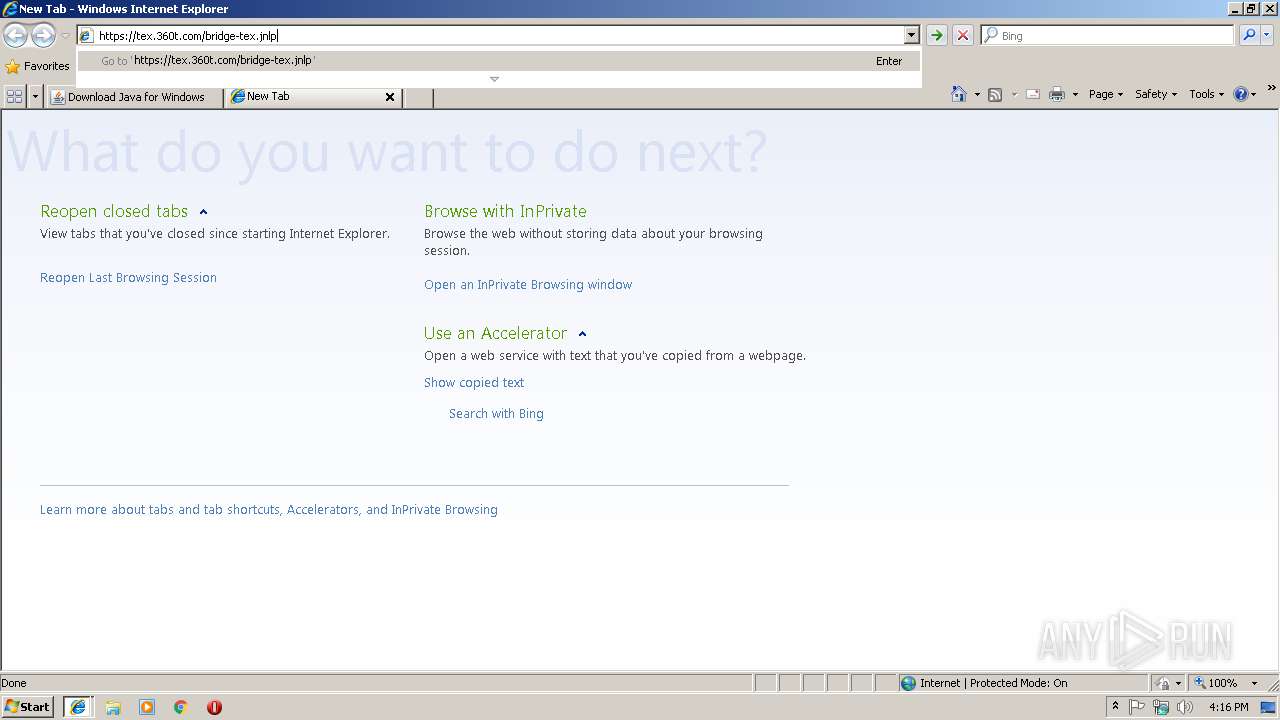
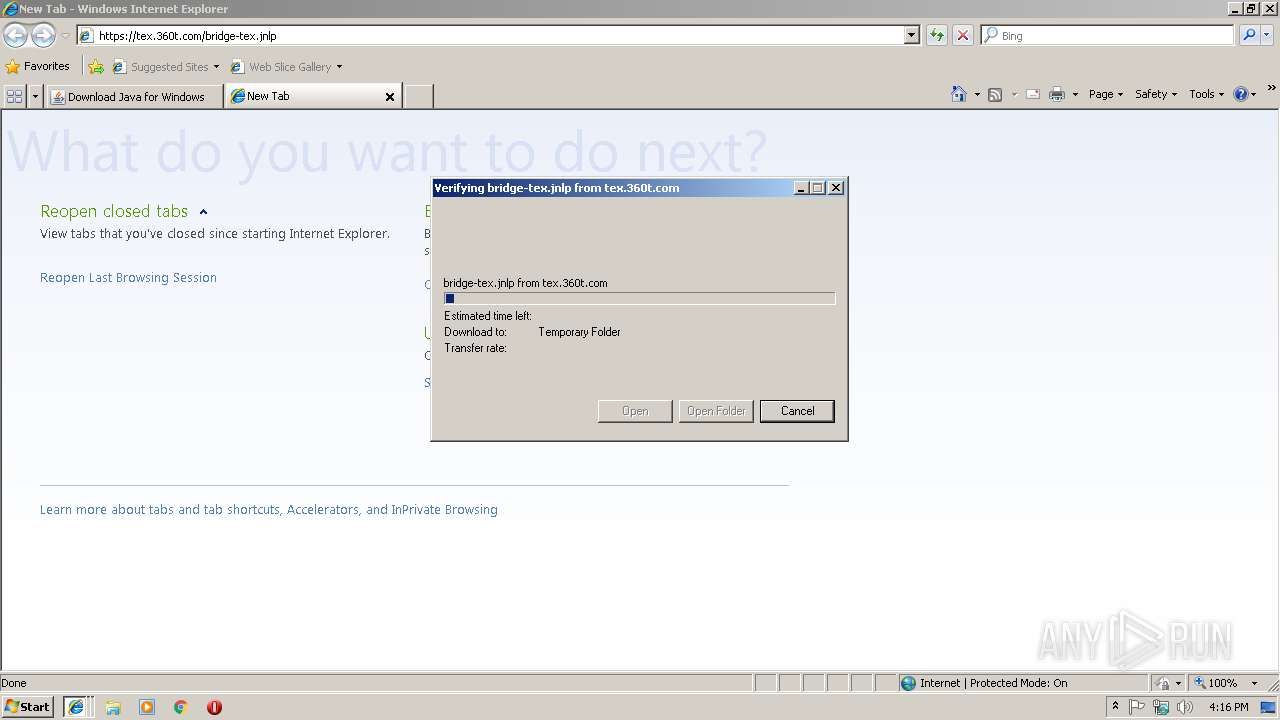
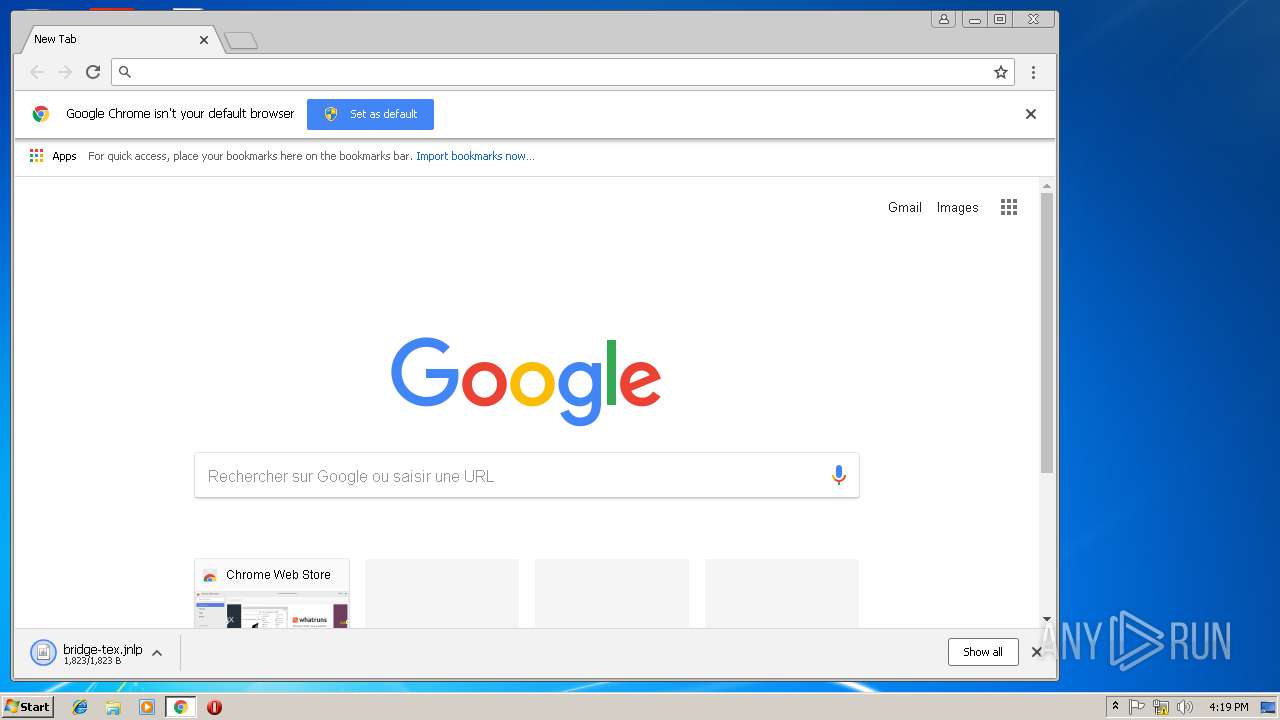
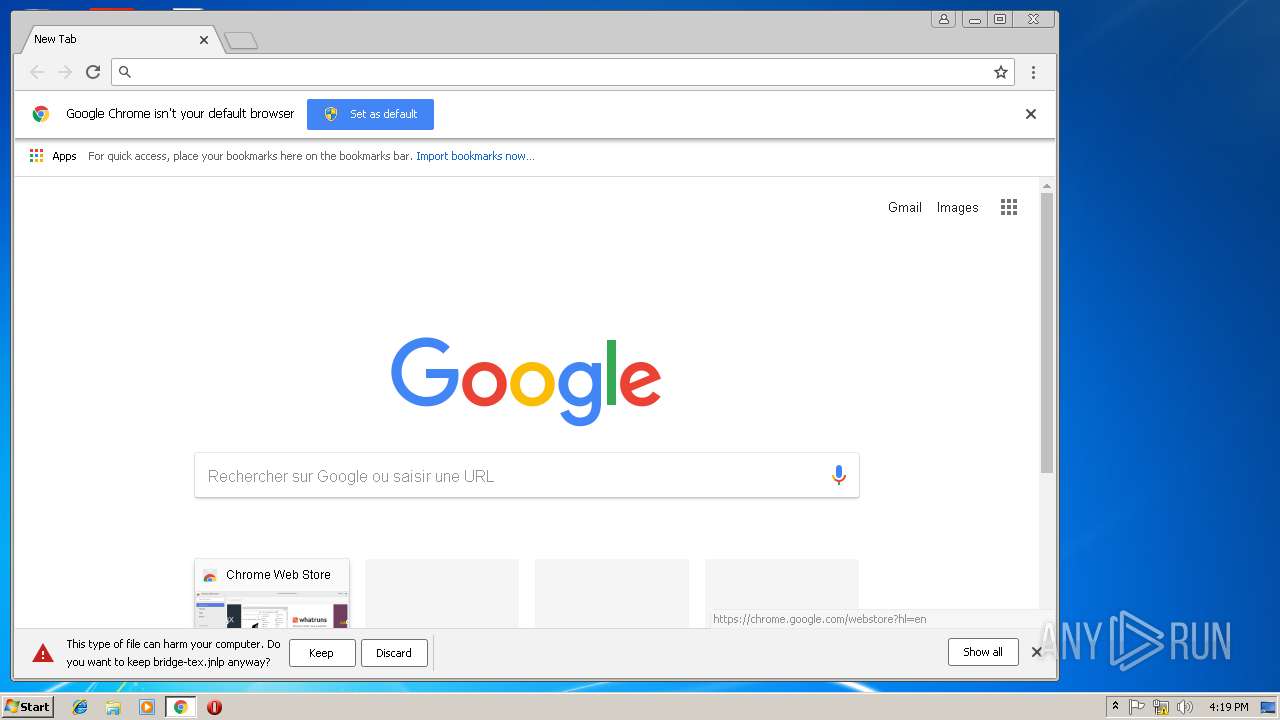
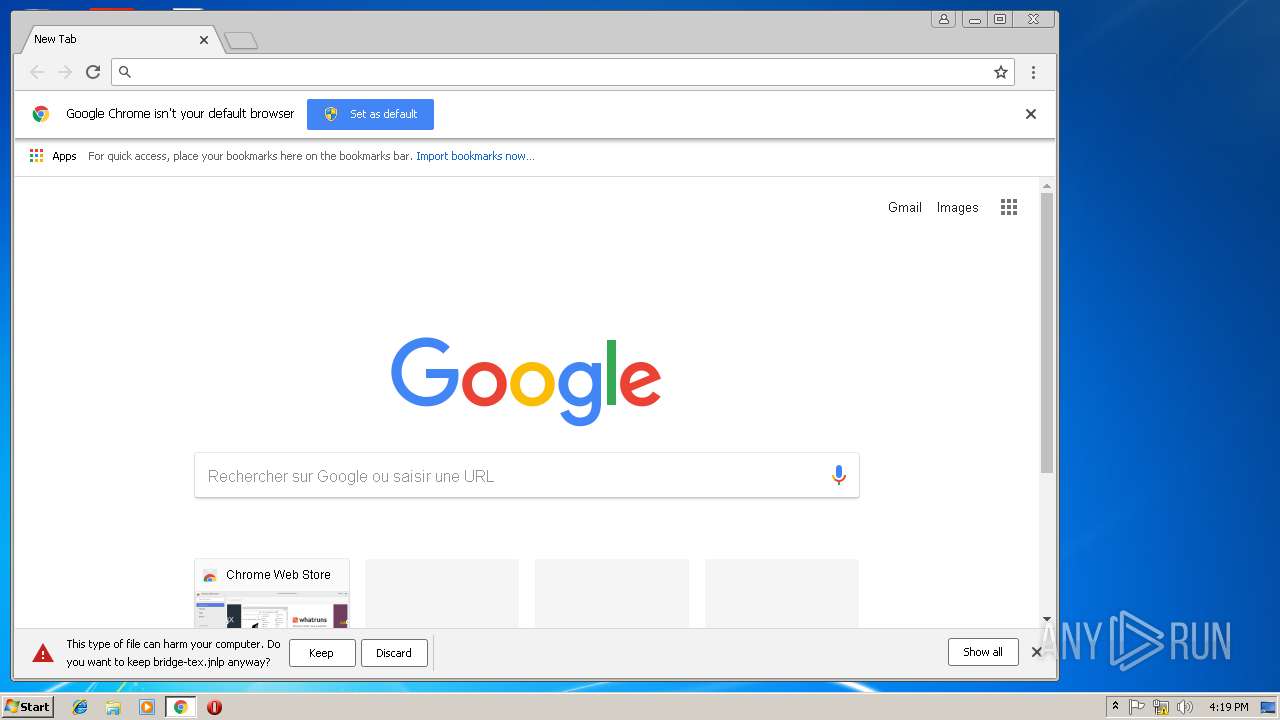
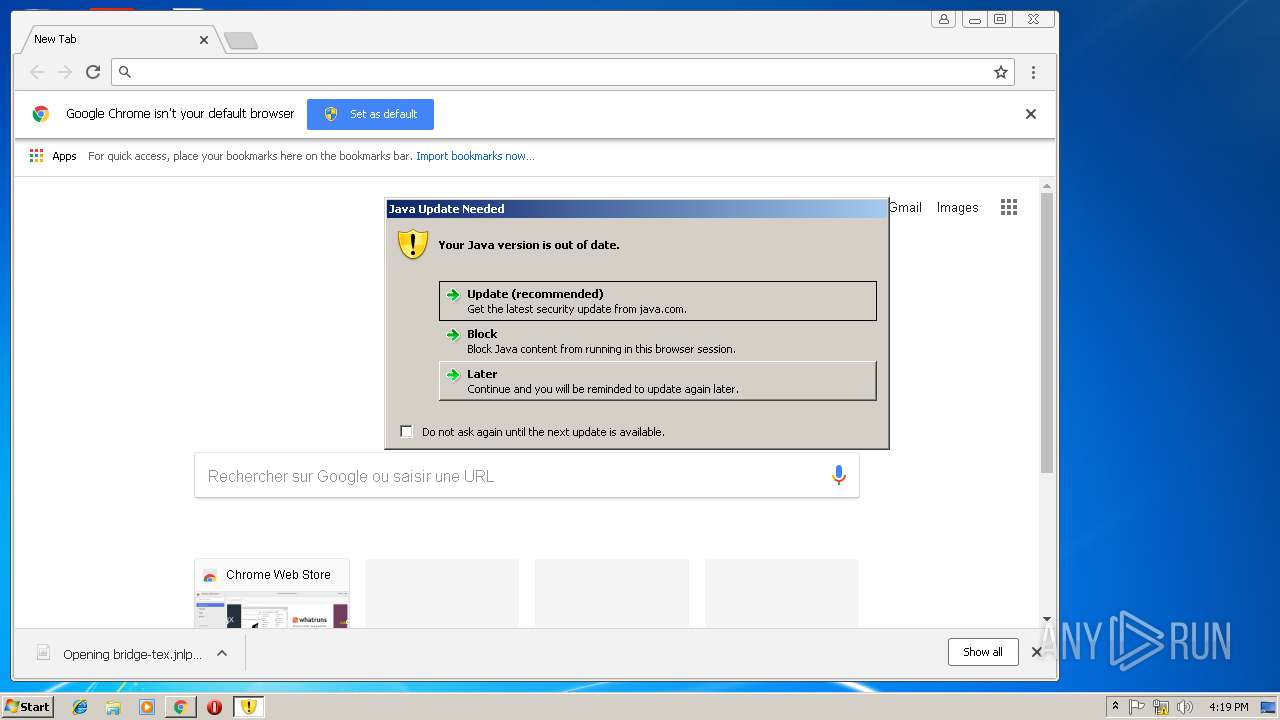
| download: | bridge-tex.jnlp |
| Full analysis: | https://app.any.run/tasks/0eebe70d-9000-4250-8f8f-a5e3f3a7acda |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2019, 16:15:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text |
| MD5: | EC6E97E94F3DA677D937320A40E5312B |
| SHA1: | 5BD037BC57457EB752DF1EDEFBF613A523C53AB0 |
| SHA256: | EB5716AACBCF188A9EDE3A5DCD4EE79ADD7FF8F22D87C1D051A45A11915B595C |
| SSDEEP: | 24:2dvKjAEbB75OVegxbRbdrW6LhKwlN42PUvMLI5xD0MTkjj7m9l5vgnbBKny0Jp:cvUxbupZBWahjO2b8pRTCfm/5yI3Jp |
MALICIOUS
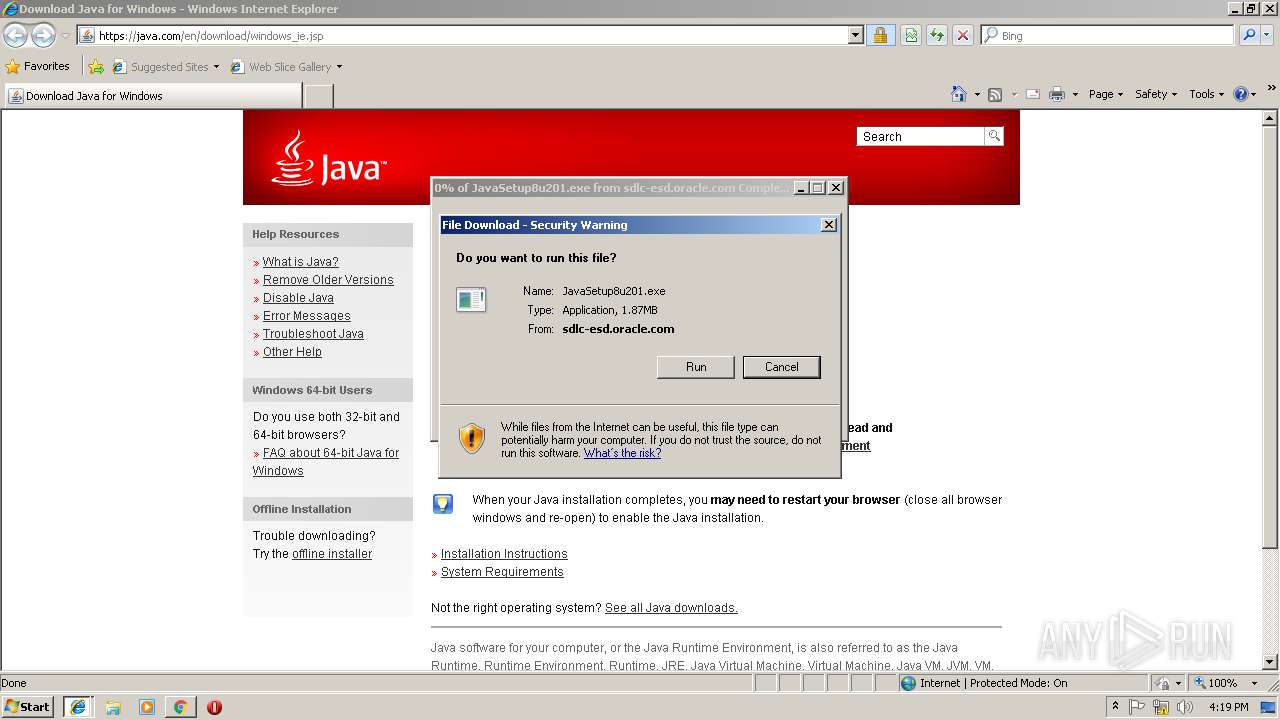
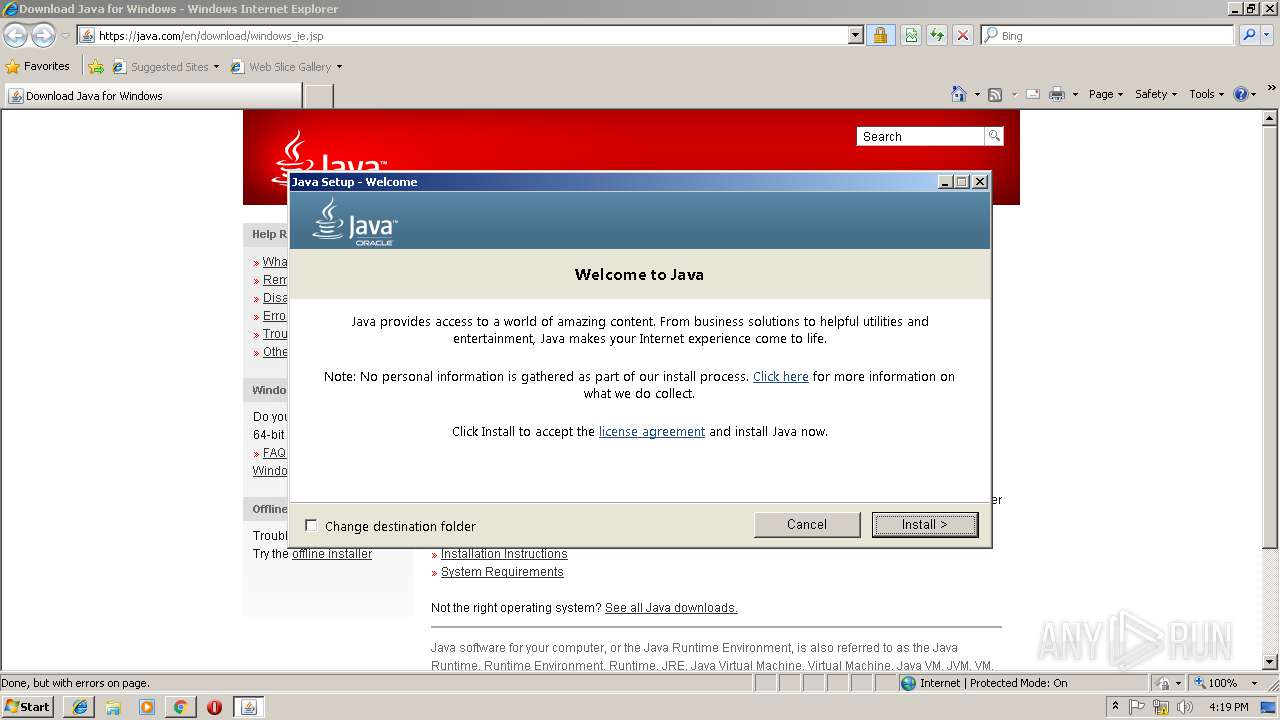
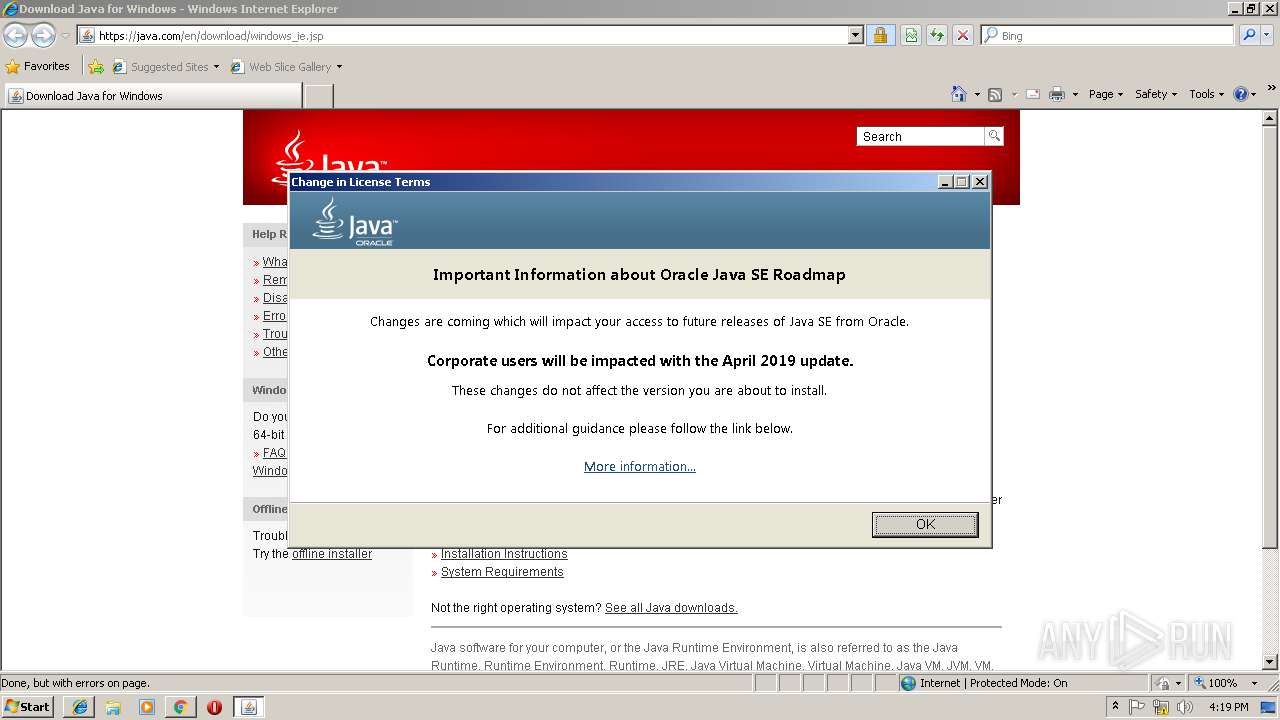
Application was dropped or rewritten from another process
- JavaSetup8u201[1].exe (PID: 3612)
- JavaSetup8u201[1].exe (PID: 3960)
- LZMA_EXE (PID: 2776)
- JavaSetup8u201[1].exe (PID: 3044)
- LZMA_EXE (PID: 3176)
- bspatch.exe (PID: 2244)
- unpack200.exe (PID: 2344)
- javaw.exe (PID: 3804)
- unpack200.exe (PID: 3608)
- unpack200.exe (PID: 1012)
- unpack200.exe (PID: 2568)
- unpack200.exe (PID: 2520)
- unpack200.exe (PID: 2692)
- unpack200.exe (PID: 2204)
Loads dropped or rewritten executable
- javaw.exe (PID: 3592)
- iexplore.exe (PID: 180)
- javaw.exe (PID: 3816)
- unpack200.exe (PID: 3608)
- javaws.exe (PID: 2972)
- iexplore.exe (PID: 2728)
- javaw.exe (PID: 304)
- javaw.exe (PID: 3220)
- javaws.exe (PID: 3392)
- javaw.exe (PID: 3744)
- iexplore.exe (PID: 2816)
- unpack200.exe (PID: 1012)
- unpack200.exe (PID: 2568)
- unpack200.exe (PID: 2692)
- unpack200.exe (PID: 2344)
- unpack200.exe (PID: 2204)
- javaw.exe (PID: 2320)
- iexplore.exe (PID: 2228)
- unpack200.exe (PID: 2520)
- javaw.exe (PID: 3804)
- installer.exe (PID: 1868)
SUSPICIOUS
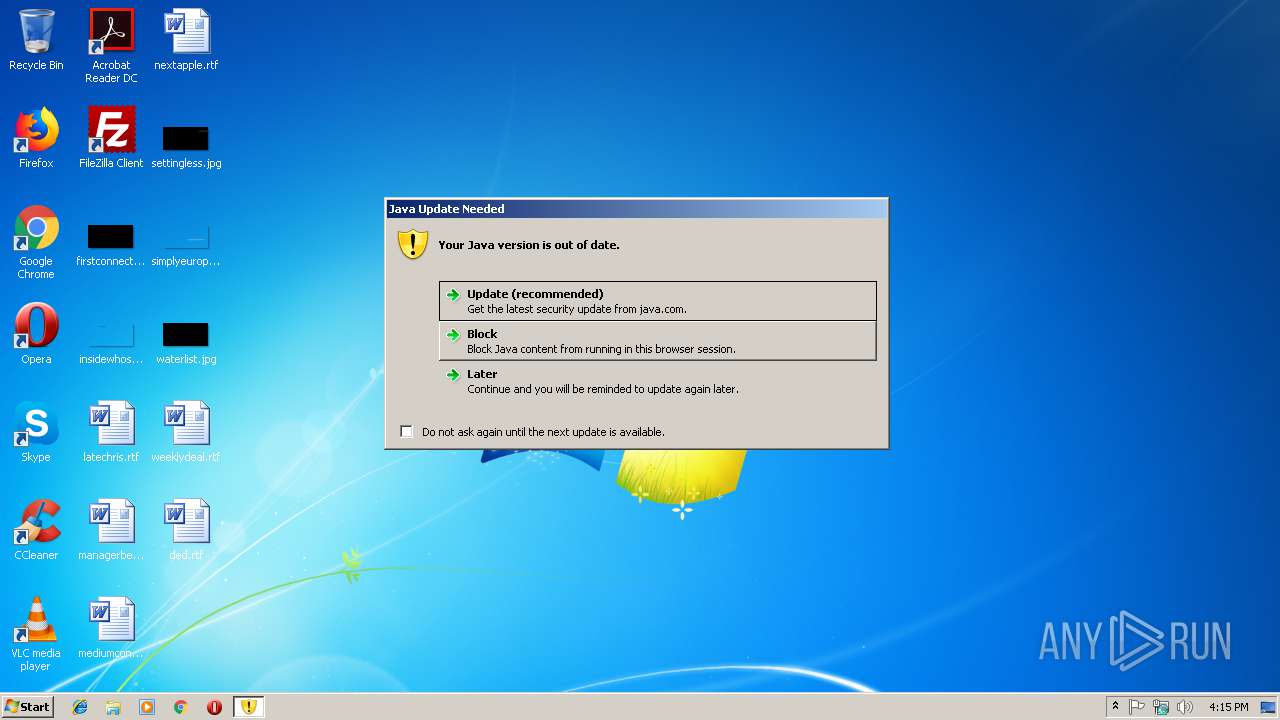
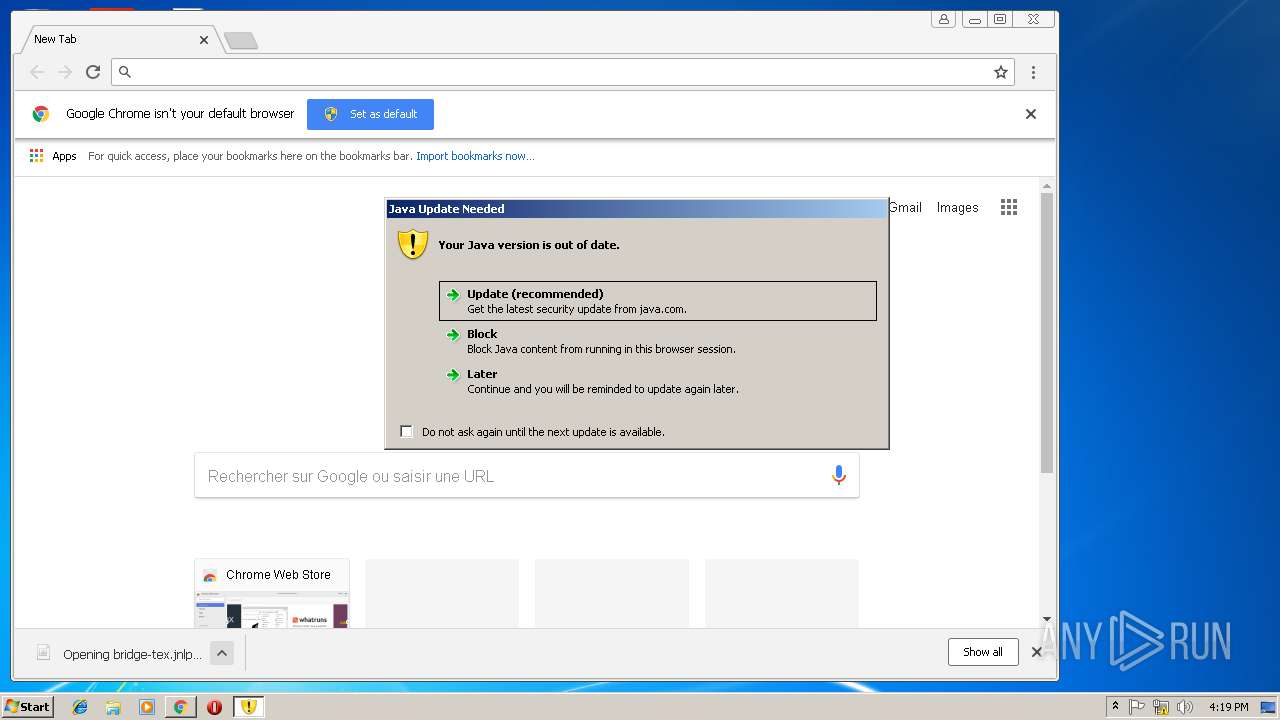
Executes JAVA applets
- javaws.exe (PID: 2972)
- javaws.exe (PID: 3392)
- installer.exe (PID: 1868)
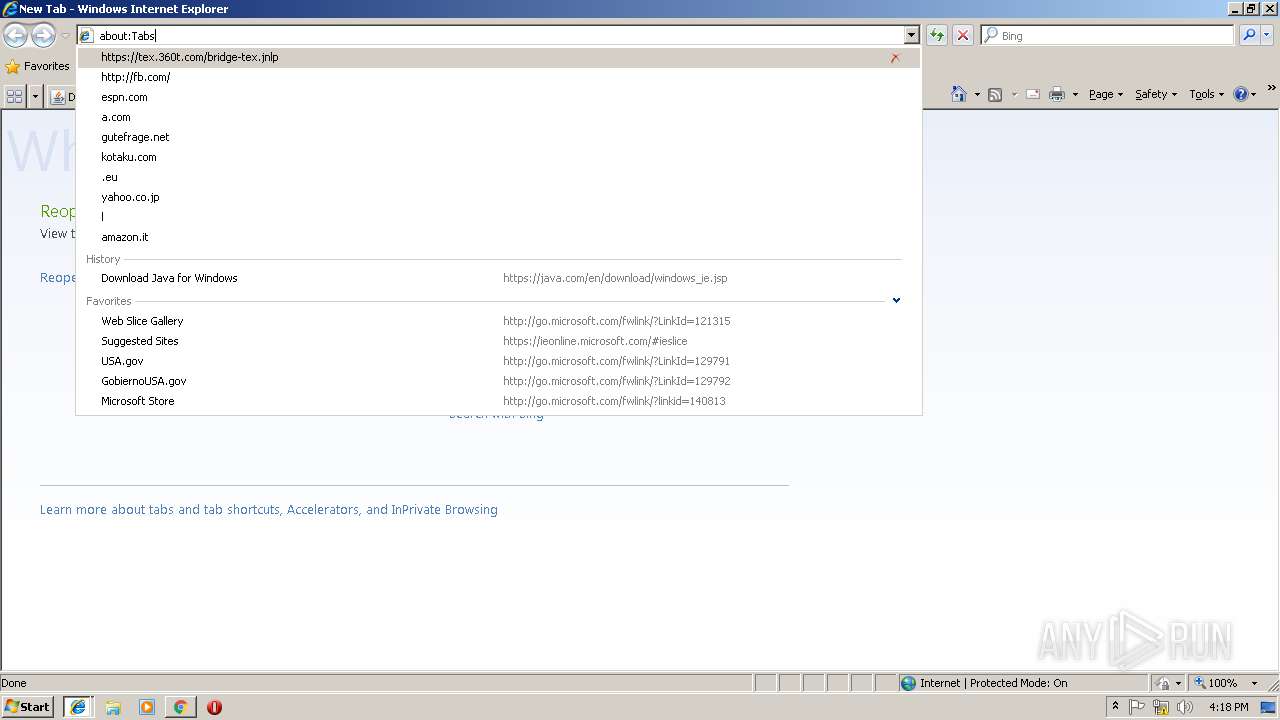
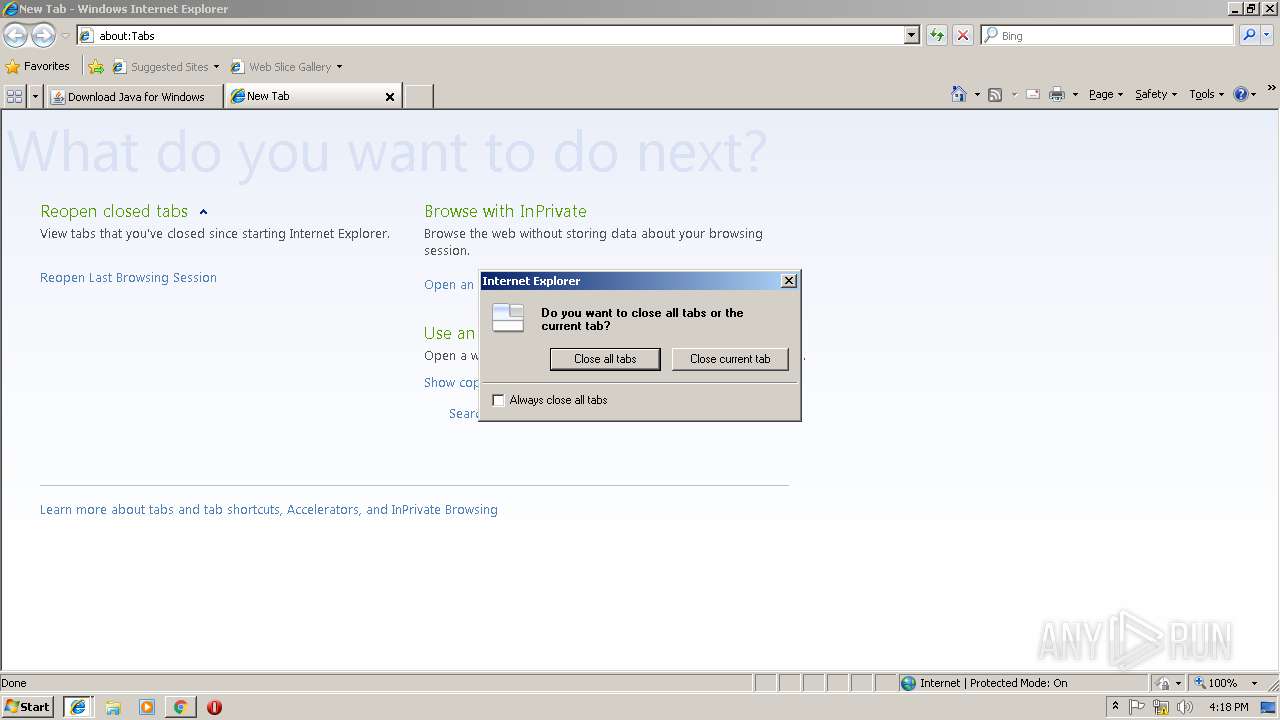
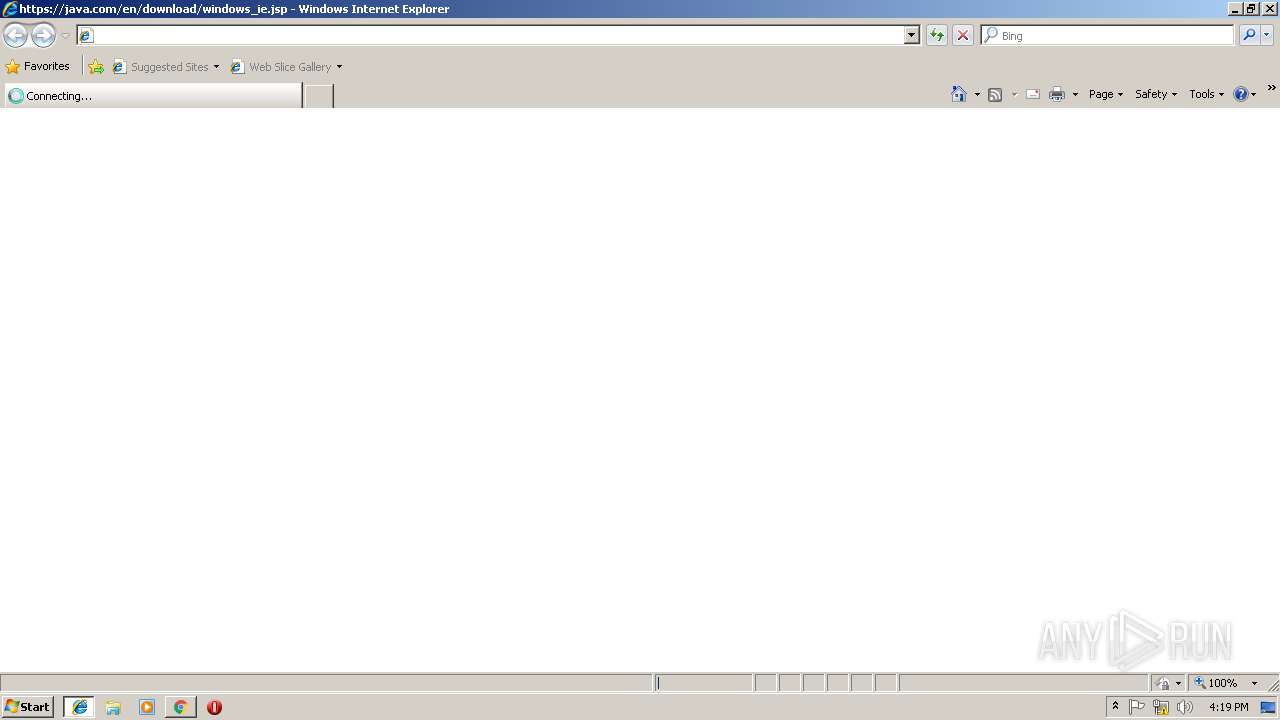
Starts Internet Explorer
- javaws.exe (PID: 2972)
- javaws.exe (PID: 3392)
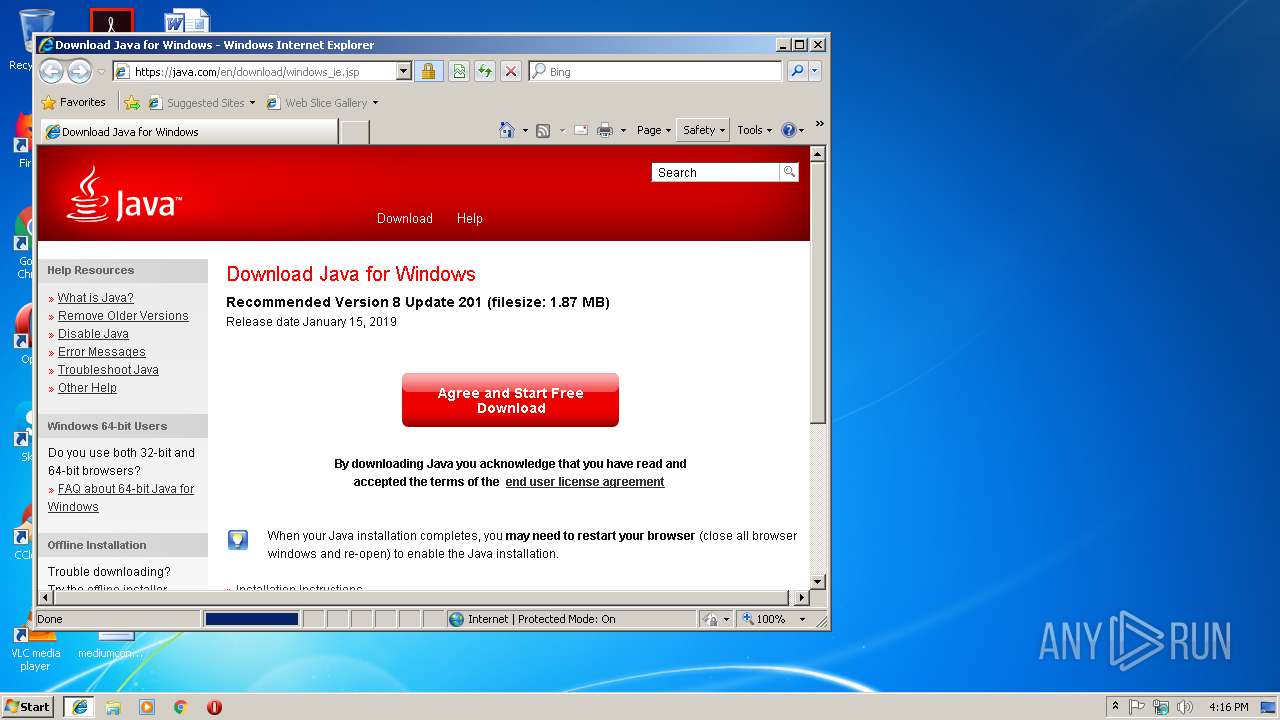
Check for Java to be installed
- javaws.exe (PID: 2972)
- javaws.exe (PID: 3392)
- installer.exe (PID: 1868)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3932)
- iexplore.exe (PID: 2816)
- JavaSetup8u201[1].exe (PID: 3960)
- JavaSetup8u201[1].exe (PID: 3044)
- msiexec.exe (PID: 2996)
- installer.exe (PID: 1868)
Starts application with an unusual extension
- JavaSetup8u201[1].exe (PID: 3044)
Reads internet explorer settings
- JavaSetup8u201[1].exe (PID: 3044)
Creates files in the program directory
- unpack200.exe (PID: 1012)
- bspatch.exe (PID: 2244)
- unpack200.exe (PID: 2568)
- unpack200.exe (PID: 3608)
- unpack200.exe (PID: 2520)
- installer.exe (PID: 1868)
- unpack200.exe (PID: 2692)
- unpack200.exe (PID: 2204)
- unpack200.exe (PID: 2344)
- javaw.exe (PID: 3804)
Creates files in the Windows directory
- installer.exe (PID: 1868)
Modifies the open verb of a shell class
- installer.exe (PID: 1868)
Removes files from Windows directory
- installer.exe (PID: 1868)
Creates COM task schedule object
- installer.exe (PID: 1868)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2272)
- iexplore.exe (PID: 3932)
Reads internet explorer settings
- iexplore.exe (PID: 2728)
- iexplore.exe (PID: 2228)
- iexplore.exe (PID: 180)
- iexplore.exe (PID: 2816)
Reads Internet Cache Settings
- iexplore.exe (PID: 2272)
- iexplore.exe (PID: 2728)
- iexplore.exe (PID: 2228)
- chrome.exe (PID: 2924)
- iexplore.exe (PID: 180)
- iexplore.exe (PID: 2816)
Application launched itself
- iexplore.exe (PID: 2272)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 2924)
- msiexec.exe (PID: 2996)
Creates files in the user directory
- iexplore.exe (PID: 2272)
- iexplore.exe (PID: 2728)
- iexplore.exe (PID: 2816)
- opera.exe (PID: 2444)
Reads settings of System Certificates
- iexplore.exe (PID: 2272)
- chrome.exe (PID: 3124)
Creates files in the program directory
- msiexec.exe (PID: 2996)
Creates a software uninstall entry
- msiexec.exe (PID: 2996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jnlp | | | Java Web Start application descriptor (82.6) |
|---|---|---|
| .xml | | | Generic XML (ASCII) (10.8) |
| .html | | | HyperText Markup Language (6.5) |
EXIF
XMP
| JnlpSpec: | 6.0+ |
|---|---|
| JnlpCodebase: | https://tex.360t.com/getdown/jnlp/tex/ |
| JnlpHref: | bridge-login.jnlp |
| JnlpInformationTitle: | TEX-PROD - 360T Bridge |
| JnlpInformationVendor: | 360 Treasury Systems AG |
| JnlpInformationHomepageHref: | http://www.360t.com/ |
| JnlpInformationDescription: | 360T Bridge Applet |
| JnlpInformationDescriptionKind: | short |
| JnlpInformationIconHref: | https://tex.360t.com/getdown/jnlp/tex/BridgeClient.gif |
| JnlpInformationIconWidth: | 64 |
| JnlpInformationIconHeight: | 64 |
| JnlpInformationShortcutOnline: | |
| JnlpInformationShortcutDesktop: | - |
| JnlpInformationShortcutMenuSubmenu: | 360 Treasury Systems AG |
| JnlpInformationOffline-allowed: | - |
| JnlpInformationUpdateCheck: | background |
| JnlpSecurityAll-permissions: | - |
| JnlpUpdateCheck: | always |
| JnlpUpdatePolicy: | always |
| JnlpApplication-descMain-class: | com.three60t.framework.launcher.Main |
| JnlpApplication-descArgument: | launcher.app.base.url=https://tex.360t.com/getdown/login/tex |
| JnlpResourcesJ2seVersion: | 1.6.0+ |
| JnlpResourcesJ2seInitial-heap-size: | 32m |
| JnlpResourcesJ2seMax-heap-size: | 256m |
| JnlpResourcesJ2seJava-vm-args: | -XX:MaxPermSize=50m -Dawt.useSystemAAFontSettings=gasp -verbose:gc -XX:+PrintGCDetails -XX:+PrintGCTimeStamps -XX:+PrintTenuringDistribution -XX:+HeapDumpOnOutOfMemoryError |
| JnlpResourcesJarHref: | https://tex.360t.com/getdown/jnlp/tex/jars/360t-bootstrap.jar |
| JnlpResourcesJarMain: | |
| JnlpResourcesPropertyName: | javax.net.debug |
| JnlpResourcesPropertyValue: | all |
Total processes
101
Monitored processes
54
Malicious processes
7
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2272 CREDAT:6404 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.92.2" "false" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,5566785746094732016,5317326655242090801,131072 --enable-features=PasswordImport --service-pipe-token=CBA5F2AE19D71616512EAFA6C86C9357 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CBA5F2AE19D71616512EAFA6C86C9357 --renderer-client-id=5 --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,5566785746094732016,5317326655242090801,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=913BA305C4EEBCF7FABD2C16F1E2C063 --mojo-platform-channel-handle=512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Java\jre1.8.0_201\bin\unpack200.exe" -r "C:\Program Files\Java\jre1.8.0_201\lib/plugin.pack" "C:\Program Files\Java\jre1.8.0_201\lib/plugin.jar" | C:\Program Files\Java\jre1.8.0_201\bin\unpack200.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2010.9 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=840,6081398825071921870,14800771413271138263,131072 --enable-features=PasswordImport --service-pipe-token=832E3D61F64CE9C7DD7F16973EF5CAE8 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=832E3D61F64CE9C7DD7F16973EF5CAE8 --renderer-client-id=5 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=840,6081398825071921870,14800771413271138263,131072 --enable-features=PasswordImport --service-pipe-token=47AD579D8CBA01AE79291DA030F3C01C --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=47AD579D8CBA01AE79291DA030F3C01C --renderer-client-id=6 --mojo-platform-channel-handle=2100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Java\jre1.8.0_201\installer.exe" /s INSTALLDIR="C:\Program Files\Java\jre1.8.0_201\\" INSTALL_SILENT=1 REPAIRMODE=0 ProductCode={26A24AE4-039D-4CA4-87B4-2F32180201F0} | C:\Program Files\Java\jre1.8.0_201\installer.exe | msiexec.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.2010.9 Modules
| |||||||||||||||
| 1908 | C:\Windows\system32\MsiExec.exe -Embedding 432724631B17C04934F04724C7F1DC81 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Java\jre1.8.0_201\bin\unpack200.exe" -r "C:\Program Files\Java\jre1.8.0_201\lib/charsets.pack" "C:\Program Files\Java\jre1.8.0_201\lib/charsets.jar" | C:\Program Files\Java\jre1.8.0_201\bin\unpack200.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2010.9 Modules
| |||||||||||||||
Total events
17 166
Read events
3 730
Write events
10 820
Delete events
2 616
Modification events
| (PID) Process: | (3220) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3220) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1535457890299 | |||
| (PID) Process: | (3220) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.roaming.profile |
Value: false | |||
| (PID) Process: | (3220) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.version |
Value: 8 | |||
| (PID) Process: | (3220) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expired.version |
Value: 11.92.2 | |||
| (PID) Process: | (3220) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.browser.path |
Value: C:\Program Files\Internet Explorer\iexplore.exe | |||
| (PID) Process: | (3220) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.11.92.2 |
Value: update | |||
| (PID) Process: | (3592) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3592) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1548692160031 | |||
| (PID) Process: | (3592) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.roaming.profile |
Value: false | |||
Executable files
159
Suspicious files
138
Text files
579
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2272 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\windows_ie[1].jsp | — | |
MD5:— | SHA256:— | |||
| 3220 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3220 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:— | SHA256:— | |||
| 3592 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:— | SHA256:— | |||
| 3220 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaDeployReg.log | text | |
MD5:— | SHA256:— | |||
| 3816 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaDeployReg.log | text | |
MD5:— | SHA256:— | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\ie[1].css | text | |
MD5:— | SHA256:— | |||
| 3816 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
70
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
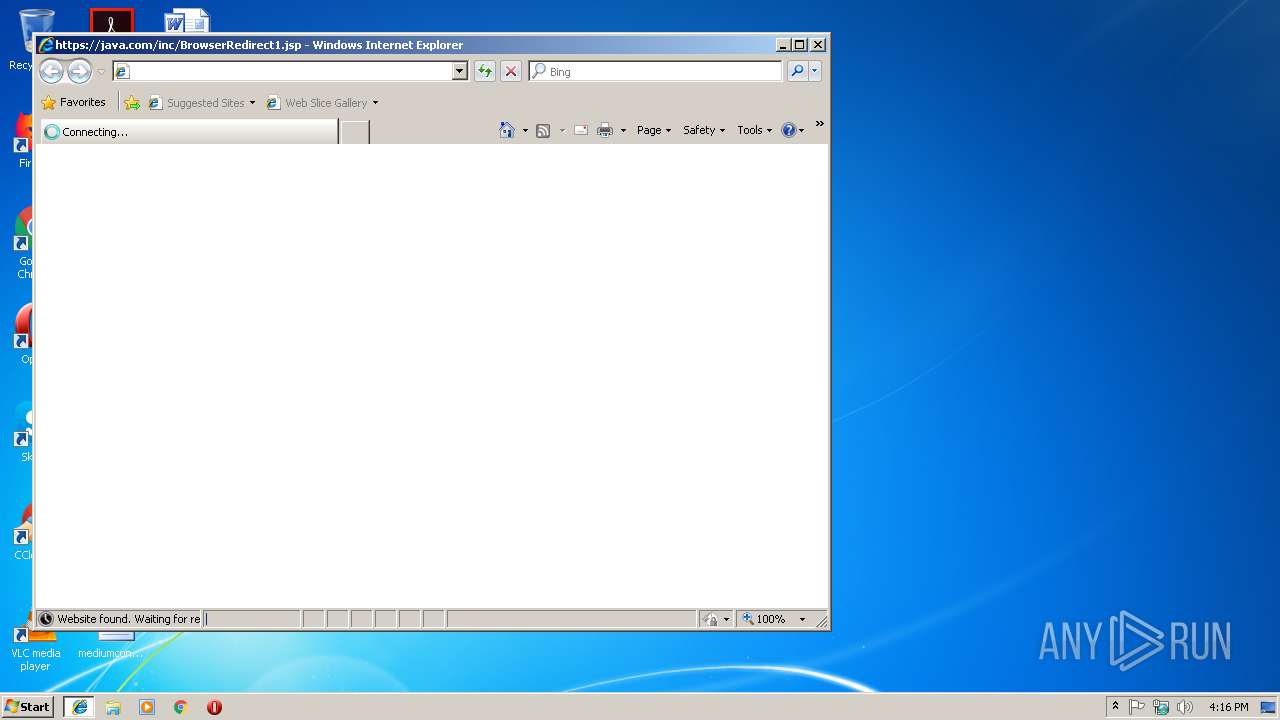
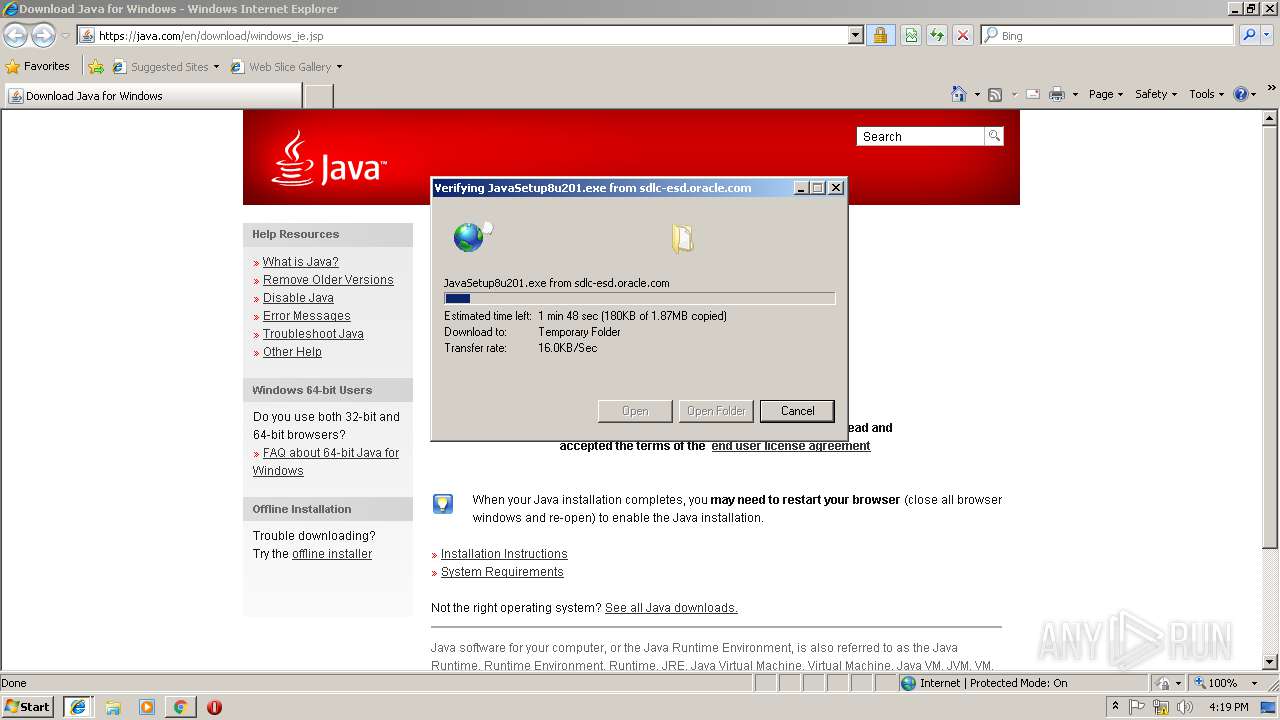
2728 | iexplore.exe | GET | 301 | 104.111.217.243:80 | http://java.com/inst-dl-redirect | NL | — | — | whitelisted |
2728 | iexplore.exe | GET | 301 | 104.111.217.243:80 | http://java.com/inst-dl-redirect/ | NL | — | — | whitelisted |
2816 | iexplore.exe | GET | 301 | 104.111.217.243:80 | http://java.com/inst-dl-redirect | NL | — | — | whitelisted |
2816 | iexplore.exe | GET | 301 | 104.111.217.243:80 | http://java.com/inst-dl-redirect/ | NL | — | — | whitelisted |
2444 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
2272 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3932 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2444 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3124 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2272 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2728 | iexplore.exe | 104.111.217.243:443 | java.com | Akamai International B.V. | NL | whitelisted |
2728 | iexplore.exe | 104.111.217.243:80 | java.com | Akamai International B.V. | NL | whitelisted |
2728 | iexplore.exe | 2.16.186.48:443 | dyn-beacon.akamaized.net | Akamai International B.V. | — | whitelisted |
2728 | iexplore.exe | 52.209.190.67:443 | consent.trustarc.com | Amazon.com, Inc. | IE | unknown |
2728 | iexplore.exe | 172.82.228.20:443 | oracle.112.2o7.net | Adobe Systems Inc. | US | whitelisted |
2272 | iexplore.exe | 104.111.217.243:443 | java.com | Akamai International B.V. | NL | whitelisted |
180 | iexplore.exe | 193.29.38.131:443 | tex.360t.com | 360 Treasury Systems AG | DE | unknown |
3124 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
java.com |
| whitelisted |
consent.trustarc.com |
| shared |
dyn-beacon.akamaized.net |
| whitelisted |
oracle.112.2o7.net |
| whitelisted |
tex.360t.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |