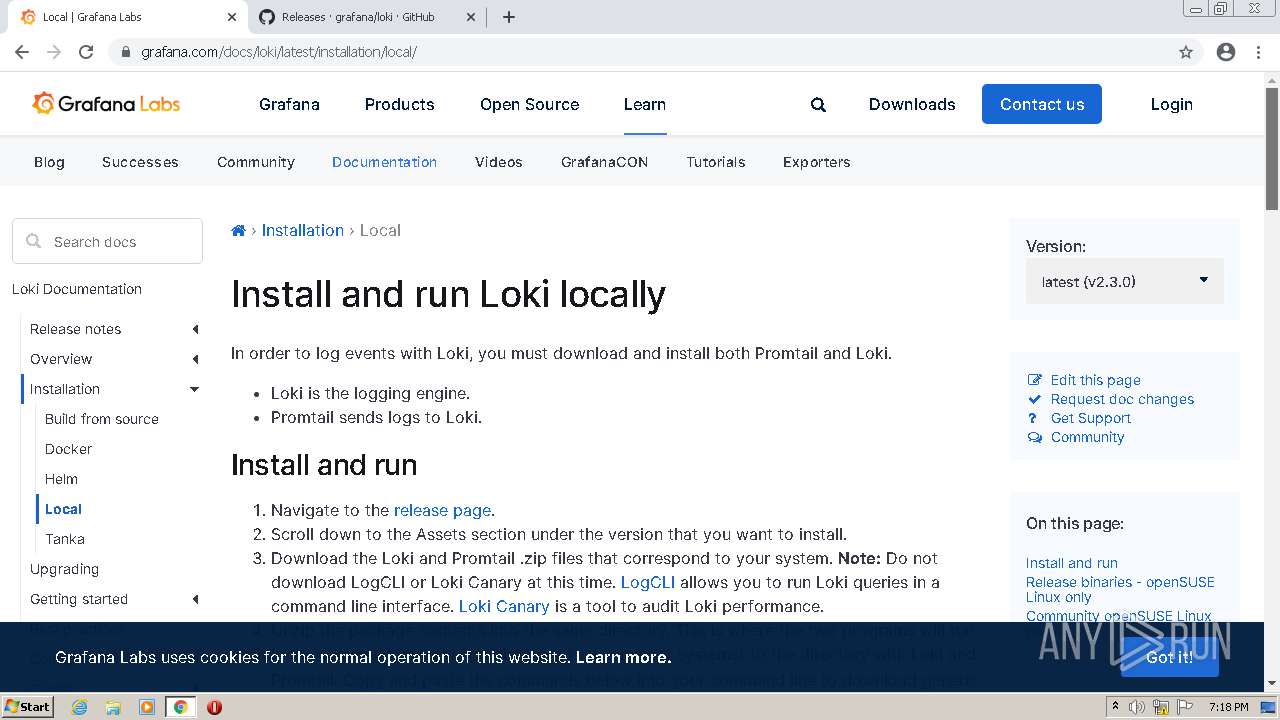
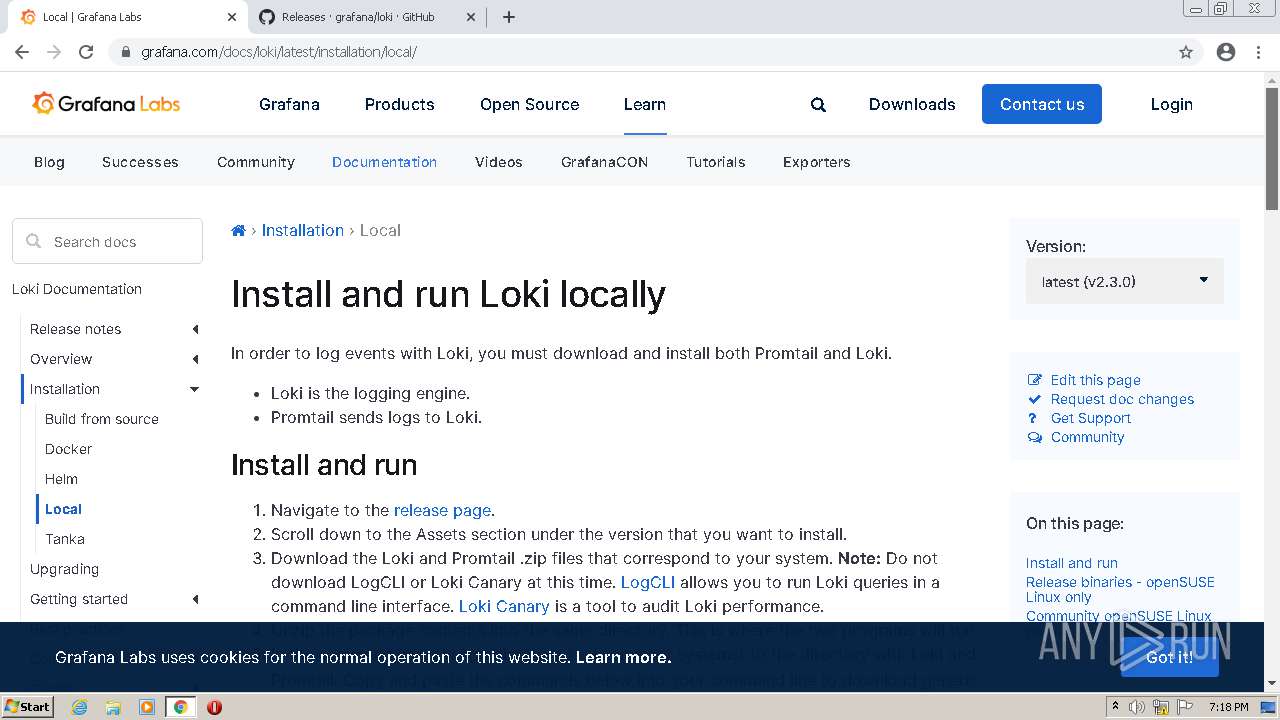
| File name: | loki.exe |
| Full analysis: | https://app.any.run/tasks/7b68158f-db59-4ec7-b6e3-f024cb795de4 |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2021, 18:16:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 6C5A13834828CC8D4ED6909BA7D1B6F7 |
| SHA1: | 8CAC440C9114FB5B3E035BC905BA0BD5520A187A |
| SHA256: | EB4015587A19A296D314359AF969F33DAE53518BD715EA196EDF1BC5B0C3E3AB |
| SSDEEP: | 196608:SwIgoP1HFnNRuZIP0ssimvlGyn8xCFXf0XCtnRYXWZ9P3p:S7P11yZ7jimt3e00B6 |
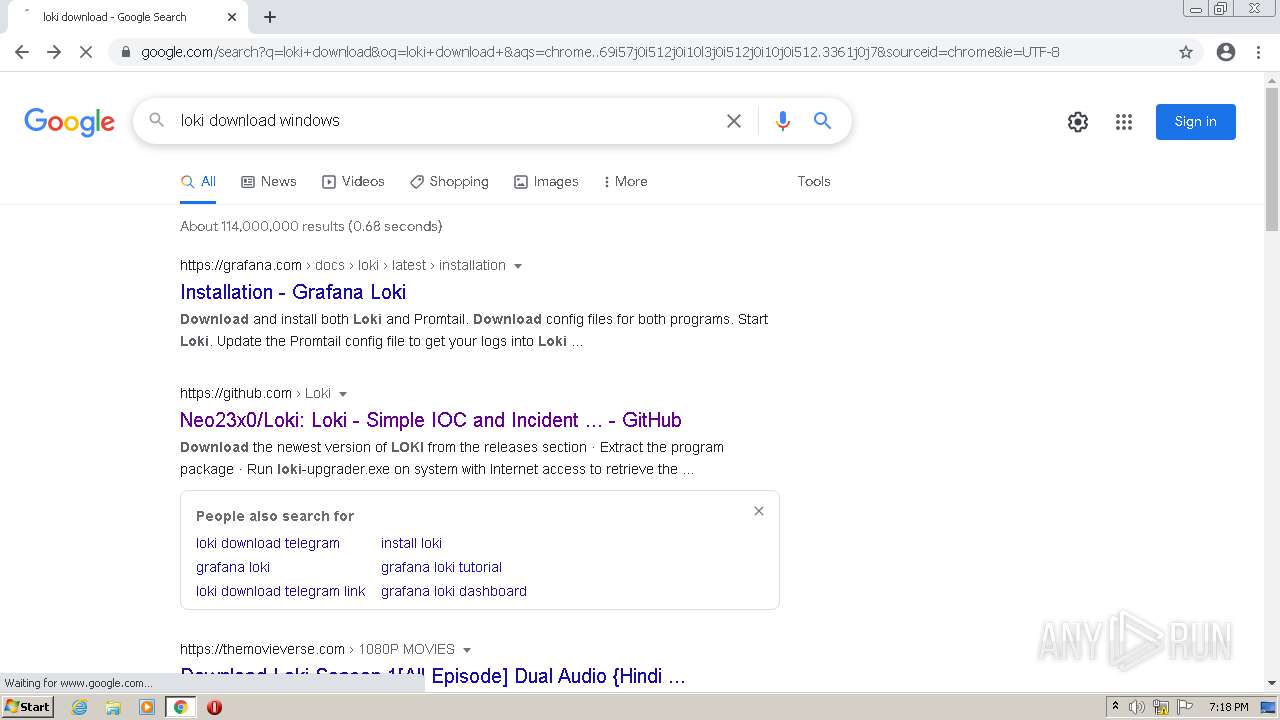
MALICIOUS
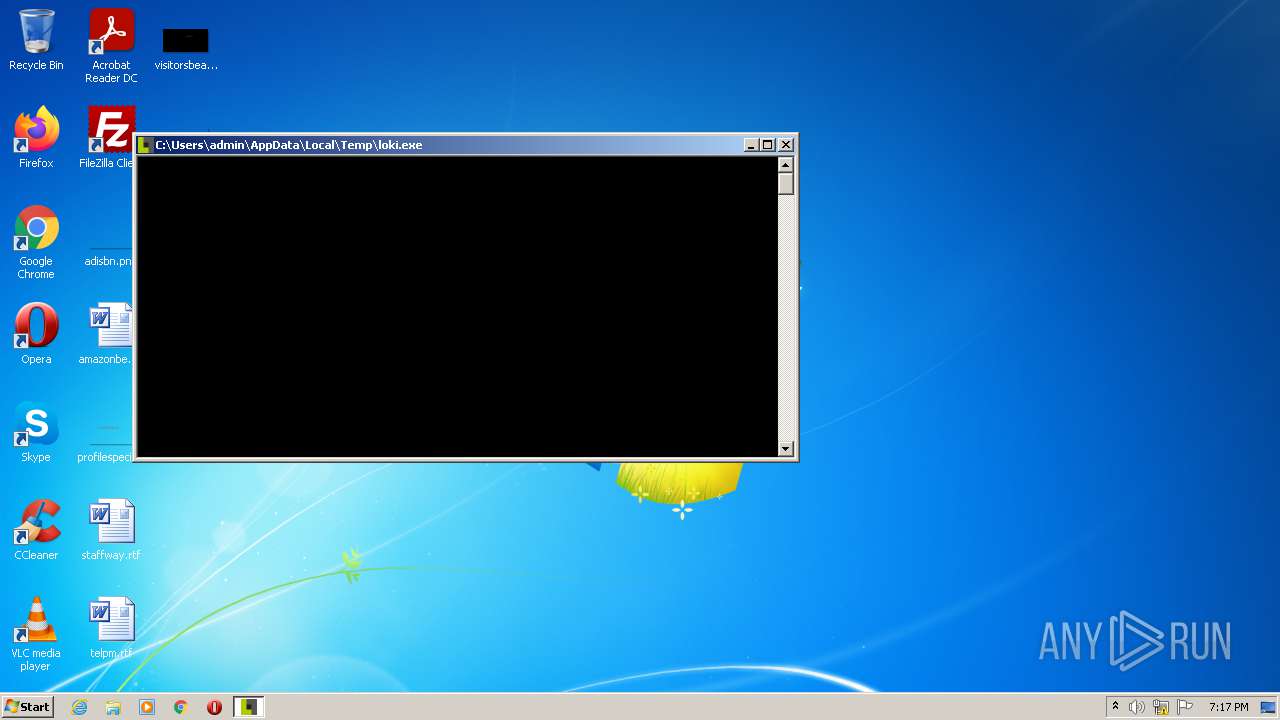
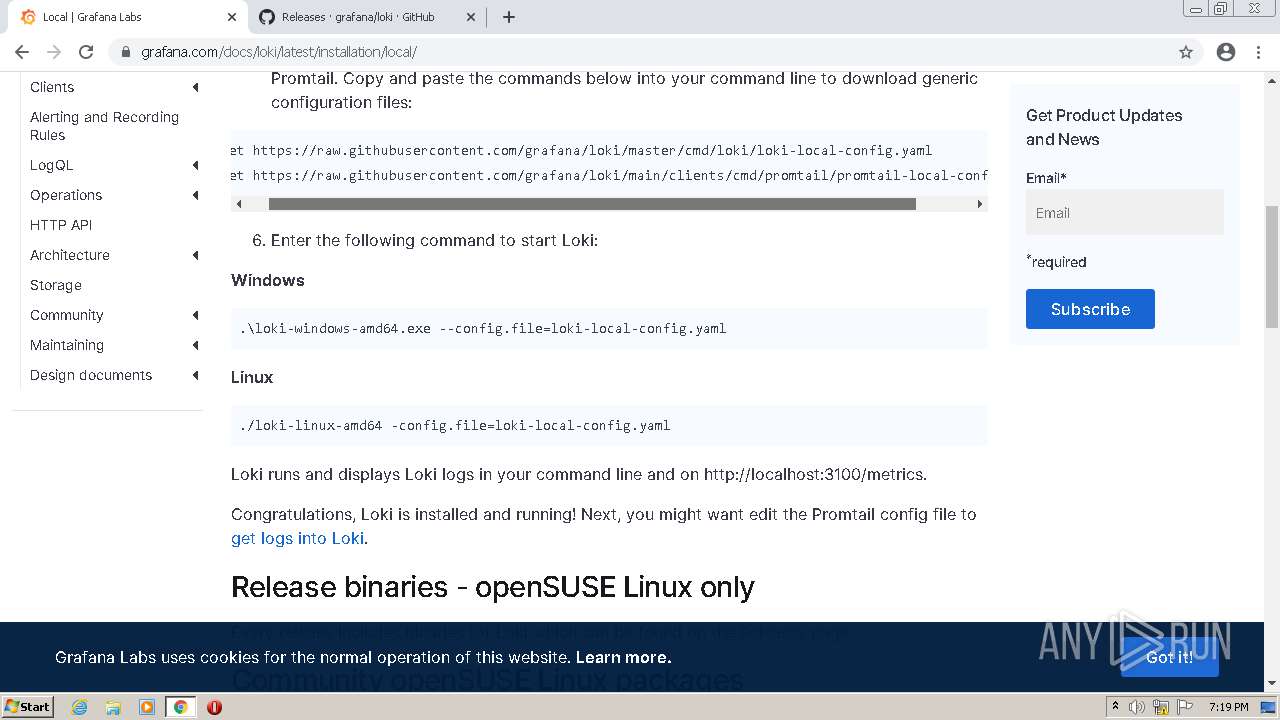
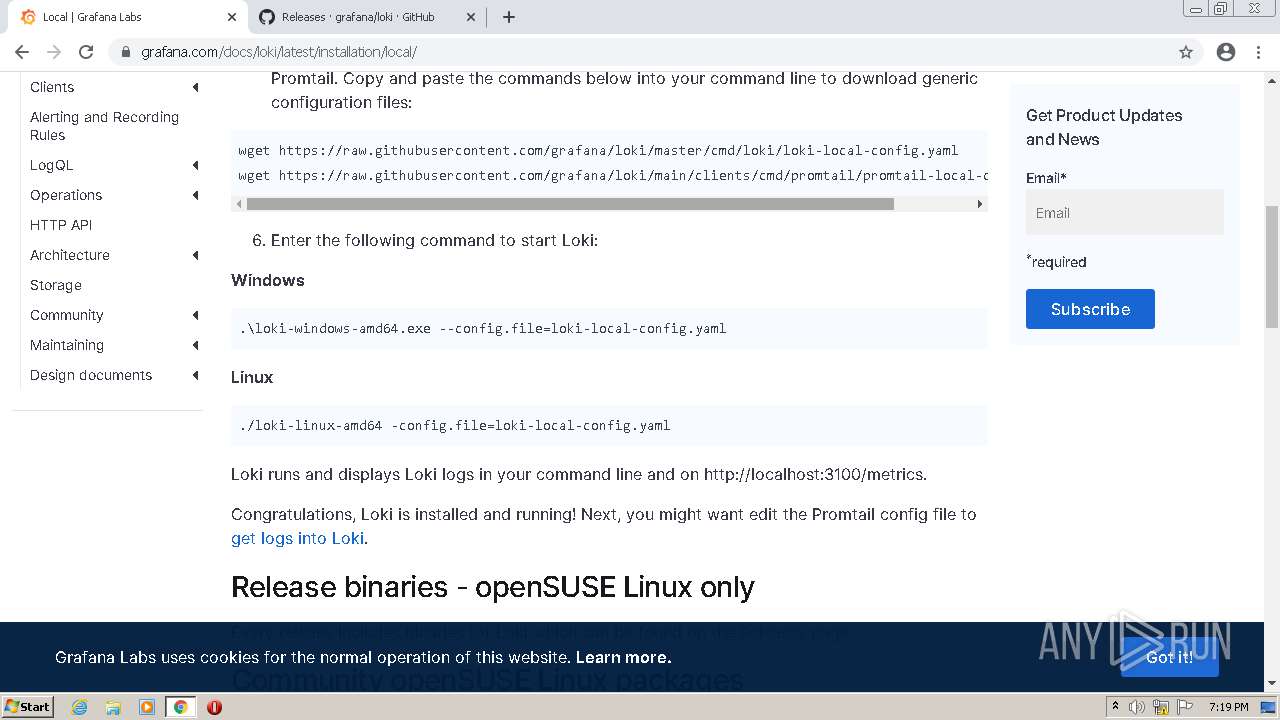
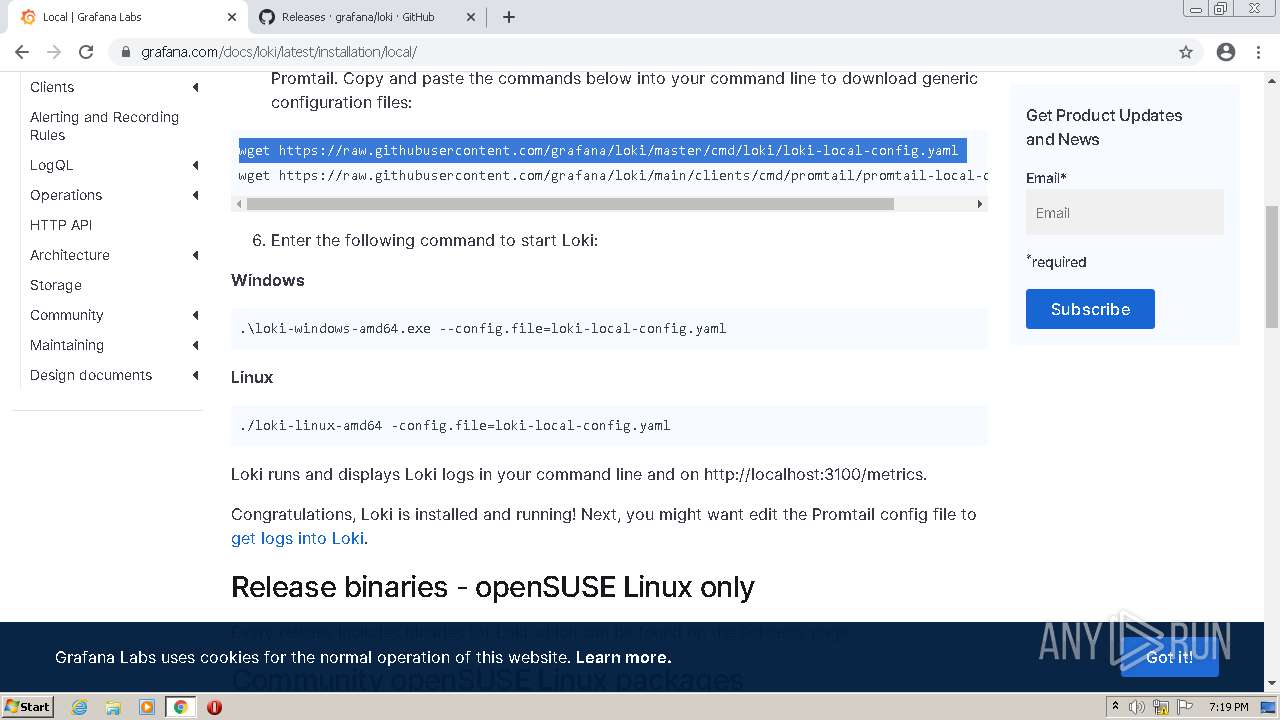
Drops executable file immediately after starts
- loki.exe (PID: 1708)
- chrome.exe (PID: 2356)
Loads dropped or rewritten executable
- loki.exe (PID: 2176)
SUSPICIOUS
Executable content was dropped or overwritten
- loki.exe (PID: 1708)
- chrome.exe (PID: 2356)
Checks supported languages
- loki.exe (PID: 1708)
- loki.exe (PID: 2176)
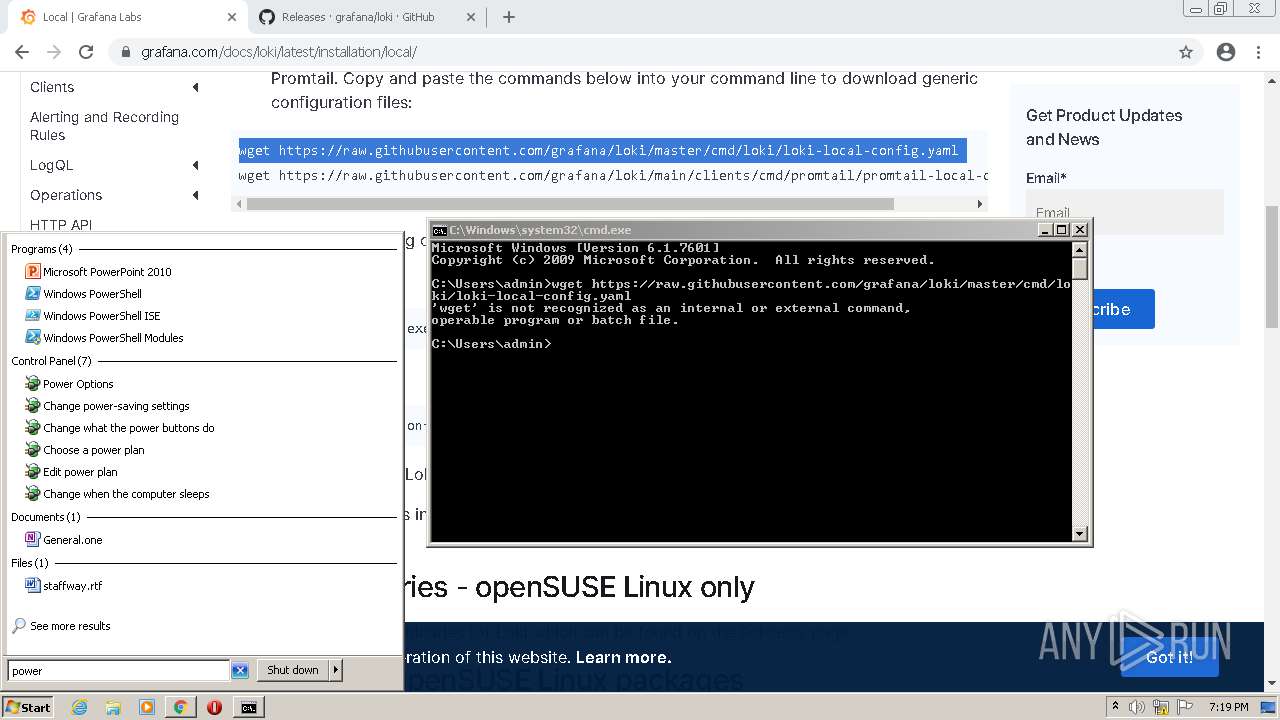
- cmd.exe (PID: 3700)
- powershell.exe (PID: 3520)
Reads the computer name
- loki.exe (PID: 1708)
- loki.exe (PID: 2176)
- powershell.exe (PID: 3520)
Application launched itself
- loki.exe (PID: 1708)
Drops a file that was compiled in debug mode
- loki.exe (PID: 1708)
- chrome.exe (PID: 2356)
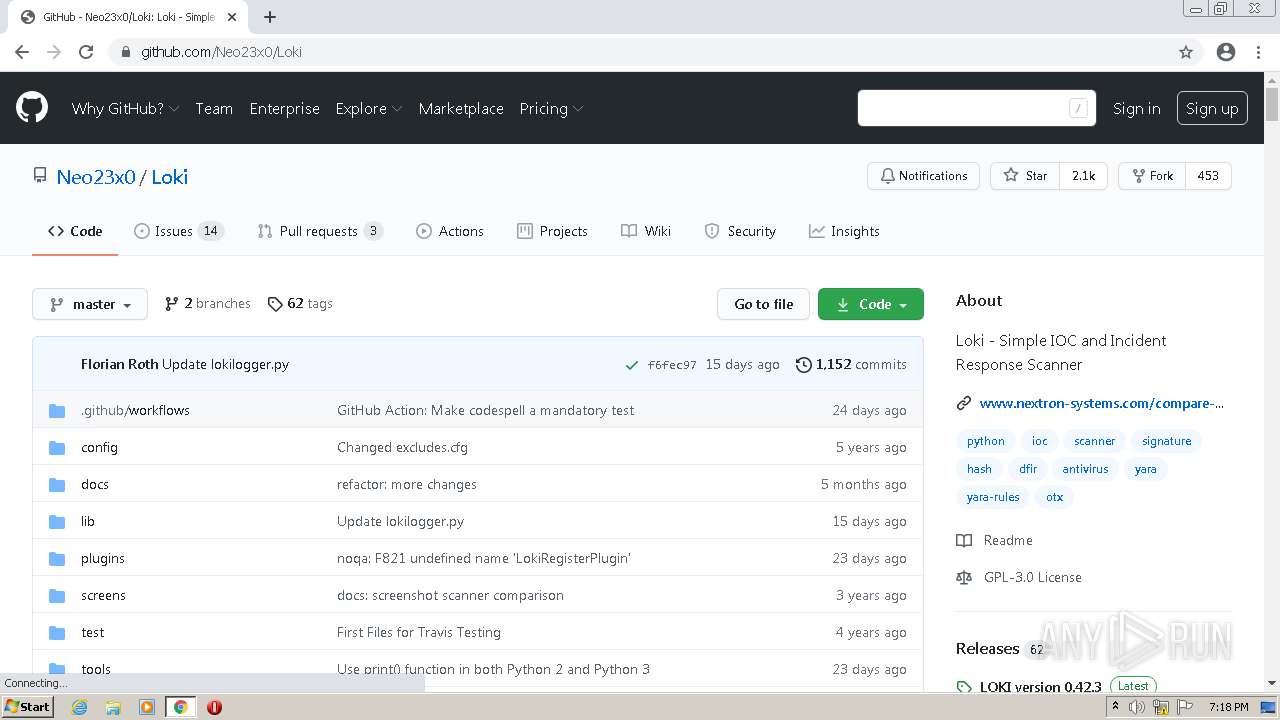
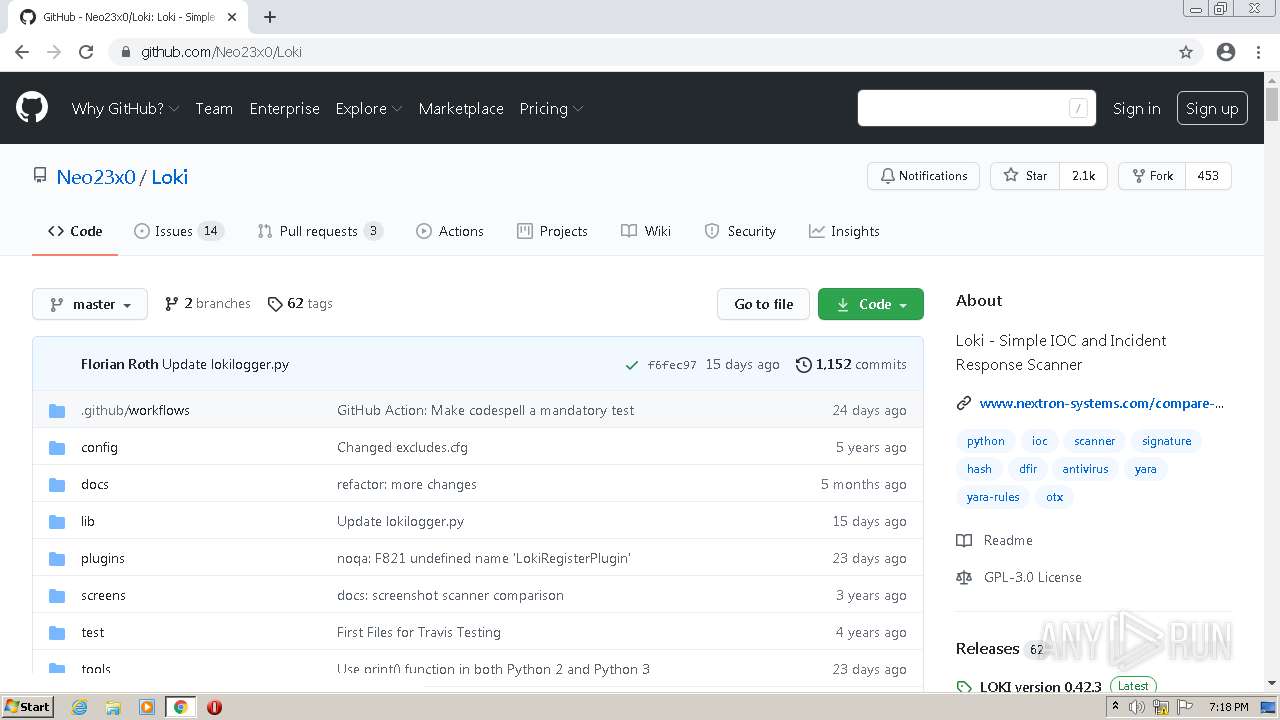
Loads Python modules
- loki.exe (PID: 2176)
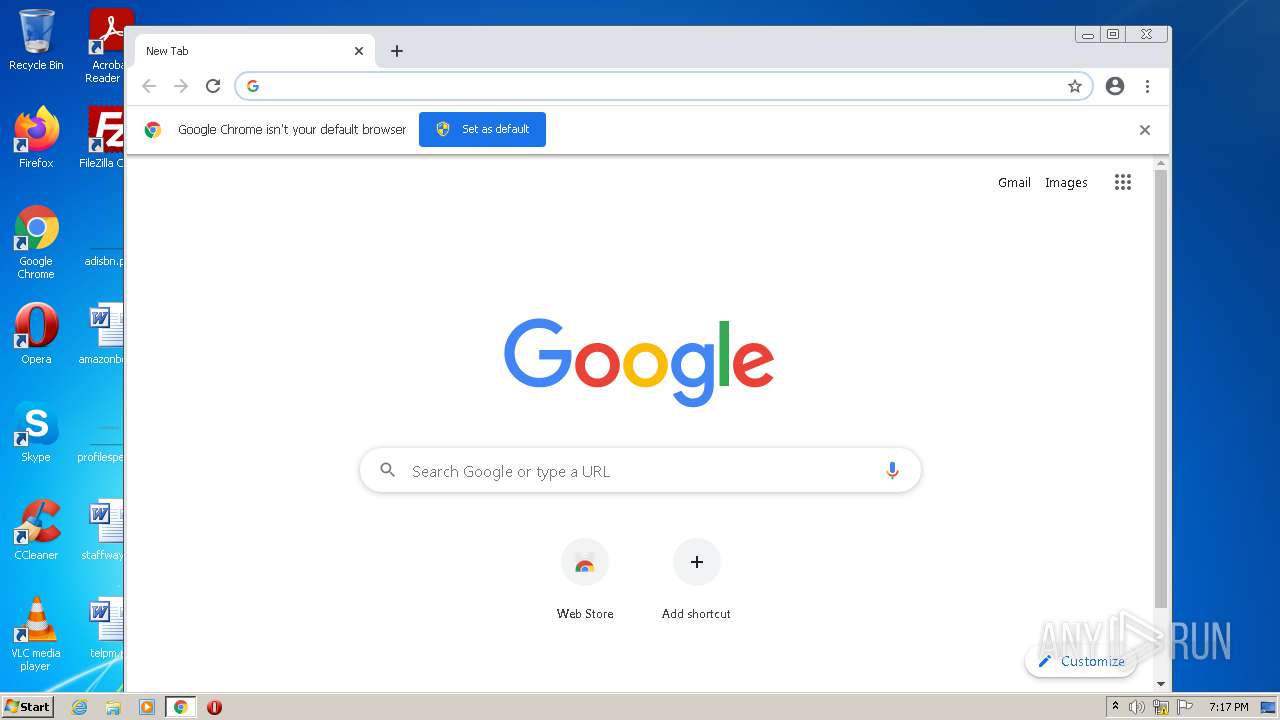
Modifies files in Chrome extension folder
- chrome.exe (PID: 188)
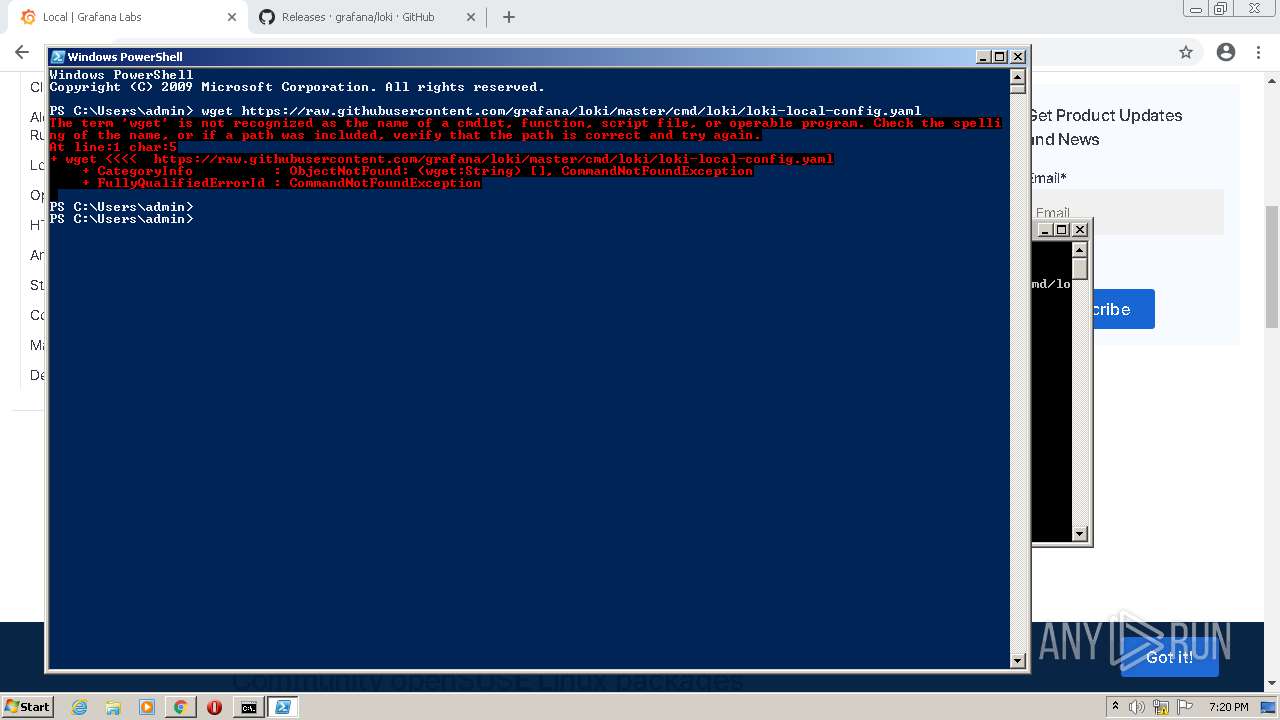
Creates files in the user directory
- powershell.exe (PID: 3520)
Reads the date of Windows installation
- powershell.exe (PID: 3520)
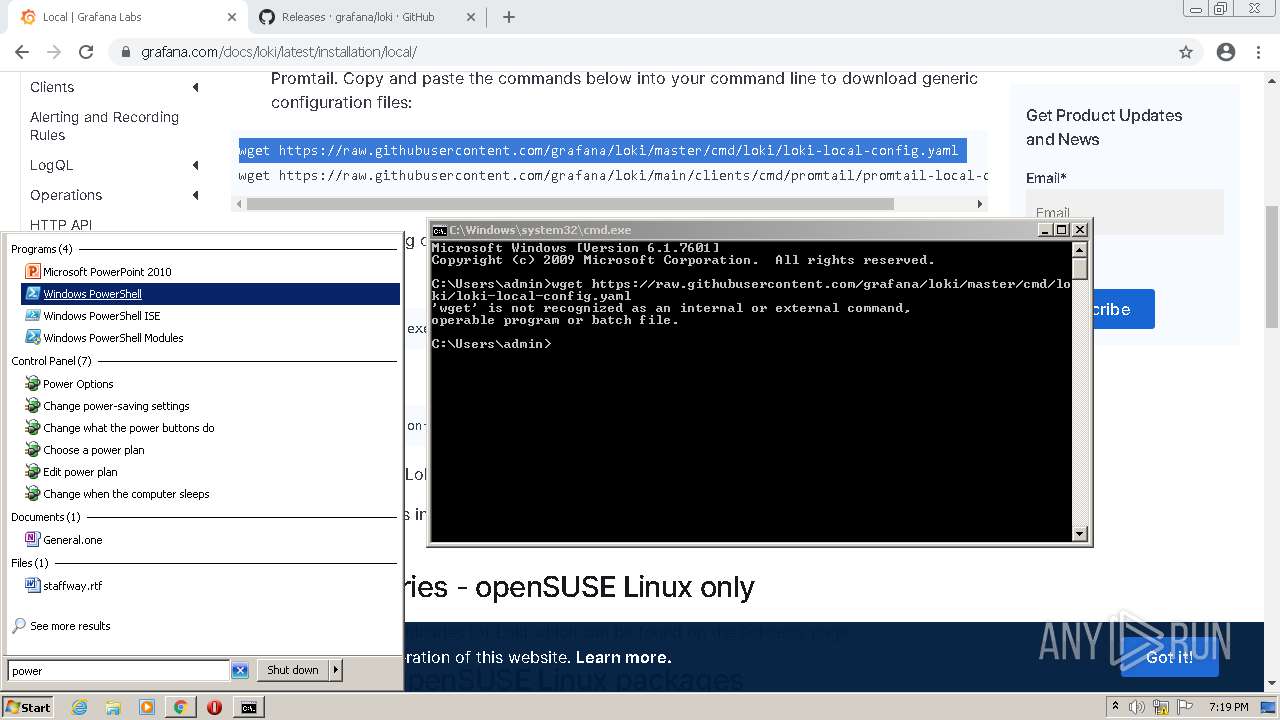
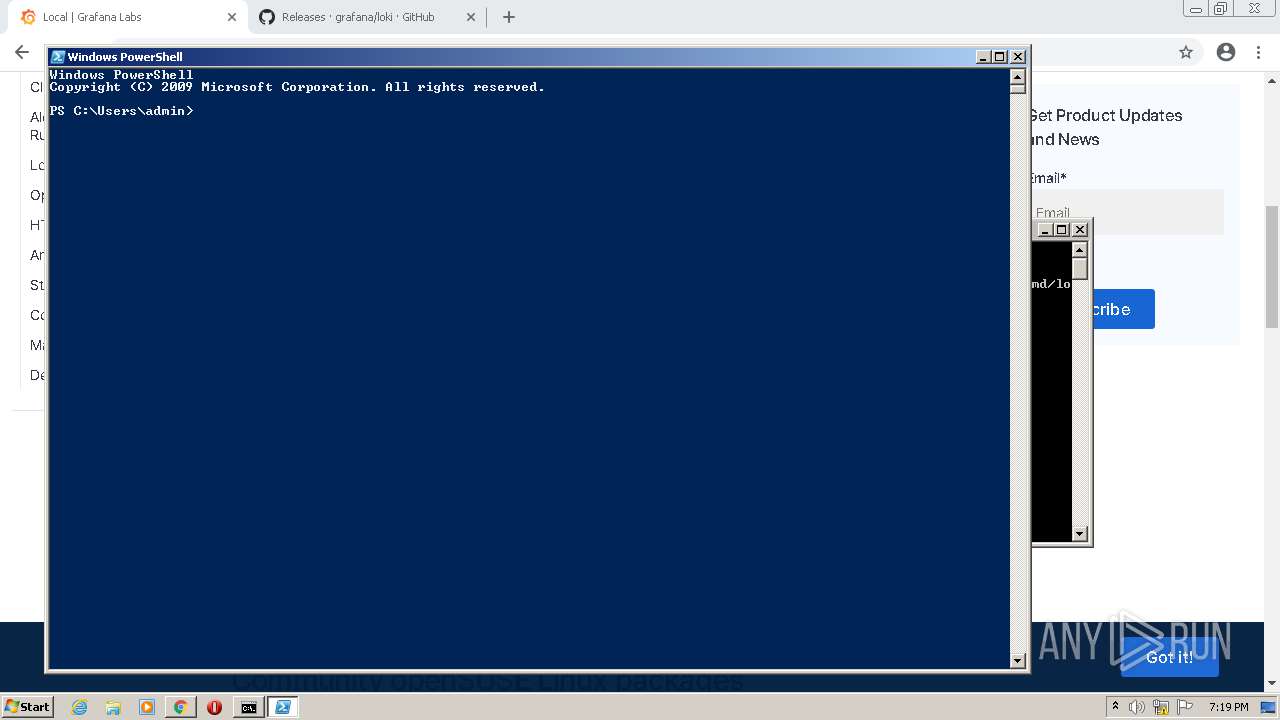
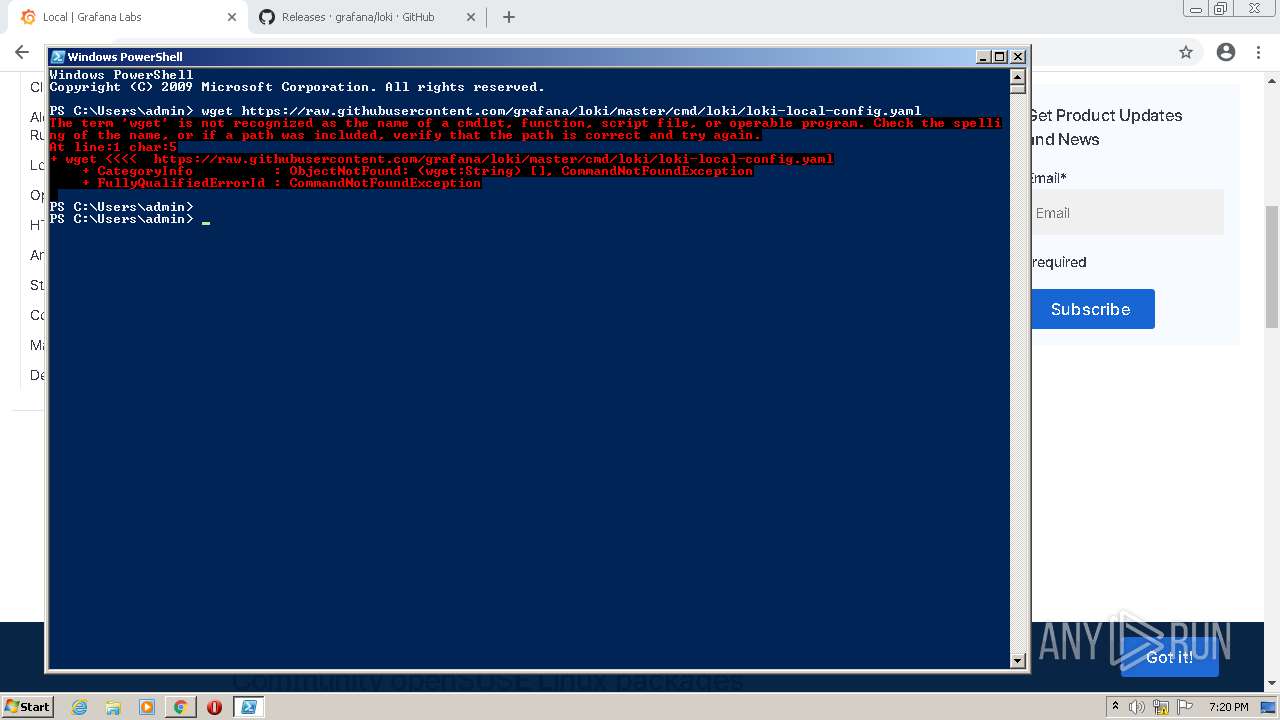
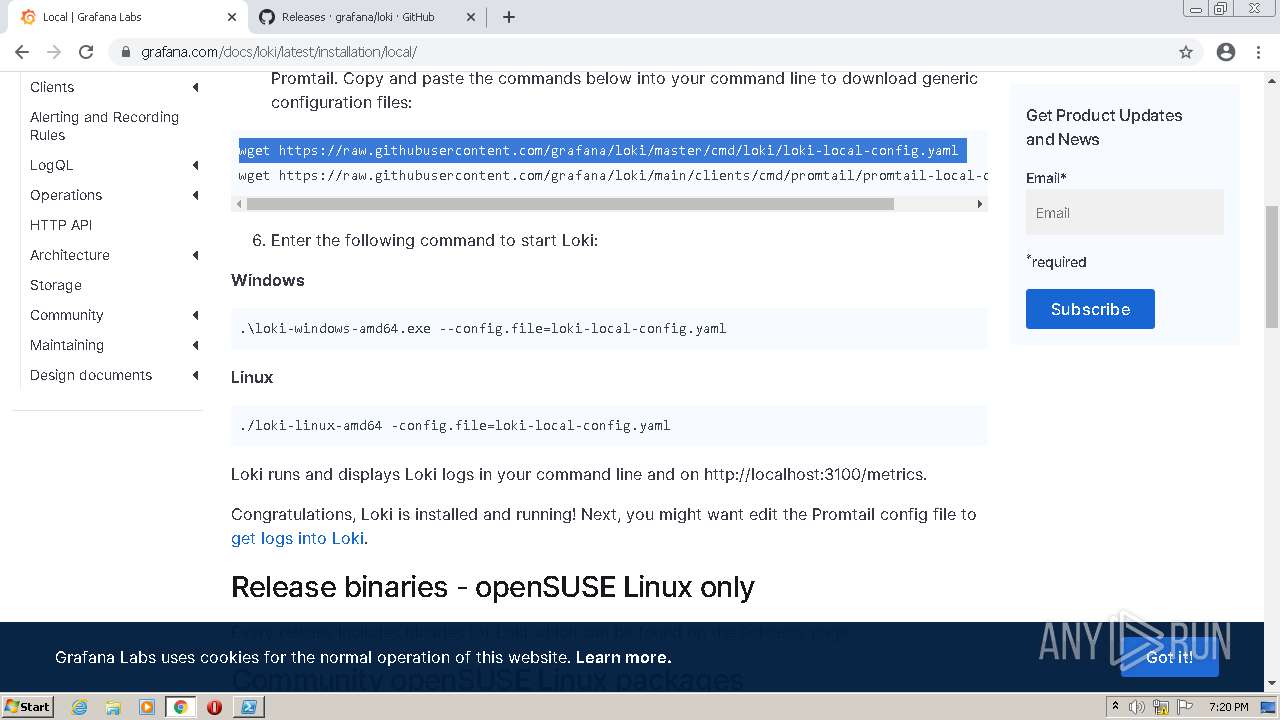
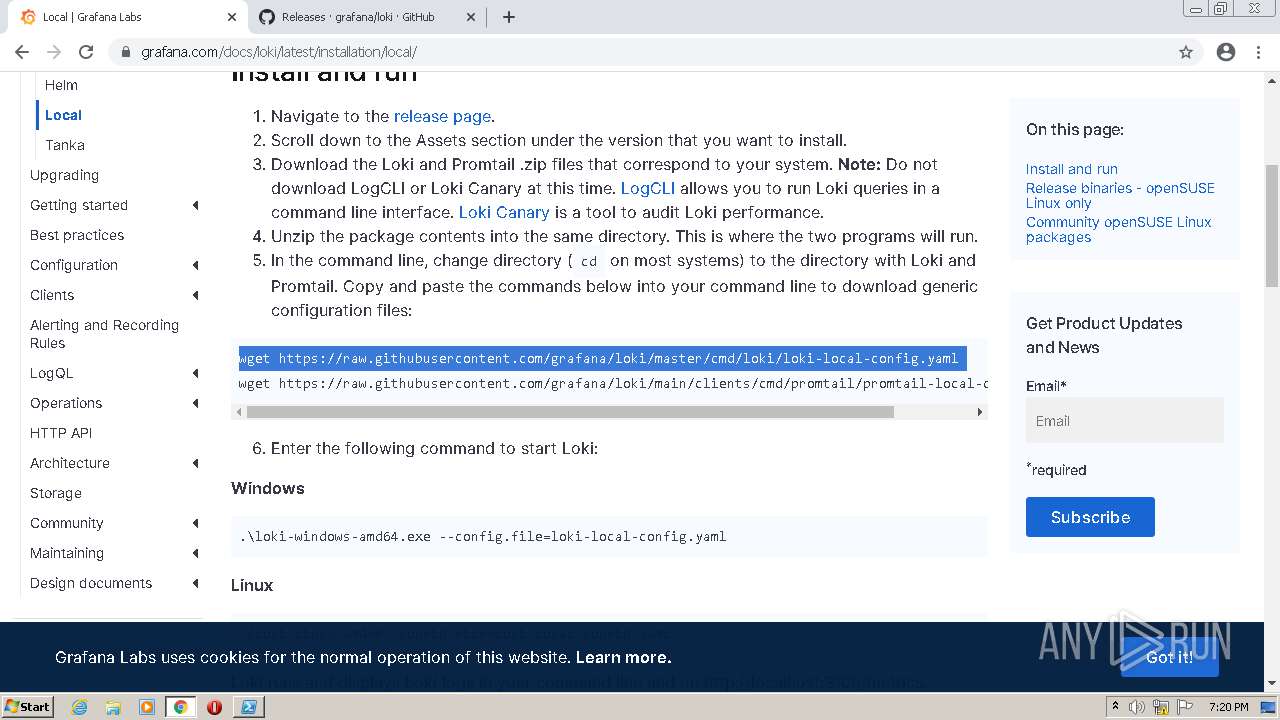
PowerShell script executed
- powershell.exe (PID: 3520)
INFO
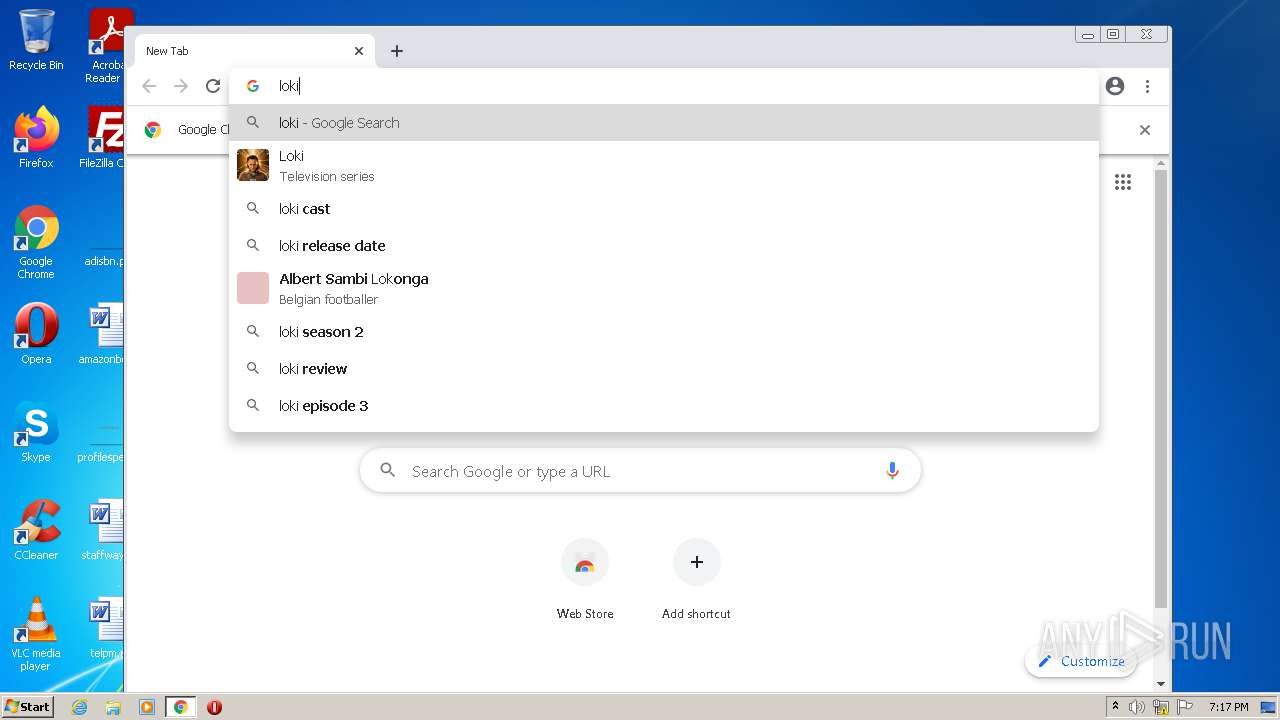
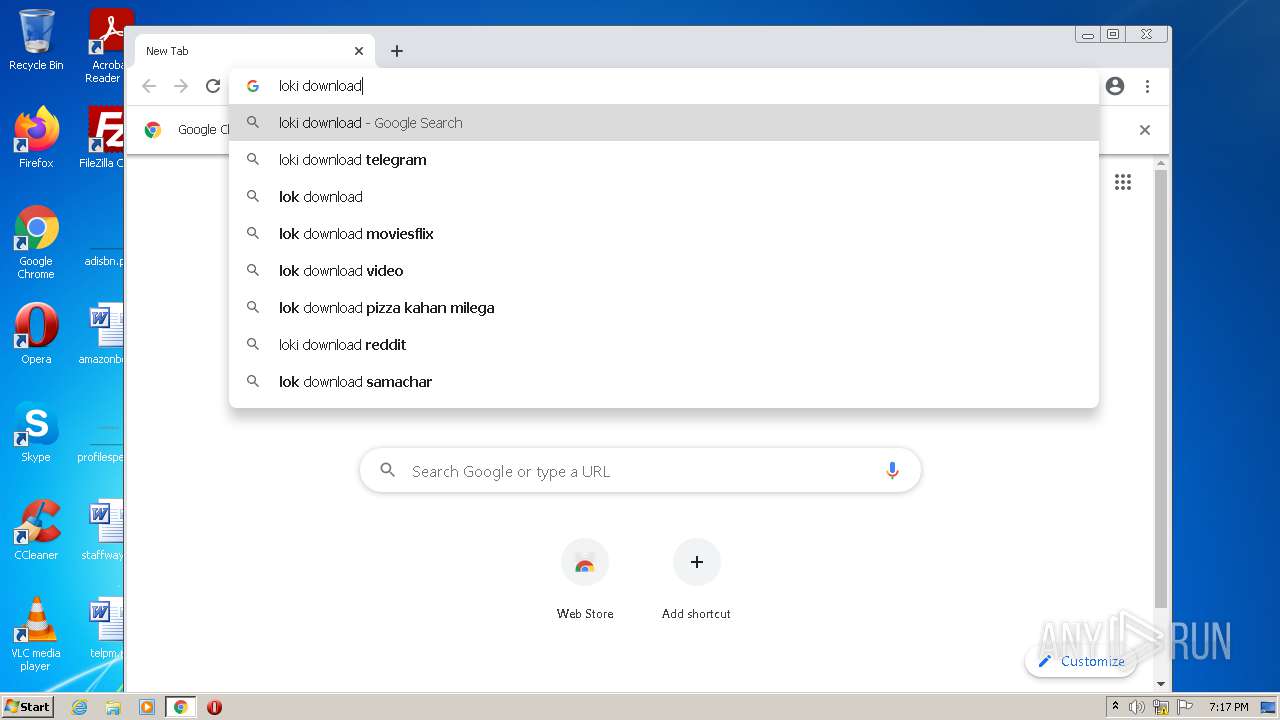
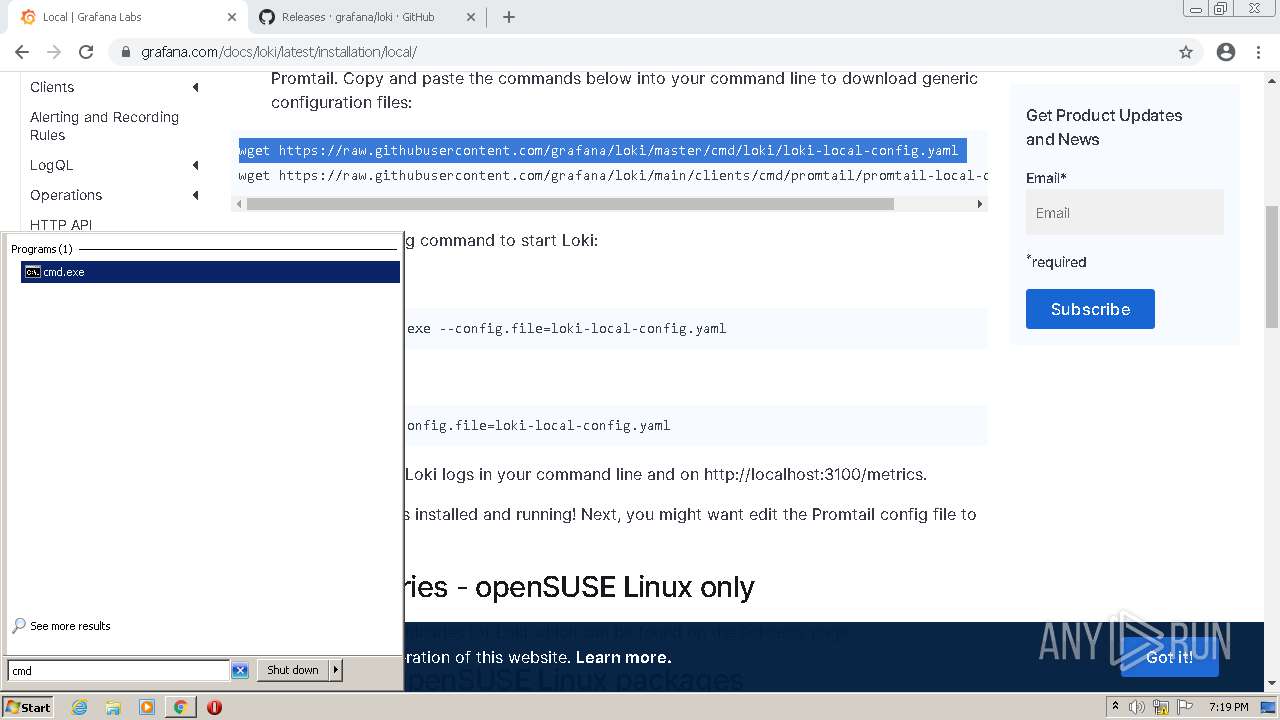
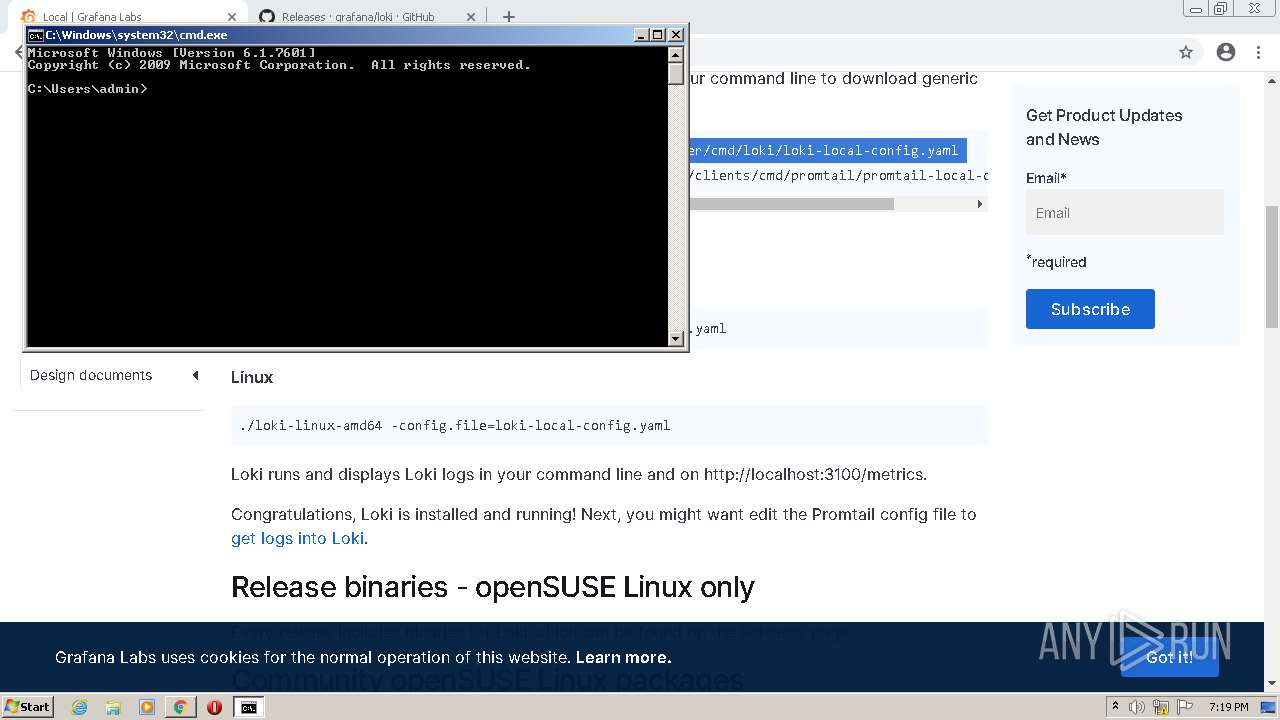
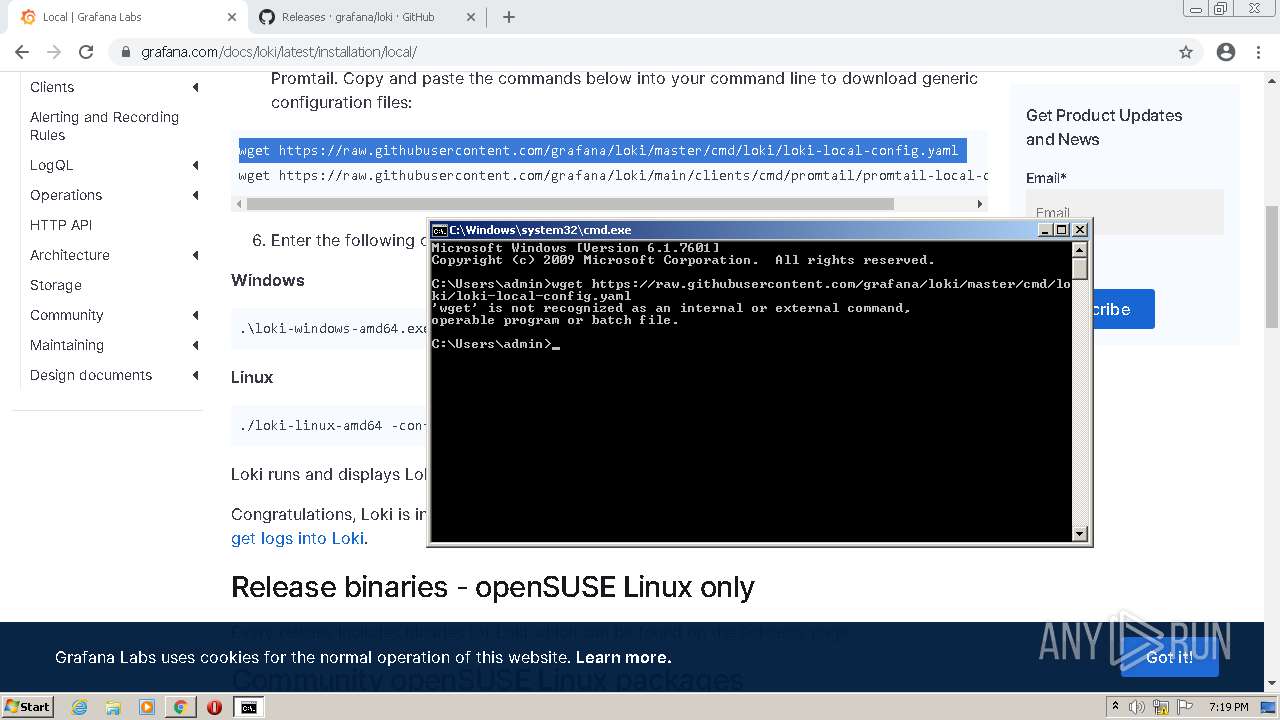
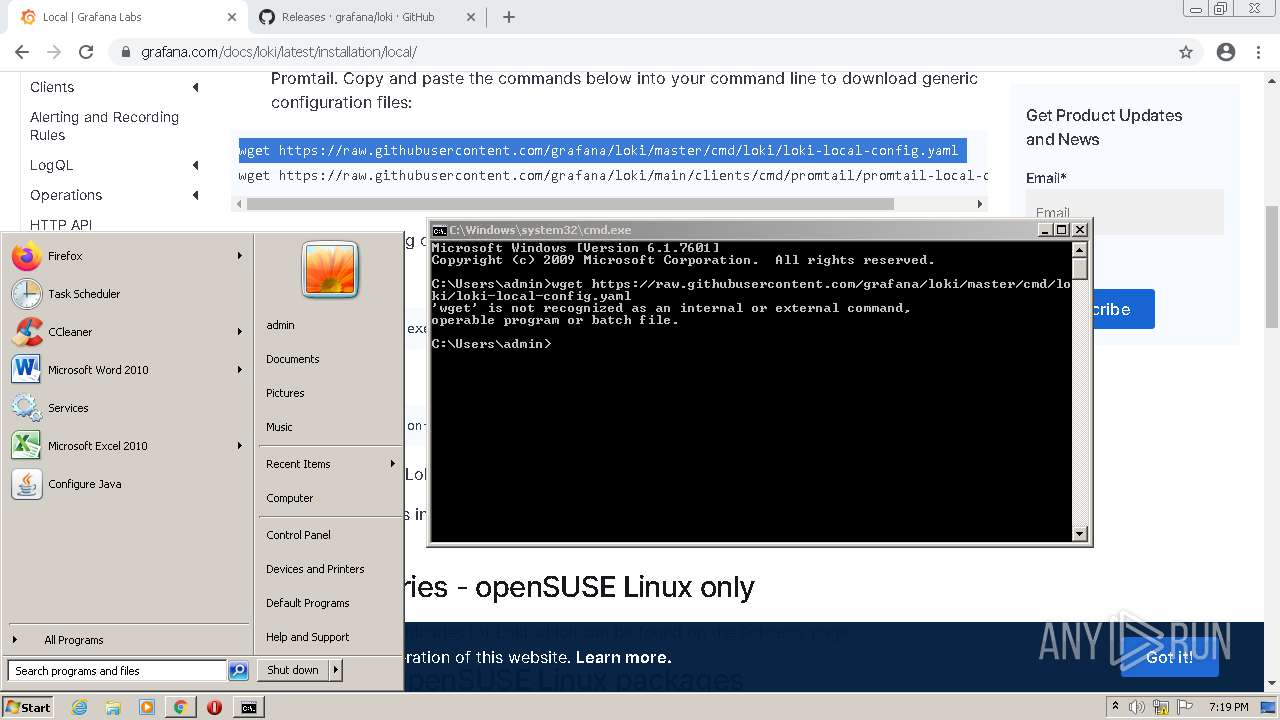
Manual execution by user
- chrome.exe (PID: 188)
- cmd.exe (PID: 3700)
- powershell.exe (PID: 3520)
Checks supported languages
- chrome.exe (PID: 188)
- chrome.exe (PID: 2736)
- chrome.exe (PID: 676)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 3632)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3708)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 3724)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 1164)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 1356)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 1124)
- chrome.exe (PID: 1976)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 460)
- chrome.exe (PID: 2624)
Application launched itself
- chrome.exe (PID: 188)
Reads the hosts file
- chrome.exe (PID: 188)
- chrome.exe (PID: 676)
Reads the computer name
- chrome.exe (PID: 188)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 676)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 4040)
Reads settings of System Certificates
- chrome.exe (PID: 676)
Reads the date of Windows installation
- chrome.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
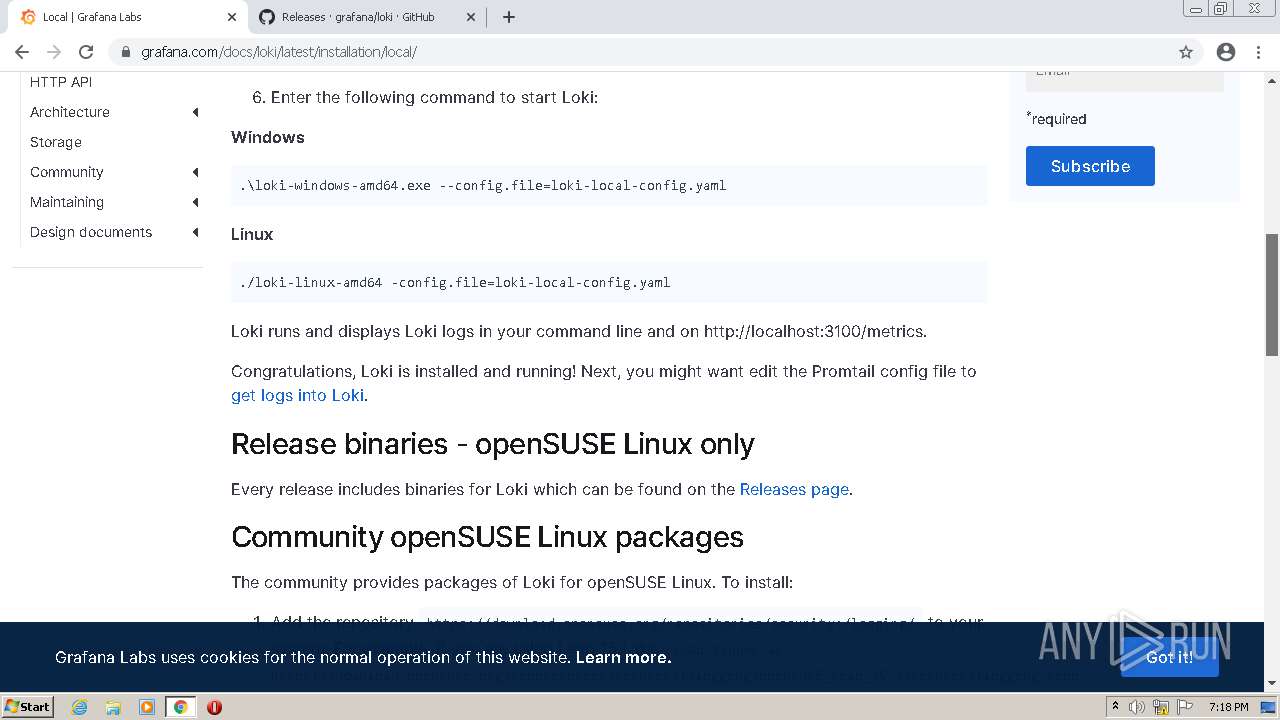
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x7eb4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 159232 |
| CodeSize: | 132096 |
| LinkerVersion: | 14.28 |
| PEType: | PE32 |
| TimeStamp: | 2021:02:27 07:13:34+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 27-Feb-2021 06:13:34 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Feb-2021 06:13:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00020295 | 0x00020400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65528 |
.rdata | 0x00022000 | 0x0000BA16 | 0x0000BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.04621 |
.data | 0x0002E000 | 0x0000A67C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.90522 |
.rsrc | 0x00039000 | 0x00018CD0 | 0x00018E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.85041 |
.reloc | 0x00052000 | 0x0000184C | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.47937 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.60989 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.27961 | 1490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.52655 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.25633 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.50351 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.49709 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
Total processes
81
Monitored processes
44
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,5013135368952973475,5014486873623588548,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1912 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1032,5013135368952973475,5014486873623588548,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1328 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5013135368952973475,5014486873623588548,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,5013135368952973475,5014486873623588548,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3264 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5013135368952973475,5014486873623588548,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1708 | "C:\Users\admin\AppData\Local\Temp\loki.exe" | C:\Users\admin\AppData\Local\Temp\loki.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,5013135368952973475,5014486873623588548,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,5013135368952973475,5014486873623588548,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=patch.mojom.FilePatcher --field-trial-handle=1032,5013135368952973475,5014486873623588548,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2192 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
15 436
Read events
15 259
Write events
169
Delete events
8
Modification events
| (PID) Process: | (188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (188) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
33
Suspicious files
104
Text files
286
Unknown types
608
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\_multiprocessing.pyd | executable | |
MD5:7D3306BA4645463CB0D4C34C77B2BDF2 | SHA256:3A183E0F6A31507C3B0ACBCAE5D6C3D843C590BB370DE5382E2DF9CFC2CB156E | |||
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\_asyncio.pyd | executable | |
MD5:A2FFF5C11F404D795E7D2B4907ED4485 | SHA256:ED7830D504D726CE42B3B7A1321F39C8E29D1EBAD7B64632E45B712F0C47E189 | |||
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\_decimal.pyd | executable | |
MD5:5CDA820A4E1427EAB472A05398B7BA36 | SHA256:49D4DCD257138718CC3F8D8BB445F8C9212CDA73B06CF70F3D706102042680BC | |||
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\VCRUNTIME140.dll | executable | |
MD5:2EBF45DA71BD8EF910A7ECE7E4647173 | SHA256:CF39E1E81F57F42F4D60ABC1D30ECF7D773E576157AA88BBC1D672BF5AD9BB8B | |||
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\_queue.pyd | executable | |
MD5:33A3AF108A41C487D6EB6FBC0BBF54DC | SHA256:E7859D57A449BA5D5E78BEF573D9FF4C68D3C9DF692A04737F0737B340D2B618 | |||
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\loki.exe.manifest | xml | |
MD5:D071BBF661800A977981D365F6E0F779 | SHA256:D4BB39C6D433489F19CE5F0D620799B8B34E4FD0A6ECF7D53CFE3E8A45CF05C6 | |||
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\_socket.pyd | executable | |
MD5:6B59705D8AC80437DD81260443912532 | SHA256:62ED631A6AD09E96B4B6F4566C2AFC710B3493795EDEE4CC14A9C9DE88230648 | |||
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\_ctypes.pyd | executable | |
MD5:C827A20FC5F1F4E0EF9431F29EBF03B4 | SHA256:D500CFF28678ECED1FC4B3AEABECC0F3B30DE735FDEFE90855536BC29FC2CB4D | |||
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\_lzma.pyd | executable | |
MD5:38C434AFB2A885A95999903977DC3624 | SHA256:BFE6E288B2D93905F5CBB6D74E9C0FC37145B9225DB6D1F00C0F69EB45AFD051 | |||
| 1708 | loki.exe | C:\Users\admin\AppData\Local\Temp\_MEI17082\libssl-1_1.dll | executable | |
MD5:697766ABA55F44BBD896CBD091A72B55 | SHA256:44A228B3646EB3575ABD5CBCB079E018DE11CA6B838A29E4391893DE69E0CF4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
63
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
896 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | — | — | whitelisted |
896 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/YGkwa4MXjfWSuERyWQYP_A_4/aapLKTSZ439A-0g3nqJr3Q | US | — | — | whitelisted |
896 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ic2svx6oiugc5qebp27wjf4pd4_2673/jflookgnkcckhobaglndicnbbgbonegd_2673_all_mas5myaqr22mmqxuxnegjylr2a.crx3 | US | — | — | whitelisted |
896 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | binary | 5.76 Kb | whitelisted |
896 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | binary | 20.8 Kb | whitelisted |
896 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | binary | 386 Kb | whitelisted |
896 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | binary | 9.63 Kb | whitelisted |
896 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | binary | 9.64 Kb | whitelisted |
896 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | binary | 718 Kb | whitelisted |
896 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/YGkwa4MXjfWSuERyWQYP_A_4/aapLKTSZ439A-0g3nqJr3Q | US | binary | 386 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
676 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
676 | chrome.exe | 142.250.186.164:443 | www.google.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 142.250.186.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 142.250.186.164:443 | www.google.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 142.250.185.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 142.250.185.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 142.250.185.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 142.250.186.46:443 | apis.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.184.238:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 142.250.185.99:443 | update.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |