| File name: | notmyfault.exe |
| Full analysis: | https://app.any.run/tasks/df9d24c4-bac2-4e21-9a47-8a50865e9c9c |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 22:33:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D41D8CD98F00B204E9800998ECF8427E |
| SHA1: | F5C95CE60E17F6C46F0EB2B0E292AD28AFEB04D1 |
| SHA256: | EAF59DFECBD26A8817237C56EB631C7E8CAE110CAD2CADDDE6082B7596D760A5 |
| SSDEEP: | 6144:xKXGoFVXuA1c24rBcpMcwWq23LaERKcfdZYvG3wHABCjO0fcyJi:oGyVXuAm2sBcpMcT3LtHfSJU6i |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- notmyfault.exe (PID: 1304)
Reads the computer name
- notmyfault.exe (PID: 1304)
Creates files in the driver directory
- notmyfault.exe (PID: 1304)
Creates files in the Windows directory
- notmyfault.exe (PID: 1304)
Executable content was dropped or overwritten
- notmyfault.exe (PID: 1304)
Reads Environment values
- notmyfault.exe (PID: 1304)
Drops a file that was compiled in debug mode
- notmyfault.exe (PID: 1304)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 4.2 |
|---|---|
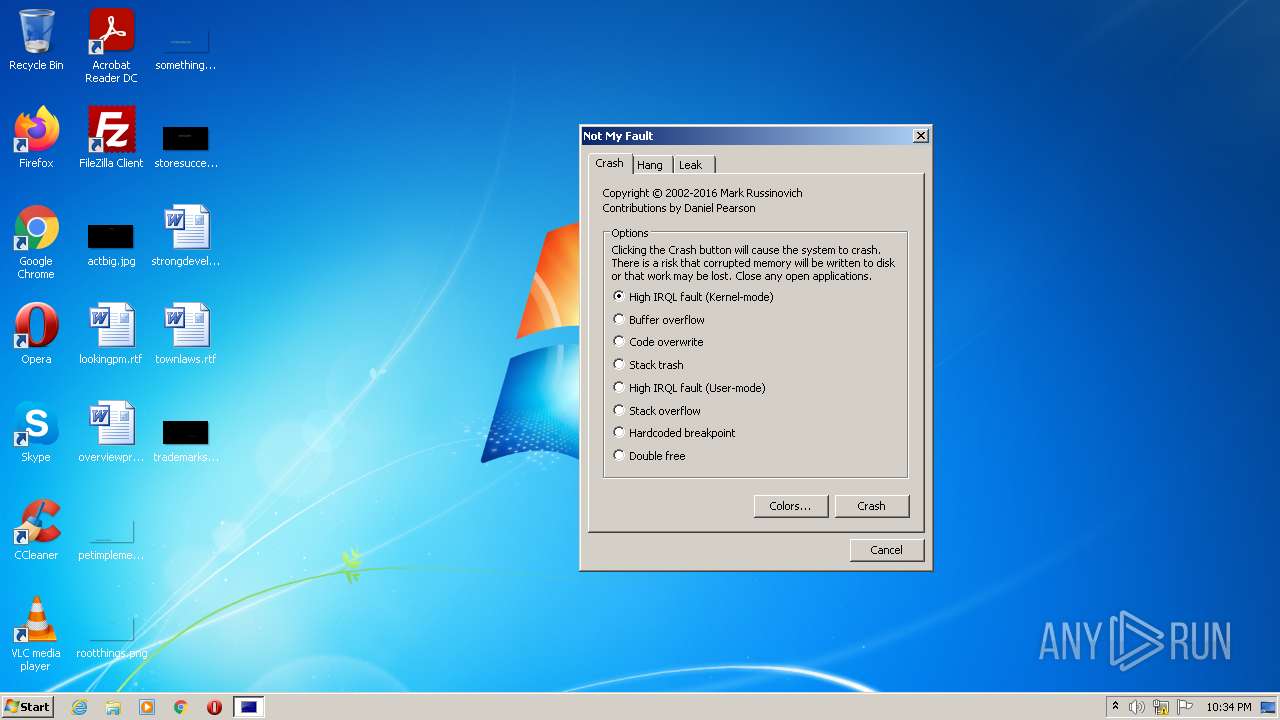
| ProductName: | Sysinternals NotMyfault |
| OriginalFileName: | NotMyfault.exe |
| LegalCopyright: | Copyright (C) 2002-2019 Mark Russinovich |
| InternalName: | Sysinternals NotMyfault |
| FileVersion: | 4.2 |
| FileDescription: | Driver Bug Test Program |
| CompanyName: | Sysinternals - www.sysinternals.com |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 4.20.0.0 |
| FileVersionNumber: | 4.20.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x489a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 183808 |
| CodeSize: | 321024 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2019:06:12 20:41:42+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Jun-2019 18:41:42 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Driver Bug Test Program |
| FileVersion: | 4.20 |
| InternalName: | Sysinternals NotMyfault |
| LegalCopyright: | Copyright (C) 2002-2019 Mark Russinovich |
| OriginalFilename: | NotMyfault.exe |
| ProductName: | Sysinternals NotMyfault |
| ProductVersion: | 4.20 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Jun-2019 18:41:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004E520 | 0x0004E600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60667 |
.rdata | 0x00050000 | 0x00010C06 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00565 |
.data | 0x00061000 | 0x00001E3C | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.07385 |
.rsrc | 0x00063000 | 0x00017520 | 0x00017600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.98138 |
.reloc | 0x0007B000 | 0x00002908 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65678 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05508 | 649 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.21081 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 1.98655 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 7.97767 | 41520 | UNKNOWN | English - United States | RT_ICON |
5 | 4.18492 | 9640 | UNKNOWN | English - United States | RT_ICON |
6 | 4.56482 | 4264 | UNKNOWN | English - United States | RT_ICON |
7 | 4.31149 | 1128 | UNKNOWN | English - United States | RT_ICON |
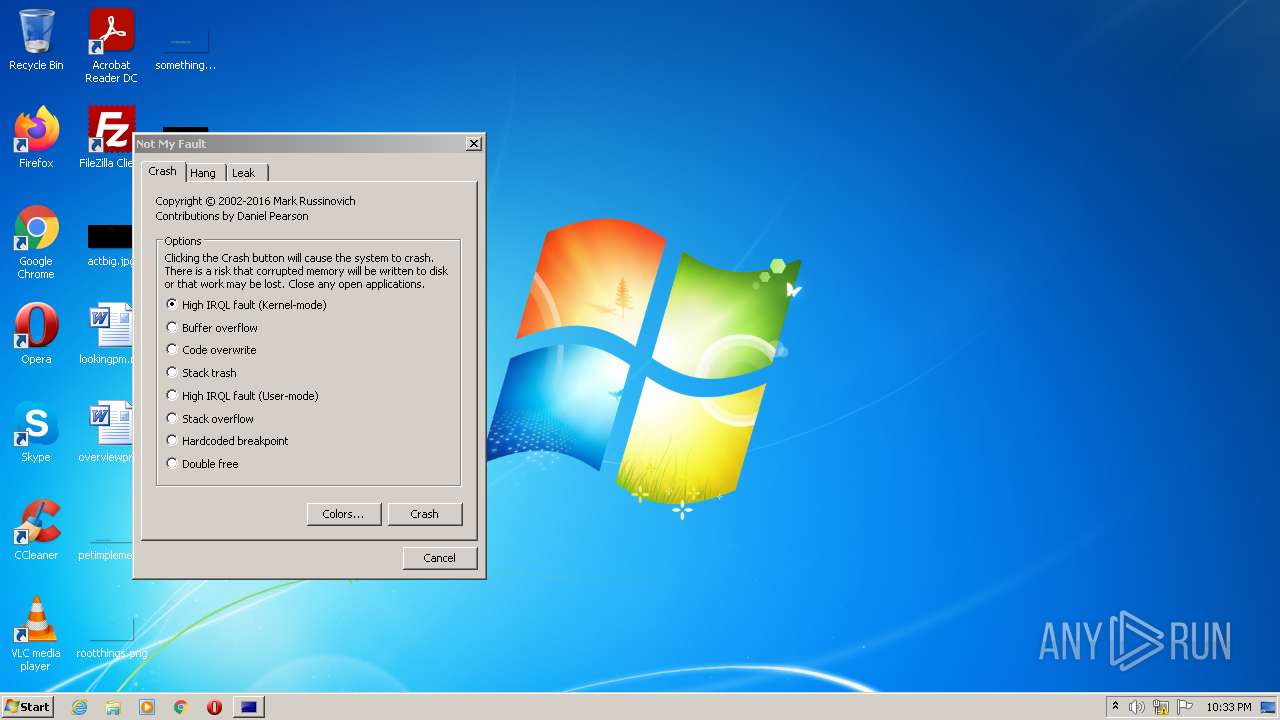
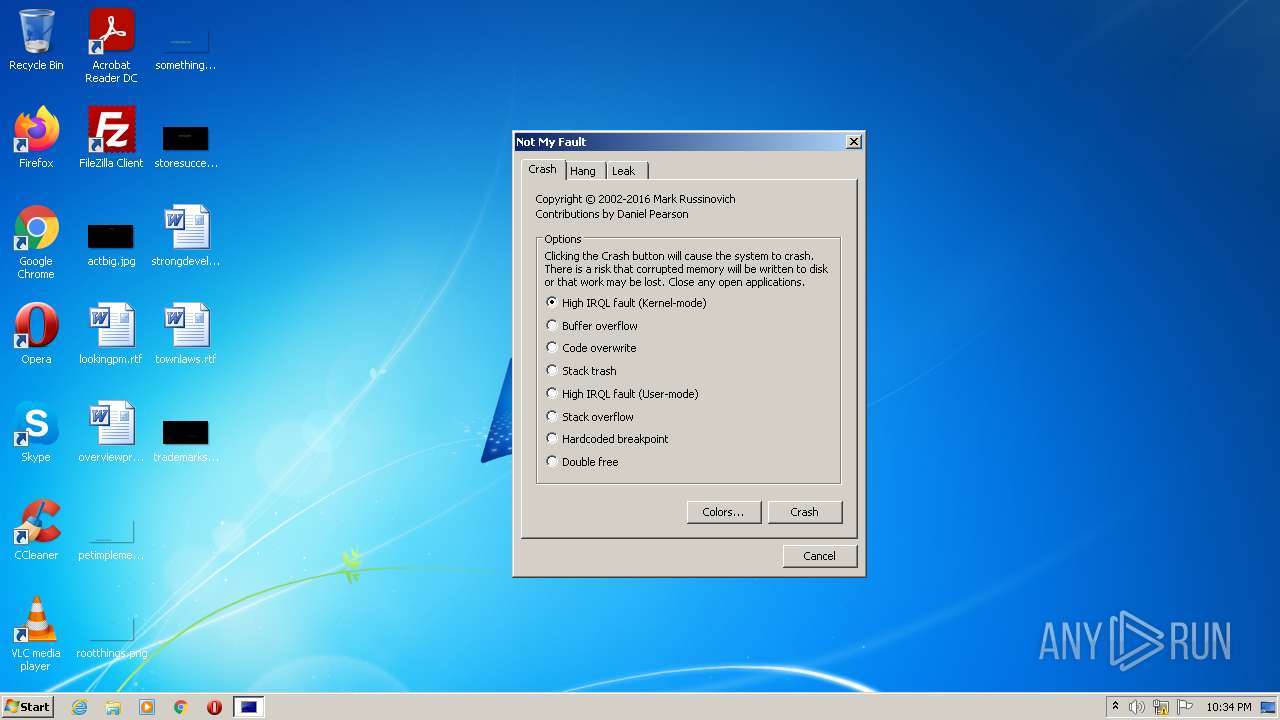
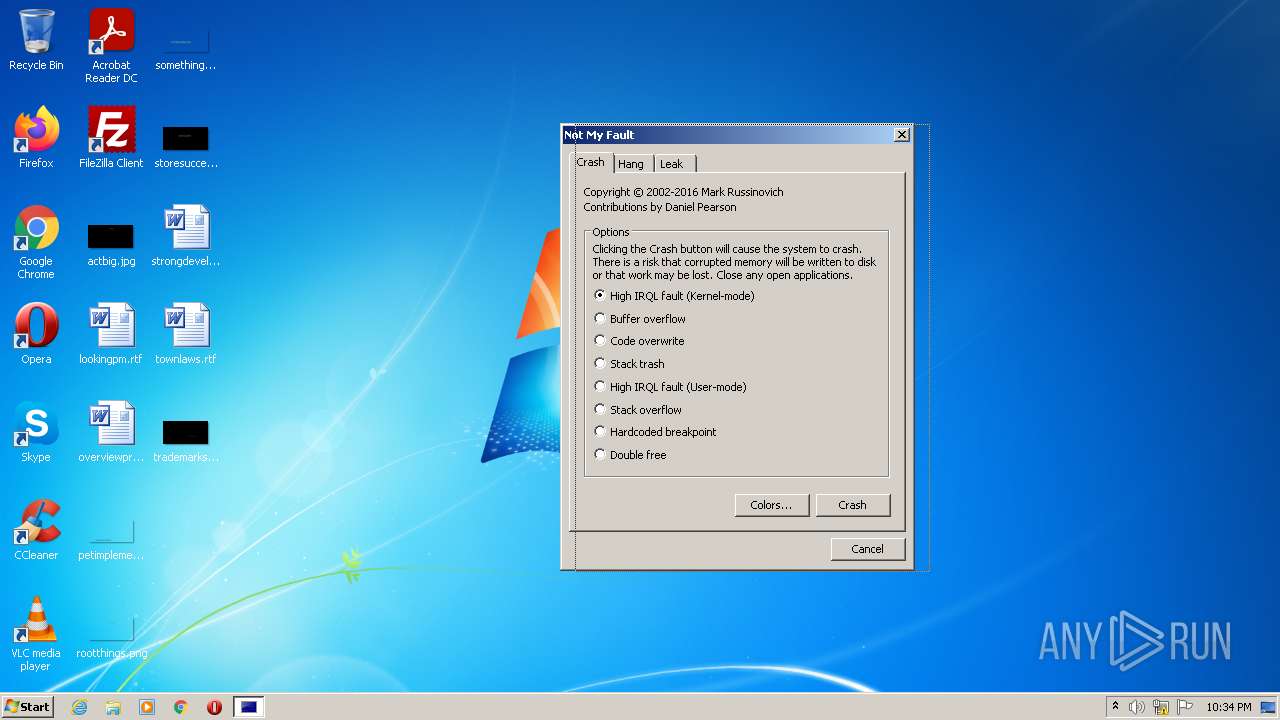
CRASH | 3.44677 | 1364 | UNKNOWN | English - United States | RT_DIALOG |
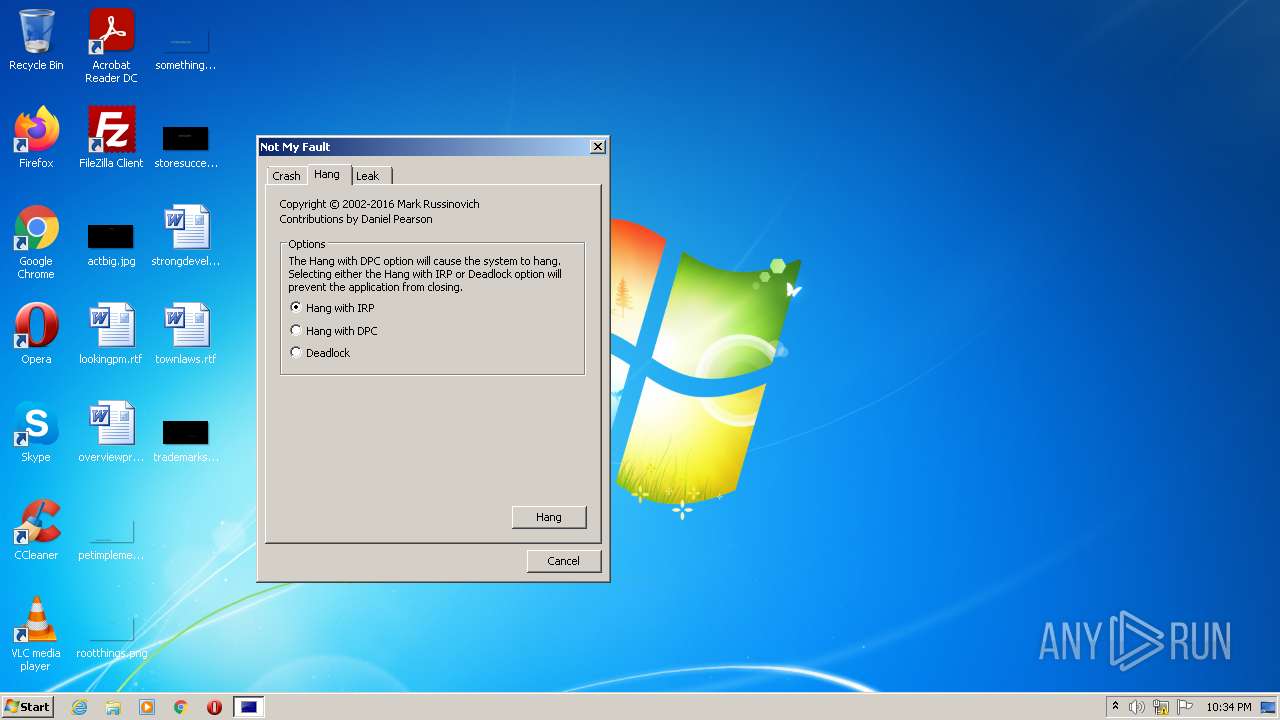
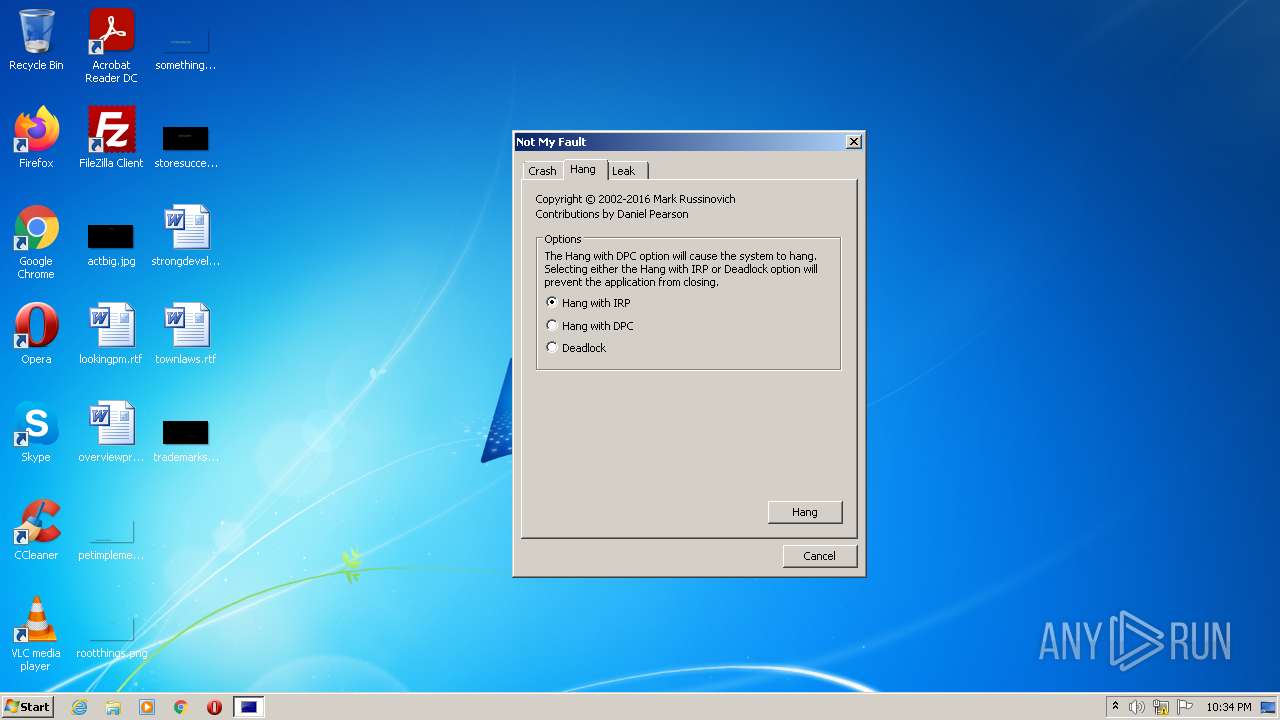
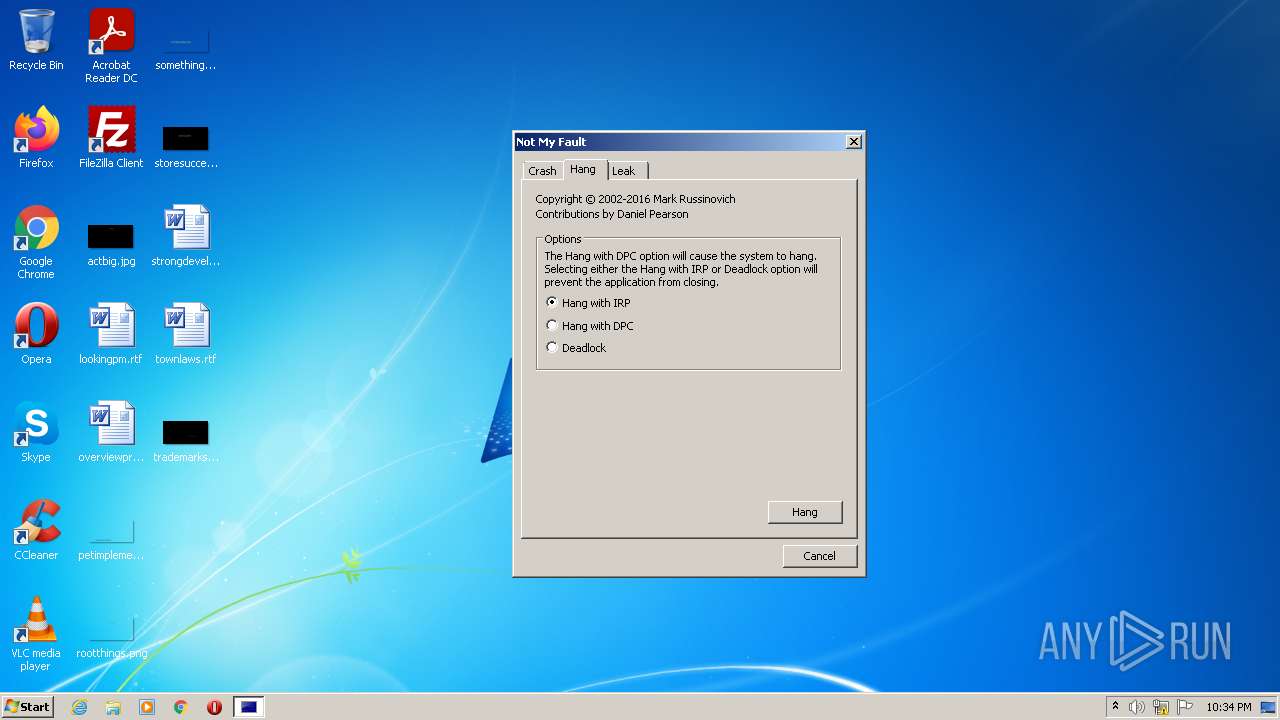
HANG | 3.38146 | 878 | UNKNOWN | English - United States | RT_DIALOG |
LEAK | 3.38596 | 1204 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll |
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1304 | "C:\Users\admin\AppData\Local\Temp\notmyfault.exe" | C:\Users\admin\AppData\Local\Temp\notmyfault.exe | Explorer.EXE | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Driver Bug Test Program Exit code: 0 Version: 4.20 Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\notmyfault.exe" | C:\Users\admin\AppData\Local\Temp\notmyfault.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Driver Bug Test Program Exit code: 3221226540 Version: 4.20 Modules
| |||||||||||||||
Total events
124
Read events
123
Write events
1
Delete events
0
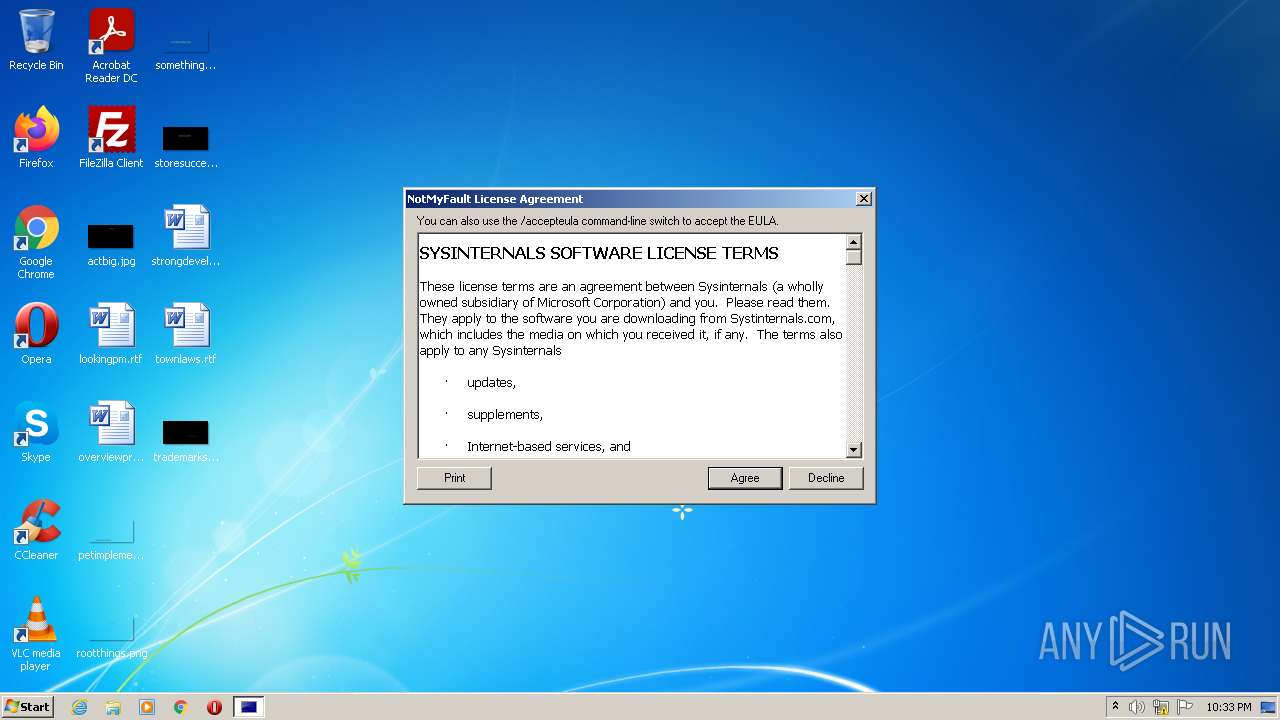
Modification events
| (PID) Process: | (1304) notmyfault.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\NotMyFault |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
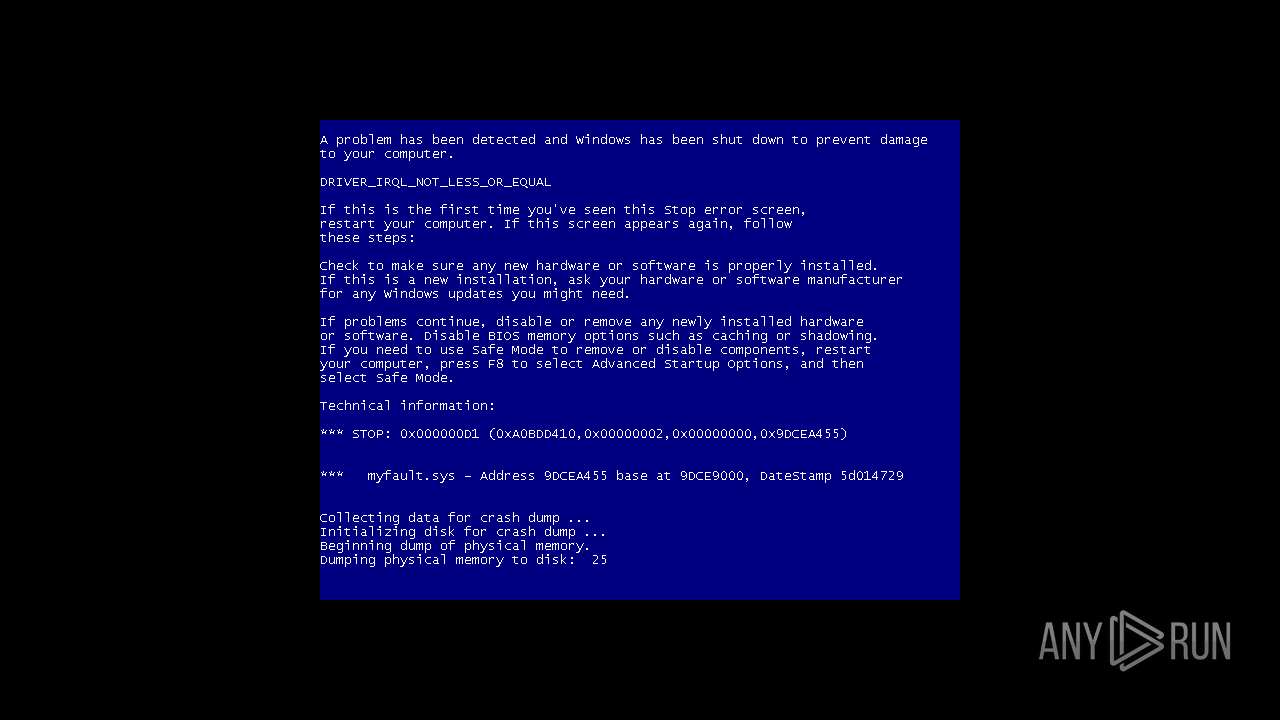
| 1304 | notmyfault.exe | C:\Windows\system32\drivers\myfault.sys | executable | |
MD5:BBE0B398C16C9F443A99688405A3541E | SHA256:1DC565BD6DCC2E4D1915B1FD660AFB7253BF9907CEE29FF2EB4E49DF46E6417A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report