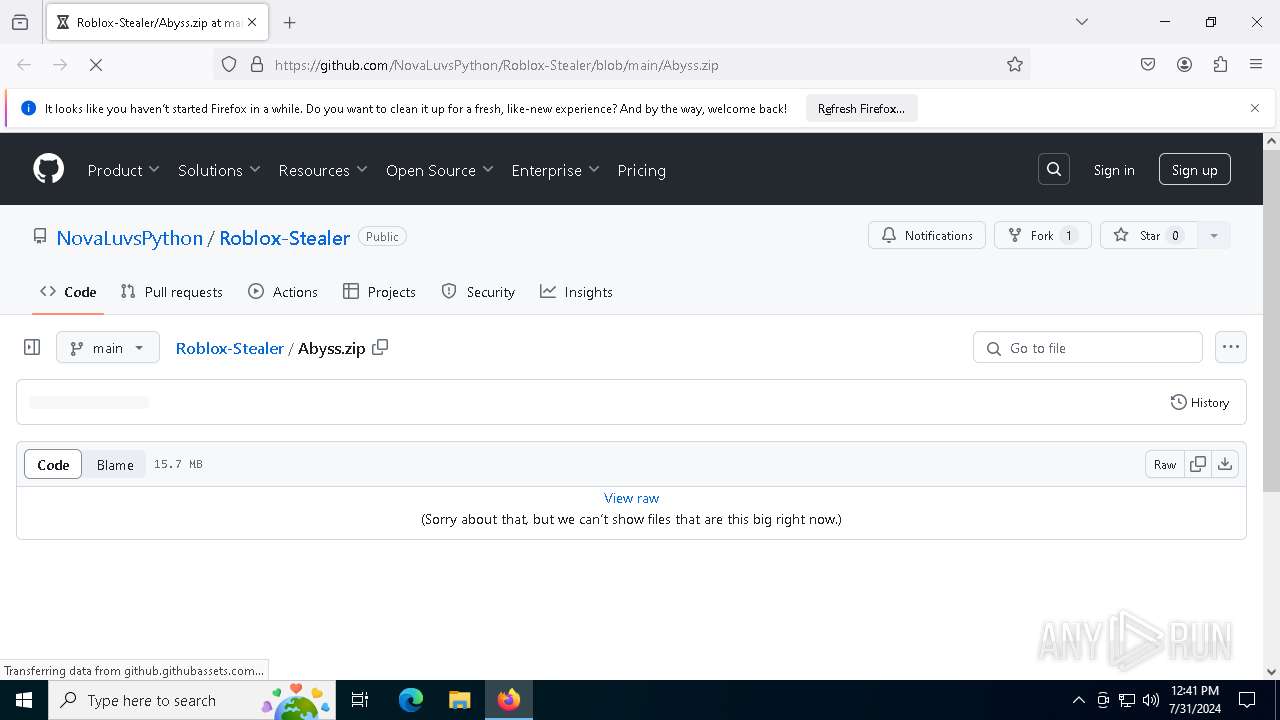
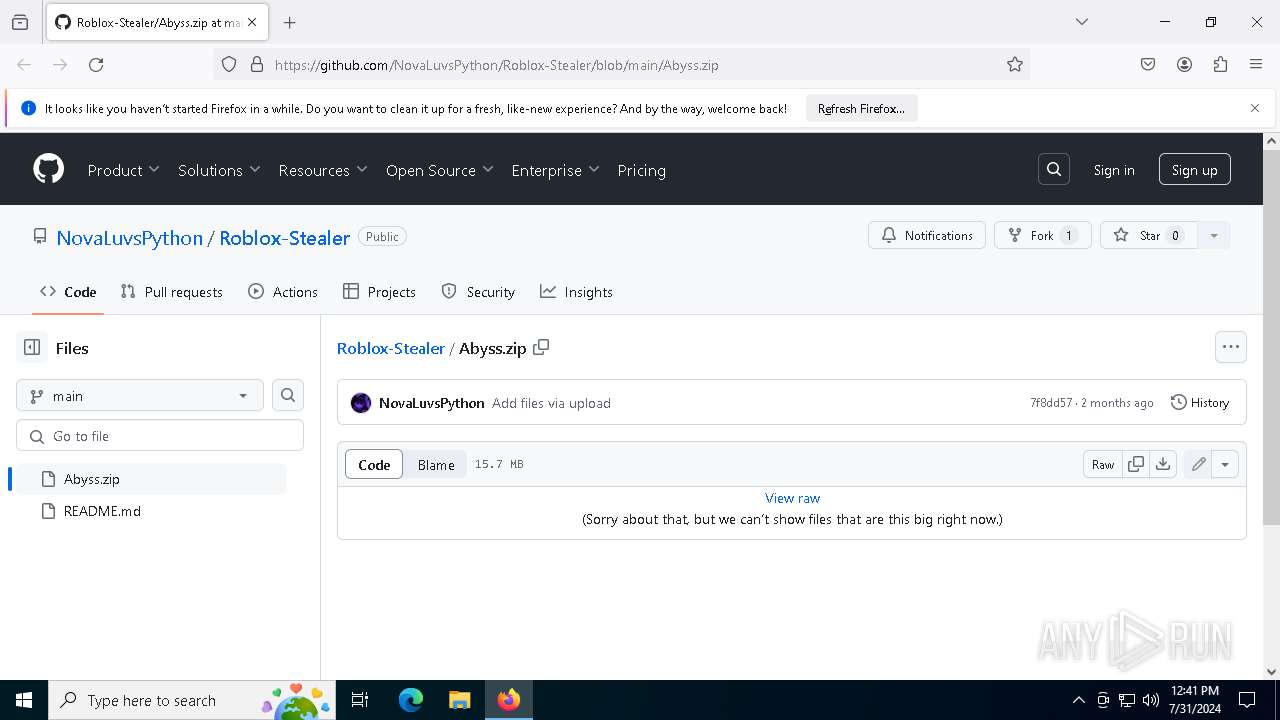
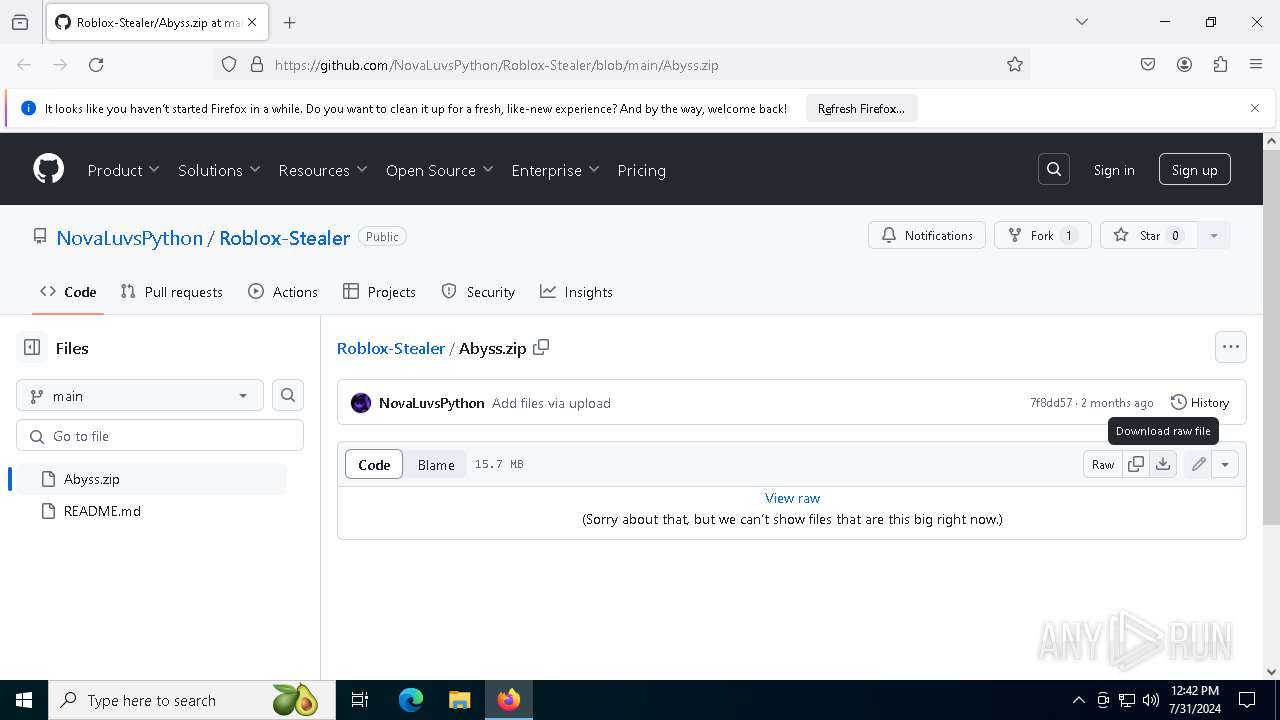
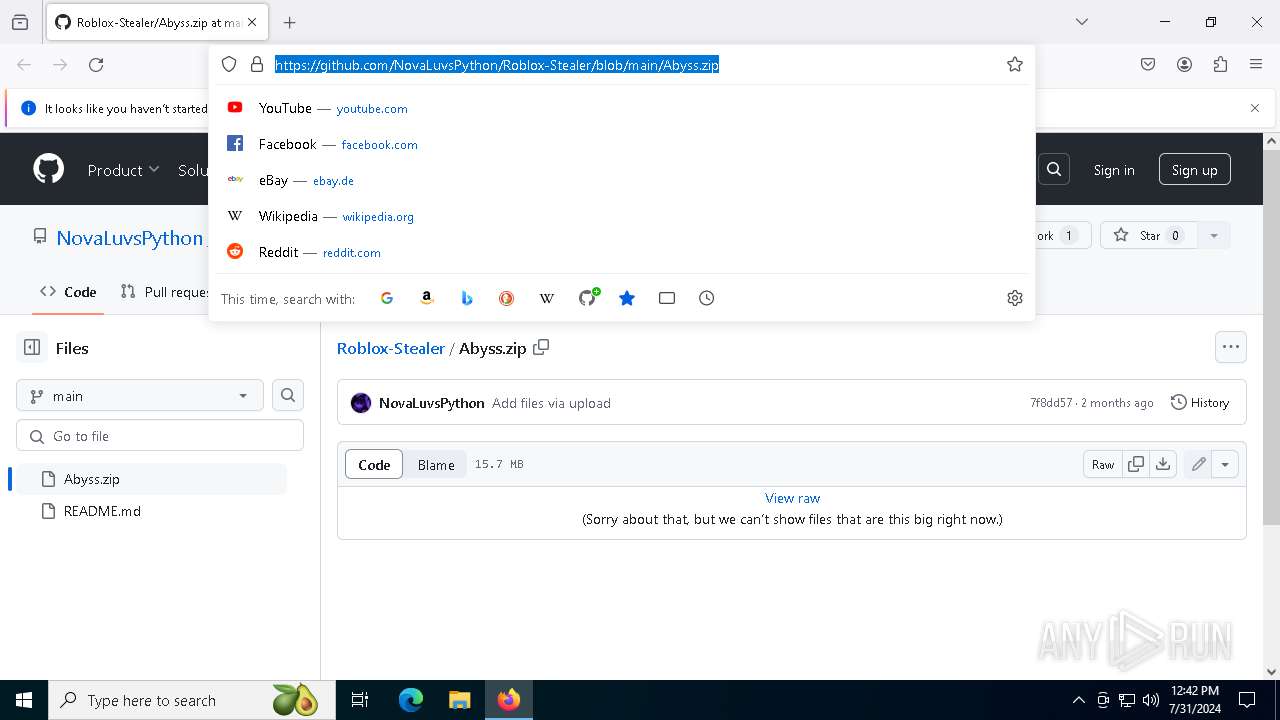
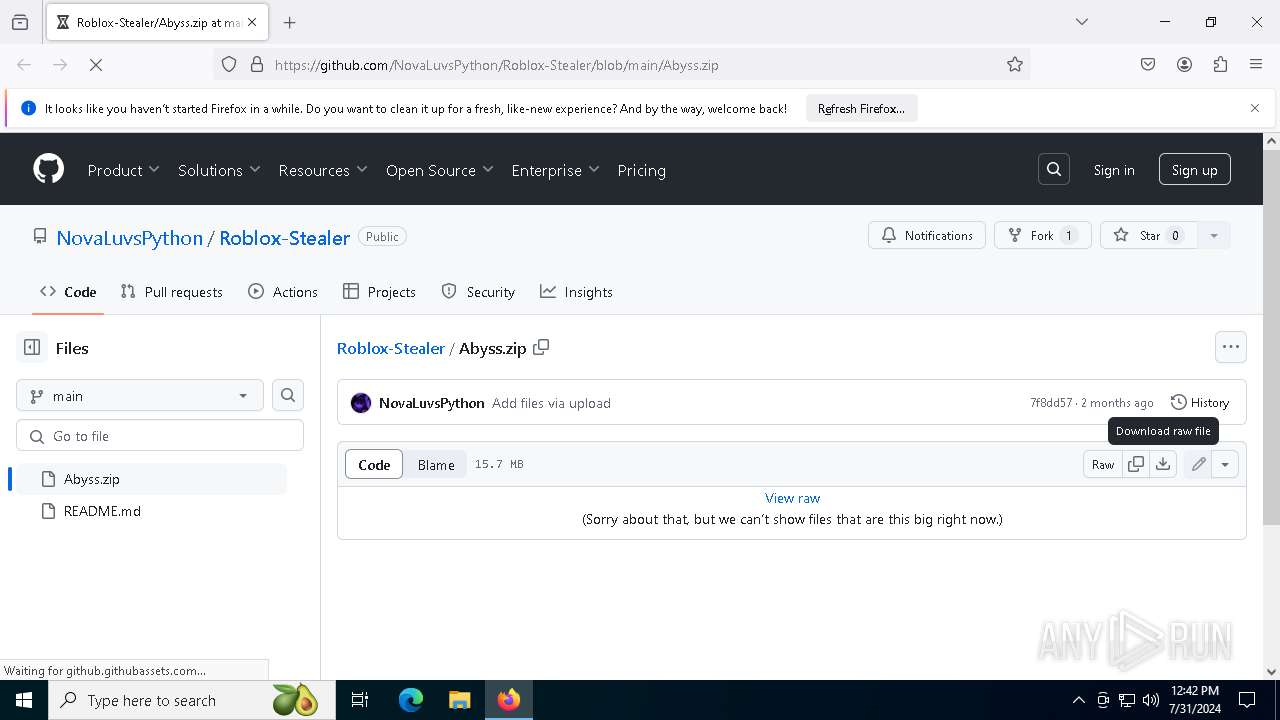
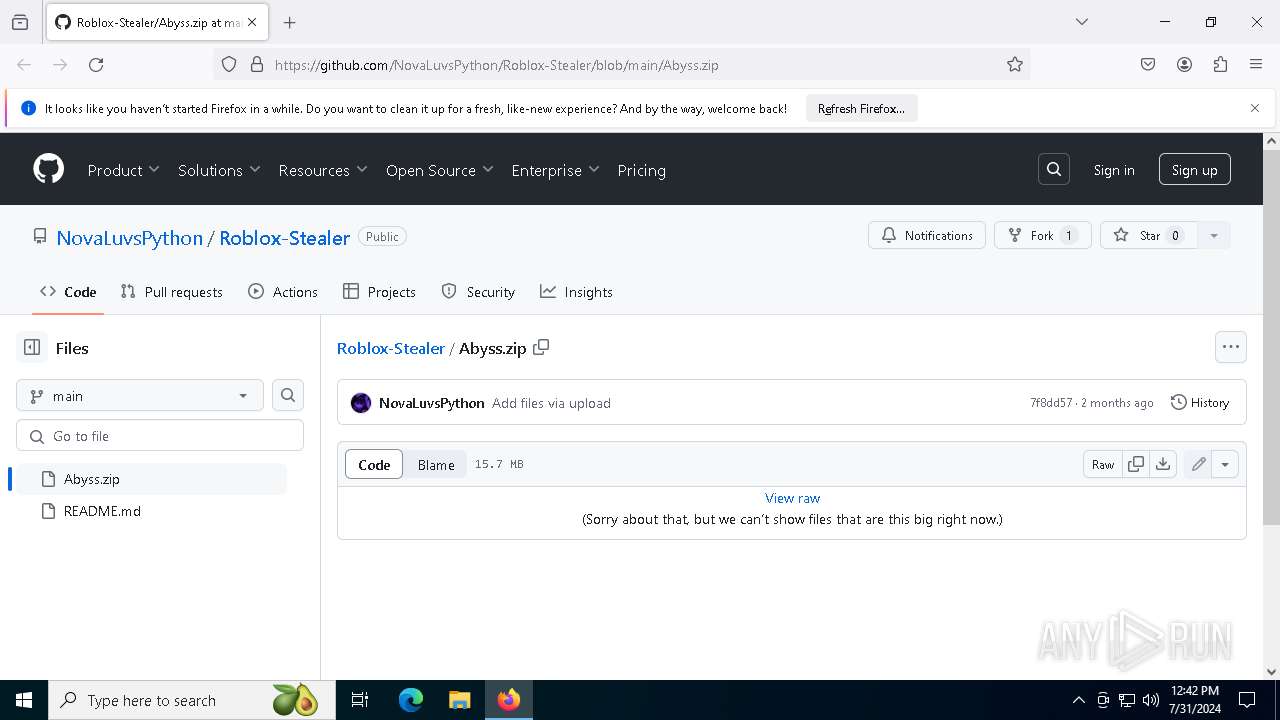
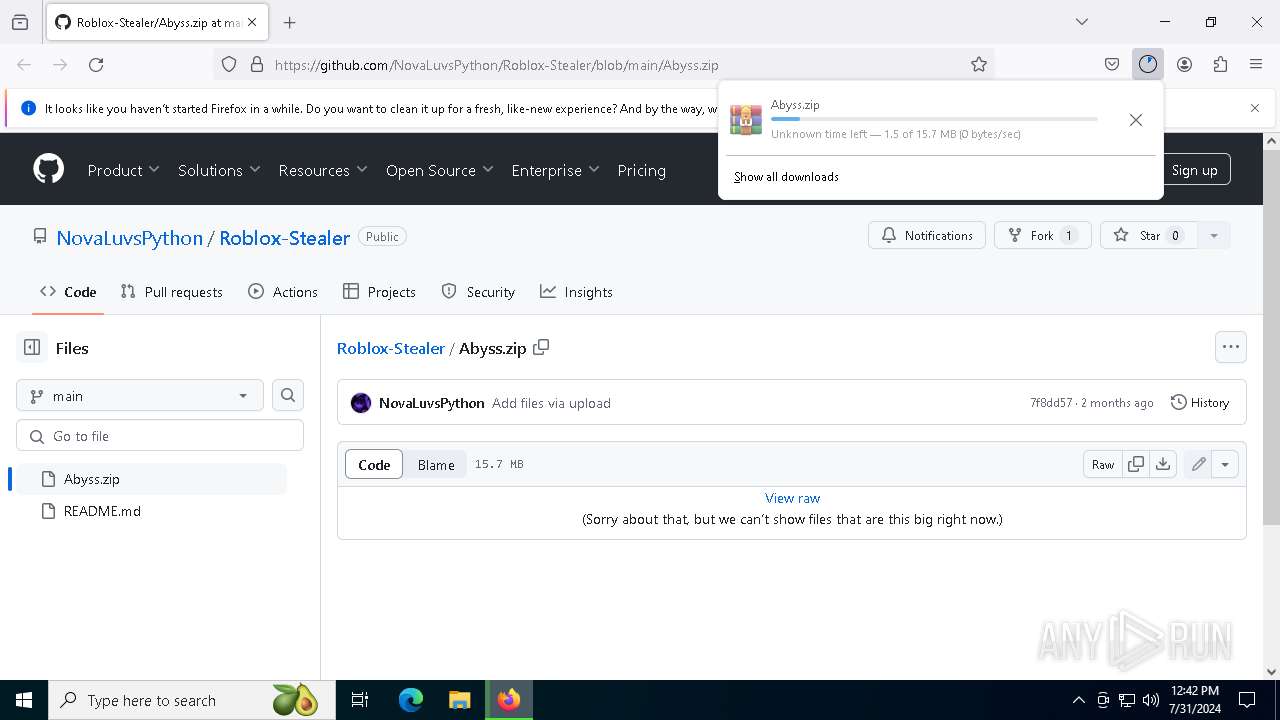
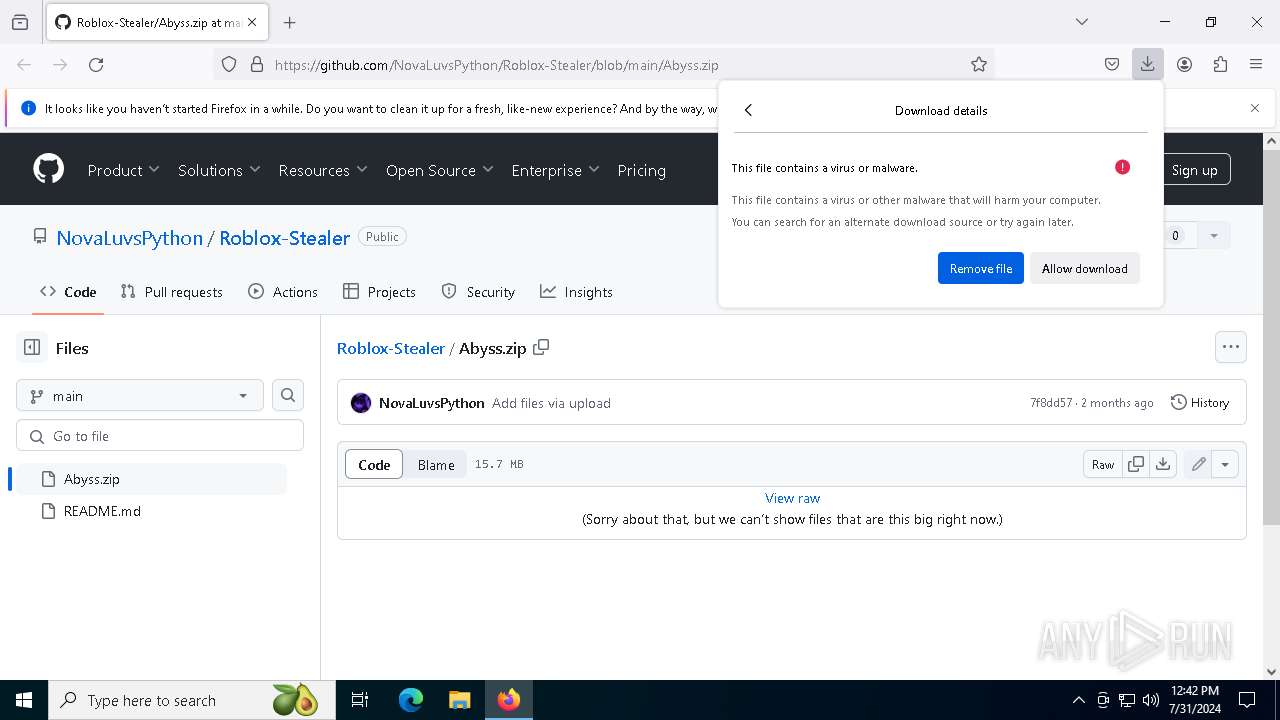
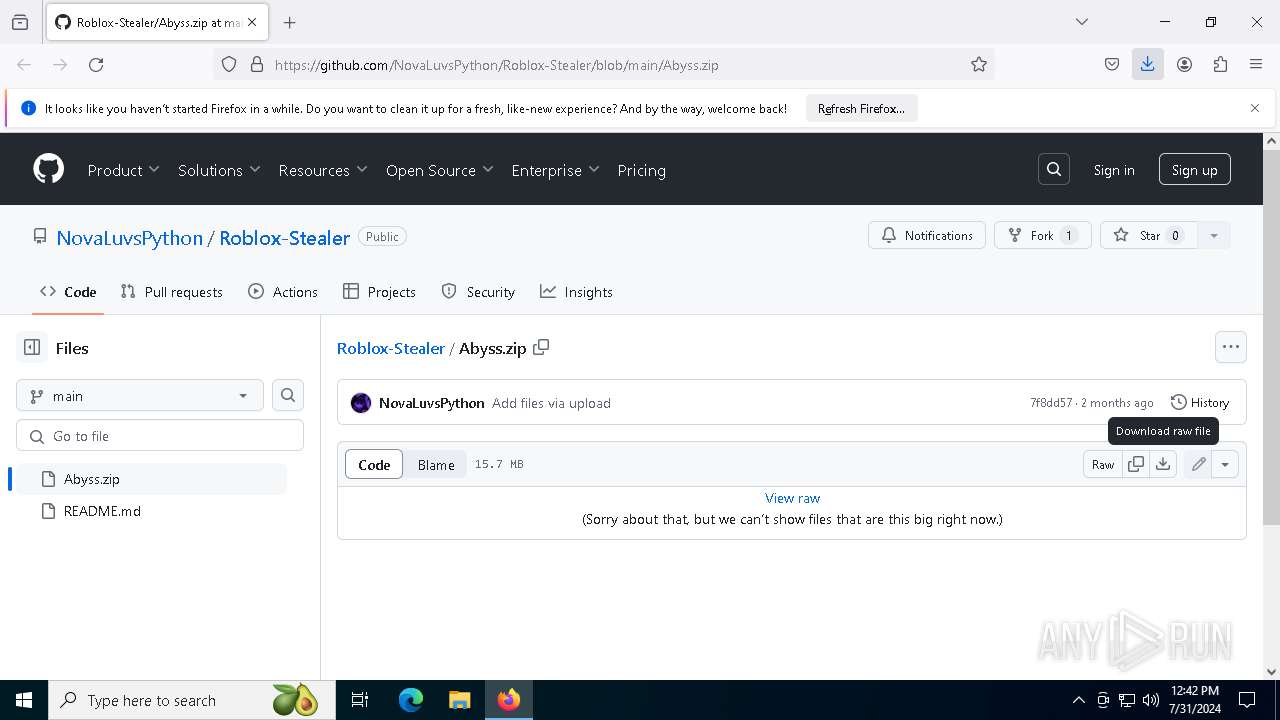
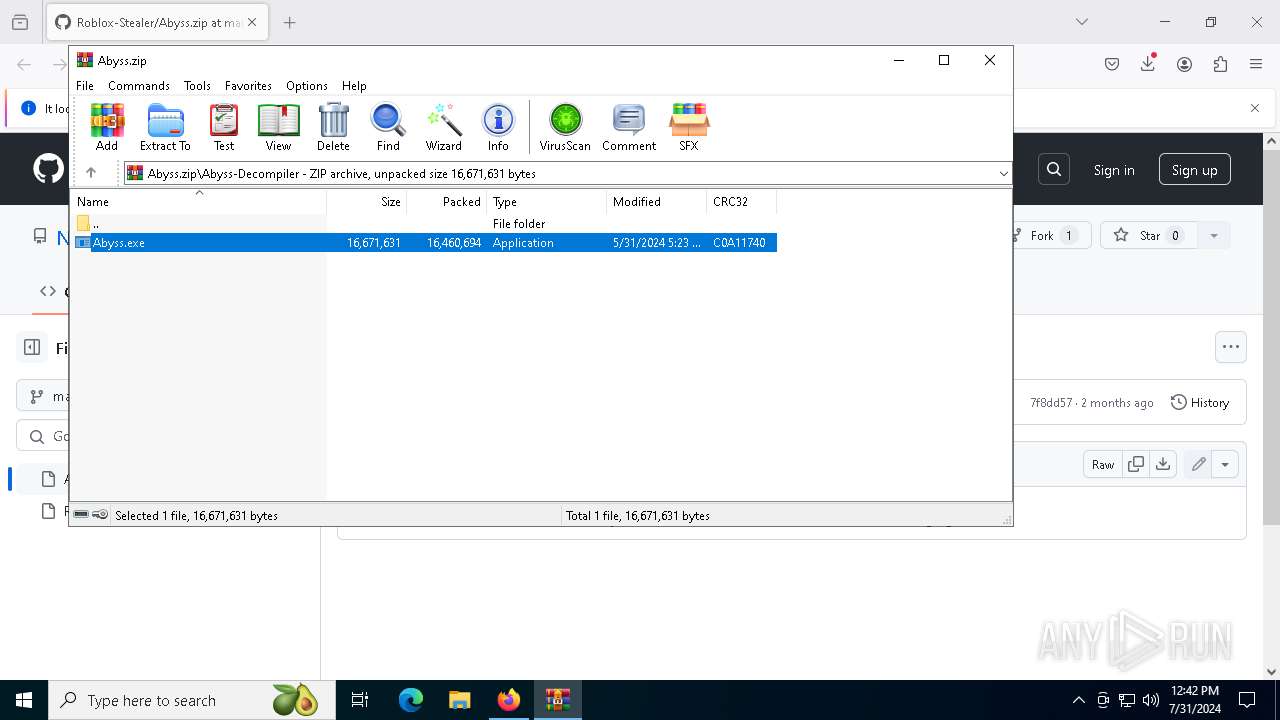
| URL: | https://github.com/NovaLuvsPython/Roblox-Stealer/blob/main/Abyss.zip |
| Full analysis: | https://app.any.run/tasks/3f02f20e-c3a2-4f20-9cd0-36535c427e92 |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2024, 12:40:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6C27C1CF8E3BB45B7AE1BCF52BBC1EA3 |
| SHA1: | 299D61CFA52EC1BFF2D7B5D4918CA1CDA5596297 |
| SHA256: | EB849E750A8AB0C010D2CDAD62A12908658F0975E626661647486CA02C308BA6 |
| SSDEEP: | 3:N8tEduTABWR9swRAg5yEROcqn:2uYTABWRCwRAKyszq |
MALICIOUS
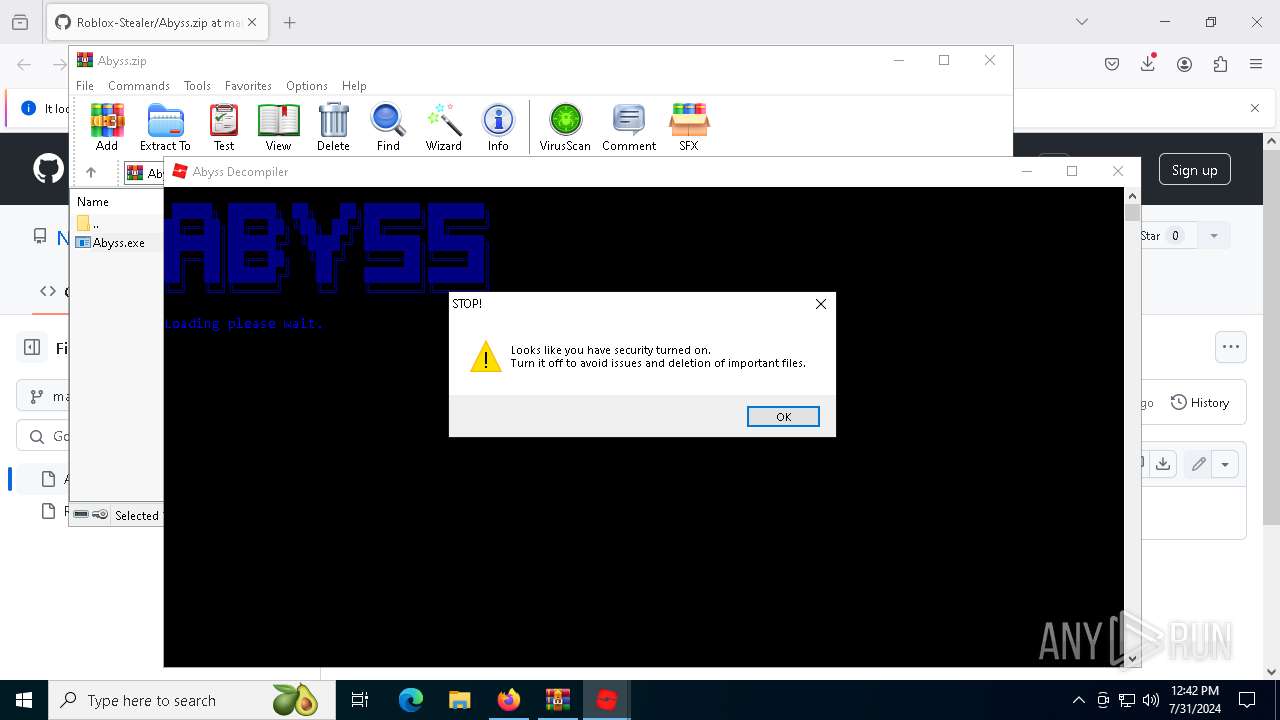
Drops the executable file immediately after the start
- Abyss.exe (PID: 1124)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8036)
Process drops legitimate windows executable
- Abyss.exe (PID: 1124)
The process drops C-runtime libraries
- Abyss.exe (PID: 1124)
Process drops python dynamic module
- Abyss.exe (PID: 1124)
Executable content was dropped or overwritten
- Abyss.exe (PID: 1124)
Application launched itself
- Abyss.exe (PID: 1124)
Loads Python modules
- Abyss.exe (PID: 8140)
Starts POWERSHELL.EXE for commands execution
- Abyss.exe (PID: 8140)
INFO
Reads Microsoft Office registry keys
- firefox.exe (PID: 6340)
Application launched itself
- firefox.exe (PID: 6308)
- firefox.exe (PID: 6340)
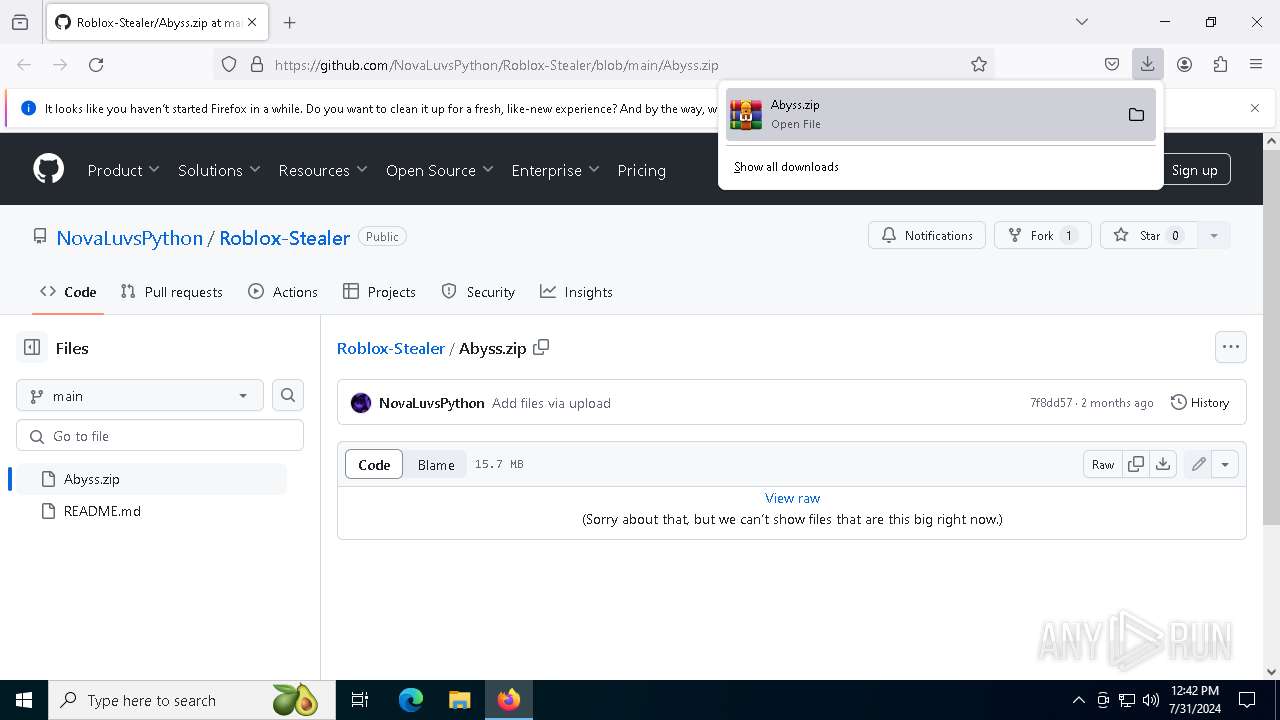
The process uses the downloaded file
- firefox.exe (PID: 6340)
- WinRAR.exe (PID: 8036)
Reads the computer name
- TextInputHost.exe (PID: 2476)
- Abyss.exe (PID: 1124)
- Abyss.exe (PID: 8140)
Checks supported languages
- TextInputHost.exe (PID: 2476)
- Abyss.exe (PID: 1124)
- Abyss.exe (PID: 8140)
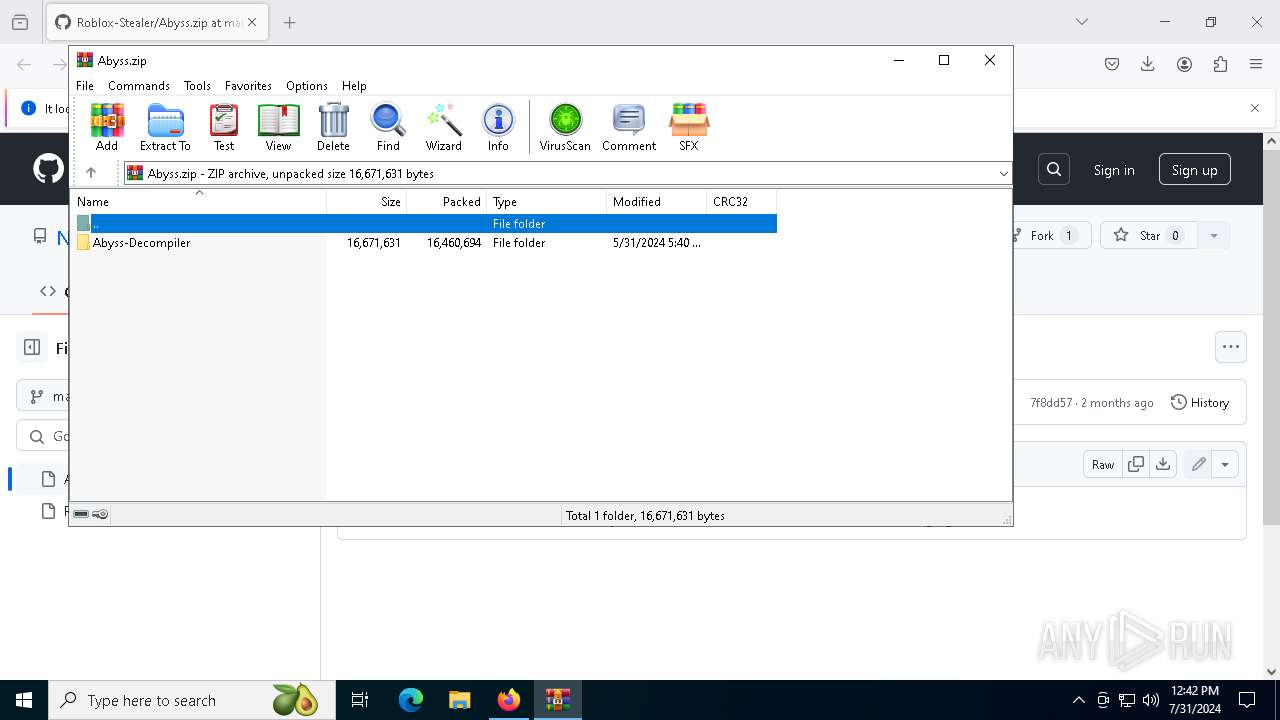
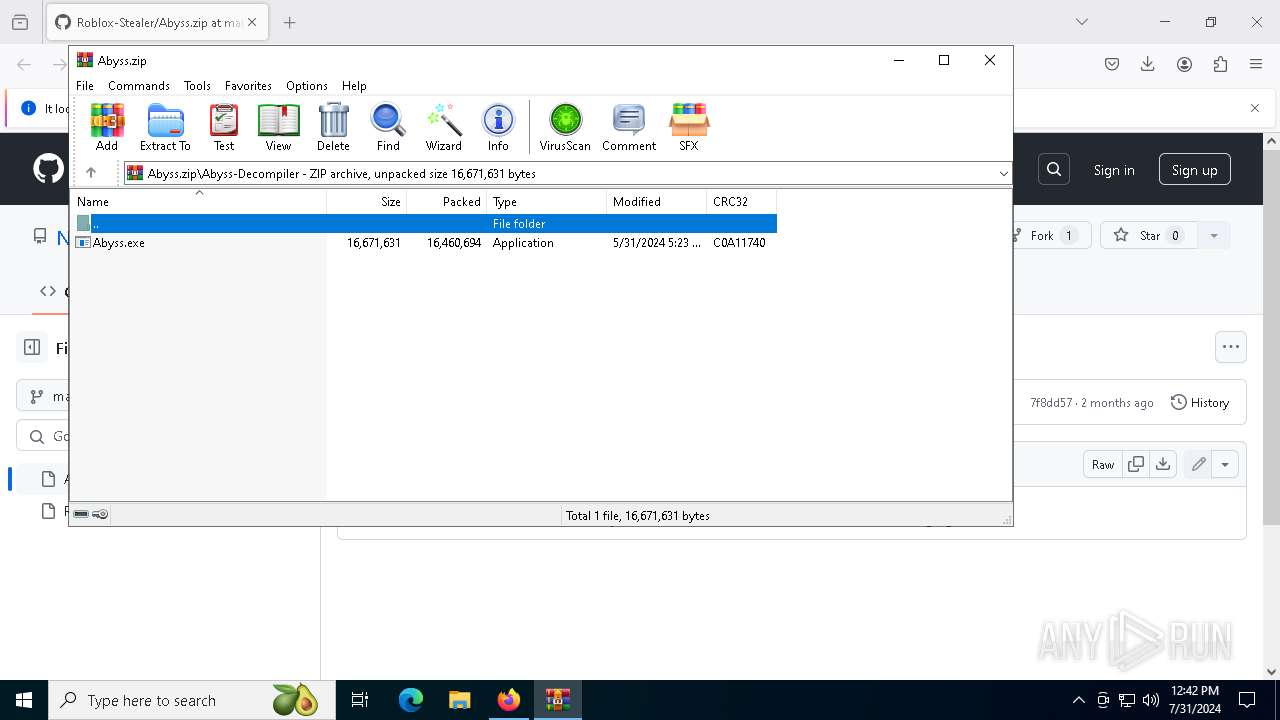
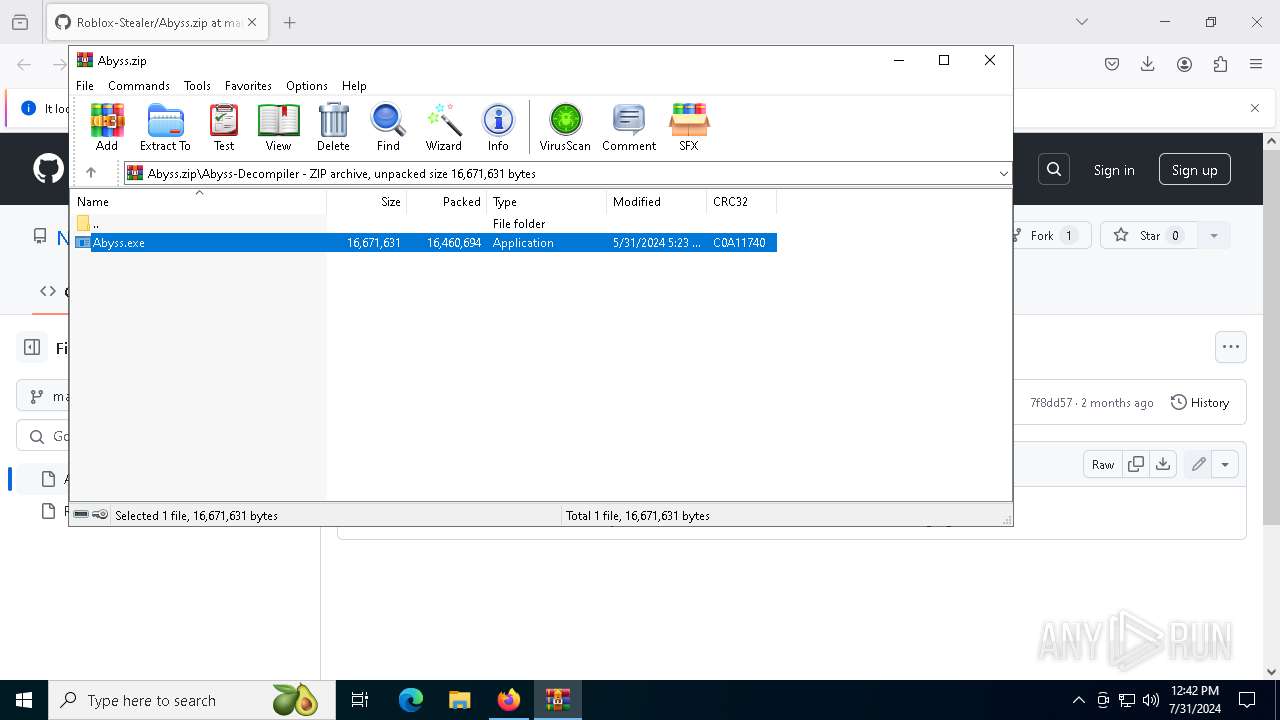
Manual execution by a user
- WinRAR.exe (PID: 8036)
Executable content was dropped or overwritten
- firefox.exe (PID: 6340)
- WinRAR.exe (PID: 8036)
Drops the executable file immediately after the start
- firefox.exe (PID: 6732)
- WinRAR.exe (PID: 8036)
- firefox.exe (PID: 6340)
Create files in a temporary directory
- Abyss.exe (PID: 1124)
PyInstaller has been detected (YARA)
- Abyss.exe (PID: 8140)
- Abyss.exe (PID: 1124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
151
Monitored processes
17
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
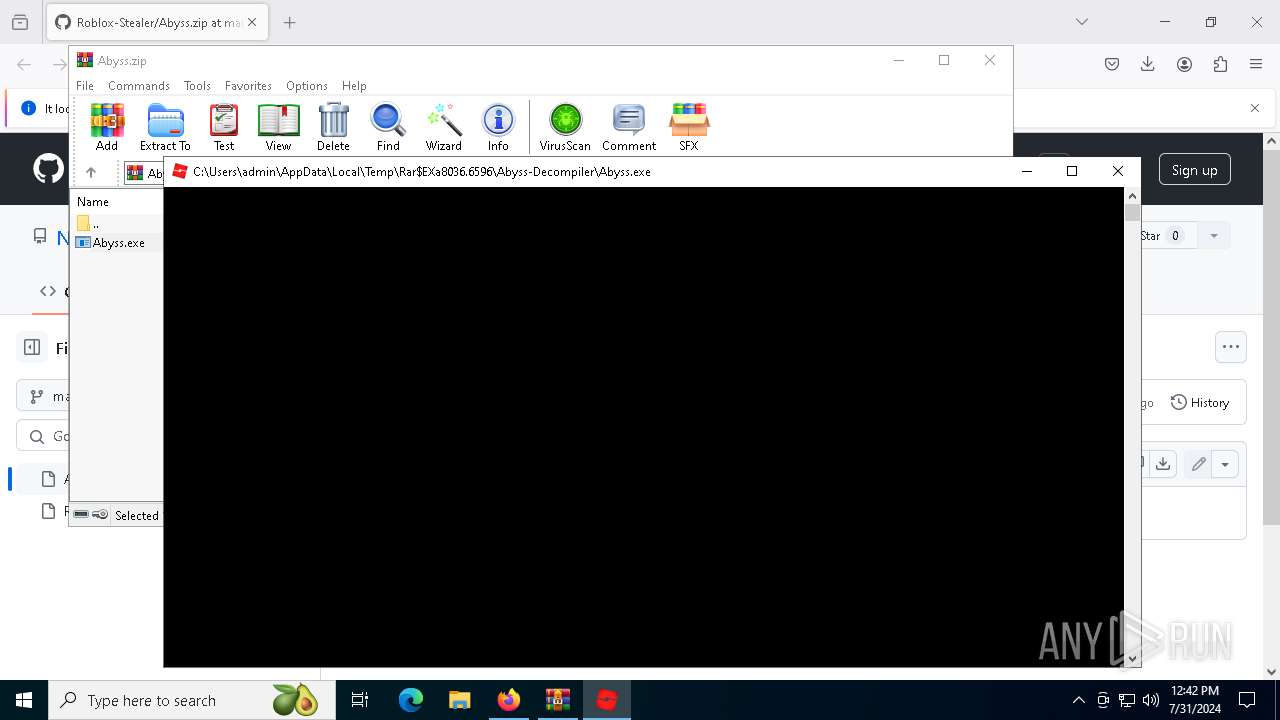
| 1124 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa8036.6596\Abyss-Decompiler\Abyss.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa8036.6596\Abyss-Decompiler\Abyss.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1360 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Abyss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5856 -childID 6 -isForBrowser -prefsHandle 5836 -prefMapHandle 5948 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1264 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {23e20e39-3c02-459b-9cc5-c37acf6134a0} 6340 "\\.\pipe\gecko-crash-server-pipe.6340" 2f43fcbbd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2476 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5548 -childID 4 -isForBrowser -prefsHandle 5536 -prefMapHandle 5604 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1264 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f9cbdbe1-4ac9-450c-9c70-88b21a215f72} 6340 "\\.\pipe\gecko-crash-server-pipe.6340" 2f43fcbb850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5948 -childID 5 -isForBrowser -prefsHandle 5872 -prefMapHandle 5876 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1264 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b80581df-bb80-4322-b5b0-6fd2a3e54fd5} 6340 "\\.\pipe\gecko-crash-server-pipe.6340" 2f43fcbbbd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6248 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5184 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 5168 -prefMapHandle 4904 -prefsLen 34713 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {74352fe9-0519-48d7-962b-c1ef1b6eb20c} 6340 "\\.\pipe\gecko-crash-server-pipe.6340" 2f43ed1eb10 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6268 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4696 -childID 3 -isForBrowser -prefsHandle 5320 -prefMapHandle 5316 -prefsLen 34713 -prefMapSize 244343 -jsInitHandle 1264 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {03a6623f-751e-45d3-abac-e1236fa04bae} 6340 "\\.\pipe\gecko-crash-server-pipe.6340" 2f43bff6f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6308 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://github.com/NovaLuvsPython/Roblox-Stealer/blob/main/Abyss.zip" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 6340 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/NovaLuvsPython/Roblox-Stealer/blob/main/Abyss.zip | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
26 792
Read events
26 745
Write events
46
Delete events
1
Modification events
| (PID) Process: | (6308) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 2BA552C800000000 | |||
| (PID) Process: | (6340) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 3A2154C800000000 | |||
| (PID) Process: | (6340) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (6340) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (6340) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (6340) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (6340) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6340) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (6340) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (6340) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
Executable files
35
Suspicious files
198
Text files
60
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6340 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6340 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6340 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6340 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6340 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:F9C1568726E31EF5D7C69E0D3824F190 | SHA256:19FA0E1444E1EB827BF91E5F4EE2FADE46315CE9AA6348872D80192D95C70843 | |||
| 6340 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6340 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6340 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:F9C1568726E31EF5D7C69E0D3824F190 | SHA256:19FA0E1444E1EB827BF91E5F4EE2FADE46315CE9AA6348872D80192D95C70843 | |||
| 6340 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:654A9BBCBD242BF9421BD7B2A1CFCC1F | SHA256:A9136D714A4A473303D903DE29775F1546800FEE2C2AD2FEB638C7E4F8357245 | |||
| 6340 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:4D79BA06E18D1DD7E1EC45DB1162D211 | SHA256:31E28B6F526EE829DDC8AC741723CB65DD89F10106143B5021170F48FC7948B3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
105
DNS requests
145
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6340 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6340 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6340 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | unknown |
6340 | firefox.exe | POST | 200 | 184.24.77.75:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6340 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
6340 | firefox.exe | POST | 200 | 184.24.77.75:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6340 | firefox.exe | POST | 200 | 184.24.77.75:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6340 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
6340 | firefox.exe | POST | 200 | 184.24.77.75:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6340 | firefox.exe | POST | — | 142.250.185.163:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4088 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5600 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6340 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | unknown |
6340 | firefox.exe | 142.250.184.234:443 | safebrowsing.googleapis.com | — | — | whitelisted |
6340 | firefox.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
6340 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6340 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
github.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
prod.ads.prod.webservices.mozgcp.net |
| unknown |
ocsp.sectigo.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |