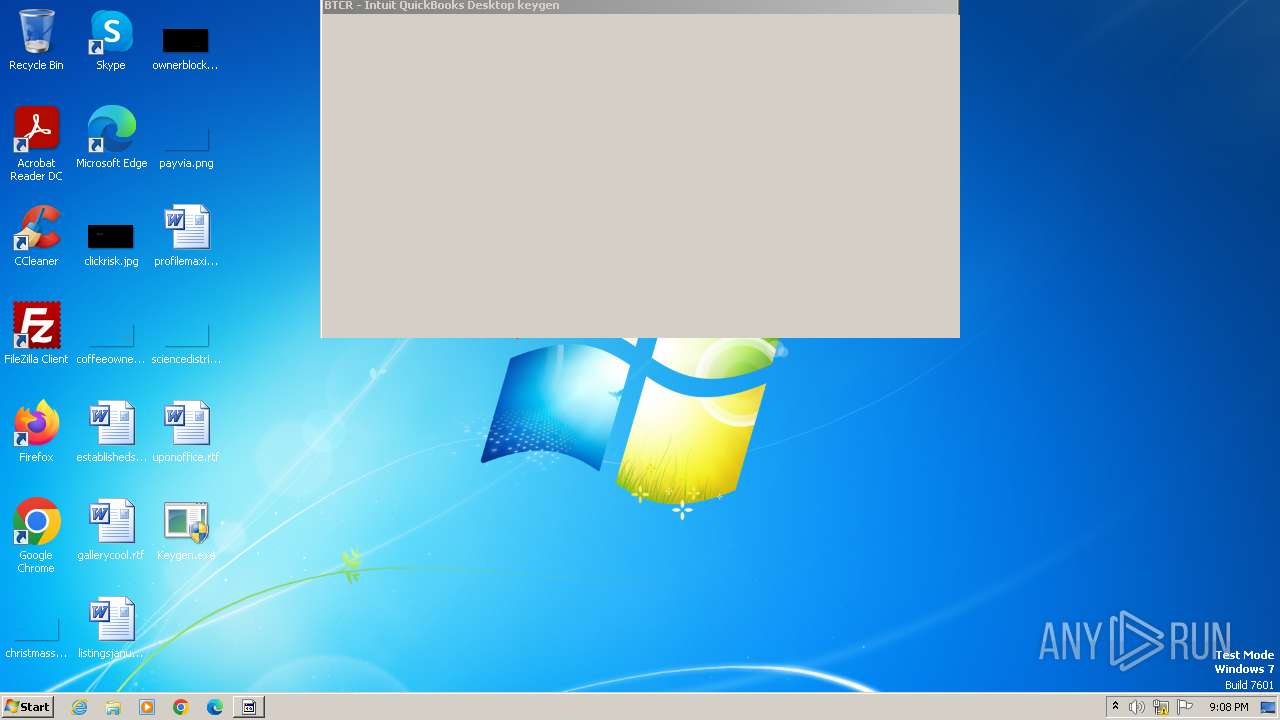
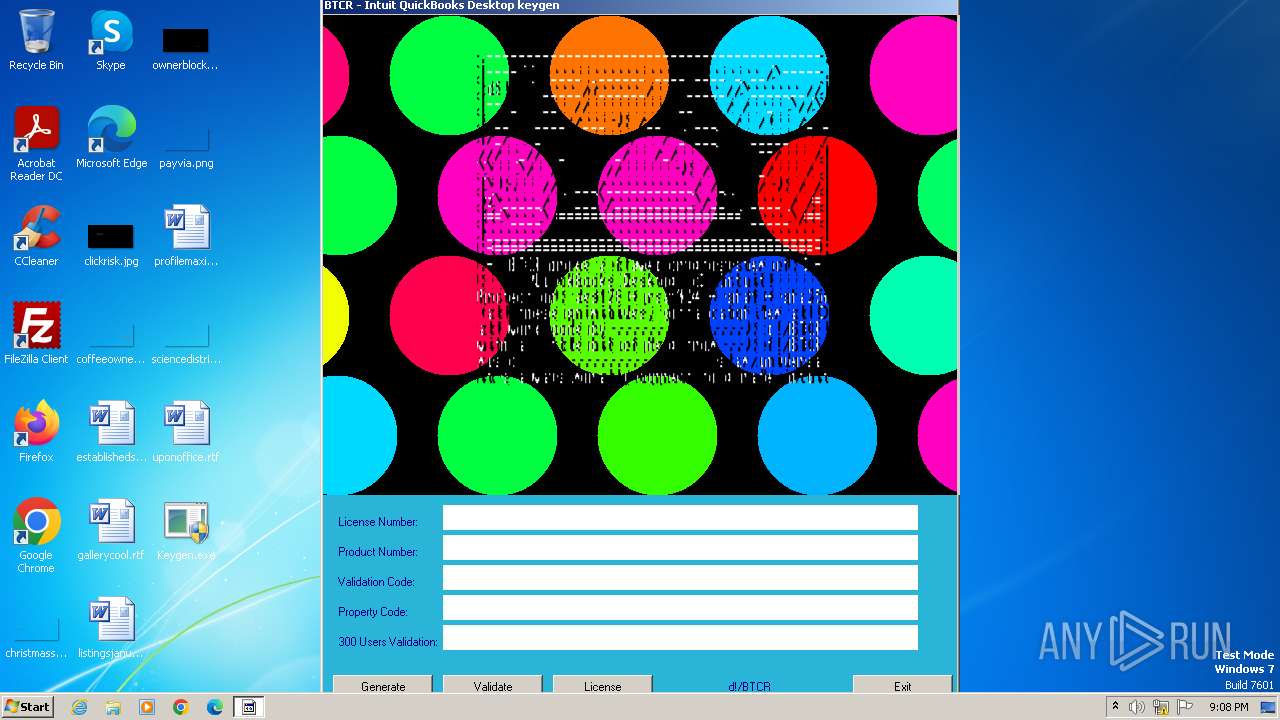
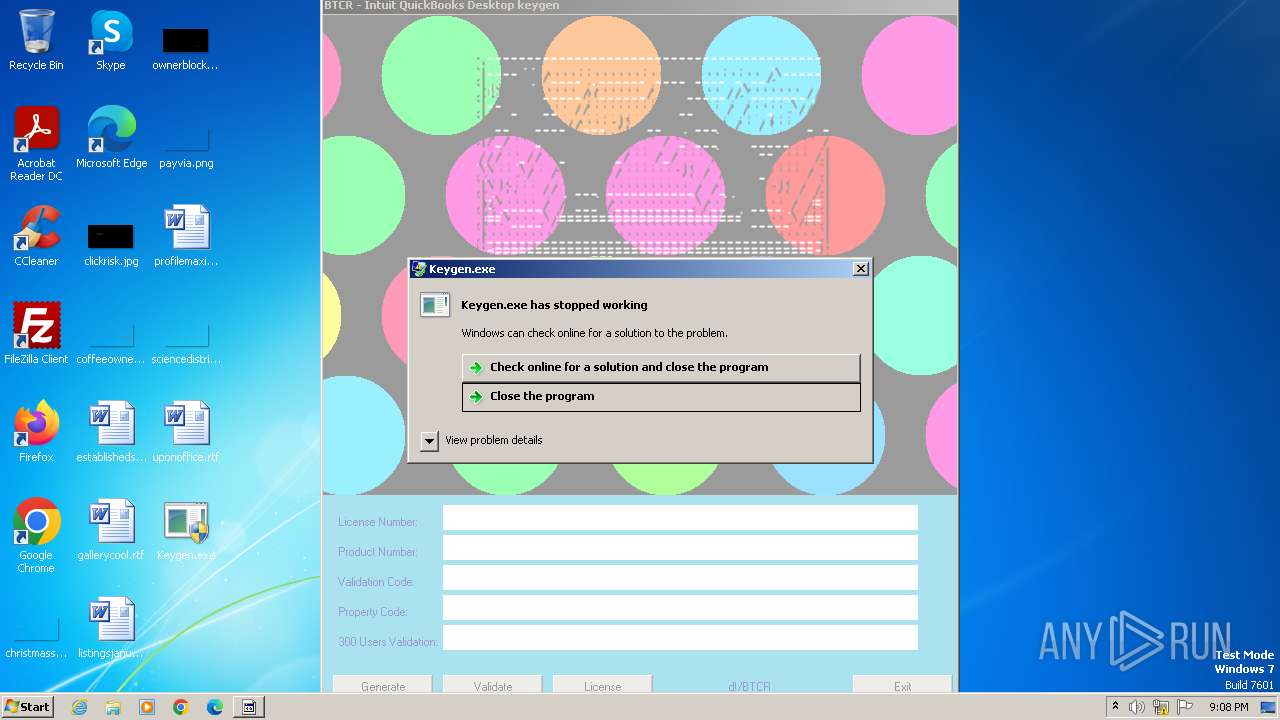
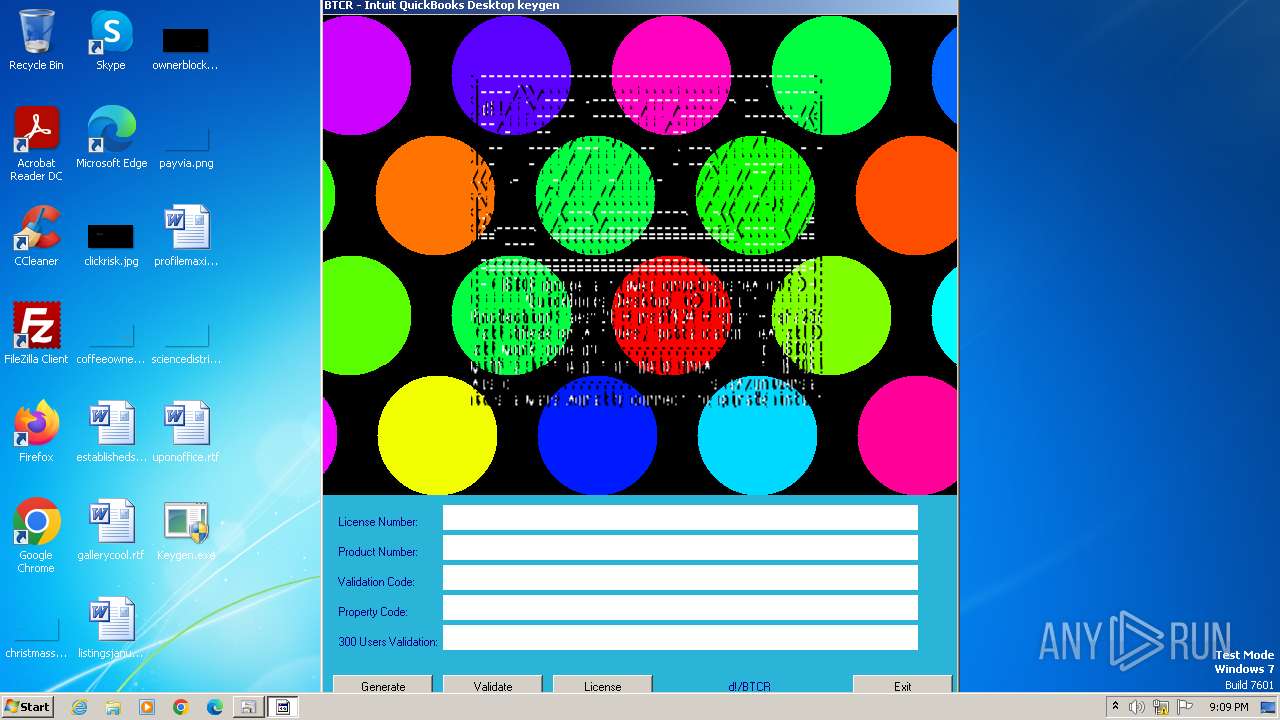
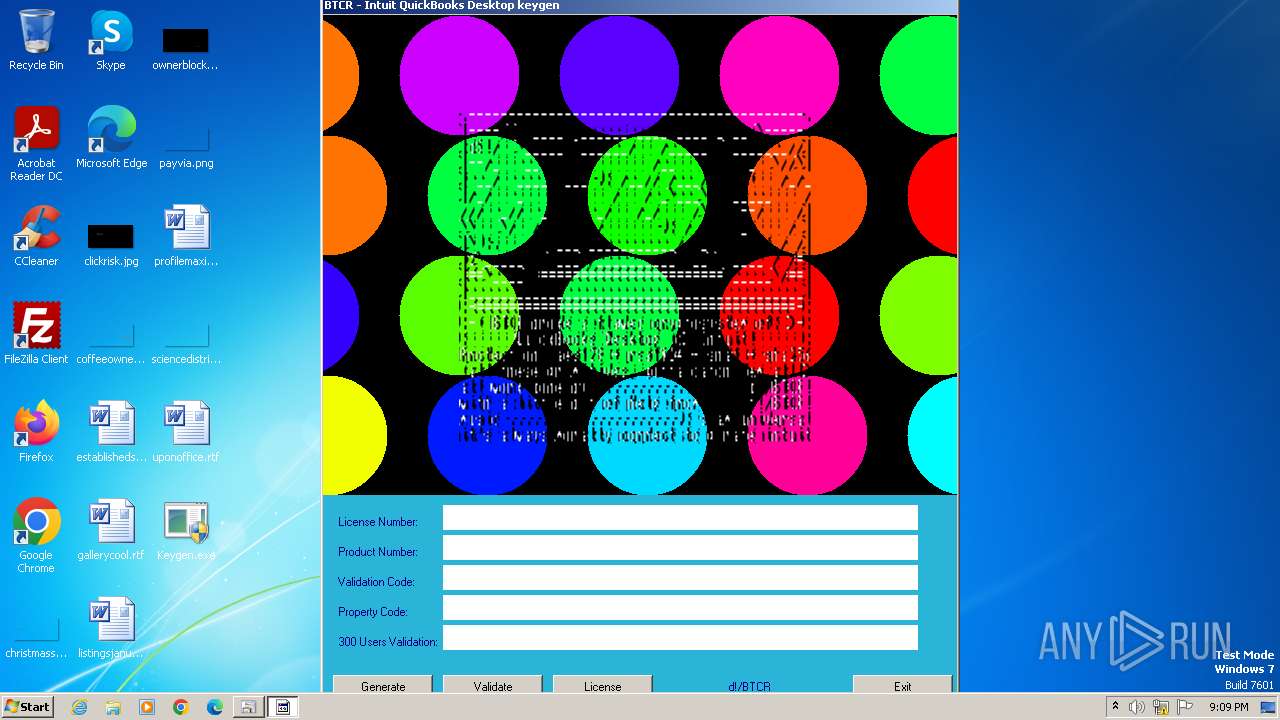
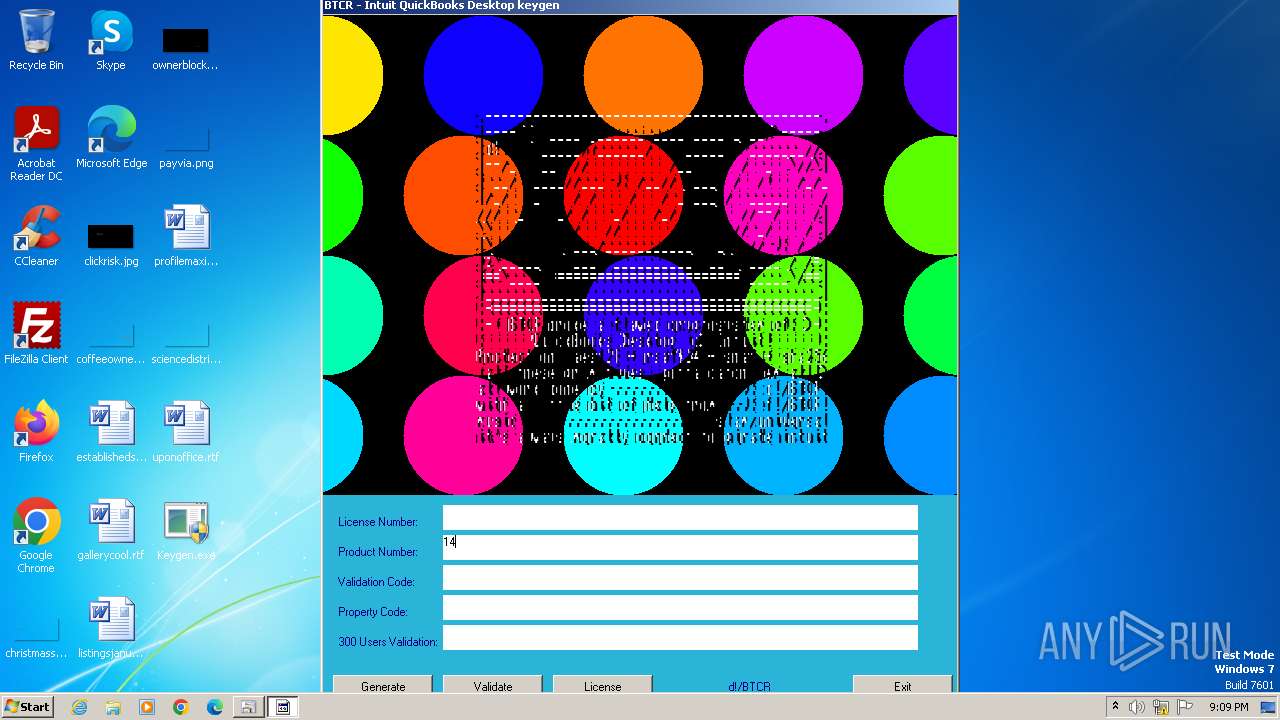
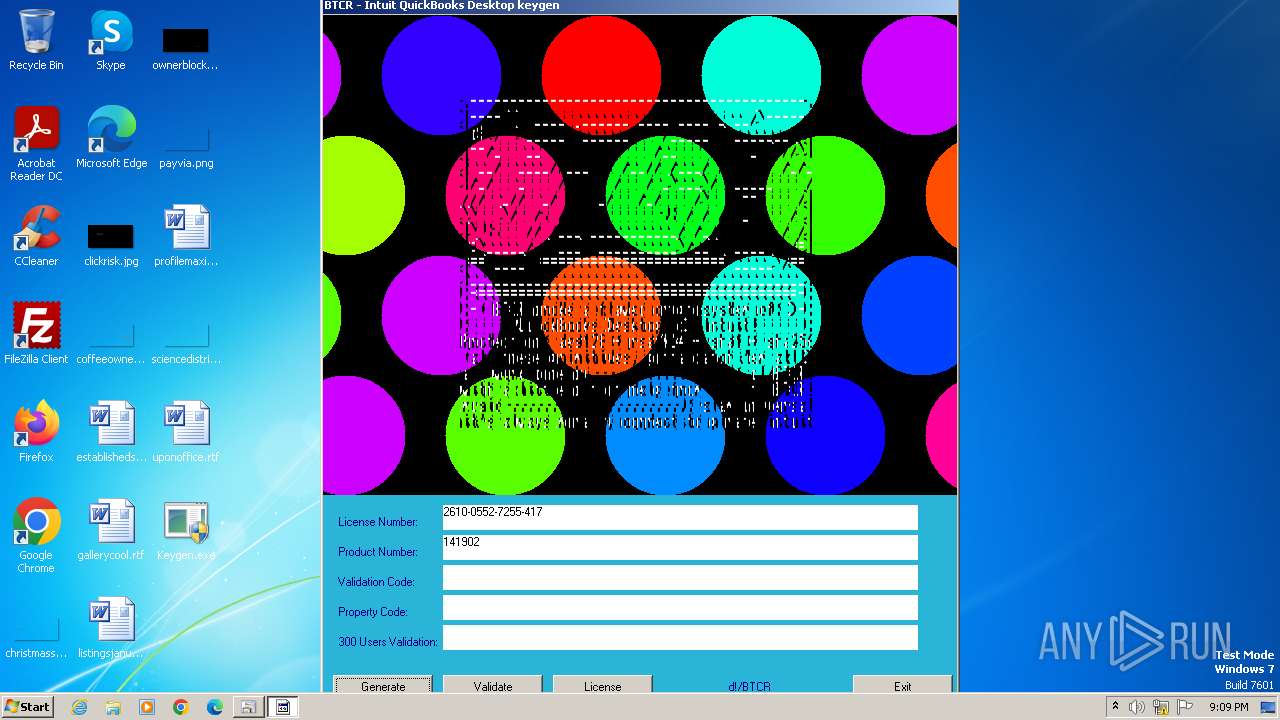
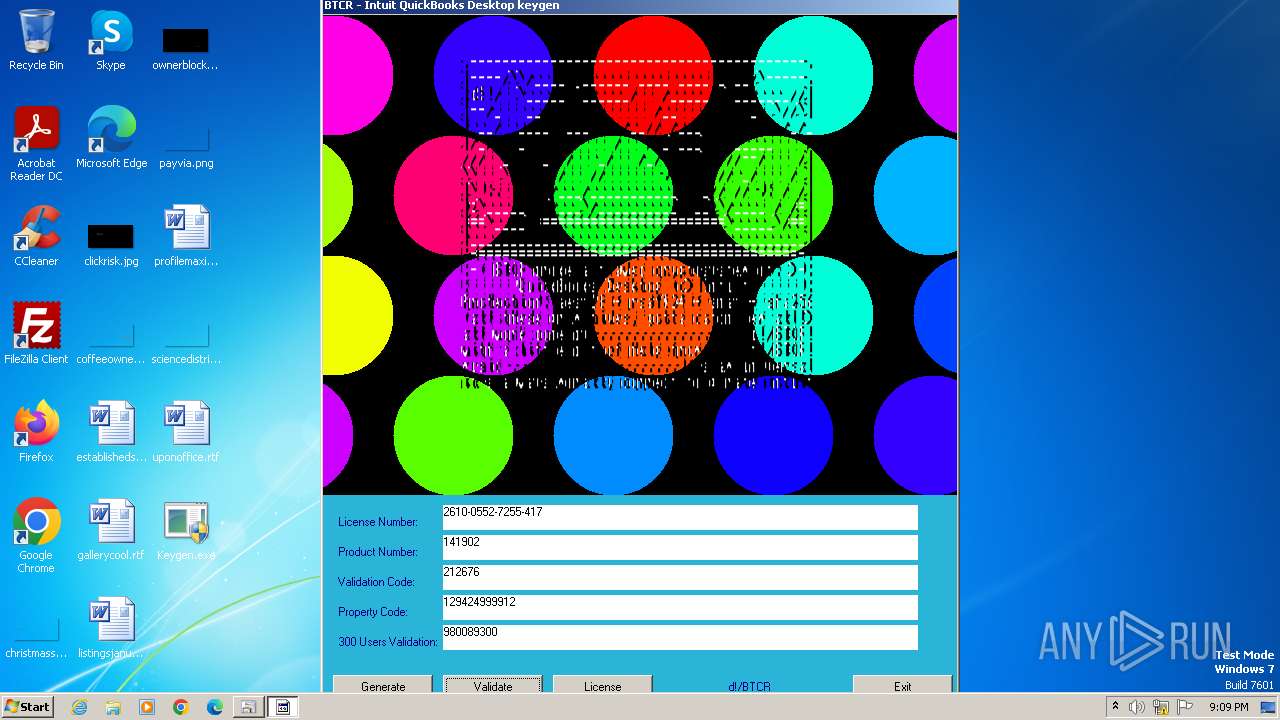
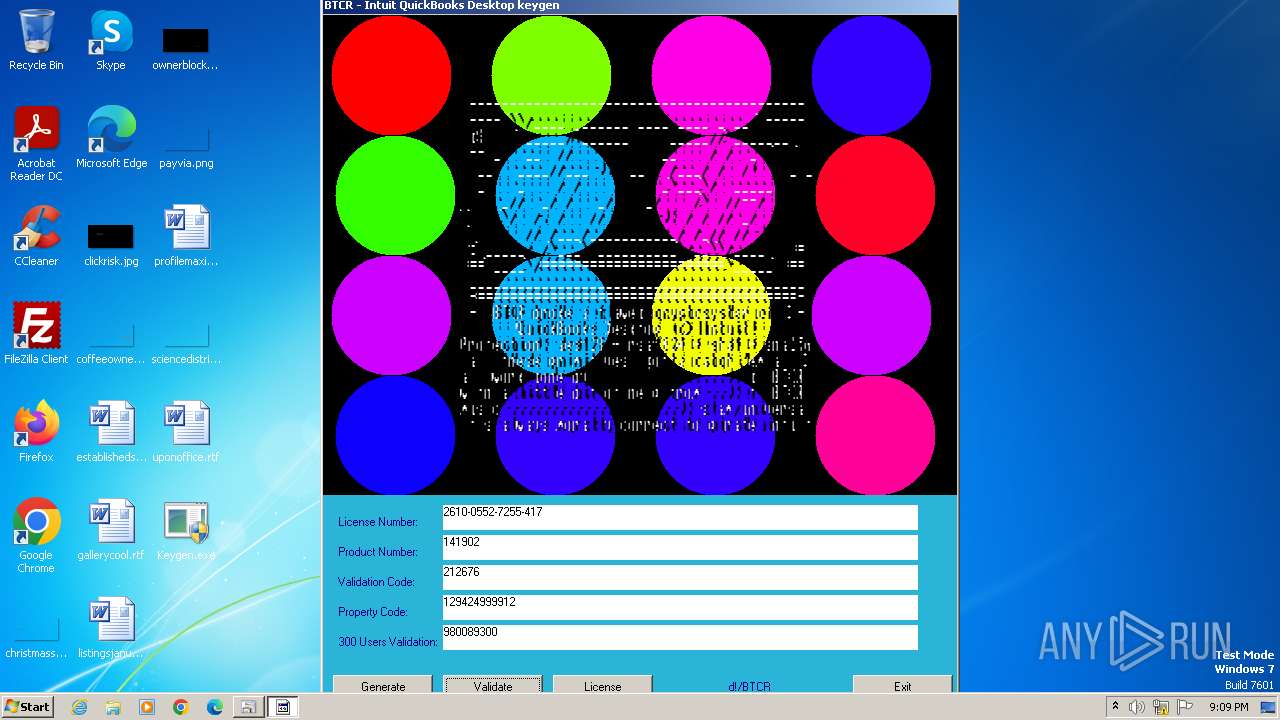
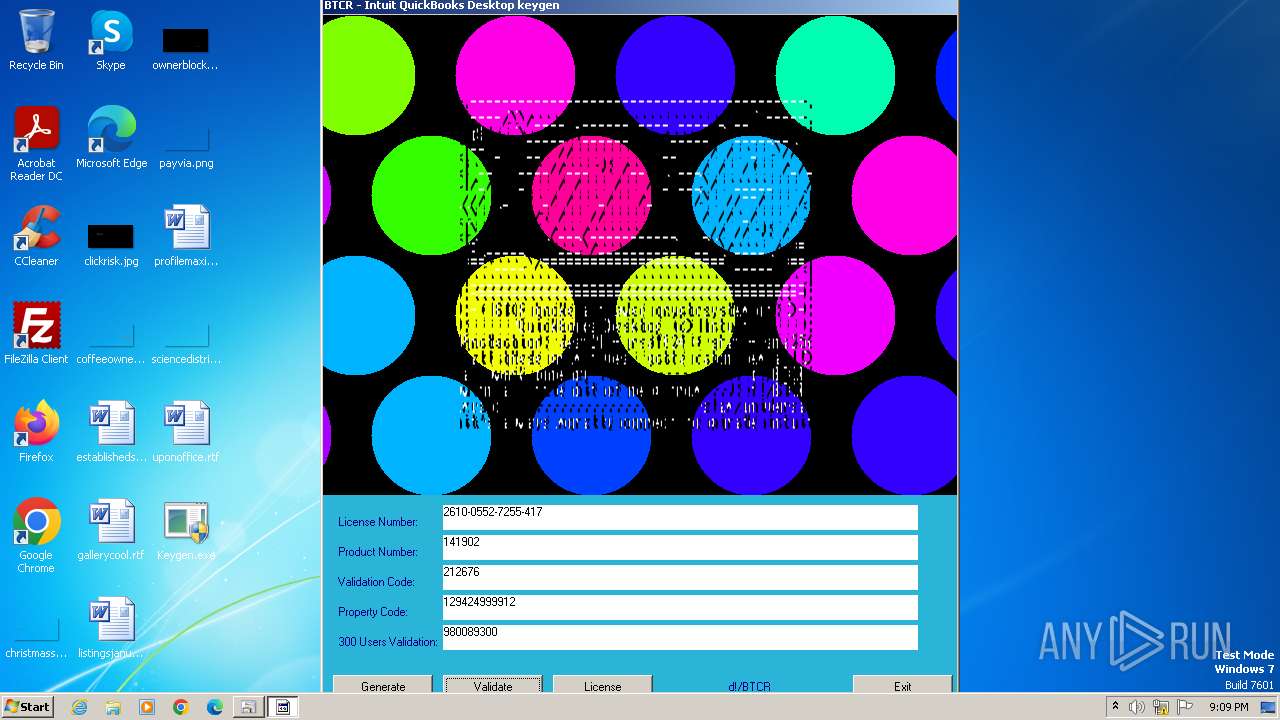
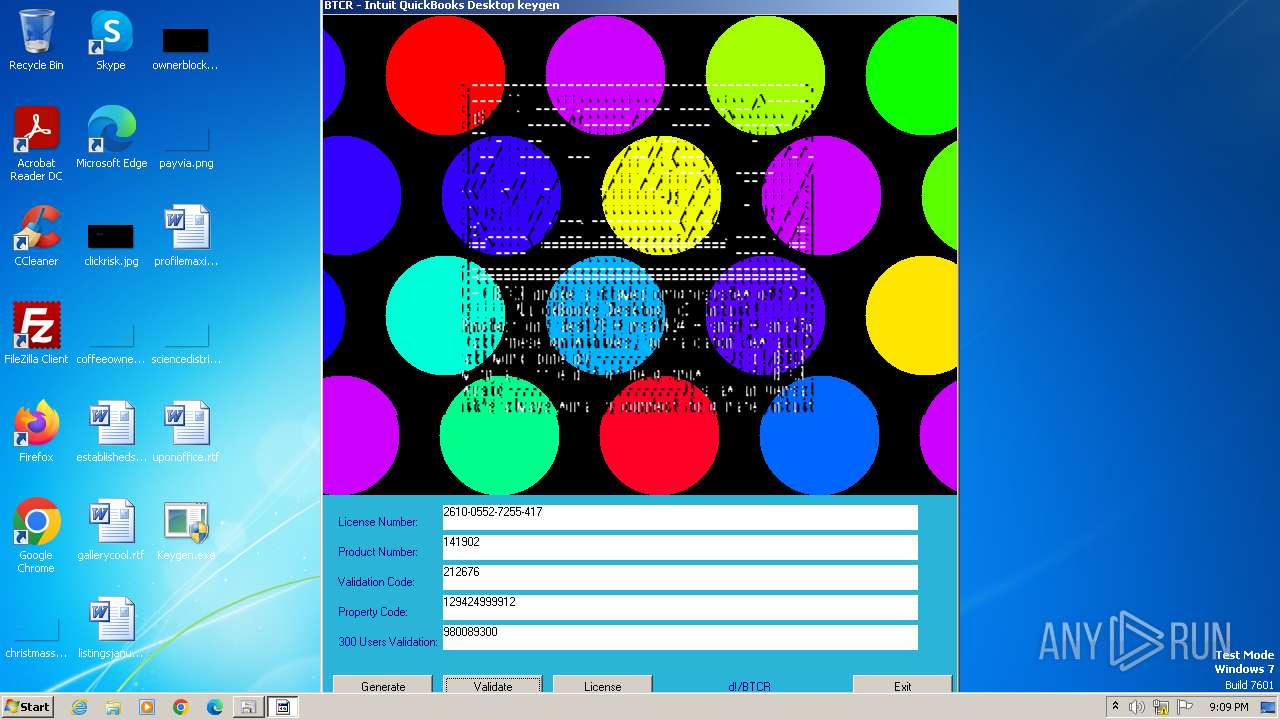
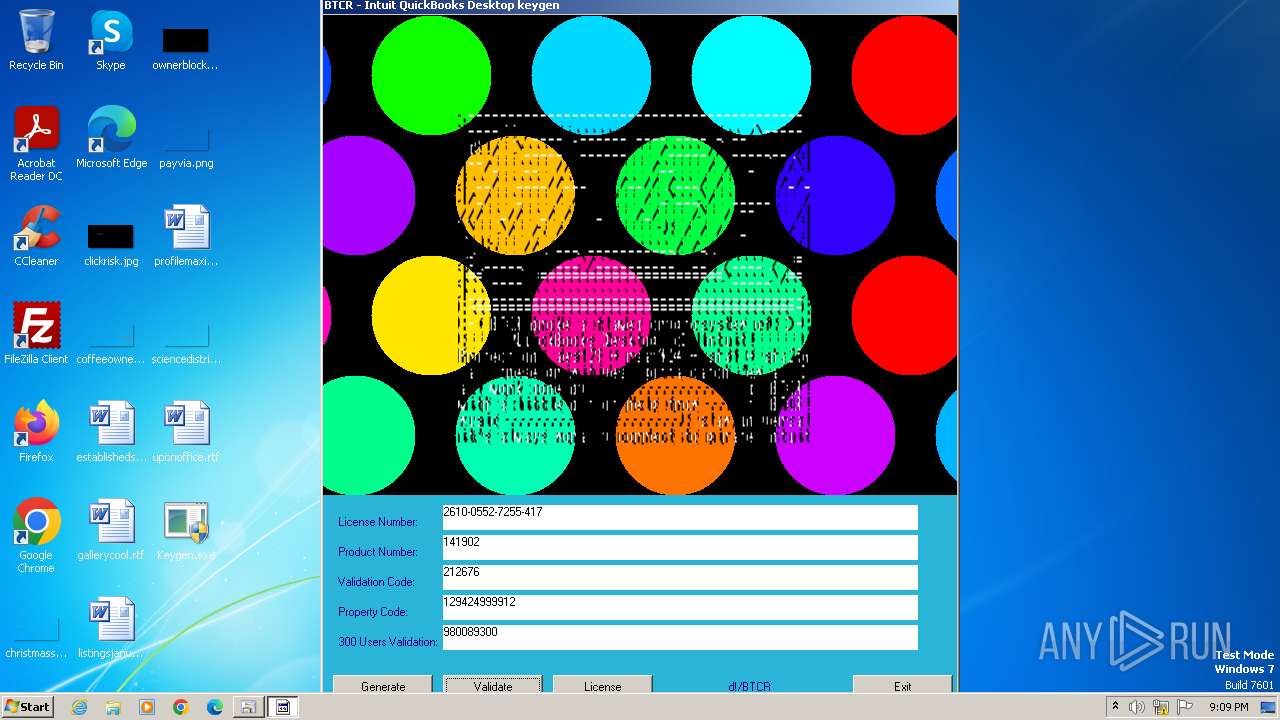
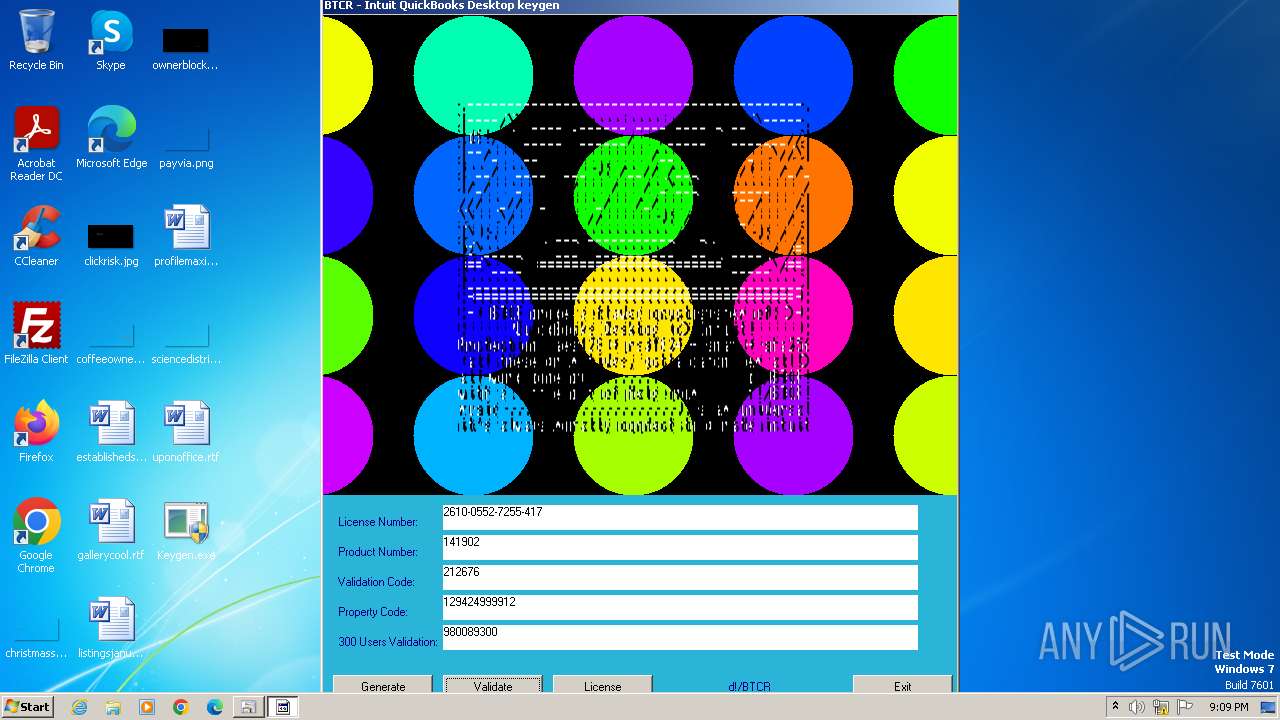
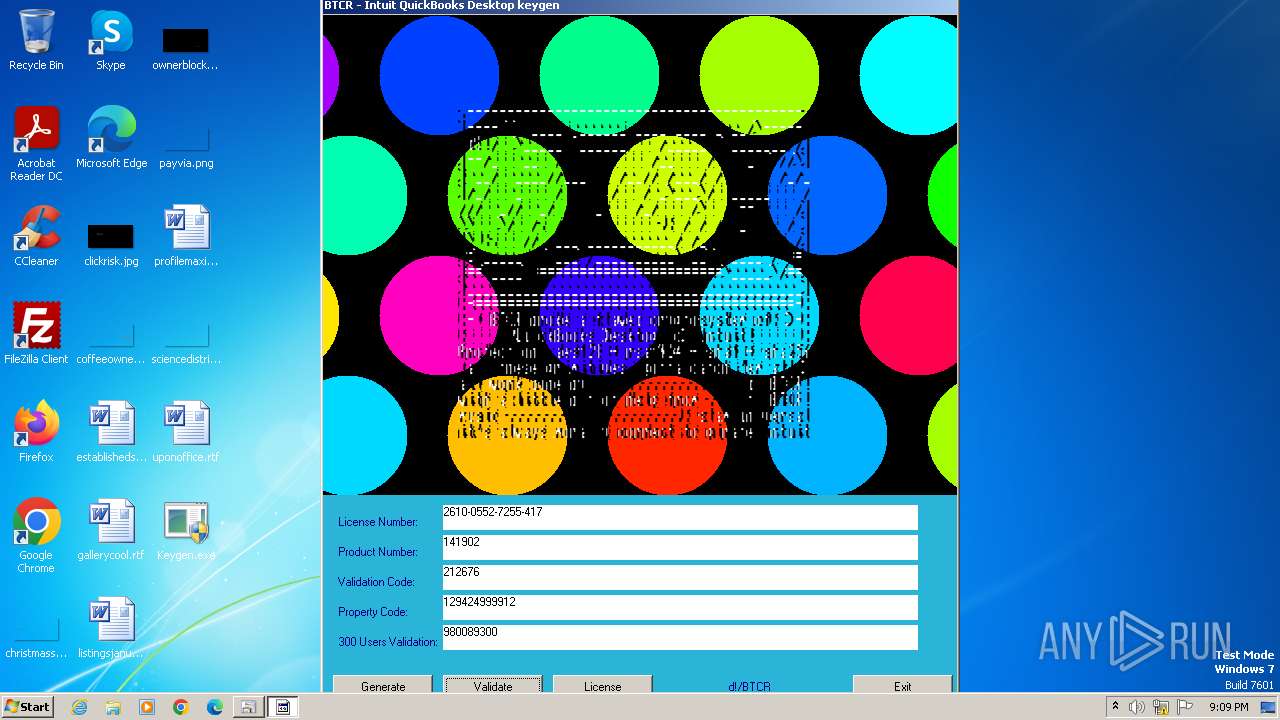
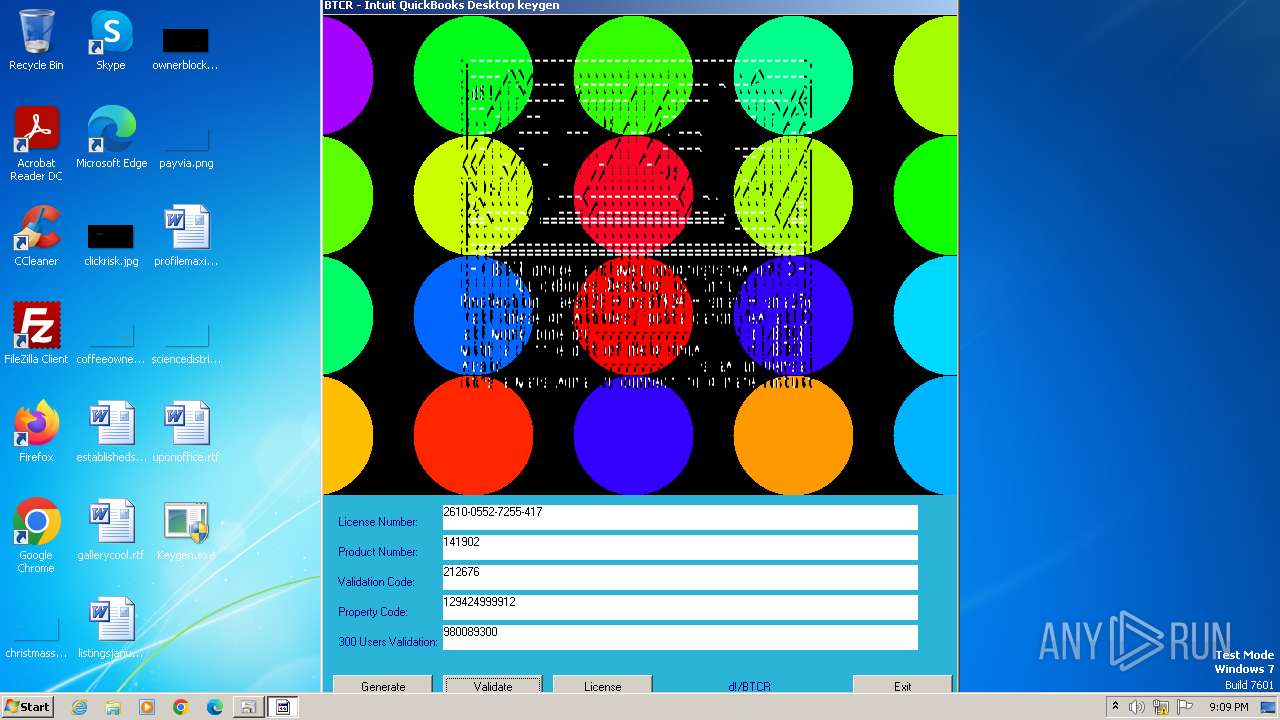
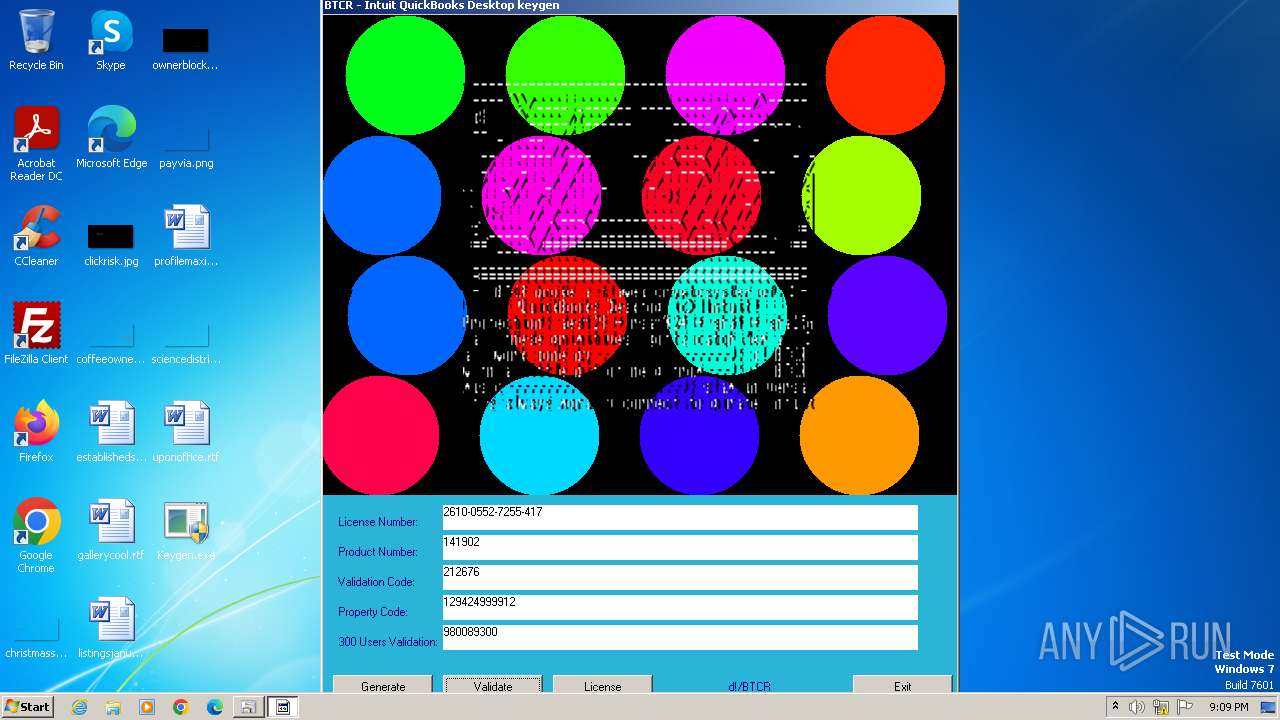
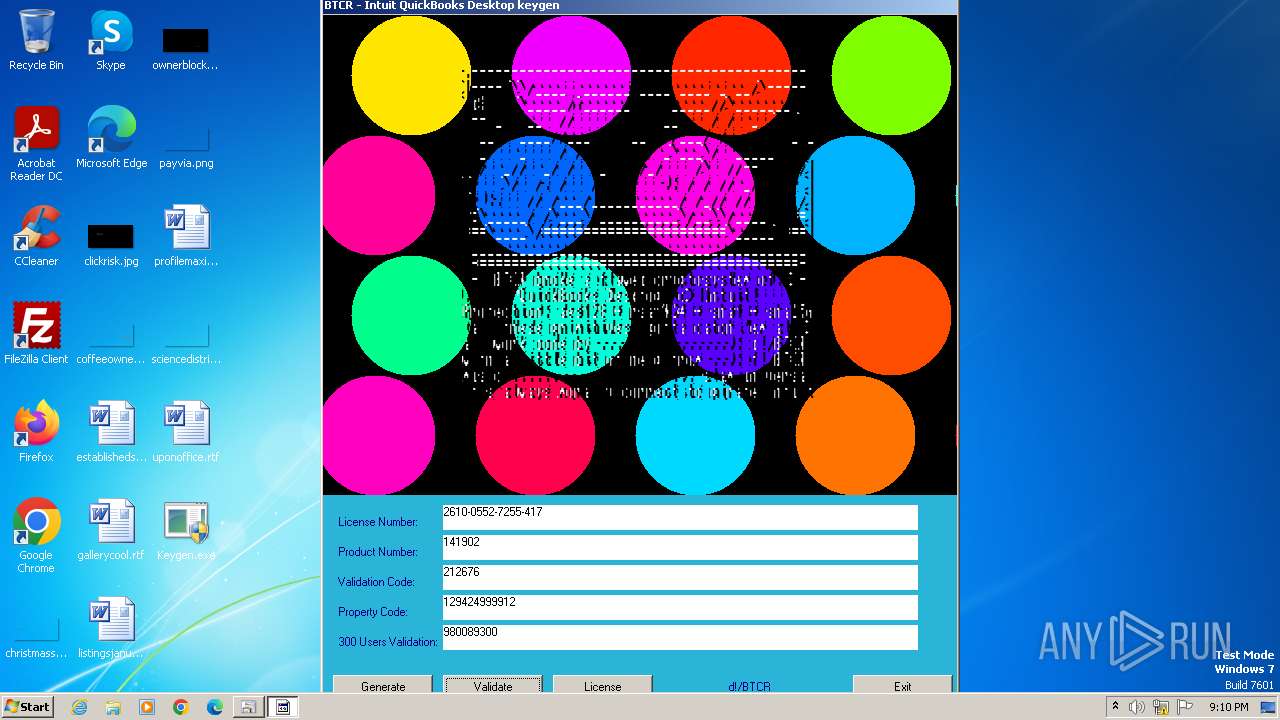
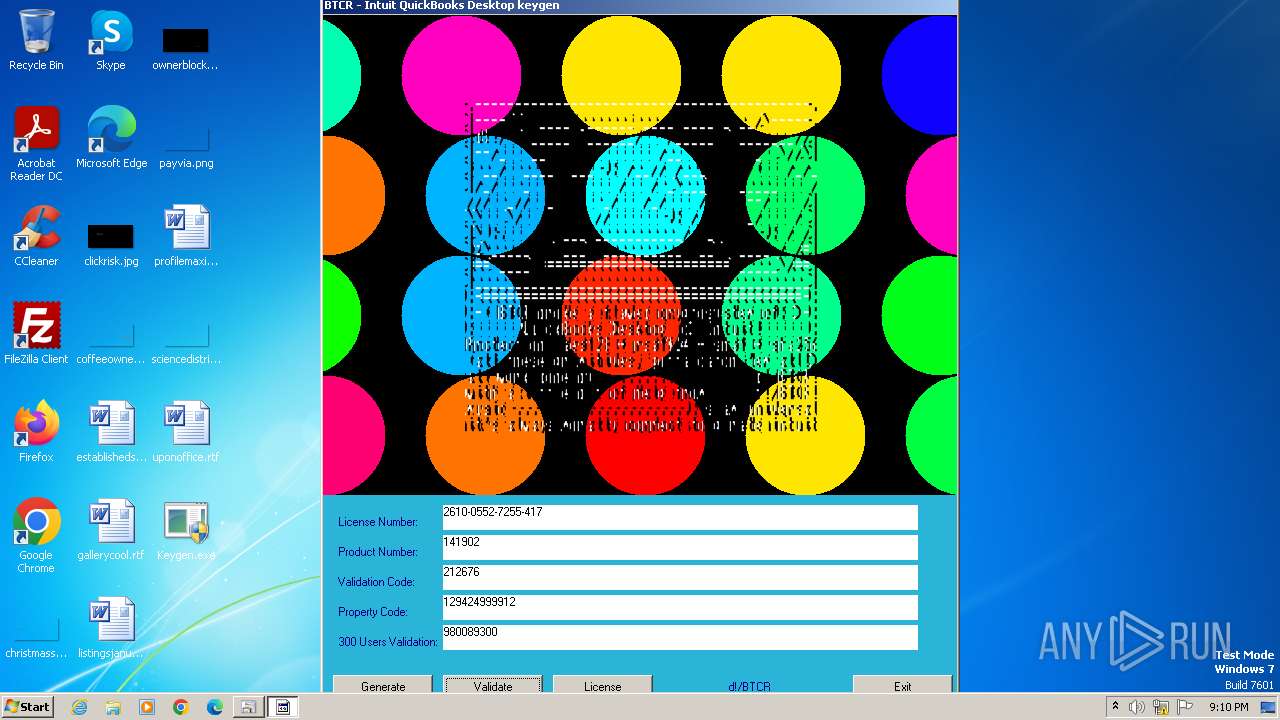
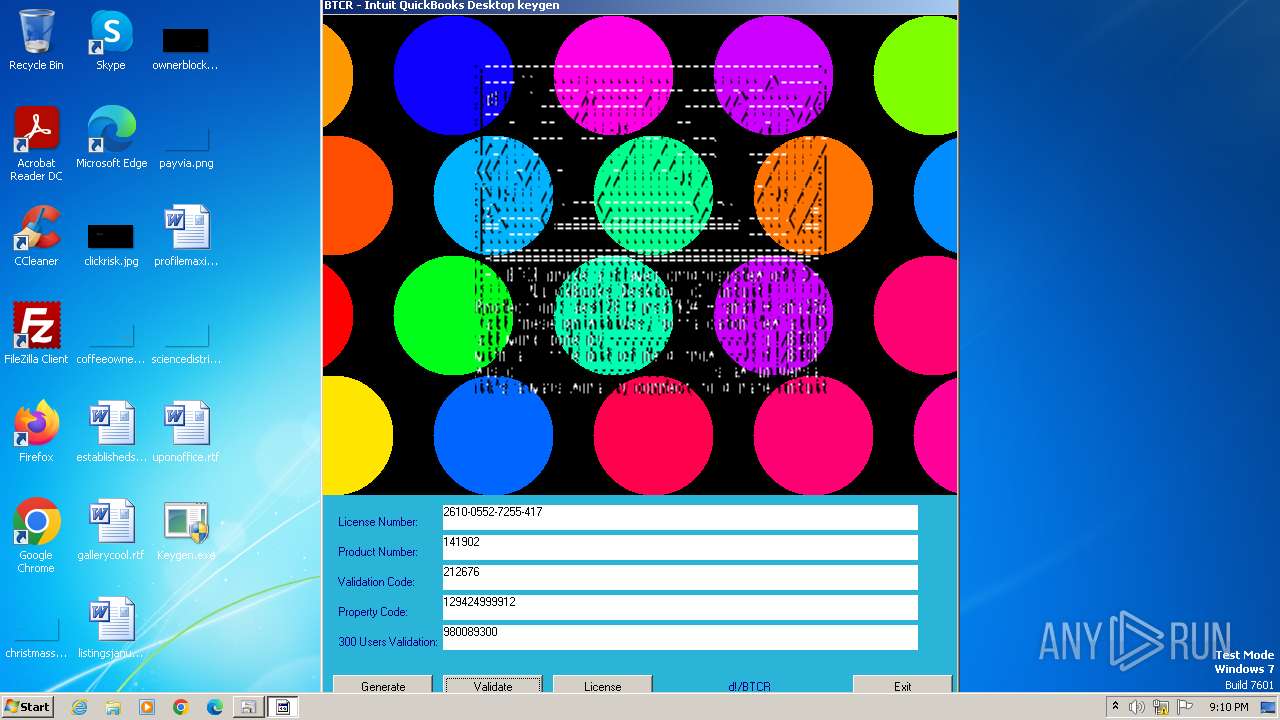
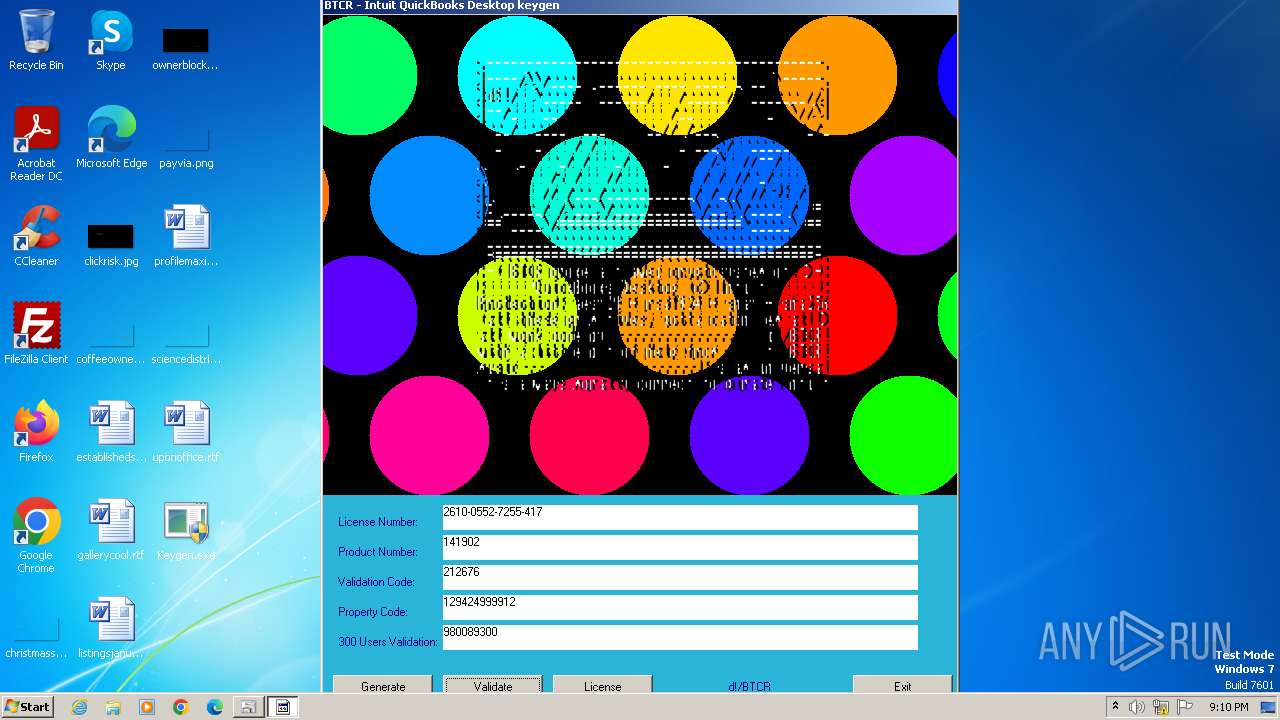
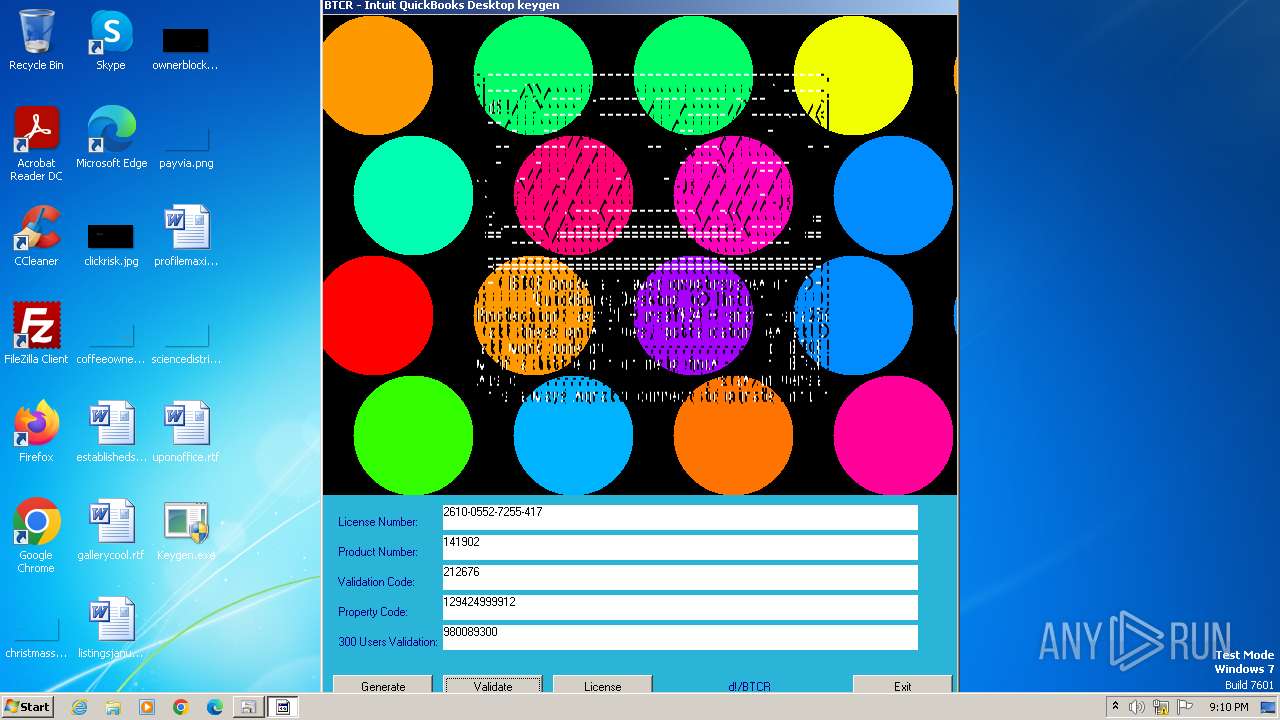
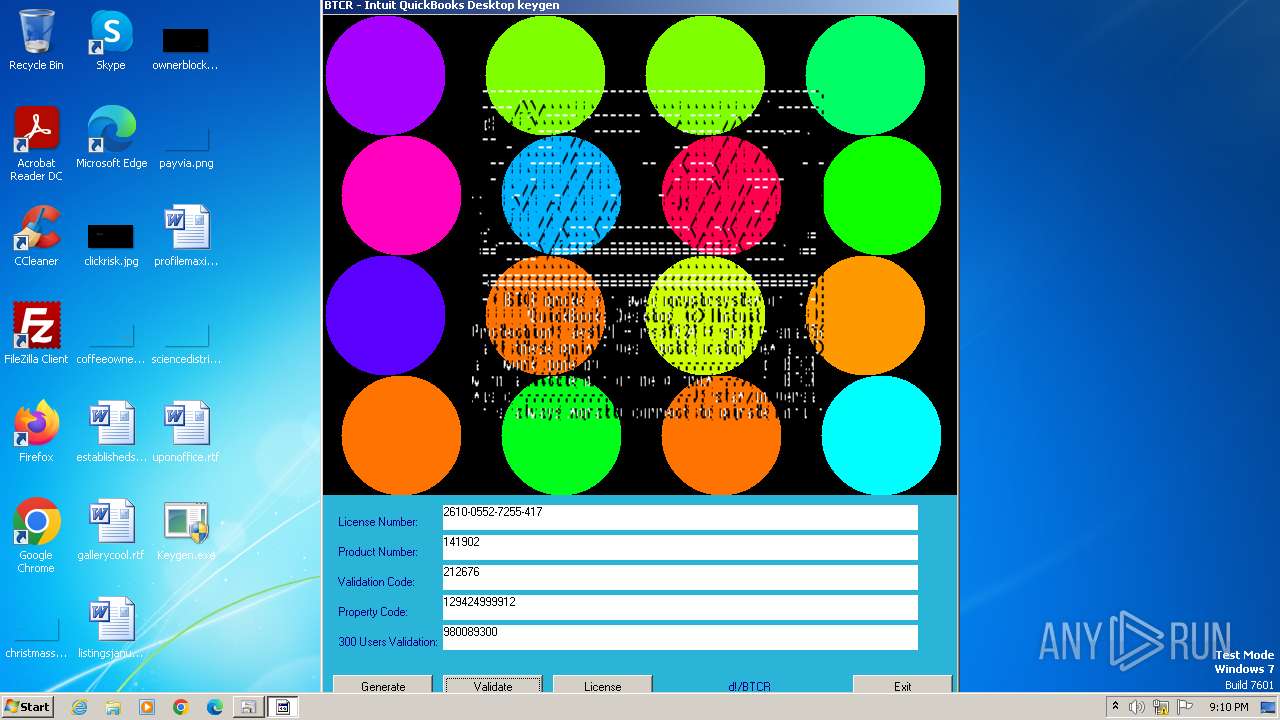
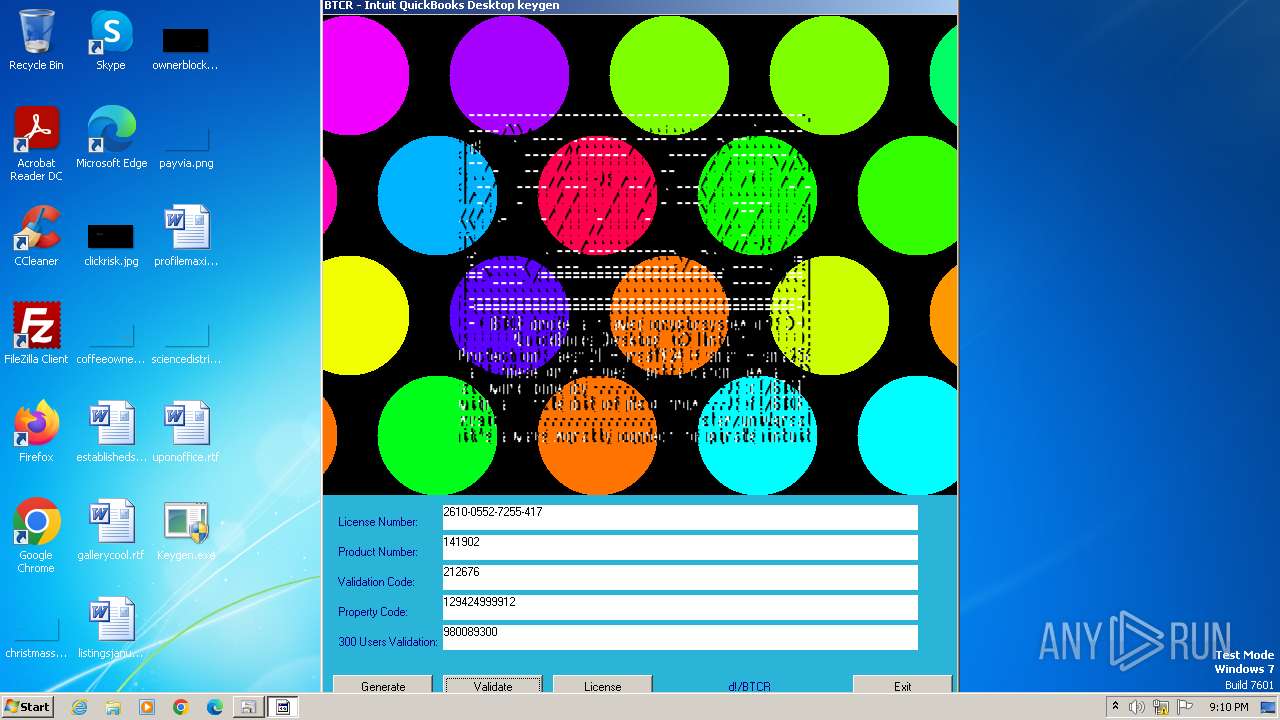
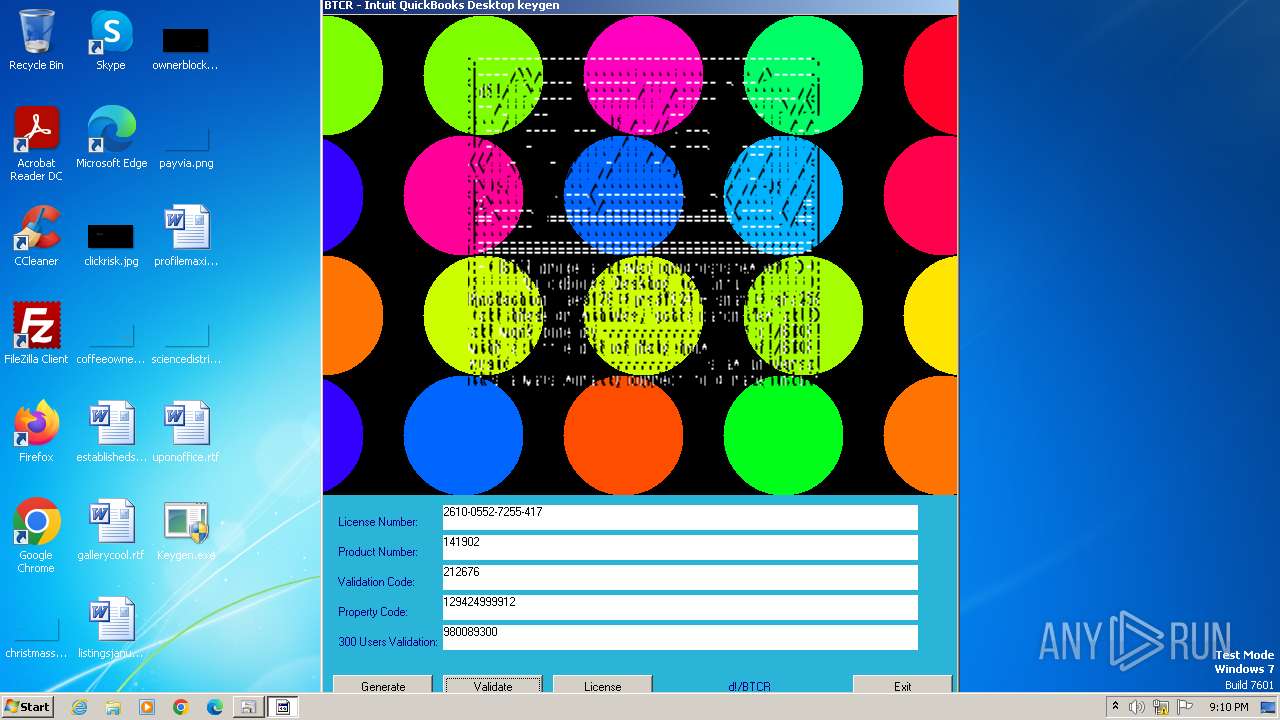
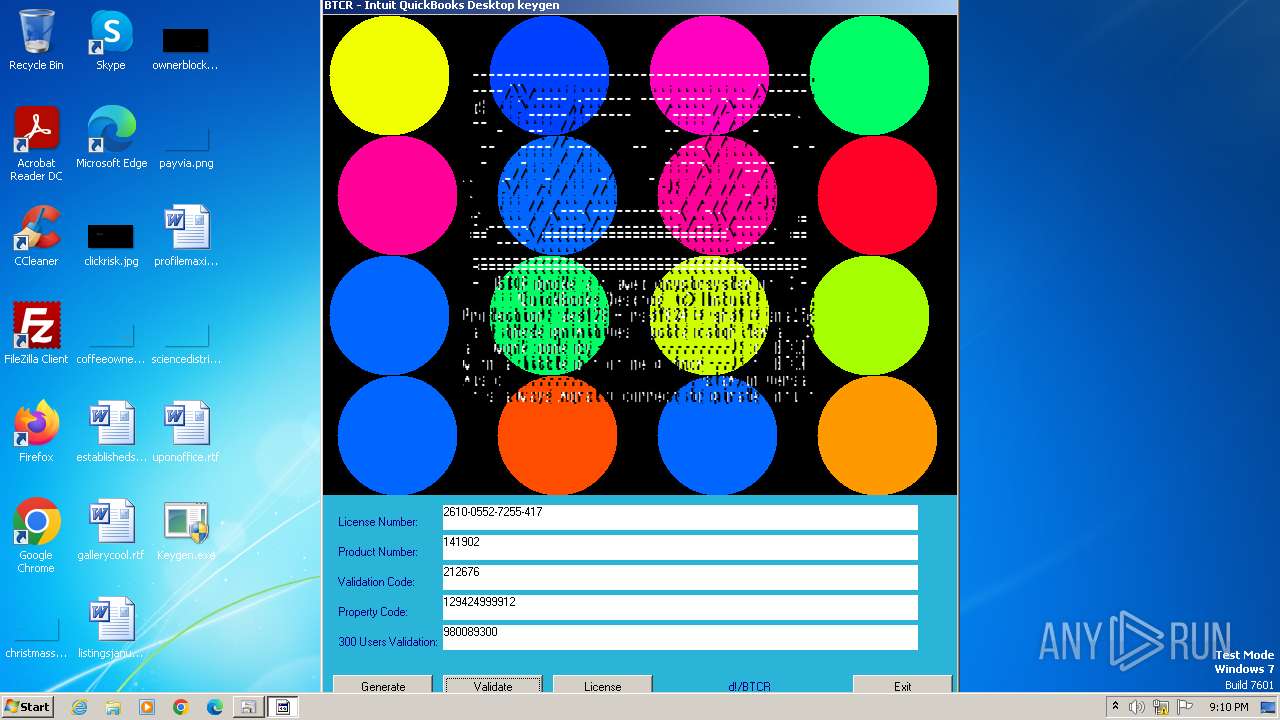
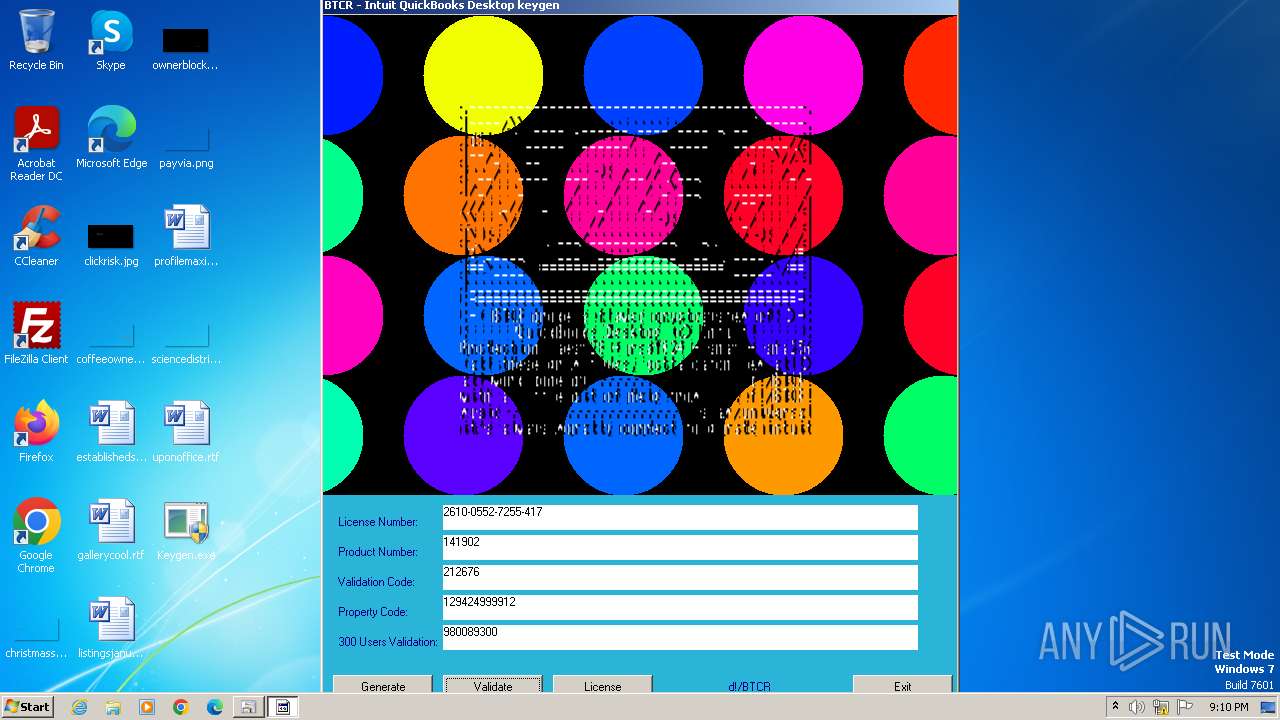
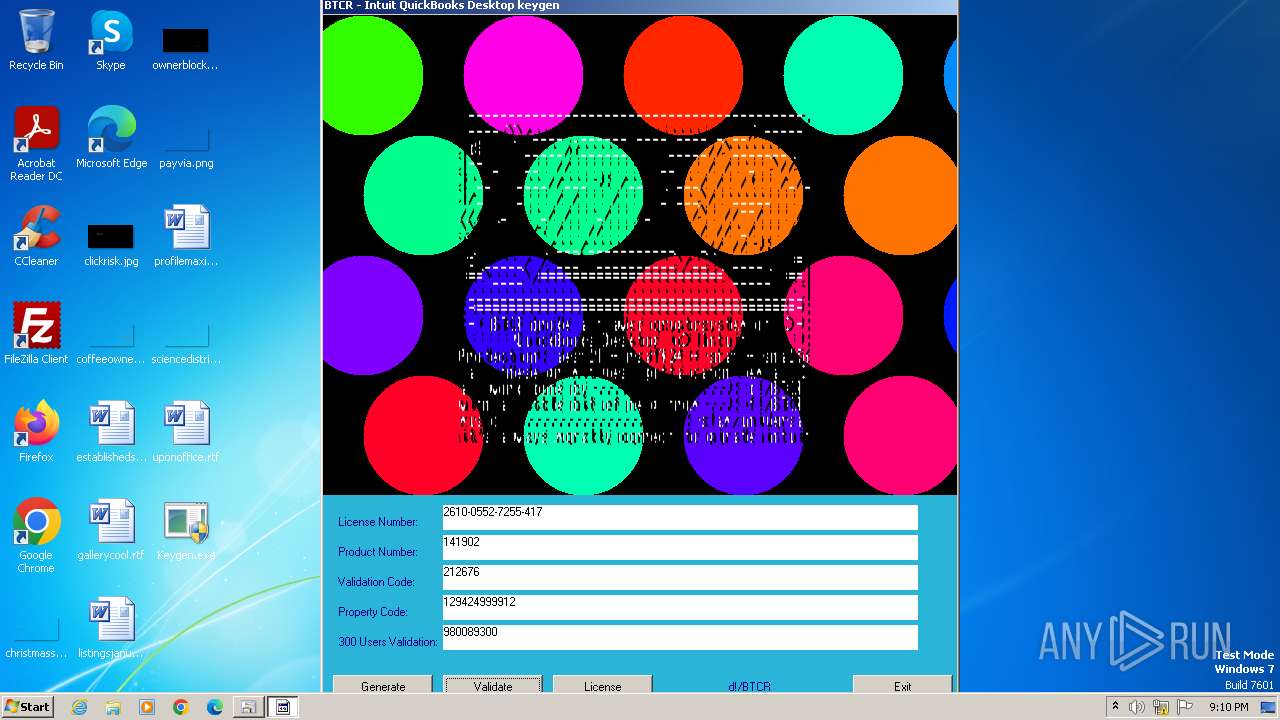
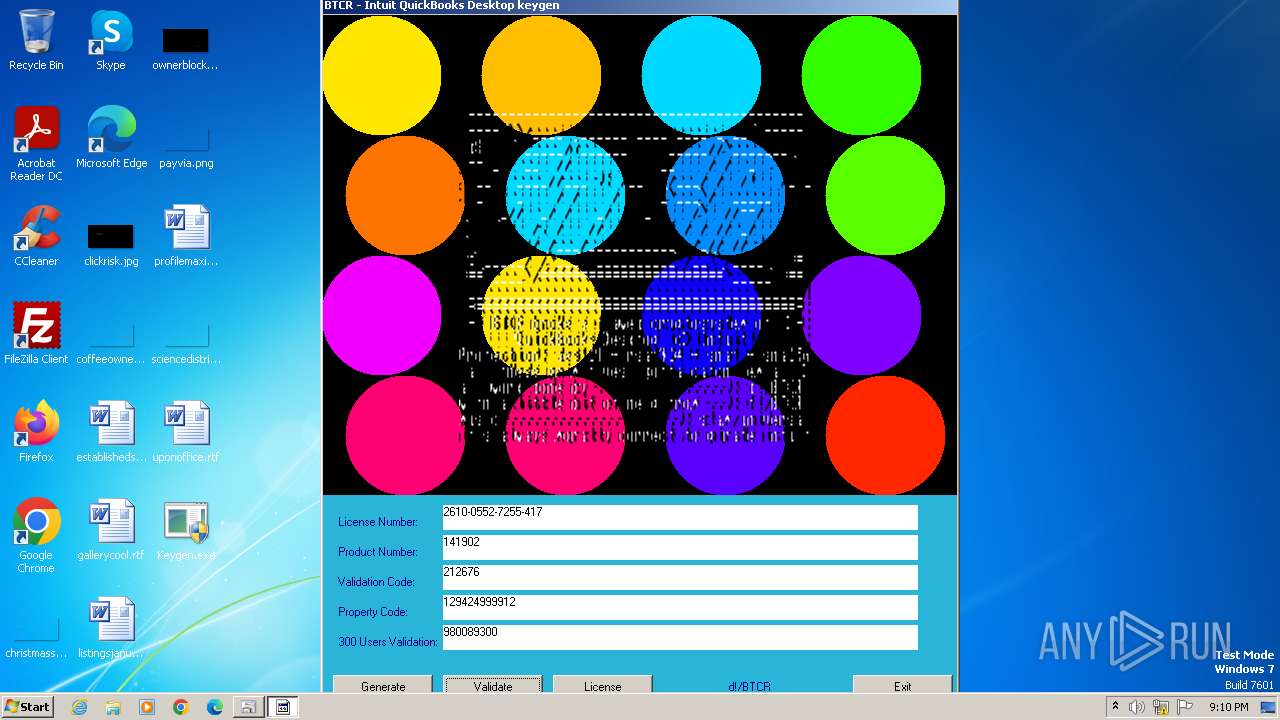
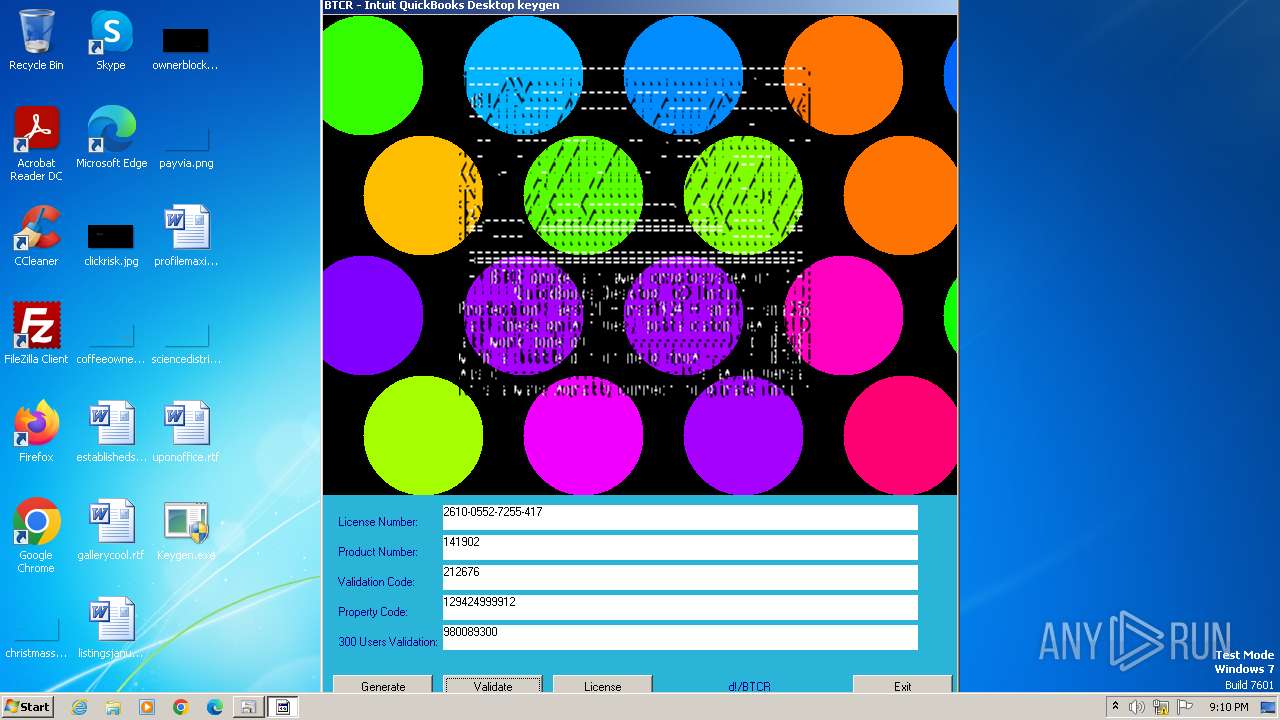
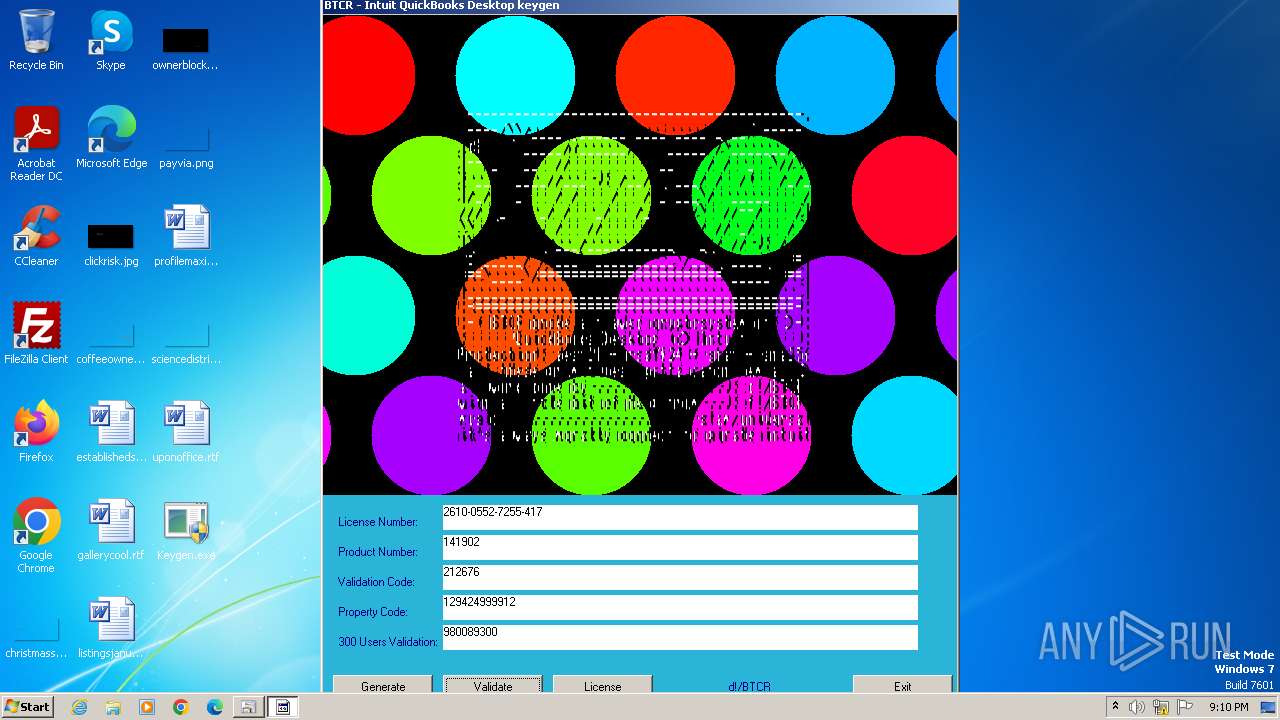
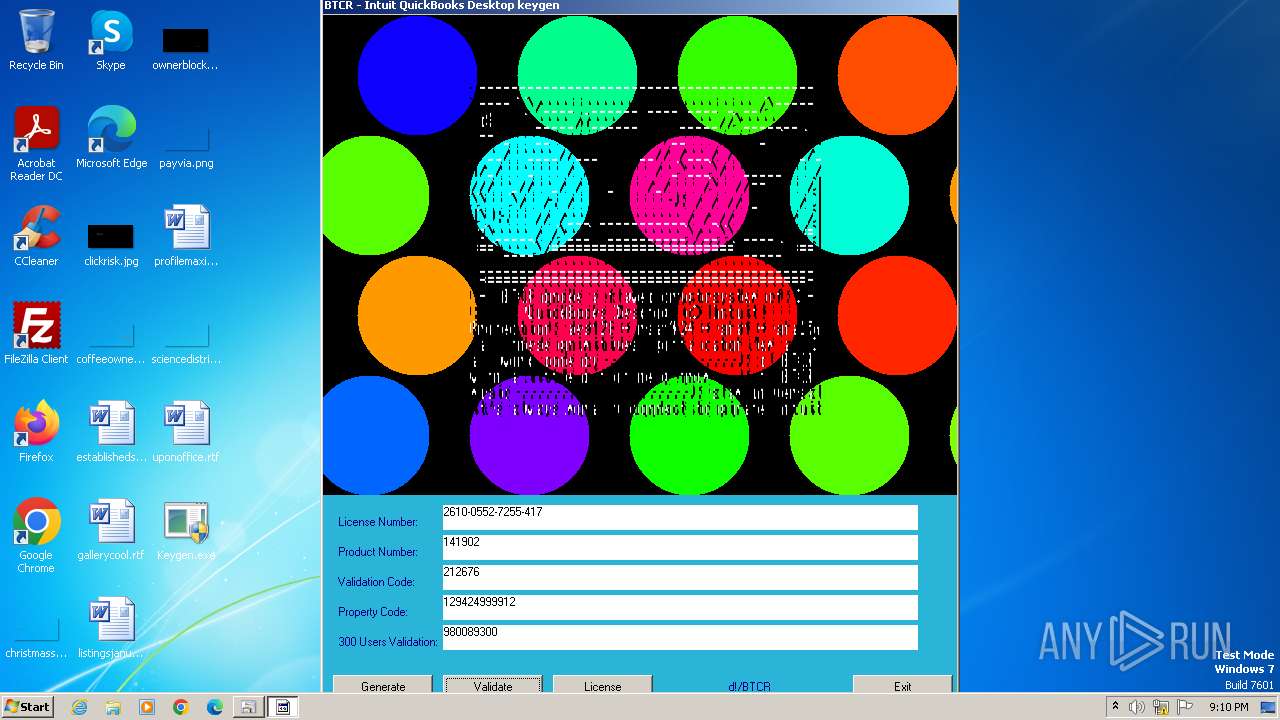
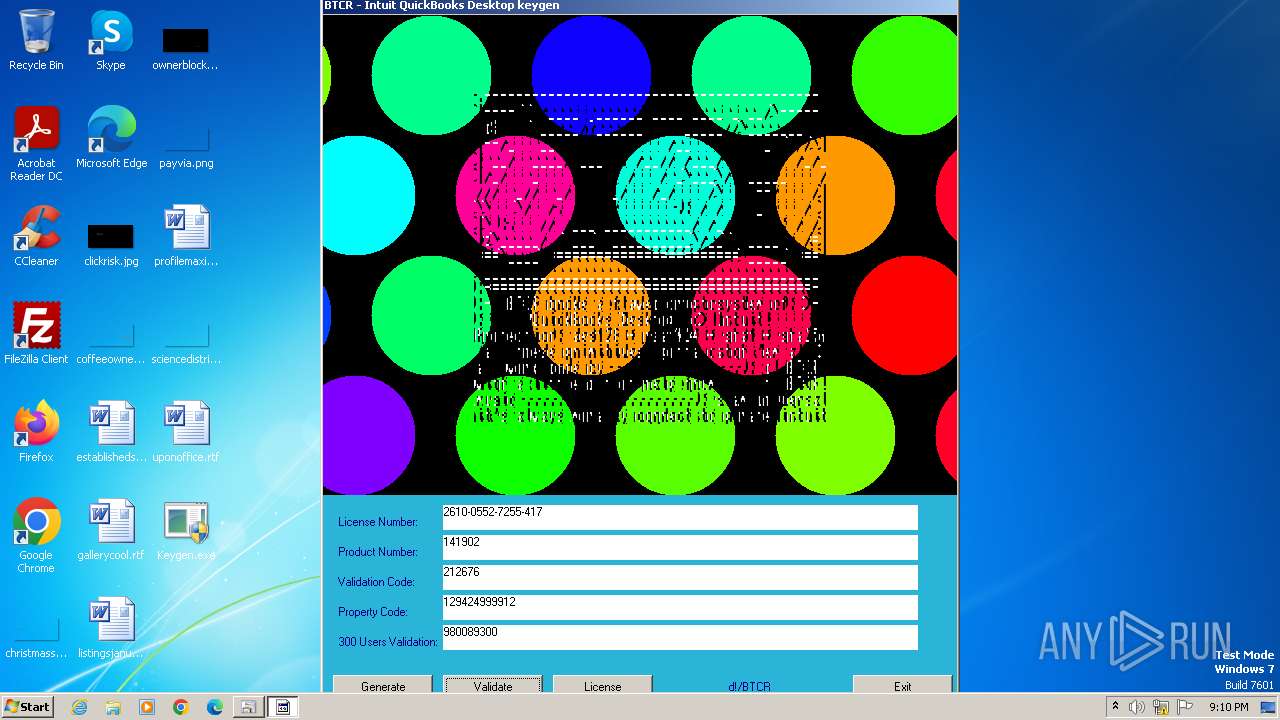
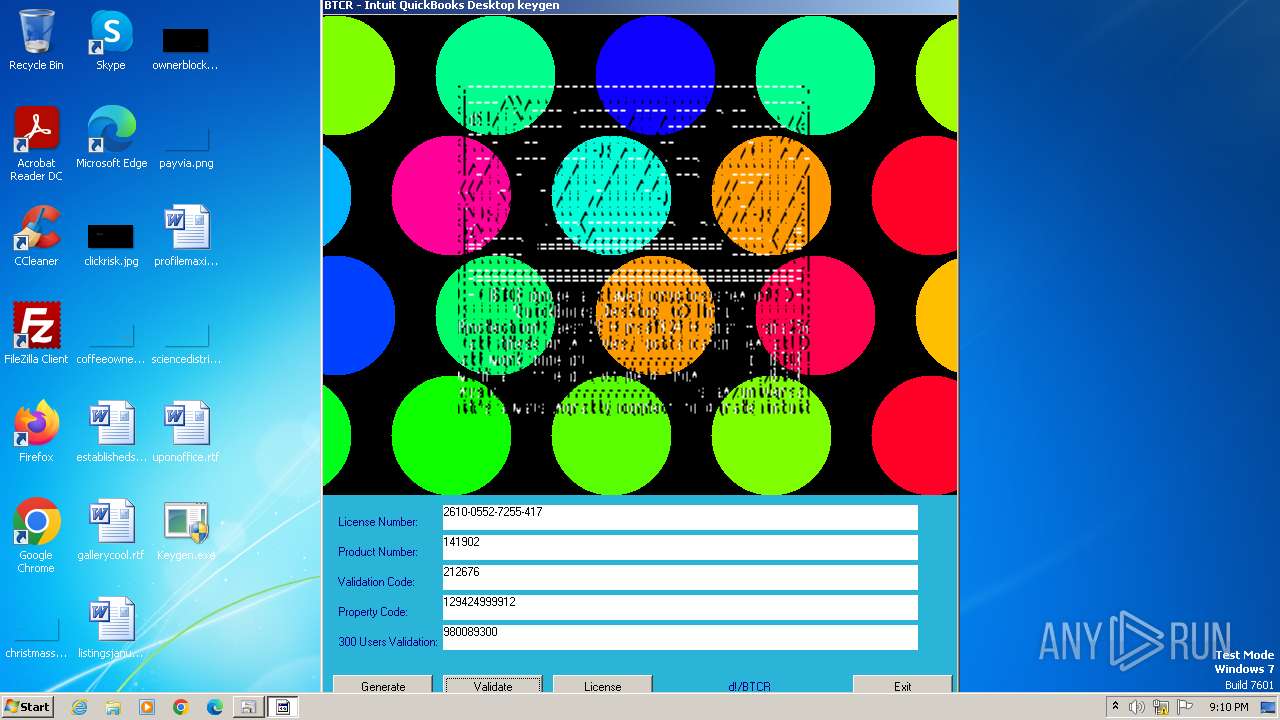
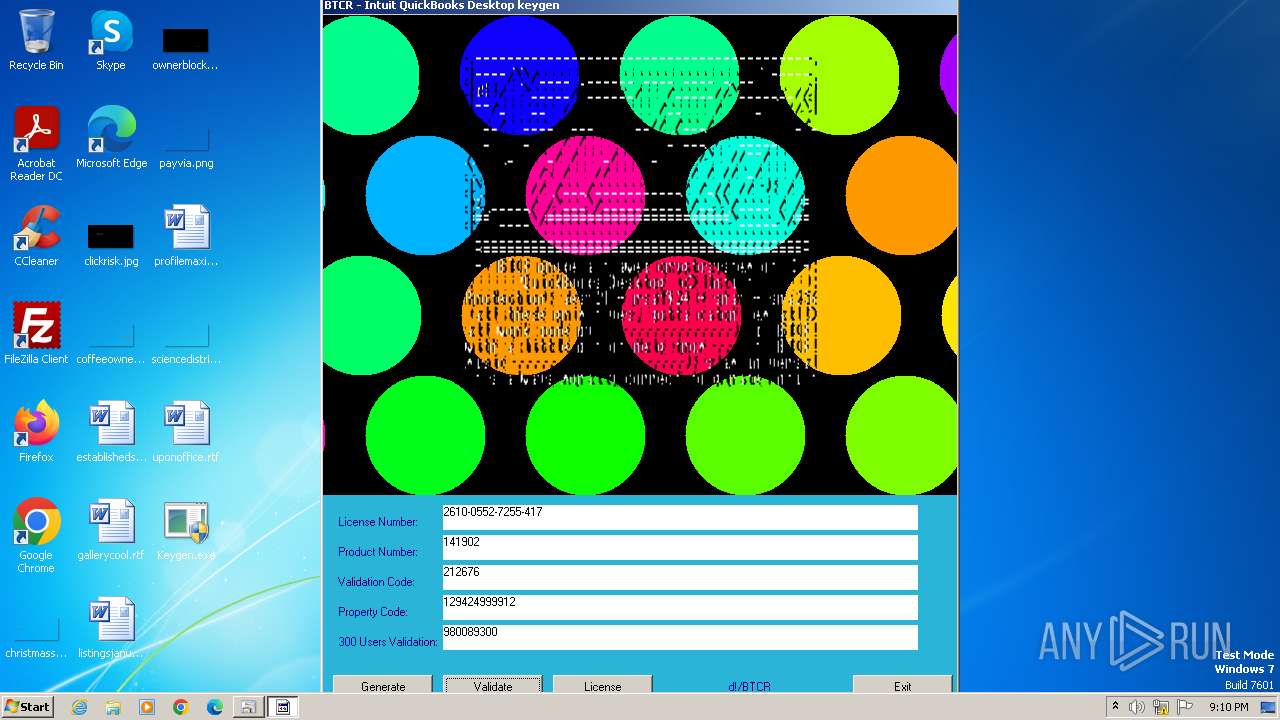
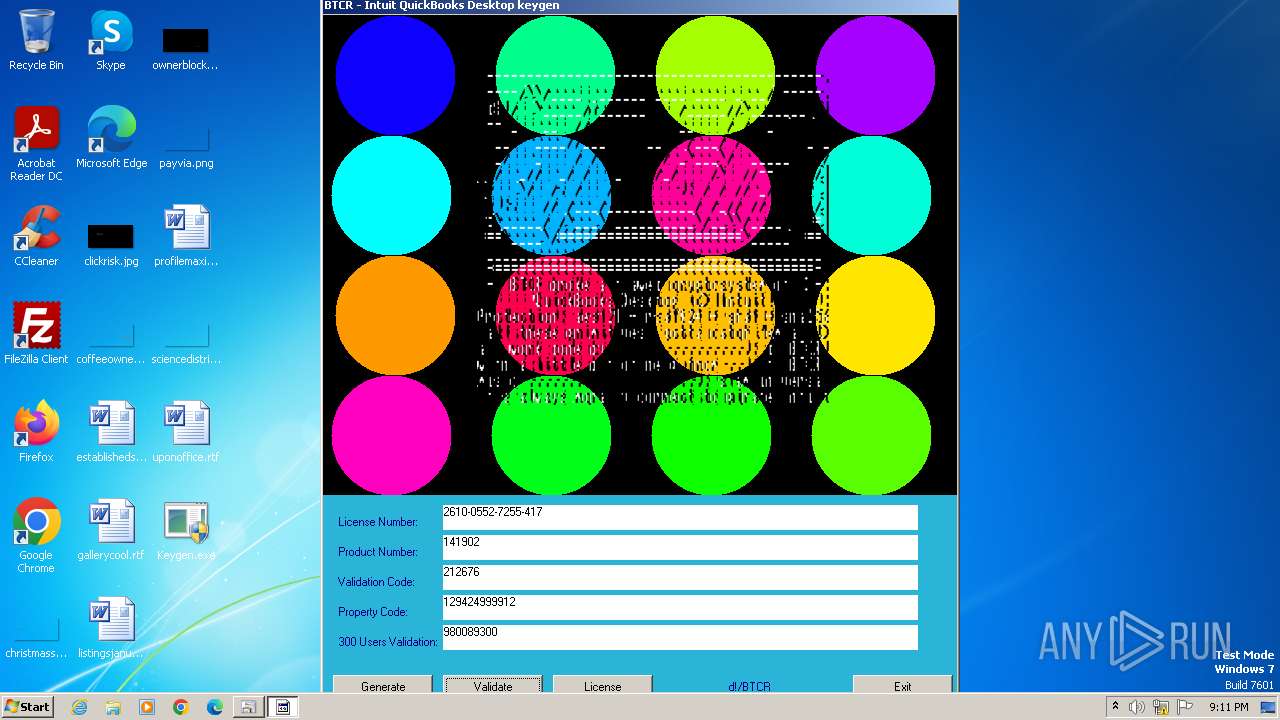
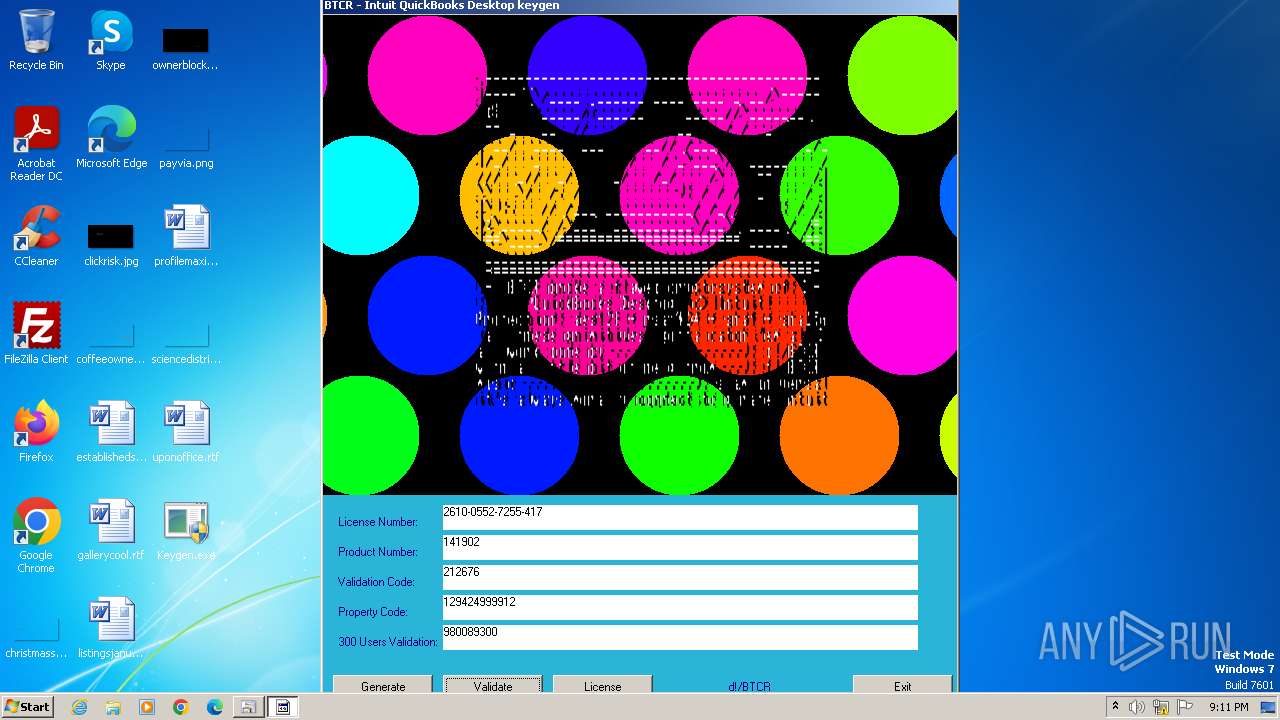
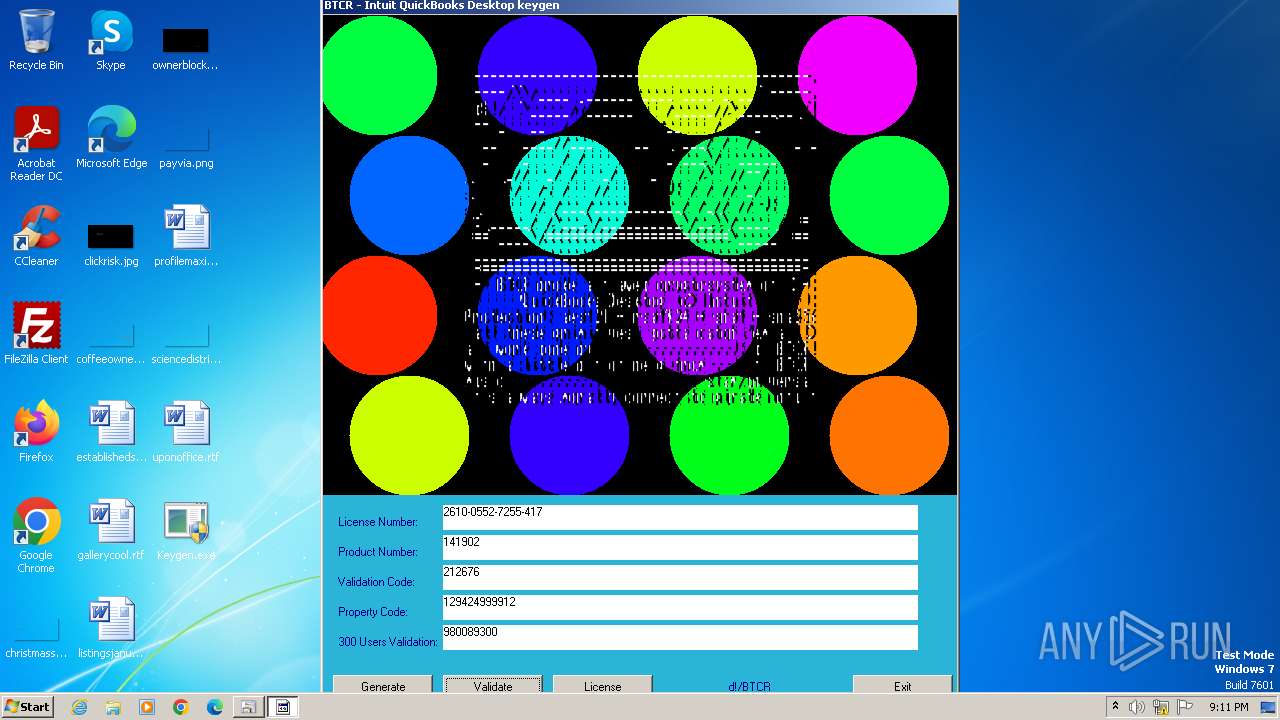
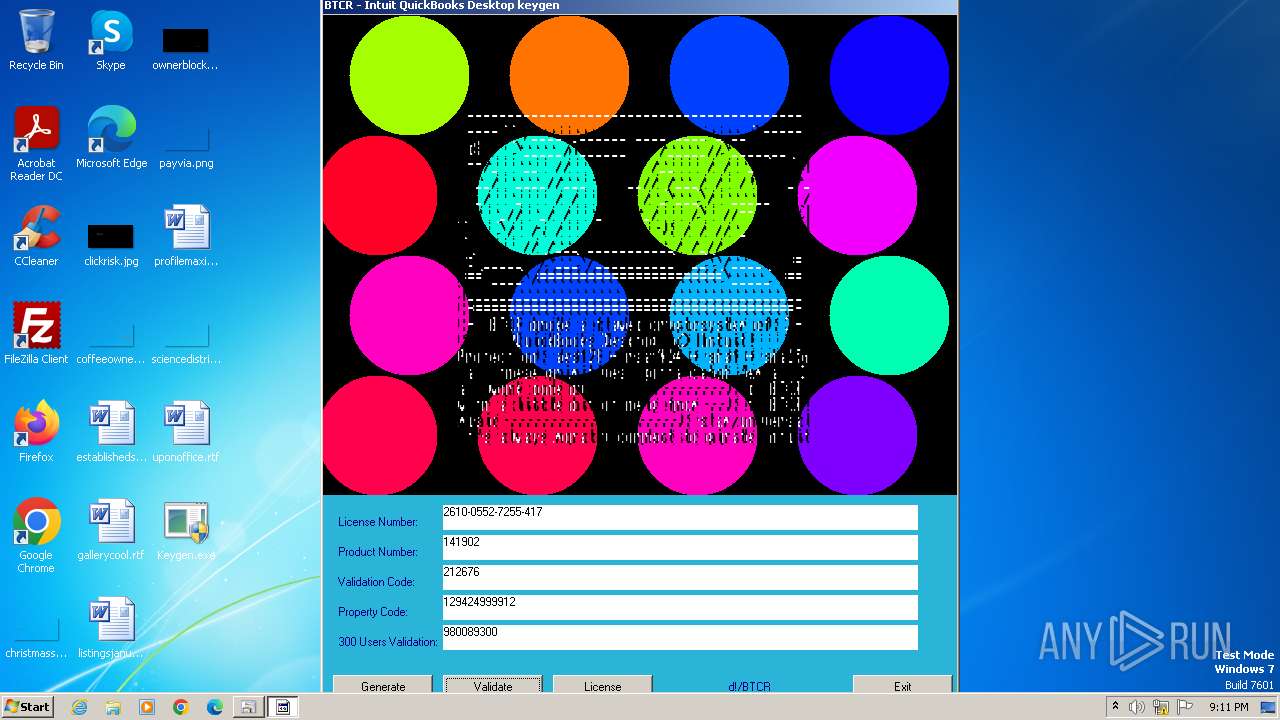
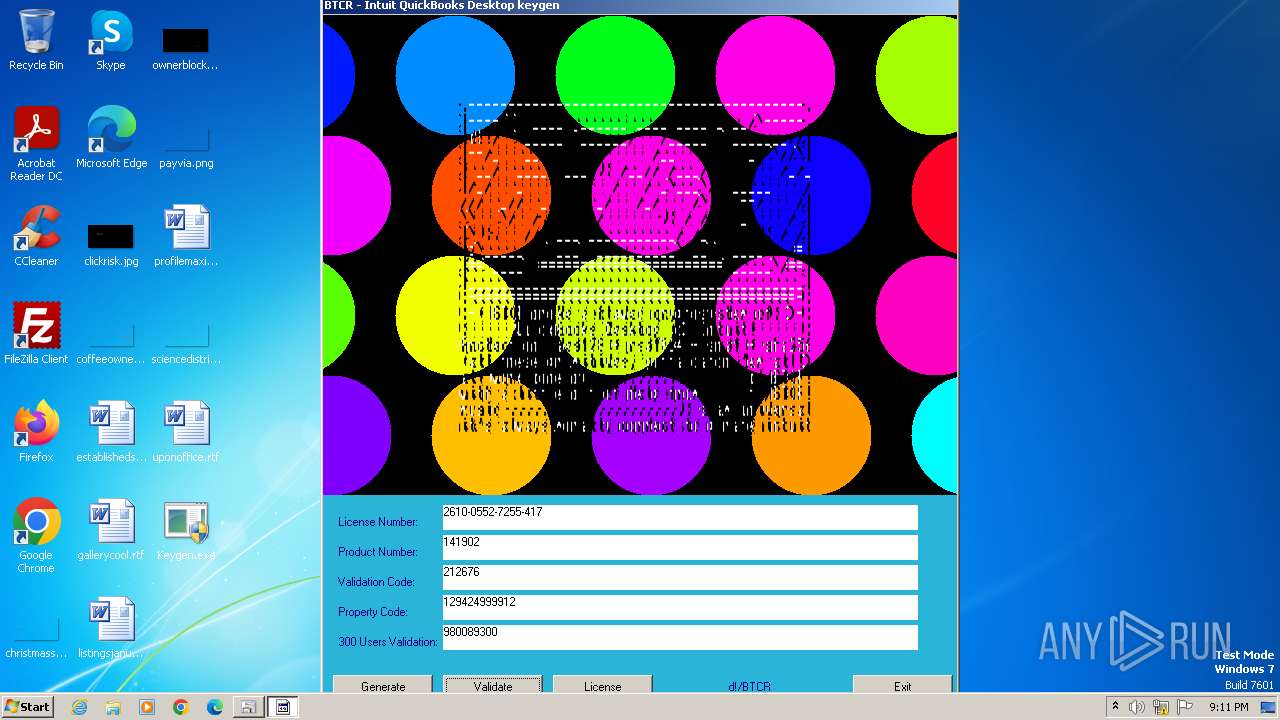
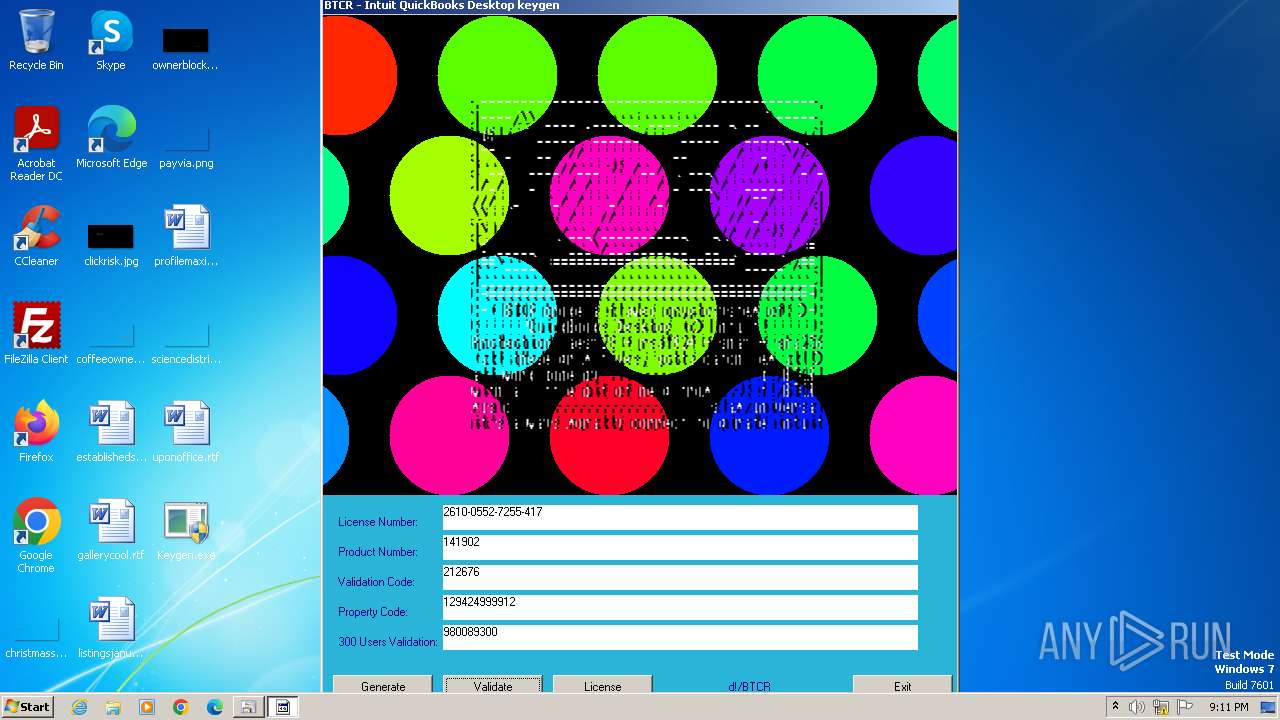
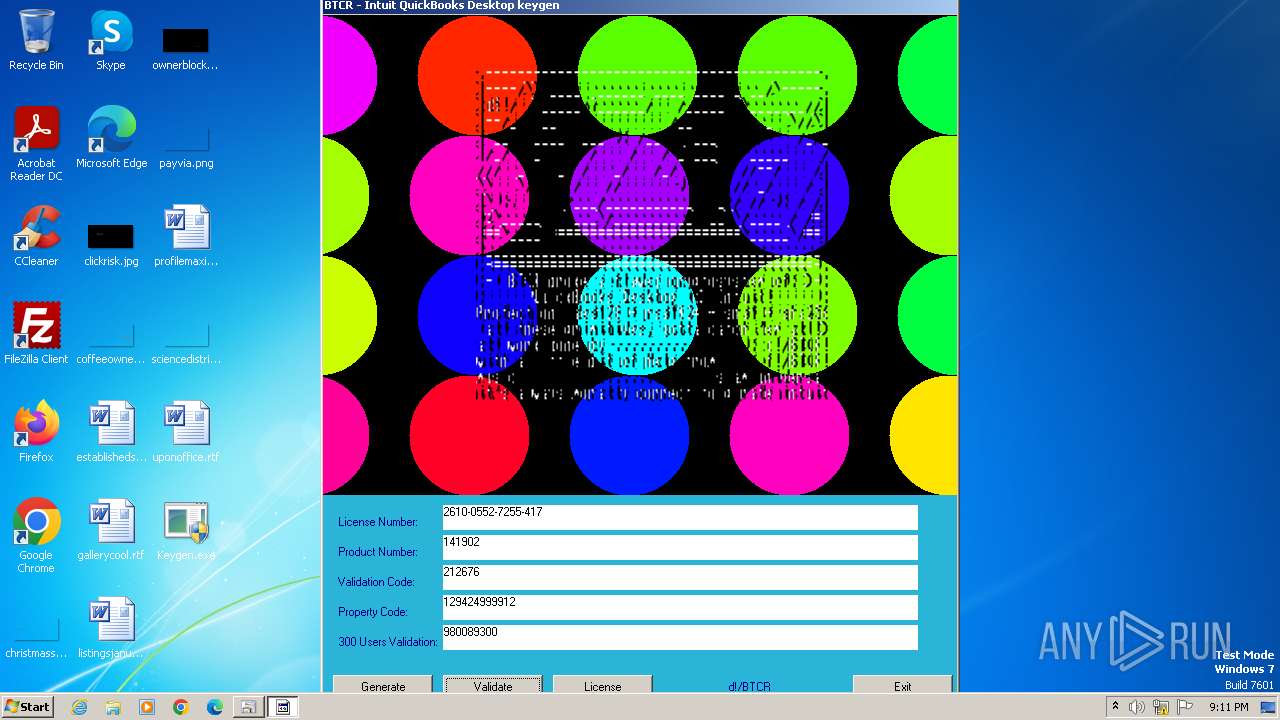
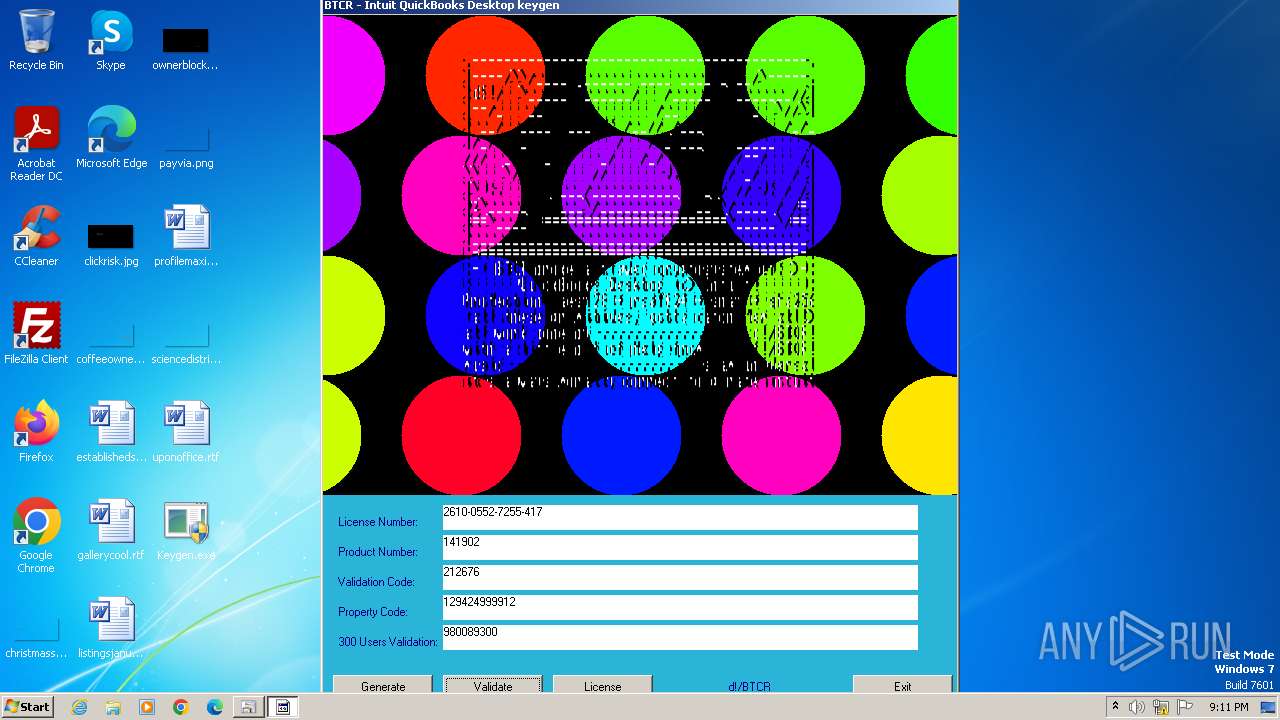
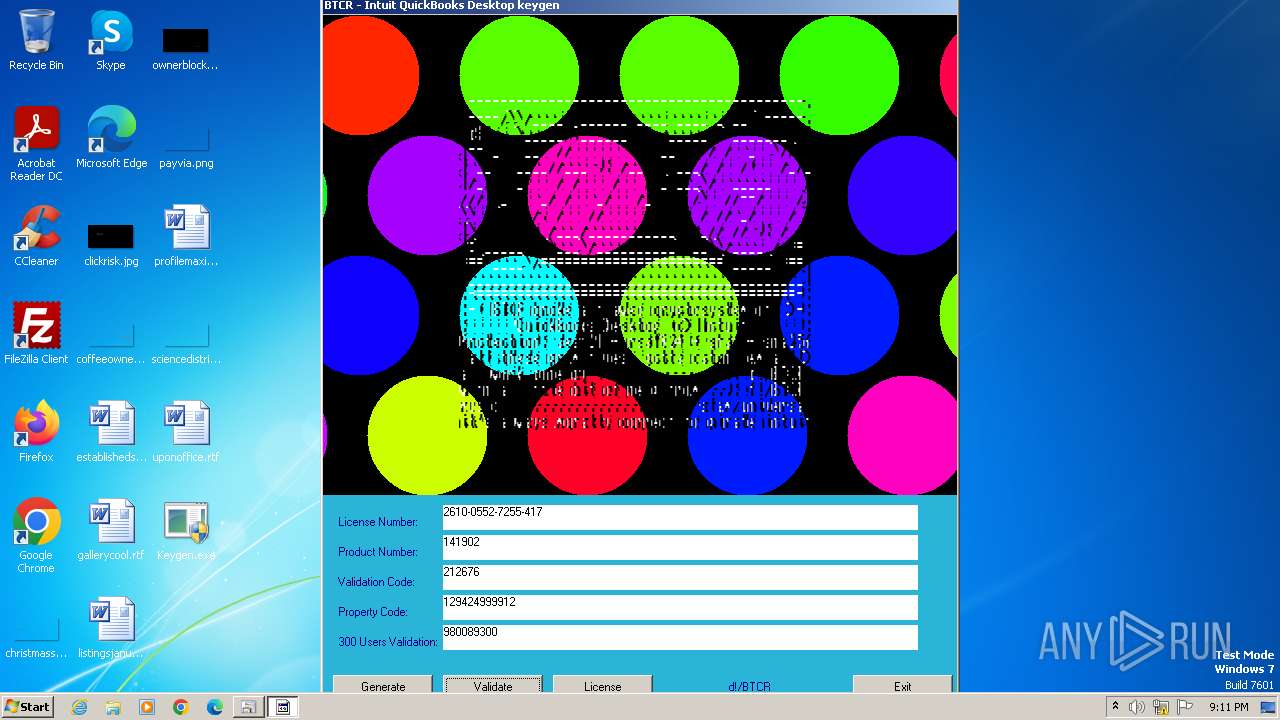
| File name: | Keygen.exe |
| Full analysis: | https://app.any.run/tasks/562f337b-092f-4b0b-b85c-fb1564e354d5 |
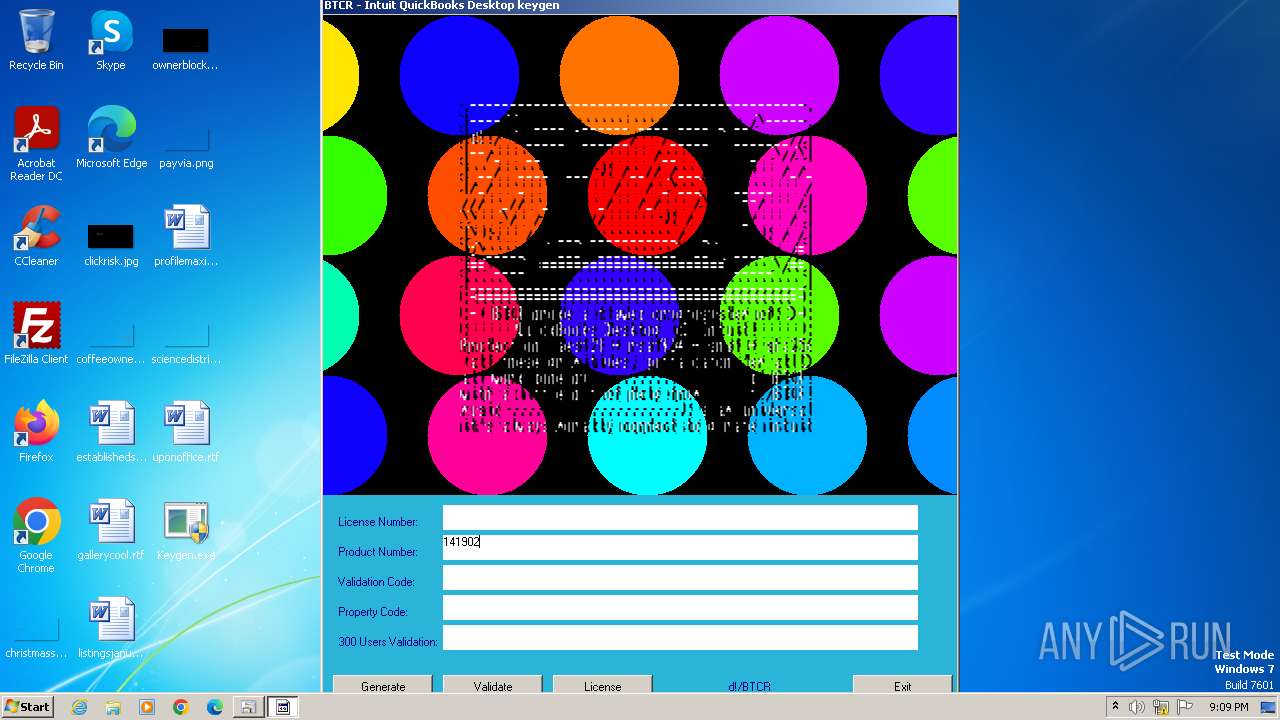
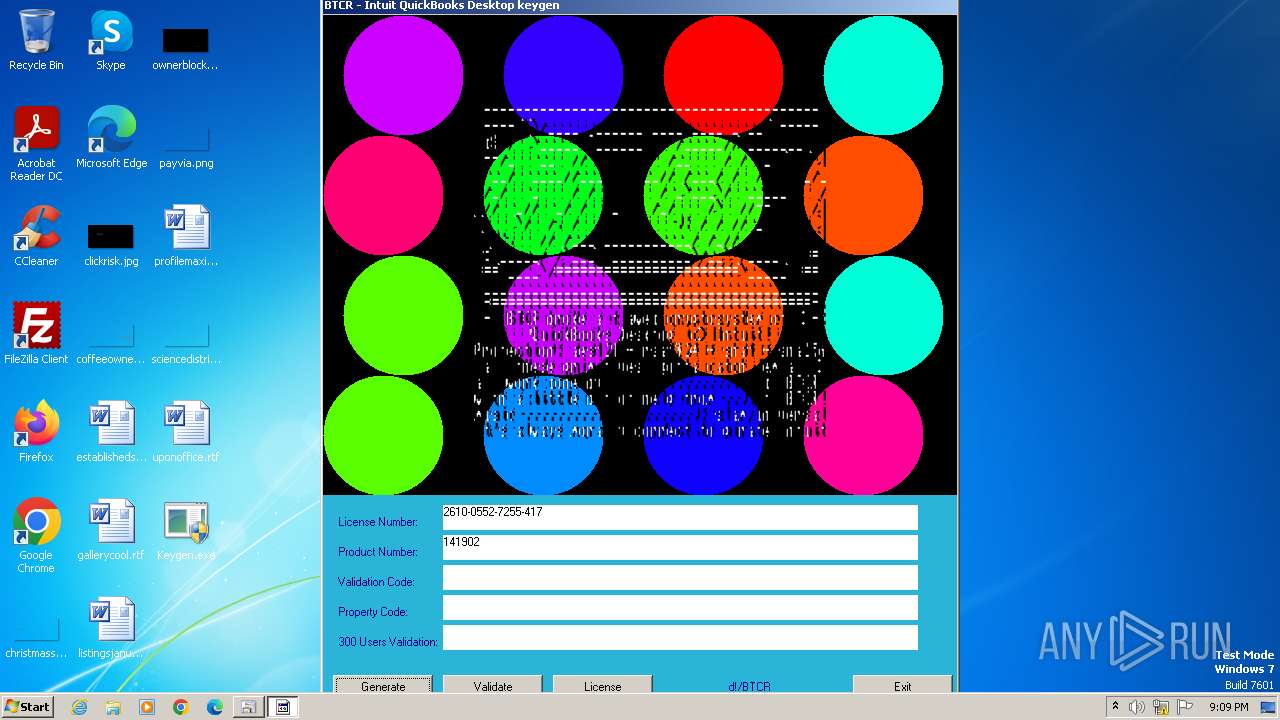
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2024, 20:08:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3767F52976D8AF98E05625F8D7FC83B8 |
| SHA1: | 1A4C9314F584646EB3633B26315653C4095C86DA |
| SHA256: | EB282DAB6AE17CBF0AF3ADED26E2B5337B9E9DA3F6882A9E107ED2BA00948053 |
| SSDEEP: | 24576:4OILwCiRu52XOx6R5+ZxY3H5XrCiVtMKzm2y6ZQ+2Kvxst:4OmzZxQH5bdVtMqmqy+2KvOt |
MALICIOUS
Drops the executable file immediately after the start
- Keygen.exe (PID: 1020)
- csc.exe (PID: 1792)
- csc.exe (PID: 1788)
- csc.exe (PID: 2276)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 1284)
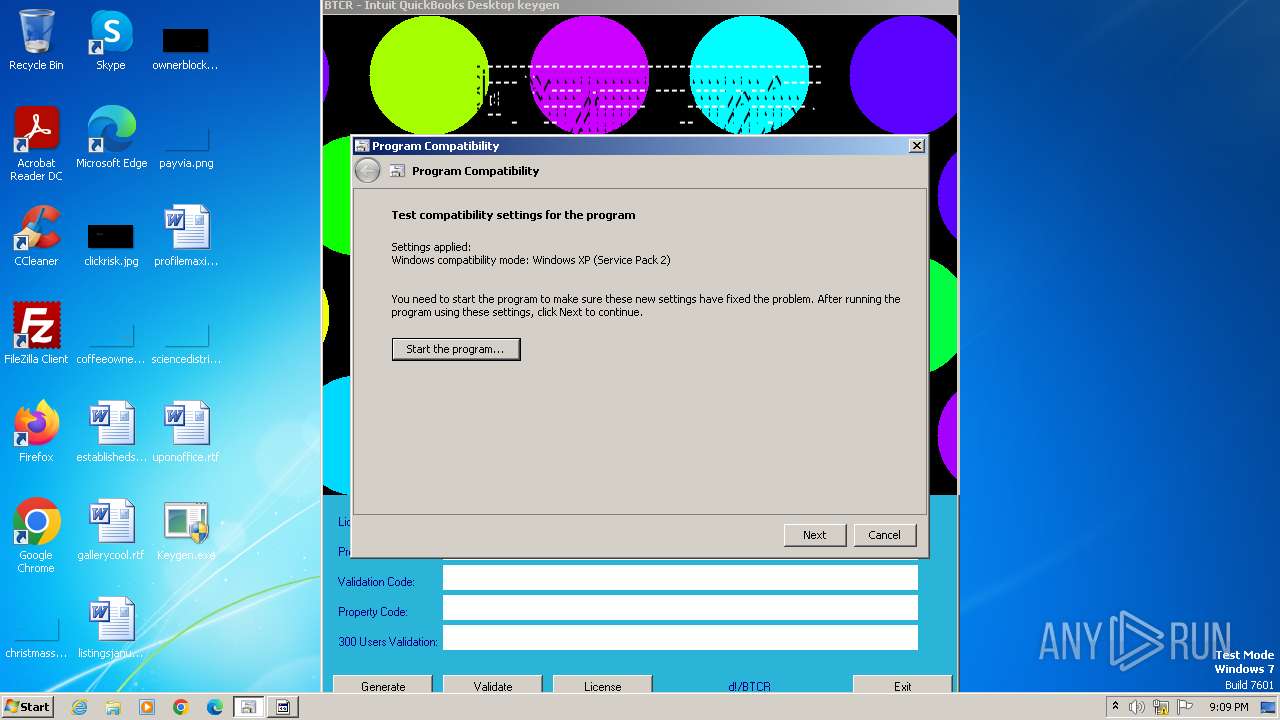
SUSPICIOUS
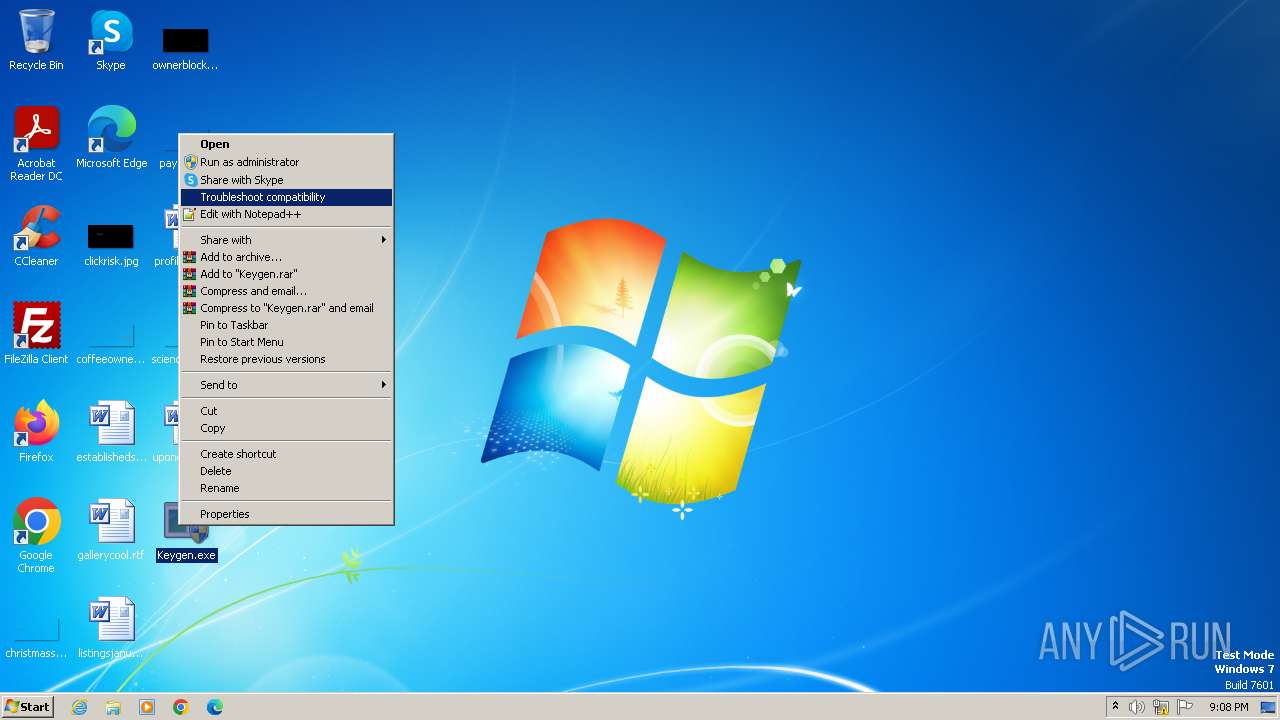
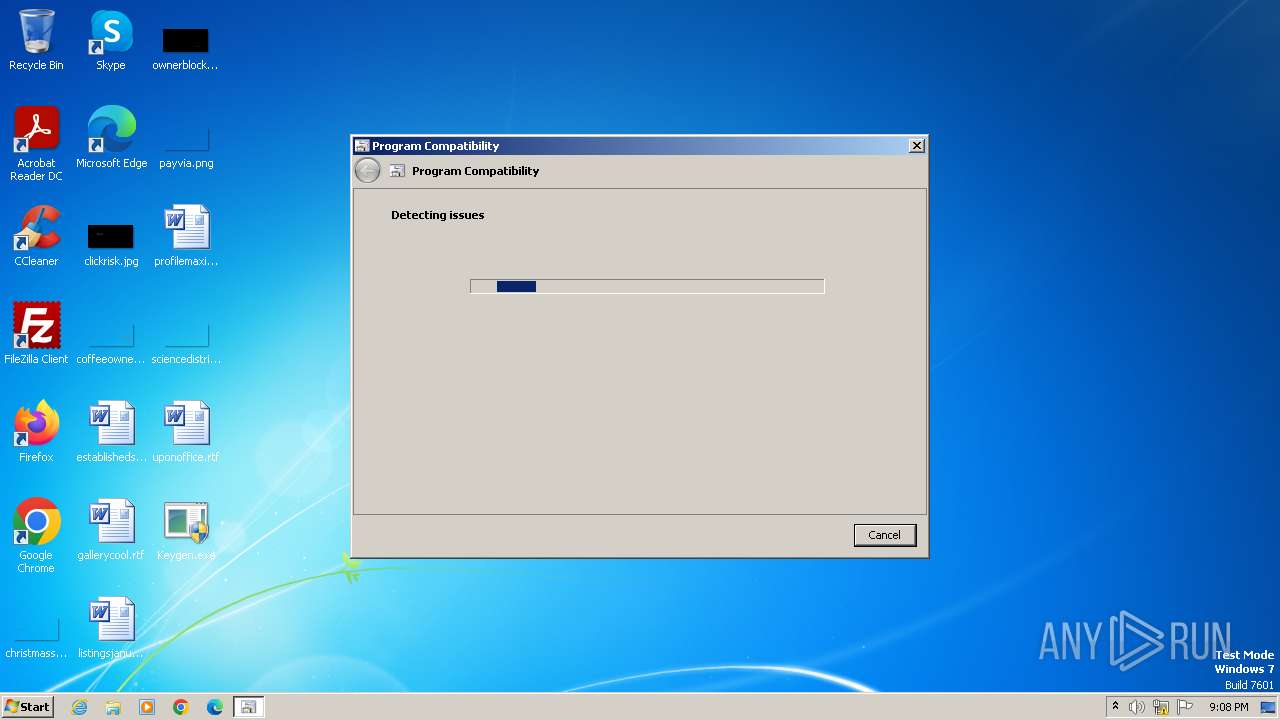
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 616)
Reads the Internet Settings
- sdiagnhost.exe (PID: 1284)
- msdt.exe (PID: 692)
Executable content was dropped or overwritten
- csc.exe (PID: 1792)
- csc.exe (PID: 1788)
- csc.exe (PID: 2276)
Uses RUNDLL32.EXE to load library
- msdt.exe (PID: 692)
The process executes via Task Scheduler
- Keygen.exe (PID: 2520)
- Keygen.exe (PID: 1596)
Uses .NET C# to load dll
- sdiagnhost.exe (PID: 1284)
INFO
Checks supported languages
- Keygen.exe (PID: 1020)
- cvtres.exe (PID: 1812)
- csc.exe (PID: 1788)
- cvtres.exe (PID: 1552)
- csc.exe (PID: 2276)
- cvtres.exe (PID: 2284)
- Keygen.exe (PID: 2520)
- csc.exe (PID: 1792)
Create files in a temporary directory
- csc.exe (PID: 1792)
- pcwrun.exe (PID: 616)
- msdt.exe (PID: 692)
- sdiagnhost.exe (PID: 1284)
- csc.exe (PID: 1788)
- cvtres.exe (PID: 1812)
- csc.exe (PID: 2276)
- cvtres.exe (PID: 1552)
- cvtres.exe (PID: 2284)
Reads the computer name
- Keygen.exe (PID: 1020)
- Keygen.exe (PID: 2520)
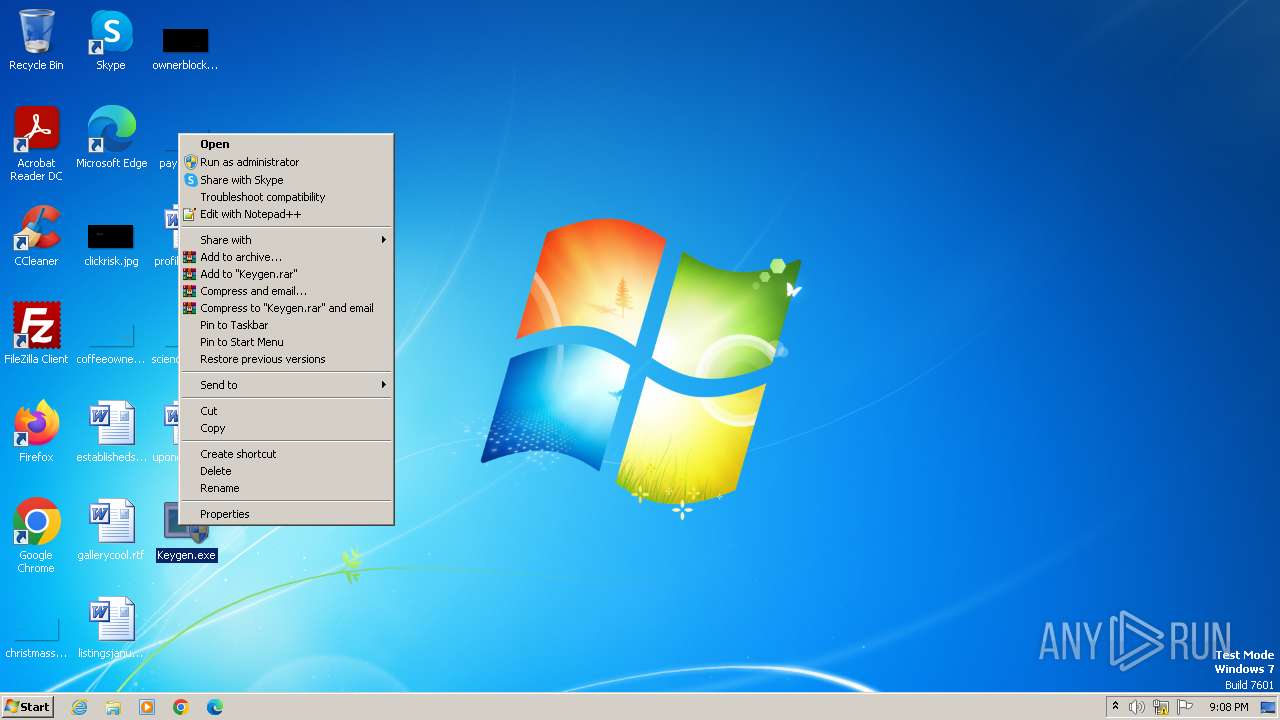
Manual execution by a user
- pcwrun.exe (PID: 616)
Drops the executable file immediately after the start
- msdt.exe (PID: 692)
Reads security settings of Internet Explorer
- msdt.exe (PID: 692)
- sdiagnhost.exe (PID: 1284)
Reads the machine GUID from the registry
- cvtres.exe (PID: 1812)
- csc.exe (PID: 1788)
- cvtres.exe (PID: 1552)
- cvtres.exe (PID: 2284)
- csc.exe (PID: 2276)
- csc.exe (PID: 1792)
Reads the software policy settings
- msdt.exe (PID: 692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:01:30 20:50:51+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.34 |
| CodeSize: | 399872 |
| InitializedDataSize: | 979968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b89 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
56
Monitored processes
14
Malicious processes
1
Suspicious processes
0
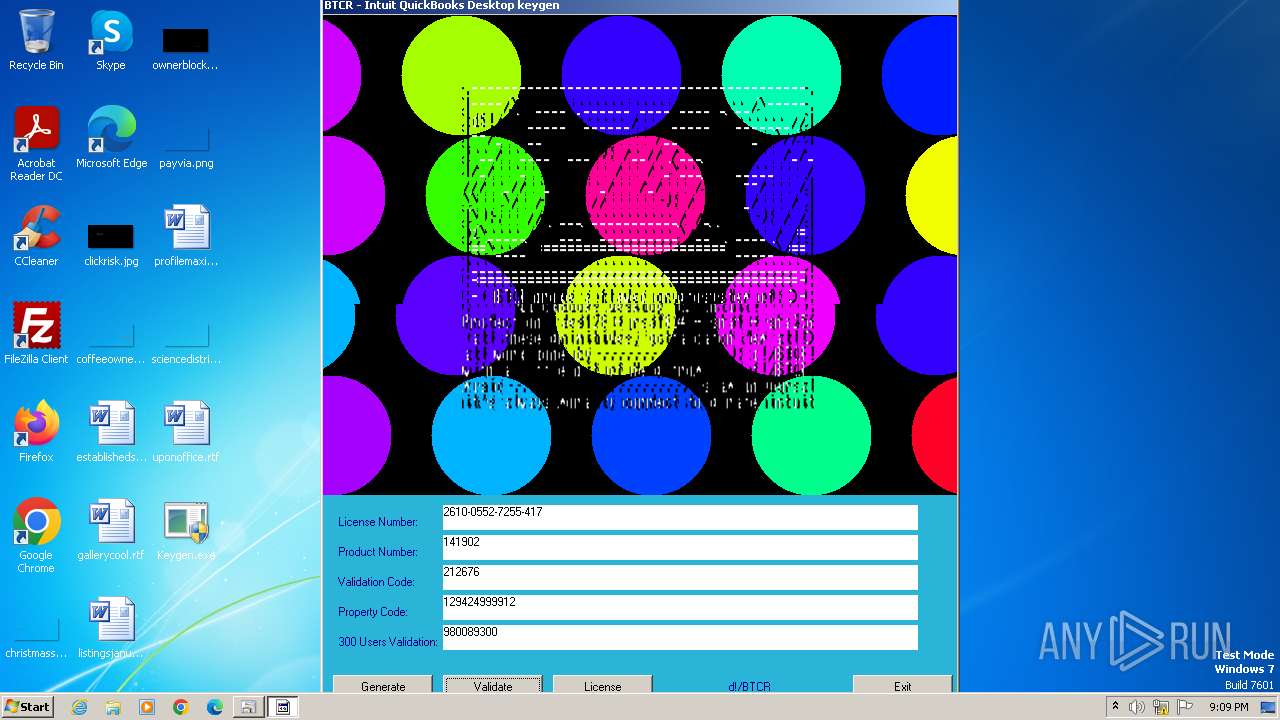
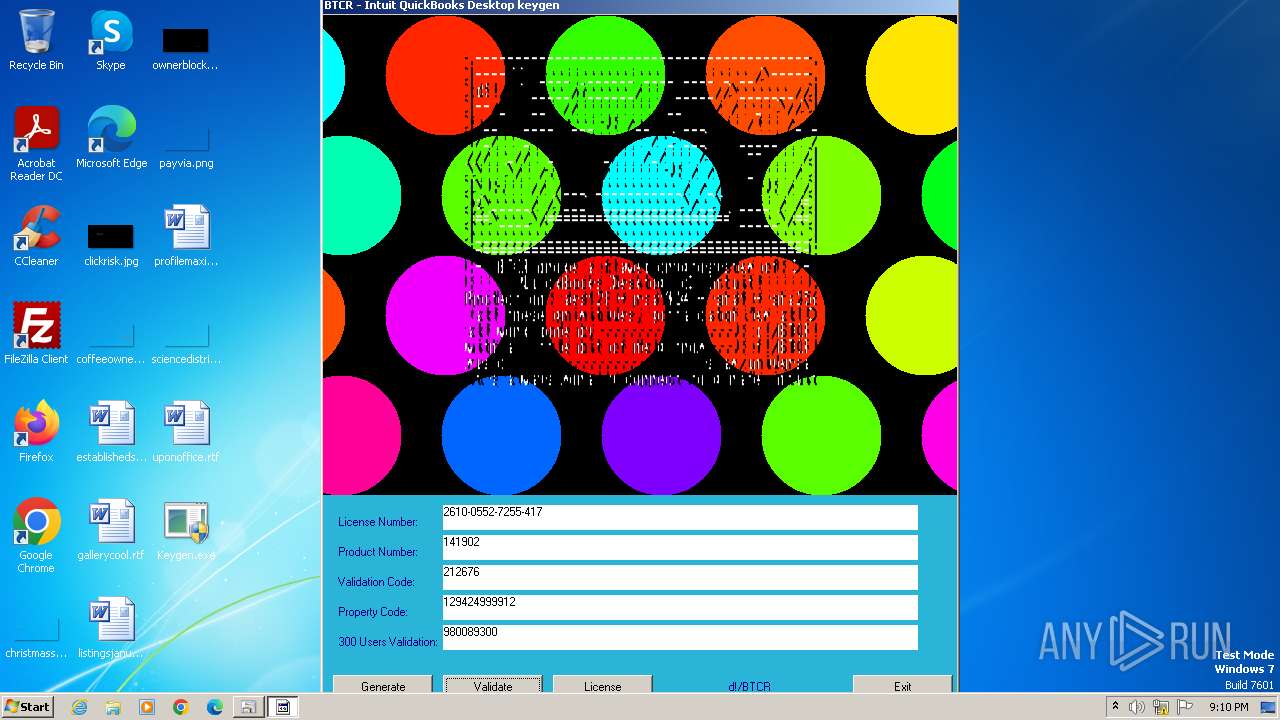
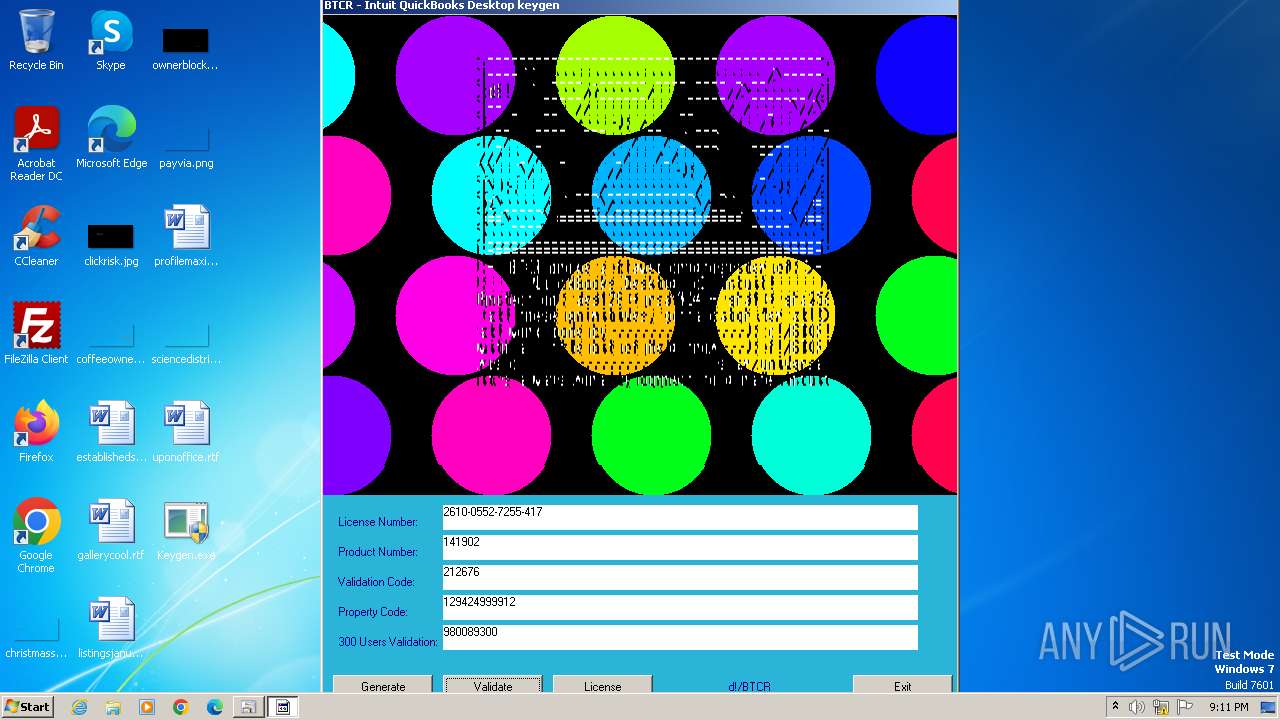
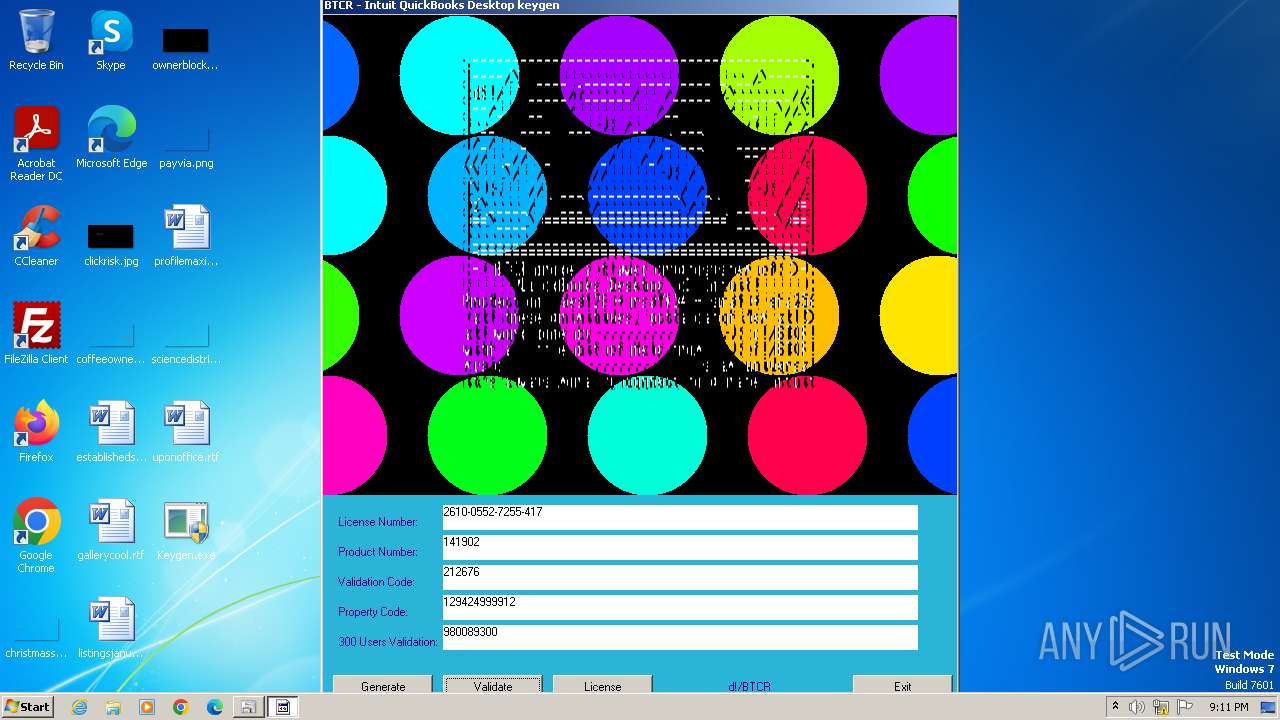
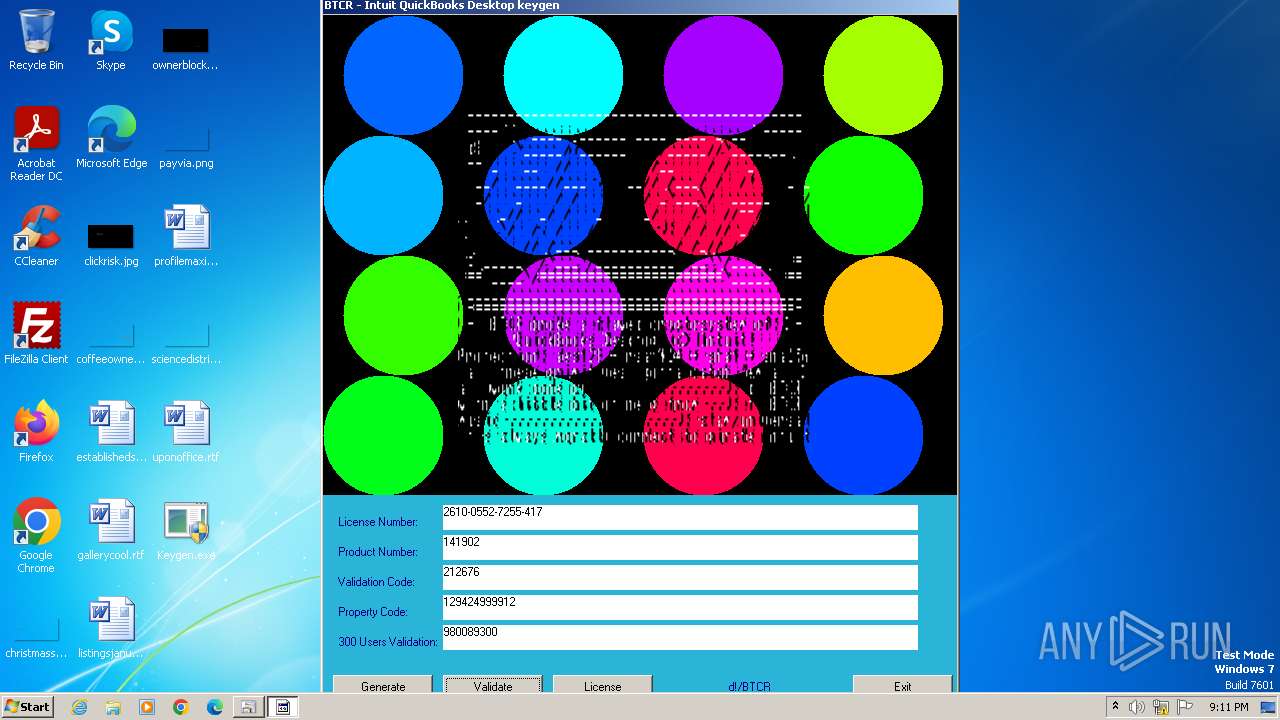
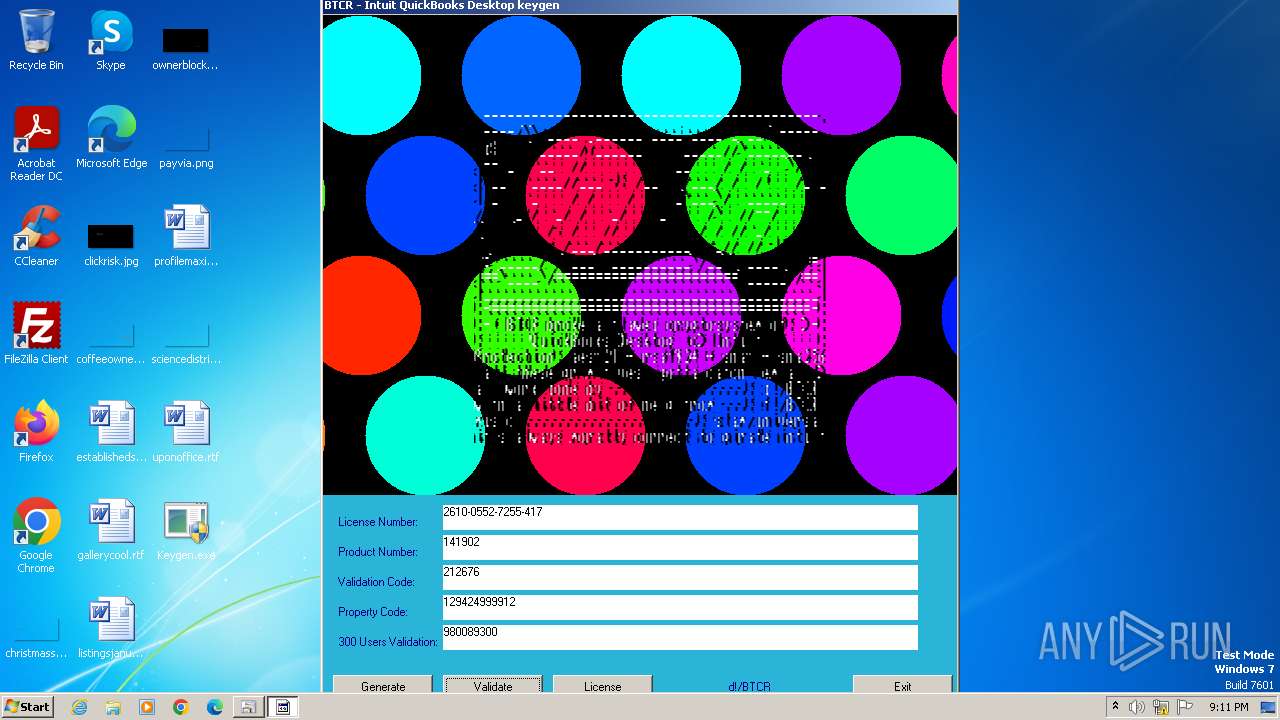
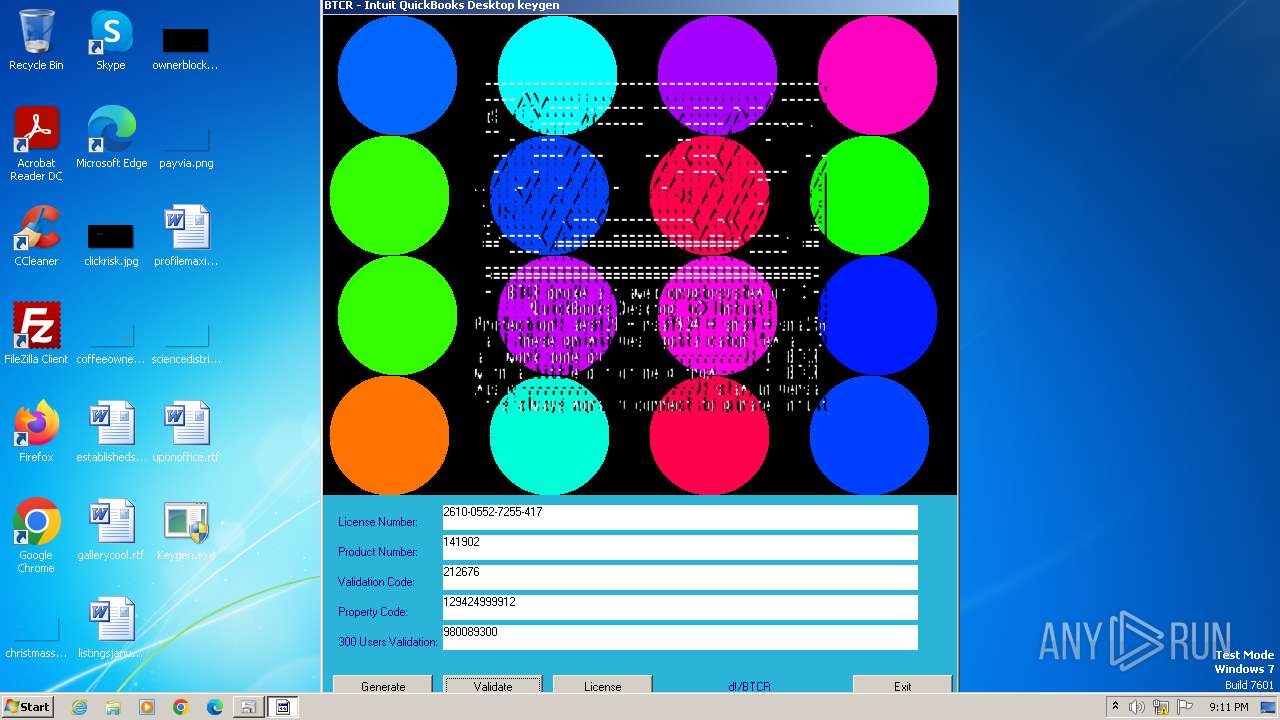
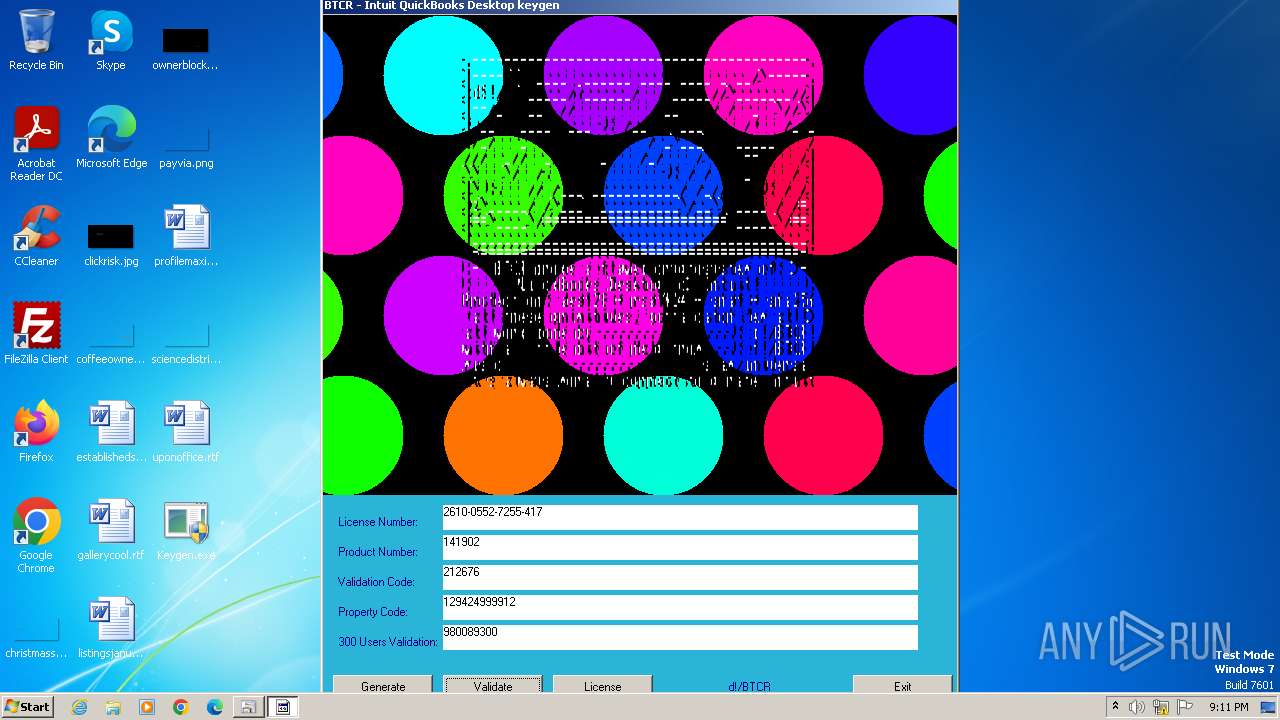
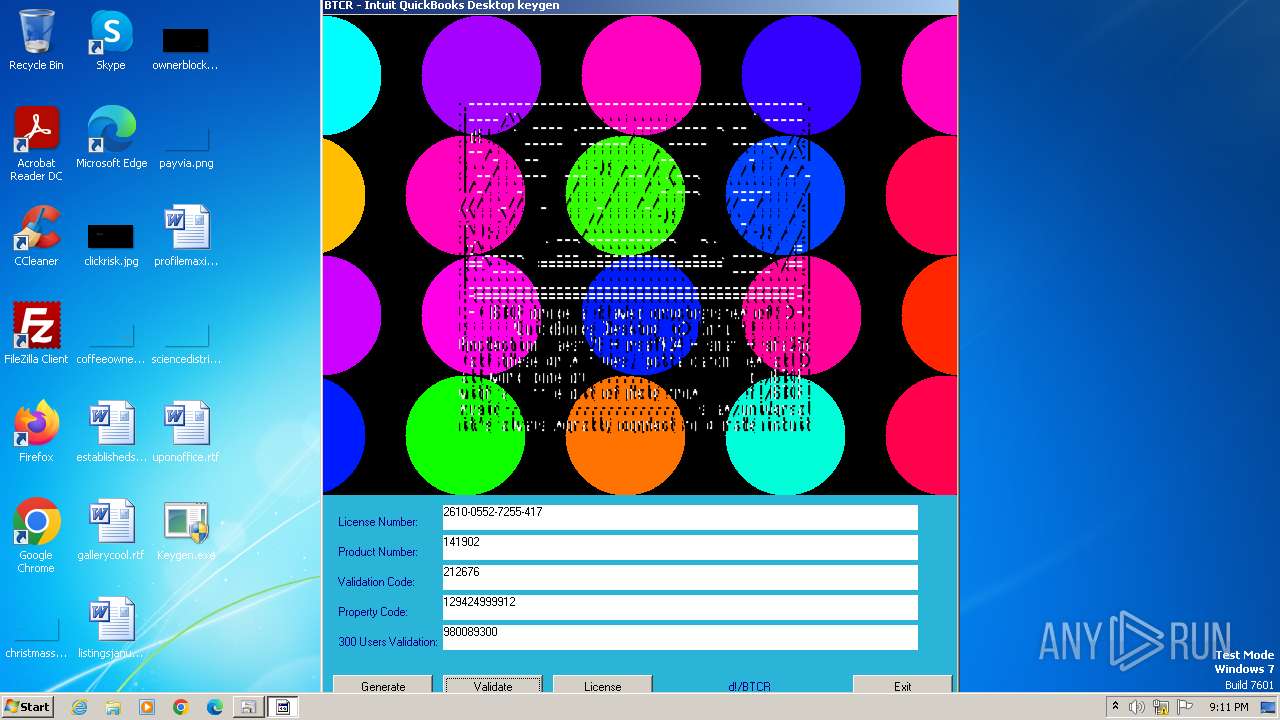
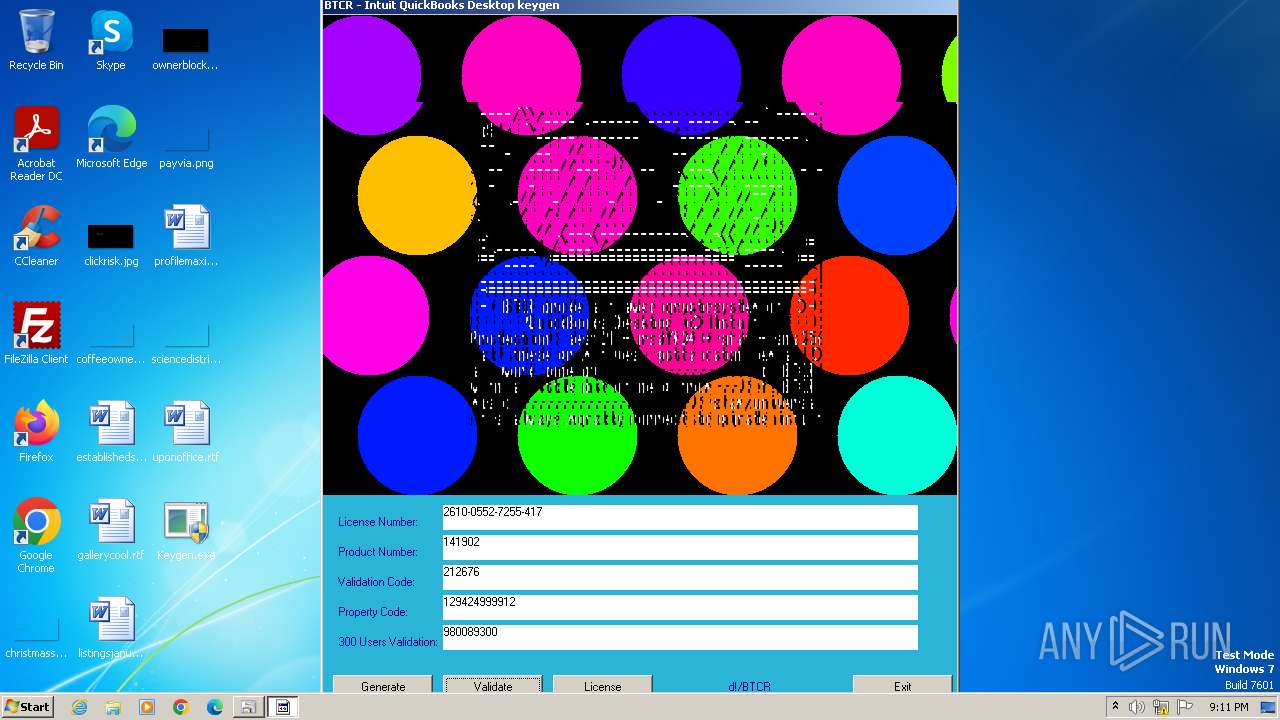
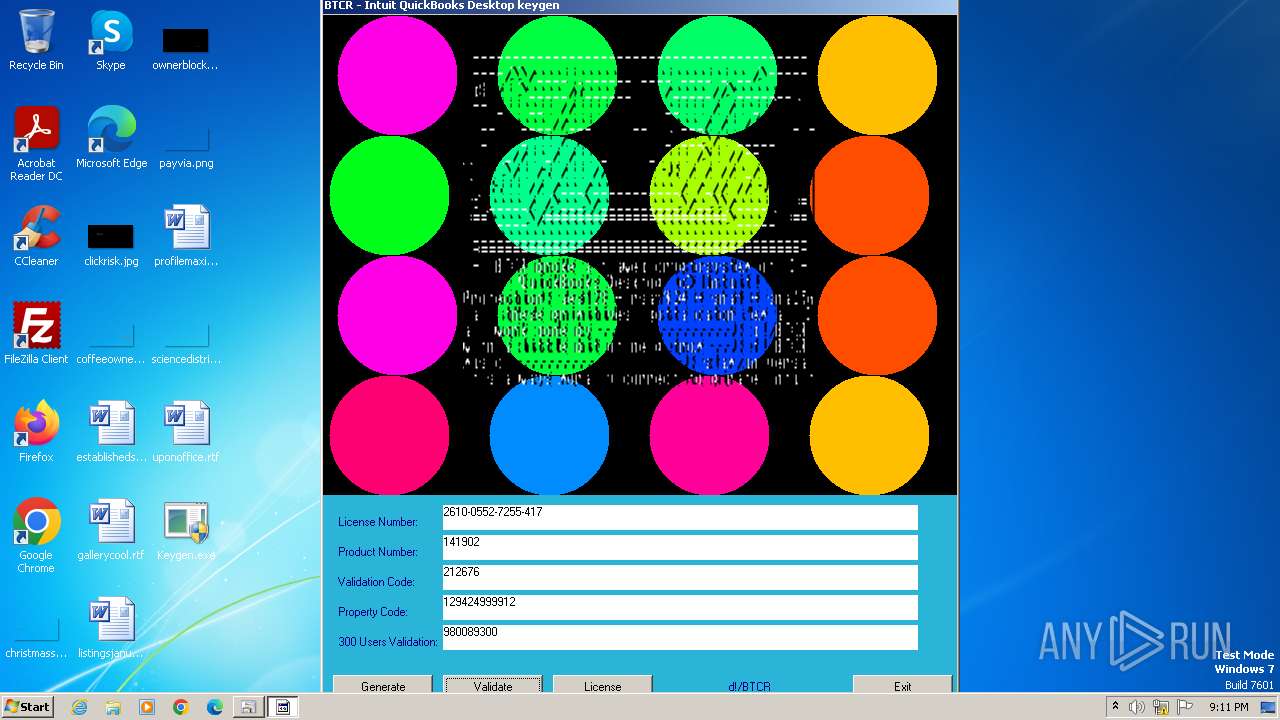
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | C:\Windows\system32\pcwrun.exe "C:\Users\admin\Desktop\Keygen.exe" | C:\Windows\System32\pcwrun.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | C:\Windows\System32\msdt.exe -path C:\Windows\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCW691C.xml /skip TRUE | C:\Windows\System32\msdt.exe | — | pcwrun.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\Desktop\Keygen.exe" | C:\Users\admin\Desktop\Keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 1284 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1552 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES7419.tmp" "c:\Users\admin\AppData\Local\Temp\CSC7418.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1596 | C:\Users\admin\Desktop\Keygen.exe | C:\Users\admin\Desktop\Keygen.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1788 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\tv9ingvm.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1792 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\qj6d8meg.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1812 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES735E.tmp" "c:\Users\admin\AppData\Local\Temp\CSC735D.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2264 | "C:\Windows\System32\rundll32.exe" C:\Windows\system32\pcwutl.dll,CreateAndRunTask -path "C:\Users\admin\Desktop\Keygen.exe" | C:\Windows\System32\rundll32.exe | — | msdt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 310
Read events
7 263
Write events
47
Delete events
0
Modification events
| (PID) Process: | (692) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1284) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1284) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1284) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1284) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
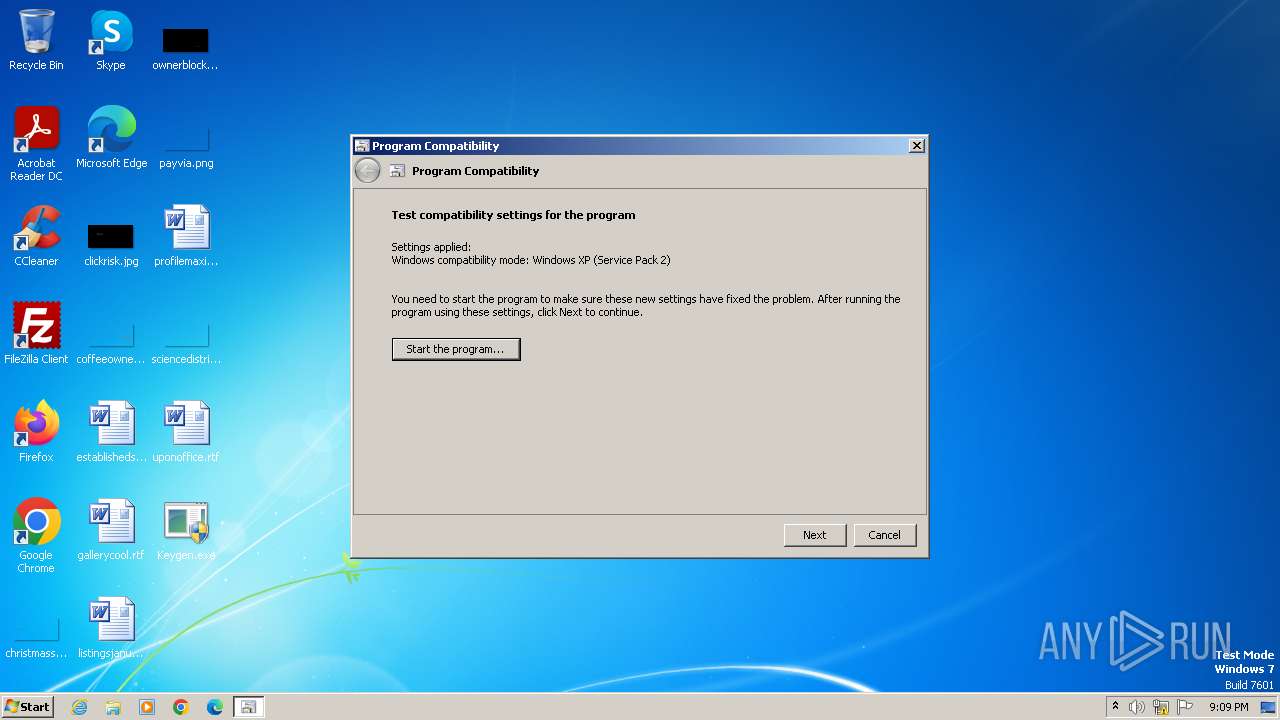
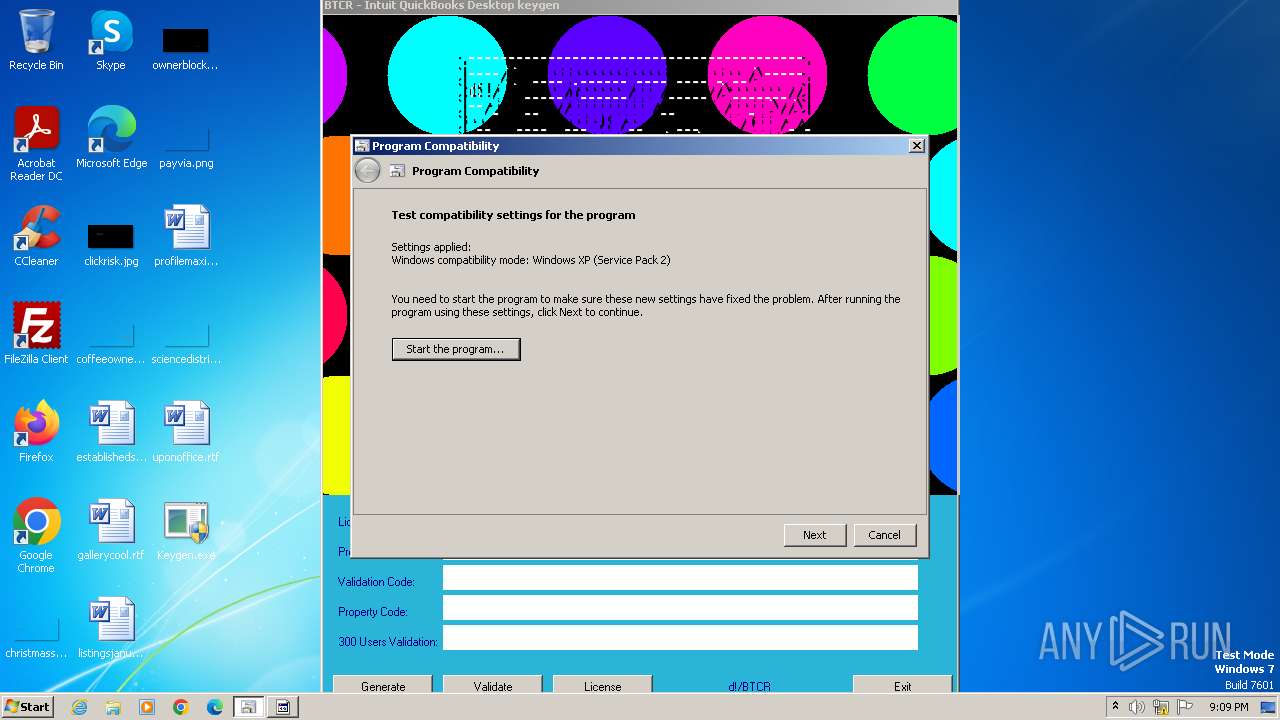
| (PID) Process: | (1284) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\Desktop\Keygen.exe |
Value: # WINXPSP2 | |||
| (PID) Process: | (692) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (692) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (692) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (692) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
5
Suspicious files
9
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 692 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_6df6b0cf-6e94-494d-a337-a48f3c2630e7\VF_ProgramCompatibilityWizard.ps1 | text | |
MD5:C219205ABF50BB950B93D0824D483780 | SHA256:5284D805B918F161565150EC64B787E4EA681DE69B1AD832F316F94DB6DBCB75 | |||
| 692 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_6df6b0cf-6e94-494d-a337-a48f3c2630e7\DiagPackage.dll | executable | |
MD5:4B9F845D6FF4BCED0EA8D7B0EA4AE7E7 | SHA256:21369005C8400B68D8CAB1A9A6C4D5809F5A685A8E18D311272467BB25D3D3C8 | |||
| 616 | pcwrun.exe | C:\Users\admin\AppData\Local\Temp\PCW691C.xml | xml | |
MD5:80681B26E76818EC8BB3F99F3C1B1D97 | SHA256:B32857E34DD8099890EC37E3D642C8738D942DEBA5FB85C0EDCB09FADCB7F0C2 | |||
| 1284 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\qj6d8meg.0.cs | text | |
MD5:B0DC59B099CA7C12FB8AD72D3C50C82C | SHA256:E75EAAA3D7908FB05000C0A957048D20091A0D2575E87D091D11CDB3A5B562E5 | |||
| 1792 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC735D.tmp | binary | |
MD5:2D4207C0DFAAD66FAB69069941C7BF60 | SHA256:39FFE67F097E89F59ED1647A0A97EDC9831C04BDBFA39D28596146FD0102C676 | |||
| 692 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_6df6b0cf-6e94-494d-a337-a48f3c2630e7\TS_ProgramCompatibilityWizard.ps1 | text | |
MD5:46E22C2582B54BE56D80D7A79FEC9BB5 | SHA256:459AF2960B08E848573D45A7350223657ADB2115F24A3C37E69FFE61DEA647F9 | |||
| 1792 | csc.exe | C:\Users\admin\AppData\Local\Temp\qj6d8meg.pdb | pdb | |
MD5:536BC0429B5BF30624C43969C38BF957 | SHA256:A5557EE3EEBD126FD37FFFEE7924B2AE2D9BE570457D8F2986D4D0165A813136 | |||
| 1284 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\qj6d8meg.cmdline | text | |
MD5:2BB869C20CBE590F4EF446DA8C6FB0E4 | SHA256:A97306AF52DE37506372C20BD316844808E2901DC76C2F367038DAEC77CCBDC7 | |||
| 692 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_6df6b0cf-6e94-494d-a337-a48f3c2630e7\RS_ProgramCompatibilityWizard.ps1 | text | |
MD5:367FE5F4C6DB87E1600F46687E5AAC54 | SHA256:177625AC9B07BBFFCBBB47101C2D1121F47B03B42226861BFD7974B9CEBC0C98 | |||
| 692 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_6df6b0cf-6e94-494d-a337-a48f3c2630e7\DiagPackage.diagpkg | html | |
MD5:18A906A43C1C3E27064DB30C81505234 | SHA256:041430D1F0AE14300C46BDCD917C882F4850DA3D6010E3FBF692023655BC406E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|