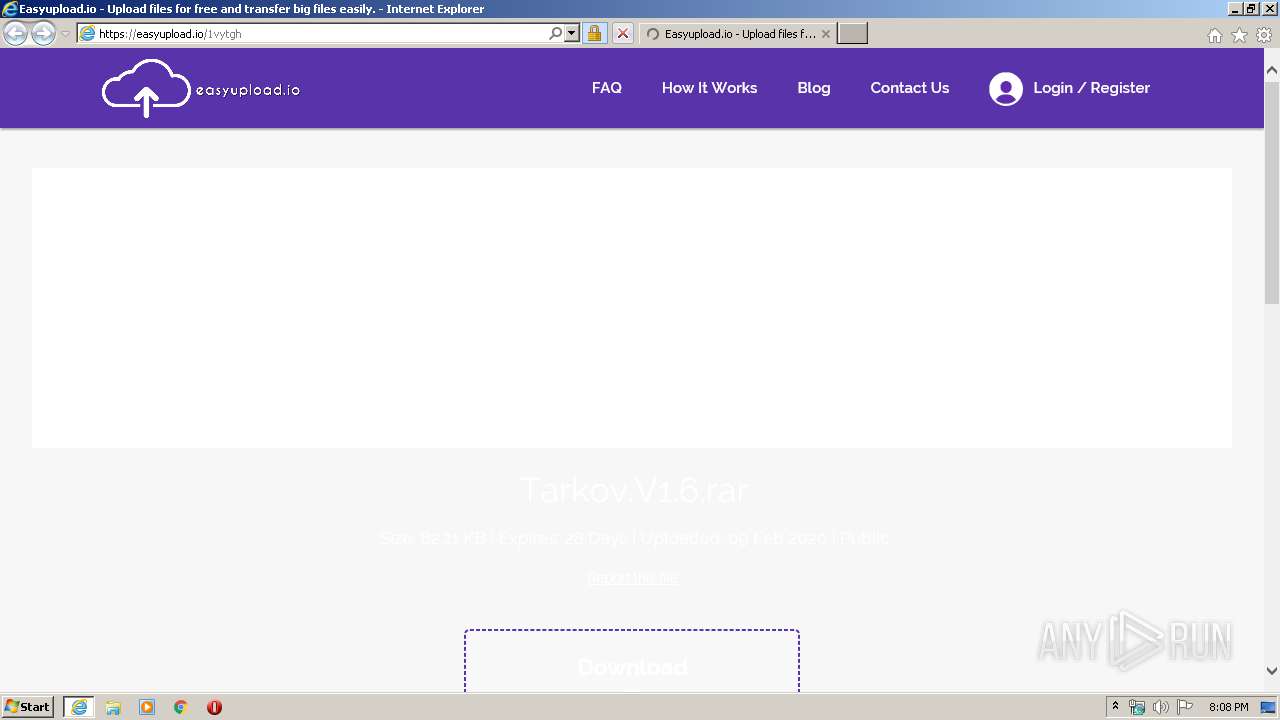
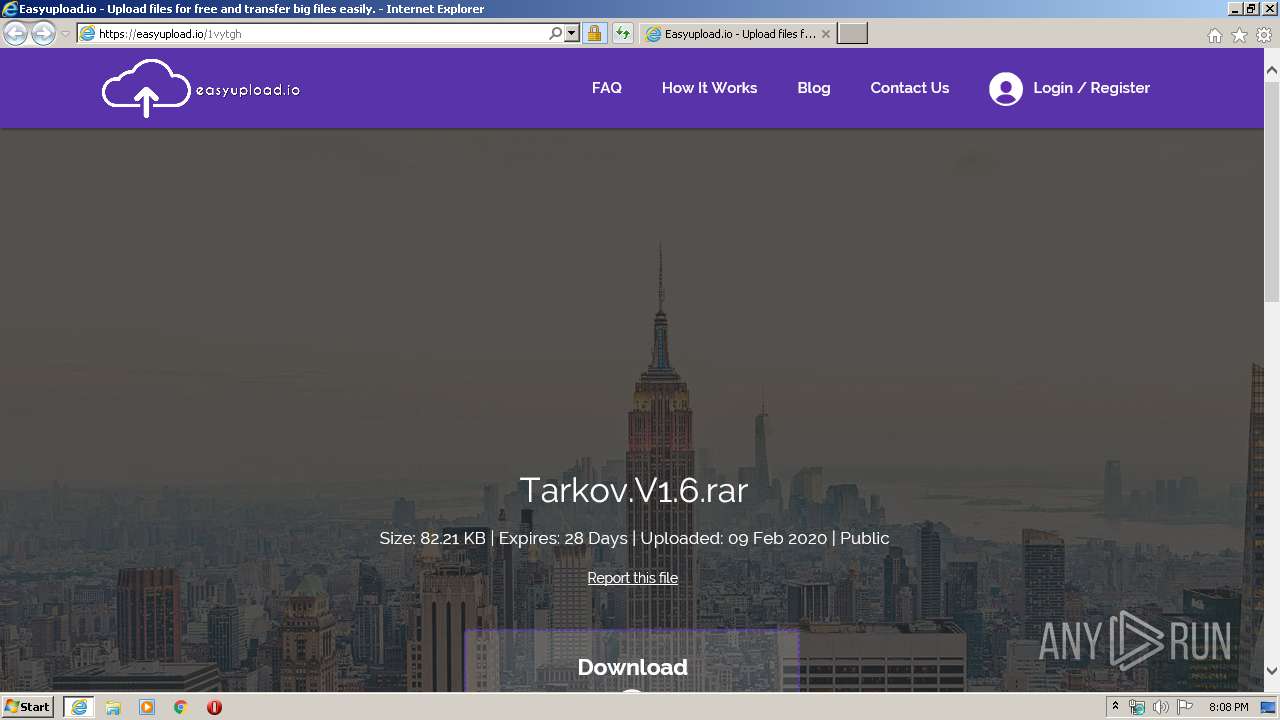
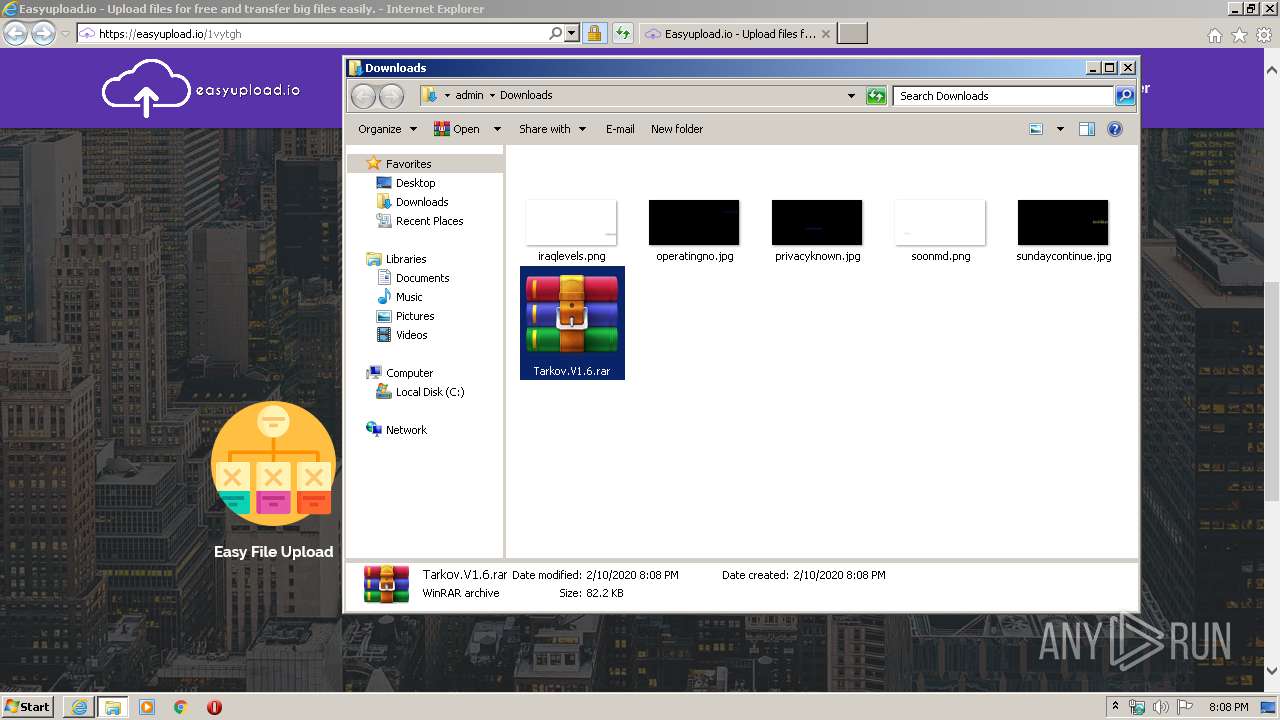
| URL: | https://easyupload.io/1vytgh |
| Full analysis: | https://app.any.run/tasks/6210830b-18d8-48a2-ae6c-8676973651d8 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2020, 20:07:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BA0C546511E7875AFBAD8854779E5E35 |
| SHA1: | DB4CBB624C10A0698A2EA6354D910FF351A74260 |
| SHA256: | EB50489416C128AD6F6C5BA1331482201855D30269EAFE2448B0A4AFB5D56DAB |
| SSDEEP: | 3:N8icQjwxCN:2iBwxO |
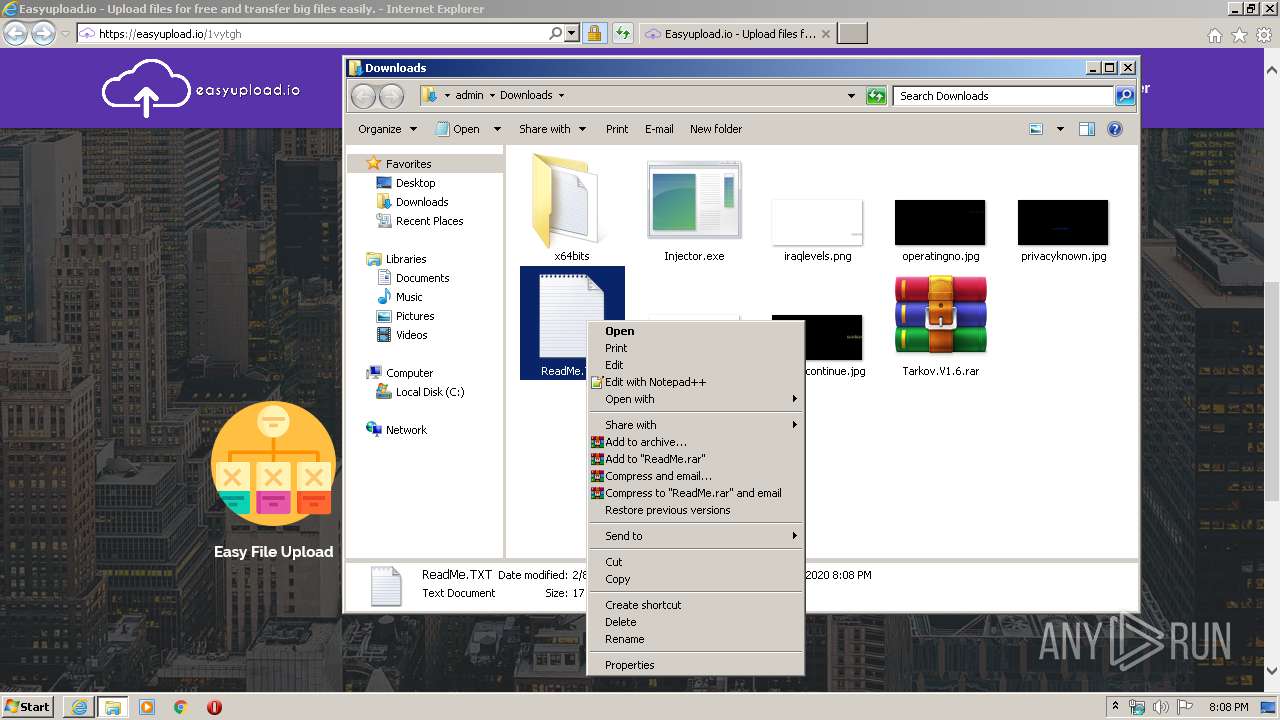
MALICIOUS
Application was dropped or rewritten from another process
- Injector.exe (PID: 3884)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3984)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 3896)
Reads internet explorer settings
- iexplore.exe (PID: 3896)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2636)
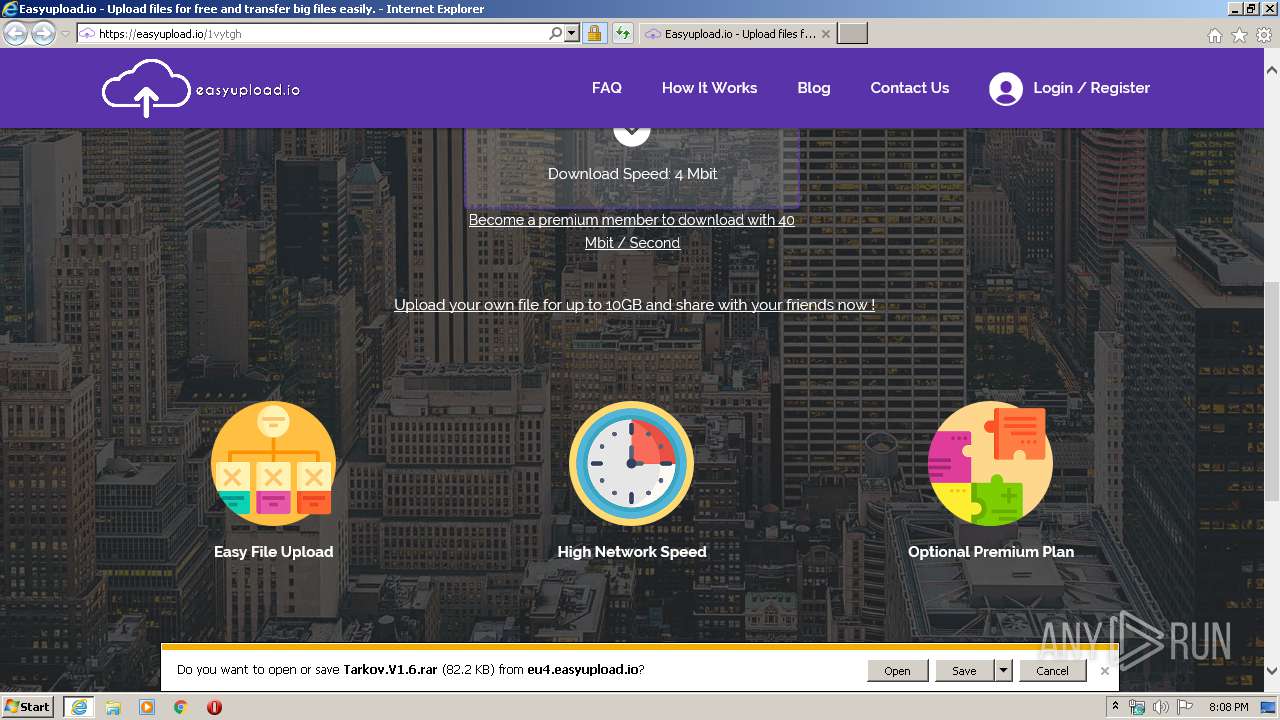
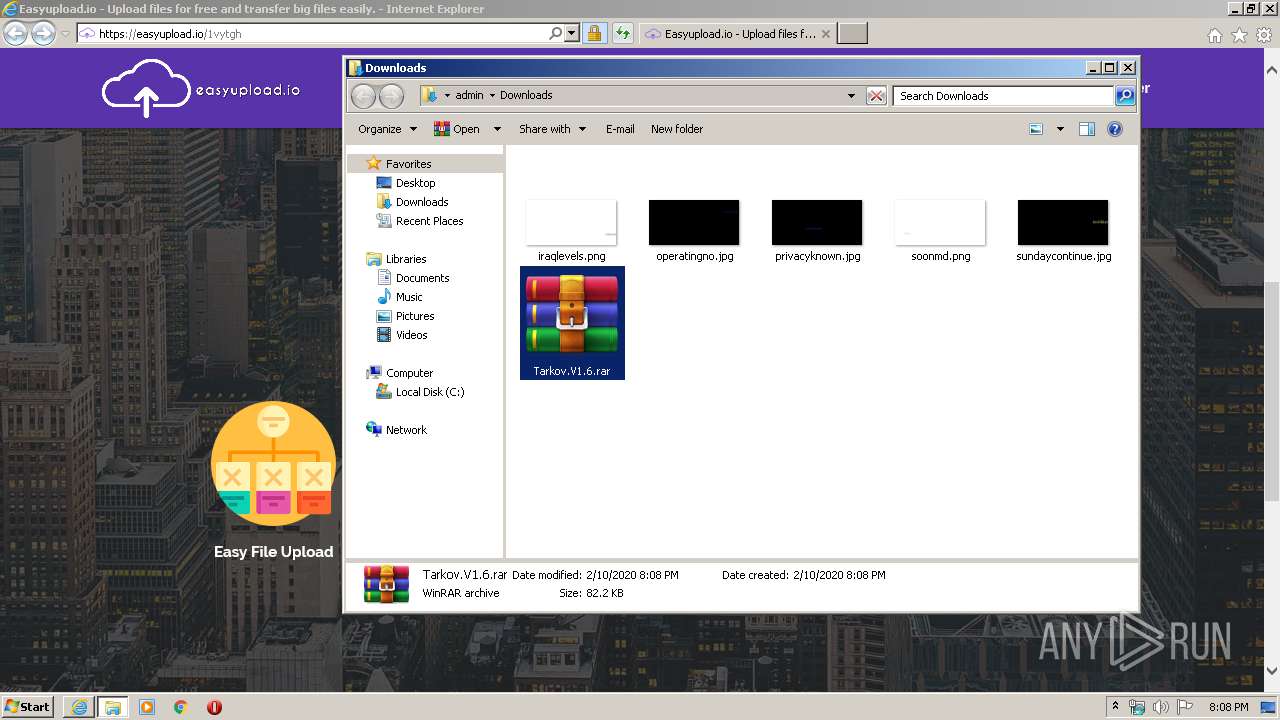
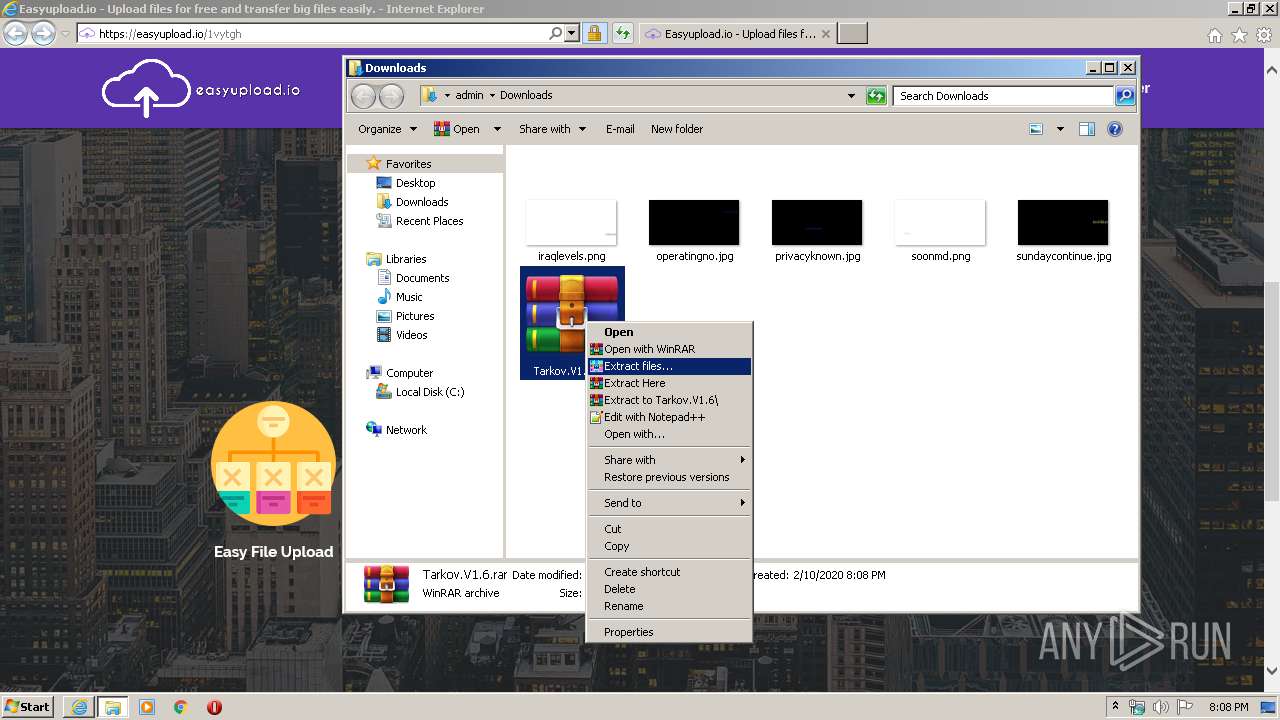
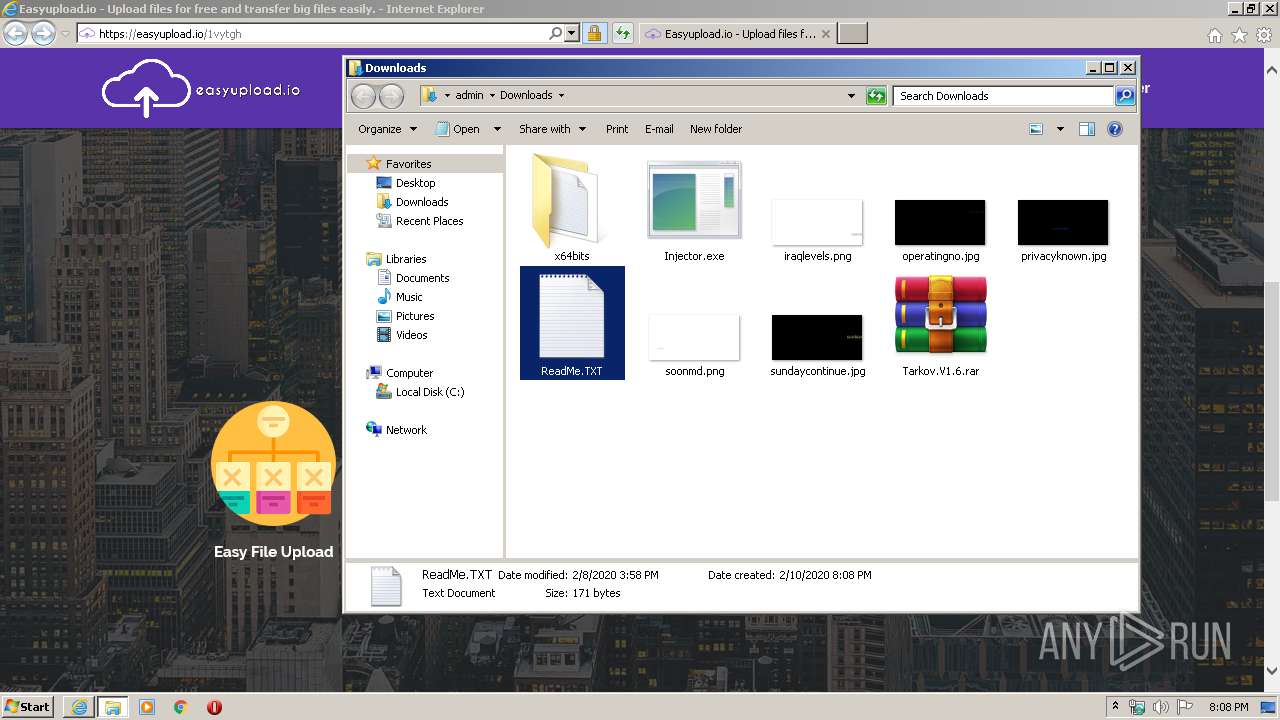
Manual execution by user
- WinRAR.exe (PID: 3984)
- Injector.exe (PID: 3884)
Creates files in the user directory
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 3896)
Reads settings of System Certificates
- iexplore.exe (PID: 2636)
Application launched itself
- iexplore.exe (PID: 2636)
Changes internet zones settings
- iexplore.exe (PID: 2636)
Changes settings of System certificates
- iexplore.exe (PID: 2636)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2636 | "C:\Program Files\Internet Explorer\iexplore.exe" https://easyupload.io/1vytgh | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3884 | "C:\Users\admin\Downloads\Injector.exe" | C:\Users\admin\Downloads\Injector.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApplication1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3896 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2636 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
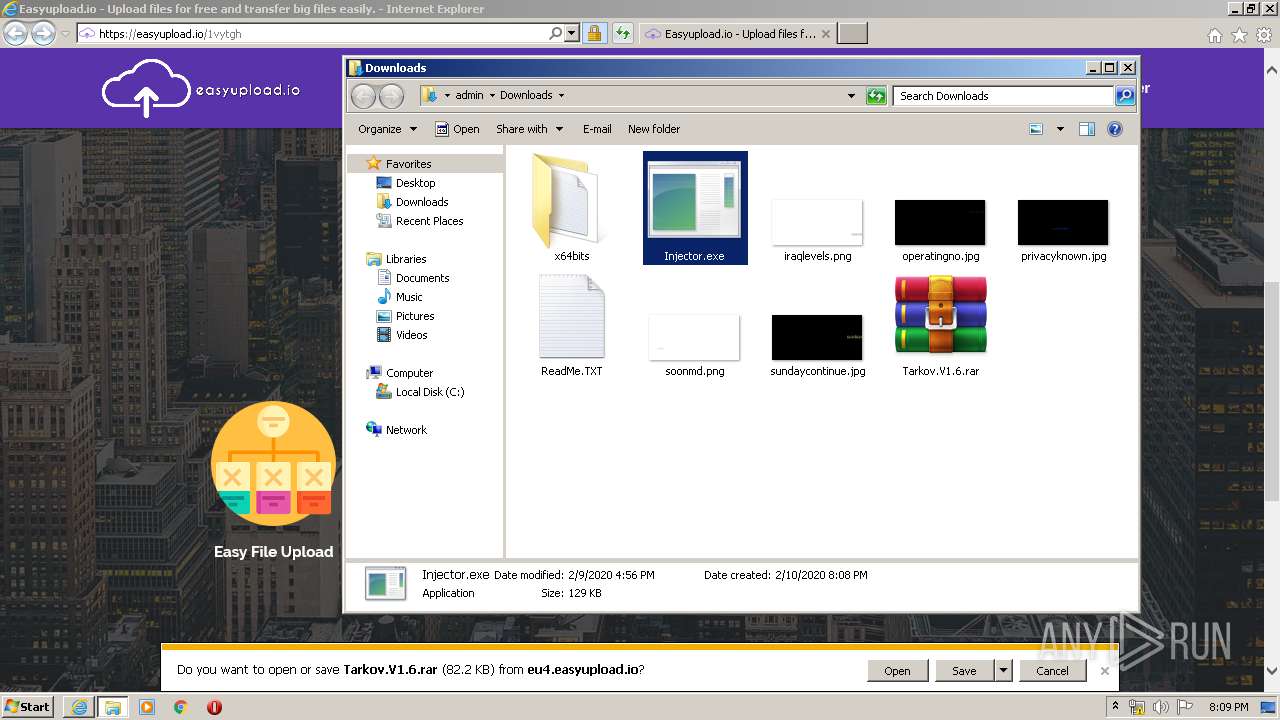
| 3984 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Tarkov.V1.6.rar" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
5 085
Read events
652
Write events
3 002
Delete events
1 431
Modification events
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3785903720 | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30793805 | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
1
Suspicious files
63
Text files
73
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7901.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7902.tmp | — | |
MD5:— | SHA256:— | |||
| 2636 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\materialize[1].css | text | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PGXAICWX.txt | text | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\1vytgh[1].htm | html | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
71
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD6Ee7RUf7bMAgAAAAAKrKe | US | der | 472 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFa0PH9RdFNVCAAAAAAqsjw%3D | US | der | 471 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDlxRGD2vLumggAAAAAKrI7 | US | der | 472 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDFzOFjNxZ%2BMAIAAAAAVmCu | US | der | 472 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
3896 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDFzOFjNxZ%2BMAIAAAAAVmCu | US | der | 472 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDlxRGD2vLumggAAAAAKrI7 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3896 | iexplore.exe | 104.18.42.98:443 | easyupload.io | Cloudflare Inc | US | unknown |
3896 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2636 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3896 | iexplore.exe | 172.217.16.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3896 | iexplore.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3896 | iexplore.exe | 172.217.22.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3896 | iexplore.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
3896 | iexplore.exe | 143.204.98.102:443 | d1f8f9xcsvx3ha.cloudfront.net | — | US | suspicious |
3896 | iexplore.exe | 172.217.16.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3896 | iexplore.exe | 216.58.205.226:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
easyupload.io |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
d1f8f9xcsvx3ha.cloudfront.net |
| whitelisted |
s.symcd.com |
| shared |
ocsp.pki.goog |
| whitelisted |