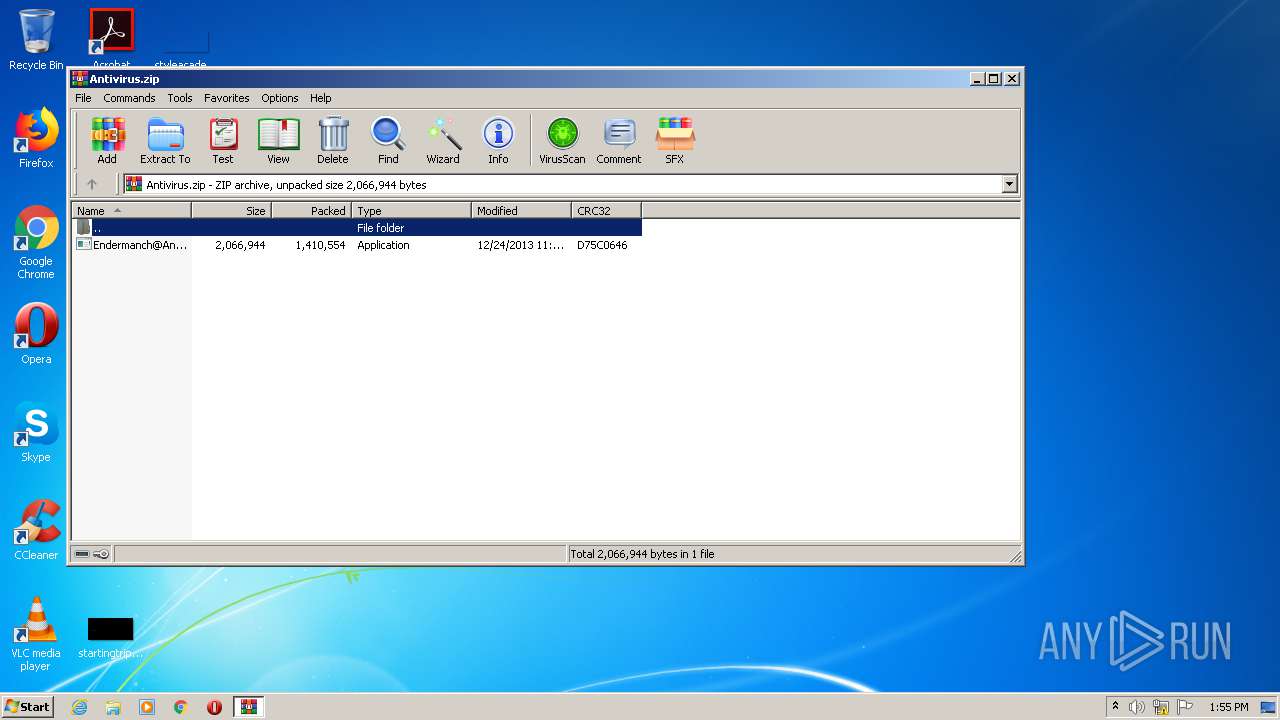
| File name: | Antivirus.zip |
| Full analysis: | https://app.any.run/tasks/6cbbd644-d1fb-41b1-a4b1-260b34c9c752 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 13:54:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E1AC4770F42BAC0E4A6826314331C6EA |
| SHA1: | 66493386AD995819871ACA4C30897B6F29AB358F |
| SHA256: | EABF7FDD31C5838D66CCBC3CA52B0F6EAF8120F83EED43F372F21E4D31734B73 |
| SSDEEP: | 24576:oSL6Ntp05P6ftXeQAPm1sPj54cubcZDUPKrFusldmR8uCbdfxgEgL+xTbQDE5GYJ:oftFtXr85409usl8R8vJgEdCY5n3Rv |
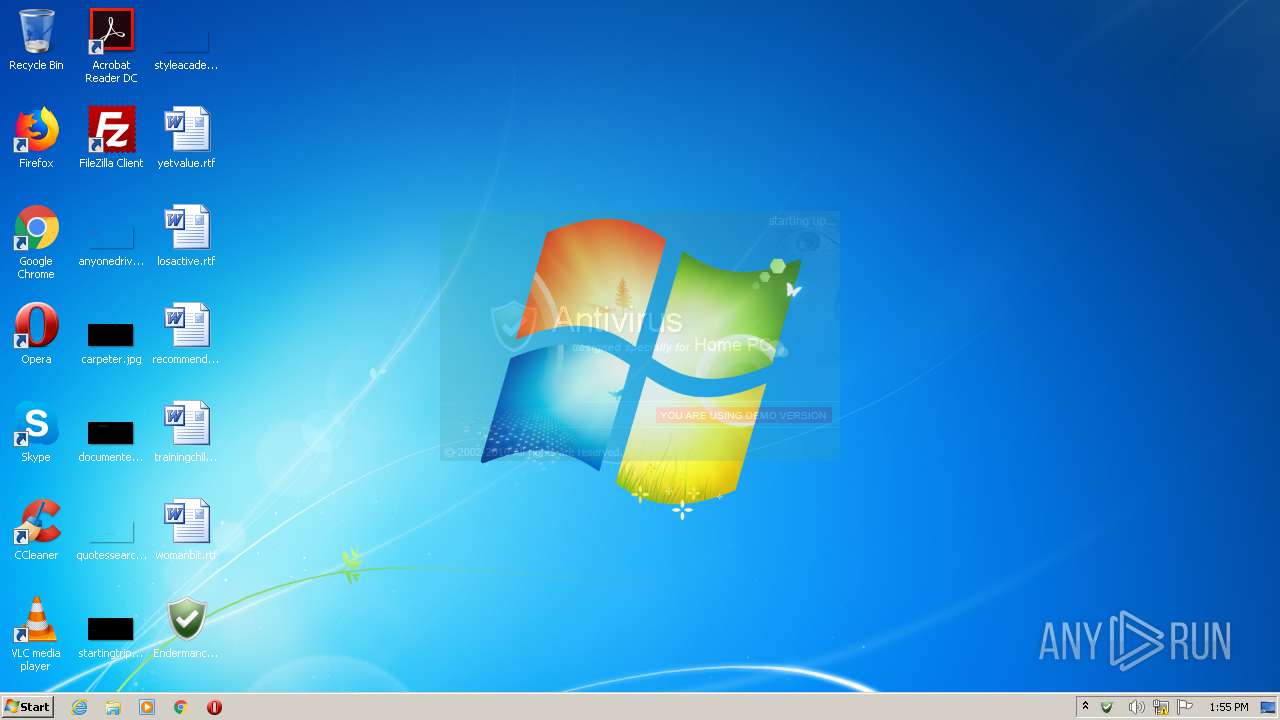
MALICIOUS
Application was dropped or rewritten from another process
- Endermanch@Antivirus.exe (PID: 3744)
Changes internet zones settings
- Endermanch@Antivirus.exe (PID: 3744)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2784)
Creates files in the user directory
- Endermanch@Antivirus.exe (PID: 3744)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2784)
INFO
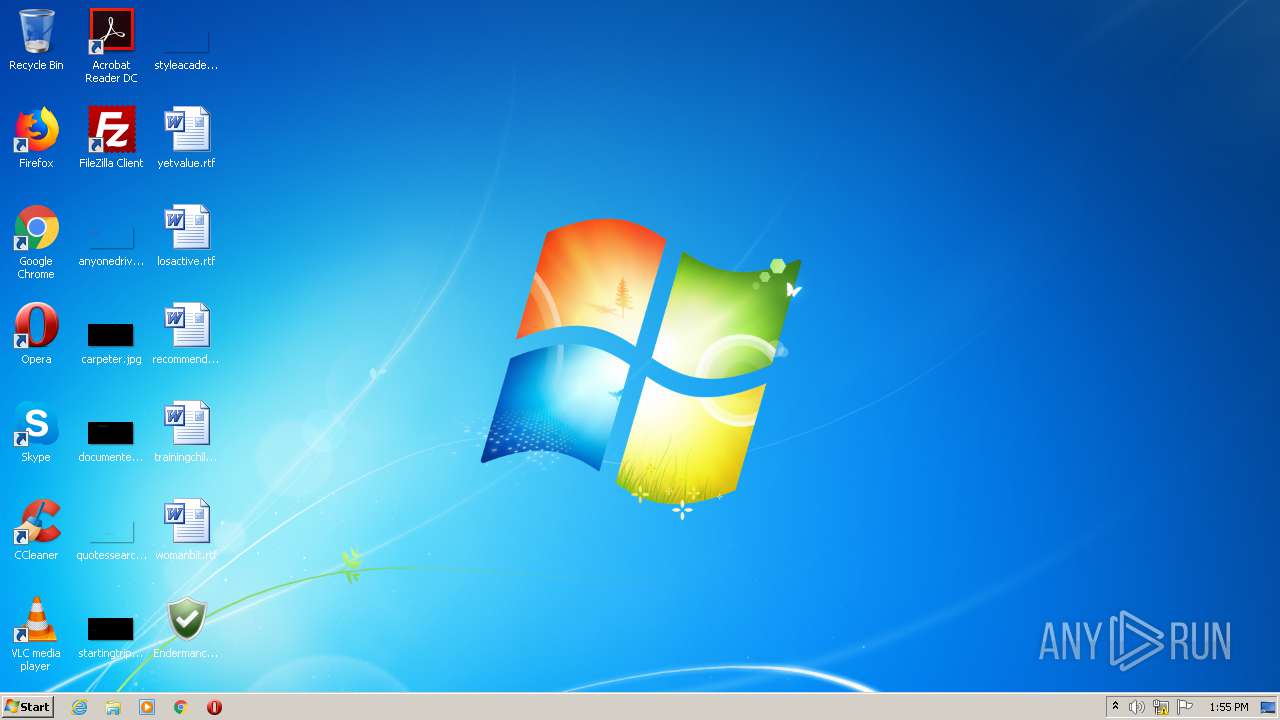
Manual execution by user
- Endermanch@Antivirus.exe (PID: 3744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
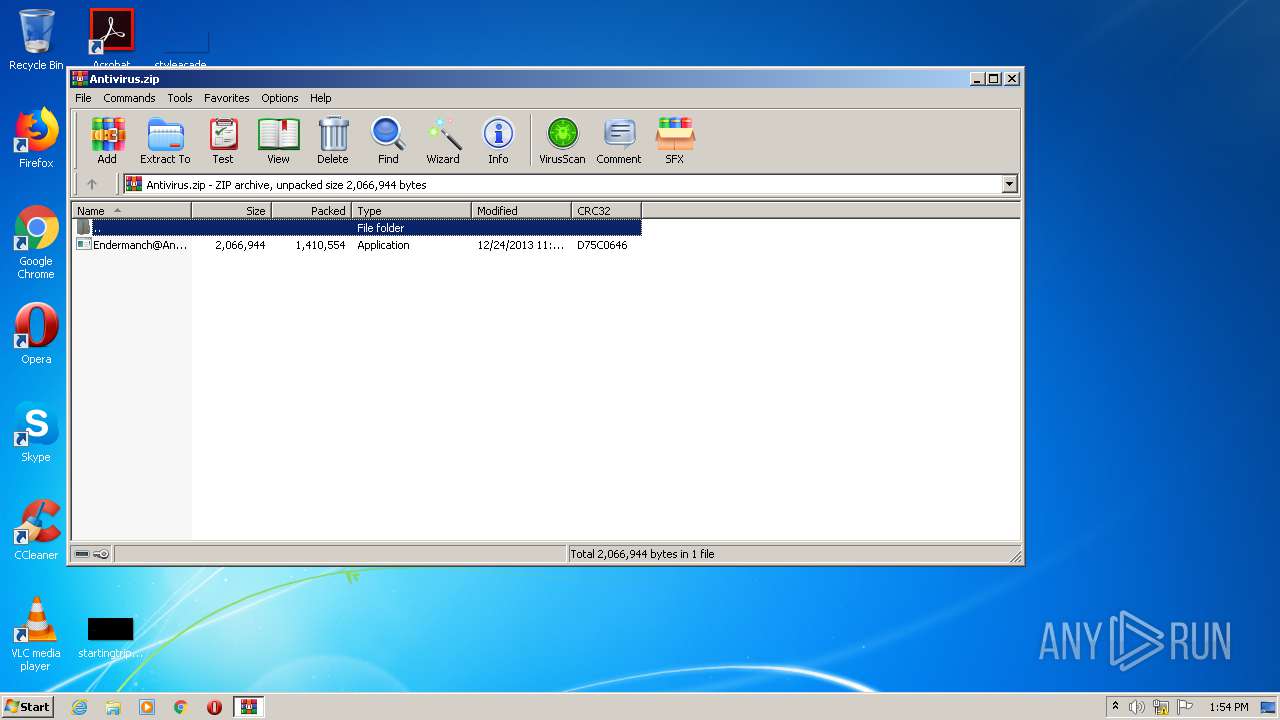
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2013:12:25 02:24:07 |
| ZipCRC: | 0xd75c0646 |
| ZipCompressedSize: | 1410554 |
| ZipUncompressedSize: | 2066944 |
| ZipFileName: | Endermanch@Antivirus.exe |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
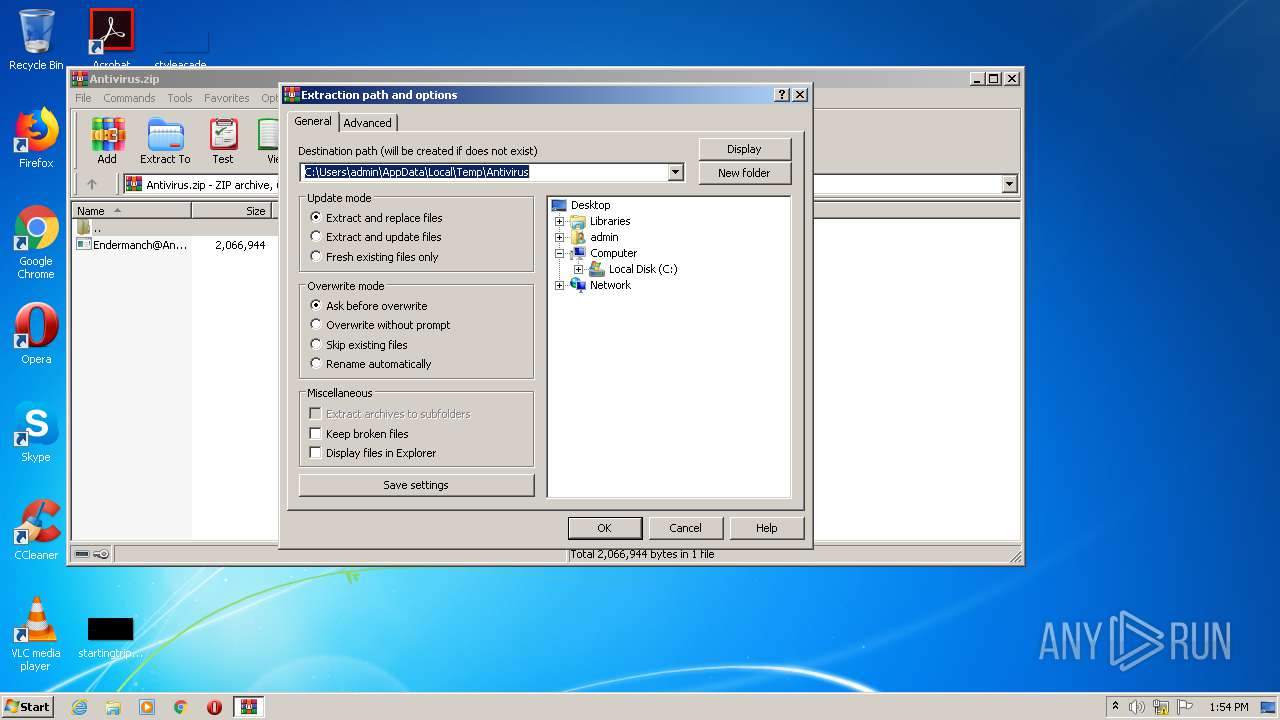
| 2784 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Antivirus.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3744 | "C:\Users\admin\Desktop\Endermanch@Antivirus.exe" | C:\Users\admin\Desktop\Endermanch@Antivirus.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
531
Read events
484
Write events
47
Delete events
0
Modification events
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Antivirus.zip | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
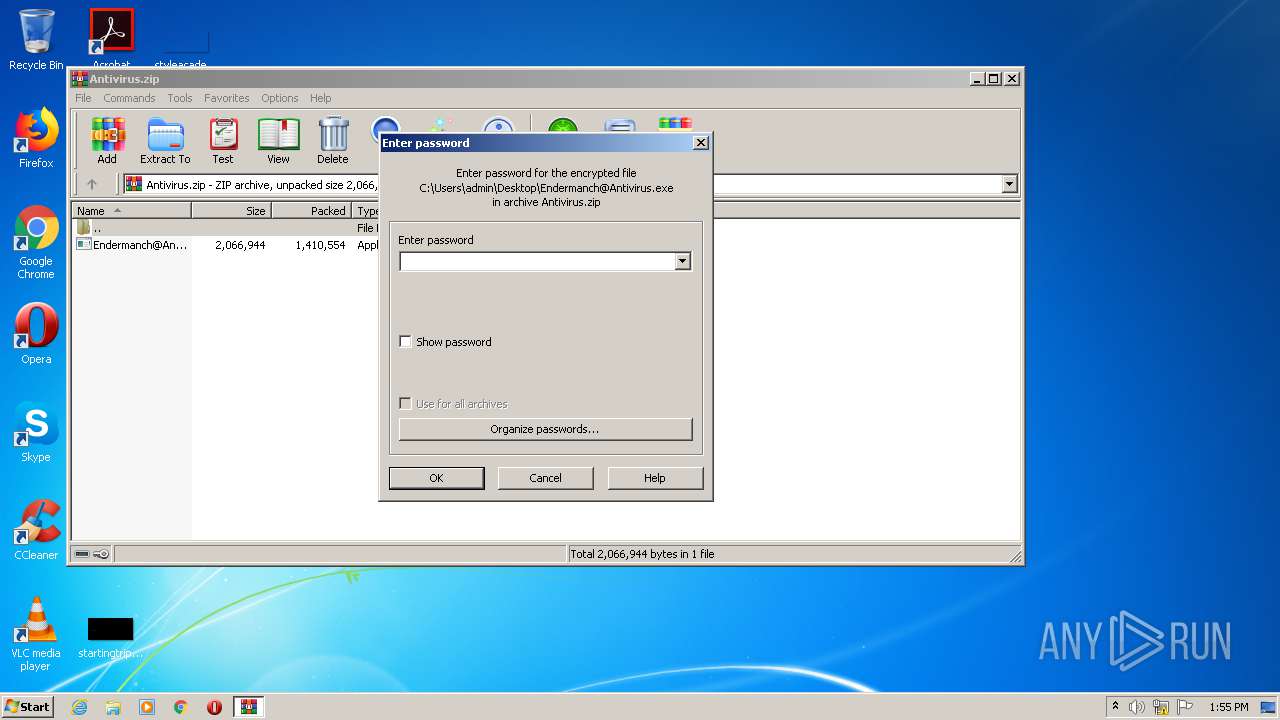
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | Endermanch@Antivirus.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\2GKVG5RO.txt | text | |
MD5:— | SHA256:— | |||
| 2784 | WinRAR.exe | C:\Users\admin\Desktop\Endermanch@Antivirus.exe | executable | |
MD5:C7E9746B1B039B8BD1106BCA3038C38F | SHA256:B1369BD254D96F7966047AD4BE06103830136629590182D49E5CB8680529EBD4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
4
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3744 | Endermanch@Antivirus.exe | GET | 429 | 212.32.237.90:80 | http://searchdusty.com/avt/avt_db | NL | text | 17 b | whitelisted |
3744 | Endermanch@Antivirus.exe | GET | 429 | 212.32.237.90:80 | http://searchdusty.com/avt/avt.dat | NL | text | 17 b | whitelisted |
3744 | Endermanch@Antivirus.exe | GET | 429 | 212.32.237.90:80 | http://searchdusty.com/avt/avtr.dat | NL | text | 17 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3744 | Endermanch@Antivirus.exe | 212.32.237.90:80 | searchdusty.com | LeaseWeb Netherlands B.V. | NL | malicious |
— | — | 212.32.237.90:80 | searchdusty.com | LeaseWeb Netherlands B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fastsofgeld.com |
| malicious |
searchdusty.com |
| whitelisted |
highway-traffic.com |
| malicious |
frequentwin.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3744 | Endermanch@Antivirus.exe | Potentially Bad Traffic | ET USER_AGENTS User-Agent (Internet Explorer) |
3744 | Endermanch@Antivirus.exe | Potentially Bad Traffic | ET USER_AGENTS User-Agent (Internet Explorer) |
3744 | Endermanch@Antivirus.exe | Potentially Bad Traffic | ET USER_AGENTS User-Agent (Internet Explorer) |