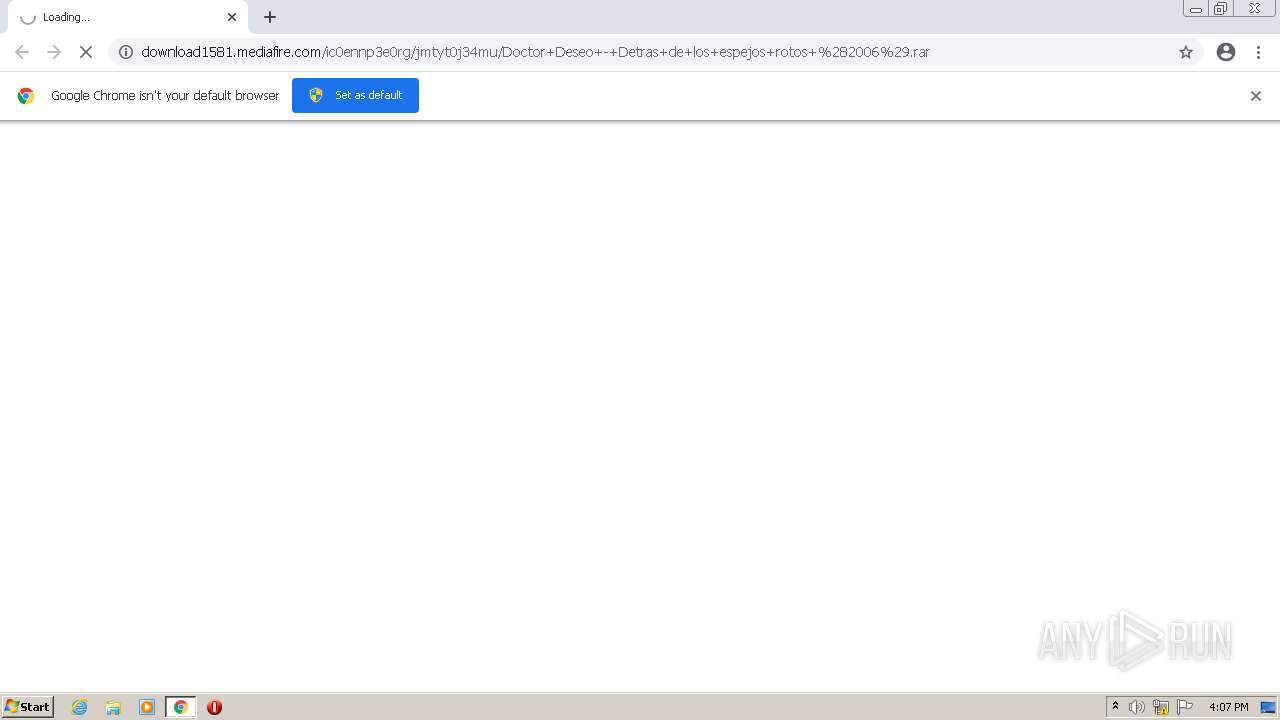
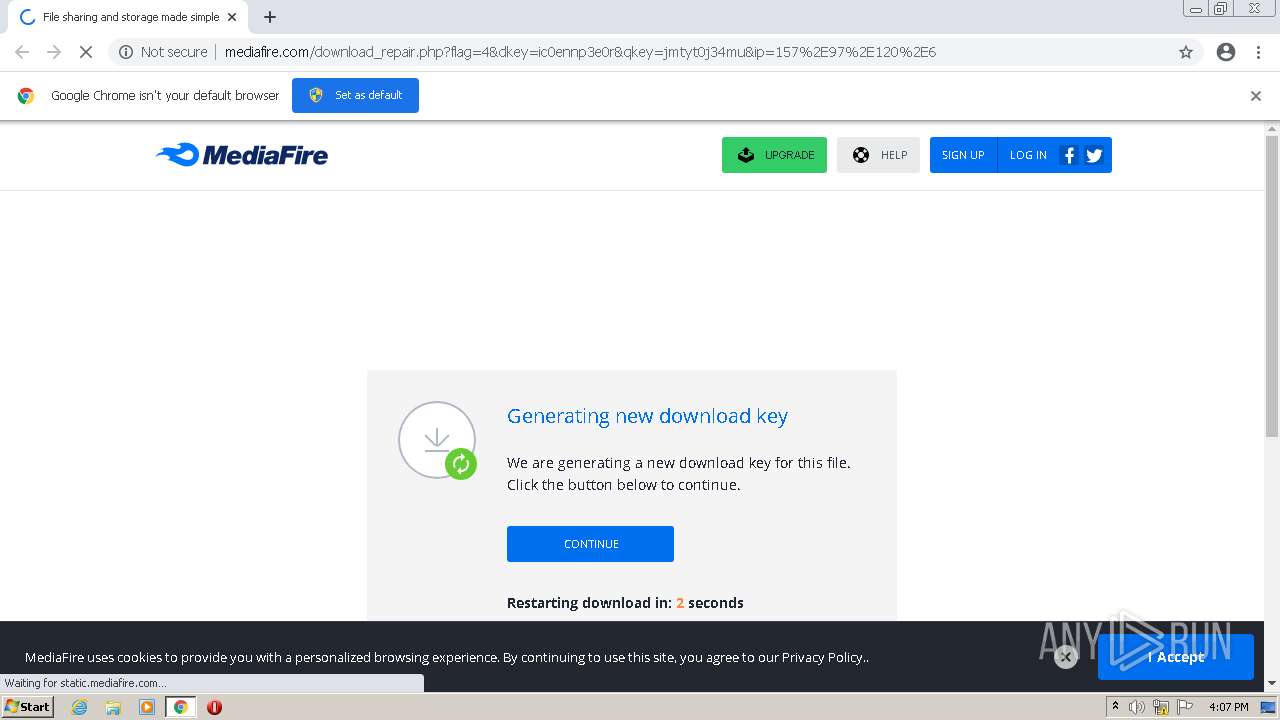
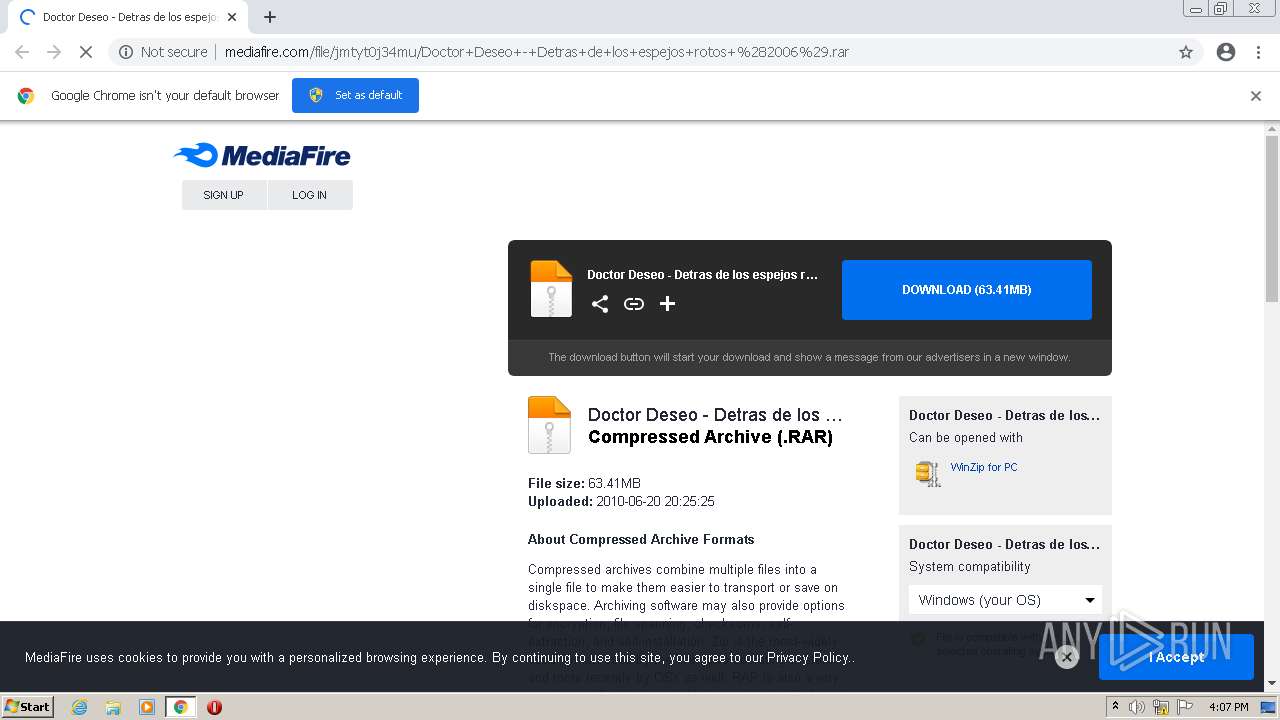
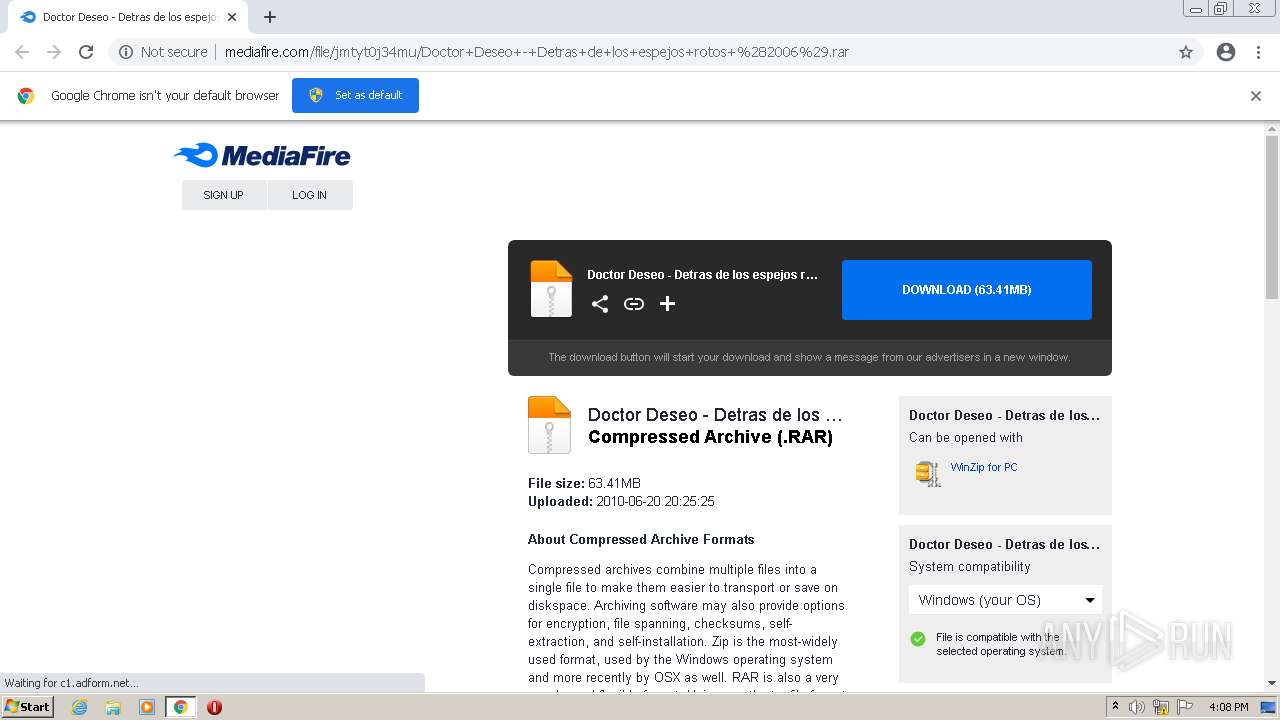
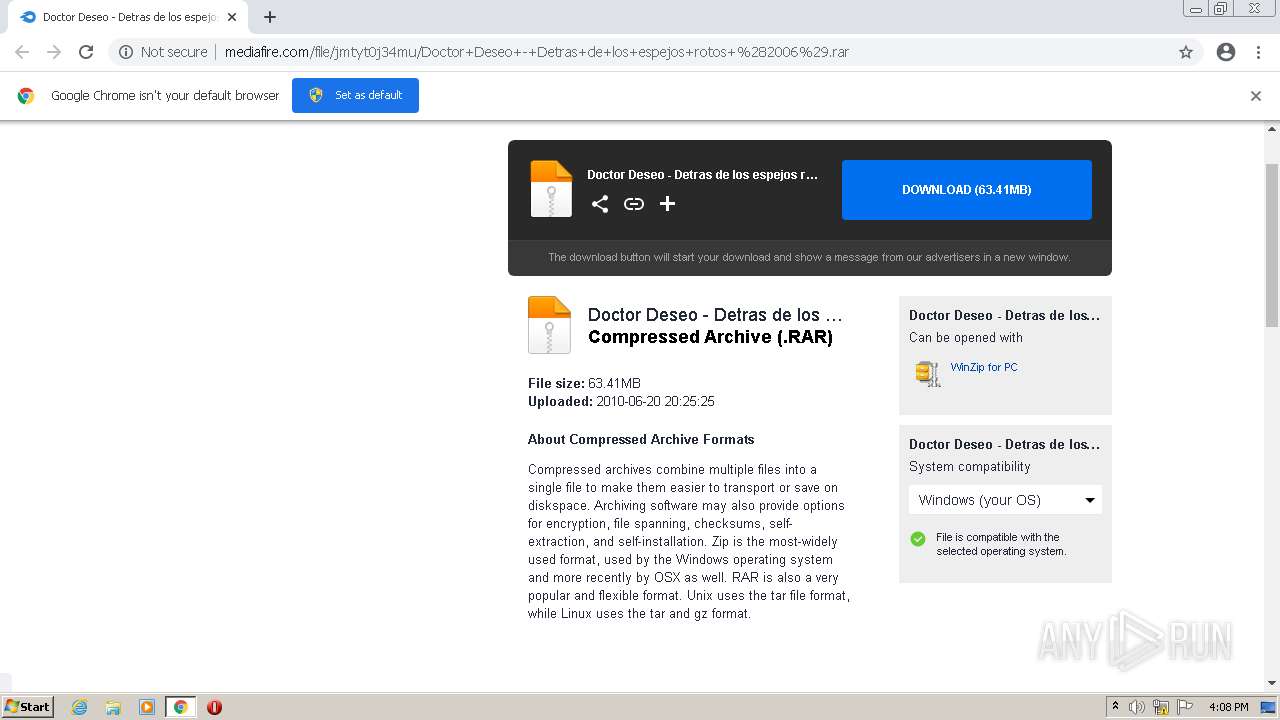
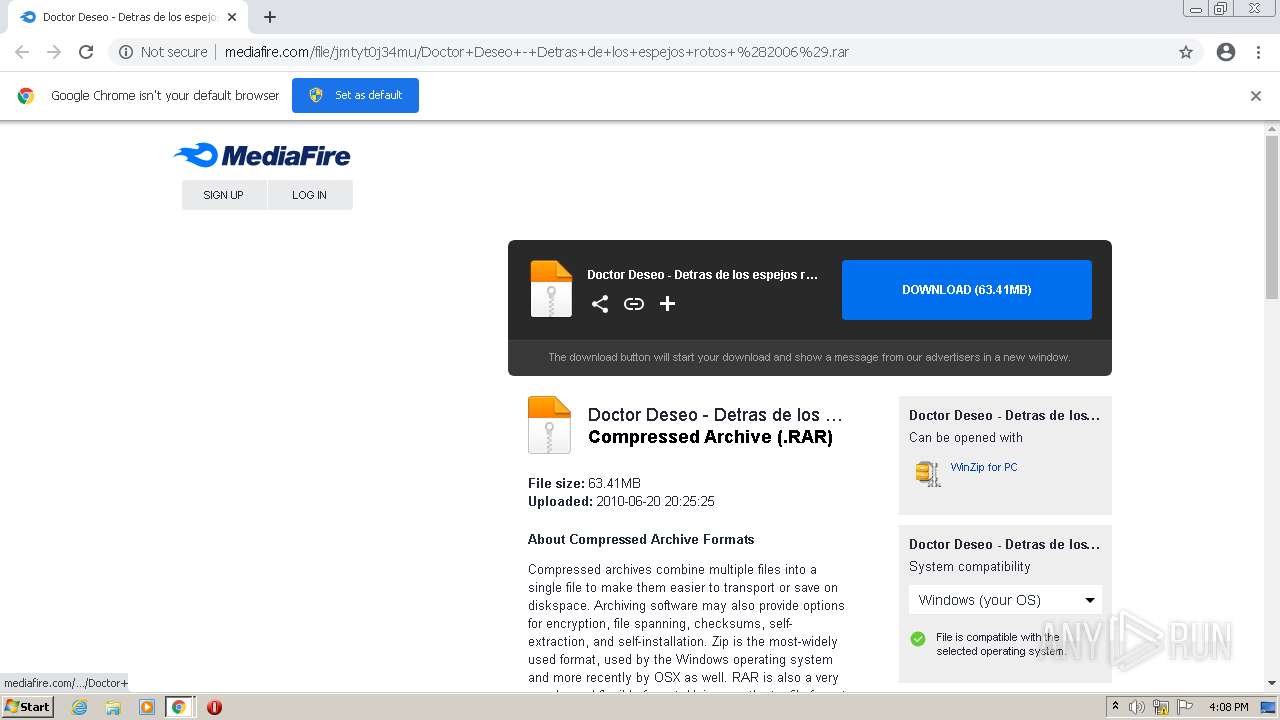
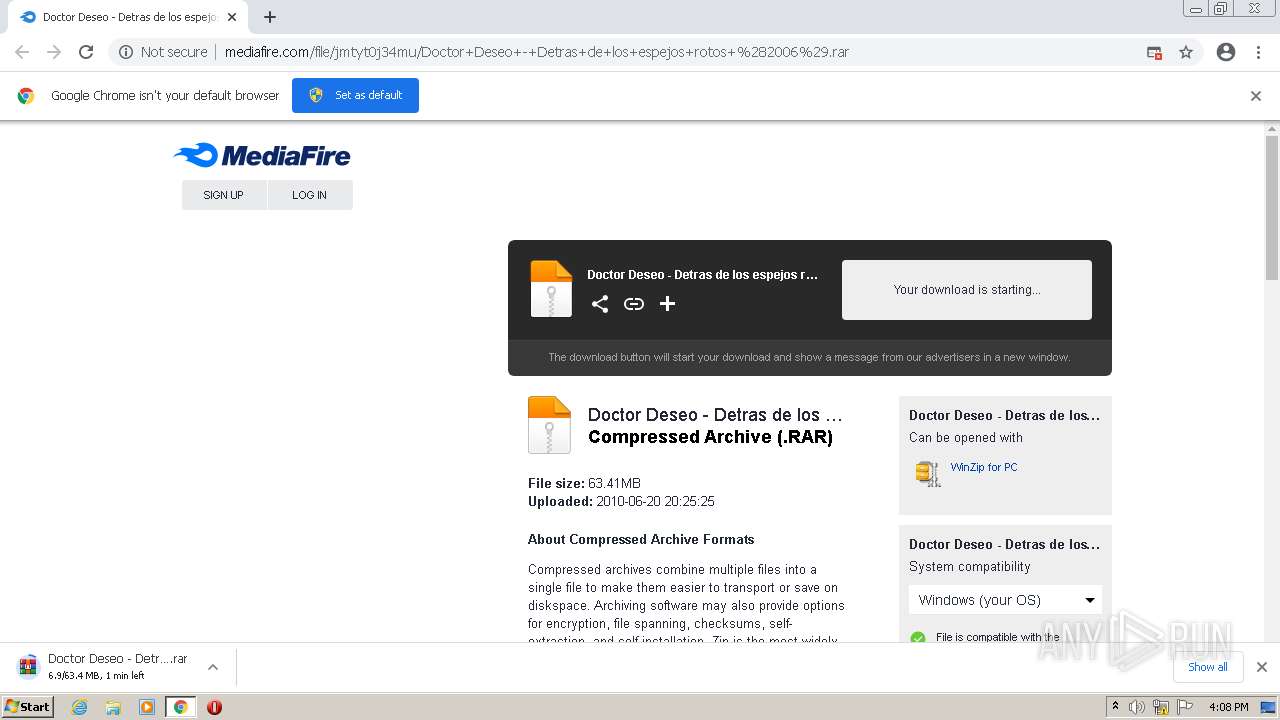
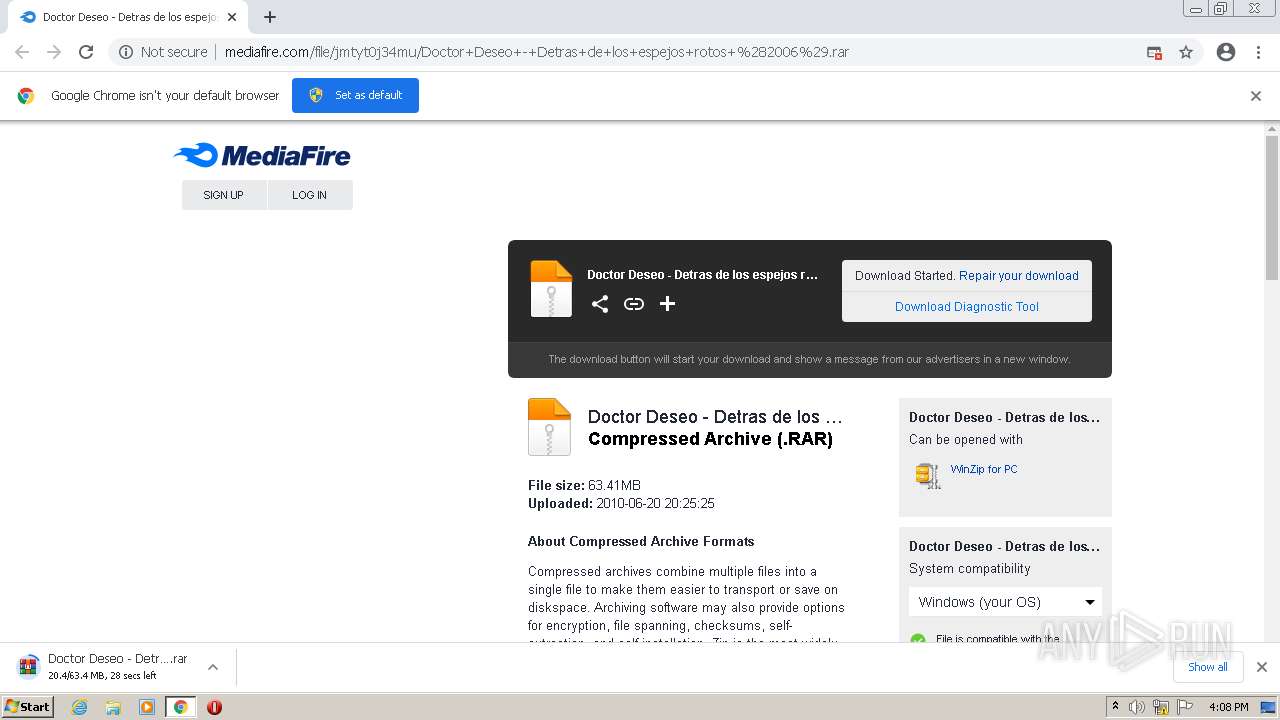
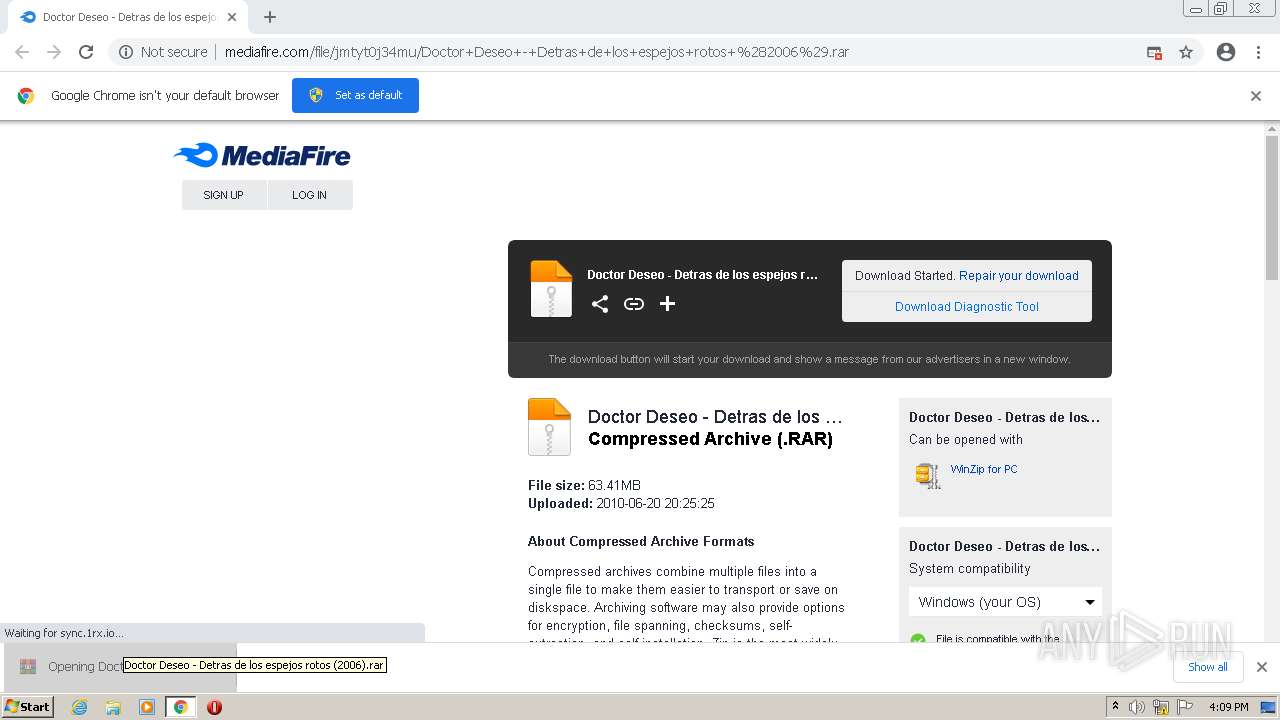
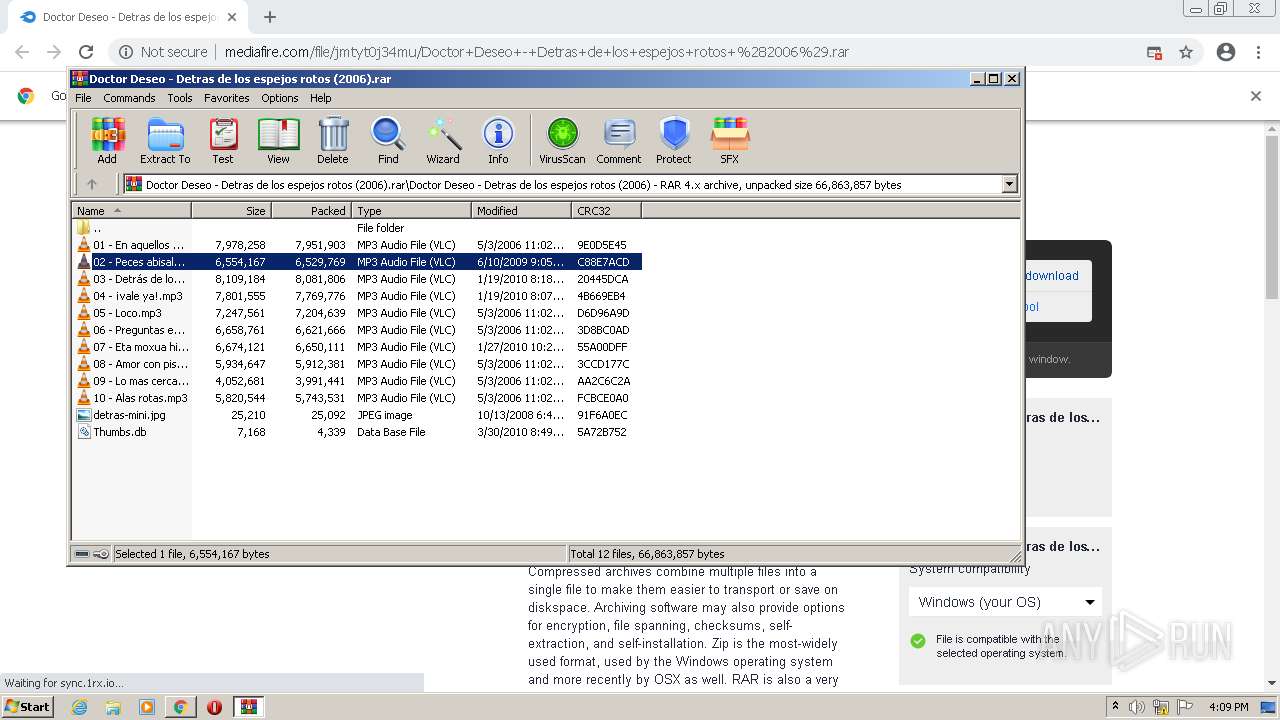
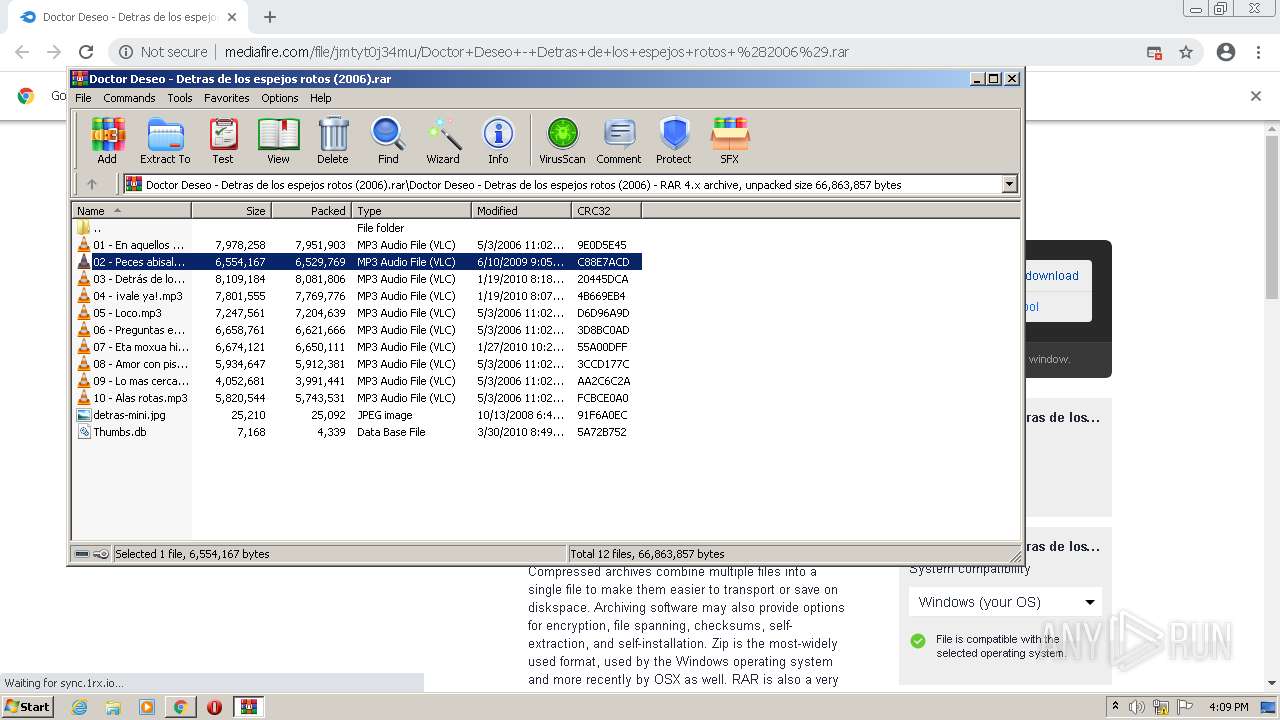
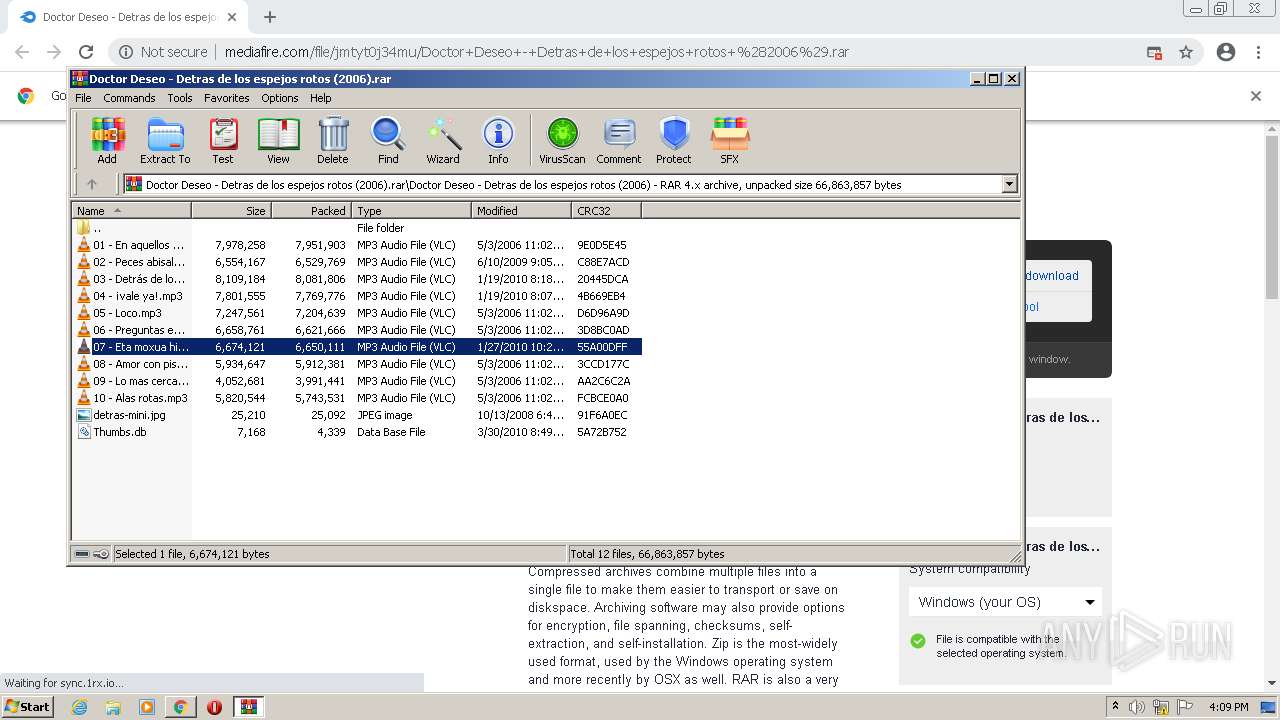
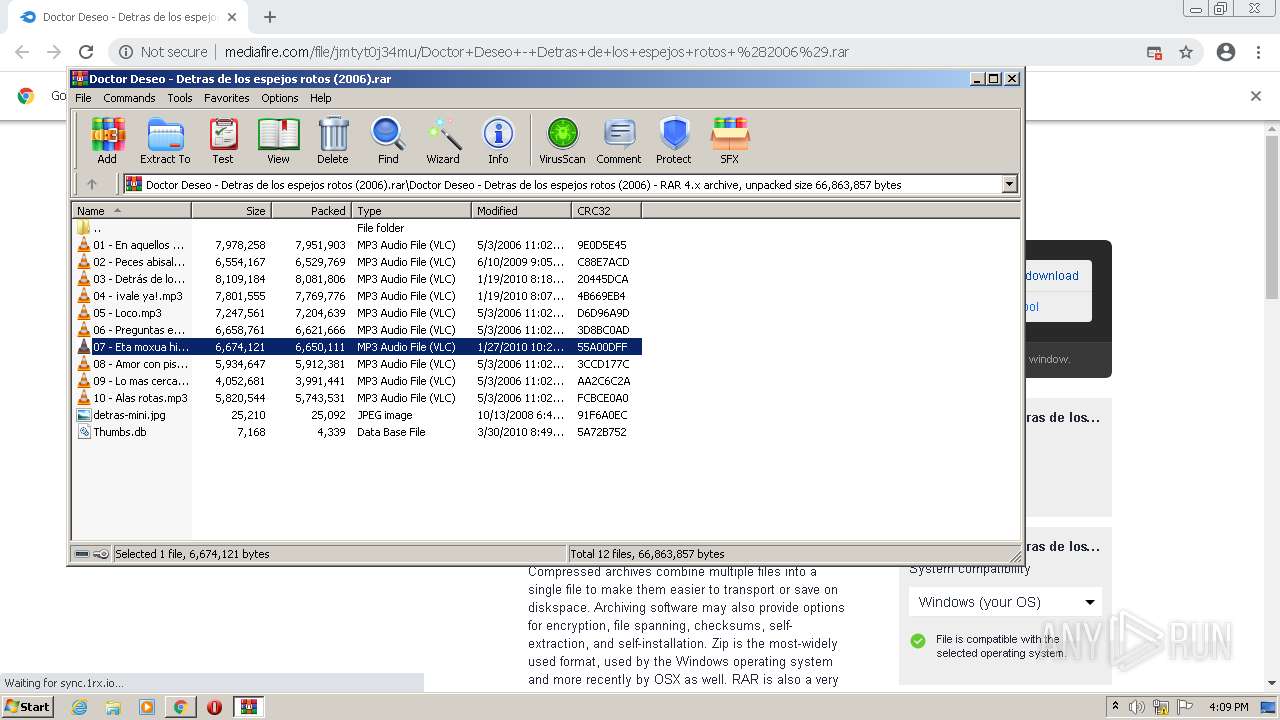
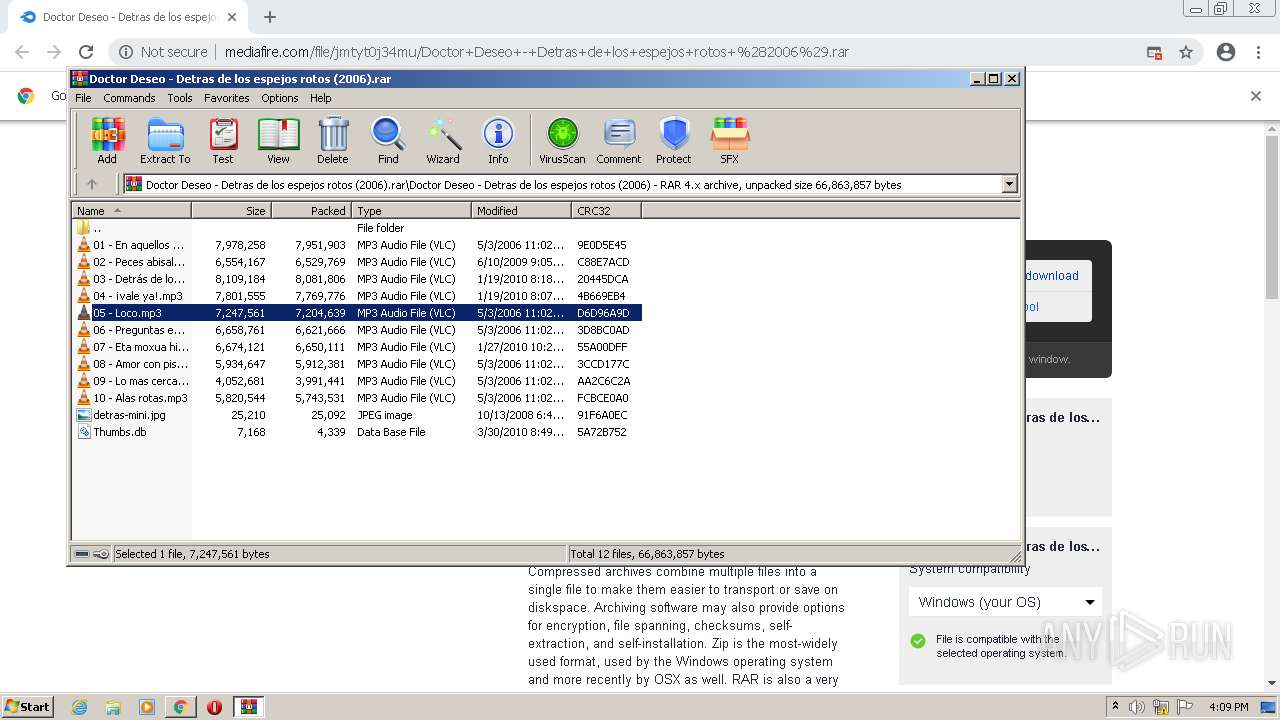
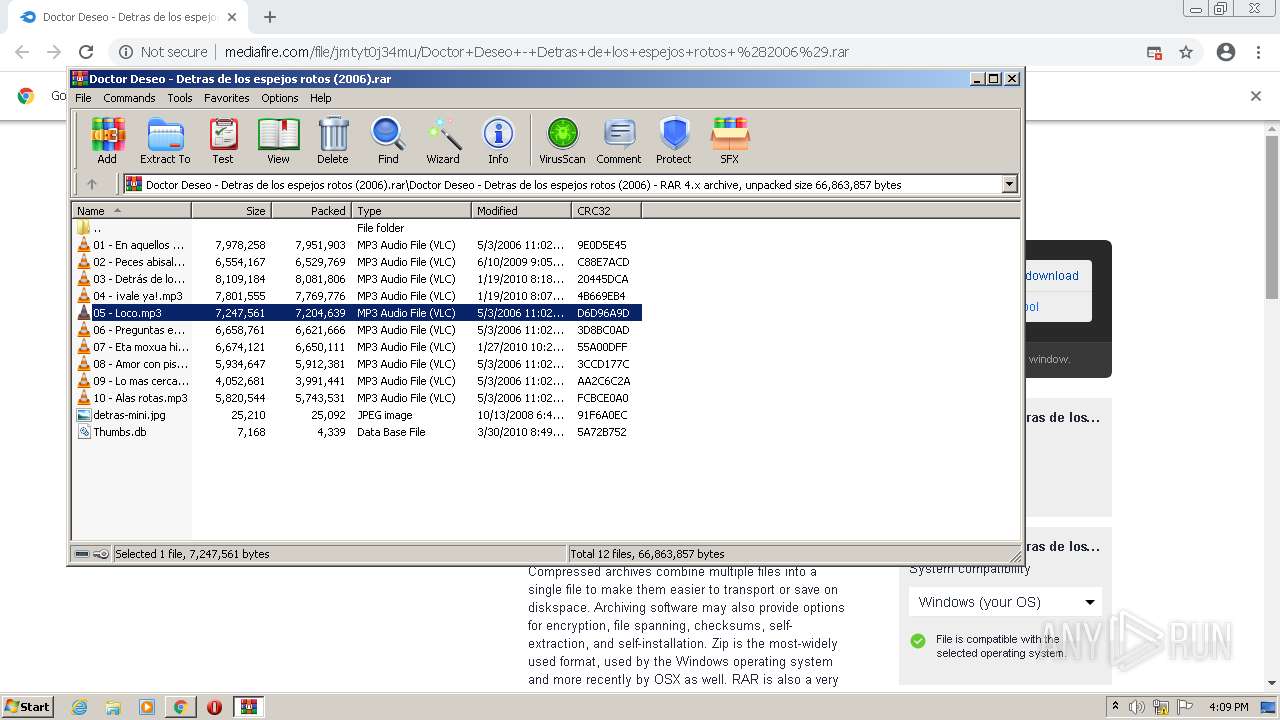
| URL: | http://download1581.mediafire.com/ic0ennp3e0rg/jmtyt0j34mu/Doctor+Deseo+-+Detras+de+los+espejos+rotos+%282006%29.rar |
| Full analysis: | https://app.any.run/tasks/3a7db6fb-eac1-41a7-86a2-5687392594f8 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 15:07:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2CF91C827E0CC4A92353E94C269D3374 |
| SHA1: | 0EF1D80D030A17AFD4B4F84E22DBB82BDB331DE9 |
| SHA256: | EAA8E3B06AD6239B979063D004B165632F40BC464DAD4DBF2CD014BAA742C0FF |
| SSDEEP: | 3:N1KaKE6QdSxQeGbCA/z5wRQAKhK+SuWdQqPN4Kf/5AMa:CanYQeGbCA/z5Oj+SuDqPmseMa |
MALICIOUS
No malicious indicators.SUSPICIOUS
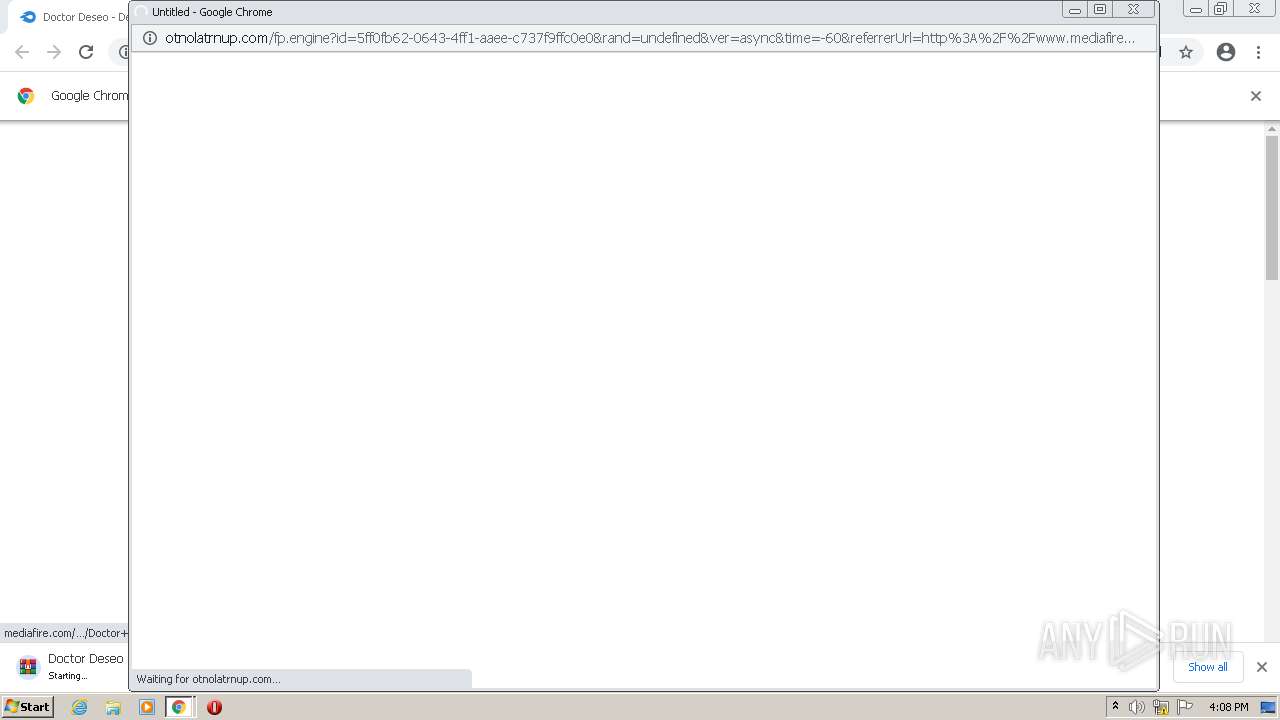
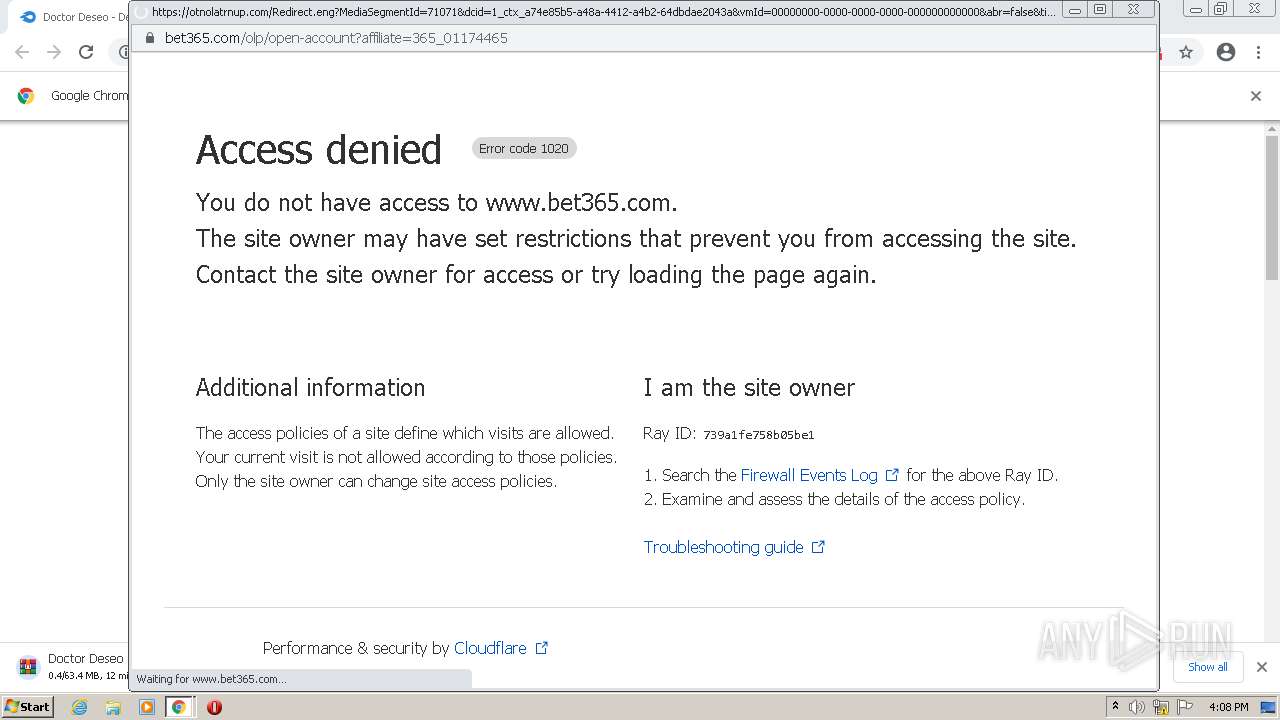
Modifies files in Chrome extension folder
- chrome.exe (PID: 3148)
Checks supported languages
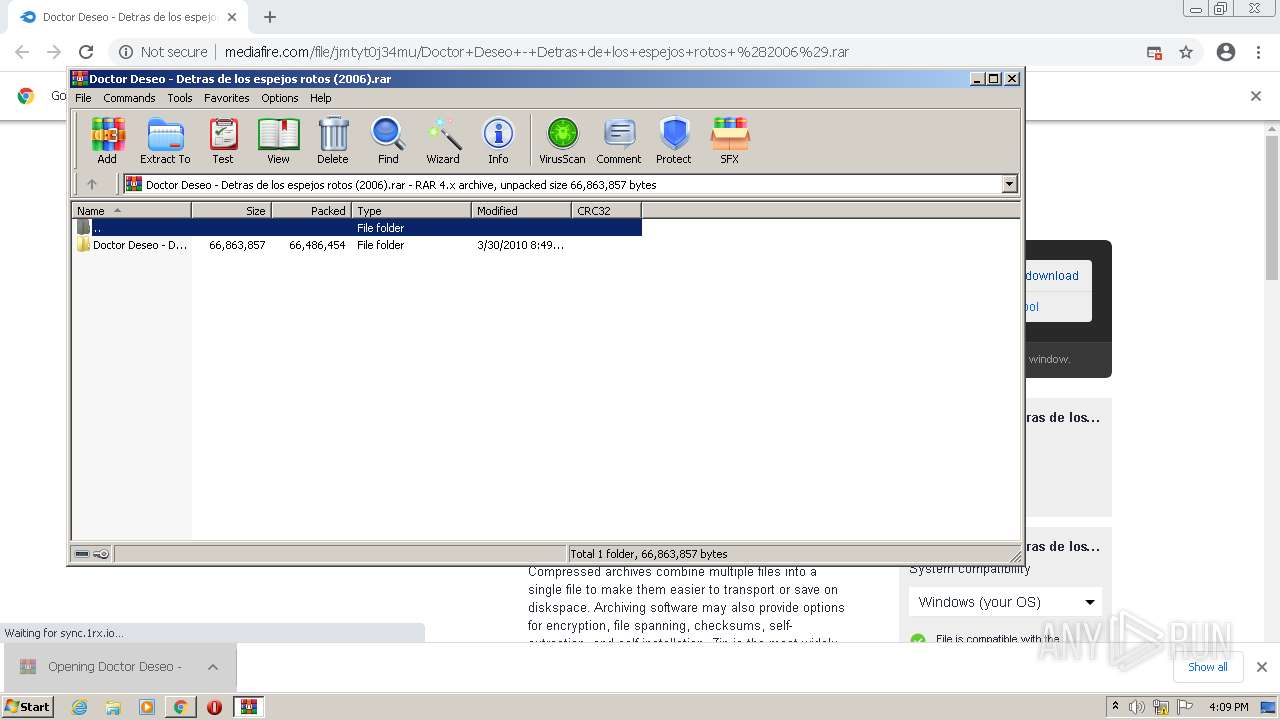
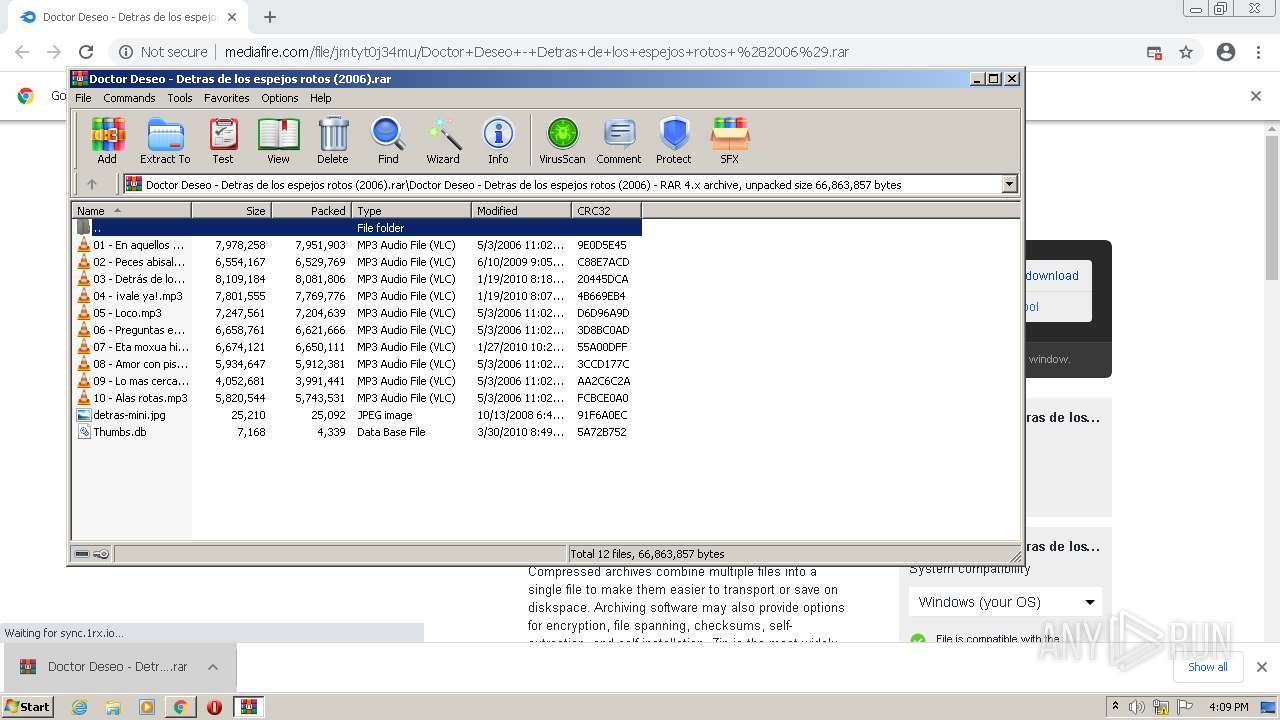
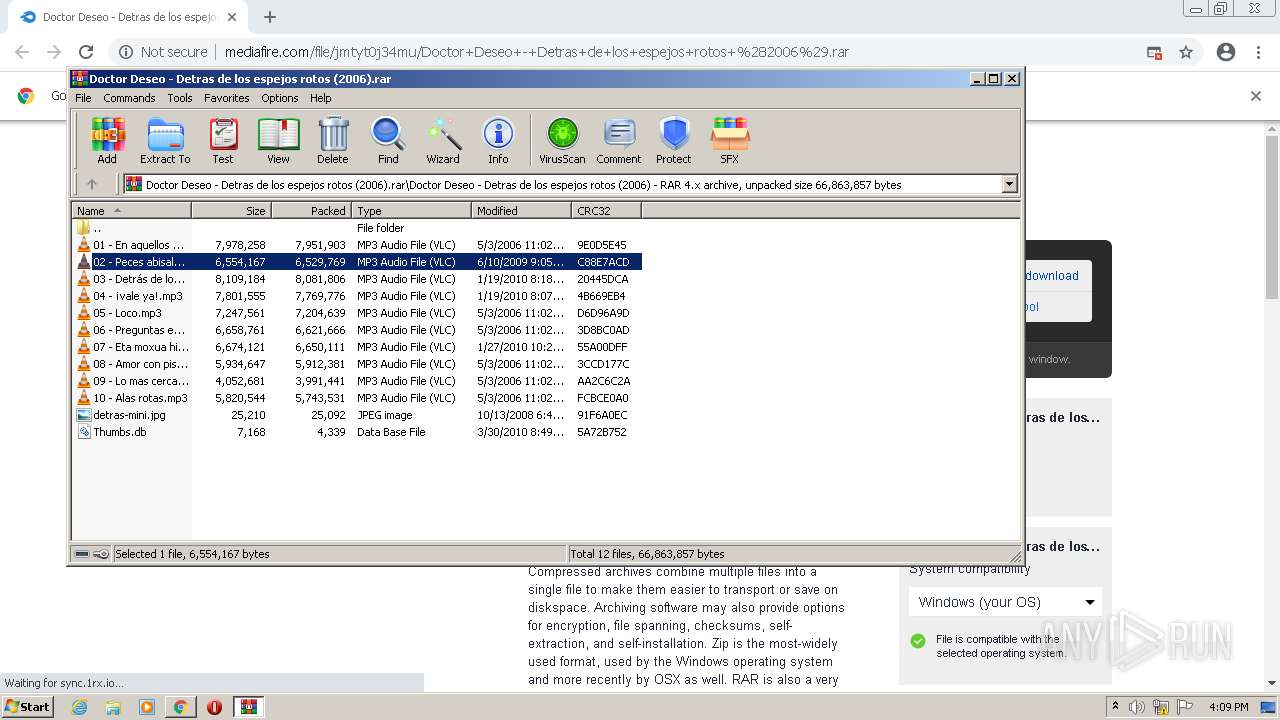
- WinRAR.exe (PID: 2904)
- vlc.exe (PID: 3124)
- vlc.exe (PID: 3472)
- vlc.exe (PID: 2084)
Reads the computer name
- WinRAR.exe (PID: 2904)
- vlc.exe (PID: 3124)
- vlc.exe (PID: 3472)
- vlc.exe (PID: 2084)
INFO
Application launched itself
- chrome.exe (PID: 3148)
Checks supported languages
- chrome.exe (PID: 3148)
- chrome.exe (PID: 560)
- chrome.exe (PID: 2344)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 1812)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 1784)
- chrome.exe (PID: 3536)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 124)
- chrome.exe (PID: 1532)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 1144)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 1080)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 3760)
- chrome.exe (PID: 368)
- chrome.exe (PID: 544)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 1360)
- chrome.exe (PID: 556)
- chrome.exe (PID: 1712)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 400)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 1312)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 3620)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 664)
Reads the computer name
- chrome.exe (PID: 1784)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 1812)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 1532)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 1712)
- chrome.exe (PID: 3888)
Reads settings of System Certificates
- chrome.exe (PID: 1812)
Reads the date of Windows installation
- chrome.exe (PID: 1532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
52
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4796 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,18369265825848302758,13629338319249528964,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1112 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
37 830
Read events
37 652
Write events
178
Delete events
0
Modification events
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
36
Text files
138
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F66CBB-C4C.pma | — | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3f568f57-a78d-426e-8a69-6a70c97c182e.tmp | text | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF134b45.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF134b35.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF134b25.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9ebf0046-15b3-4871-a048-cbc19e25647d.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
219
DNS requests
123
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1812 | chrome.exe | GET | 302 | 199.91.152.81:80 | http://download1581.mediafire.com/ic0ennp3e0rg/jmtyt0j34mu/Doctor+Deseo+-+Detras+de+los+espejos+rotos+%282006%29.rar | US | — | — | suspicious |
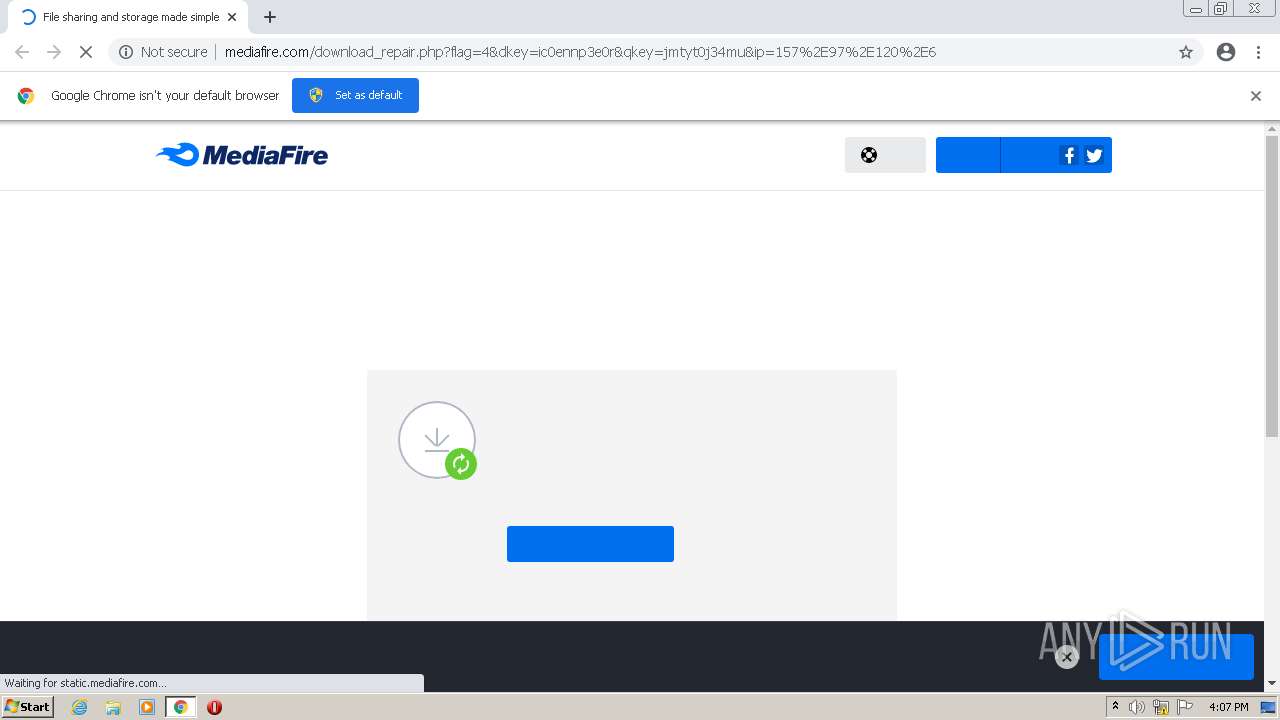
1812 | chrome.exe | GET | 200 | 104.18.183.224:80 | http://static.mediafire.com/css/mfv4_121885.php?ver=nonssl&date=2022-08-12 | US | text | 51.6 Kb | shared |
1812 | chrome.exe | GET | 200 | 104.18.183.224:80 | http://static.mediafire.com/js/master_121885.js | US | text | 149 Kb | shared |
1812 | chrome.exe | GET | 200 | 185.60.216.19:80 | http://connect.facebook.net/en_US/fbevents.js | IE | text | 25.8 Kb | whitelisted |
1812 | chrome.exe | GET | 301 | 142.250.186.78:80 | http://translate.google.com/translate_a/element.js?cb=googleTranslateElementInit | US | — | — | whitelisted |
1812 | chrome.exe | GET | 200 | 104.18.182.224:80 | http://www.mediafire.com/images/icons/myfiles/default.png | US | image | 363 b | shared |
1812 | chrome.exe | GET | 200 | 142.250.186.74:80 | http://ajax.googleapis.com/ajax/libs/jquery/1.7.2/jquery.min.js | US | html | 92.6 Kb | whitelisted |
1812 | chrome.exe | GET | 200 | 104.18.183.224:80 | http://static.mediafire.com/images/backgrounds/header/mf_logo_u1_full_color.svg | US | image | 2.04 Kb | shared |
1812 | chrome.exe | GET | 200 | 104.18.183.224:80 | http://static.mediafire.com/images/icons/svg_light/facebook.svg | US | image | 298 b | shared |
1812 | chrome.exe | GET | 200 | 104.18.182.224:80 | http://www.mediafire.com/blank.html | US | html | 174 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1812 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 199.91.152.81:80 | download1581.mediafire.com | MediaFire, LLC | US | suspicious |
1812 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
1812 | chrome.exe | 172.217.18.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 142.250.185.132:443 | www.google.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 142.250.186.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 142.250.185.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 104.18.182.224:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
1812 | chrome.exe | 104.18.183.224:80 | www.mediafire.com | Cloudflare Inc | US | suspicious |
1812 | chrome.exe | 172.64.156.26:443 | static.cloudflareinsights.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
download1581.mediafire.com |
| suspicious |
clients2.googleusercontent.com |
| whitelisted |
www.mediafire.com |
| shared |
static.mediafire.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
Process | Message |
|---|---|
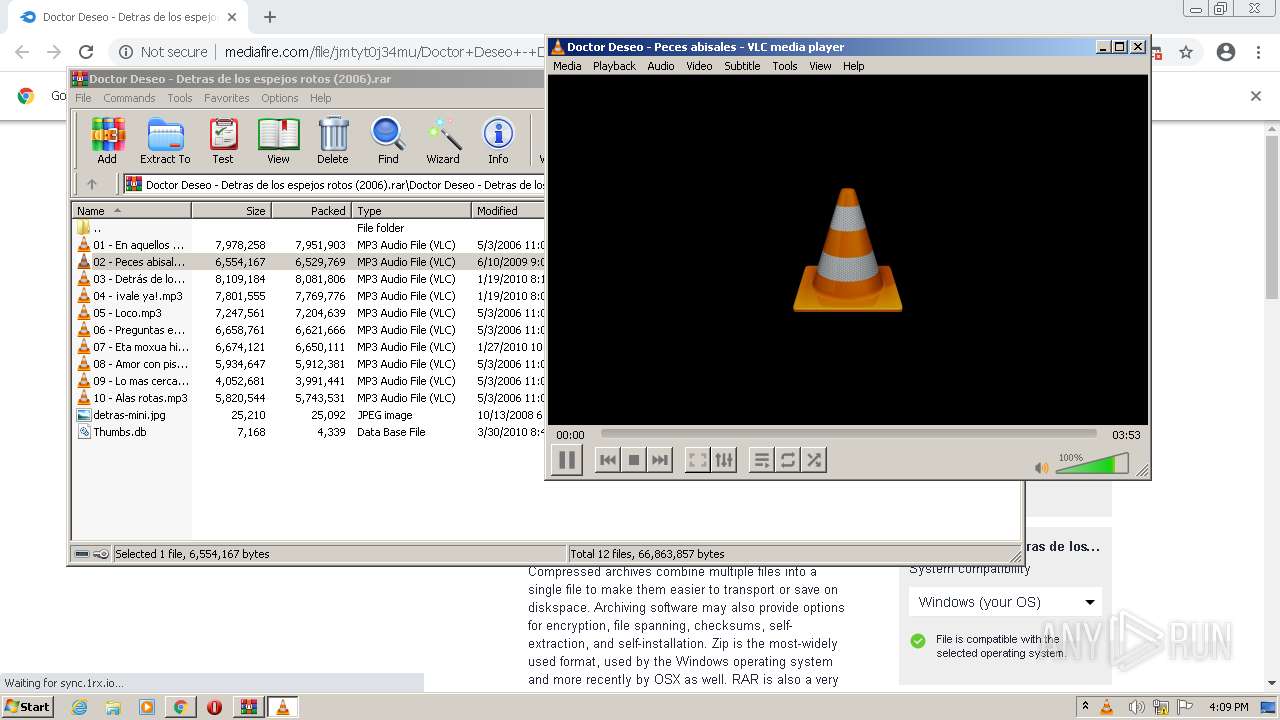
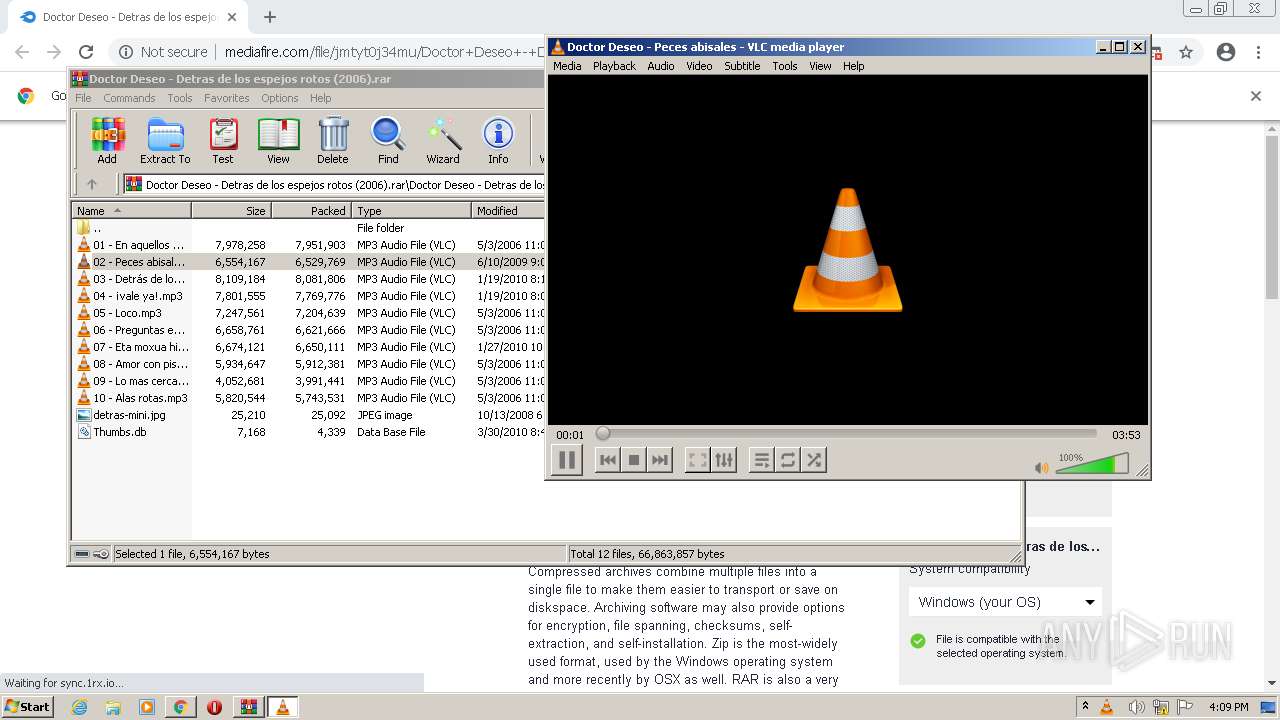
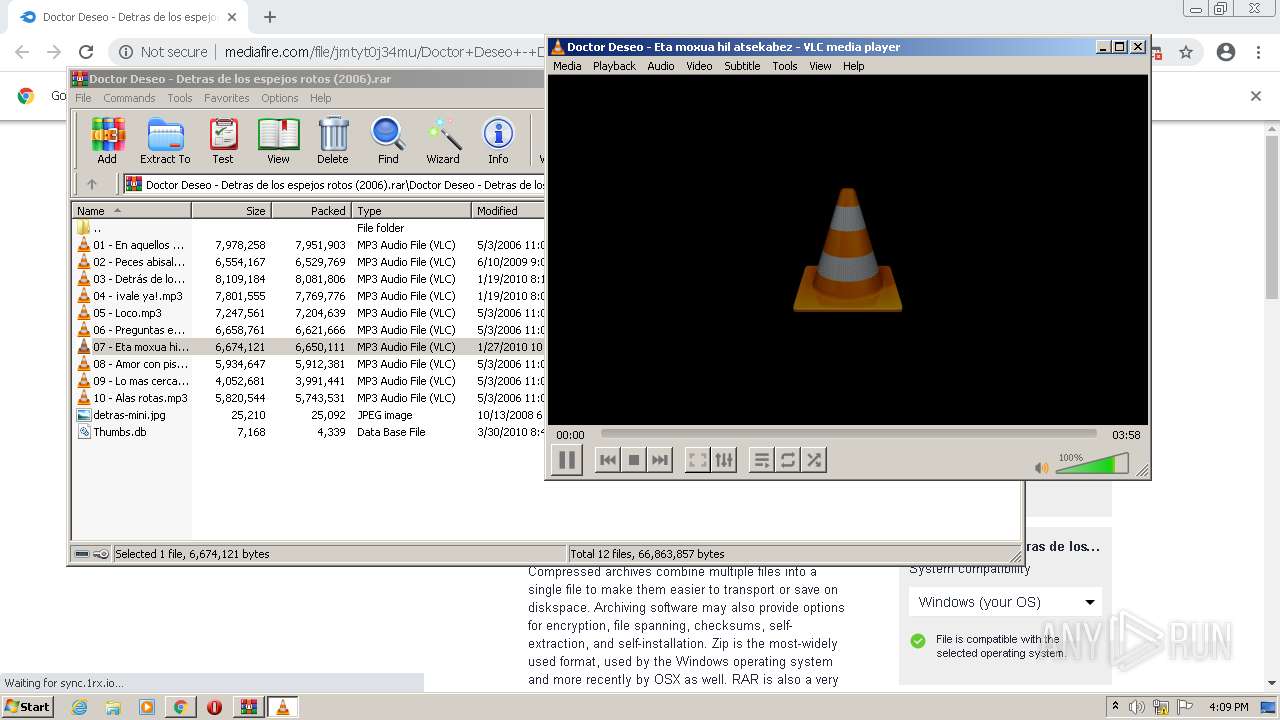
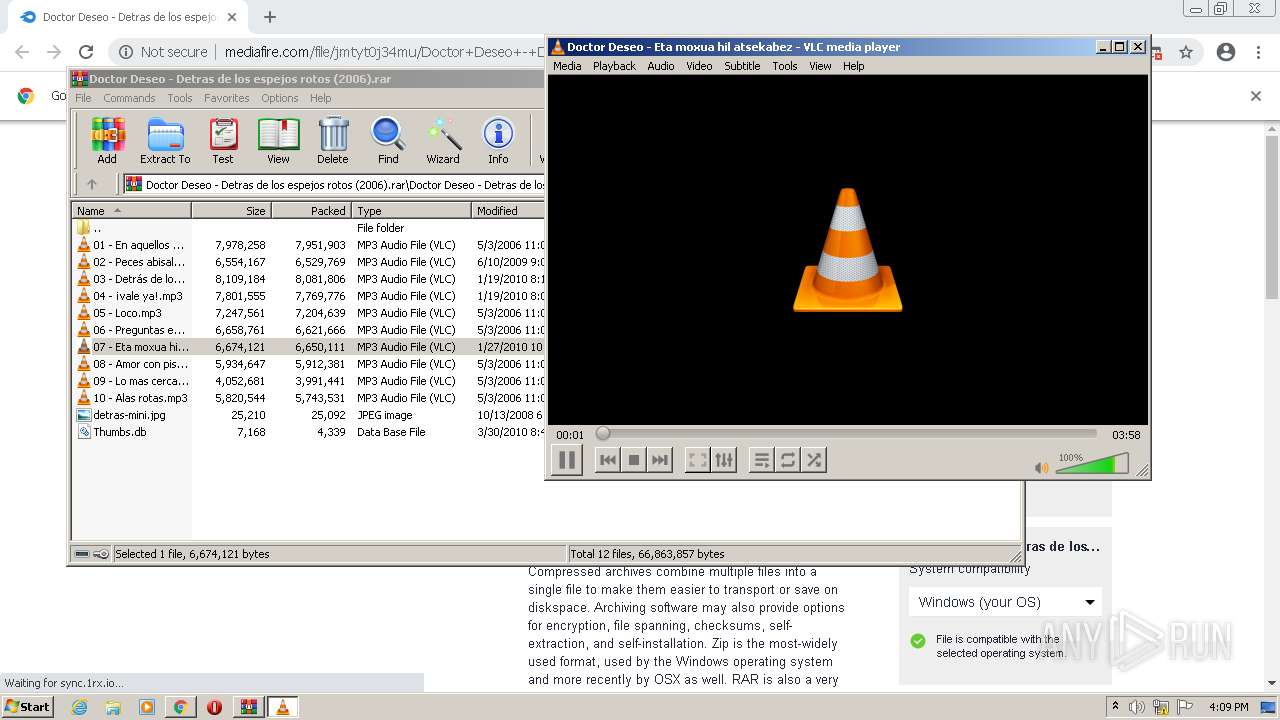
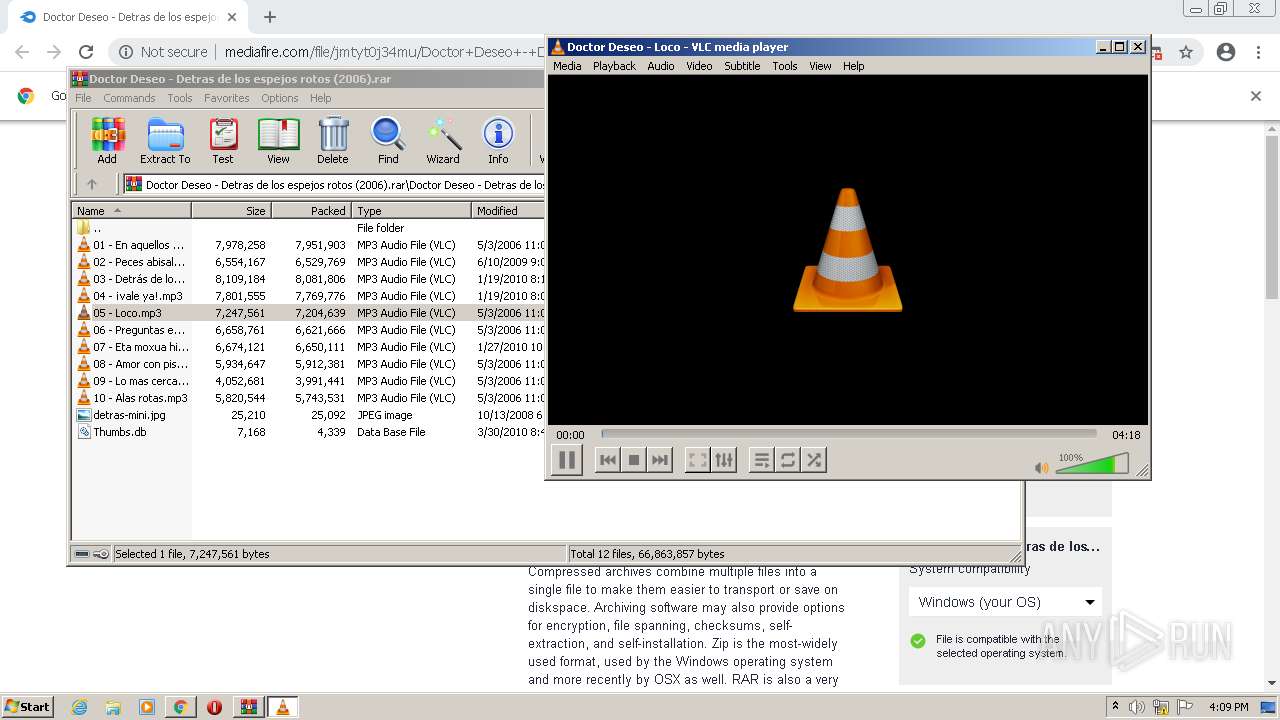
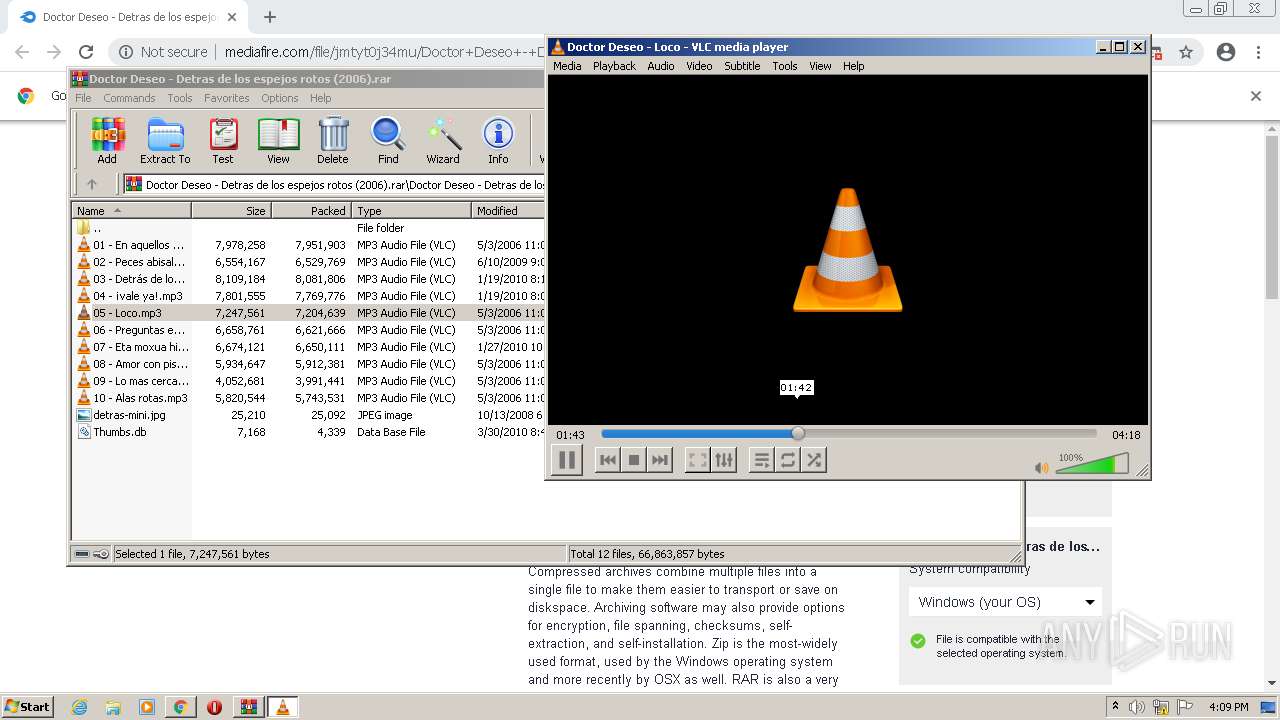
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=i686-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x86/contrib/i686-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc error: stale plugins cache: modified C:\Program Files\VideoLAN\VLC\plugins\access\libaccess_concat_plugin.dll
|