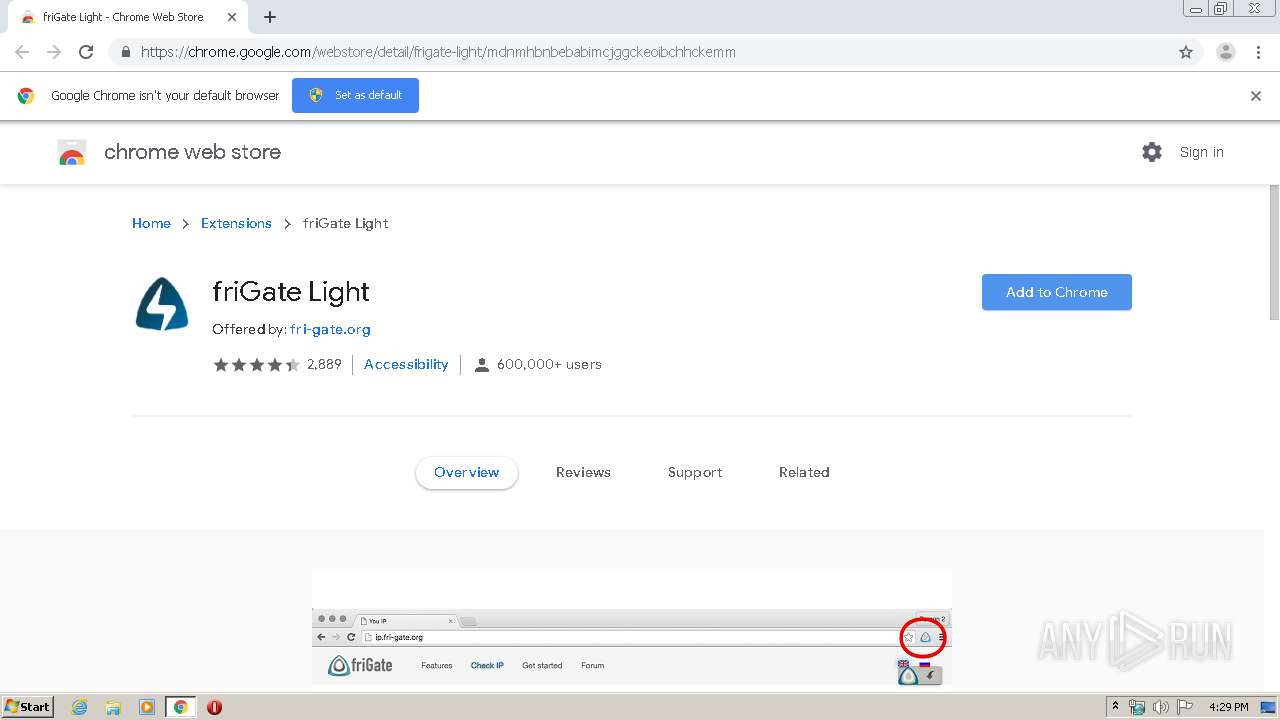
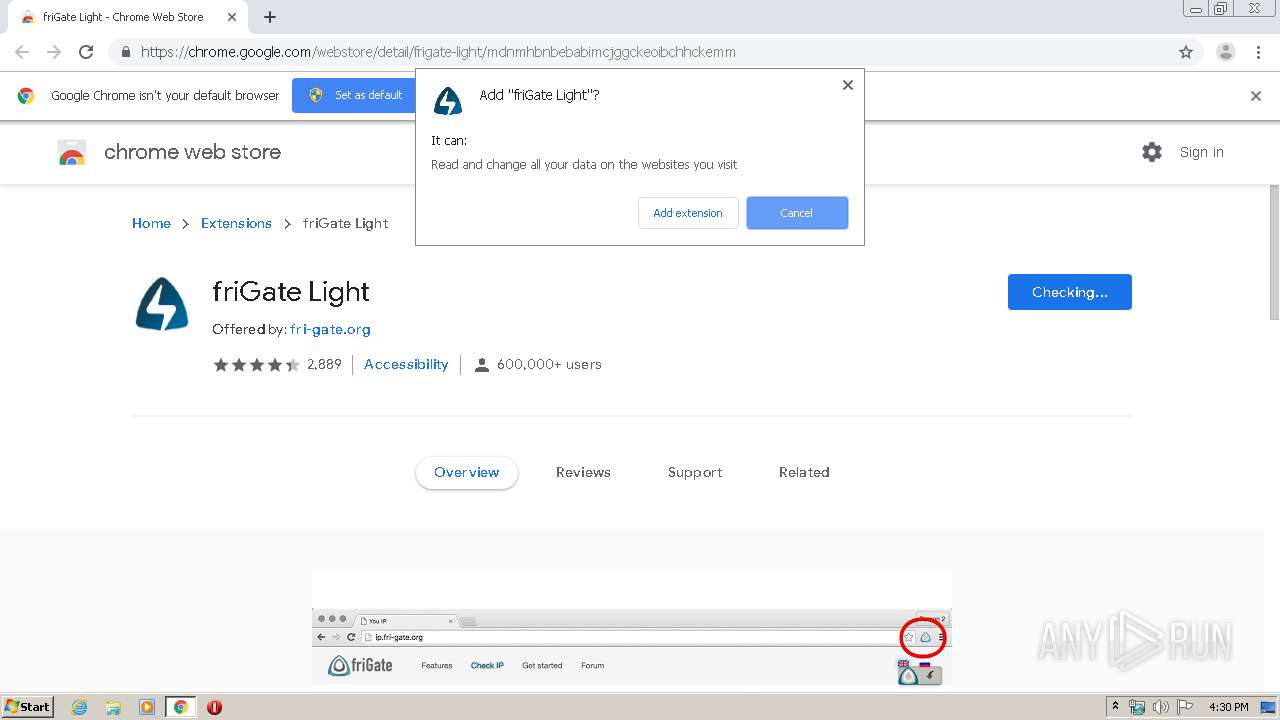
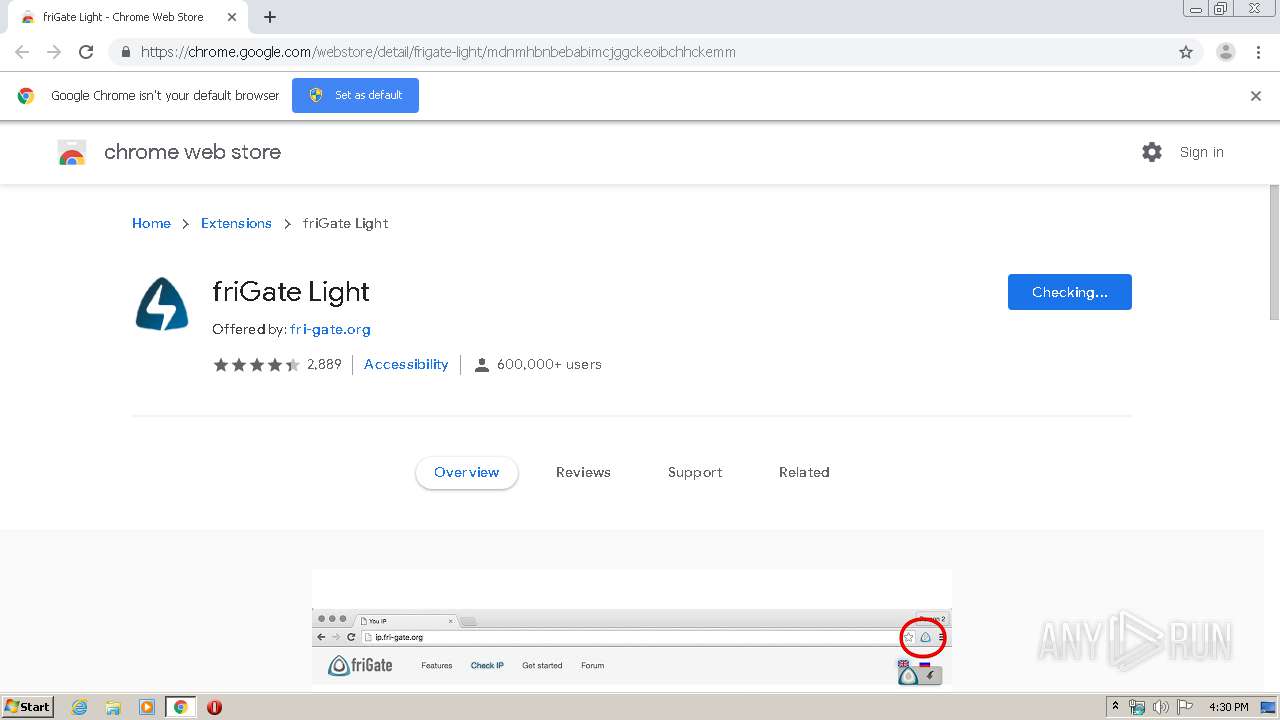
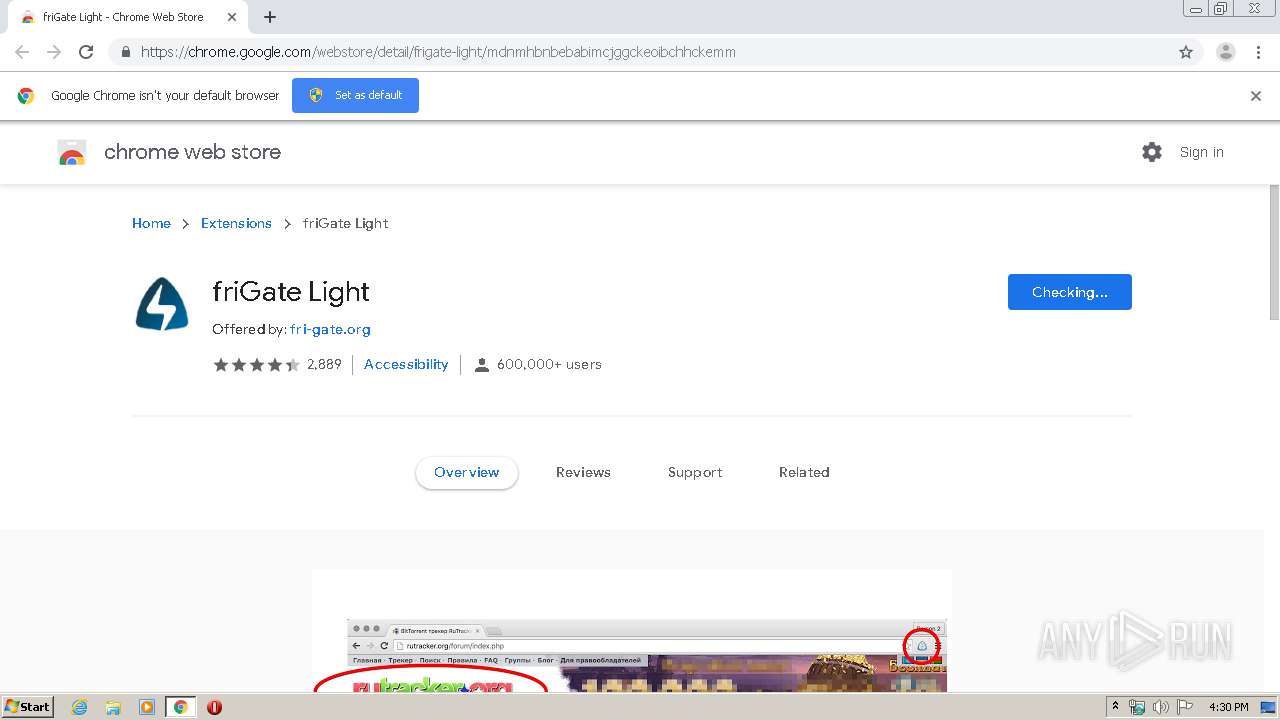
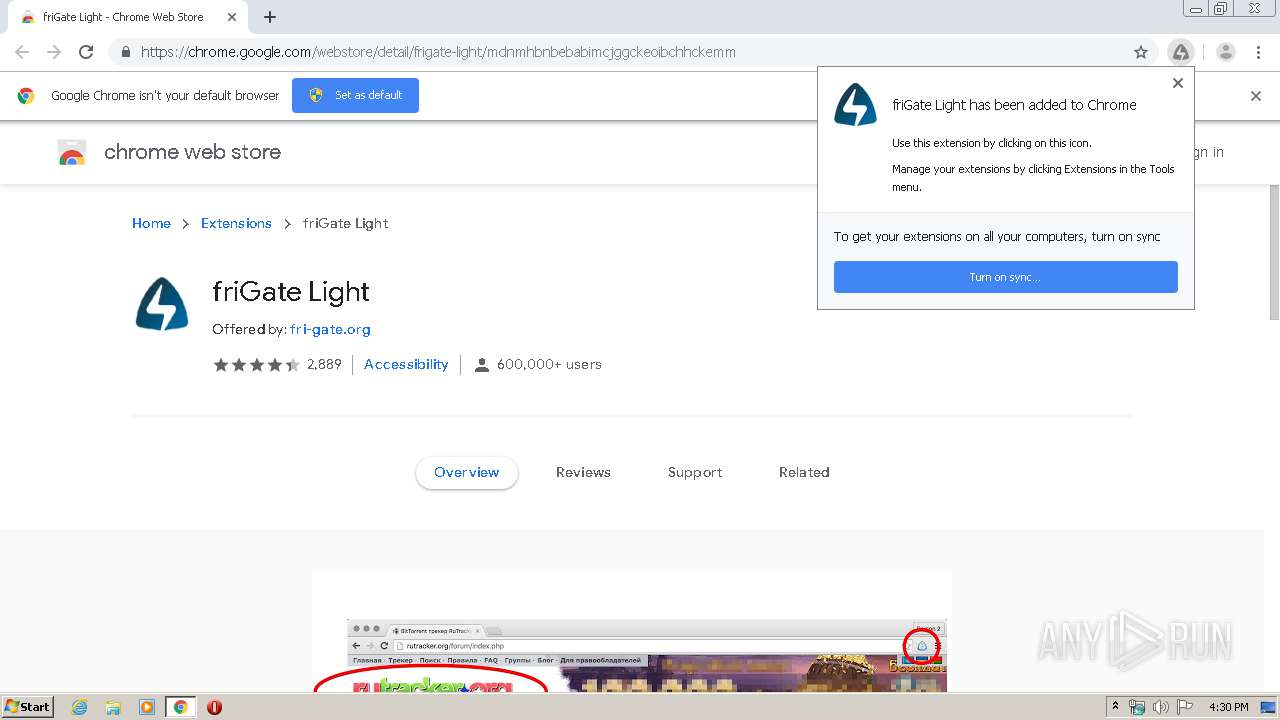
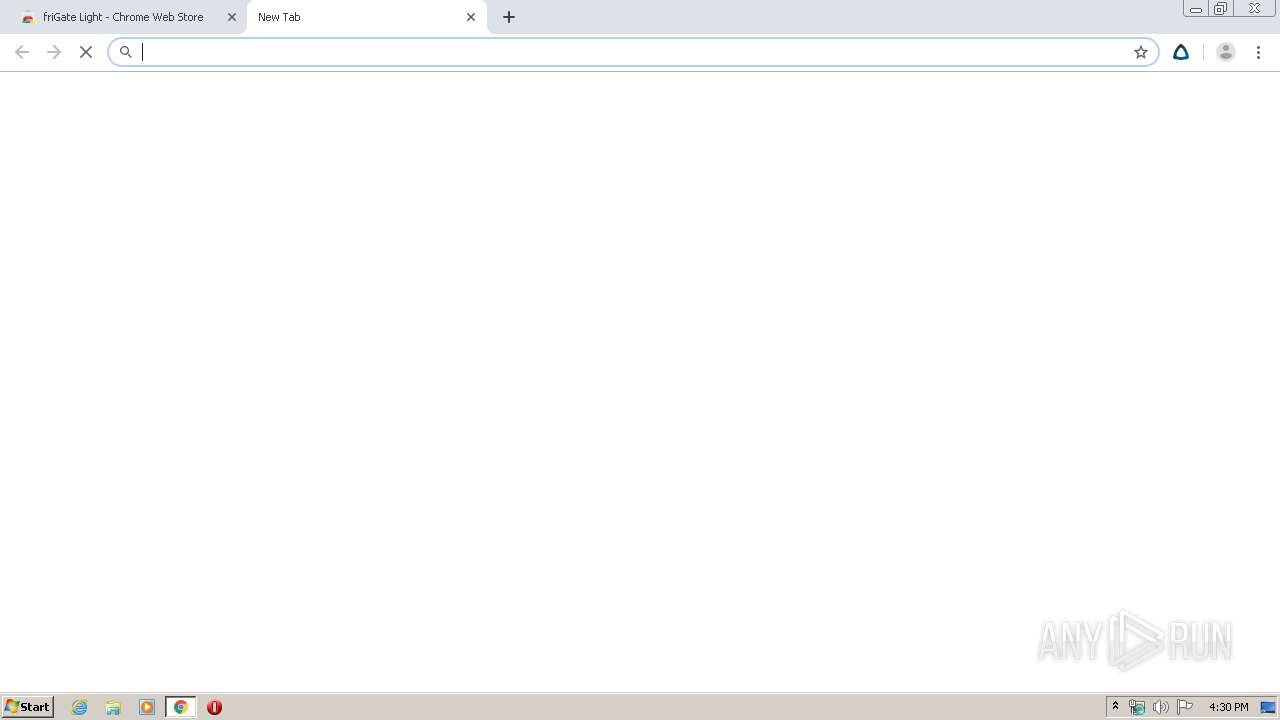
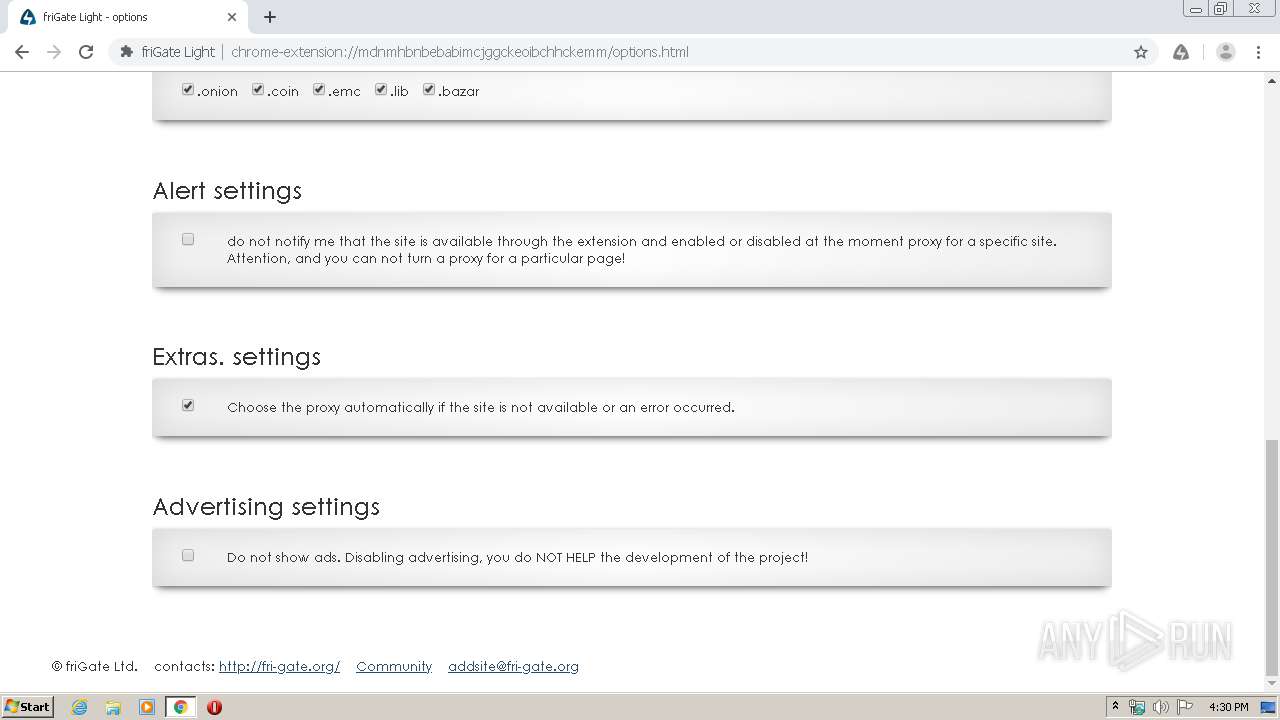
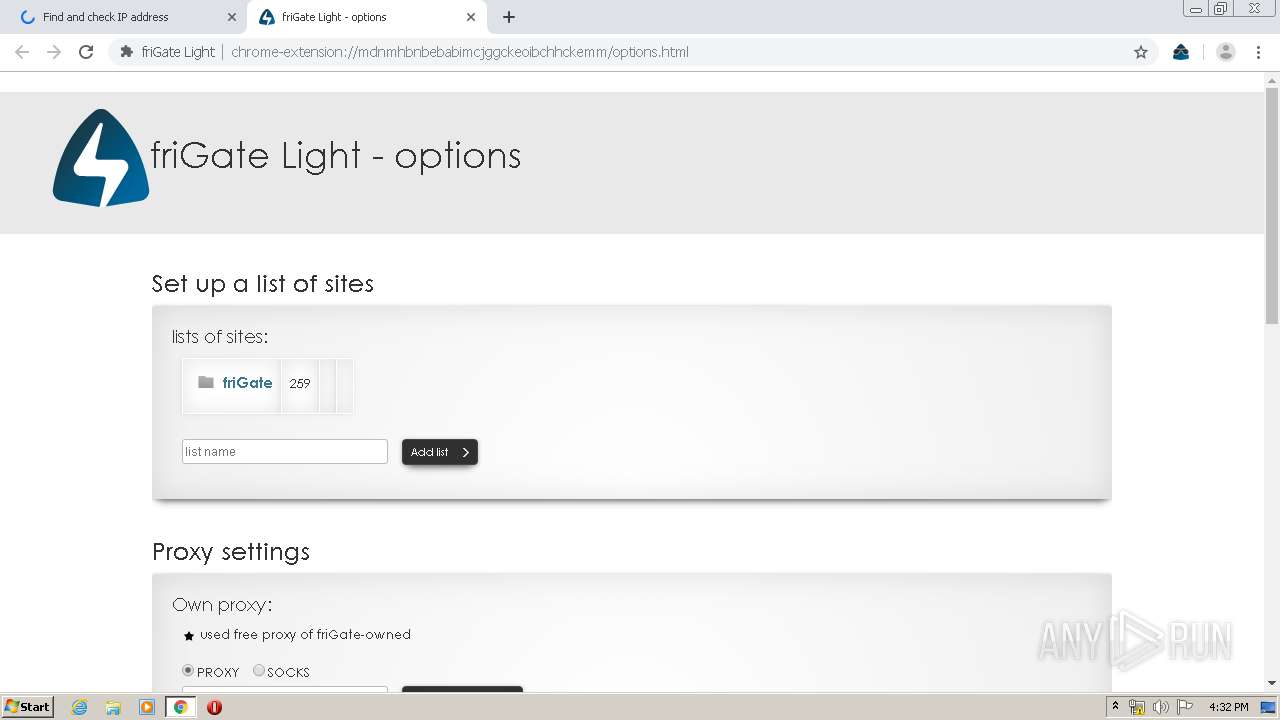
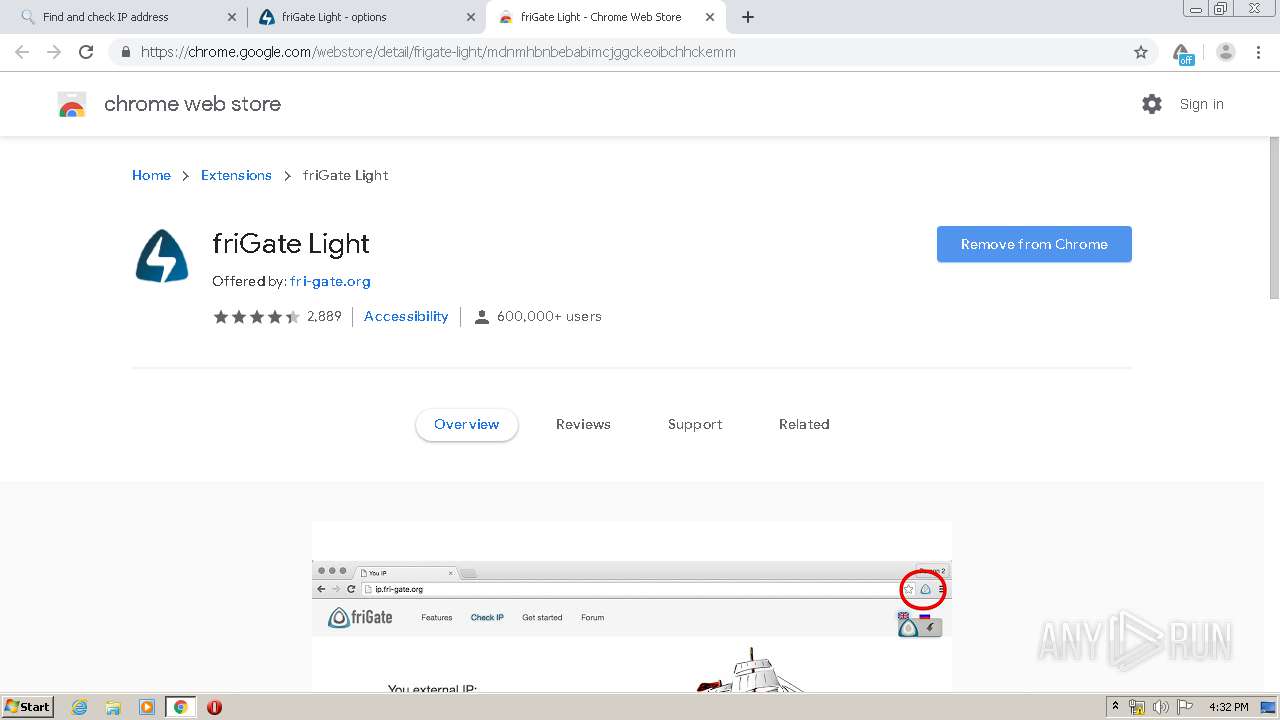
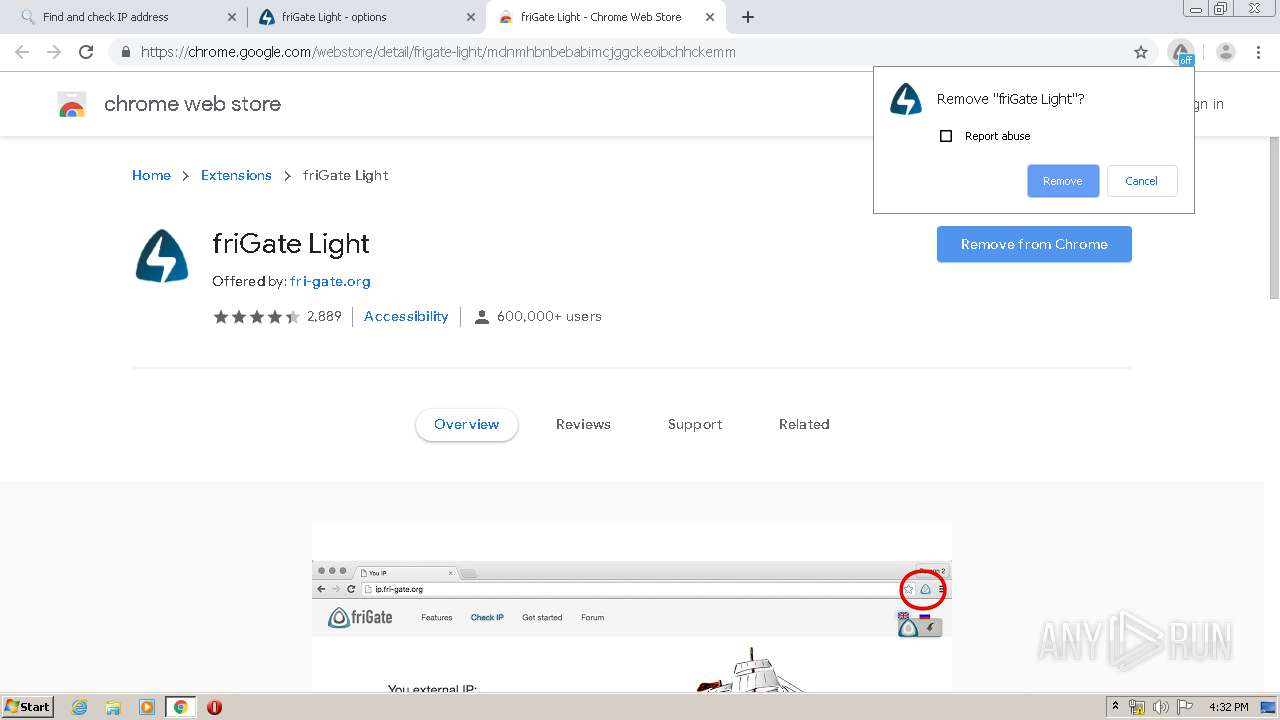
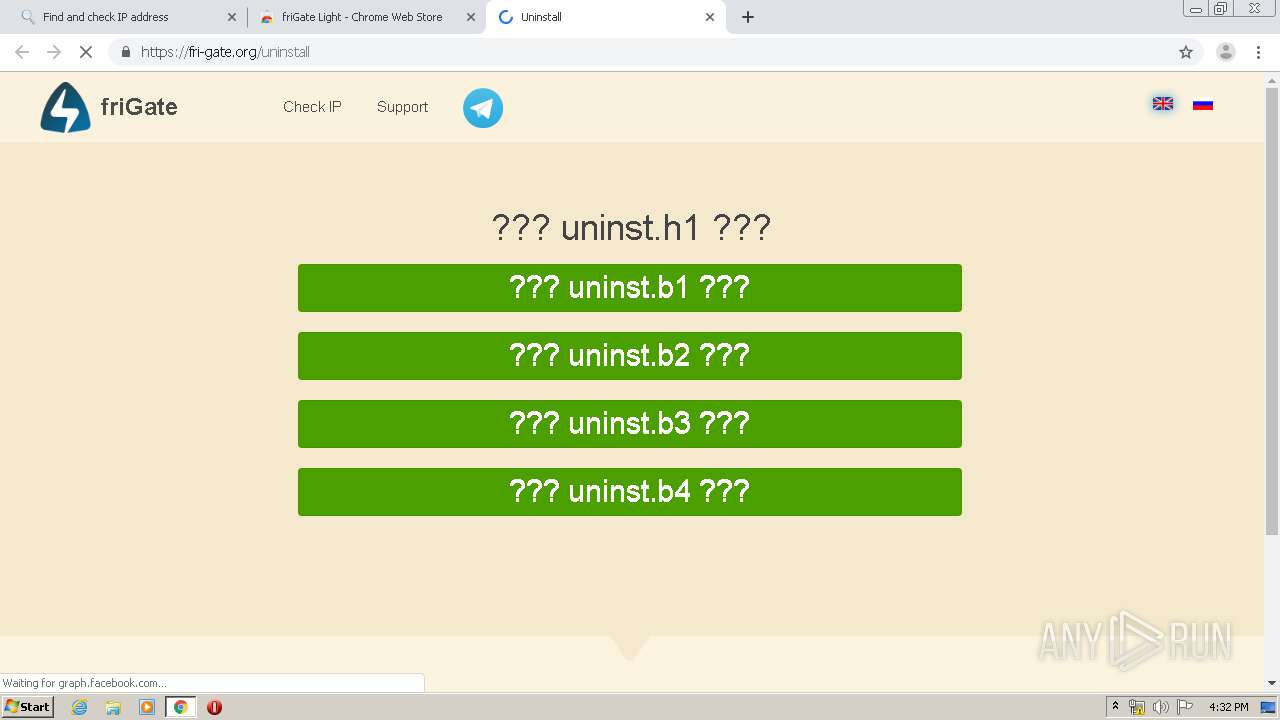
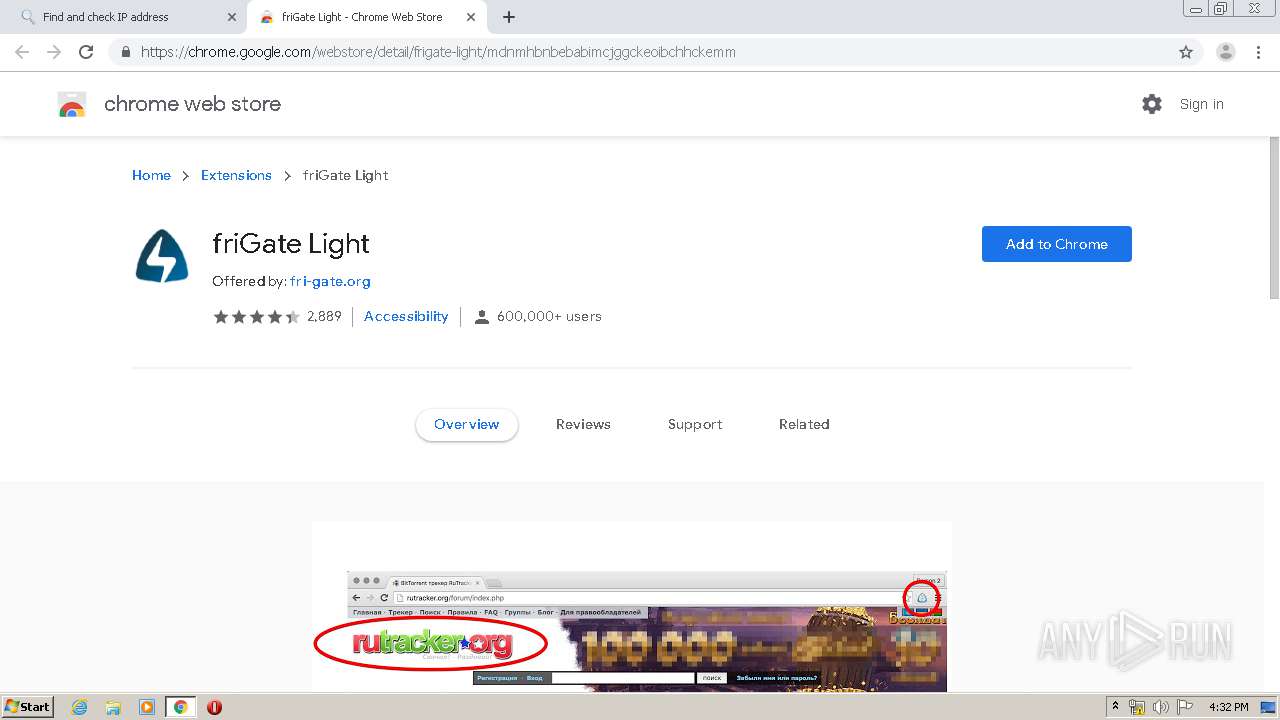
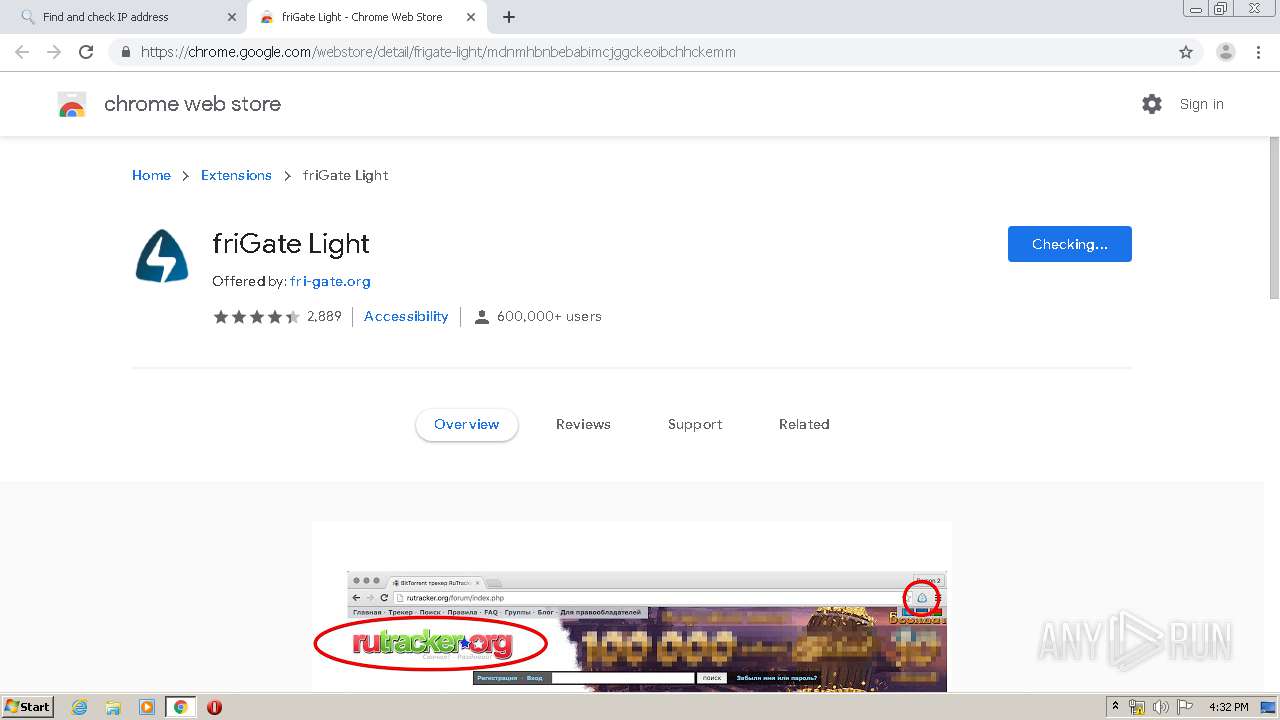
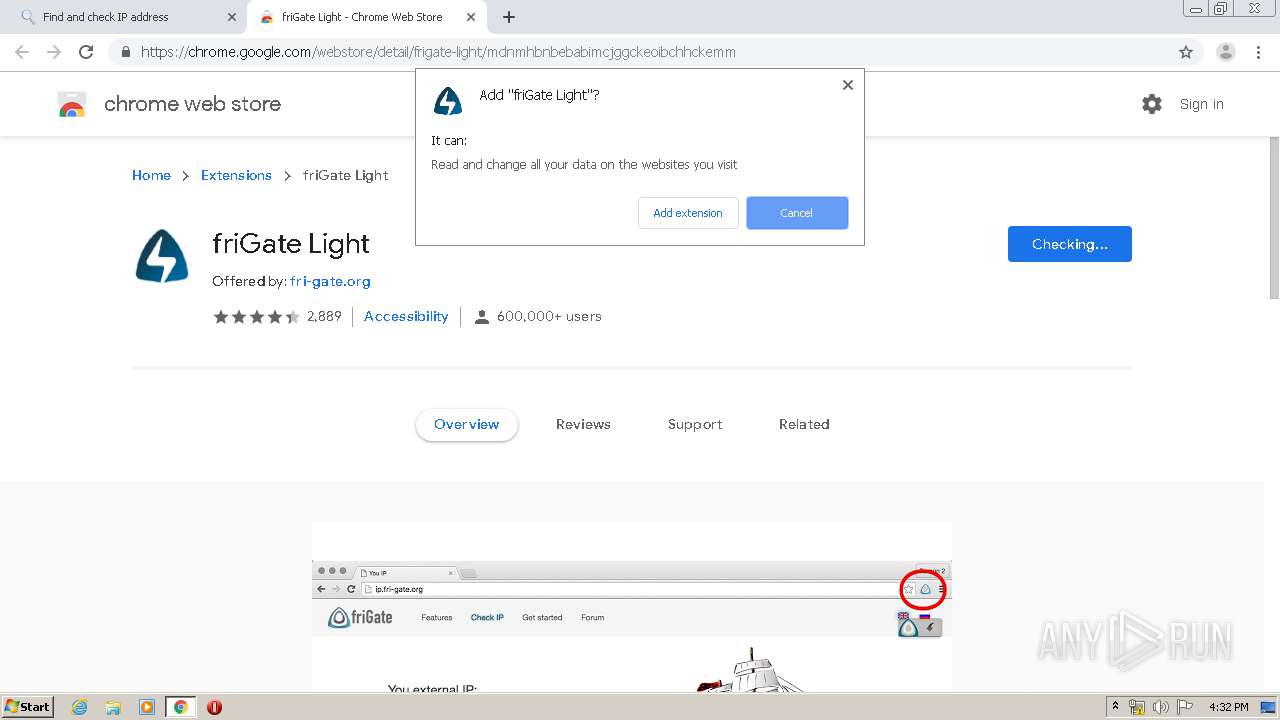
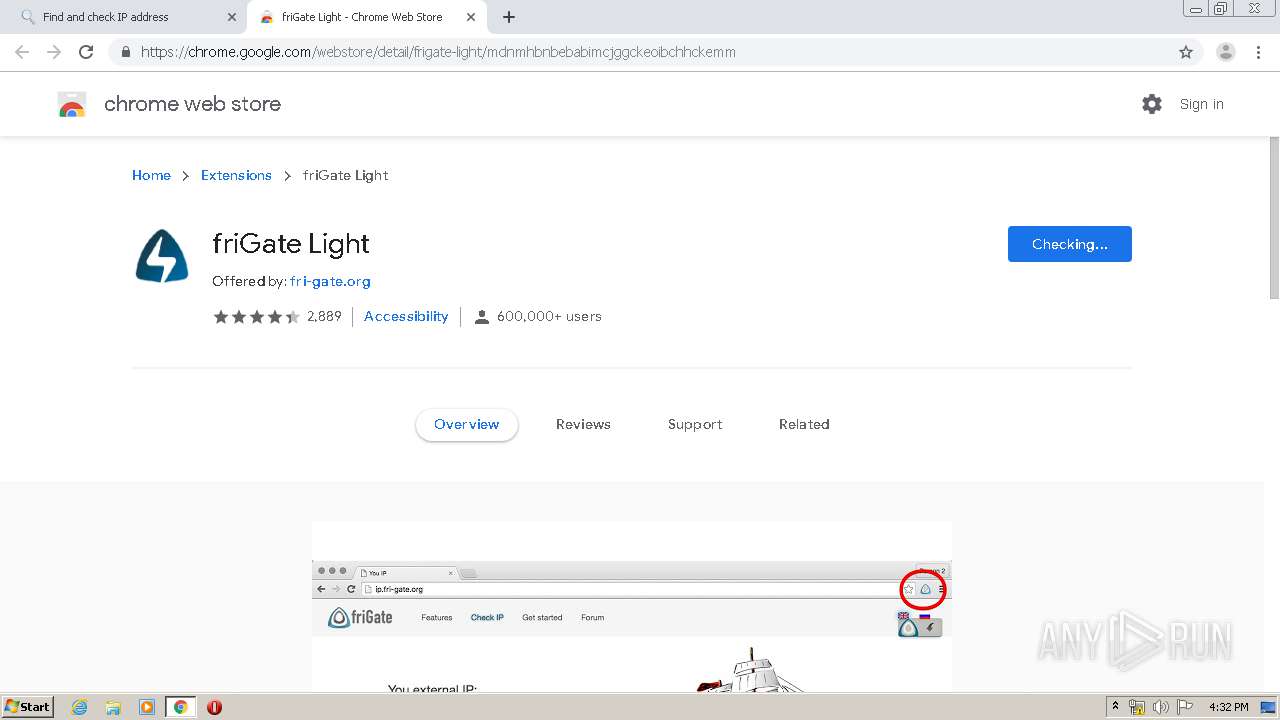
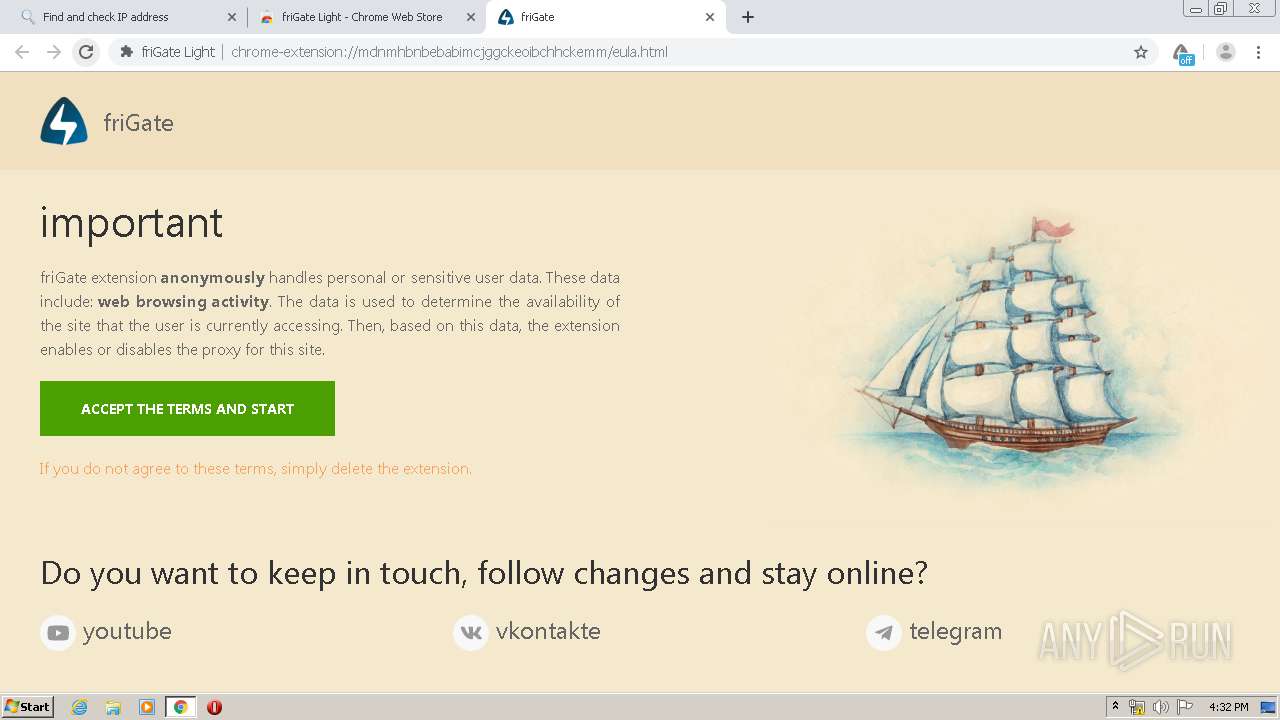
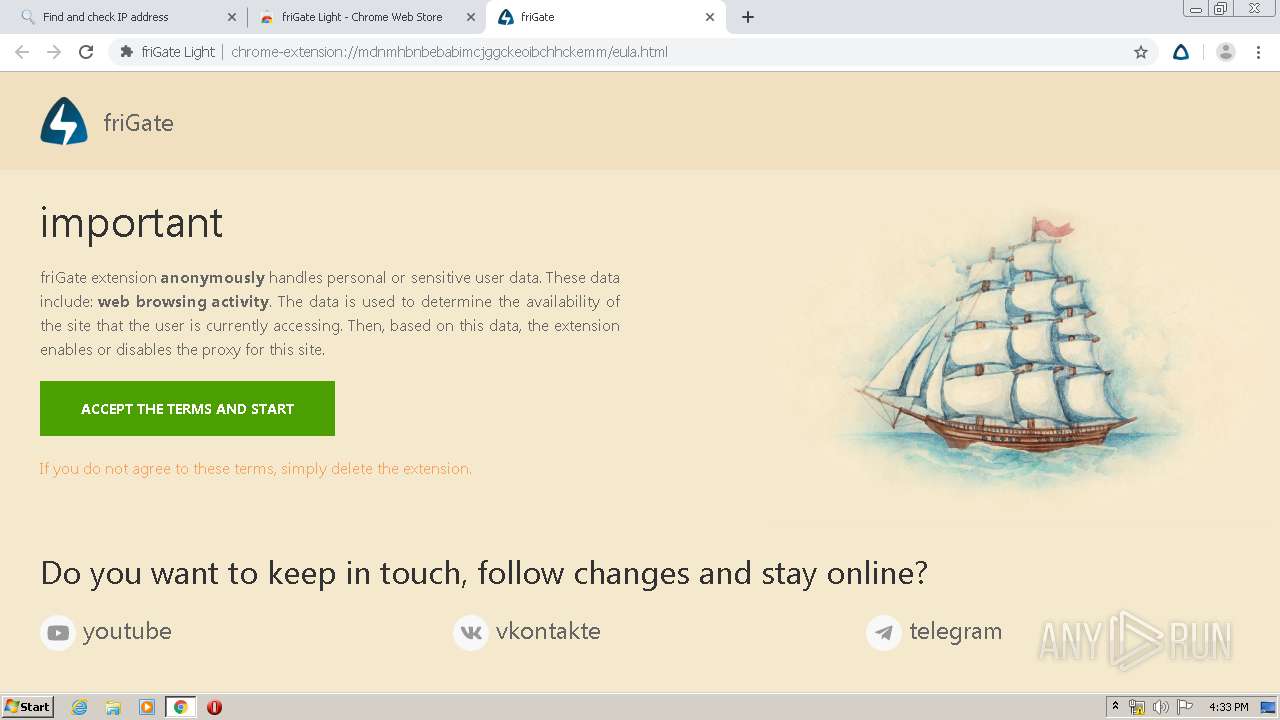
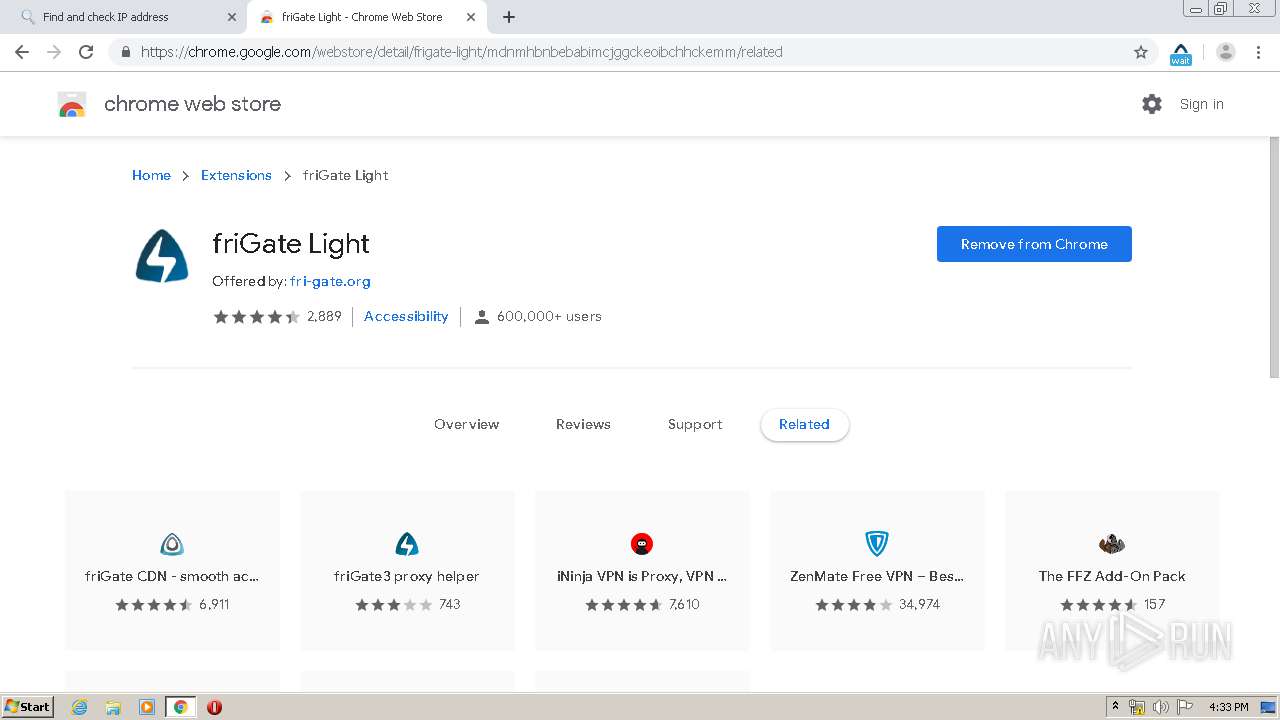
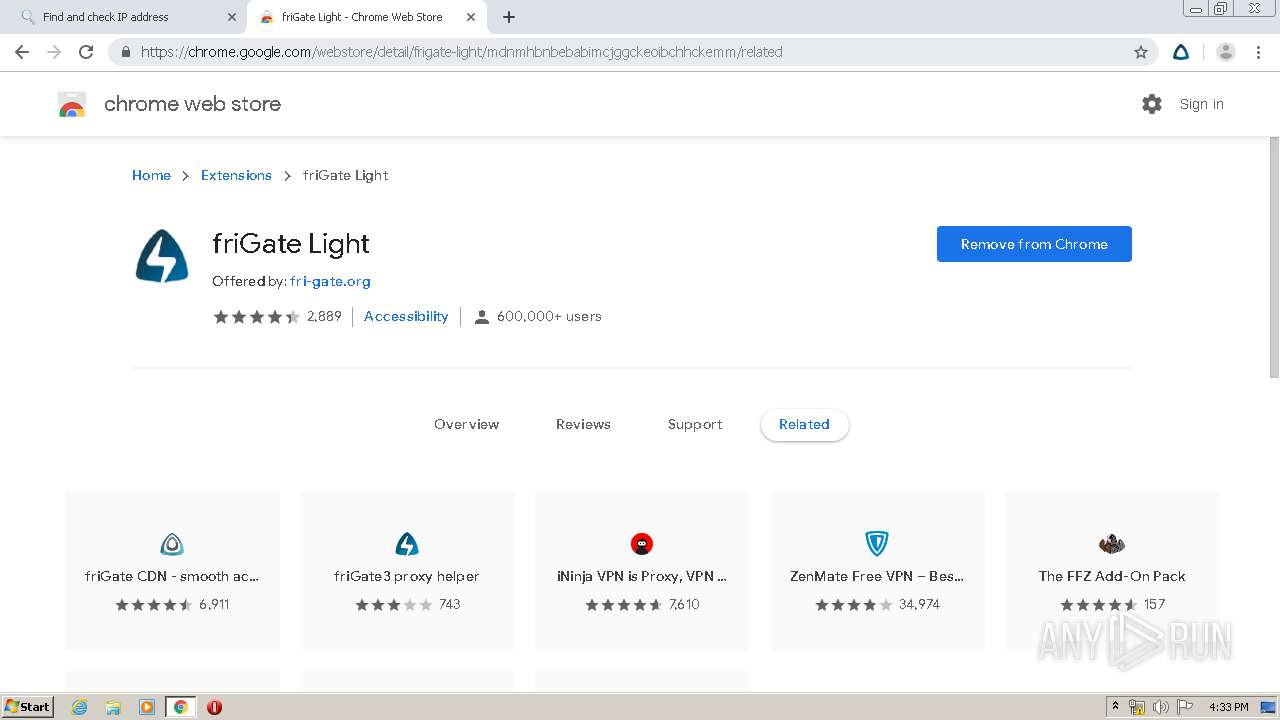
| URL: | https://chrome.google.com/webstore/detail/frigate-light/mdnmhbnbebabimcjggckeoibchhckemm |
| Full analysis: | https://app.any.run/tasks/c66b4541-af09-4732-be6c-0e81fee344c7 |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2020, 15:29:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CD2A2B1B1D1A672A9E49A80FA028A935 |
| SHA1: | 3DC50CAF9FC32BED6D3B06FD00FE08A15BC9B50F |
| SHA256: | EAD4BD5F9DD892710F42E883720A706F5DE9337AF2988ADB9994C10863D4EE60 |
| SSDEEP: | 3:N8Qa9t3u0A2RKelJnCEBDDTBLIRiuJG6URBA1:2Qa9c01RnnHpP9DV21 |
MALICIOUS
No malicious indicators.SUSPICIOUS
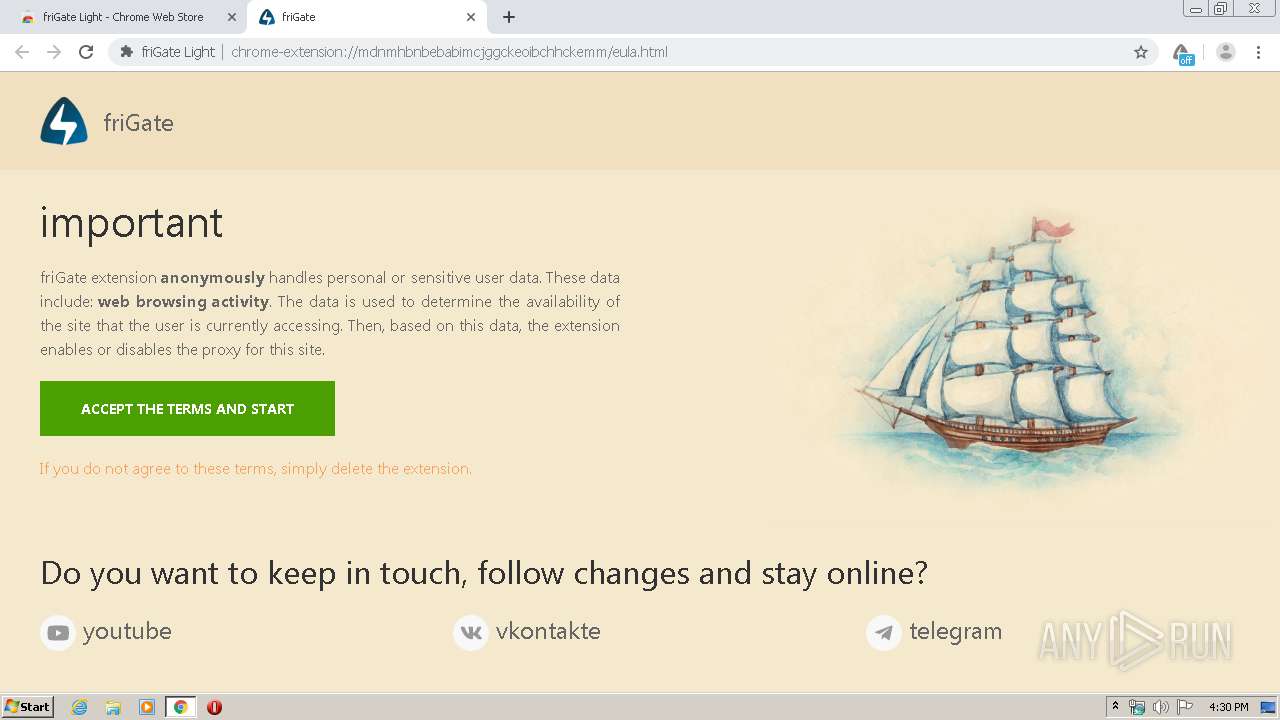
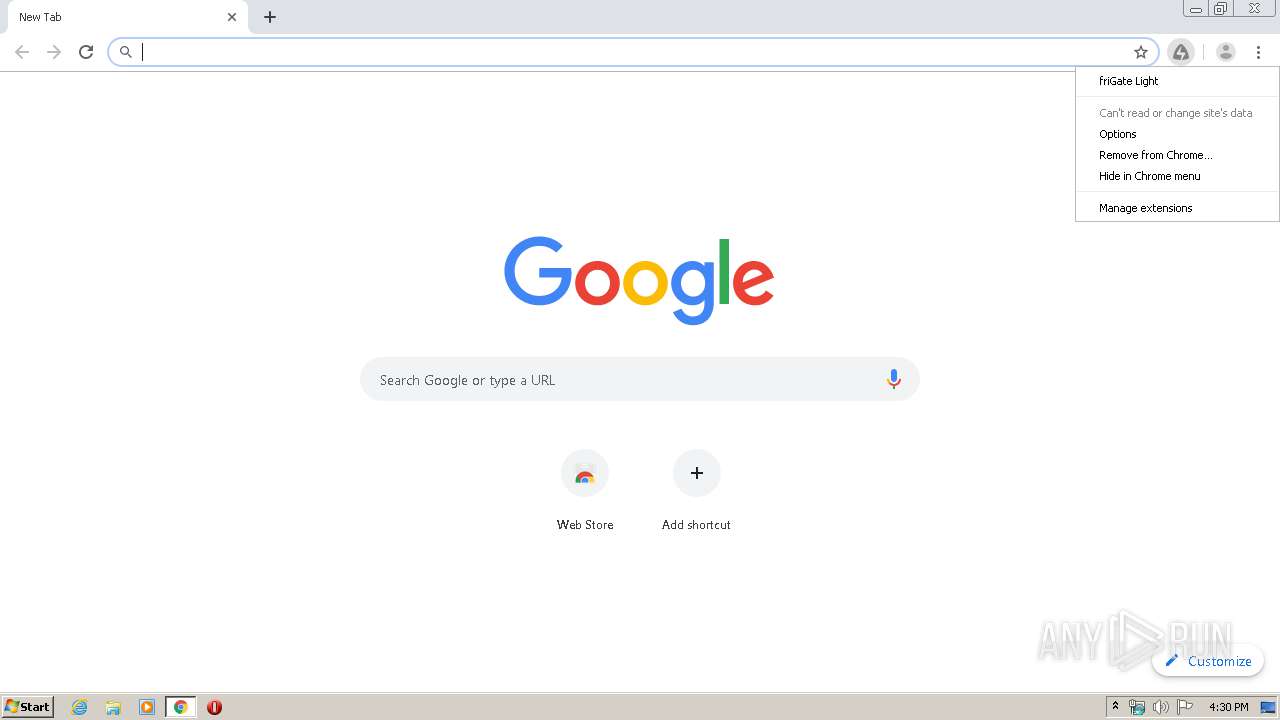
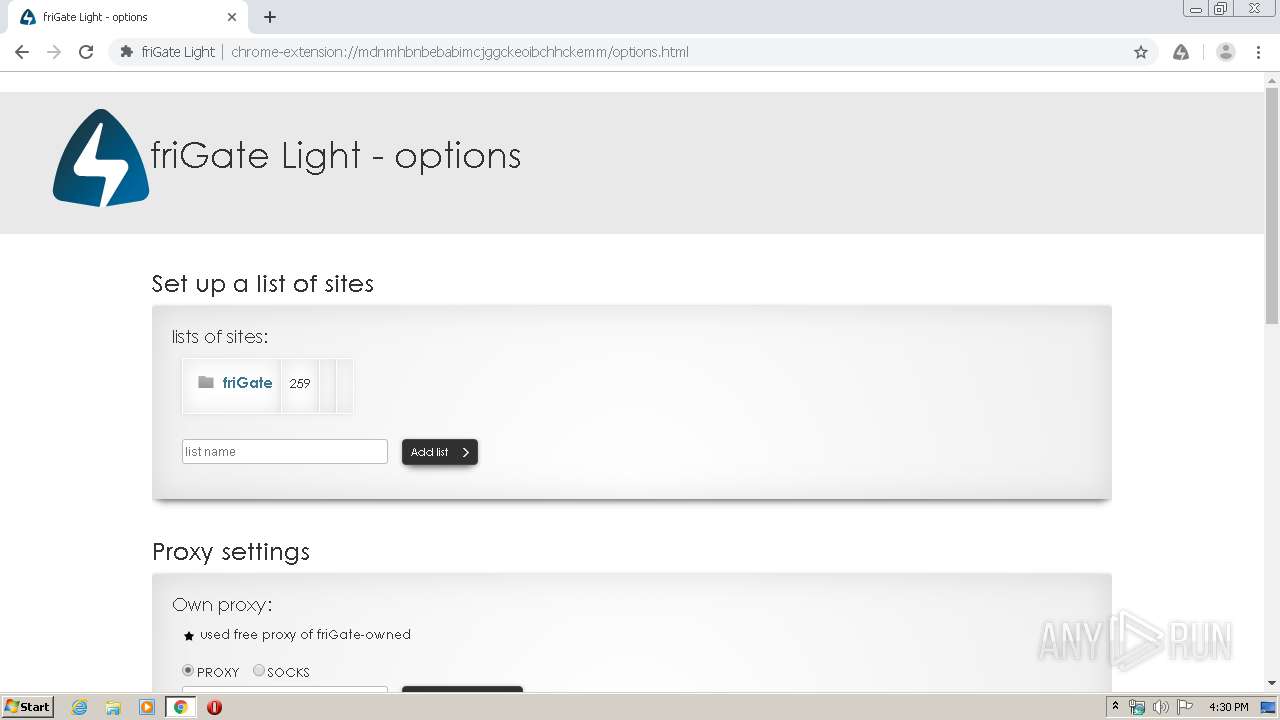
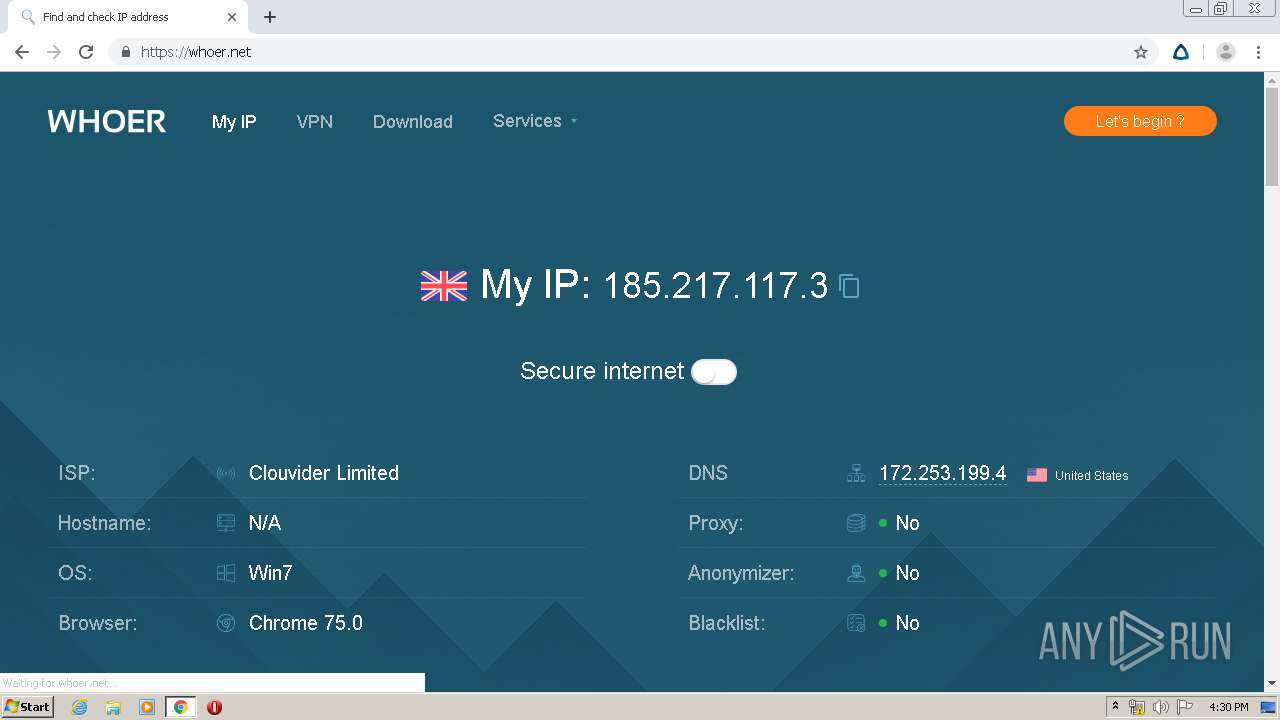
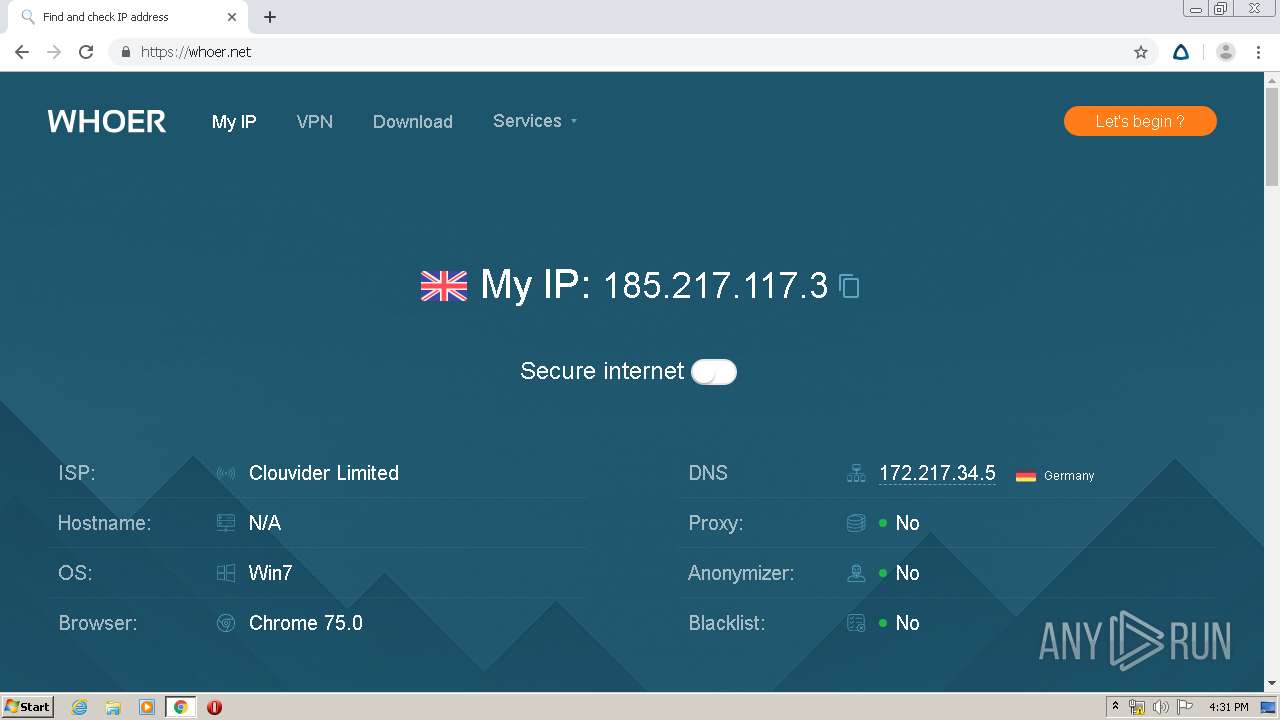
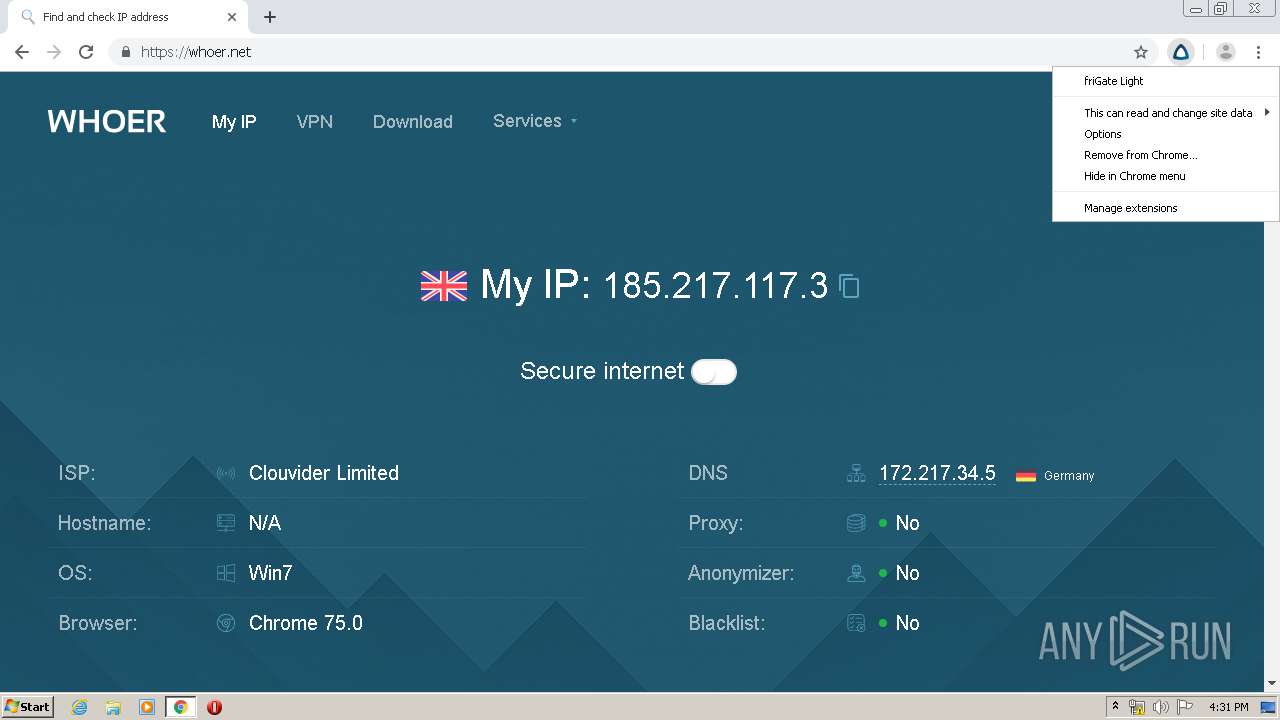
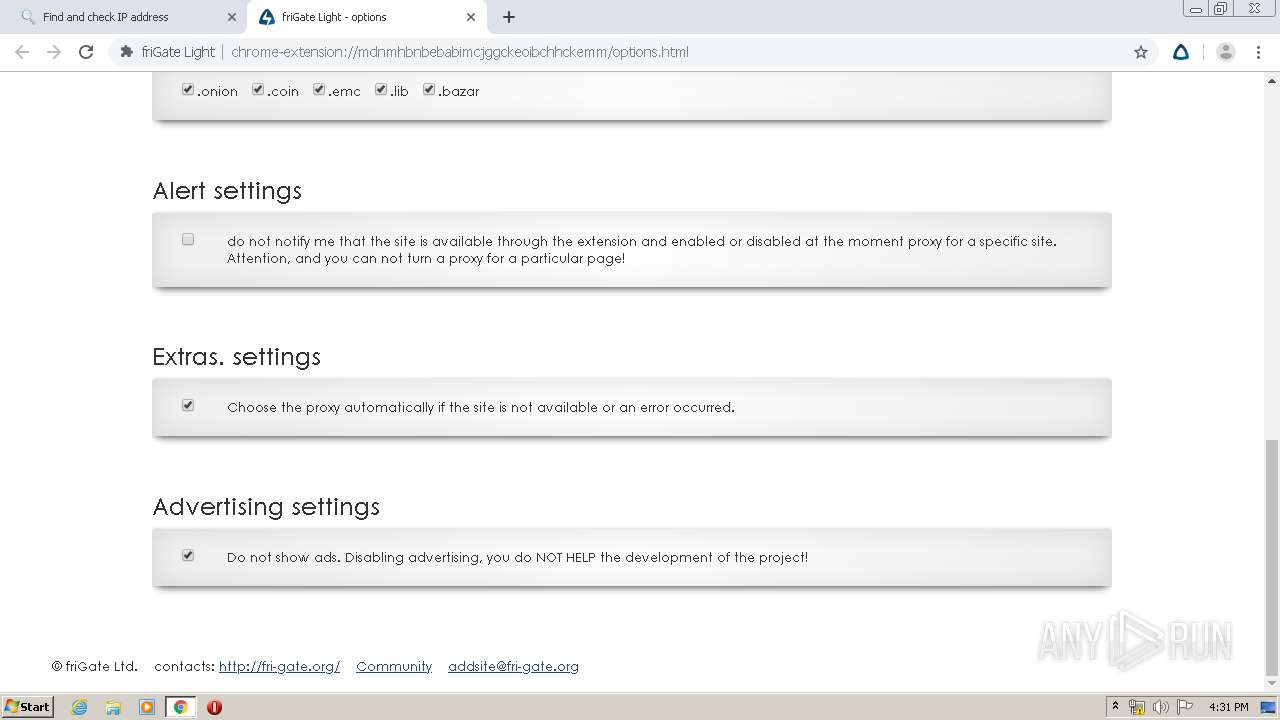
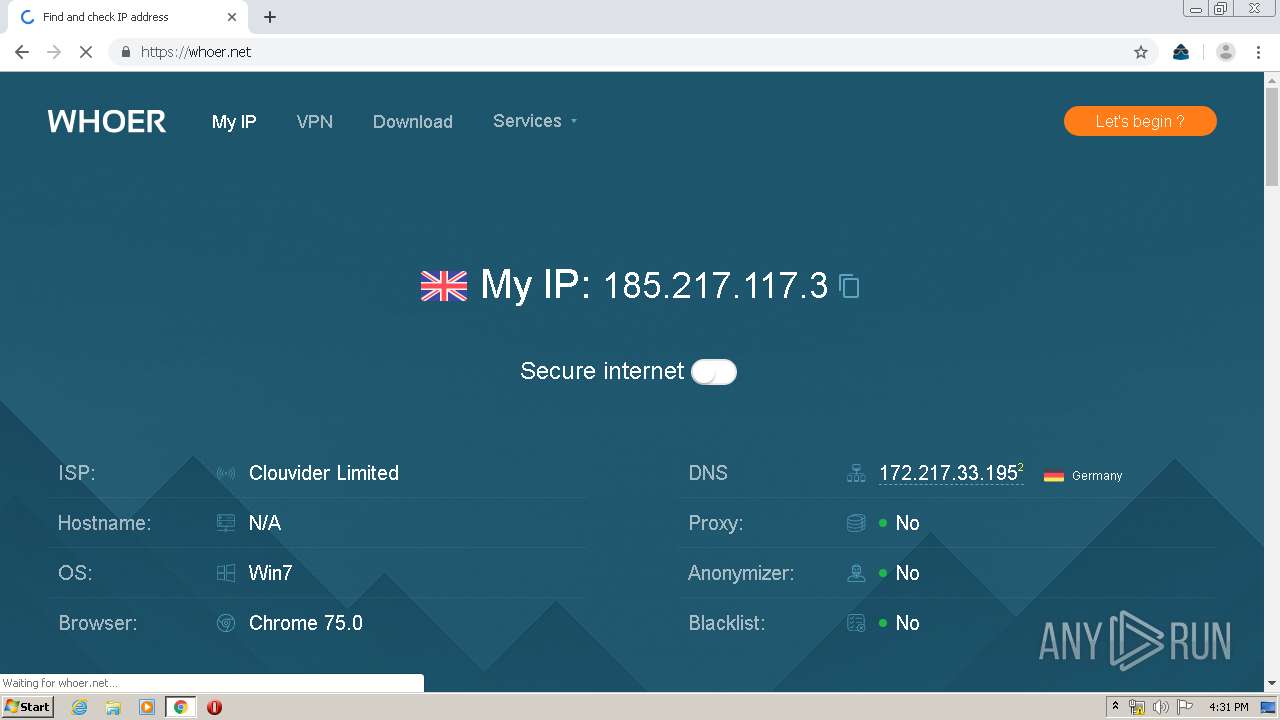
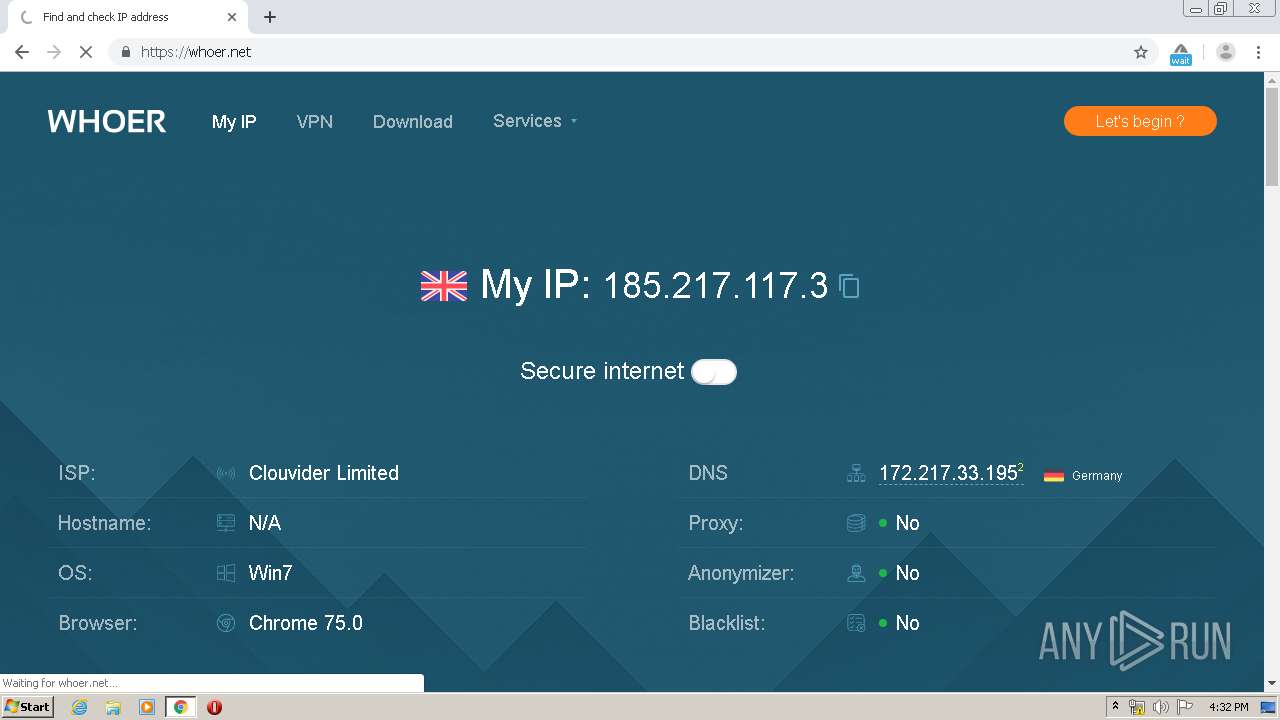
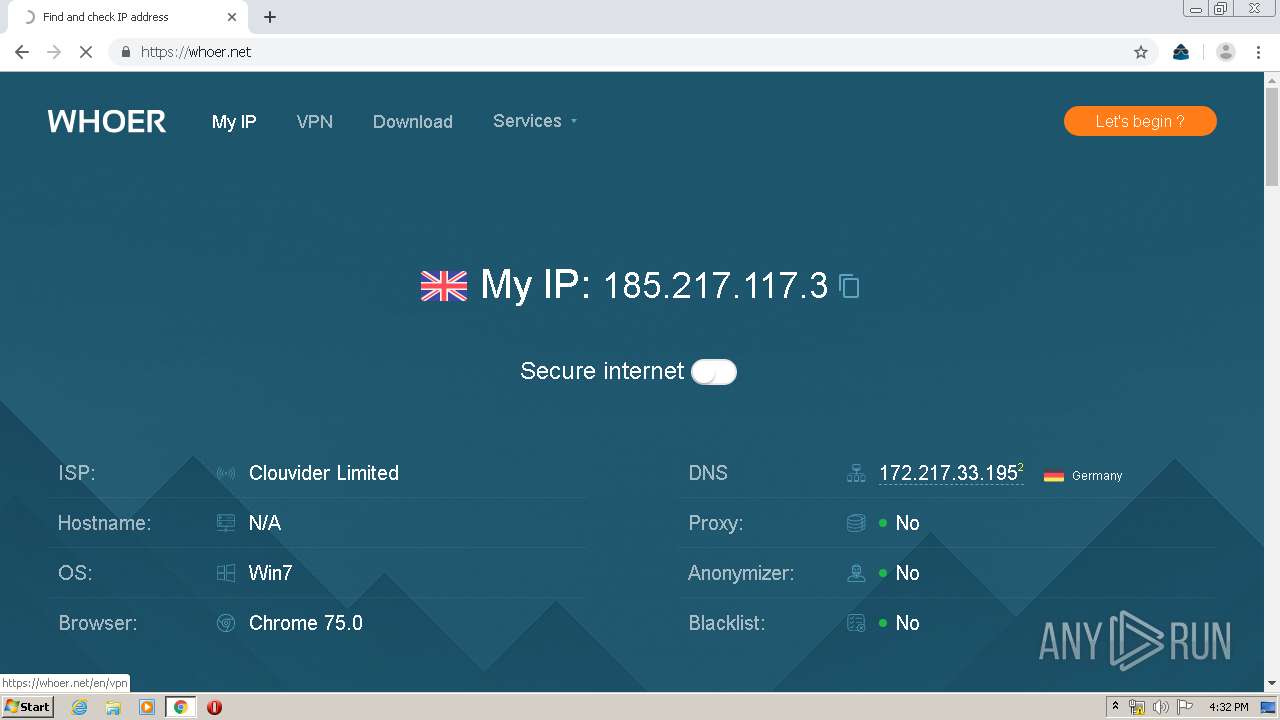
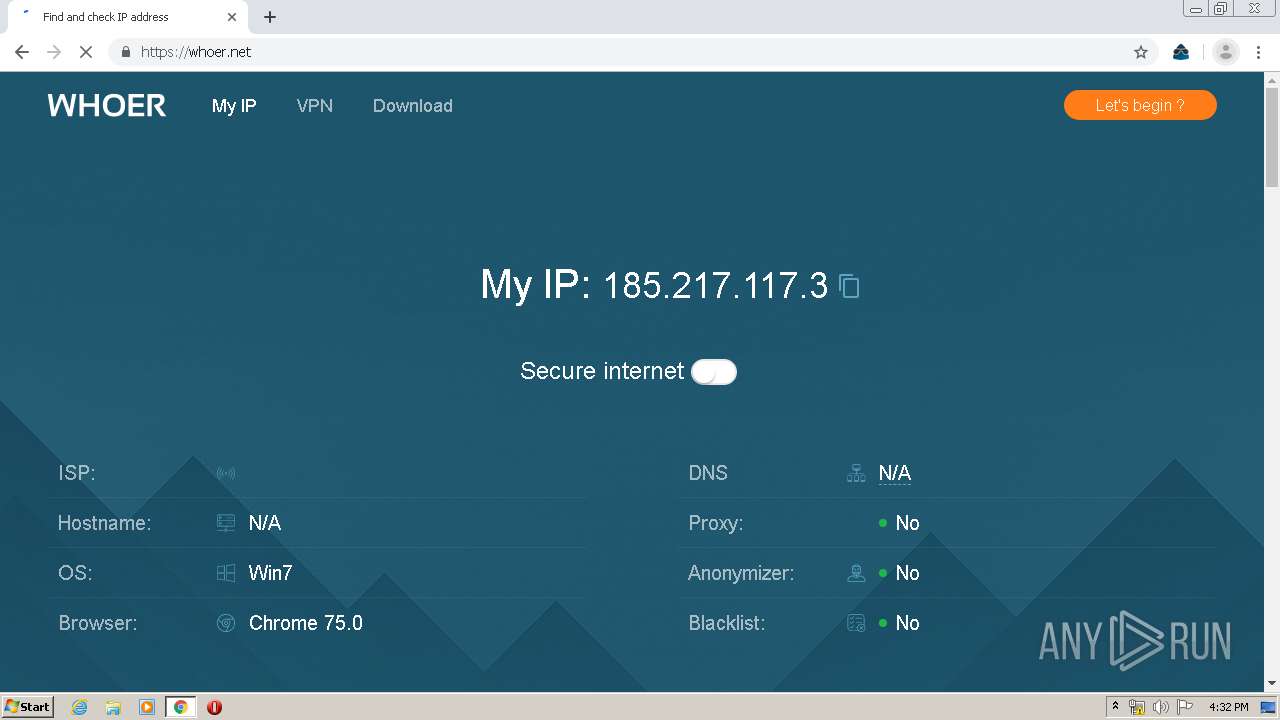
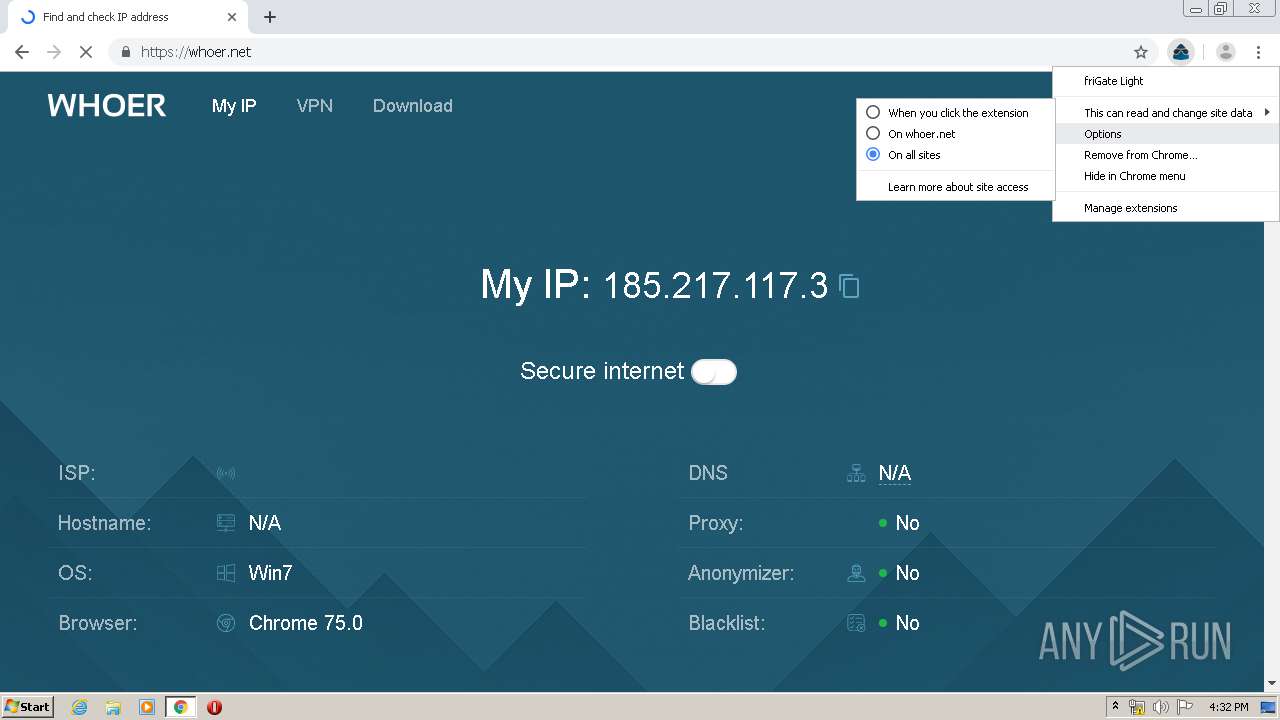
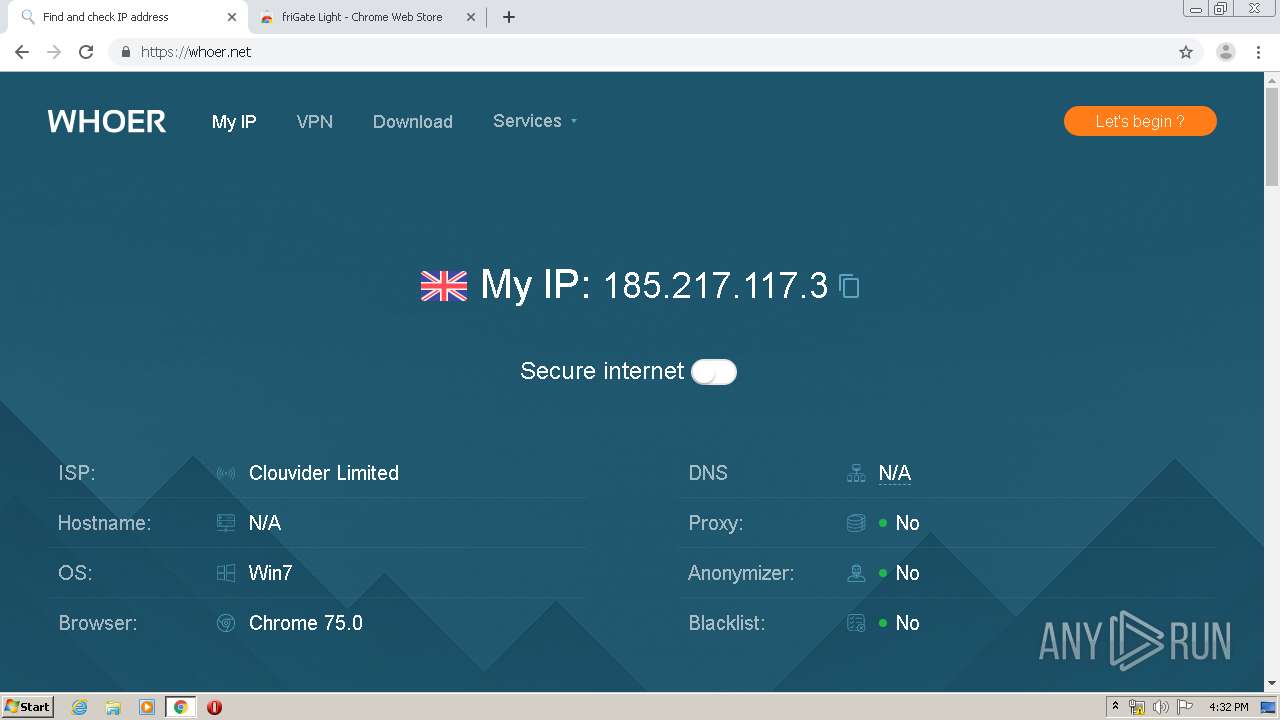
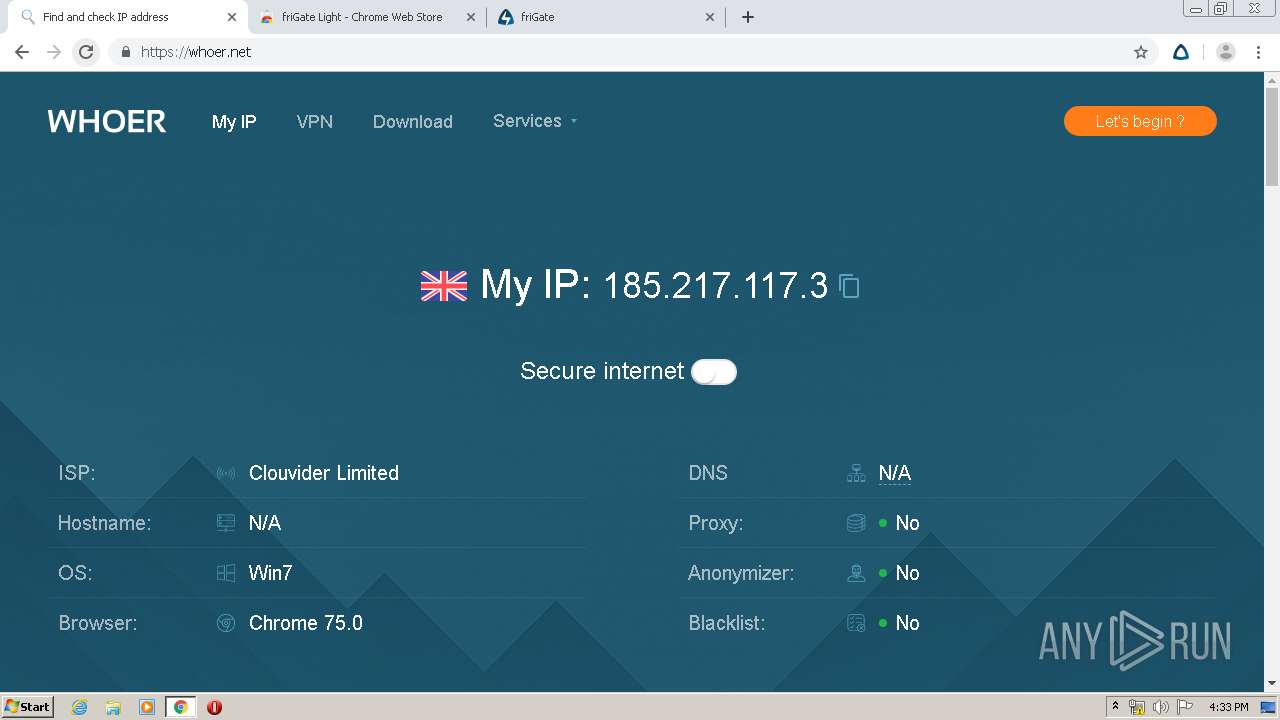
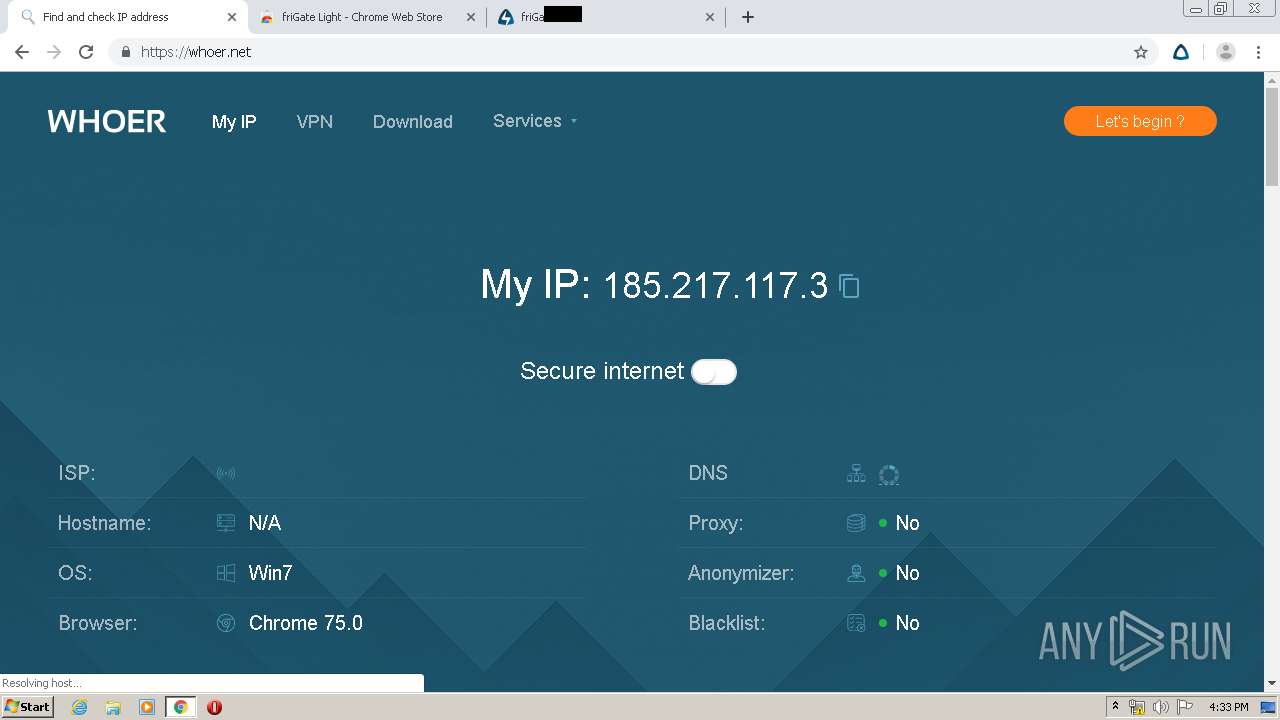
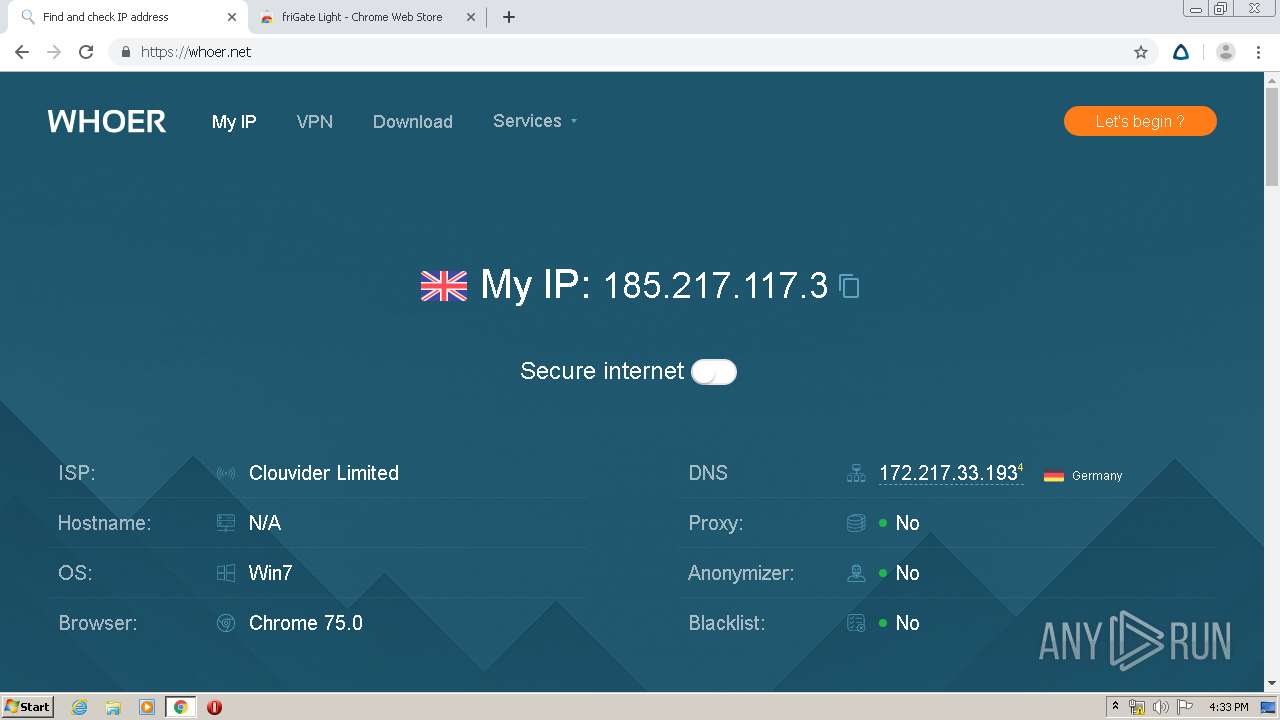
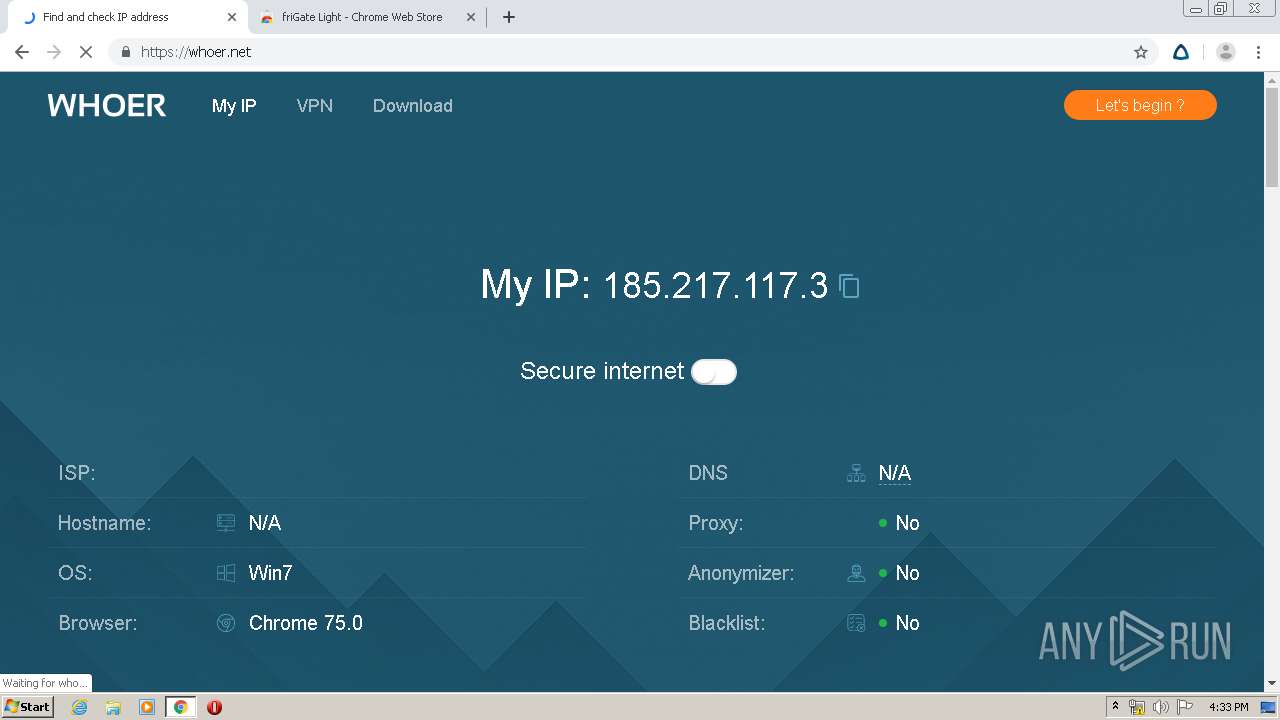
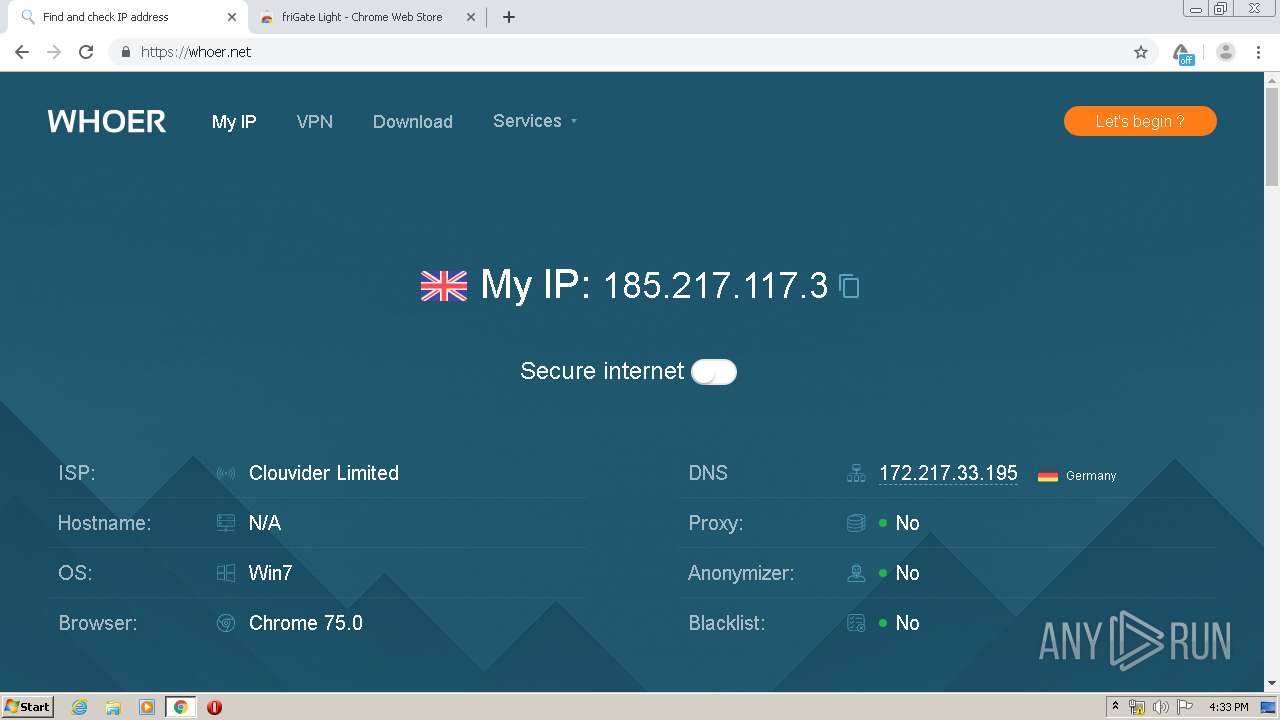
Checks for external IP
- chrome.exe (PID: 3360)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3820)
Connects to server without host name
- chrome.exe (PID: 3360)
INFO
Reads the hosts file
- chrome.exe (PID: 3820)
- chrome.exe (PID: 3360)
Reads settings of System Certificates
- chrome.exe (PID: 3360)
Reads Internet Cache Settings
- chrome.exe (PID: 3820)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3820)
Creates files in the user directory
- chrome.exe (PID: 3820)
Application launched itself
- chrome.exe (PID: 3820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
57
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11715171242257658547,3119120817712758551,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14500841658418243999 --mojo-platform-channel-handle=4592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=272 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11715171242257658547,3119120817712758551,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12419645681577353252 --mojo-platform-channel-handle=4204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11715171242257658547,3119120817712758551,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14651879667506168655 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11715171242257658547,3119120817712758551,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3289958933649771664 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4312 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11715171242257658547,3119120817712758551,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6418015406622877457 --mojo-platform-channel-handle=4012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11715171242257658547,3119120817712758551,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=69977176886752306 --mojo-platform-channel-handle=4592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11715171242257658547,3119120817712758551,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11810298896718736831 --mojo-platform-channel-handle=1072 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11715171242257658547,3119120817712758551,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=656200033831719996 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11715171242257658547,3119120817712758551,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5927711293286447396 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4092 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
879
Read events
599
Write events
263
Delete events
17
Modification events
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3820-13230660591823000 |
Value: 259 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
131
Text files
601
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E8B4AF0-EEC.pma | — | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\48645833-a8da-442e-b0bc-e696b6aa2786.tmp | — | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa6e22b.TMP | text | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa6e288.TMP | text | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e20b.TMP | text | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e45d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
136
DNS requests
81
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
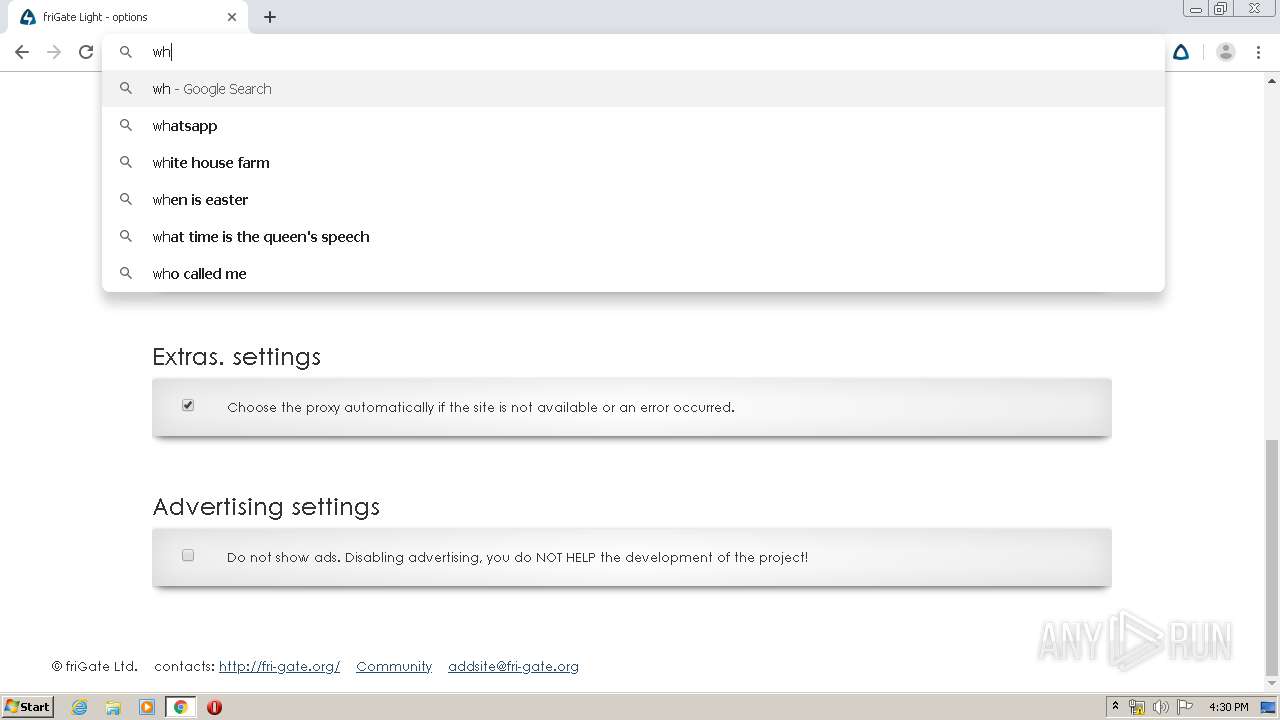
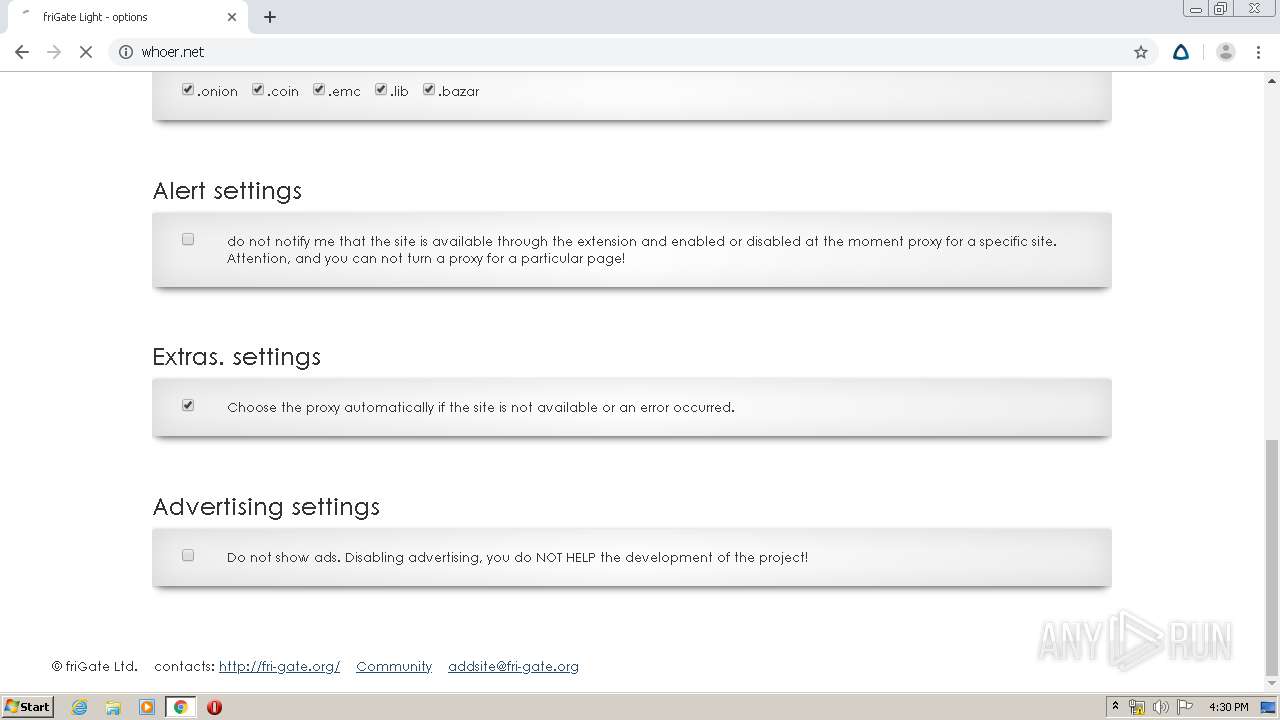
3360 | chrome.exe | GET | 301 | 104.26.2.223:80 | http://whoer.net/ | US | — | — | shared |
3360 | chrome.exe | POST | 200 | 188.165.30.217:80 | http://188.165.30.217/?1586187006665&k8omsf6n | LT | text | 1.98 Mb | unknown |
3360 | chrome.exe | POST | 200 | 188.165.30.217:80 | http://188.165.30.217/r?1586187007818&k8omsf6o | LT | text | 364 b | unknown |
3360 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEHbYt4bR81JP7pU%2BcUA9mdU%3D | US | der | 471 b | whitelisted |
3360 | chrome.exe | GET | 200 | 173.194.183.200:80 | http://r3---sn-aigl6nl7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.217.117.3&mm=28&mn=sn-aigl6nl7&ms=nvh&mt=1586186900&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3360 | chrome.exe | POST | 200 | 188.165.30.217:80 | http://188.165.30.217/r?1586187178041&k8omw228 | LT | text | 364 b | unknown |
3360 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3360 | chrome.exe | GET | 200 | 173.194.5.219:80 | http://r5---sn-aigl6n7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=185.217.117.3&mm=28&mn=sn-aigl6n7d&ms=nvh&mt=1586186900&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3360 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3360 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ2xvBYPgmu%2FP%2FmXiVKe%2BjES00TfwQU78EqlQwy2vtzMNyKE9gVS%2FcT6PgCEG8uQSIolB1kqNt7vj9%2B2M4%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3360 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 216.58.207.40:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.23.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.16.206:443 | chrome.google.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 64.233.167.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.16.170:443 | www.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chrome.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.gstatic.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
safebrowsing.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3360 | chrome.exe | Misc activity | APP [PTsecurity] FriGate Proxy |
3360 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup whoer.net |
3360 | chrome.exe | Misc activity | APP [PTsecurity] FriGate Proxy |
3360 | chrome.exe | Misc activity | APP [PTsecurity] FriGate Proxy |