| File name: | LicitacionelectronicaPLACSP.jnlp |
| Full analysis: | https://app.any.run/tasks/ddb16e08-d4f6-4bc8-94fb-b7812264a214 |
| Verdict: | No threats detected |
| Analysis date: | September 25, 2020, 11:09:54 |
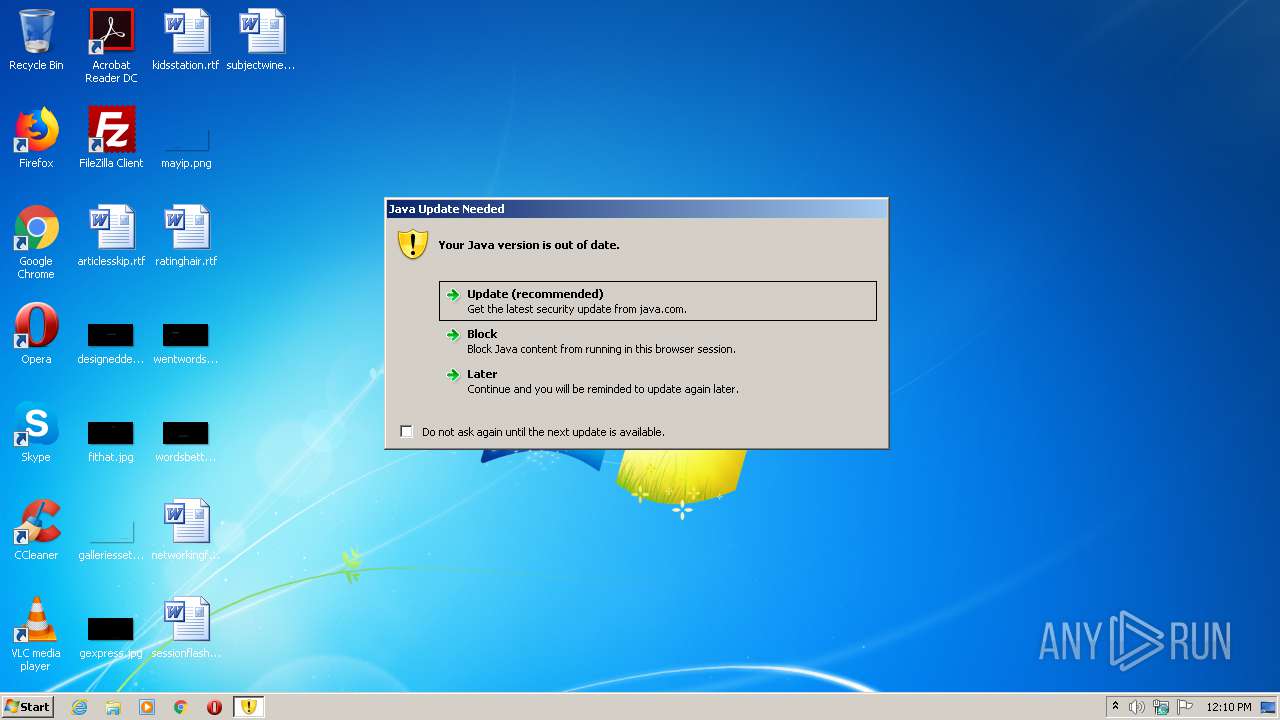
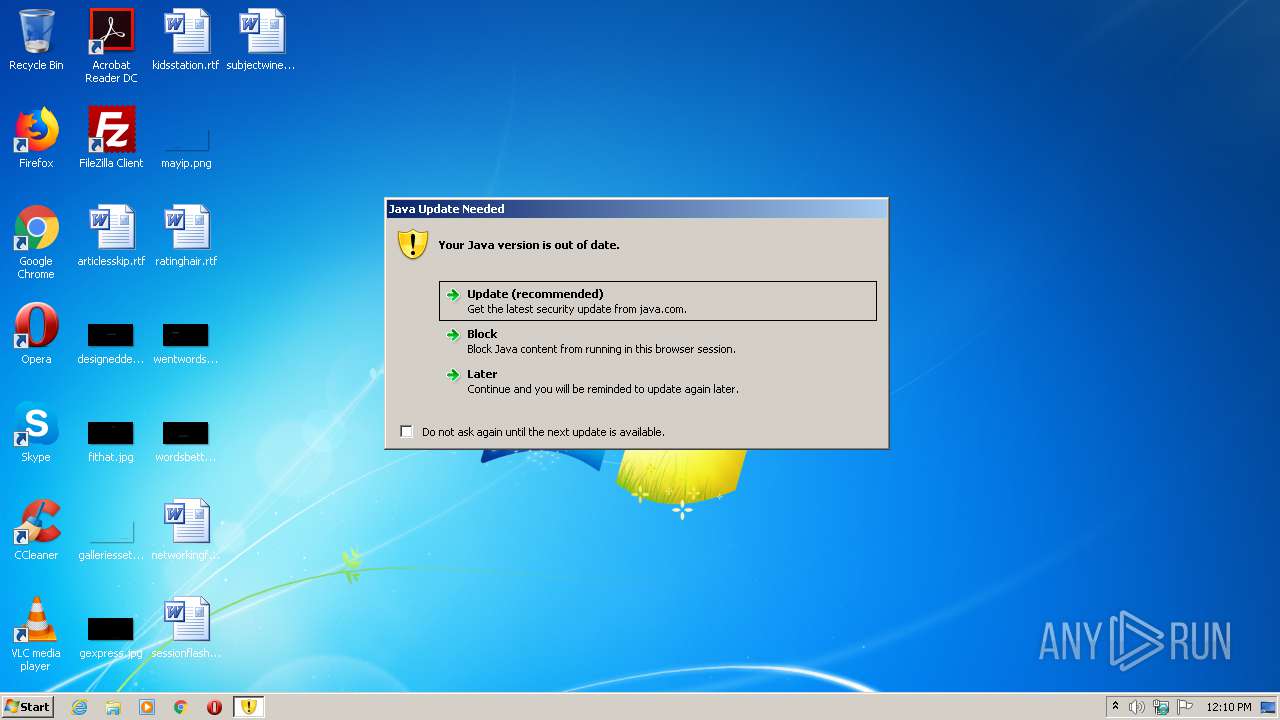
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/xml |
| File info: | XML 1.0 document, UTF-8 Unicode text |
| MD5: | 259BB0E33F43814529A3E820AF726701 |
| SHA1: | F11B72746BF58E03B69D2942604855D8F7F227A9 |
| SHA256: | EB20BF9F0821AA8DBAEEE4403D2B4056917EF1F646BDE1E9E89EBA59598834C6 |
| SSDEEP: | 48:cTtEBBEzI84lfQHp51BkRHuqHQy4Txgm/UiWJWn8d5CNXXUp:iSBO546Hp5rqHuqHcTmm5W97eUp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Check for Java to be installed
- javaws.exe (PID: 2304)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jnlp | | | Java Web Start application descriptor (88.3) |
|---|---|---|
| .xml | | | Generic XML (ASCII) (11.6) |
EXIF
XMP
| JnlpSpec: | 1.0+ |
|---|---|
| JnlpCodebase: | https://contrataciondelestado.es/LE_PreparacionYPresentacion_Applet/ |
| JnlpHref: | - |
| JnlpInformationTitle: | Herramienta de Preparacion y Presentacion de Ofertas y Proposiciones |
| JnlpInformationVendor: | IBM |
| JnlpInformationHomepageHref: | http://www.contrataciondelestado.es |
| JnlpInformationDescription: | Herramienta de Preparacion y Presentacion de Ofertas y Proposiciones |
| JnlpInformationDescriptionKind: | short |
| JnlpSecurityAll-permissions: | - |
| JnlpResourcesJarHref: | LE_PreparacionYPresentacion.jar |
| JnlpResourcesJarVersion: | 1.1227 |
| JnlpResourcesJarMain: | |
| JnlpResourcesPropertyName: | jnlp.versionEnabled |
| JnlpResourcesPropertyValue: | |
| JnlpResourcesArch: | x86_64 amd64 |
| JnlpResourcesJ2seVersion: | 1.8+ |
| JnlpResourcesJ2seInitial-heap-size: | 1024m |
| JnlpResourcesJ2seMax-heap-size: | 1536m |
| JnlpResourcesJ2seJava-vm-args: | -Djava.net.preferIPv4Stack=true |
| JnlpResourcesJ2seHref: | http://www.noExiste.com |
| JnlpApplication-descName: | Preparación y presentación de Licitaciones electrónicas |
| JnlpApplication-descWidth: | 1180 |
| JnlpApplication-descHeight: | 1000 |
| JnlpApplication-descMain-class: | com.applet.Preparacion |
| JnlpApplication-descArgument: | idusuario=d80oMRtpLicfGbWFTC2Emw== |
| JnlpUpdateCheck: | always |
| JnlpUpdatePolicy: | always |
Total processes
37
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2304 | "C:\Program Files\Java\jre1.8.0_92\bin\javaws.exe" "C:\Users\admin\AppData\Local\Temp\LicitacionelectronicaPLACSP.jnlp" | C:\Program Files\Java\jre1.8.0_92\bin\javaws.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.92.2.14 Modules
| |||||||||||||||
Total events
3
Read events
3
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report