall entry
- novapdf.exe (PID: 3632)
Searches for installed software
- novapdf.exe (PID: 3632)
Executed via COM
- DrvInst.exe (PID: 3992)
- DrvInst.exe (PID: 3312)
- DrvInst.exe (PID: 2532)
- rundll32.exe (PID: 2520)
Creates files in the program directory
- novapdf.exe (PID: 3632)
- sqlite3.exe (PID: 4000)
- sqlite3.exe (PID: 3304)
- sqlite3.exe (PID: 3448)
Adds / modifies Windows certificates
- msiexec.exe (PID: 2292)
Creates COM task schedule object
- MsiExec.exe (PID: 3536)
Creates files in the Windows directory
- msiexec.exe (PID: 2292)
- DrvInst.exe (PID: 3312)
- spoolsv.exe (PID: 1204)
- DrvInst.exe (PID: 2532)
- spoolsv.exe (PID: 2088)
- spoolsv.exe (PID: 3744)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 2292)
Removes files from Windows directory
- DrvInst.exe (PID: 3312)
- spoolsv.exe (PID: 1204)
- DrvInst.exe (PID: 2532)
- spoolsv.exe (PID: 3744)
Creates files in the driver directory
- DrvInst.exe (PID: 3312)
- DrvInst.exe (PID: 2532)
Changes IE settings (feature browser emulation)
- msiexec.exe (PID: 2292)
Reads Internet Cache Settings
- Startup.exe (PID: 1680)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3568)
INFO
Reads the hosts file
- chrome.exe (PID: 3568)
- chrome.exe (PID: 2932)
Reads Internet Cache Settings
- chrome.exe (PID: 3568)
Reads settings of System Certificates
- dopdf-full-8.exe (PID: 3920)
- Startup.exe (PID: 1680)
Low-level read access rights to disk partition
- vssvc.exe (PID: 4084)
Application launched itself
- chrome.exe (PID: 3568)
- msiexec.exe (PID: 2292)
Creates a software uninstall entry
- msiexec.exe (PID: 2292)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3852)
- MsiExec.exe (PID: 4036)
Creates files in the program directory
- msiexec.exe (PID: 2292)
- MsiExec.exe (PID: 2084)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2292)
- sqlite3.exe (PID: 4000)
- sqlite3.exe (PID: 3304)
- sqlite3.exe (PID: 3448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
45
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13783692089702013552 --mojo-platform-channel-handle=4056 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1204 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1220 | "schtasks.exe" /CREATE /SC DAILY /F /TN "doPDF Update" /ST 13:00:01 /TR "\"C:\Program Files\Softland\novaPDF 8\Driver\UpdateApplication.exe\" /oem=doPdf8_Softland /silent" /RU "USER-PC\admin" | C:\Windows\system32\schtasks.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17210956008885780665 --mojo-platform-channel-handle=4324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Softland\novaPDF 8\Driver\Startup.exe" /oem=doPdf8_Softland /close | C:\Program Files\Softland\novaPDF 8\Driver\Startup.exe | dopdf-full-8.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Startup Exit code: 0 Version: 8.9.954.0 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12668713057659475820 --mojo-platform-channel-handle=4012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | C:\Windows\system32\MsiExec.exe -Embedding A4425936FE24A7173403BA005D399729 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6081271175792194740 --mojo-platform-channel-handle=2556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fdea9d0,0x6fdea9e0,0x6fdea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 526
Read events
2 269
Write events
1 216
Delete events
41
Modification events
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3568-13211897698081375 |
Value: 259 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
508
Suspicious files
57
Text files
299
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169bd7.TMP | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e0d00640-24ce-4ca6-8cbc-05f62225e7c7.tmp | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169bd7.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
27
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | chrome.exe | GET | — | 151.139.239.32:80 | http://download.dopdf.com/download/setup/dopdf-full-8.exe | US | — | — | malicious |
1680 | Startup.exe | GET | — | 206.221.191.151:80 | http://www.dopdf.com/announcements/dopdf_ribbon_try_novapdf.html?&ctx=novapdf-ads-tab&tday=0&key=AAAA-BBBB-CCCC-DDDD-EEEE-FFFF-D0BD-F000 | US | — | — | whitelisted |
2932 | chrome.exe | GET | 206 | 151.139.239.32:80 | http://download.dopdf.com/download/setup/dopdf-full-8.exe | US | binary | 16.8 Mb | malicious |
2932 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
2292 | msiexec.exe | GET | 200 | 2.16.106.186:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.6 Kb | whitelisted |
2932 | chrome.exe | GET | 200 | 74.125.100.38:80 | http://r1---sn-5hnekn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.107.227&mm=28&mn=sn-5hnekn7s&ms=nvh&mt=1567424239&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.22.110:443 | clients4.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.23.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3920 | dopdf-full-8.exe | 206.221.191.157:443 | secure.novapdf.com | Choopa, LLC | US | unknown |
2932 | chrome.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
2292 | msiexec.exe | 2.16.106.186:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1680 | Startup.exe | 206.221.191.157:443 | secure.novapdf.com | Choopa, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.dopdf.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients4.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
secure.novapdf.com |
| unknown |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2932 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2932 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
Process | Message |
|---|---|
MsiExec.exe | 2019-09-02 12:36:35 ScanPorts dll started
|
MsiExec.exe | 2019-09-02 12:36:35 ScanFreePorts - Start
|
MsiExec.exe | 2019-09-02 12:36:35 ReadProcessIdVariable - CustomActionData=
|
MsiExec.exe | 2019-09-02 12:36:35 MsiGetProperty PROCESS_ID=3920
|
MsiExec.exe | 2019-09-02 12:36:35 InitPortScan - Start
|
MsiExec.exe | 2019-09-02 12:36:35 InitPortScan - End (ok)
|
MsiExec.exe | 2019-09-02 12:36:35 get properties...
|
MsiExec.exe | 2019-09-02 12:36:35 MsiGetProperty SCAN_START_PORT=8501
|
MsiExec.exe | 2019-09-02 12:36:35 MsiGetProperty SCAN_END_PORT=55000
|
MsiExec.exe | 2019-09-02 12:36:35 MsiGetProperty SERVICE_INSTALL_PORT=-1
|