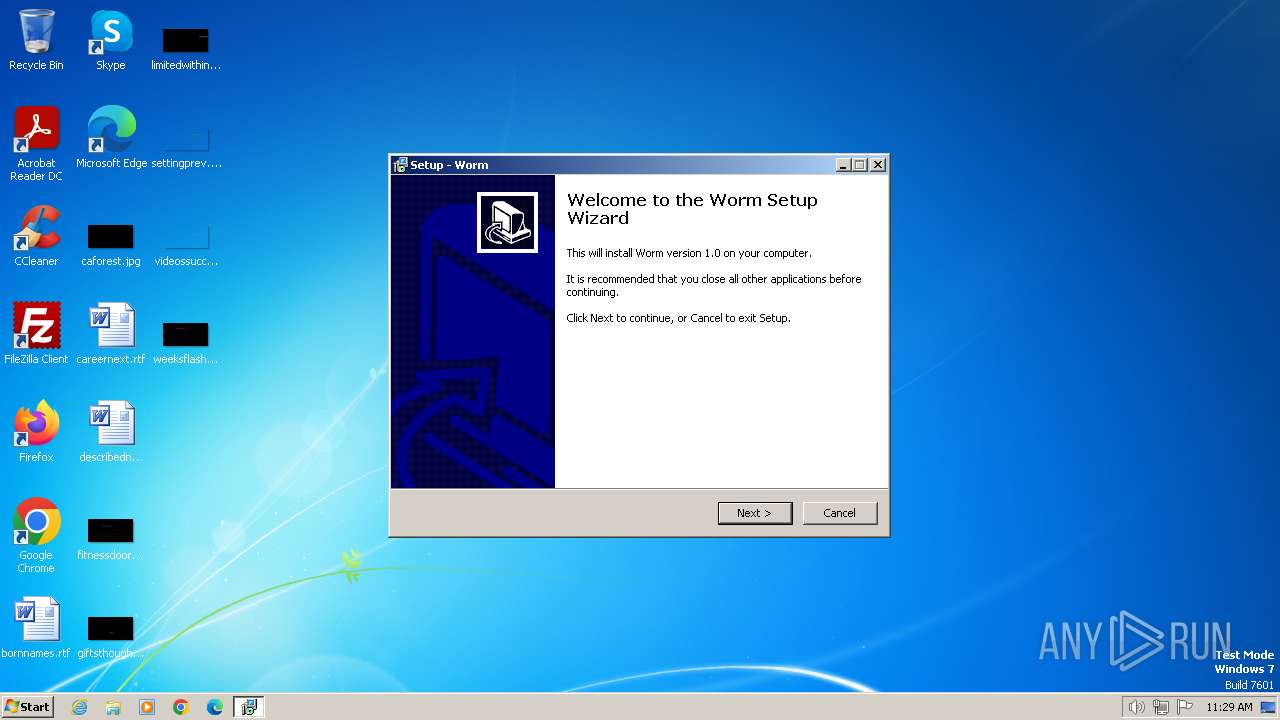
| File name: | Worm.exe |
| Full analysis: | https://app.any.run/tasks/5006c191-7231-4562-9b14-4bc6ddb9c777 |
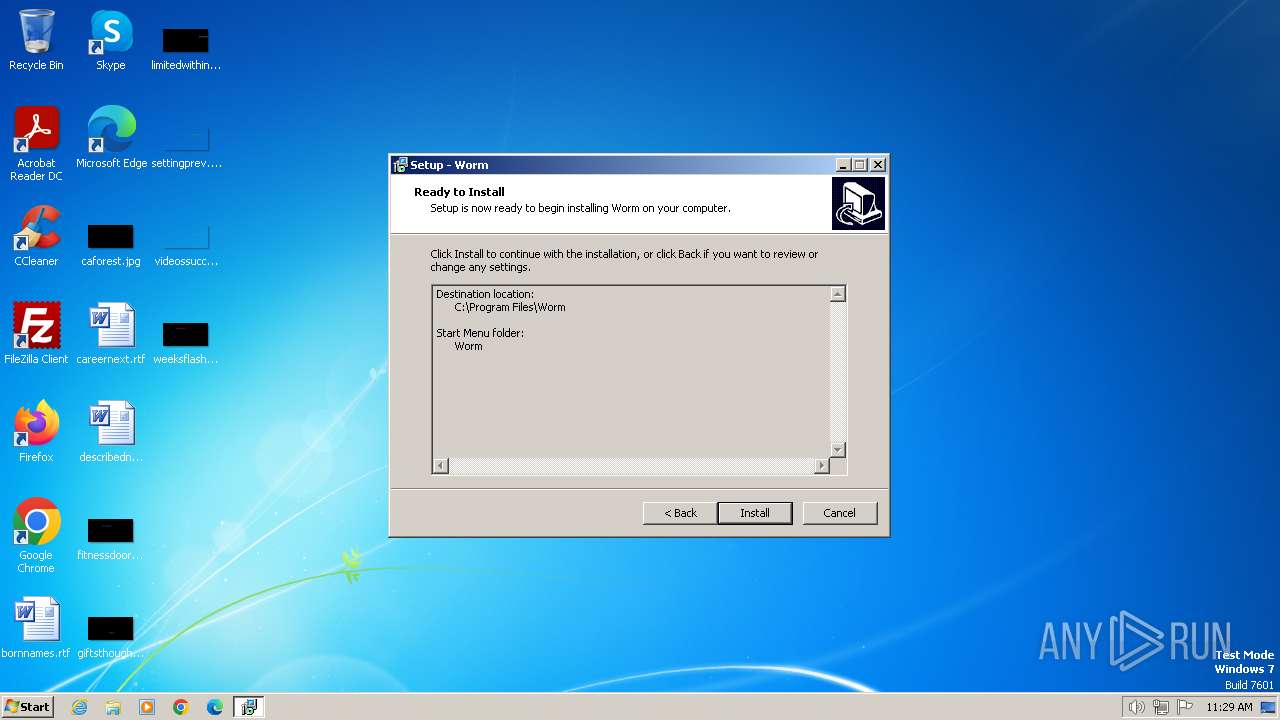
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2024, 11:28:39 |
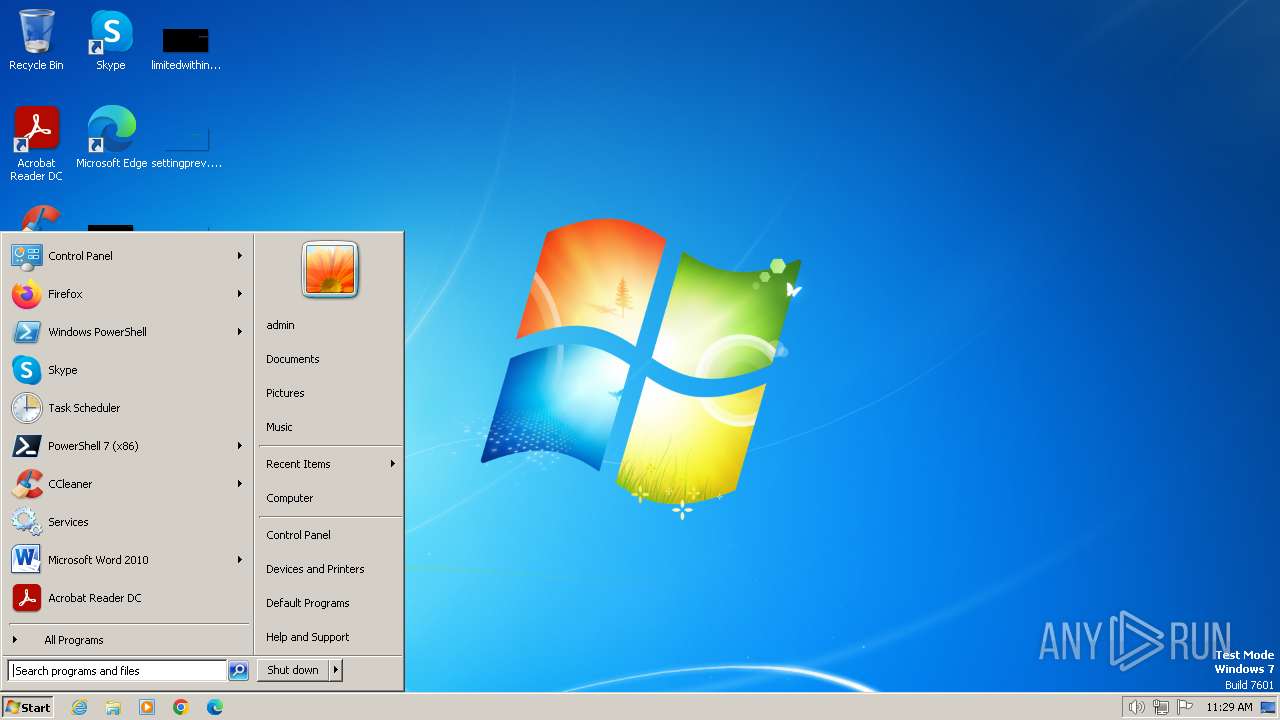
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0F9EE5D40776B69E4631E8A5AF6A6AA4 |
| SHA1: | 1859F921E7E25EA5F2178E1CB01E96431E637F86 |
| SHA256: | EB6AC5A8248DC2B48A96F4CE116AE6E045E5C09B4F57F1F3D9797EA7C9ADDEFB |
| SSDEEP: | 98304:Y6ZMVLTGqsu0NUIf0qbZnWtXIT6VoFlJn3H19nDq3I1VEK8osW6FCOyWGpI6AkPD:3fPWK7d |
MALICIOUS
Drops the executable file immediately after the start
- Worm.exe (PID: 752)
- Worm.exe (PID: 2032)
- Worm.tmp (PID: 3768)
Actions looks like stealing of personal data
- Worm.tmp (PID: 3768)
SUSPICIOUS
Process drops legitimate windows executable
- Worm.tmp (PID: 3768)
Executable content was dropped or overwritten
- Worm.exe (PID: 2032)
- Worm.tmp (PID: 3768)
- Worm.exe (PID: 752)
Reads the Windows owner or organization settings
- Worm.tmp (PID: 3768)
INFO
Checks supported languages
- Worm.exe (PID: 752)
- Worm.tmp (PID: 1652)
- Worm.exe (PID: 2032)
- Worm.tmp (PID: 3768)
Reads the computer name
- Worm.tmp (PID: 1652)
- Worm.tmp (PID: 3768)
Create files in a temporary directory
- Worm.exe (PID: 752)
- Worm.exe (PID: 2032)
- Worm.tmp (PID: 3768)
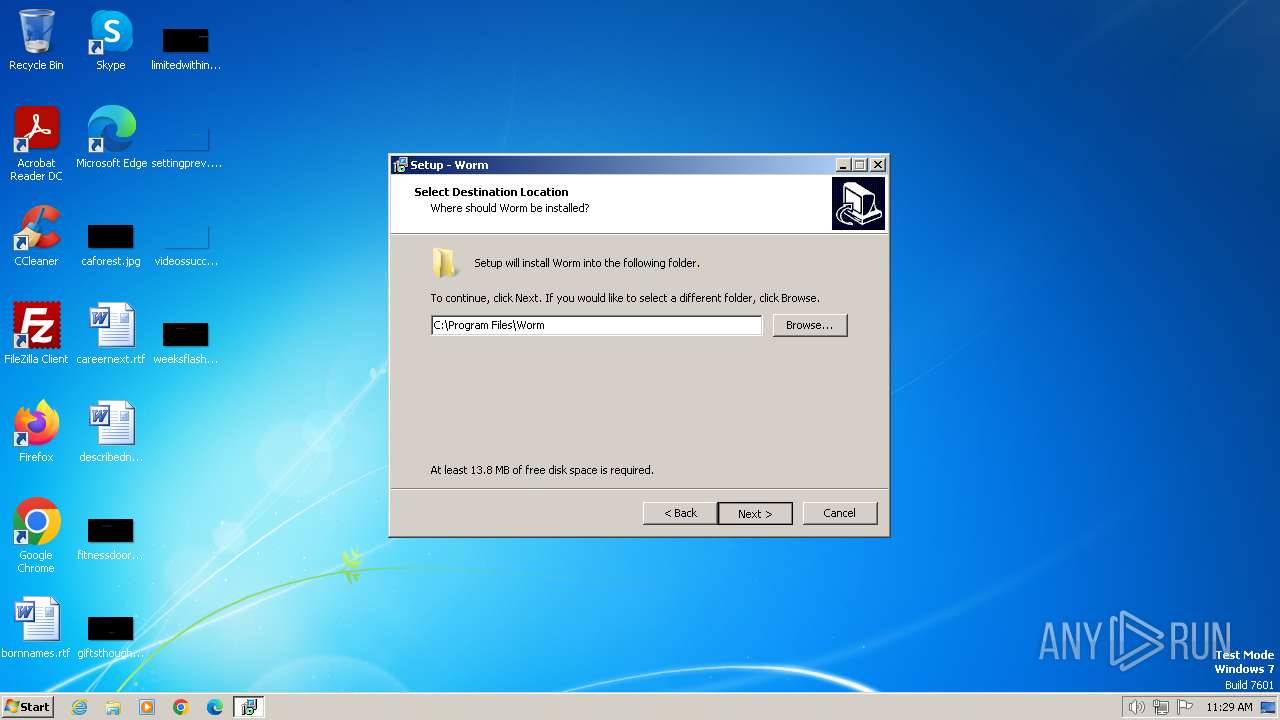
Creates files in the program directory
- Worm.tmp (PID: 3768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (71.1) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.1) |
| .scr | | | Windows screen saver (8.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | My Company, Inc. |
| FileDescription: | Worm Setup |
| FileVersion: | |
| LegalCopyright: | |
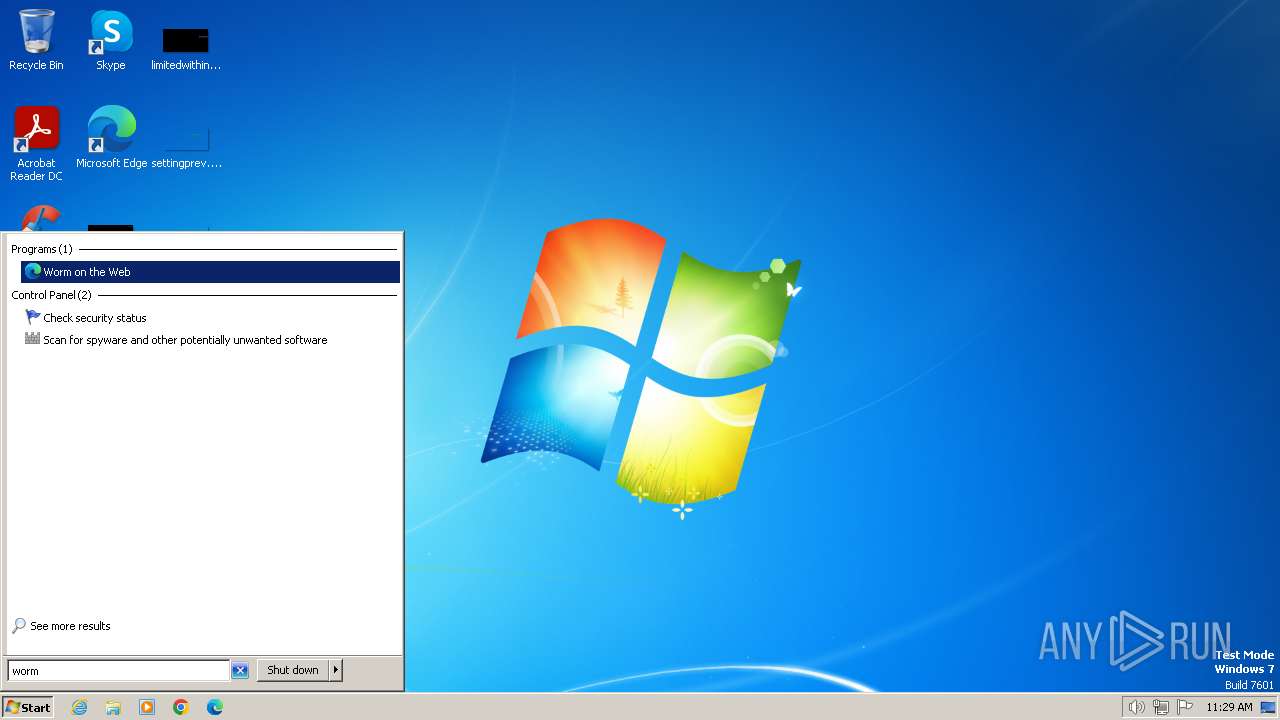
| ProductName: | Worm |
| ProductVersion: | 1.0 |
Total processes
42
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Users\admin\AppData\Local\Temp\Worm.exe" | C:\Users\admin\AppData\Local\Temp\Worm.exe | explorer.exe | ||||||||||||
User: admin Company: My Company, Inc. Integrity Level: MEDIUM Description: Worm Setup Exit code: 0 Version: Modules
| |||||||||||||||
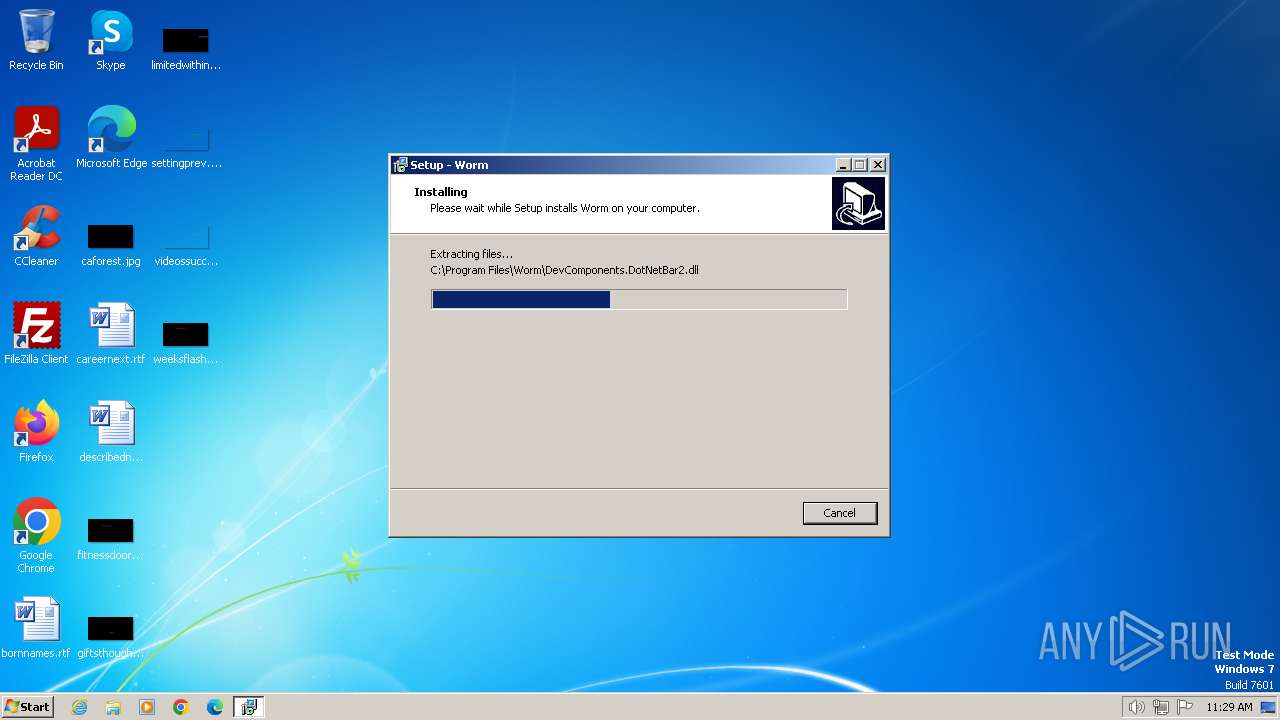
| 1652 | "C:\Users\admin\AppData\Local\Temp\is-HV8M4.tmp\Worm.tmp" /SL5="$F0184,2786258,56832,C:\Users\admin\AppData\Local\Temp\Worm.exe" | C:\Users\admin\AppData\Local\Temp\is-HV8M4.tmp\Worm.tmp | — | Worm.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2032 | "C:\Users\admin\AppData\Local\Temp\Worm.exe" /SPAWNWND=$100166 /NOTIFYWND=$F0184 | C:\Users\admin\AppData\Local\Temp\Worm.exe | Worm.tmp | ||||||||||||
User: admin Company: My Company, Inc. Integrity Level: HIGH Description: Worm Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3768 | "C:\Users\admin\AppData\Local\Temp\is-QJ9GB.tmp\Worm.tmp" /SL5="$1301B4,2786258,56832,C:\Users\admin\AppData\Local\Temp\Worm.exe" /SPAWNWND=$100166 /NOTIFYWND=$F0184 | C:\Users\admin\AppData\Local\Temp\is-QJ9GB.tmp\Worm.tmp | Worm.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
772
Read events
766
Write events
0
Delete events
6
Modification events
| (PID) Process: | (3768) Worm.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: FF026CAD0F6BFF1DB948016AA586557D399FA13A84A421453CF046A6AB823D88 | |||
| (PID) Process: | (3768) Worm.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Program Files\Worm\Builder (2).exe | |||
| (PID) Process: | (3768) Worm.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3768) Worm.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: AFAFA0C619F5E4984389814EF68F569BA44FBD7BC84F3E0837E404FD697E0F43 | |||
| (PID) Process: | (3768) Worm.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: B80E0000C61E62812658DA01 | |||
| (PID) Process: | (3768) Worm.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
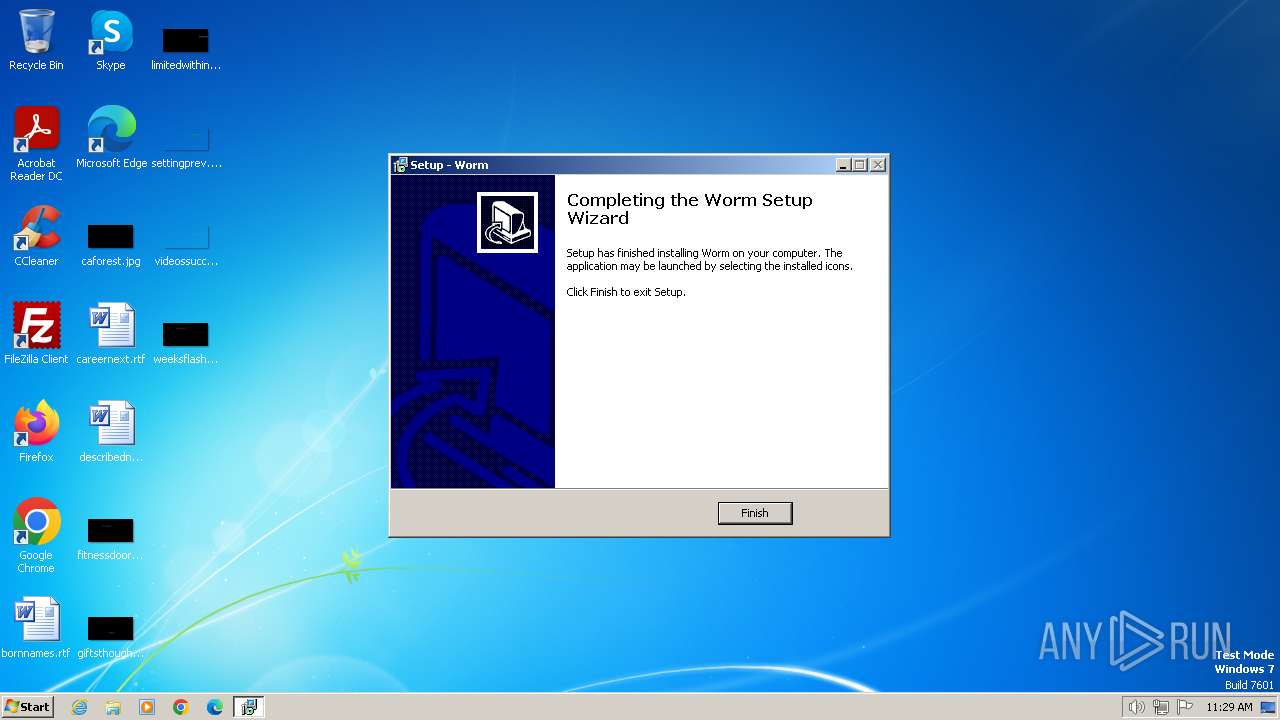
Executable files
47
Suspicious files
19
Text files
403
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | Worm.tmp | C:\Program Files\Worm\is-MNAF4.tmp | executable | |
MD5:92C00B0F2E9ECBFC5155A7E789E19DEB | SHA256:A9CF3E1218F8E0AB71A81C0F4339C0A6C7047EF04A6AE3A20488AF638CB9F931 | |||
| 3768 | Worm.tmp | C:\Users\admin\AppData\Local\Temp\is-O3TNO.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 3768 | Worm.tmp | C:\Program Files\Worm\Dat.dat | text | |
MD5:360EE0FDC26784CAA46411DAE500A138 | SHA256:308036D74BBE6C52EE379CE01937168DF6930EE11D10B076751B8D4049970AFF | |||
| 3768 | Worm.tmp | C:\Program Files\Worm\unins000.exe | executable | |
MD5:60145B5523F4CADA56F4ECD5B7ABF671 | SHA256:10A30041D45A78C5C13740545007EBDC17930D10AE3E1914222B2746643FBC58 | |||
| 3768 | Worm.tmp | C:\Program Files\Worm\is-4AQSP.tmp | executable | |
MD5:71CF577CAF188F332C8D6C88B582EF53 | SHA256:FE6031DD64C31D1ABF4DF4A1BEF2F5F3D7EDA0149DD0B89AF27F6F83593526B5 | |||
| 3768 | Worm.tmp | C:\Program Files\Worm\Builder (2).exe | executable | |
MD5:6CFF2B5B9476059689E6F0F28F471D9C | SHA256:98A3D61ED8583703BD6B3D1FE8A3A6F8D31643115DD4825D819A8FCA64064068 | |||
| 3768 | Worm.tmp | C:\Program Files\Worm\Builder.exe | executable | |
MD5:71CF577CAF188F332C8D6C88B582EF53 | SHA256:FE6031DD64C31D1ABF4DF4A1BEF2F5F3D7EDA0149DD0B89AF27F6F83593526B5 | |||
| 3768 | Worm.tmp | C:\Program Files\Worm\is-F1KG3.tmp | text | |
MD5:360EE0FDC26784CAA46411DAE500A138 | SHA256:308036D74BBE6C52EE379CE01937168DF6930EE11D10B076751B8D4049970AFF | |||
| 3768 | Worm.tmp | C:\Program Files\Worm\is-4OAGC.tmp | executable | |
MD5:6CFF2B5B9476059689E6F0F28F471D9C | SHA256:98A3D61ED8583703BD6B3D1FE8A3A6F8D31643115DD4825D819A8FCA64064068 | |||
| 3768 | Worm.tmp | C:\Program Files\Worm\Bytes Worm.exe | executable | |
MD5:92C00B0F2E9ECBFC5155A7E789E19DEB | SHA256:A9CF3E1218F8E0AB71A81C0F4339C0A6C7047EF04A6AE3A20488AF638CB9F931 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |