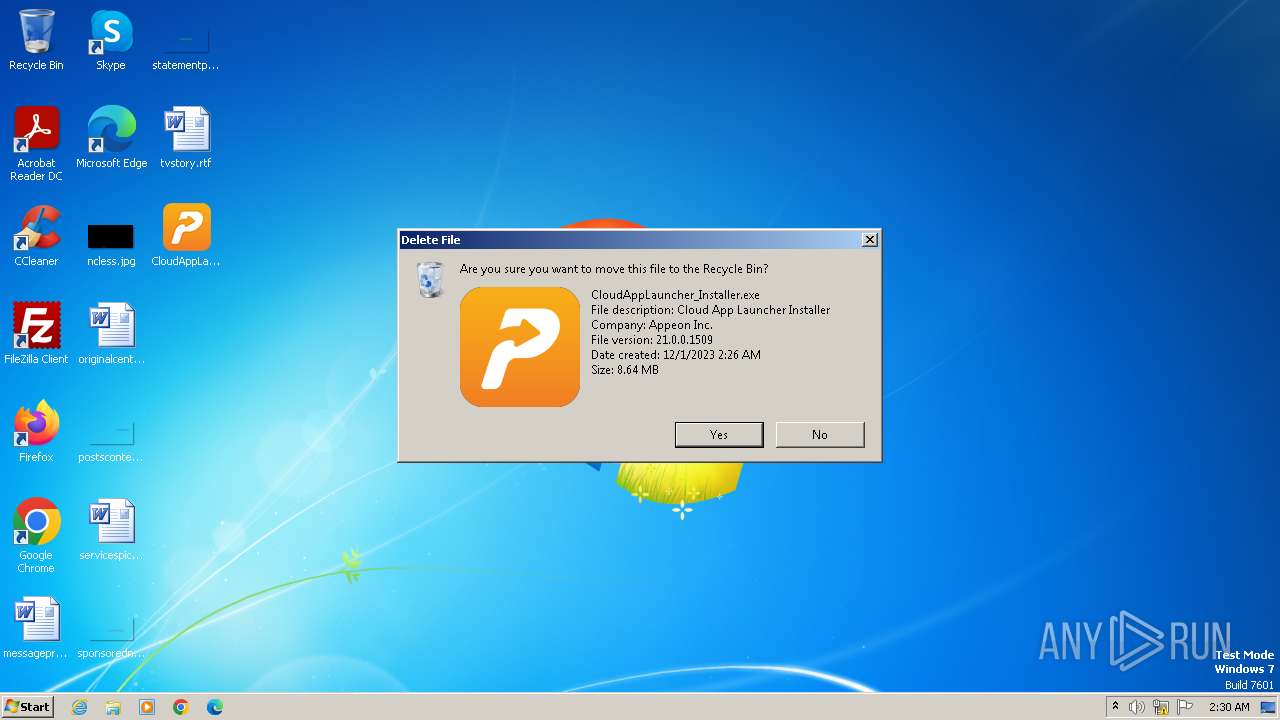
| File name: | CloudAppLauncher_Installer.exe |
| Full analysis: | https://app.any.run/tasks/d3bbb1a4-4574-4b83-8d27-e798869b76ee |
| Verdict: | Malicious activity |
| Analysis date: | December 01, 2023, 02:26:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
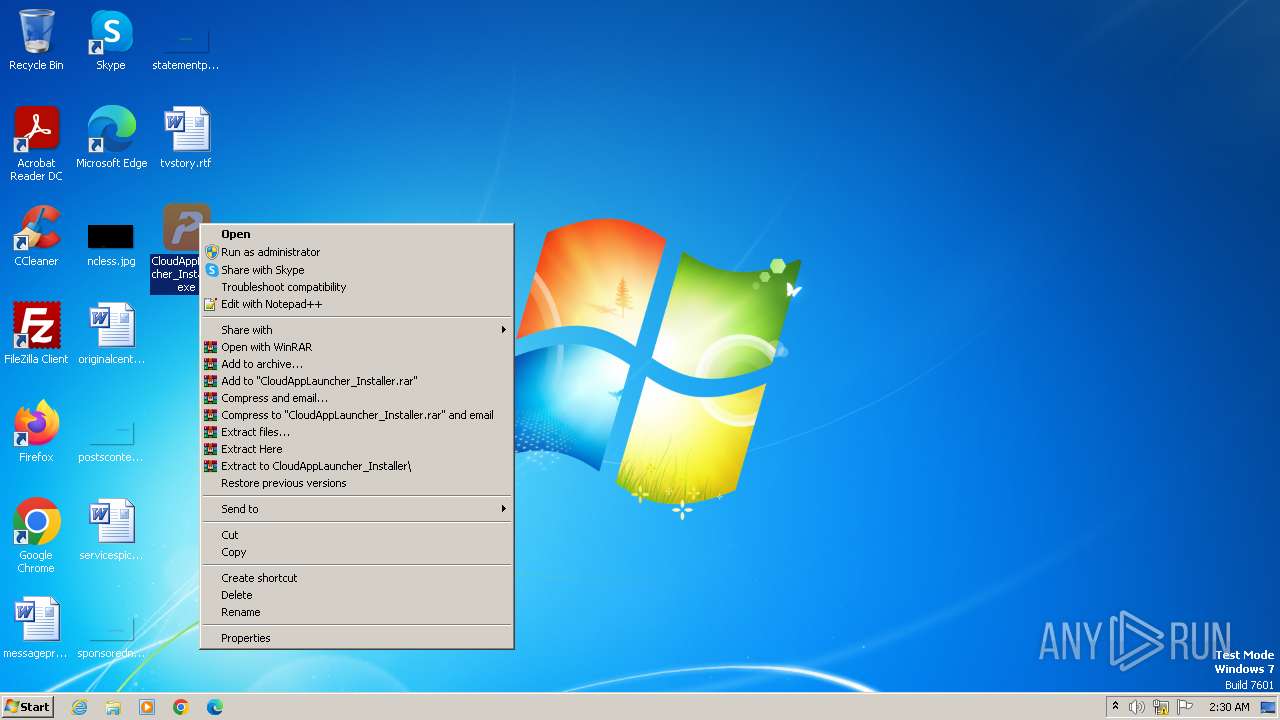
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 69132375F3AB54F169AD57CF7AB138A1 |
| SHA1: | 37DF748A0C3E0A1C92CE846891B2E69C556F96C5 |
| SHA256: | EB0045F2CCA4E9FB6ABC4C4F11672614FDC60FF63903C582A06D4D350C568BDD |
| SSDEEP: | 196608:JgAqo7xzYzCJpuMCOkyCnd6yOtUvOj7tp40+8jVKwoU:5qgnuMCnyCnd6hHtpl3VKwoU |
MALICIOUS
Drops the executable file immediately after the start
- CloudAppLauncher_Installer.exe (PID: 2480)
- LauncherSetup_withoutservice.exe (PID: 2916)
- LauncherSetup_withoutservice.exe (PID: 2864)
SUSPICIOUS
Reads the Internet Settings
- CloudAppLauncher_Installer.exe (PID: 2480)
Reads the Windows owner or organization settings
- LauncherSetup_withoutservice.exe (PID: 2864)
Starts CMD.EXE for commands execution
- LauncherSetup_withoutservice.exe (PID: 2864)
- cmd.exe (PID: 1900)
Creates a software uninstall entry
- LauncherSetup_withoutservice.exe (PID: 2864)
Executing commands from a ".bat" file
- LauncherSetup_withoutservice.exe (PID: 2864)
Application launched itself
- cmd.exe (PID: 1900)
Process drops legitimate windows executable
- LauncherSetup_withoutservice.exe (PID: 2864)
The process drops C-runtime libraries
- LauncherSetup_withoutservice.exe (PID: 2864)
Searches for installed software
- LauncherSetup_withoutservice.exe (PID: 2864)
INFO
Creates files or folders in the user directory
- CloudAppLauncher_Installer.exe (PID: 2480)
- LauncherSetup_withoutservice.exe (PID: 2864)
- SetupProgress.exe (PID: 2504)
- AppLauncher.exe (PID: 3432)
Checks supported languages
- CloudAppLauncher_Installer.exe (PID: 2480)
- wmpnscfg.exe (PID: 3004)
- LauncherSetup_withoutservice.exe (PID: 2916)
- LauncherSetup_withoutservice.exe (PID: 2864)
- SetupProgress.exe (PID: 2504)
- AppLauncher.exe (PID: 3432)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3004)
- LauncherSetup_withoutservice.exe (PID: 2864)
Reads the computer name
- wmpnscfg.exe (PID: 3004)
- CloudAppLauncher_Installer.exe (PID: 2480)
- LauncherSetup_withoutservice.exe (PID: 2916)
- LauncherSetup_withoutservice.exe (PID: 2864)
- AppLauncher.exe (PID: 3432)
Create files in a temporary directory
- CloudAppLauncher_Installer.exe (PID: 2480)
- LauncherSetup_withoutservice.exe (PID: 2916)
- LauncherSetup_withoutservice.exe (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (14.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.4) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:04:23 06:19:03+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 1273856 |
| InitializedDataSize: | 7777792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1084c6 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 21.0.0.1509 |
| ProductVersionNumber: | 22.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Appeon Inc. |
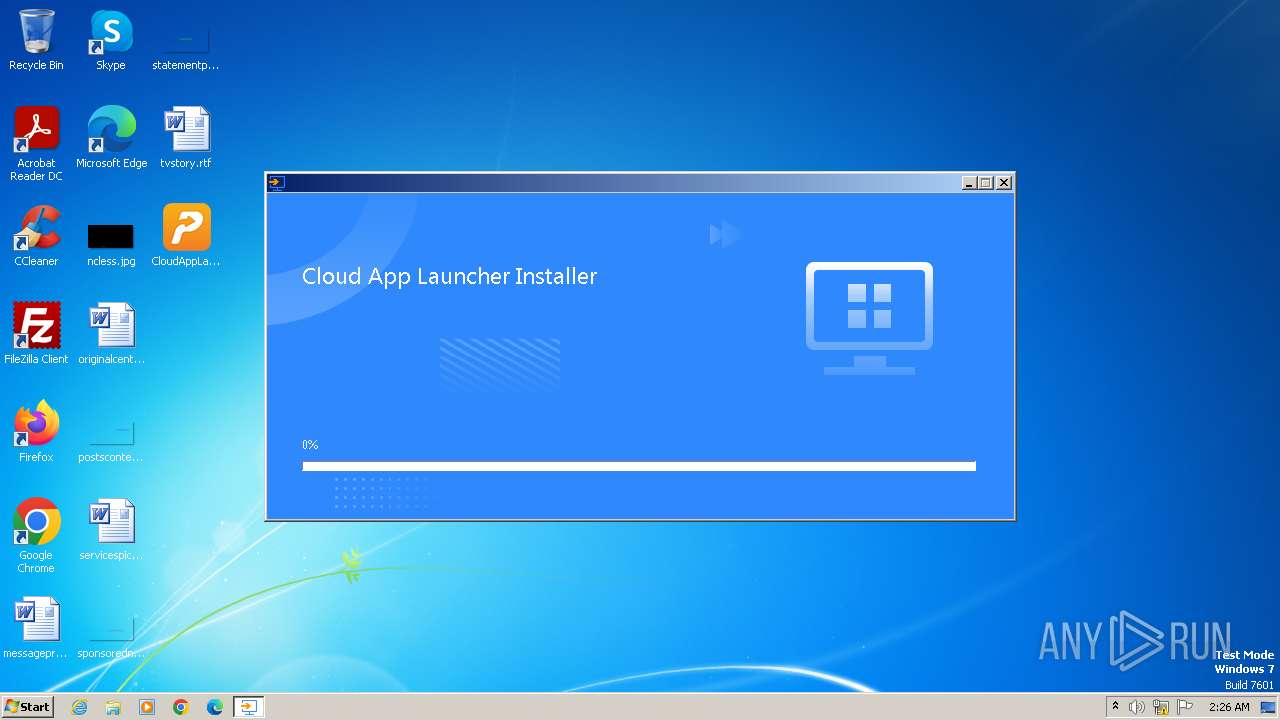
| FileDescription: | Cloud App Launcher Installer |
| FileVersion: | 21.0.0.1509 |
| InternalName: | CloudAppLauncher_installer.exe |
| LegalCopyright: | Copyright (c) Appeon. All rights reserved. |
| OriginalFileName: | - |
| ProductName: | Cloud App Launcher Installer |
| ProductVersion: | 21.0.0.1509 |
Total processes
95
Monitored processes
58
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Windows\system32\cmd.exe /S /D /c" echo 0.0.0.0:7780 " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 304 | C:\Windows\system32\cmd.exe /S /D /c" echo 127.0.0.1:49192 " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 580 | find /i ":26569 " | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | find /i ":26569 " | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 924 | netstat -ano | C:\Windows\System32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | find /i ":26569 " | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1064 | C:\Windows\system32\cmd.exe /S /D /c" echo 0.0.0.0:7781 " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1452 | find /i ":26569 " | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | C:\Windows\system32\cmd.exe /S /D /c" echo 0.0.0.0:49155 " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1788 | C:\Windows\system32\cmd.exe /c netstat -ano | find /i "TCP" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 927
Read events
1 912
Write events
9
Delete events
6
Modification events
| (PID) Process: | (3004) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{F6898EAA-CCE6-4E62-B03E-95AE1DEF63F1}\{617884B6-F5BF-4A47-9752-3D3E2DDF9627} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3004) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{F6898EAA-CCE6-4E62-B03E-95AE1DEF63F1} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3004) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{3C6484D6-164B-452E-A8F5-38AE4AC56601} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2480) CloudAppLauncher_Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2480) CloudAppLauncher_Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2480) CloudAppLauncher_Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2480) CloudAppLauncher_Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2864) LauncherSetup_withoutservice.exe | Key: | HKEY_CURRENT_USER\Software\Appeon Inc.\Cloud App Launcher\21.0.0.1509 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2864) LauncherSetup_withoutservice.exe | Key: | HKEY_CURRENT_USER\Software\Appeon Inc.\Cloud App Launcher |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2864) LauncherSetup_withoutservice.exe | Key: | HKEY_CURRENT_USER\Software\Appeon Inc. |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
53
Suspicious files
25
Text files
38
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | CloudAppLauncher_Installer.exe | C:\Users\admin\AppData\Local\Temp\CAL_Installer_20231201-022629\setup.cab | — | |
MD5:— | SHA256:— | |||
| 2480 | CloudAppLauncher_Installer.exe | C:\Users\admin\AppData\Local\Temp\CAL_Installer_20231201-022629\LauncherCfg.ini | text | |
MD5:9BD7C1569CAD6BEEB22E43EEBDAACBD8 | SHA256:A571BD9F79AE671F9CCE18CCE3B5FEA0DB3F8C5AB814FC3266BEEF7F50B11301 | |||
| 2480 | CloudAppLauncher_Installer.exe | C:\Users\admin\AppData\Local\Appeon\appeoninstalllog\CAL_unzip.log | text | |
MD5:8372D9B35BAC56C00E0E0F1BF37CFB5A | SHA256:C200CDE35C7639B6DCF675C3A903E3D8C6C5E66F9A8FBF6621714071F9154DC7 | |||
| 2916 | LauncherSetup_withoutservice.exe | C:\Users\admin\AppData\Local\Temp\{A6D347A8-FCE5-4D19-ABE5-1075A9B0DDBD}\Disk1\data1.hdr | compressed | |
MD5:369D5956FE371A4EEDD214156D58452A | SHA256:A24493D6D350942599893C0C198FD07A8E81A550BB238066A1A123DBFF2F4E9F | |||
| 2916 | LauncherSetup_withoutservice.exe | C:\Users\admin\AppData\Local\Temp\{A6D347A8-FCE5-4D19-ABE5-1075A9B0DDBD}\Disk1\0x0409.ini | text | |
MD5:A108F0030A2CDA00405281014F897241 | SHA256:8B76DF0FFC9A226B532B60936765B852B89780C6E475C152F7C320E085E43948 | |||
| 2916 | LauncherSetup_withoutservice.exe | C:\Users\admin\AppData\Local\Temp\{A6D347A8-FCE5-4D19-ABE5-1075A9B0DDBD}\Disk1\layout.bin | binary | |
MD5:83D13DAC65882F7CE329BAB92A267C15 | SHA256:C3CCFD80084E0DF6A4FFE150EA1A08BCABF1B9FA0C9DBB11646858A60749C47C | |||
| 2916 | LauncherSetup_withoutservice.exe | C:\Users\admin\AppData\Local\Temp\{A6D347A8-FCE5-4D19-ABE5-1075A9B0DDBD}\Disk1\ISSetup.dll | executable | |
MD5:A18CBD87B67AC3F4D10BB3AF7AB5651A | SHA256:0031CE302FD5900DFAB753F71B712AA7142BFD1568CB6D1C3A2D39D7434EC6A9 | |||
| 2480 | CloudAppLauncher_Installer.exe | C:\Users\admin\AppData\Local\Temp\CAL_Installer_20231201-022629\LauncherSetup_withoutservice.exe | executable | |
MD5:76EEA6EA9FDC663BB29C0AD5B58371B0 | SHA256:34724F40C756C8C66A787D83E327A20E765E1EF4071CE410F39BE1D8B72E78E3 | |||
| 2480 | CloudAppLauncher_Installer.exe | C:\Users\admin\AppData\Local\Temp\CAL_Installer_20231201-022629\Config.ini | text | |
MD5:C29B568A1F1C4F030C3DB13AD31A84B4 | SHA256:860F540FCA0F0E55815B213BB754C5E64A508F9A79924E222FF070718C82DB86 | |||
| 2480 | CloudAppLauncher_Installer.exe | C:\Users\admin\AppData\Local\Temp\CAL_Installer_20231201-022629\pcas.ico | image | |
MD5:FFCC644409E8CE9DC9BDECDDAA99F090 | SHA256:BD15BE60A360DC393DEDE82F57D15336752880558FAE56E4F6795212CDCE78E9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b257947f6e02507e | GB | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |