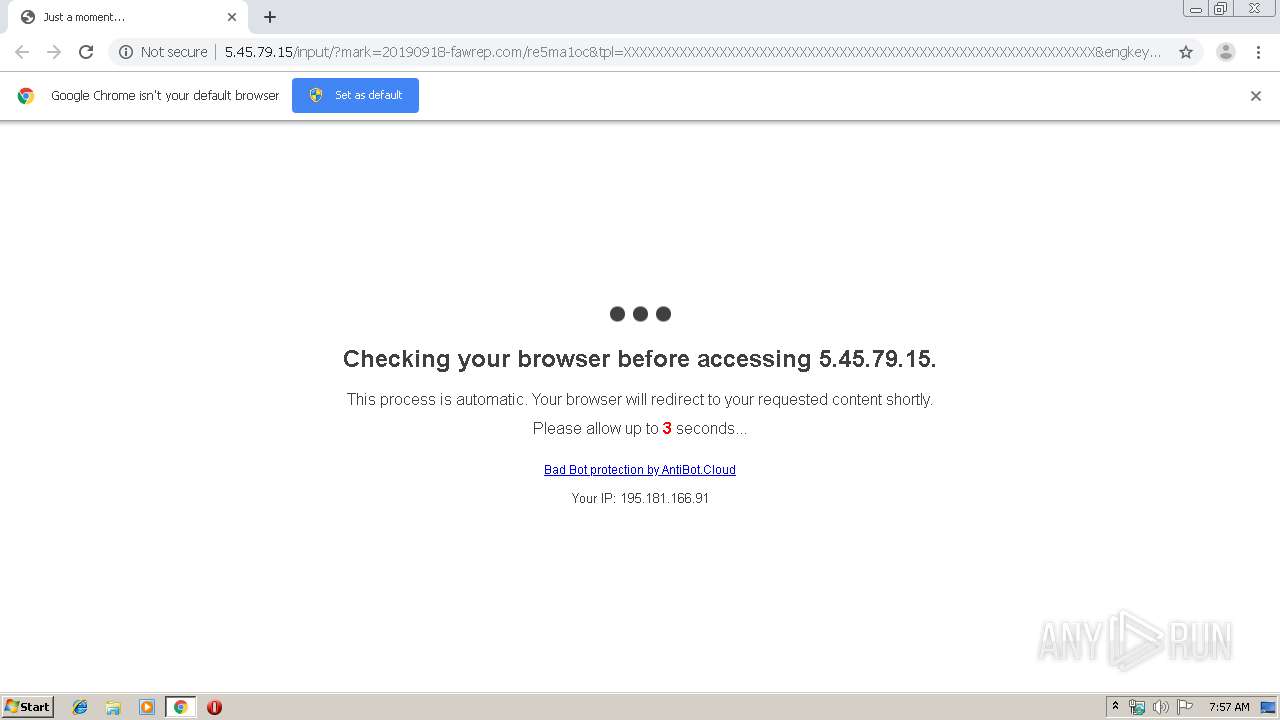
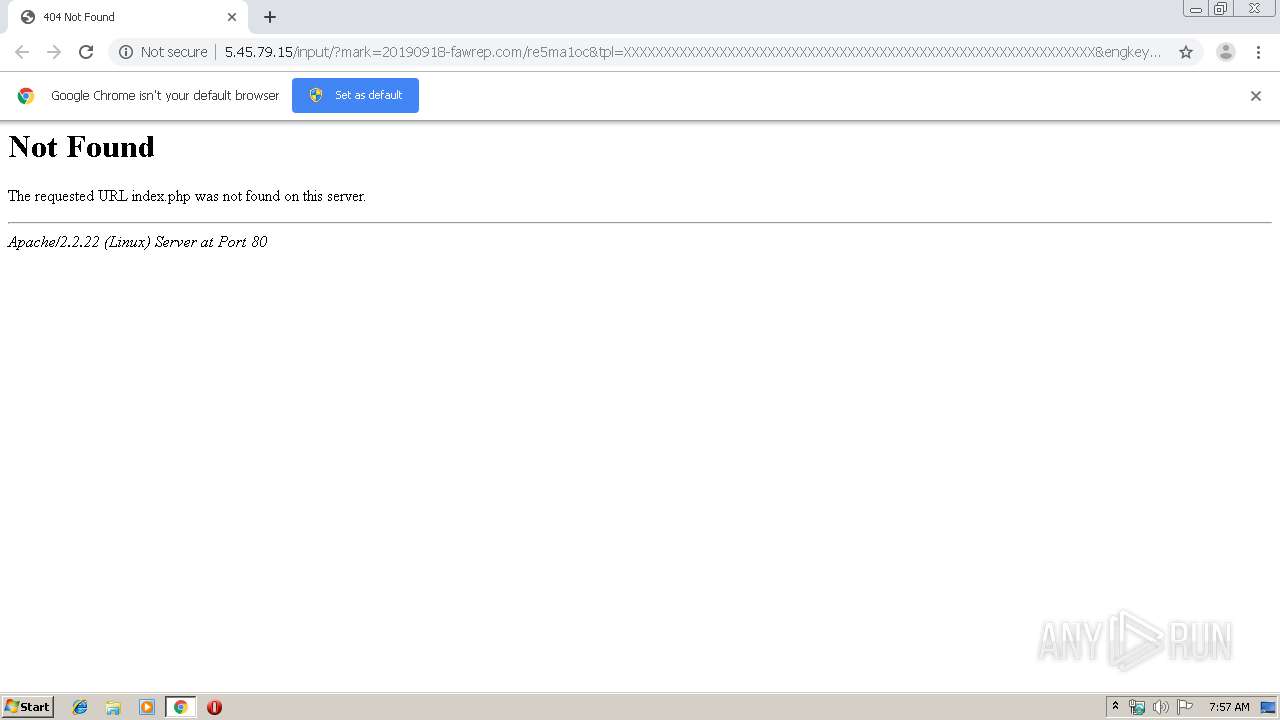
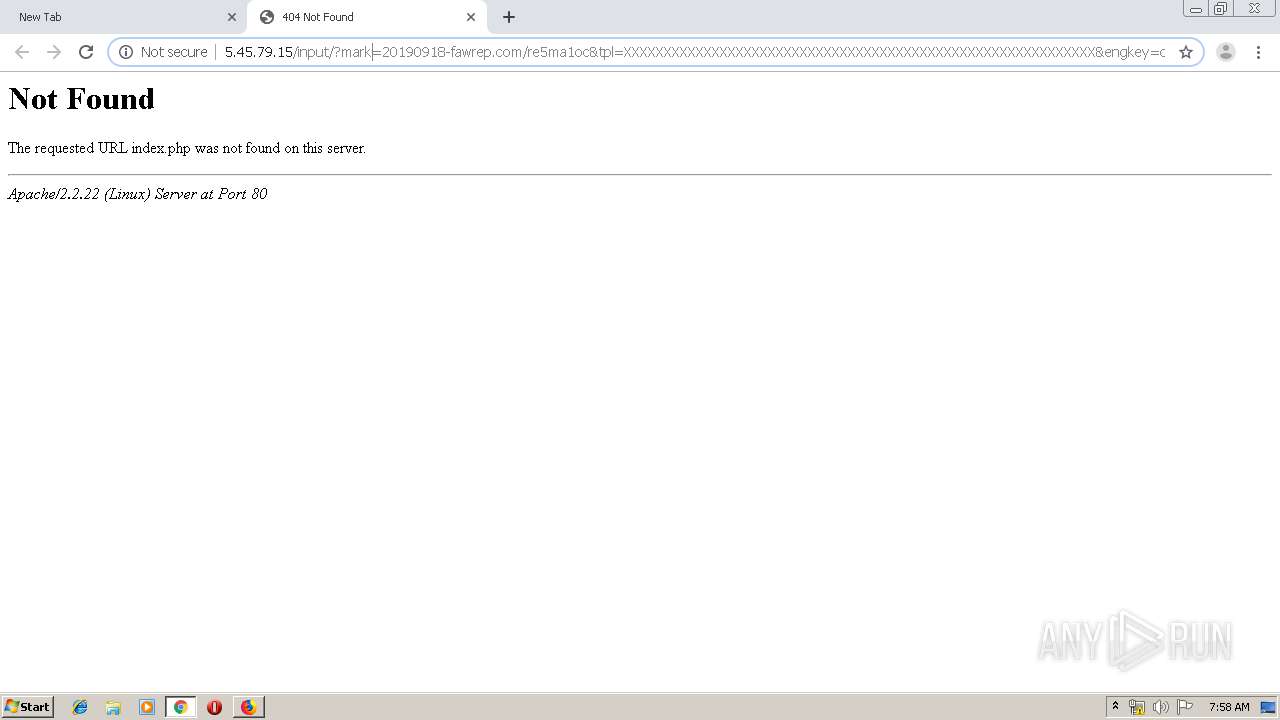
| URL: | http://5.45.79.15/input/?mark=20190918-fawrep.com/re5ma1oc&tpl=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX&engkey=clinical+study+results |
| Full analysis: | https://app.any.run/tasks/8e5ba414-d847-4c3c-a466-efc8e7b1f7ae |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 06:57:00 |
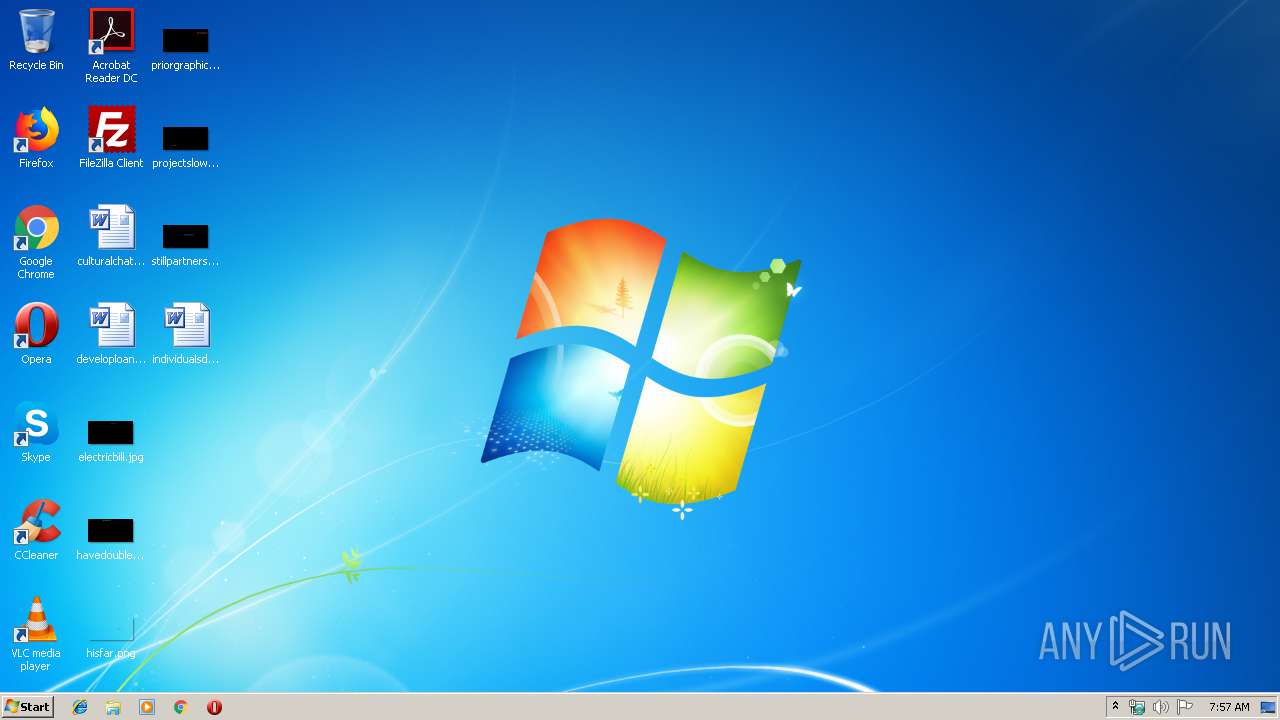
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BA15F6F1C0E2963806903E2FD7E528F3 |
| SHA1: | 9A5AFFAFE7123ACA29DEA4D6073DCCF0CC96321C |
| SHA256: | EB118A0455E72722380BD383B74062A824D80B0FED55FFAD0B3F17B96D0E56E3 |
| SSDEEP: | 3:N1K/2LScgfOQRKYzVHVfIKybHW9fX9999999999999999999999999999999999Z:Curgf/57gKy+fPZn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3432)
Creates files in the program directory
- firefox.exe (PID: 2840)
INFO
Reads the hosts file
- chrome.exe (PID: 2824)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3432)
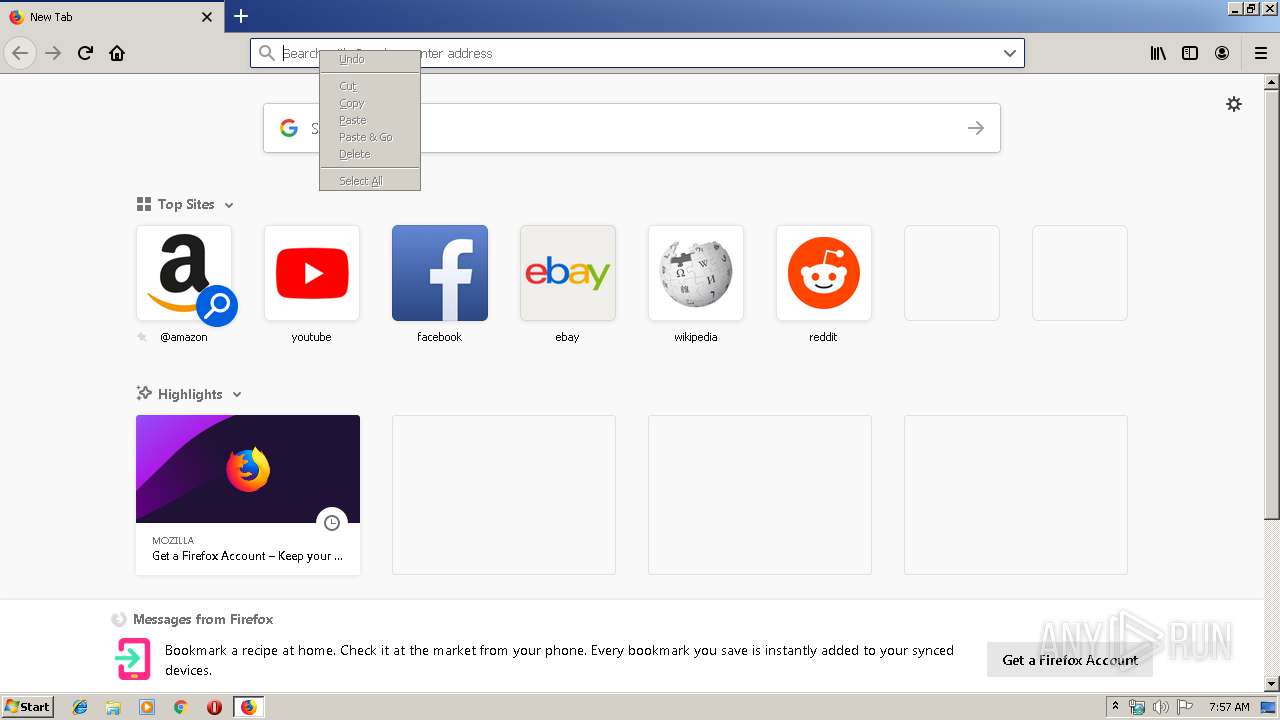
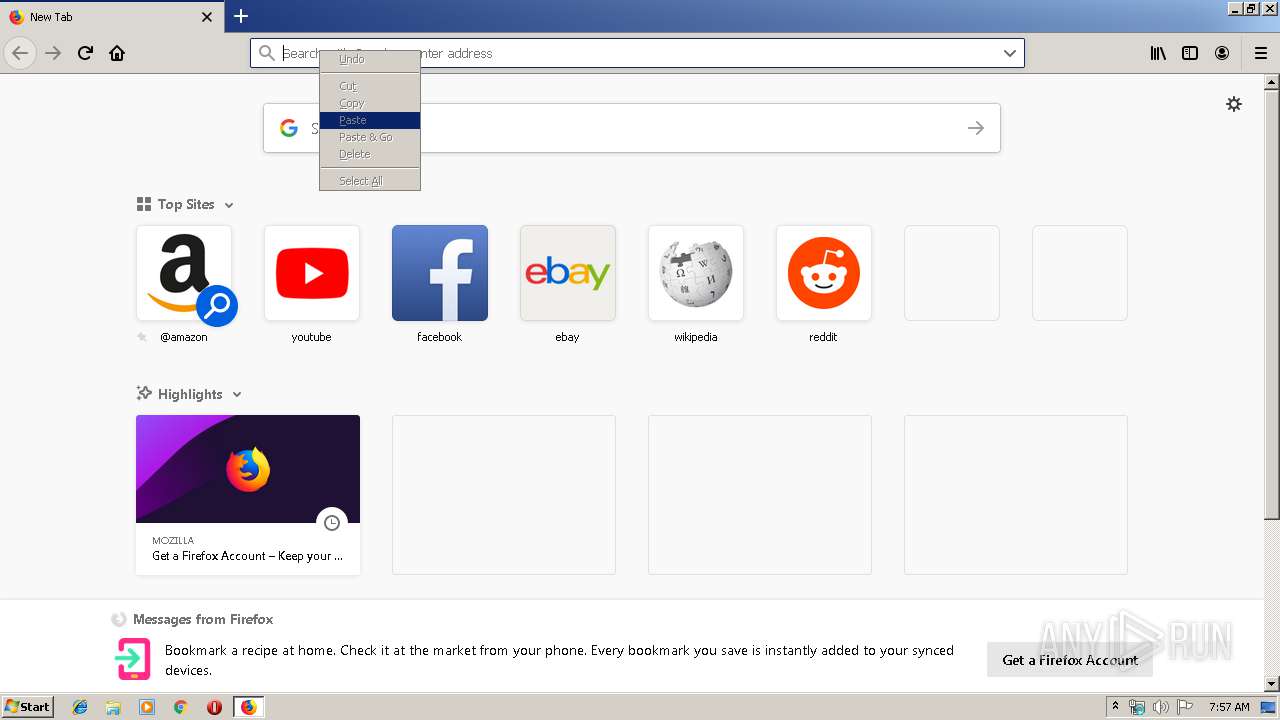
Manual execution by user
- firefox.exe (PID: 364)
- chrome.exe (PID: 3896)
Reads settings of System Certificates
- chrome.exe (PID: 2824)
- chrome.exe (PID: 4088)
Creates files in the user directory
- firefox.exe (PID: 2840)
Application launched itself
- firefox.exe (PID: 2840)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 3432)
Reads CPU info
- firefox.exe (PID: 2840)
Reads Internet Cache Settings
- firefox.exe (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
42
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,3011696790113115568,12596623861463178111,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7976218179340123419 --mojo-platform-channel-handle=3860 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,3011696790113115568,12596623861463178111,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1594555846283860400 --mojo-platform-channel-handle=1192 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fe6a9d0,0x6fe6a9e0,0x6fe6a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,3011696790113115568,12596623861463178111,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6303521283259758118 --mojo-platform-channel-handle=3272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,3011696790113115568,12596623861463178111,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5393754425103974643 --mojo-platform-channel-handle=3380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,3011696790113115568,12596623861463178111,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16088070319013139063 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2840.13.1045797400\1468722008" -childID 2 -isForBrowser -prefsHandle 2812 -prefMapHandle 2816 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2840 "\\.\pipe\gecko-crash-server-pipe.2840" 2828 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,3011696790113115568,12596623861463178111,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5871197843928519166 --mojo-platform-channel-handle=3380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11811941344145020013,17336914047156979523,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17412566040590948349 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
888
Read events
742
Write events
137
Delete events
9
Modification events
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3432-13213349835056750 |
Value: 259 | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
97
Text files
230
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\690cf4fb-c8bb-4f7d-984b-e8ffac38ec16.tmp | — | |
MD5:— | SHA256:— | |||
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169bf6.TMP | text | |
MD5:— | SHA256:— | |||
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
64
DNS requests
97
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2824 | chrome.exe | GET | — | 5.45.79.15:80 | http://5.45.79.15/input/?mark=20190918-fawrep.com/re5ma1oc&tpl=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX&engkey=clinical+study+results | NL | — | — | suspicious |
2824 | chrome.exe | GET | — | 5.45.79.15:80 | http://5.45.79.15/input/?mark=20190918-fawrep.com/re5ma1oc&tpl=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX&engkey=clinical+study+results | NL | — | — | suspicious |
2824 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2824 | chrome.exe | GET | 200 | 5.45.79.15:80 | http://5.45.79.15/input/?mark=20190918-fawrep.com/re5ma1oc&tpl=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX&engkey=clinical+study+results | NL | html | 225 b | suspicious |
2824 | chrome.exe | GET | 200 | 5.45.79.15:80 | http://5.45.79.15/input/?mark=20190918-fawrep.com/re5ma1oc&tpl=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX&engkey=clinical+study+results | NL | html | 225 b | suspicious |
2840 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2824 | chrome.exe | GET | 200 | 5.45.79.15:80 | http://5.45.79.15/input/?mark=20190918-fawrep.com/re5ma1oc&tpl=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX&engkey=clinical+study+results | NL | html | 225 b | suspicious |
2824 | chrome.exe | GET | 200 | 5.45.79.15:80 | http://5.45.79.15/input/?mark=20190918-fawrep.com/re5ma1oc&tpl=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX&engkey=clinical+study+results | NL | html | 225 b | suspicious |
2840 | firefox.exe | GET | 404 | 5.45.79.15:80 | http://5.45.79.15/favicon.ico | NL | html | 404 b | suspicious |
2840 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2824 | chrome.exe | 5.45.79.15:80 | — | Serverius Holding B.V. | NL | suspicious |
2824 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2824 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2824 | chrome.exe | 172.217.22.110:443 | clients4.google.com | Google Inc. | US | whitelisted |
2824 | chrome.exe | 185.82.216.241:443 | ipv4alt.antibot.cloud | ITL Company | BG | suspicious |
2824 | chrome.exe | 185.211.246.22:443 | antibot.cloud | Chernyshov Aleksandr Aleksandrovich | RU | unknown |
2824 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2824 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2824 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2824 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients4.google.com |
| whitelisted |
antibot.cloud |
| whitelisted |
ipv4alt.antibot.cloud |
| whitelisted |
ipv4main.antibot.cloud |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
2 ETPRO signatures available at the full report