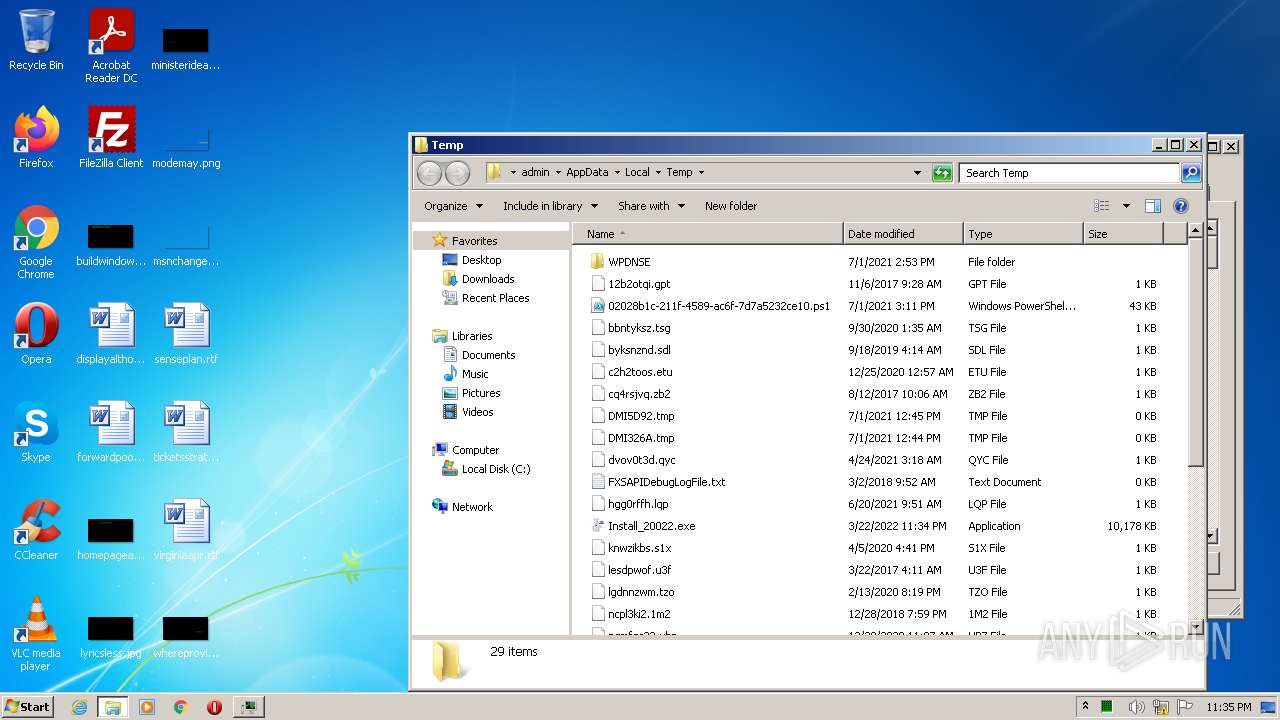
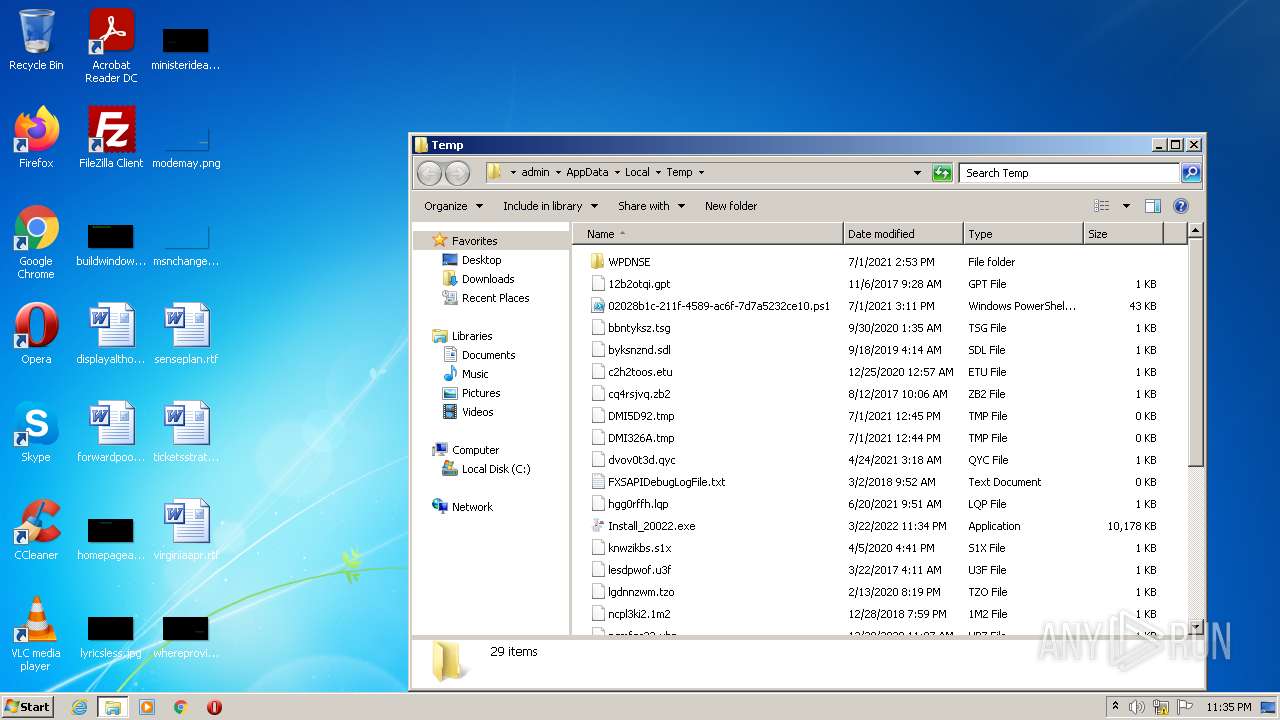
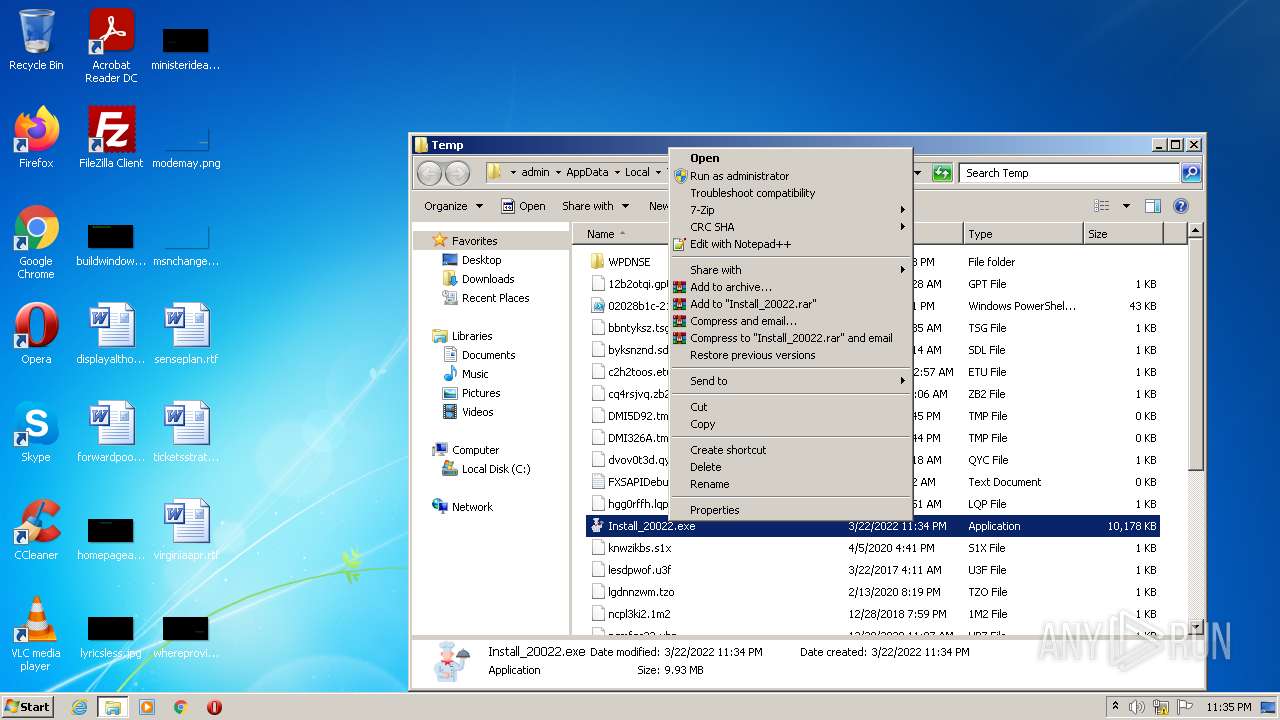
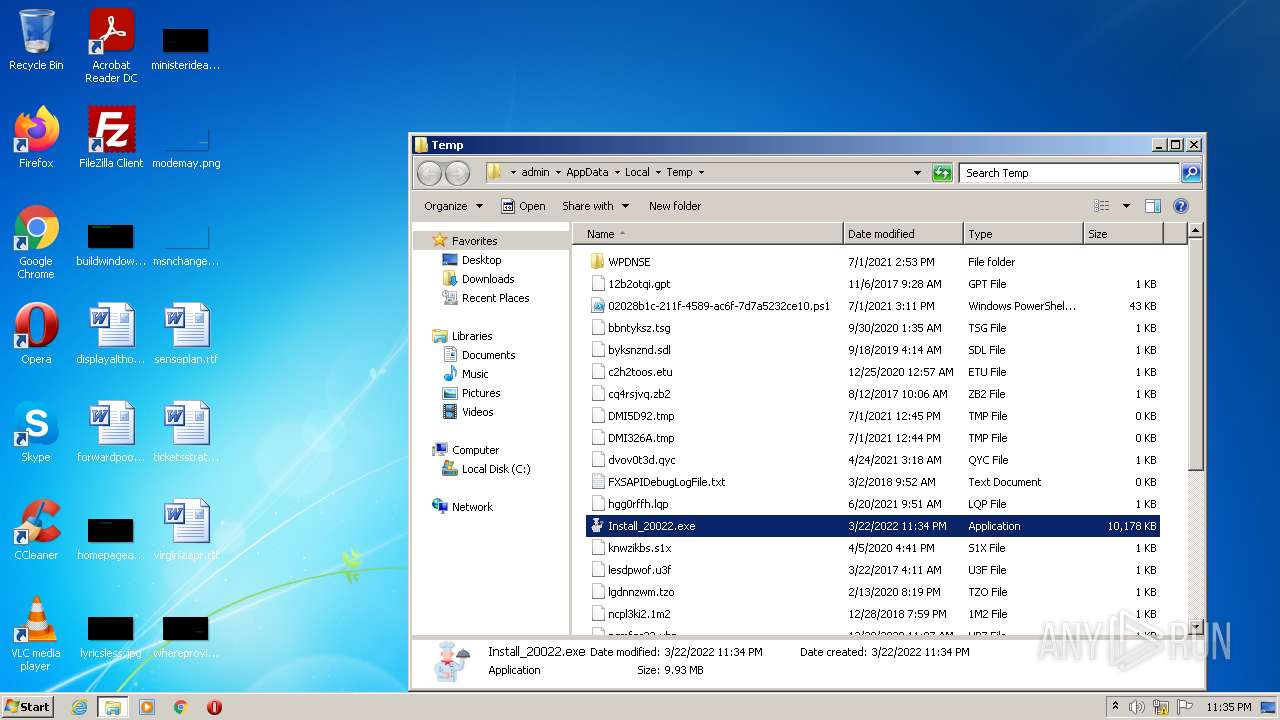
| File name: | Install_20022.exe |
| Full analysis: | https://app.any.run/tasks/fc5c7494-cad8-41ca-934d-b481c19b4f8d |
| Verdict: | Malicious activity |
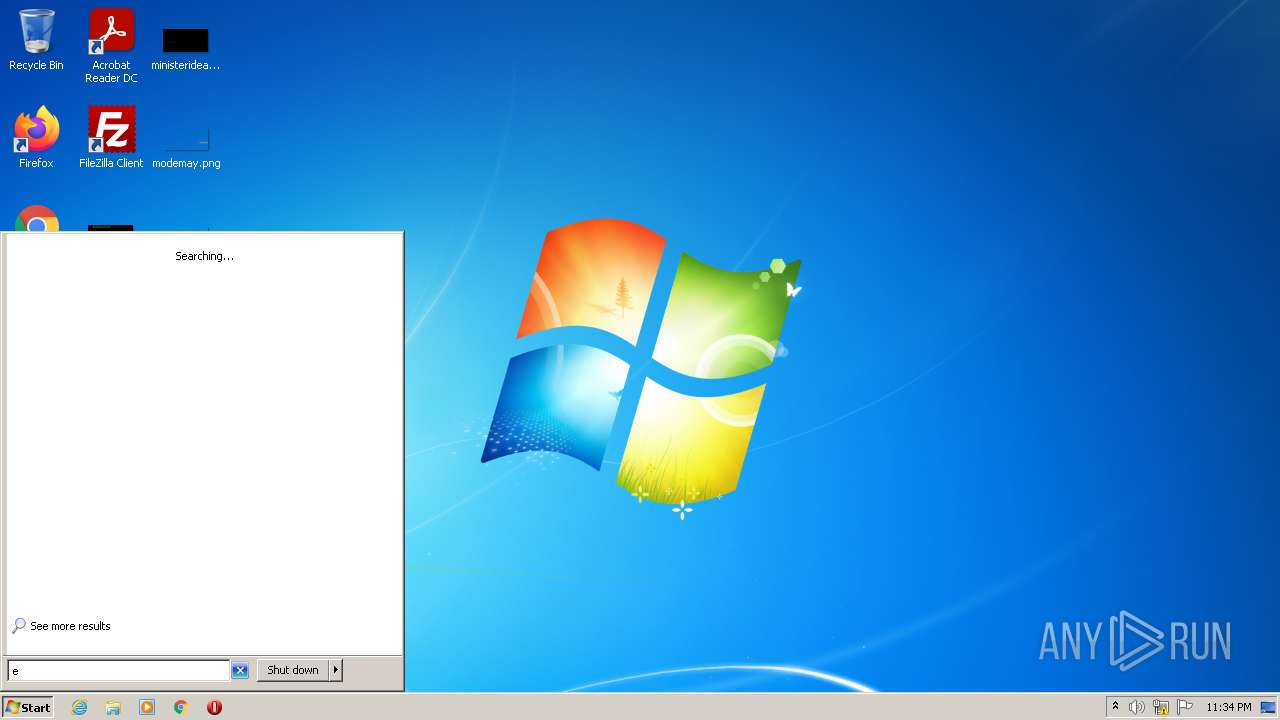
| Analysis date: | March 22, 2022, 23:34:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E5D1A3E4C87BF27FC658F14E363BF1F0 |
| SHA1: | 85C3A69E6F1C64671776DD0032715B8F9504F446 |
| SHA256: | EAFEAF2A4411078895122ED0DF36EC8F0FD1AEDF0194A137DEE401DA21B30A34 |
| SSDEEP: | 196608:fe8bPiUpwydE5foIBz7SEf6KBloYUzMbkCE/Jsv6tWKFdu9CbHFg3H:fUCEVhUFCE/Jsv6tWKFdu9Cy3H |
MALICIOUS
Application was dropped or rewritten from another process
- AgreeablemSoft.exe (PID: 276)
- AgreeablerSoft.exe (PID: 2792)
Loads dropped or rewritten executable
- svchost.exe (PID: 876)
- Explorer.EXE (PID: 612)
- SearchProtocolHost.exe (PID: 1328)
SUSPICIOUS
Application launched itself
- Install_20022.exe (PID: 3892)
- Install_20022.exe (PID: 3104)
Checks supported languages
- Install_20022.exe (PID: 3892)
- Install_20022.exe (PID: 1740)
- AgreeablemSoft.exe (PID: 276)
- Install_20022.exe (PID: 3104)
- Install_20022.exe (PID: 3604)
- AgreeablerSoft.exe (PID: 2792)
Reads the computer name
- Install_20022.exe (PID: 1740)
- Install_20022.exe (PID: 3892)
- AgreeablemSoft.exe (PID: 276)
- Install_20022.exe (PID: 3104)
- Install_20022.exe (PID: 3604)
- AgreeablerSoft.exe (PID: 2792)
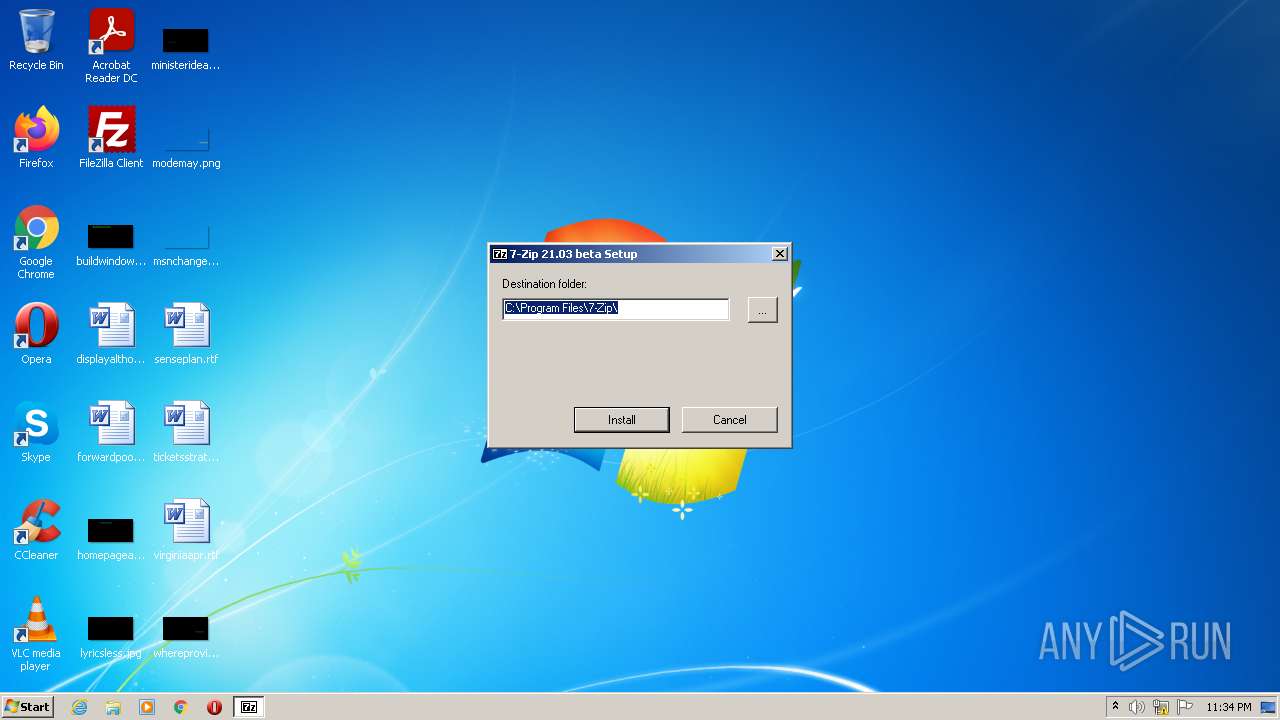
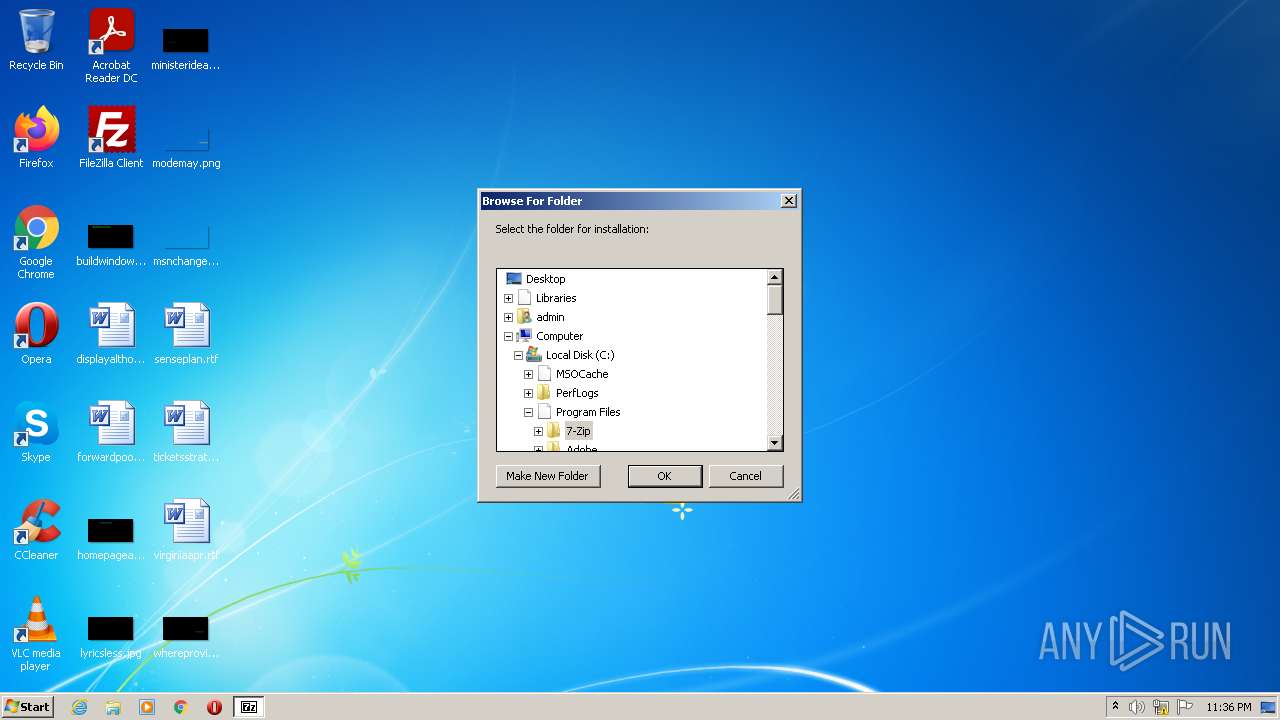
Creates a directory in Program Files
- Install_20022.exe (PID: 1740)
- AgreeablemSoft.exe (PID: 276)
- Install_20022.exe (PID: 3604)
Creates files in the program directory
- Install_20022.exe (PID: 1740)
- AgreeablemSoft.exe (PID: 276)
- Install_20022.exe (PID: 3604)
Executable content was dropped or overwritten
- Install_20022.exe (PID: 1740)
- AgreeablemSoft.exe (PID: 276)
- AgreeablerSoft.exe (PID: 2792)
- Install_20022.exe (PID: 3604)
Creates/Modifies COM task schedule object
- AgreeablemSoft.exe (PID: 276)
- AgreeablerSoft.exe (PID: 2792)
Creates a software uninstall entry
- AgreeablemSoft.exe (PID: 276)
- AgreeablerSoft.exe (PID: 2792)
INFO
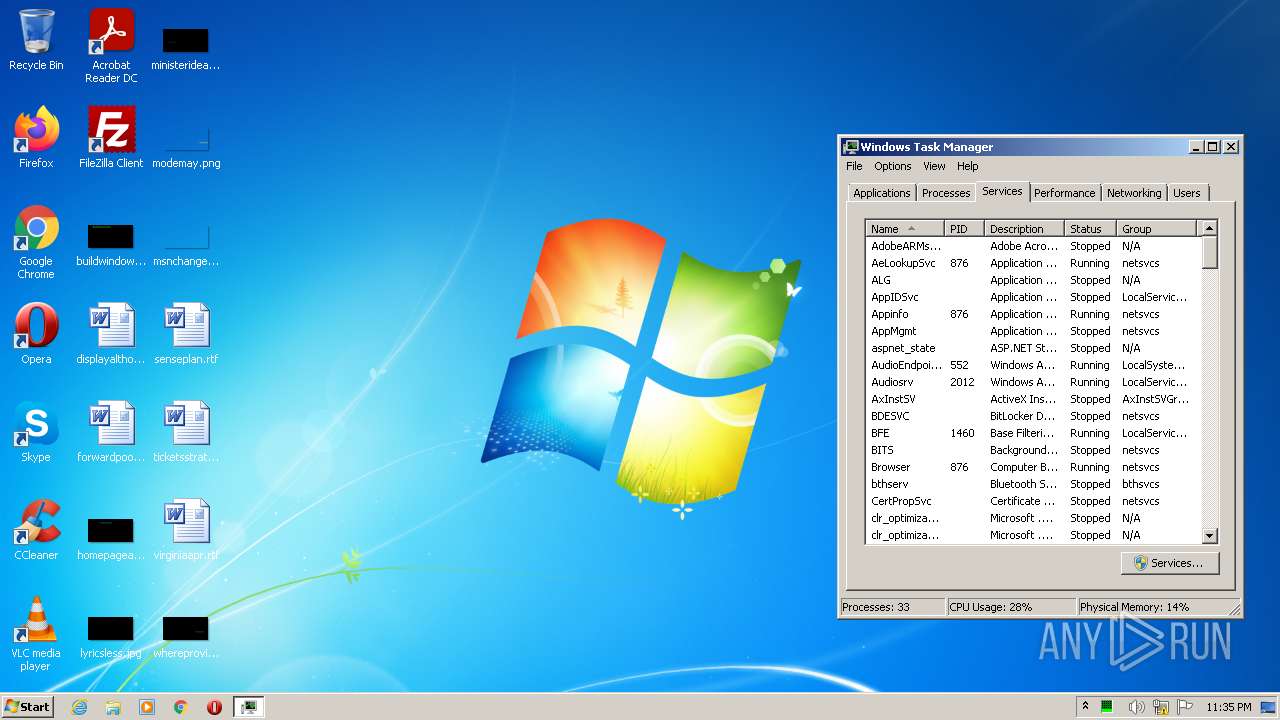
Reads the computer name
- taskmgr.exe (PID: 1388)
- consent.exe (PID: 1104)
- SearchProtocolHost.exe (PID: 1328)
Checks supported languages
- Explorer.EXE (PID: 612)
- consent.exe (PID: 1104)
- taskmgr.exe (PID: 1388)
- SearchProtocolHost.exe (PID: 1328)
Reads Microsoft Office registry keys
- Explorer.EXE (PID: 612)
Checks Windows Trust Settings
- consent.exe (PID: 1104)
Reads settings of System Certificates
- consent.exe (PID: 1104)
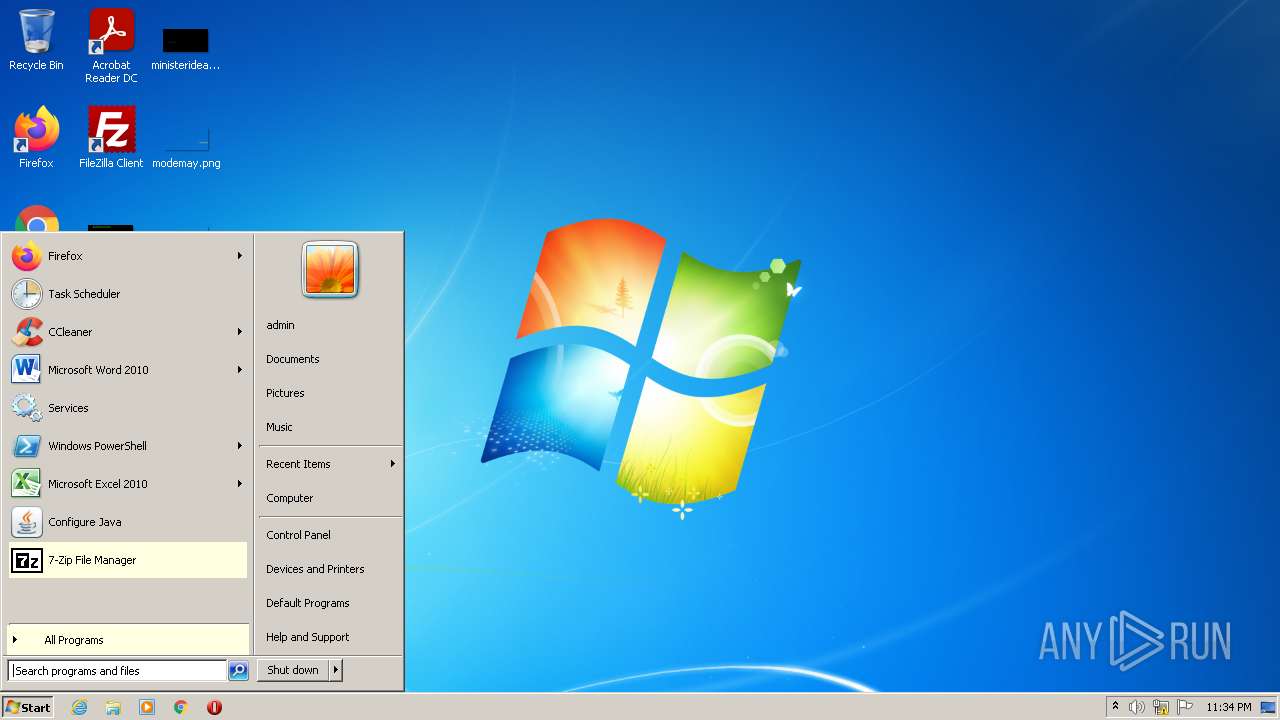
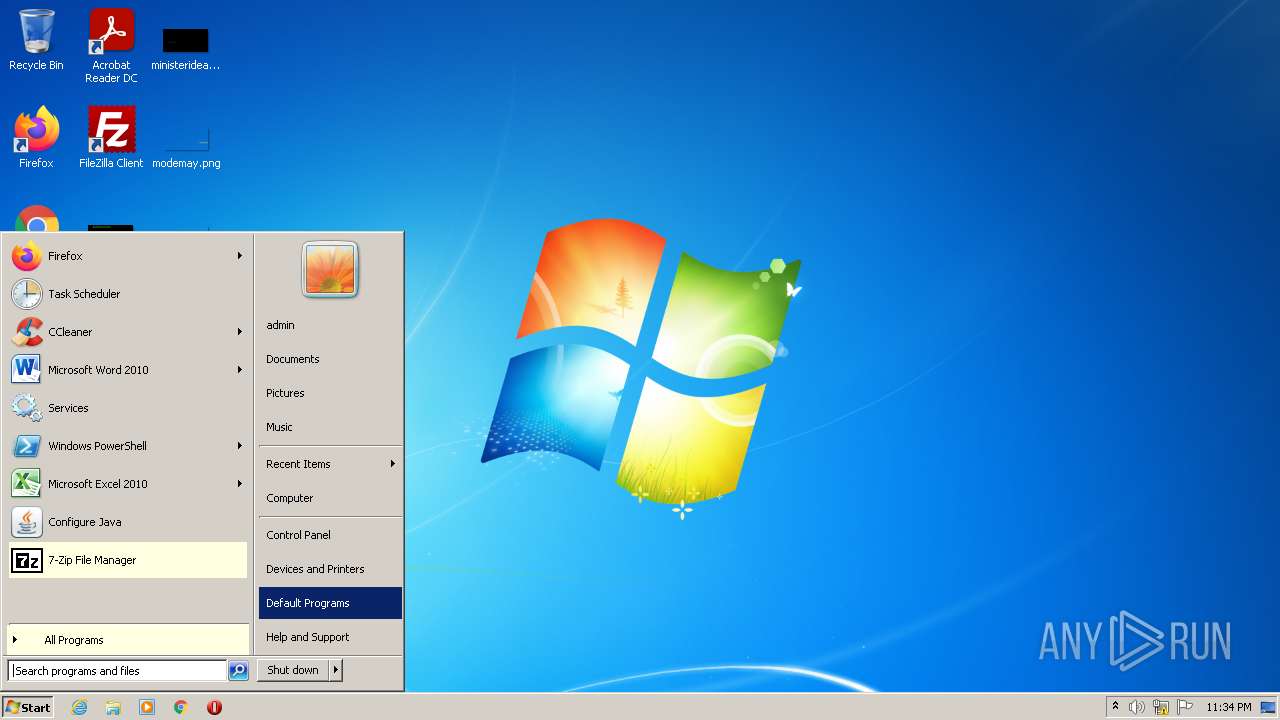
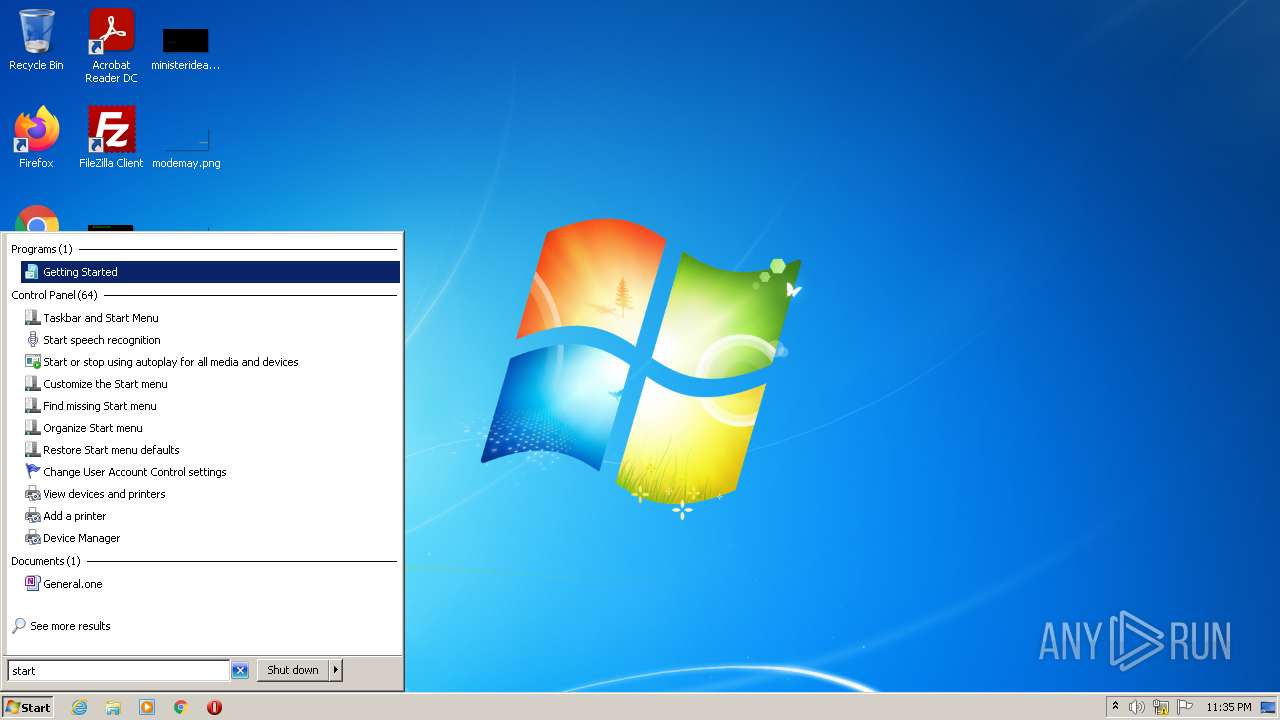
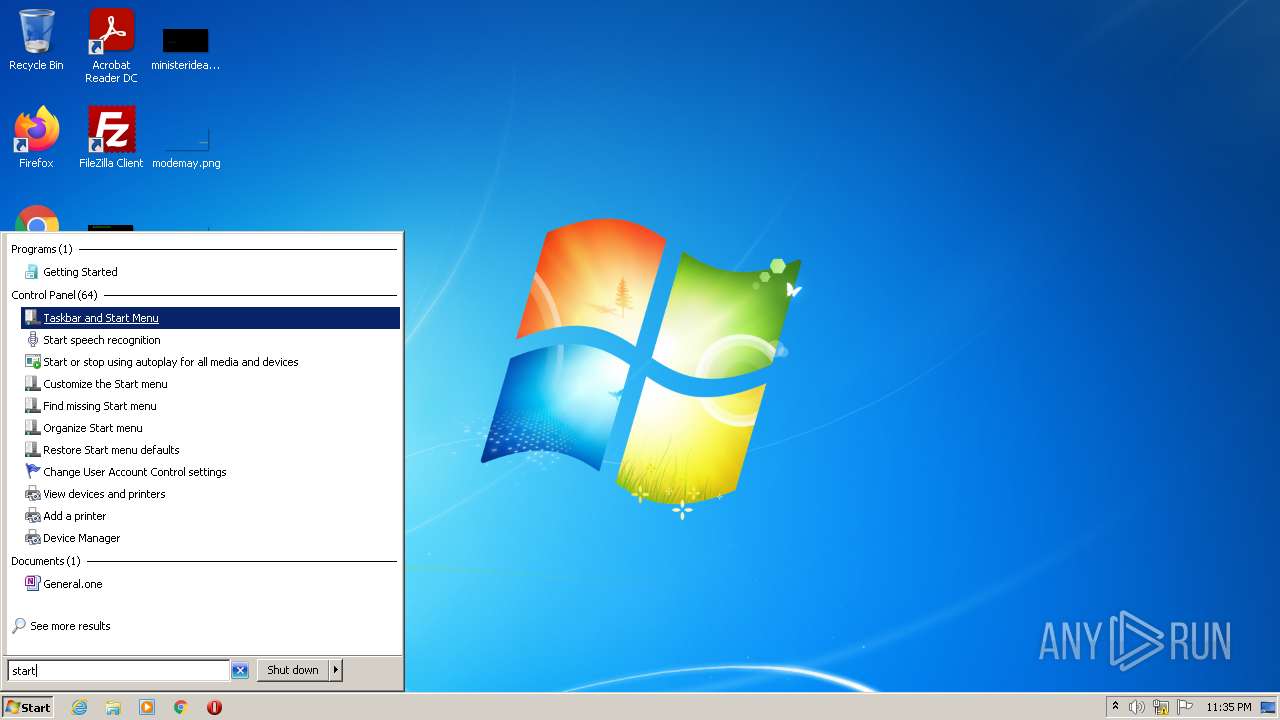
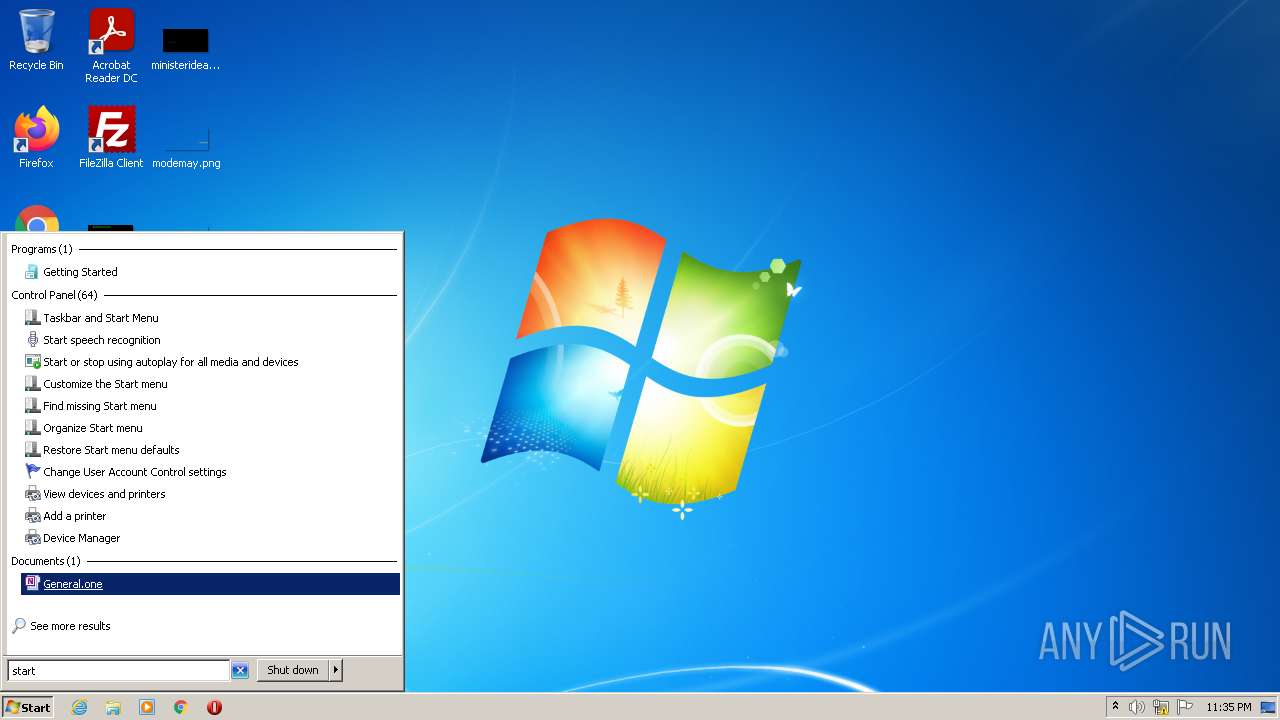
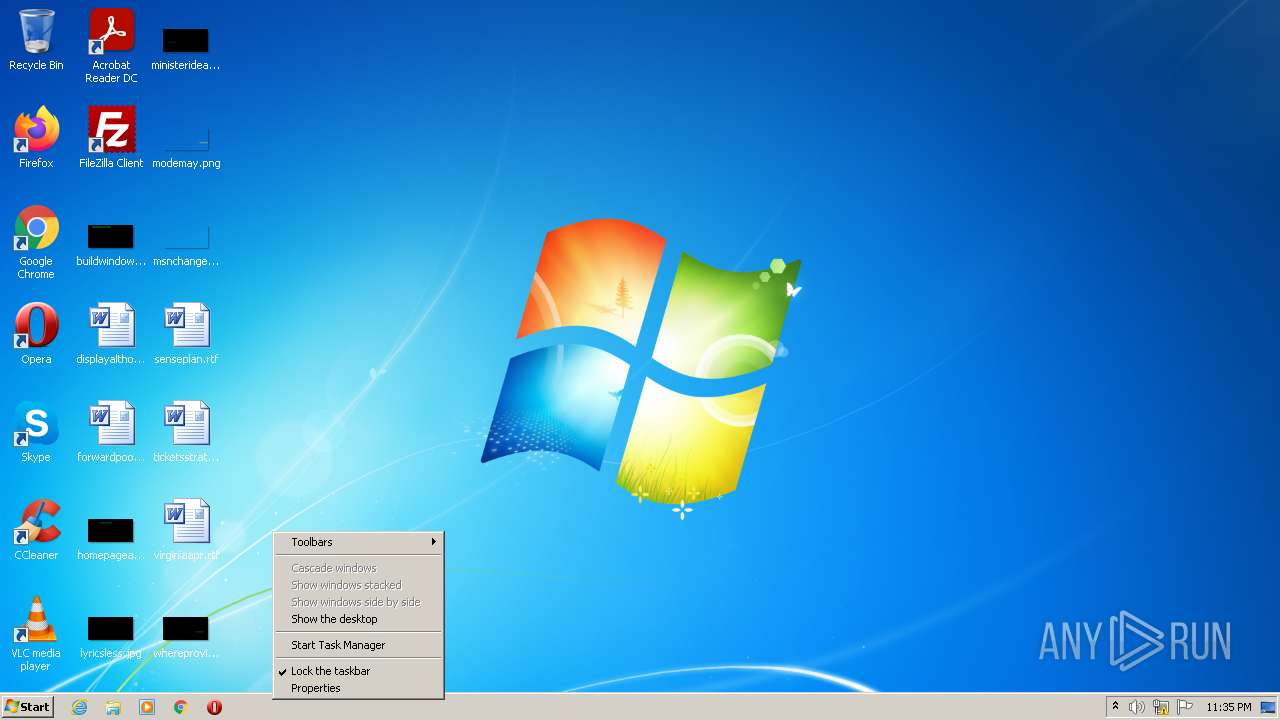
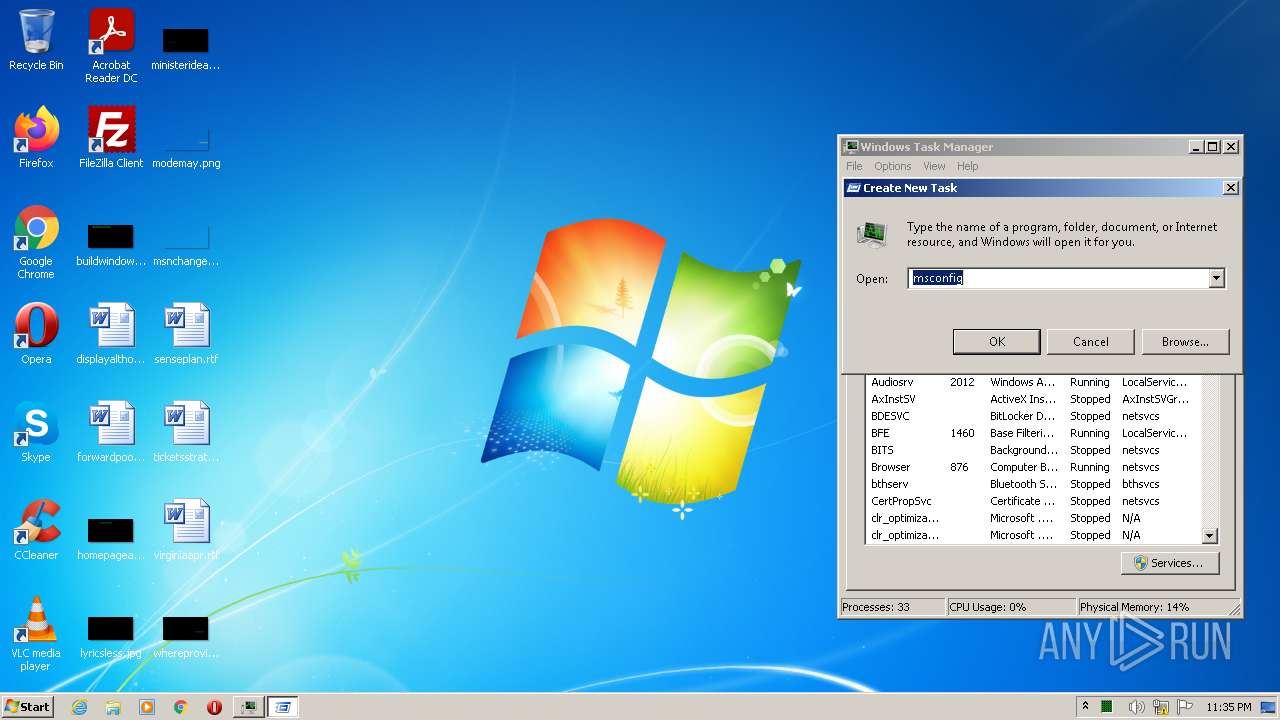
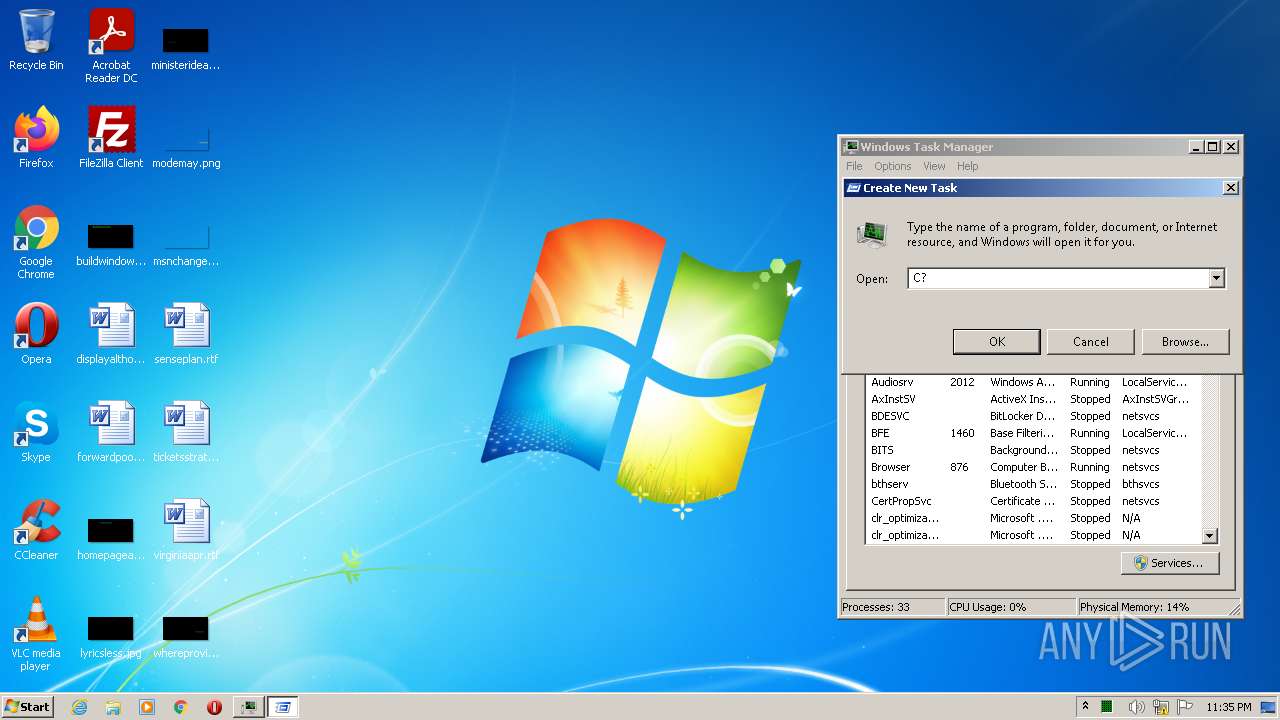
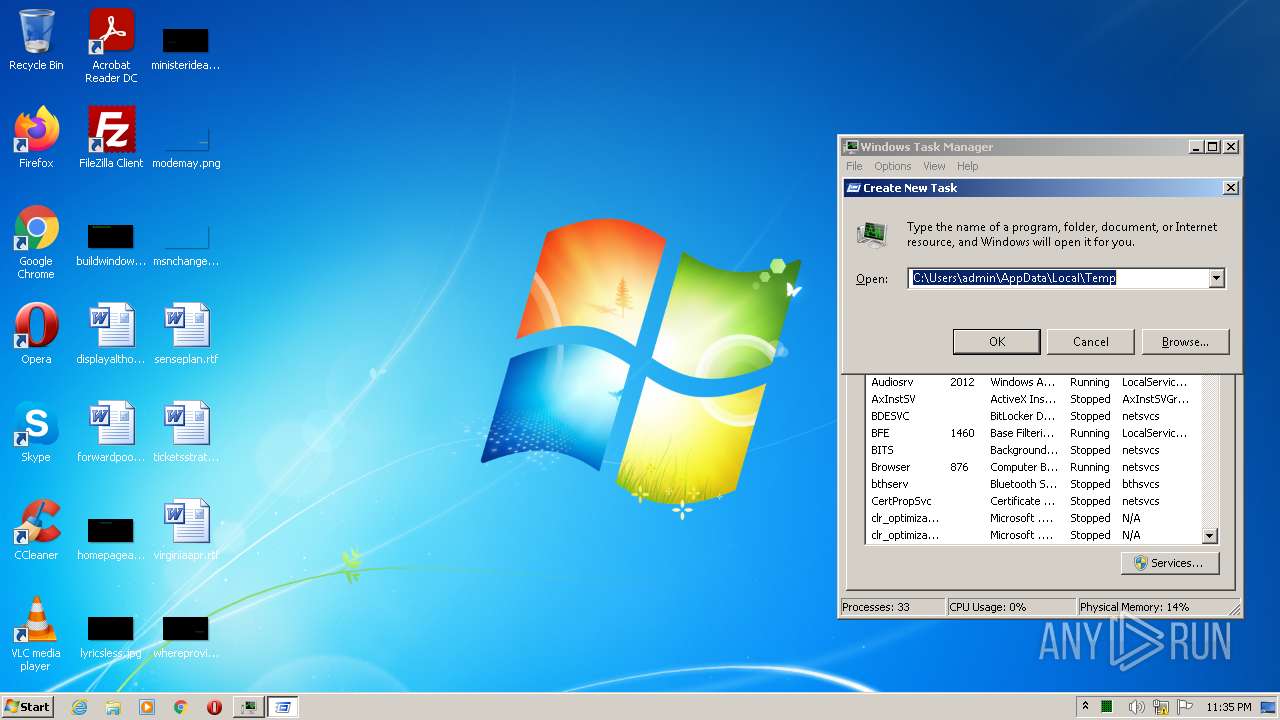
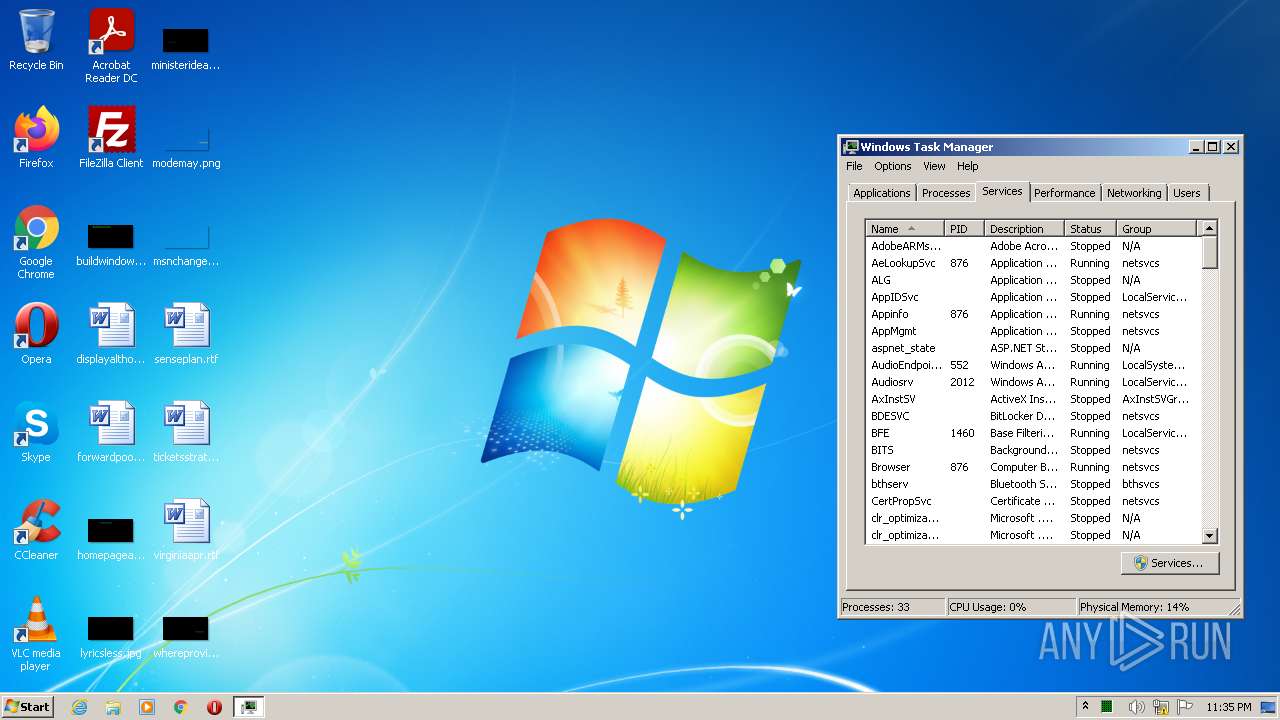
Manual execution by user
- taskmgr.exe (PID: 1388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (46.2) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (44.6) |
| .exe | | | Win32 Executable (generic) (4.8) |
| .exe | | | Generic Win/DOS Executable (2.1) |
| .exe | | | DOS Executable Generic (2.1) |
EXIF
EXE
| ProductVersion: | 1.0.0.0 |
|---|---|
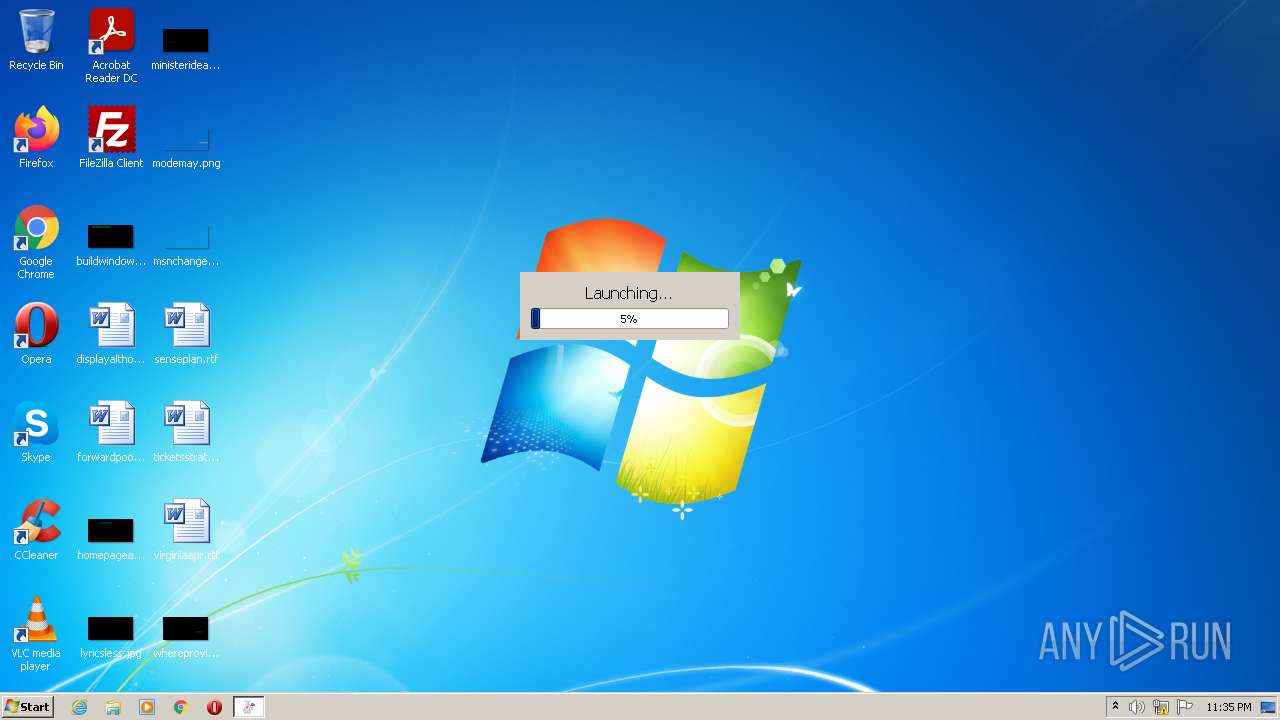
| ProductName: | Agreeable goldfish soft |
| OriginalFileName: | Agreeablegoldfishsoft.exe |
| LegalCopyright: | Agreeable goldfish soft Company. |
| InternalName: | Agreeablegoldfishsoft.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Agreeable goldfish soft |
| CompanyName: | Agreeable goldfish |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x5f3281 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 3850240 |
| CodeSize: | 6604800 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2022:02:18 19:06:22+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Feb-2022 18:06:22 |
| Detected languages: |
|
| CompanyName: | Agreeable goldfish |
| FileDescription: | Agreeable goldfish soft |
| FileVersion: | 1.0.0.0 |
| InternalName: | Agreeablegoldfishsoft.exe |
| LegalCopyright: | Agreeable goldfish soft Company. |
| OriginalFilename: | Agreeablegoldfishsoft.exe |
| ProductName: | Agreeable goldfish soft |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 18-Feb-2022 18:06:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0064C7EC | 0x0064C800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69505 |
.rdata | 0x0064E000 | 0x002EF4A0 | 0x002EF600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.26242 |
.data | 0x0093E000 | 0x00024260 | 0x00019E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.34607 |
.gfids | 0x00963000 | 0x0000021C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.48188 |
.tls | 0x00964000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.qtmetad\x95\x02 | 0x00965000 | 0x00000295 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.28268 |
.qtmimed\xe5\xec\x04 | 0x00966000 | 0x0004ECE5 | 0x0004EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.998 |
.rsrc | 0x009B5000 | 0x00010F58 | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.7284 |
.reloc | 0x009C6000 | 0x00037D04 | 0x00037E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58541 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06467 | 638 | UNKNOWN | English - United States | RT_MANIFEST |
IDI_ICON1 | 1.98048 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
NETAPI32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
USERENV.dll |
Total processes
50
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\AgreeablegoldfishqrfSoft\AgreeablemSoft.exe" | C:\Program Files\AgreeablegoldfishqrfSoft\AgreeablemSoft.exe | Install_20022.exe | ||||||||||||
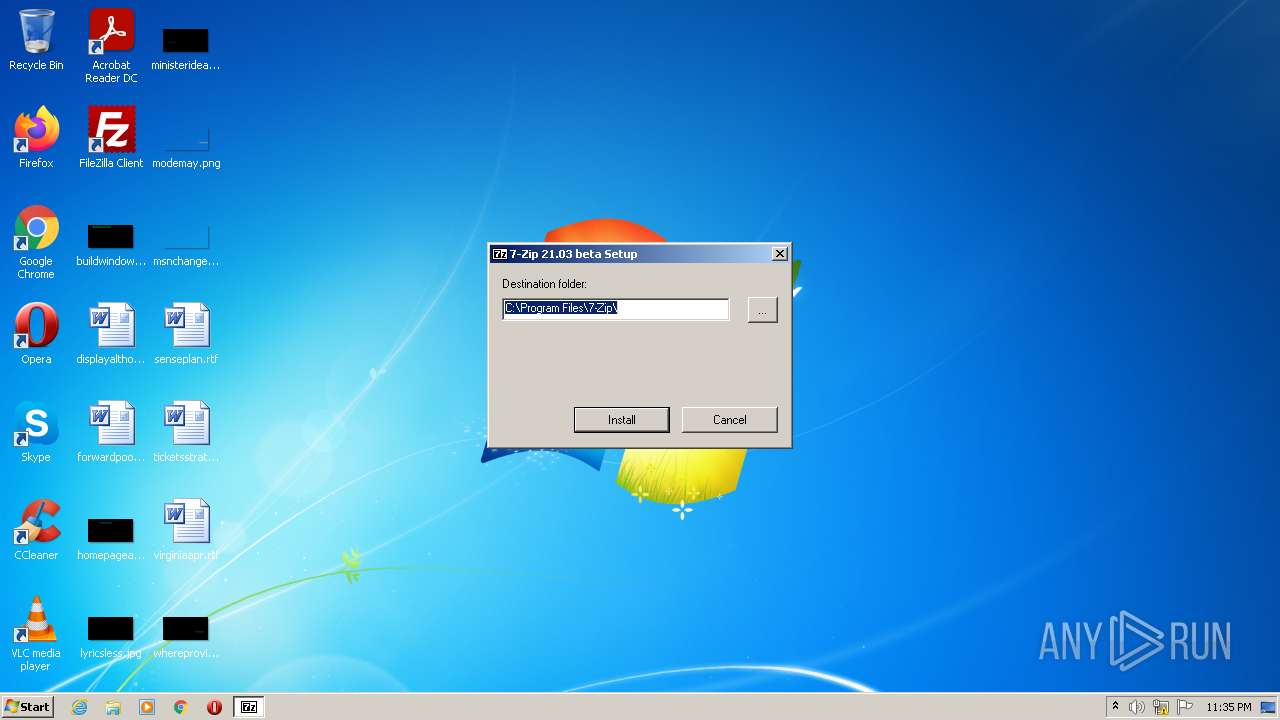
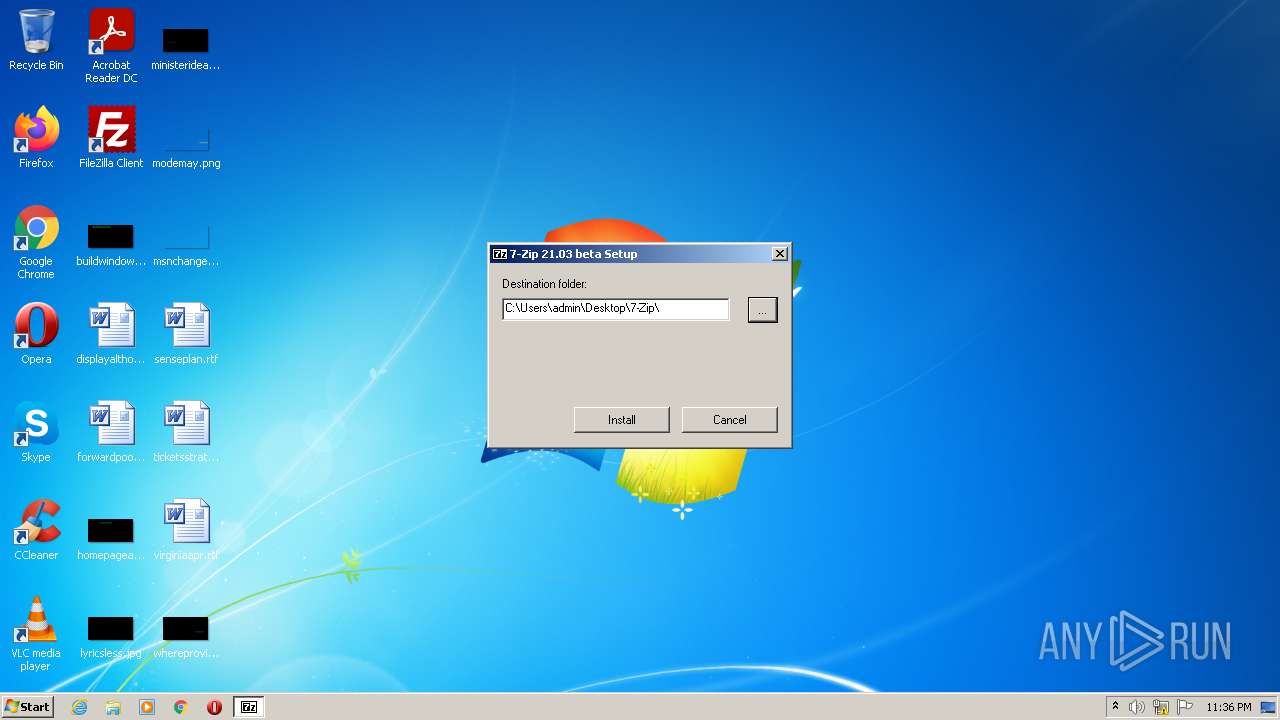
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 21.03 beta Modules
| |||||||||||||||
| 612 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1104 | consent.exe 876 384 022D6740 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1328 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 1388 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | "C:\Users\admin\AppData\Local\Temp\Install_20022.exe" -dam /tx | C:\Users\admin\AppData\Local\Temp\Install_20022.exe | Install_20022.exe | ||||||||||||
User: admin Company: Agreeable goldfish Integrity Level: HIGH Description: Agreeable goldfish soft Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2792 | "C:\Program Files\AgreeablegoldfishzebSoft\AgreeablerSoft.exe" | C:\Program Files\AgreeablegoldfishzebSoft\AgreeablerSoft.exe | Install_20022.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 21.03 beta Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\AppData\Local\Temp\Install_20022.exe" | C:\Users\admin\AppData\Local\Temp\Install_20022.exe | Explorer.EXE | ||||||||||||
User: admin Company: Agreeable goldfish Integrity Level: HIGH Description: Agreeable goldfish soft Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3604 | "C:\Users\admin\AppData\Local\Temp\Install_20022.exe" -dam /tx | C:\Users\admin\AppData\Local\Temp\Install_20022.exe | Install_20022.exe | ||||||||||||
User: admin Company: Agreeable goldfish Integrity Level: HIGH Description: Agreeable goldfish soft Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
23 523
Read events
22 312
Write events
1 207
Delete events
4
Modification events
| (PID) Process: | (3892) Install_20022.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Install_20022.exe | |||
| (PID) Process: | (612) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Vafgnyy_20022.rkr |
Value: 00000000000000000100000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (612) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000480100007C0200001C6B17013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01 | |||
| (PID) Process: | (3892) Install_20022.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3892) Install_20022.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3892) Install_20022.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3892) Install_20022.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (876) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 2 | |||
| (PID) Process: | (876) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 1 | |||
| (PID) Process: | (1740) Install_20022.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Install_20022.exe | |||
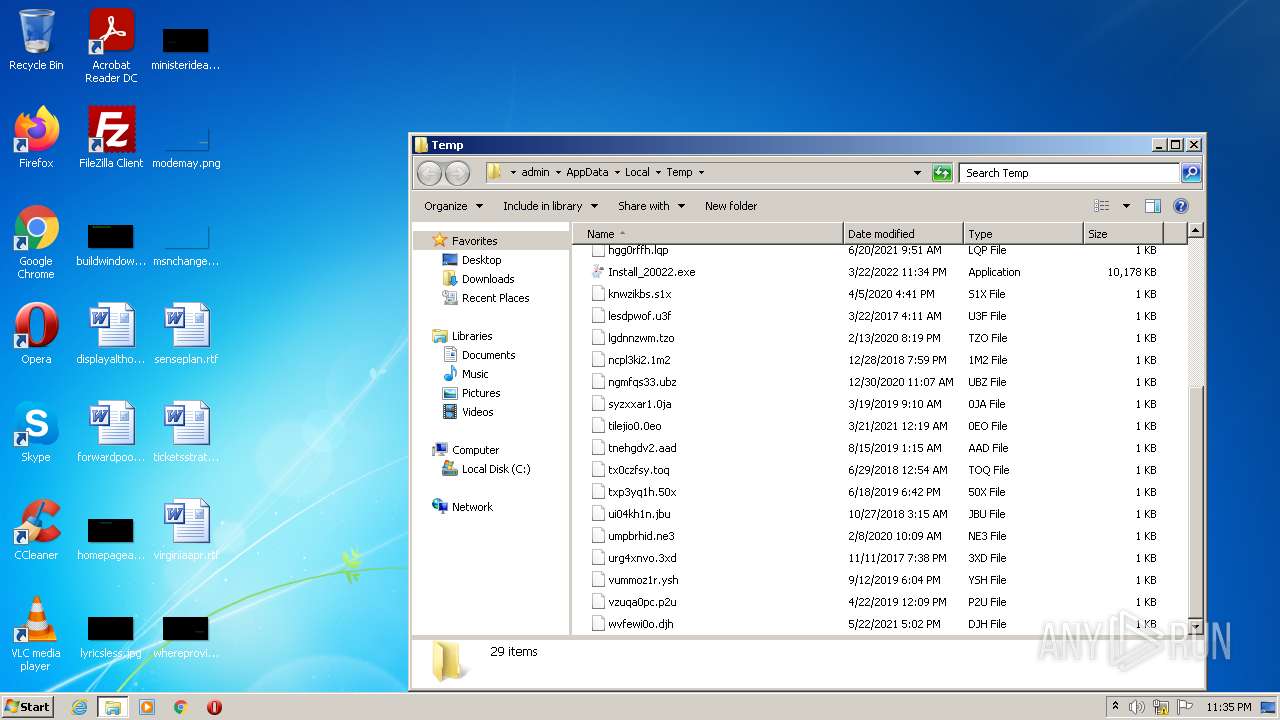
Executable files
18
Suspicious files
0
Text files
194
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 876 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
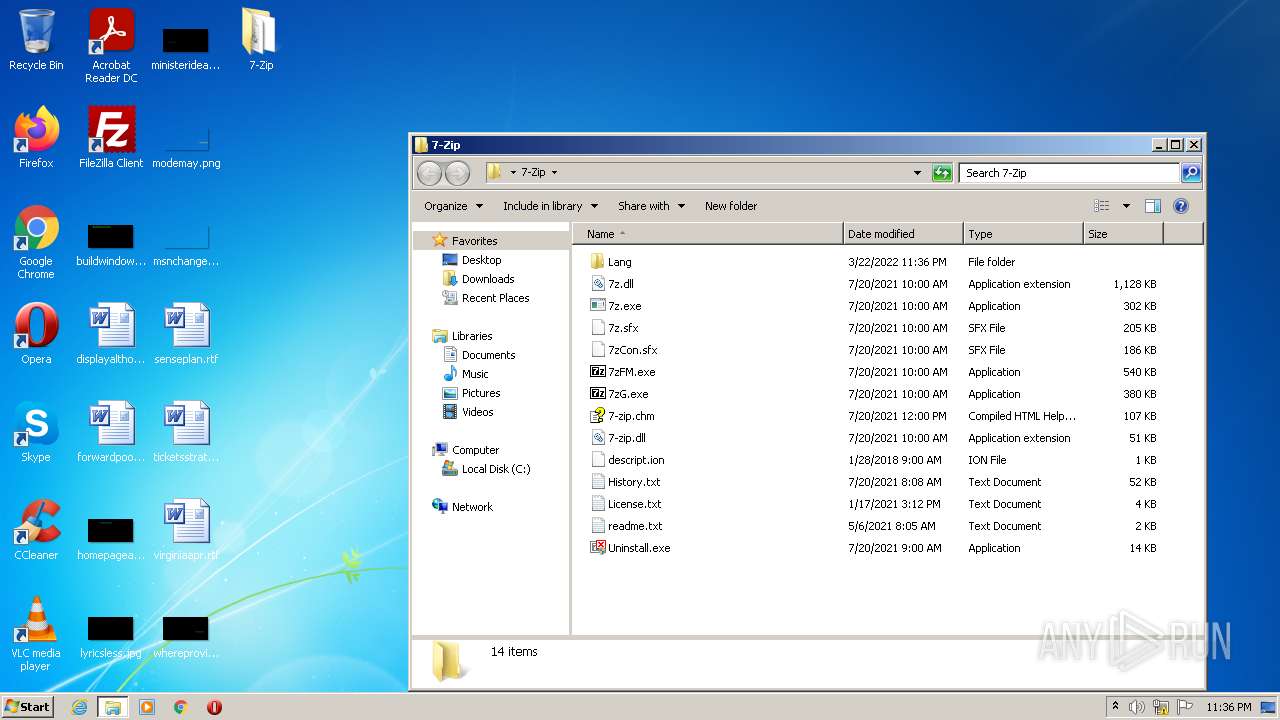
| 276 | AgreeablemSoft.exe | C:\Program Files\7-Zip\descript.ion | text | |
MD5:EB7E322BDC62614E49DED60E0FB23845 | SHA256:1DA513F5A4E8018B9AE143884EB3EAF72454B606FD51F2401B7CFD9BE4DBBF4F | |||
| 276 | AgreeablemSoft.exe | C:\Program Files\7-Zip\History.txt | text | |
MD5:9EBDE31BD2CD85CD81DCD76977318B8A | SHA256:C588599CAA710A918E330D41A41A5BA876BE7BB5CBCE1A43D7793586410CD6A2 | |||
| 276 | AgreeablemSoft.exe | C:\Program Files\7-Zip\Lang\ast.txt | text | |
MD5:1F86AE235BC747A279C9E9EC72675CE4 | SHA256:8FCD1B8CE6FED05F406C4B81AEA821132800BC494D3FD6F42A4258A81F8998EC | |||
| 276 | AgreeablemSoft.exe | C:\Program Files\7-Zip\7-zip.chm | chm | |
MD5:2968879E0E6AC82FE3EB5E5A09E9BE34 | SHA256:CCCCFD236FAD1FC054829A549AFE1A9C7E0E04D4C0AC7DF38E52DD8546E99ACF | |||
| 276 | AgreeablemSoft.exe | C:\Program Files\7-Zip\Lang\az.txt | text | |
MD5:81B732A8B4206FB747BFBFE524DDE192 | SHA256:CAEC460E73BD0403C2BCDE7E773459BEA9112D1BFACBE413D4F21E51A5762BA6 | |||
| 276 | AgreeablemSoft.exe | C:\Program Files\7-Zip\Lang\ba.txt | text | |
MD5:D83B65AC086DA0C94D6EB57BEE669C2B | SHA256:2901B54F7621C95429658CB4EDB28ABD0CB5B6E257C7D9A364FC468A8B86BAAE | |||
| 276 | AgreeablemSoft.exe | C:\Program Files\7-Zip\Lang\be.txt | text | |
MD5:3C21135144AC7452E7DB66F0214F9D68 | SHA256:D095879B8BBC67A1C9875C5E9896942BACF730BD76155C06105544408068C59E | |||
| 276 | AgreeablemSoft.exe | C:\Program Files\7-Zip\Lang\af.txt | text | |
MD5:FBBE51ACB879B525CC6B19D386697924 | SHA256:3793FB69EE9FD958CF15A272B1ED54E4B3D75592836EBCD085DC0E7B1400D1CB | |||
| 276 | AgreeablemSoft.exe | C:\Program Files\7-Zip\Lang\ar.txt | text | |
MD5:1C45E6A6ECB3B71A7316C466B6A77C1C | SHA256:972261B53289DE2BD8A65E787A6E7CD6DEFC2B5F7E344128F2FE0492ED30CCF1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1740 | Install_20022.exe | 172.67.74.159:443 | onlysoftwaresolutions.com | — | US | suspicious |
3604 | Install_20022.exe | 172.67.74.159:443 | onlysoftwaresolutions.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onlysoftwaresolutions.com |
| suspicious |