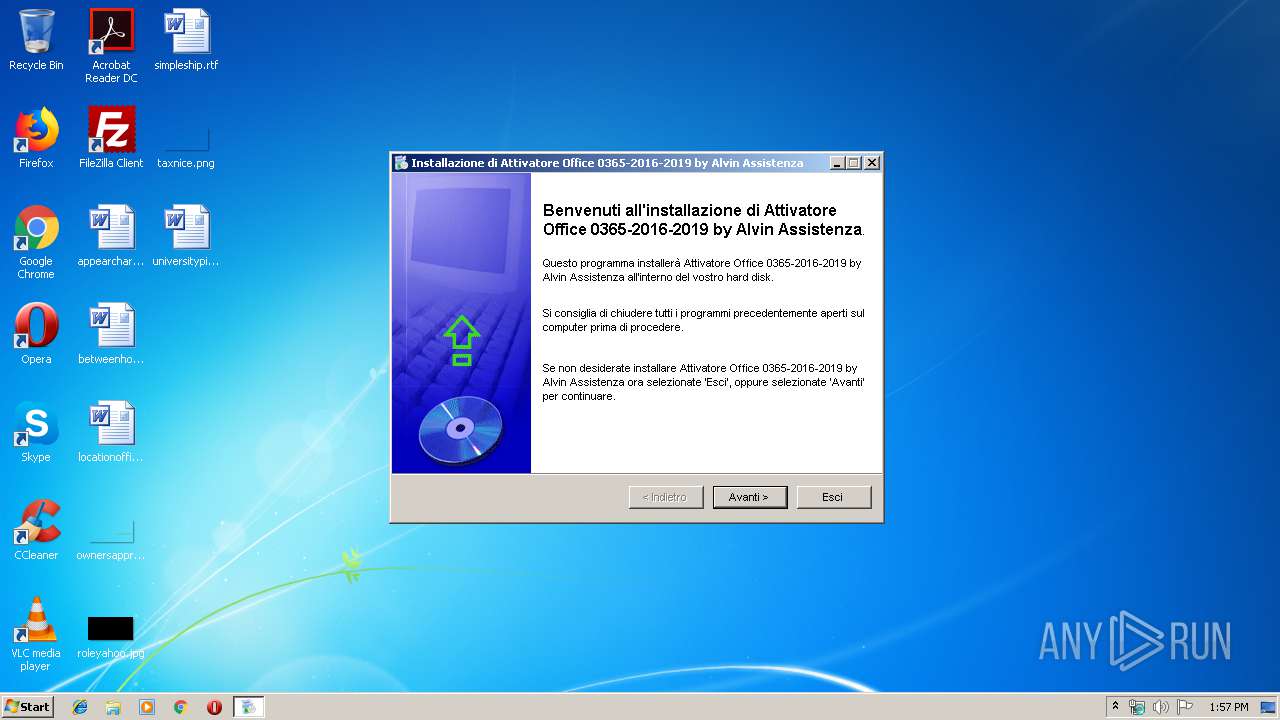
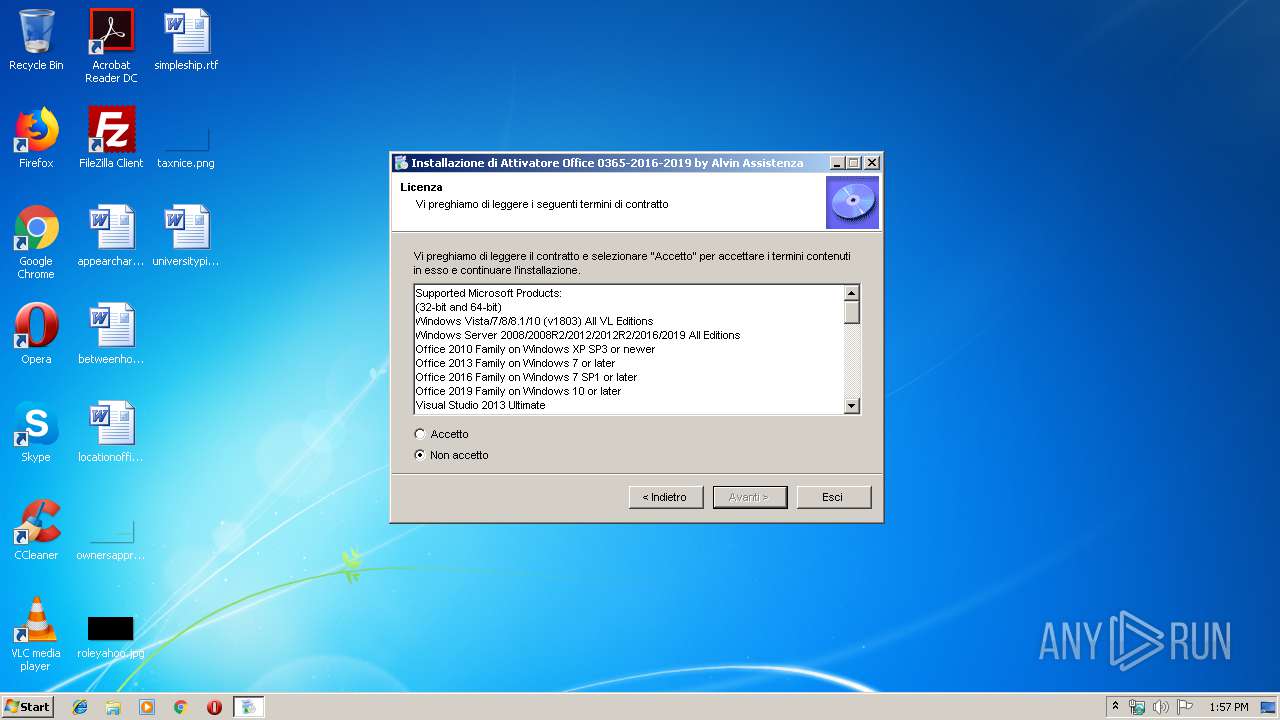
| File name: | Attivatore Office 0365-2016-2019.exe |
| Full analysis: | https://app.any.run/tasks/3acff21c-1fe5-46e4-bba0-297fb61a4ae8 |
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2019, 13:57:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C388FF923B654BCCA9FA4175FD31F9A1 |
| SHA1: | FB228781087498729E38F8DC59F08A7D12619CCA |
| SHA256: | EAB94F7D122901CD68BFBF3E9ACFA680F9B884E4324617D18E84E5B82C5004B9 |
| SSDEEP: | 12288:jnNRa3zuXA8mwftWHWCqwHPUZQn0TIuQJn9qAn20yXqTCRvy+zxZe:DS3zozmw3aPU00T0nkwgqAvTxZe |
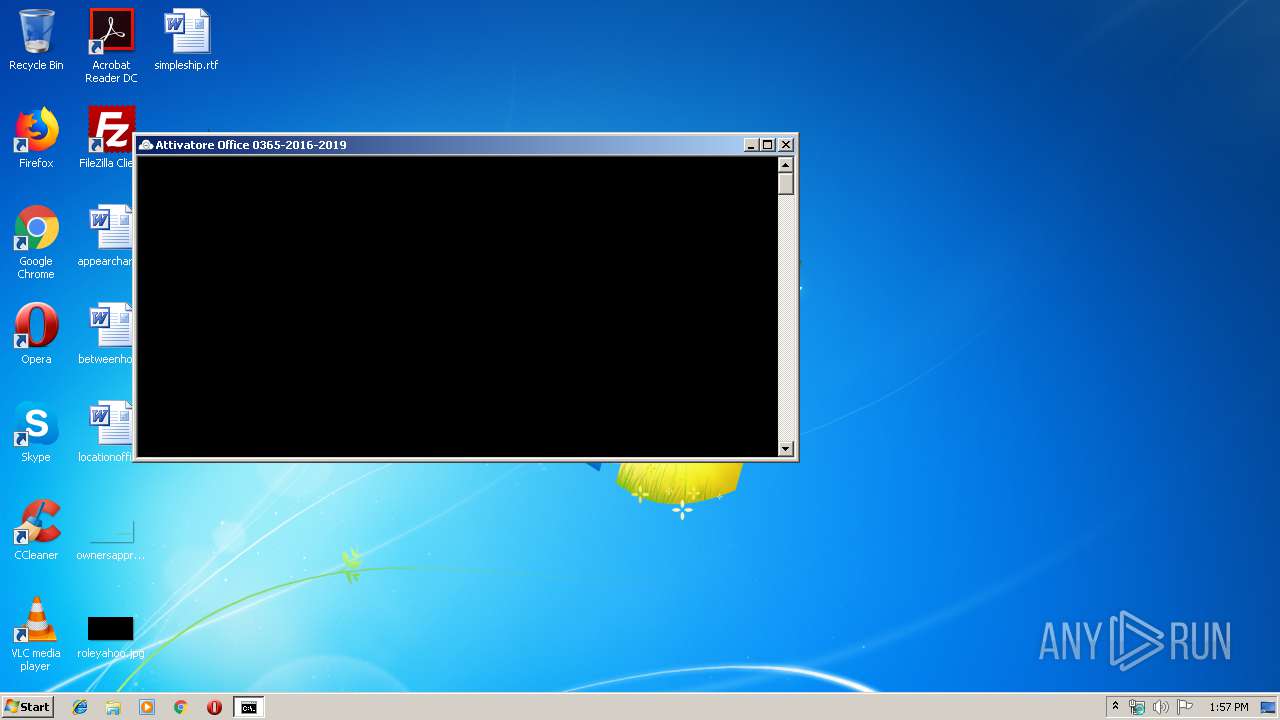
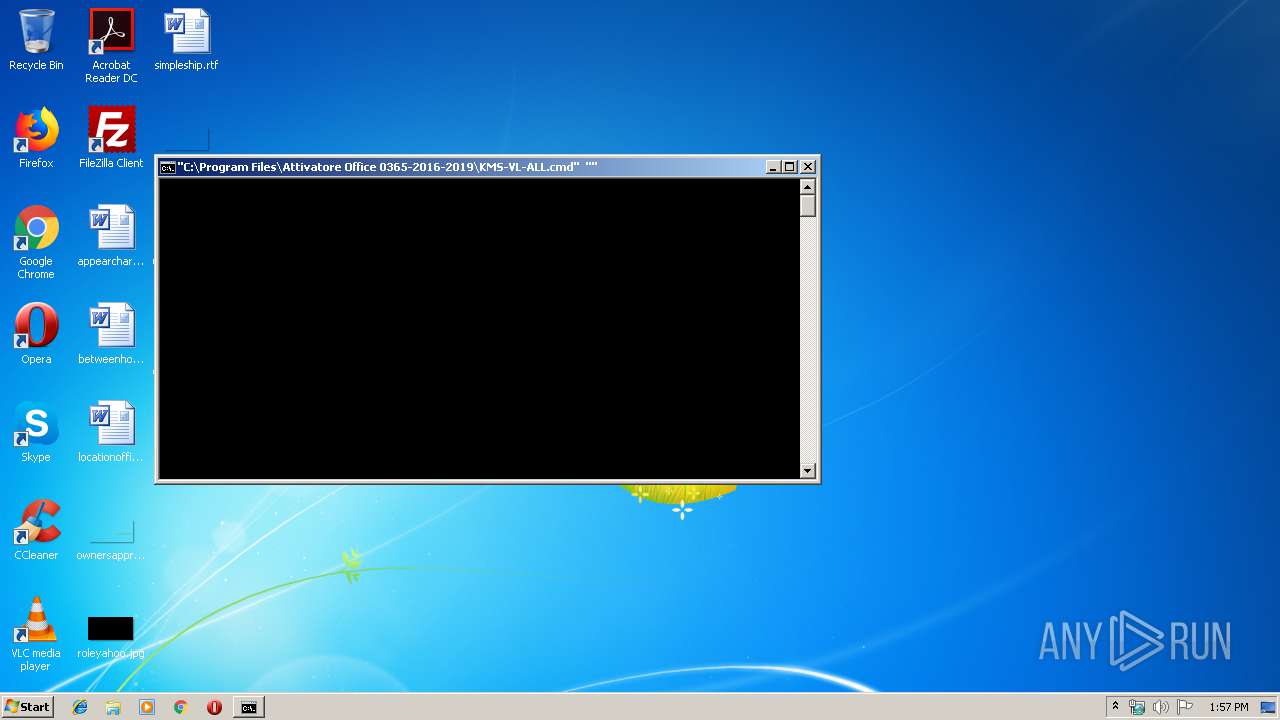
MALICIOUS
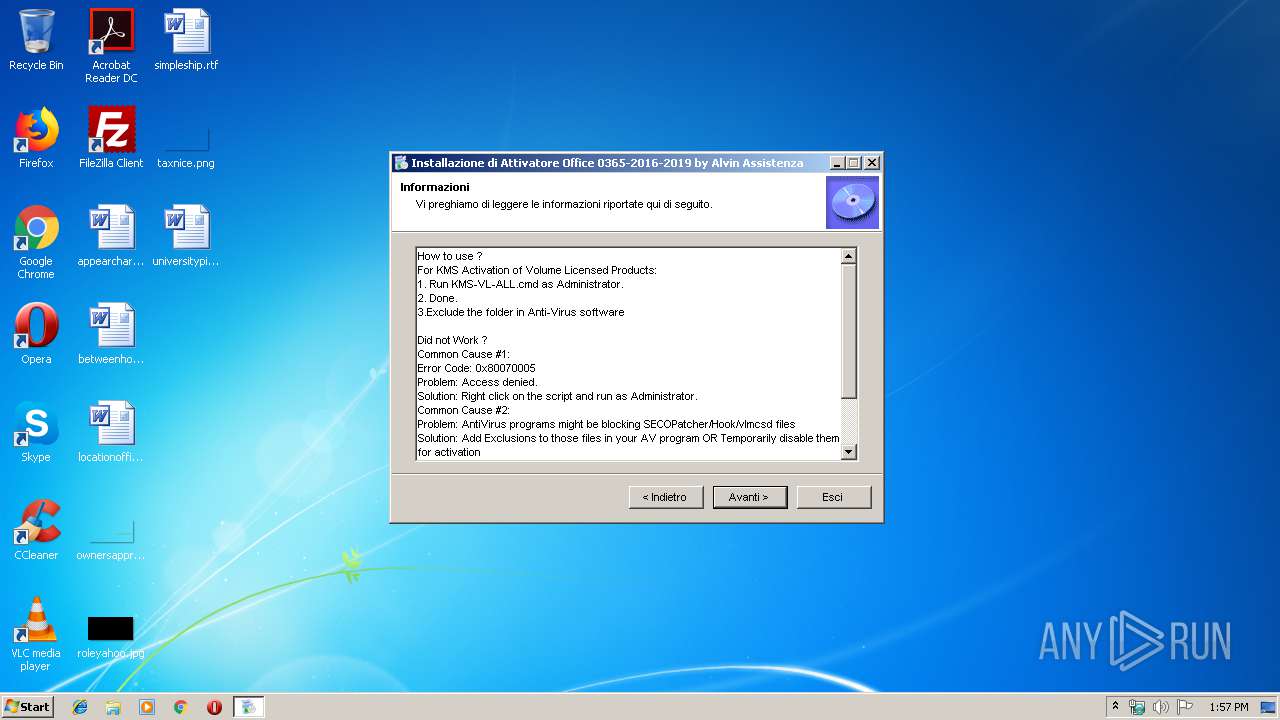
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1400)
- schtasks.exe (PID: 2800)
Application was dropped or rewritten from another process
- vlmcsd.exe (PID: 2028)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2136)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2136)
SUSPICIOUS
Executable content was dropped or overwritten
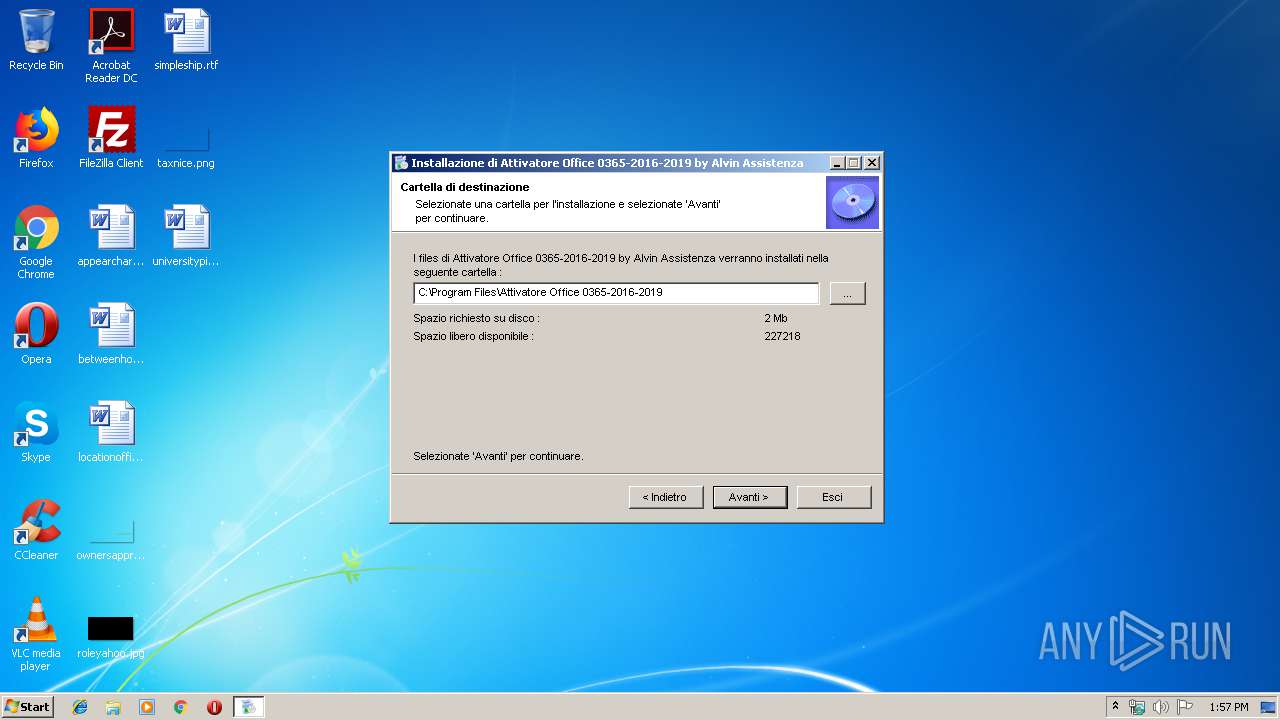
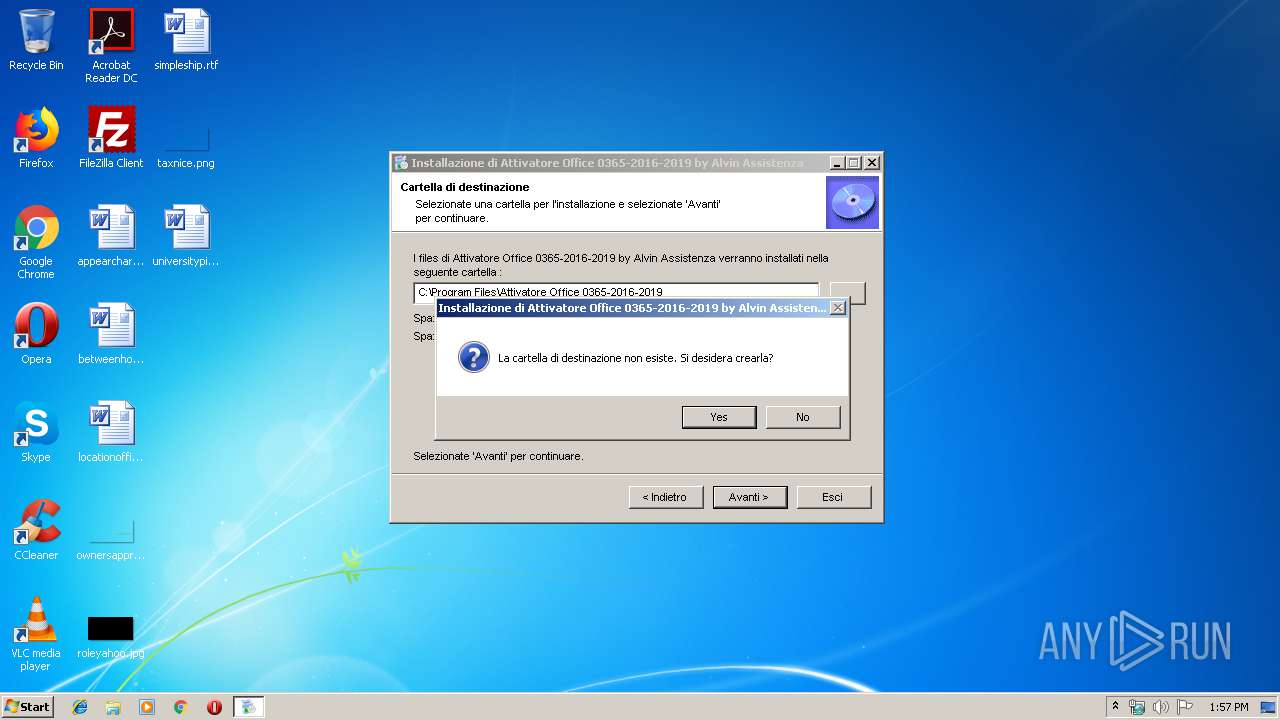
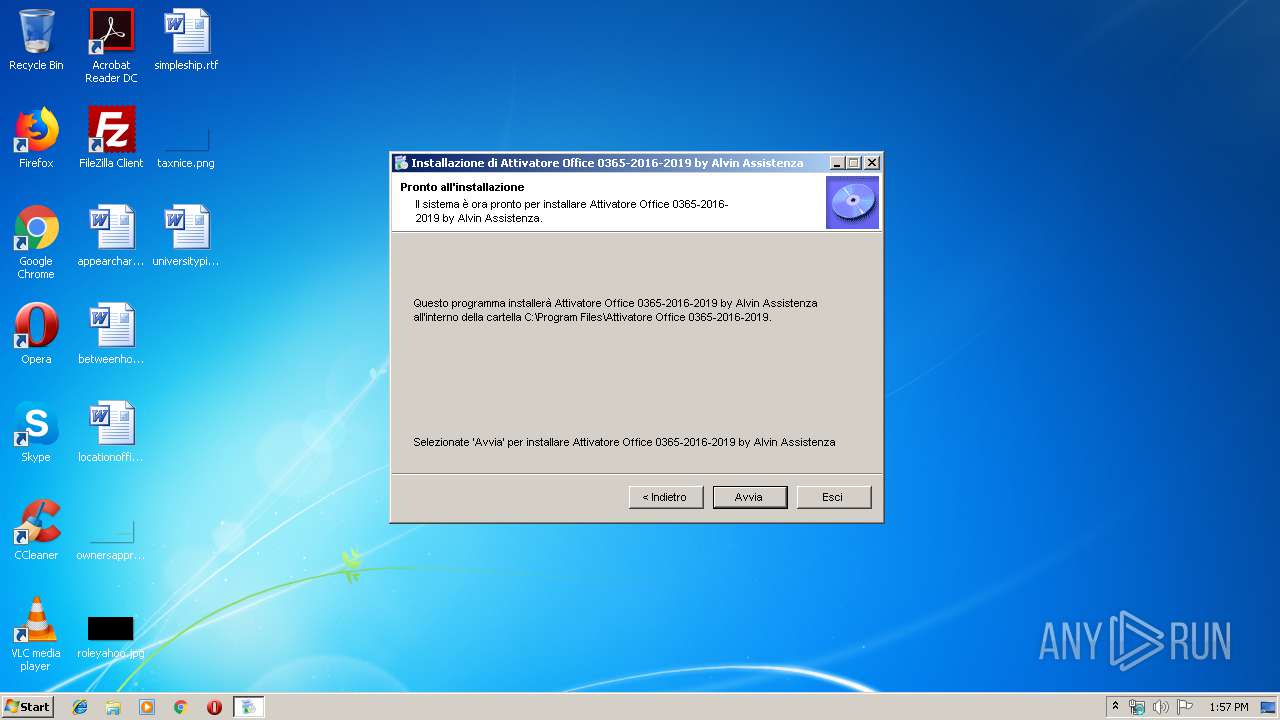
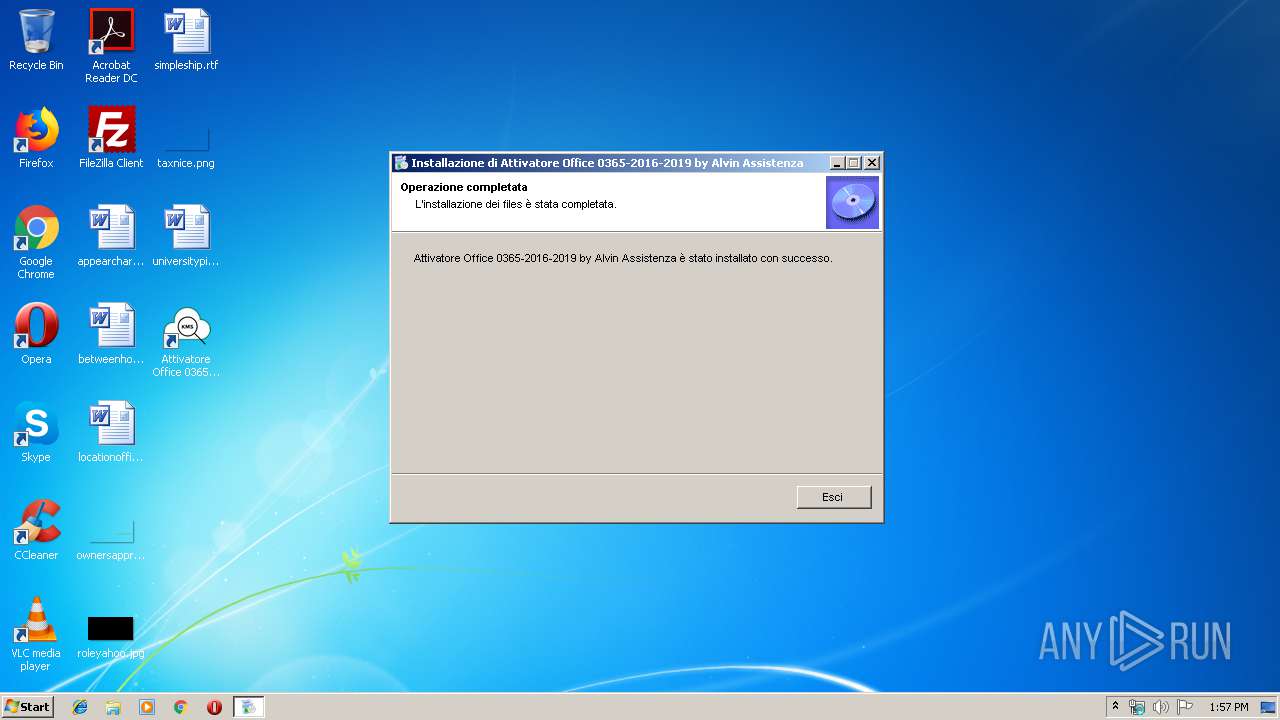
- Attivatore Office 0365-2016-2019.exe (PID: 3948)
Creates files in the program directory
- Attivatore Office 0365-2016-2019.exe (PID: 3948)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3016)
- WScript.exe (PID: 2992)
- cmd.exe (PID: 2136)
Application launched itself
- cmd.exe (PID: 3016)
- cmd.exe (PID: 2136)
Executes scripts
- cmd.exe (PID: 3016)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1608)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 2200)
- cmd.exe (PID: 3348)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 2684)
- cmd.exe (PID: 656)
- cmd.exe (PID: 2724)
- cmd.exe (PID: 2584)
- cmd.exe (PID: 2136)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2136)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 4072)
- cmd.exe (PID: 4028)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 2416)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 2572)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2136)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2136)
INFO
Manual execution by user
- cmd.exe (PID: 3016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:12:08 08:35:06+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 139264 |
| InitializedDataSize: | 1183744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1bcf2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.43 |
| ProductVersionNumber: | 2.0.0.43 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 2, 0, 0, 43 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| PrivateBuild: | - |
| ProductName: | Installazione di Attivatore Office 0365-2016-2019 by Alvin As |
| enzactVersion: | 2, 0, 0, 43 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Dec-2011 07:35:06 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 2, 0, 0, 43 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| PrivateBuild: | - |
| ProductName: | Installazione di Attivatore Office 0365-2016-2019 by Alvin Assistenza ctVersion |
| 0, 0, 43: | - |
| ecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 08-Dec-2011 07:35:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000215BA | 0x00022000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6021 |
.rdata | 0x00023000 | 0x0000206A | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.12694 |
.data | 0x00026000 | 0x00006260 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.07035 |
.rsrc | 0x0002D000 | 0x00117DAC | 0x00118000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.54224 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.24462 | 971 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.65697 | 872 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.37871 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.6351 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.67794 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.19306 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.10986 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.66471 | 7336 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.30274 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.15982 | 2664 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
comdlg32.dll |
ole32.dll |
Total processes
138
Monitored processes
92
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | C:\Windows\system32\cmd.exe /S /D /c" echo """ | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 592 | wmic path OfficeSoftwareProtectionService get Version /value | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 640 | findstr /i "Windows" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 656 | C:\Windows\system32\cmd.exe /c "reg query HKLM\SOFTWARE\Microsoft\VisualStudio\12.0 /v InstallDir" 2>nul | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 656 | wmic path SoftwareLicensingProduct where ID='b92e9980-b9d5-4821-9c94-140f632f6312' get Name /value | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 716 | fltmc | C:\Windows\system32\fltMC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Filter Manager Control Program Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 720 | reg query HKLM\SOFTWARE\Microsoft\VisualStudio\12.0 /v InstallDir | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 736 | wmic path SoftwareLicensingProduct where (Description like '%KMSCLIENT%') get Name /value | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 784 | wmic path SoftwareLicensingProduct where (PartialProductKey is not NULL) get ID | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | netsh advfirewall firewall add rule name="vlmcsd" dir=in action=allow profile=any program="C:\Program Files\Attivatore Office 0365-2016-2019\32-bit\vlmcsd.exe" | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 520
Read events
1 370
Write events
150
Delete events
0
Modification events
| (PID) Process: | (3016) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3016) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2992) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2992) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2956) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2956) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2956) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2956) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (892) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2956) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
Executable files
5
Suspicious files
1
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\Uninstal.$A | — | |
MD5:— | SHA256:— | |||
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\32-bit\SECOPatcher.$A | — | |
MD5:— | SHA256:— | |||
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\32-bit\vlmcsd.$A | — | |
MD5:— | SHA256:— | |||
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\64-bit\SECOPatcher.$A | — | |
MD5:— | SHA256:— | |||
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\Install.$A | — | |
MD5:— | SHA256:— | |||
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\KMS-VL-ALL.$A | — | |
MD5:— | SHA256:— | |||
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\KMSicon.$A | — | |
MD5:— | SHA256:— | |||
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\Uninstall.$A | — | |
MD5:— | SHA256:— | |||
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\Uninstal.exe | executable | |
MD5:— | SHA256:— | |||
| 3948 | Attivatore Office 0365-2016-2019.exe | C:\Program Files\Attivatore Office 0365-2016-2019\32-bit\vlmcsd.exe | executable | |
MD5:3199D660B6D2DA836FCABCA41ECBC0E5 | SHA256:BFC3DB2E8D0BCA6F4E189191D5500D6D6B5D9CE83C3EE379253CC20505FA24C3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report