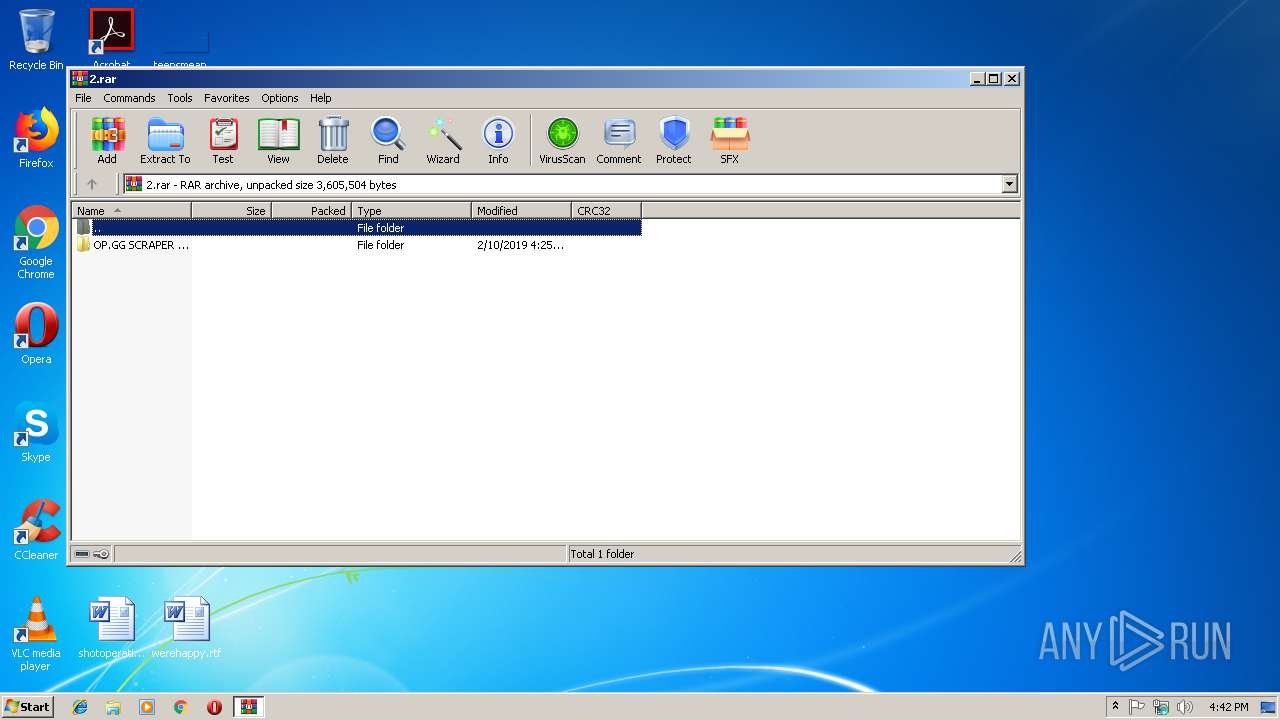
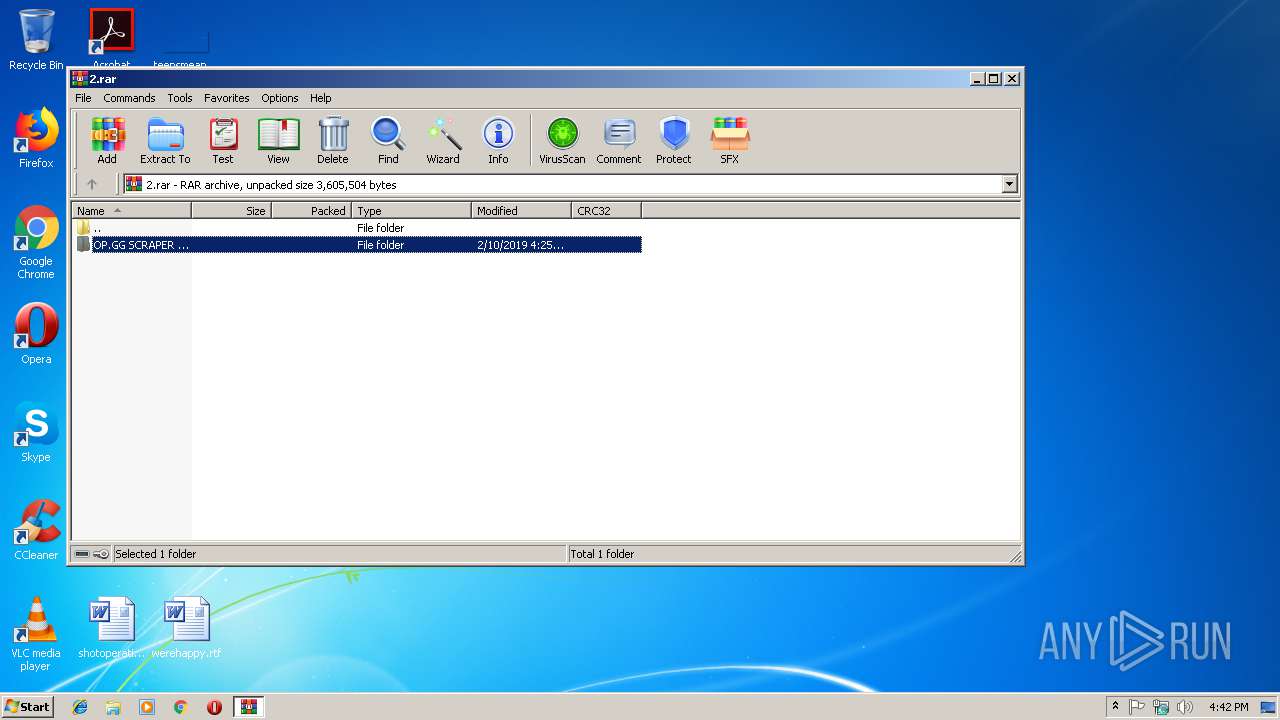
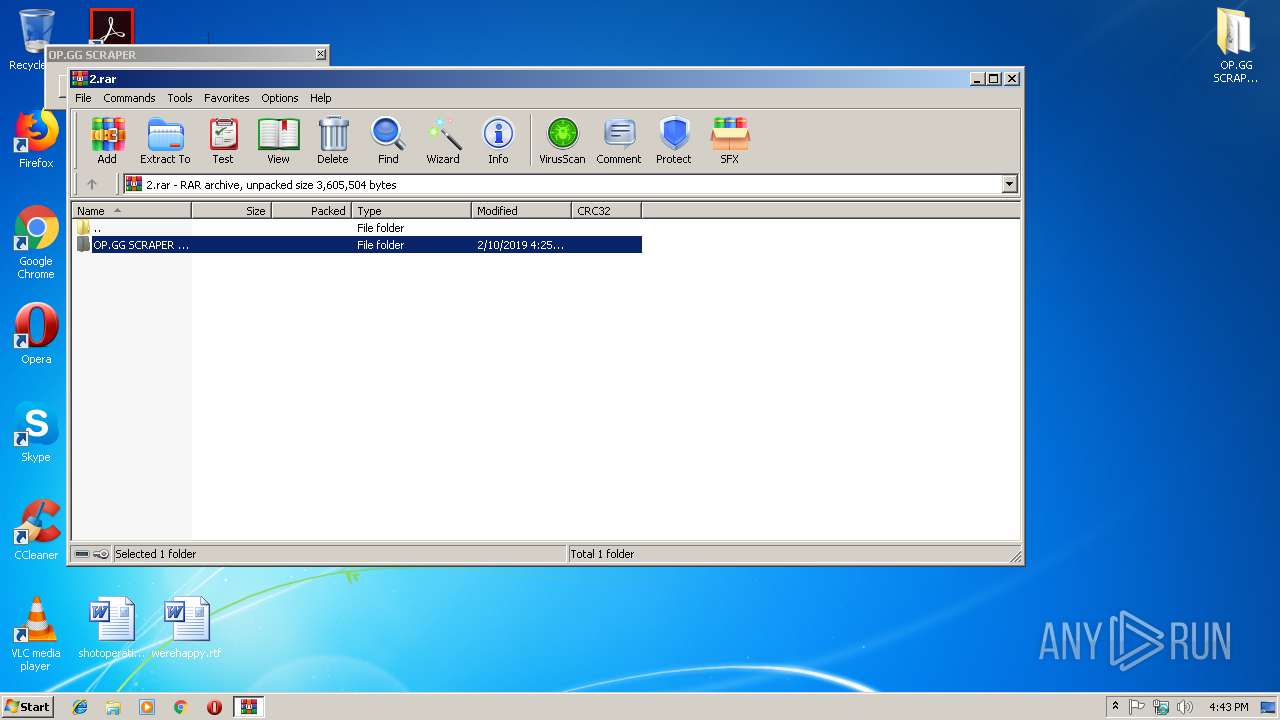
| File name: | 2.rar |
| Full analysis: | https://app.any.run/tasks/b2d27979-37bb-423f-8f48-641faf54d24d |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2019, 16:42:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | E81B648401165E53C123487DEC35908A |
| SHA1: | E5F60A04D5A22AA524B6FB81E7A164F4101D6F3D |
| SHA256: | EB86689834FD802BC5BF3851677F67DCF34B53D0CC481DD3E6759500C9BAAE05 |
| SSDEEP: | 49152:gy+fn2fdmis/VDE+/Ia0co4rzxmheexa1i3iQoOp1:gl/Ywis/VDE+/smzxmhNxa4Db1 |
MALICIOUS
Application was dropped or rewritten from another process
- Windows Defender.exe (PID: 2608)
- svchost.exe (PID: 2260)
- summitdghardware.exe (PID: 3848)
- summitdghardware.exe (PID: 3500)
- summitdghardware.exe (PID: 3540)
- summitdghardware.exe (PID: 3152)
- summitdghardware.exe (PID: 2716)
- summitdghardware.exe (PID: 3096)
Writes to a start menu file
- csc.exe (PID: 4016)
- csc.exe (PID: 3828)
SUSPICIOUS
Reads Environment values
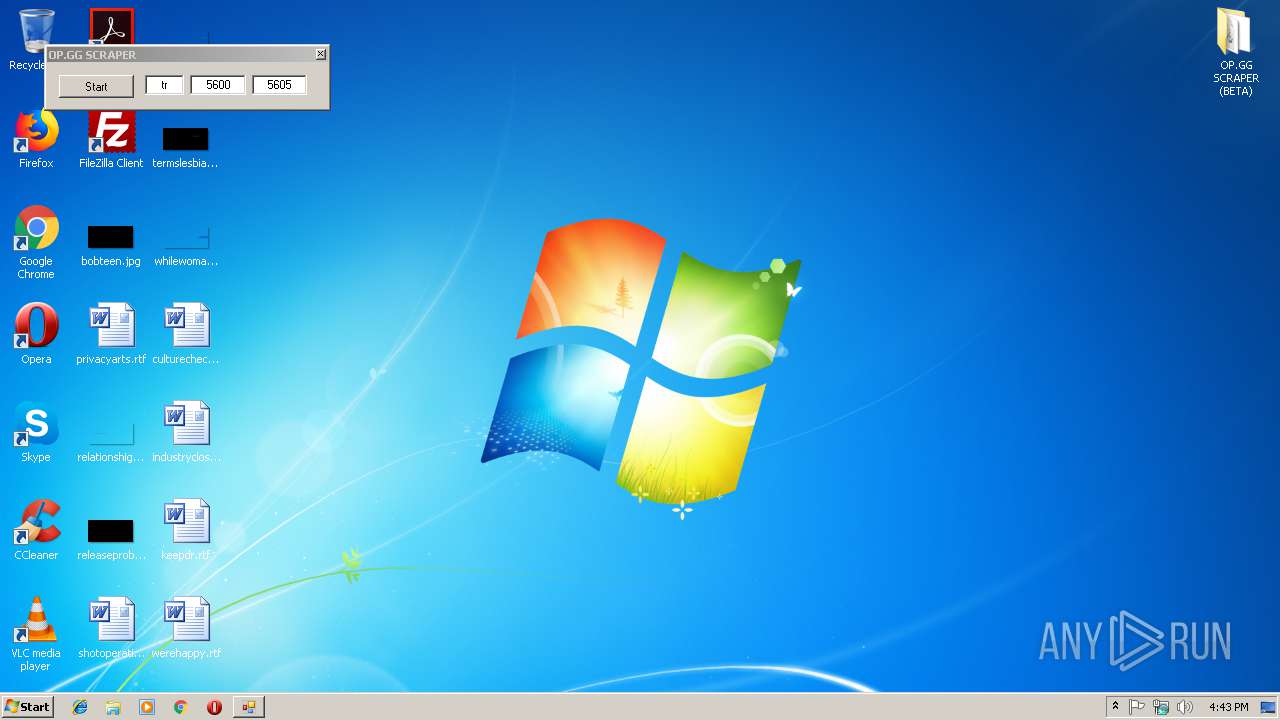
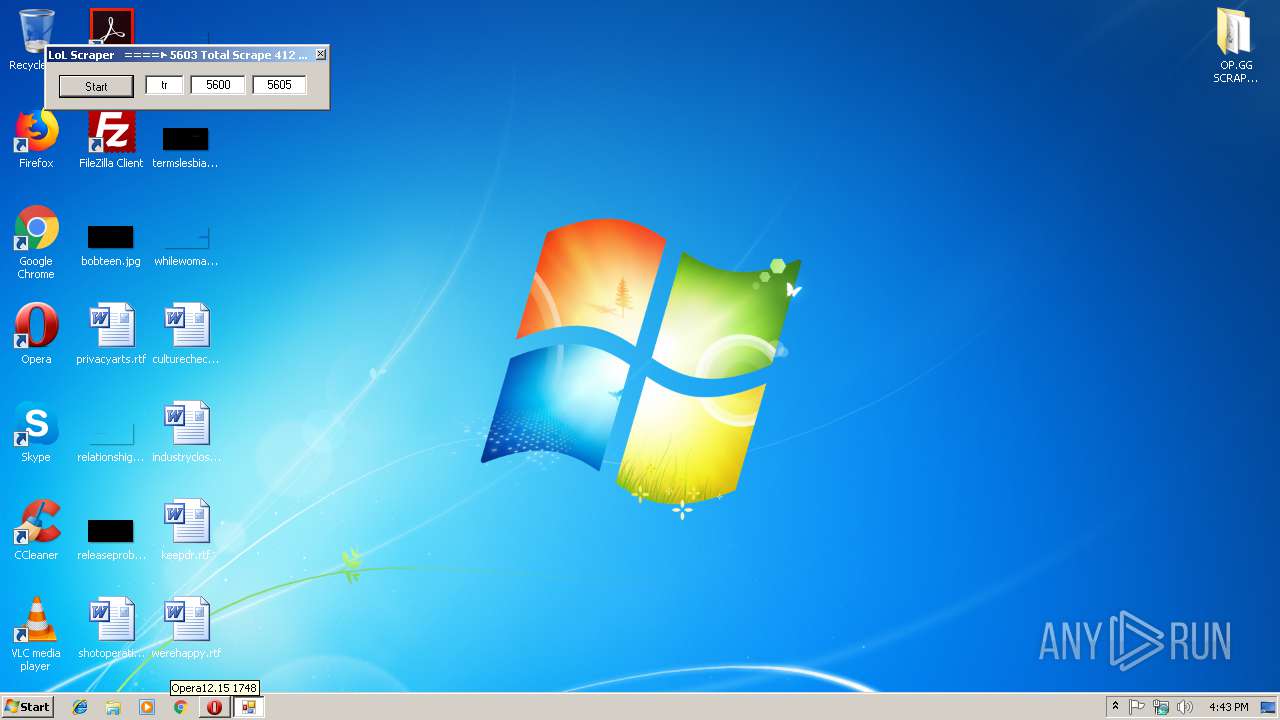
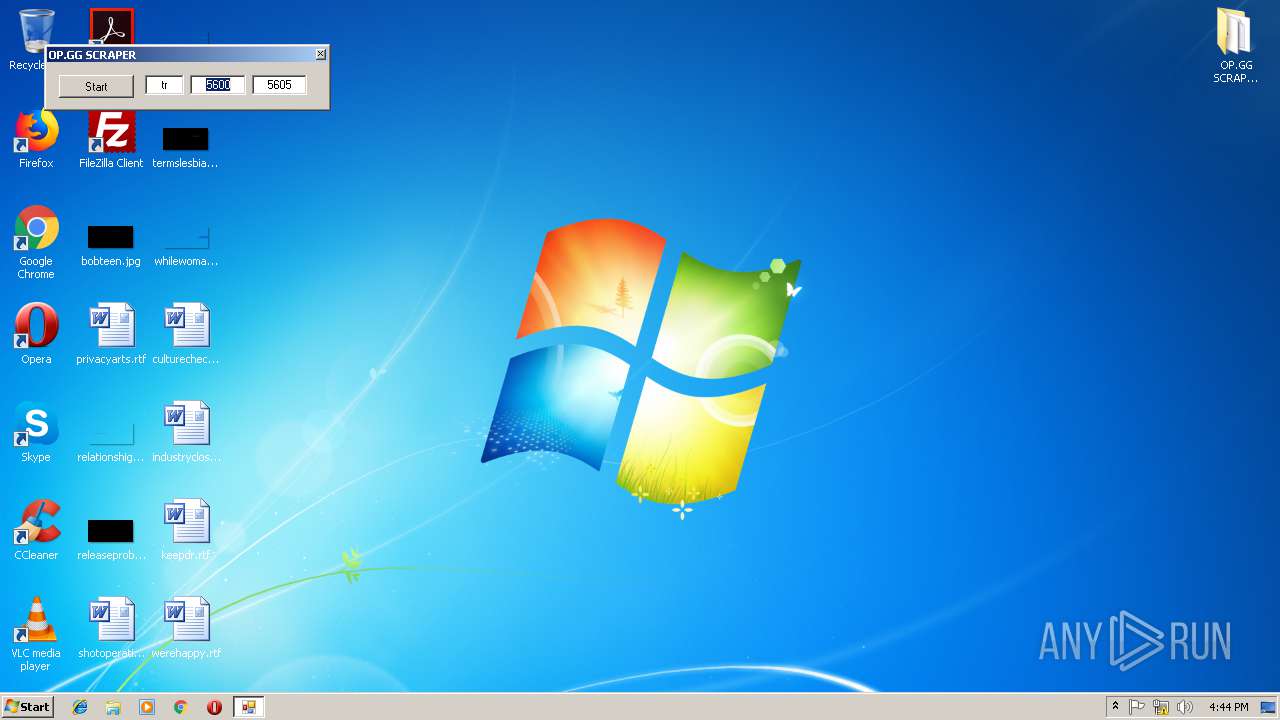
- OP.GG SCRAPER(BETA).exe (PID: 2564)
- svchost.exe (PID: 2260)
Creates files in the user directory
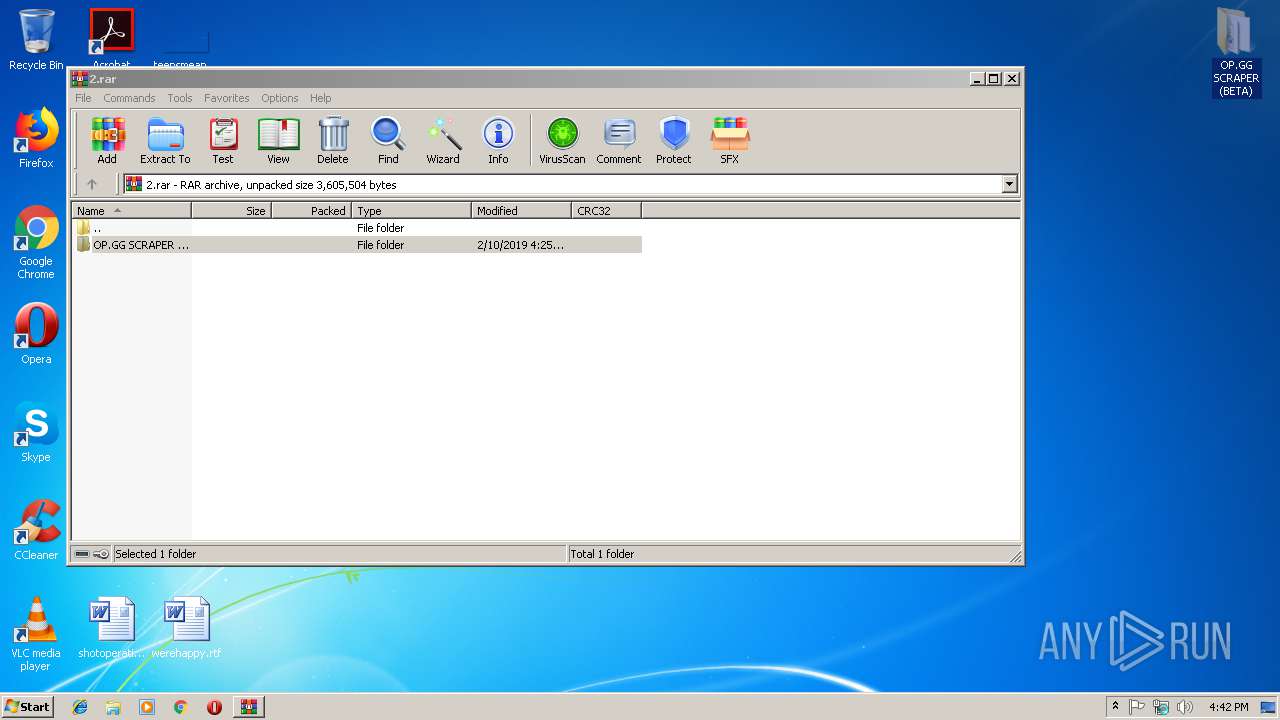
- OP.GG SCRAPER(BETA).exe (PID: 2564)
- Windows Defender.exe (PID: 2608)
- csc.exe (PID: 4016)
- csc.exe (PID: 3852)
- svchost.exe (PID: 2260)
- csc.exe (PID: 3828)
- csc.exe (PID: 3788)
- csc.exe (PID: 1700)
- csc.exe (PID: 2304)
- csc.exe (PID: 3672)
- csc.exe (PID: 1740)
- csc.exe (PID: 3760)
Executable content was dropped or overwritten
- csc.exe (PID: 4016)
- csc.exe (PID: 3852)
- csc.exe (PID: 3672)
- csc.exe (PID: 3788)
- csc.exe (PID: 3828)
- csc.exe (PID: 1700)
- csc.exe (PID: 2304)
- csc.exe (PID: 1740)
- csc.exe (PID: 3760)
Application launched itself
- OP.GG SCRAPER(BETA).exe (PID: 2564)
Creates executable files which already exist in Windows
- csc.exe (PID: 3852)
Reads internet explorer settings
- svchost.exe (PID: 2260)
INFO
Application launched itself
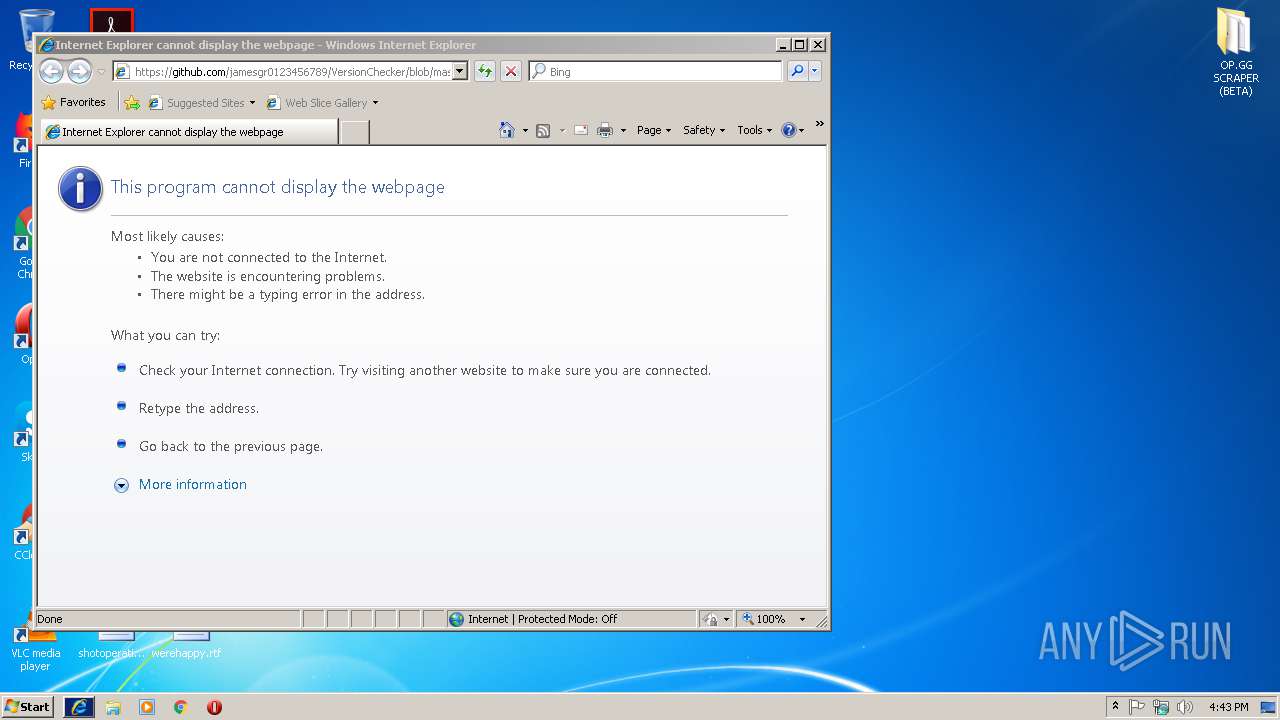
- iexplore.exe (PID: 3532)
Reads internet explorer settings
- iexplore.exe (PID: 1488)
Changes internet zones settings
- iexplore.exe (PID: 3532)
Reads Internet Cache Settings
- iexplore.exe (PID: 1488)
Creates files in the user directory
- iexplore.exe (PID: 1488)
- iexplore.exe (PID: 3532)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1488)
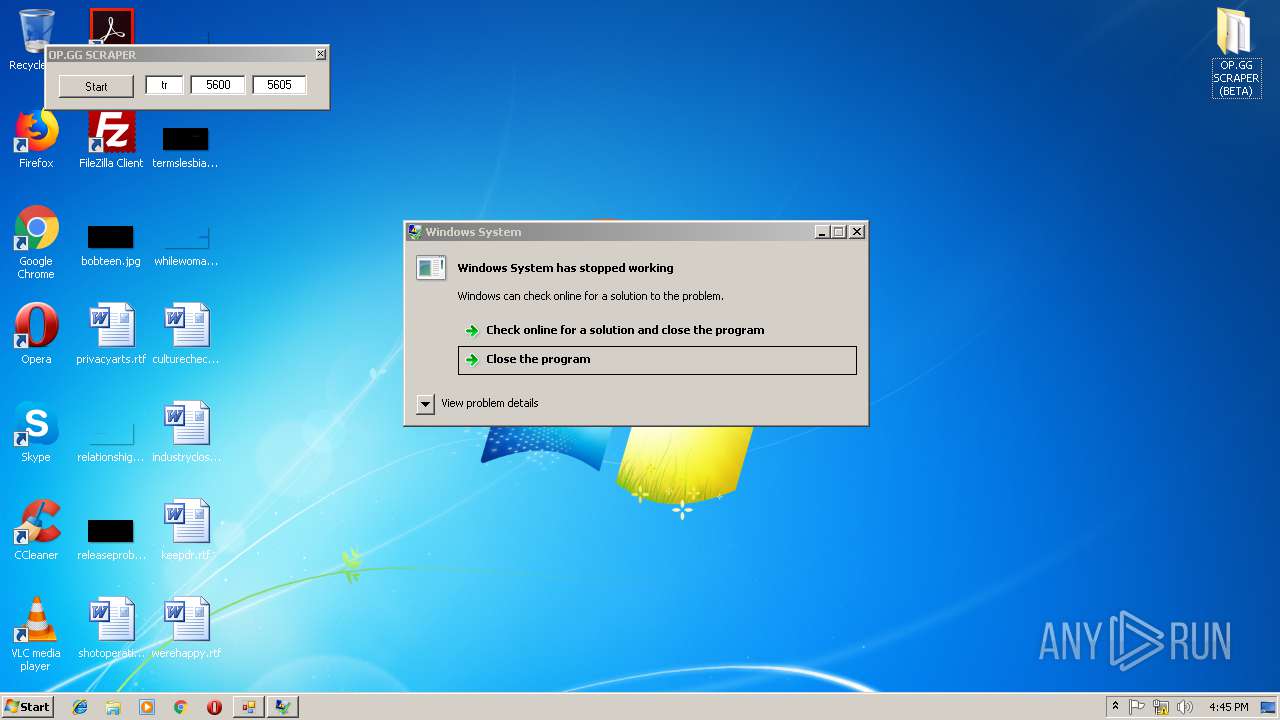
Application was crashed
- summitdghardware.exe (PID: 3848)
- summitdghardware.exe (PID: 3500)
- summitdghardware.exe (PID: 3152)
- summitdghardware.exe (PID: 3540)
- summitdghardware.exe (PID: 2716)
- summitdghardware.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
86
Monitored processes
33
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1236 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES9E69.tmp" "c:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CSCD0B65FB352444B3878D19678270E3C7.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 12.00.52512.0 built by: VSWINSERVICING Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3532 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1700 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\dsagpxll.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1740 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\llyueeq2.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2260 | "C:\Users\admin\AppData\Roaming\Windows Defender\svchost.exe" | C:\Users\admin\AppData\Roaming\Windows Defender\svchost.exe | Windows Defender.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows NT Kernel & System Exit code: 0 Version: 0.2.4.1 Modules
| |||||||||||||||
| 2304 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\1hbd5yjr.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2464 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
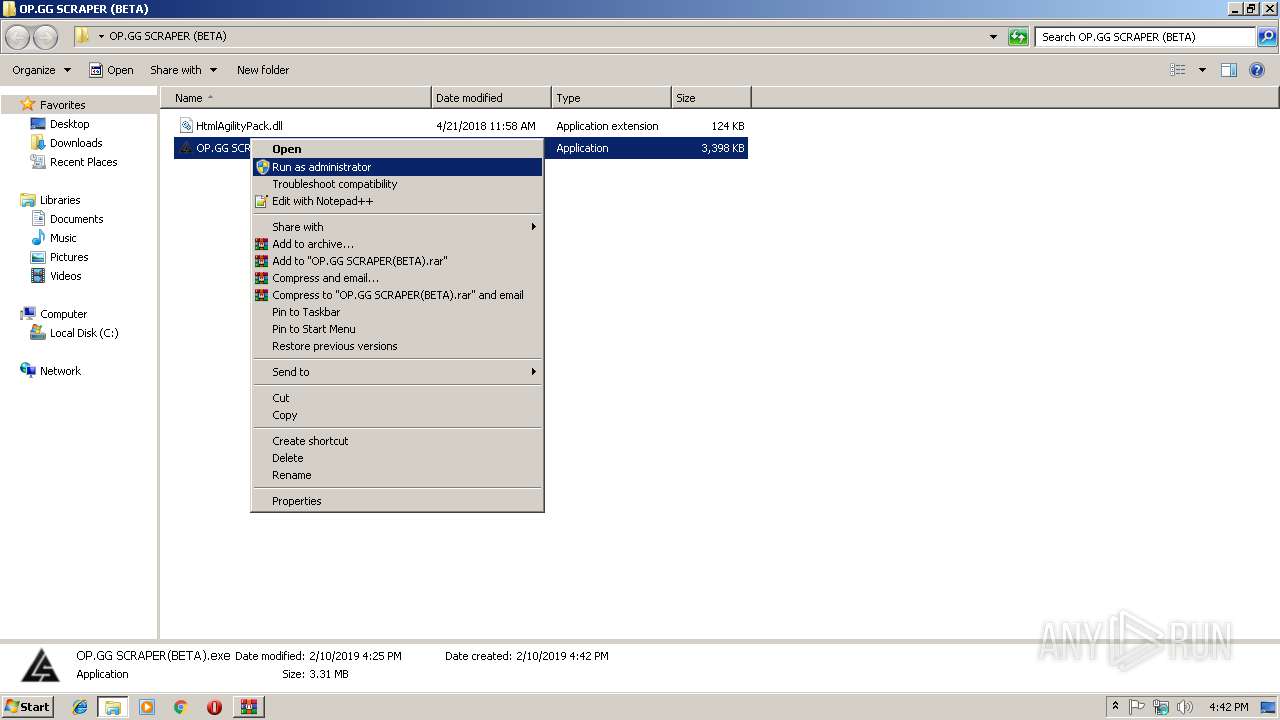
| 2564 | "C:\Users\admin\Desktop\OP.GG SCRAPER (BETA)\OP.GG SCRAPER(BETA).exe" | C:\Users\admin\Desktop\OP.GG SCRAPER (BETA)\OP.GG SCRAPER(BETA).exe | explorer.exe | ||||||||||||
User: admin Company: fishing lowly Integrity Level: HIGH Description: OP.GG Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
| 2608 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Windows Defender.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Windows Defender.exe | — | OP.GG SCRAPER(BETA).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Defender Exit code: 0 Version: 1.8.0.0 Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Roaming\Windows Defender\summitdghardware.exe" | C:\Users\admin\AppData\Roaming\Windows Defender\summitdghardware.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows System Exit code: 4294967295 Version: 0.5.3.4 Modules
| |||||||||||||||
Total events
2 446
Read events
2 311
Write events
134
Delete events
1
Modification events
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2.rar | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
9
Suspicious files
14
Text files
49
Unknown types
4
Dropped files
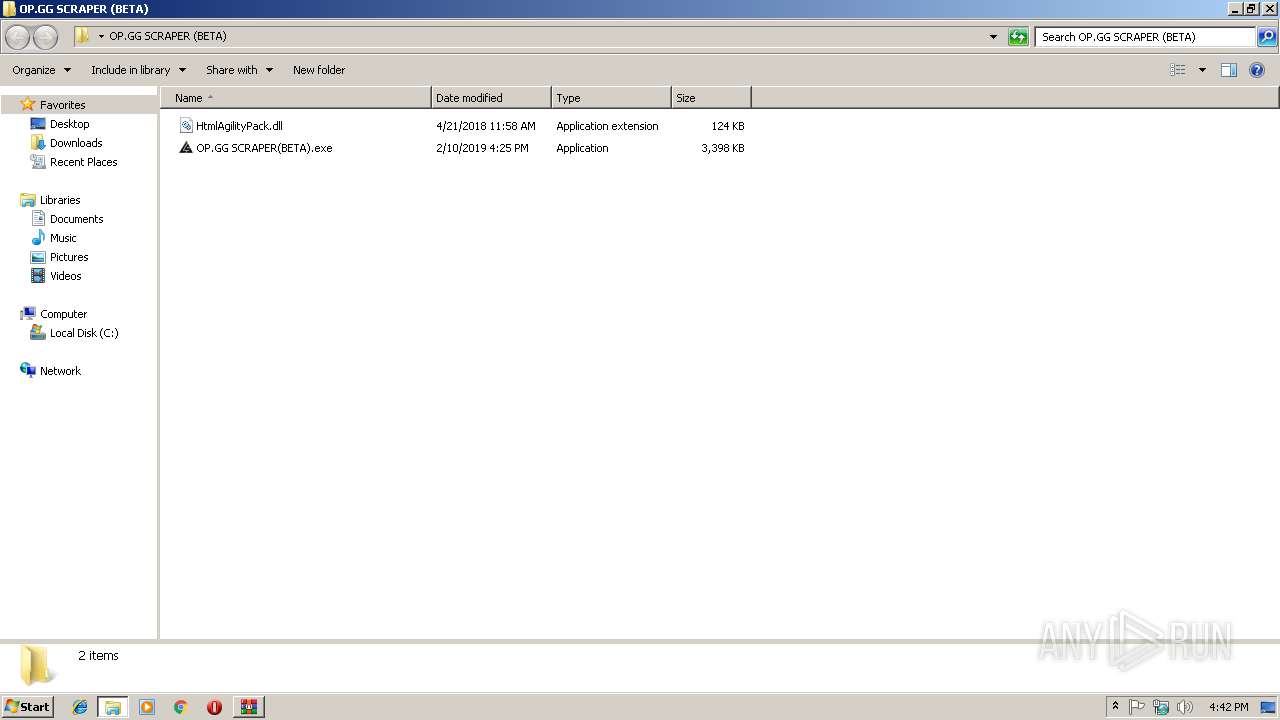
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.47626\OP.GG SCRAPER (BETA)\HtmlAgilityPack.dll | — | |
MD5:— | SHA256:— | |||
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.47626\OP.GG SCRAPER (BETA)\OP.GG SCRAPER(BETA).exe | — | |
MD5:— | SHA256:— | |||
| 2564 | OP.GG SCRAPER(BETA).exe | C:\Users\admin\AppData\Local\Temp\tmpDF74.tmp | — | |
MD5:— | SHA256:— | |||
| 2564 | OP.GG SCRAPER(BETA).exe | C:\Users\admin\AppData\Local\Temp\lbujwygd.0.cs | — | |
MD5:— | SHA256:— | |||
| 2564 | OP.GG SCRAPER(BETA).exe | C:\Users\admin\AppData\Local\Temp\lbujwygd.cmdline | — | |
MD5:— | SHA256:— | |||
| 4016 | csc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CSC28C6249C648D472AB7F7EBD7BCD3B48.TMP | — | |
MD5:— | SHA256:— | |||
| 3372 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESE08D.tmp | — | |
MD5:— | SHA256:— | |||
| 4016 | csc.exe | C:\Users\admin\AppData\Local\Temp\lbujwygd.out | — | |
MD5:— | SHA256:— | |||
| 2608 | Windows Defender.exe | C:\Users\admin\AppData\Roaming\Windows Defender\orj3.txt | — | |
MD5:— | SHA256:— | |||
| 2608 | Windows Defender.exe | C:\Users\admin\AppData\Local\Temp\tmp914.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
12
DNS requests
7
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | OP.GG SCRAPER(BETA).exe | GET | 200 | 143.204.101.18:80 | http://tr.op.gg/ranking/level/page=5604 | US | html | 163 Kb | whitelisted |
2564 | OP.GG SCRAPER(BETA).exe | GET | 200 | 143.204.101.18:80 | http://tr.op.gg/ranking/level/page=5603 | US | html | 144 Kb | whitelisted |
2564 | OP.GG SCRAPER(BETA).exe | GET | 200 | 143.204.101.18:80 | http://tr.op.gg/ranking/level/page=5602 | US | html | 127 Kb | whitelisted |
2564 | OP.GG SCRAPER(BETA).exe | GET | 200 | 143.204.101.18:80 | http://tr.op.gg/ranking/level/page=5601 | US | html | 127 Kb | whitelisted |
2564 | OP.GG SCRAPER(BETA).exe | GET | 200 | 143.204.101.18:80 | http://tr.op.gg/ranking/level/page=5605 | US | html | 163 Kb | whitelisted |
1488 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=asdasdasdasdas&maxwidth=253&rowheight=20§ionHeight=400&FORM=IE8SSC&market=en-us | US | xml | 222 b | whitelisted |
2564 | OP.GG SCRAPER(BETA).exe | GET | 200 | 143.204.101.18:80 | http://tr.op.gg/ranking/level/page=5600 | US | html | 127 Kb | whitelisted |
3532 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2260 | svchost.exe | 88.99.66.31:443 | iplogger.com | Hetzner Online GmbH | DE | malicious |
3532 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1488 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
2260 | svchost.exe | 140.82.118.4:443 | github.com | — | US | malicious |
2564 | OP.GG SCRAPER(BETA).exe | 143.204.101.18:80 | tr.op.gg | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tr.op.gg |
| whitelisted |
github.com |
| malicious |
iplogger.com |
| shared |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report