| File name: | brain.exe |
| Full analysis: | https://app.any.run/tasks/636b7ddf-dcbc-46ae-9b27-52c5024bd0b5 |
| Verdict: | Malicious activity |
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | June 28, 2024, 20:25:49 |
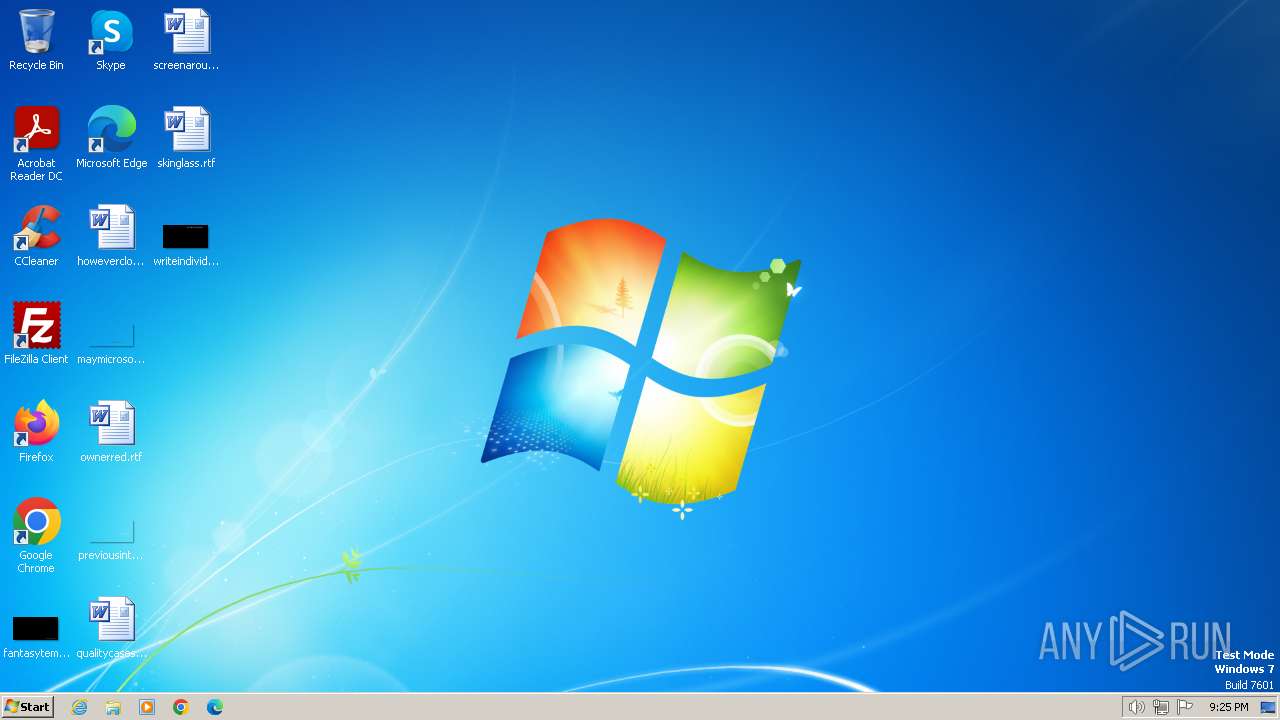
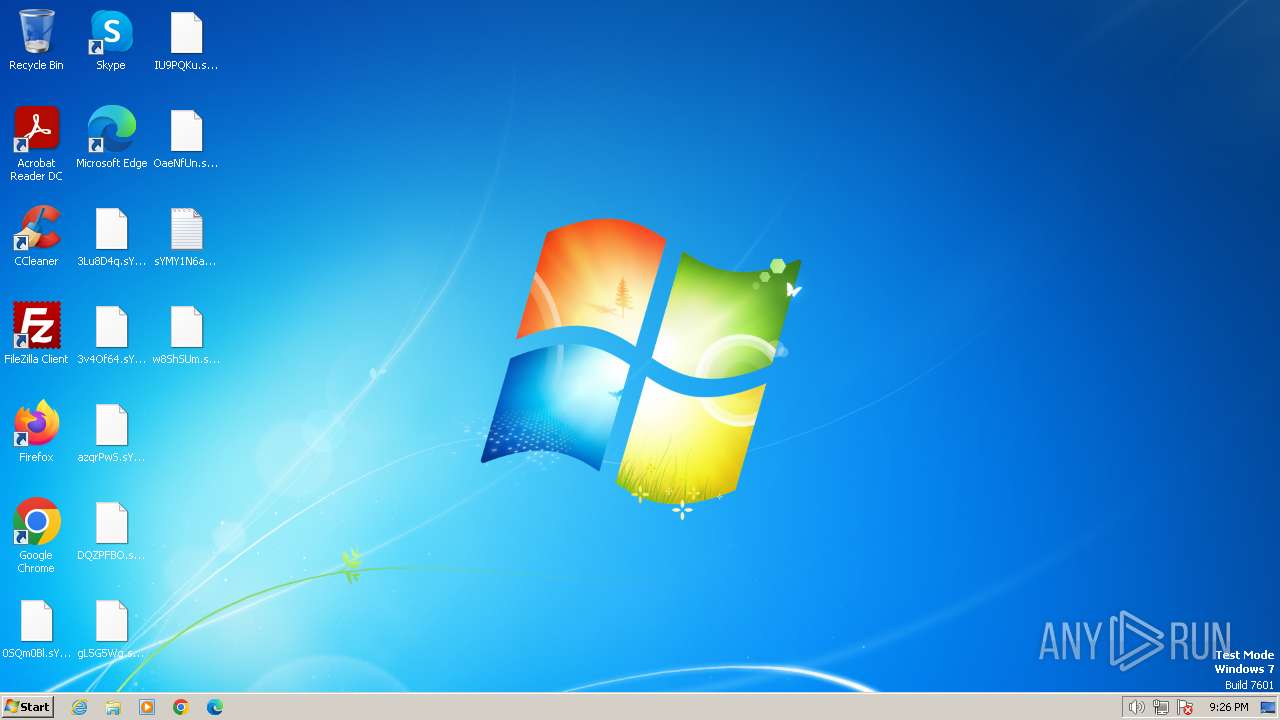
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 448F1796FE8DE02194B21C0715E0A5F6 |
| SHA1: | 935C0B39837319FDA571AA800B67D997B79C3198 |
| SHA256: | EB82946FA0DE261E92F8F60AA878C9FEF9EBB34FDABABA66995403B110118B12 |
| SSDEEP: | 3072:nmhXodguLP/5qUpfDT6zT73Ew8Ym9wV9JyknP7SAy:bKzkw8YKwVLyknzSA |
MALICIOUS
Drops the executable file immediately after the start
- brain.exe (PID: 3520)
- brain.exe (PID: 2092)
[YARA] LockBit is detected
- brain.exe (PID: 2092)
Known privilege escalation attack
- dllhost.exe (PID: 3372)
Steals credentials from Web Browsers
- brain.exe (PID: 2092)
Actions looks like stealing of personal data
- brain.exe (PID: 2092)
SUSPICIOUS
Write to the desktop.ini file (may be used to cloak folders)
- brain.exe (PID: 2092)
Executable content was dropped or overwritten
- brain.exe (PID: 2092)
Hides command output
- cmd.exe (PID: 2512)
Starts CMD.EXE for commands execution
- 2D2D.tmp (PID: 2796)
Creates files like ransomware instruction
- brain.exe (PID: 2092)
Reads browser cookies
- brain.exe (PID: 2092)
Starts application with an unusual extension
- brain.exe (PID: 2092)
Reads the Internet Settings
- 2D2D.tmp (PID: 2796)
Reads security settings of Internet Explorer
- 2D2D.tmp (PID: 2796)
INFO
Checks supported languages
- brain.exe (PID: 3520)
- brain.exe (PID: 2092)
- wmpnscfg.exe (PID: 2864)
- 2D2D.tmp (PID: 2796)
Reads the machine GUID from the registry
- brain.exe (PID: 3520)
- brain.exe (PID: 2092)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 3372)
Reads the computer name
- brain.exe (PID: 3520)
- brain.exe (PID: 2092)
- wmpnscfg.exe (PID: 2864)
- 2D2D.tmp (PID: 2796)
Checks transactions between databases Windows and Oracle
- brain.exe (PID: 3520)
Manual execution by a user
- wmpnscfg.exe (PID: 2864)
Create files in a temporary directory
- brain.exe (PID: 2092)
Creates files in the program directory
- brain.exe (PID: 2092)
Creates files or folders in the user directory
- brain.exe (PID: 2092)
Dropped object may contain TOR URL's
- brain.exe (PID: 2092)
The dropped object may contain a URL to Tor Browser
- brain.exe (PID: 2092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:09:09 01:27:01+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 99328 |
| InitializedDataSize: | 50688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1946f |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
52
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2092 | "C:\Users\admin\AppData\Local\Temp\brain.exe" | C:\Users\admin\AppData\Local\Temp\brain.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2512 | "C:\Windows\System32\cmd.exe" /C DEL /F /Q C:\PROGRA~2\2D2D.tmp >> NUL | C:\Windows\System32\cmd.exe | — | 2D2D.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2796 | "C:\ProgramData\2D2D.tmp" | C:\ProgramData\2D2D.tmp | — | brain.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3372 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3520 | "C:\Users\admin\AppData\Local\Temp\brain.exe" | C:\Users\admin\AppData\Local\Temp\brain.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 263
Read events
3 247
Write events
1 016
Delete events
0
Modification events
| (PID) Process: | (3372) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3372) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3372) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3372) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2092) brain.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\Analytic |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (2092) brain.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\Analytic |
| Operation: | write | Name: | ChannelAccess |
Value: O:BAG:SYD:(A;;0x1;;;SY)(A;;0x5;;;BA)(A;;0x1;;;LA) | |||
| (PID) Process: | (2092) brain.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\DirectShowFilterGraph |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (2092) brain.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\DirectShowFilterGraph |
| Operation: | write | Name: | ChannelAccess |
Value: O:BAG:SYD:(A;;0x1;;;SY)(A;;0x5;;;BA)(A;;0x1;;;LA) | |||
| (PID) Process: | (2092) brain.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\DirectShowPluginControl |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (2092) brain.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\DirectShowPluginControl |
| Operation: | write | Name: | ChannelAccess |
Value: O:BAG:SYD:(A;;0x1;;;SY)(A;;0x5;;;BA)(A;;0x1;;;LA) | |||
Executable files
11
Suspicious files
1 365
Text files
967
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2092 | brain.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\DDDDDDDDDDD | binary | |
MD5:8D703B6D49AB62FFDD5BACFEC541E929 | SHA256:8711ADF9F806B63623A046913DF888A8B41A54BD6516C8E5F2C22515BB68BBDA | |||
| 2092 | brain.exe | C:\Users\sYMY1N6ah.README.txt | text | |
MD5:DEB2E0756D331362D57AD9FE408C4FF3 | SHA256:1DDACEE1D25936970279557169037A335B362F86C3797DED625D68077BD0145C | |||
| 2092 | brain.exe | C:\Users\Administrator\sYMY1N6ah.README.txt | text | |
MD5:DEB2E0756D331362D57AD9FE408C4FF3 | SHA256:1DDACEE1D25936970279557169037A335B362F86C3797DED625D68077BD0145C | |||
| 2092 | brain.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\AAAAAAAAAAA | binary | |
MD5:8D703B6D49AB62FFDD5BACFEC541E929 | SHA256:8711ADF9F806B63623A046913DF888A8B41A54BD6516C8E5F2C22515BB68BBDA | |||
| 2092 | brain.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\CCCCCCCCCCC | binary | |
MD5:8D703B6D49AB62FFDD5BACFEC541E929 | SHA256:8711ADF9F806B63623A046913DF888A8B41A54BD6516C8E5F2C22515BB68BBDA | |||
| 2092 | brain.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\GGGGGGGGGGG | binary | |
MD5:8D703B6D49AB62FFDD5BACFEC541E929 | SHA256:8711ADF9F806B63623A046913DF888A8B41A54BD6516C8E5F2C22515BB68BBDA | |||
| 2092 | brain.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\BBBBBBBBBBB | binary | |
MD5:8D703B6D49AB62FFDD5BACFEC541E929 | SHA256:8711ADF9F806B63623A046913DF888A8B41A54BD6516C8E5F2C22515BB68BBDA | |||
| 2092 | brain.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\JJJJJJJJJJJ | binary | |
MD5:8D703B6D49AB62FFDD5BACFEC541E929 | SHA256:8711ADF9F806B63623A046913DF888A8B41A54BD6516C8E5F2C22515BB68BBDA | |||
| 2092 | brain.exe | C:\Users\Administrator\Videos\sYMY1N6ah.README.txt | text | |
MD5:DEB2E0756D331362D57AD9FE408C4FF3 | SHA256:1DDACEE1D25936970279557169037A335B362F86C3797DED625D68077BD0145C | |||
| 2092 | brain.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\IIIIIIIIIII | binary | |
MD5:8D703B6D49AB62FFDD5BACFEC541E929 | SHA256:8711ADF9F806B63623A046913DF888A8B41A54BD6516C8E5F2C22515BB68BBDA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
12
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.53.40.40:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 23.53.40.83:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1372 | svchost.exe | 23.53.40.40:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 23.53.40.83:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |