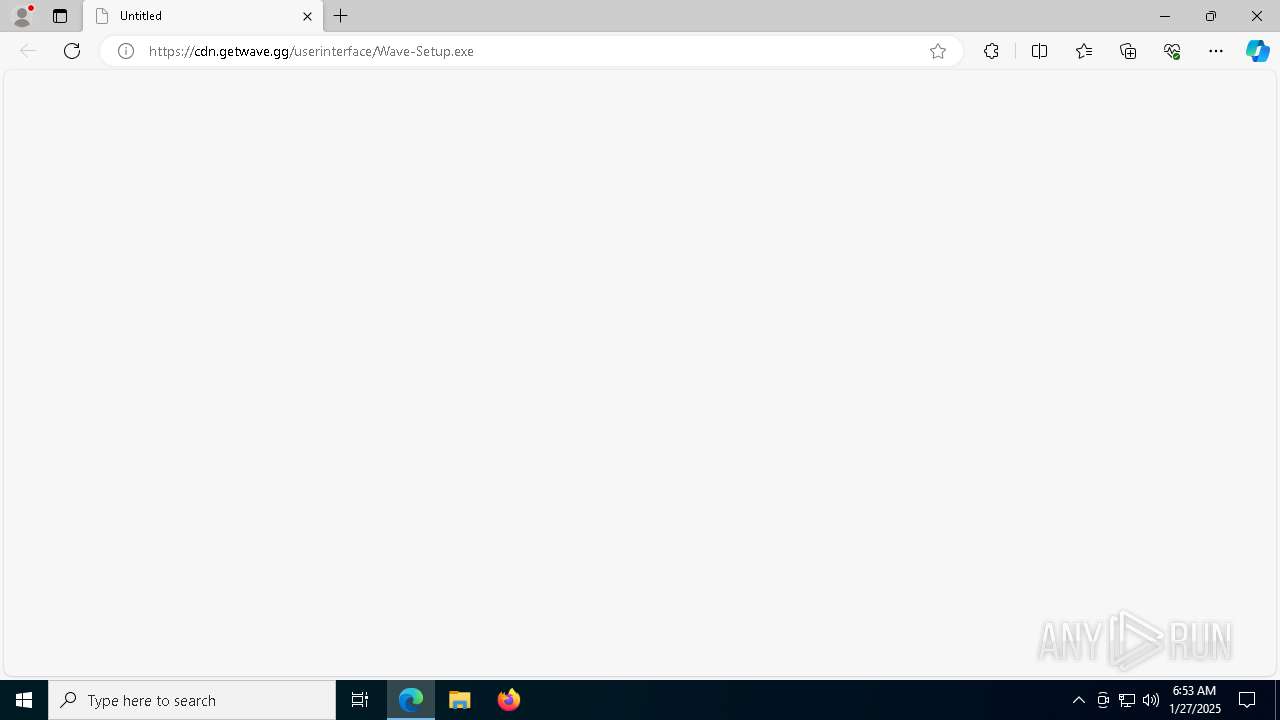
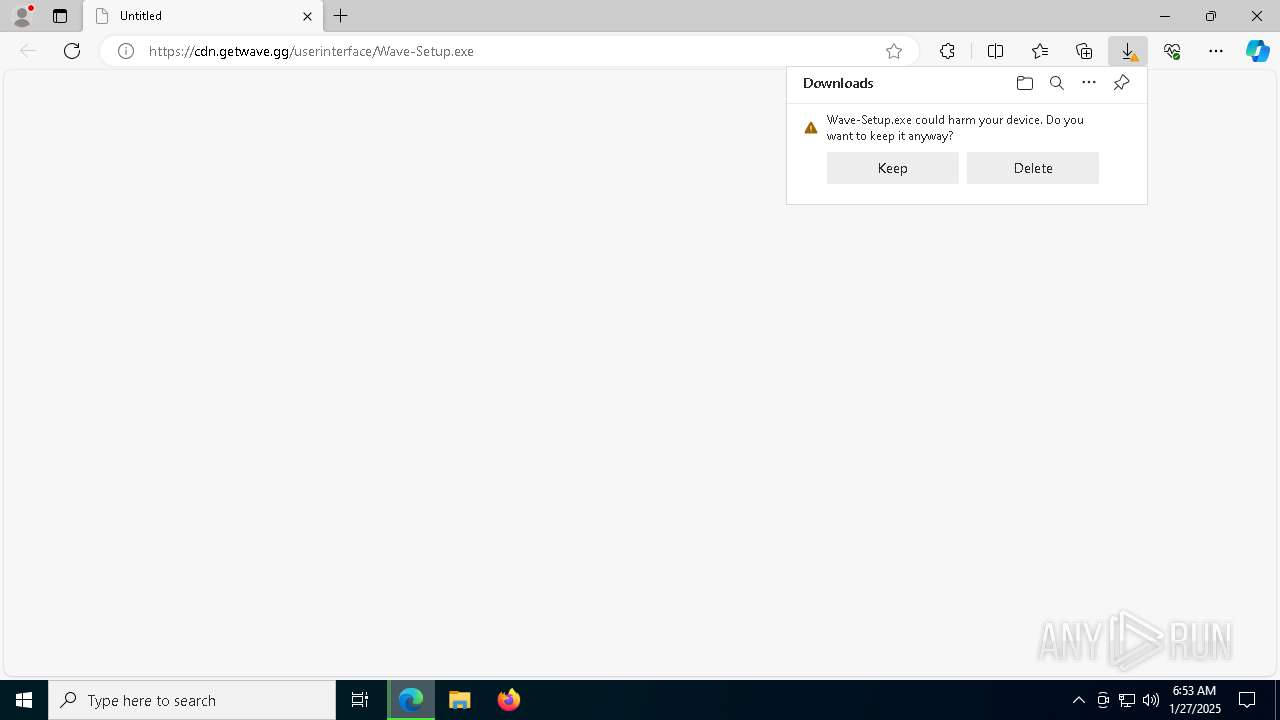
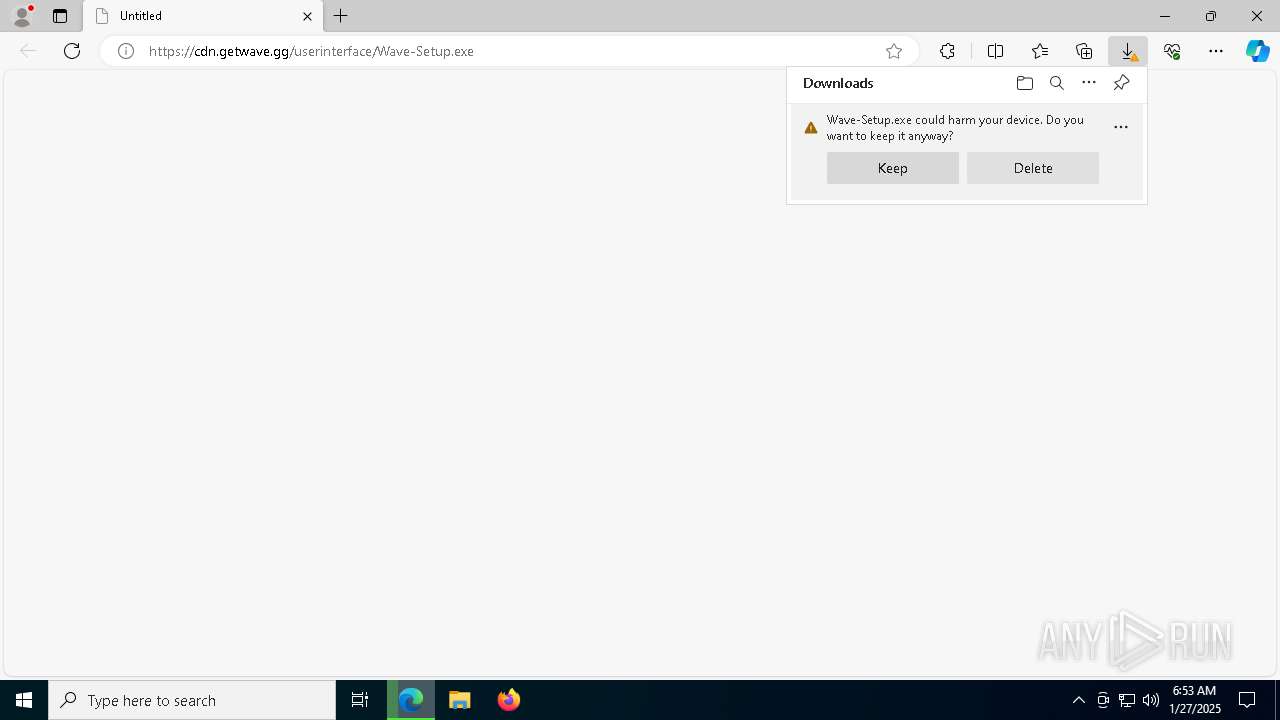
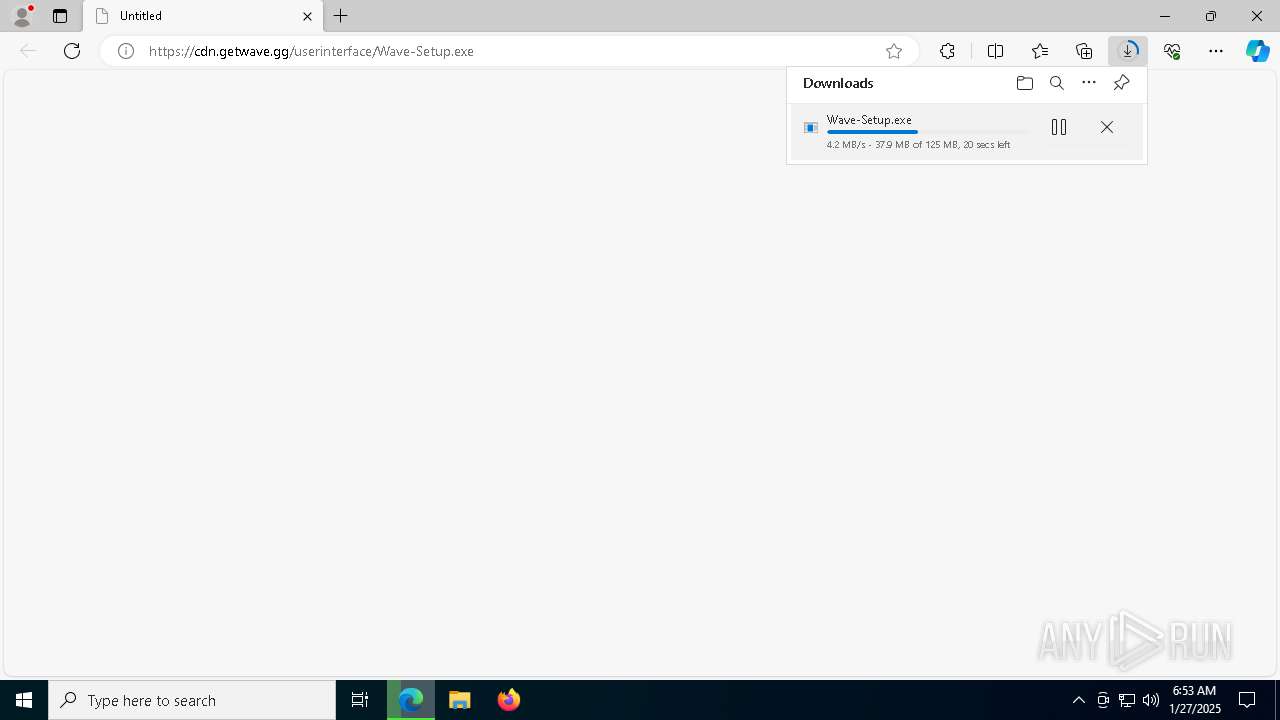
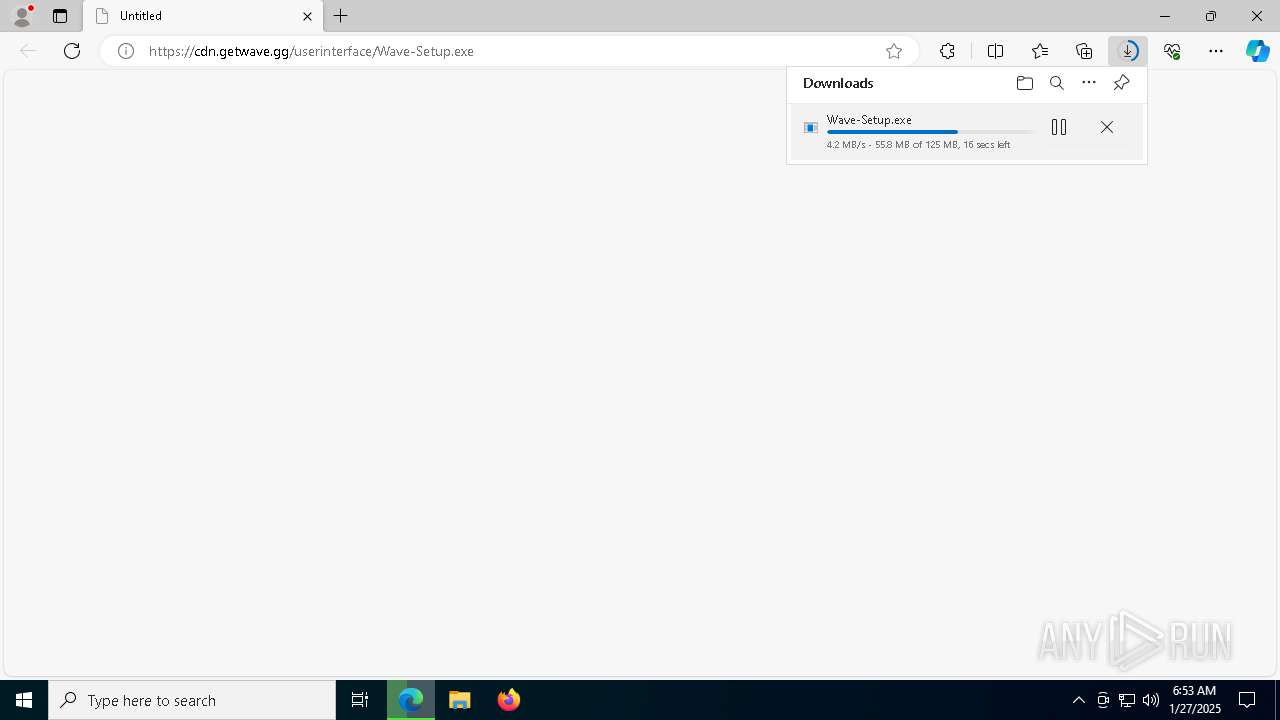
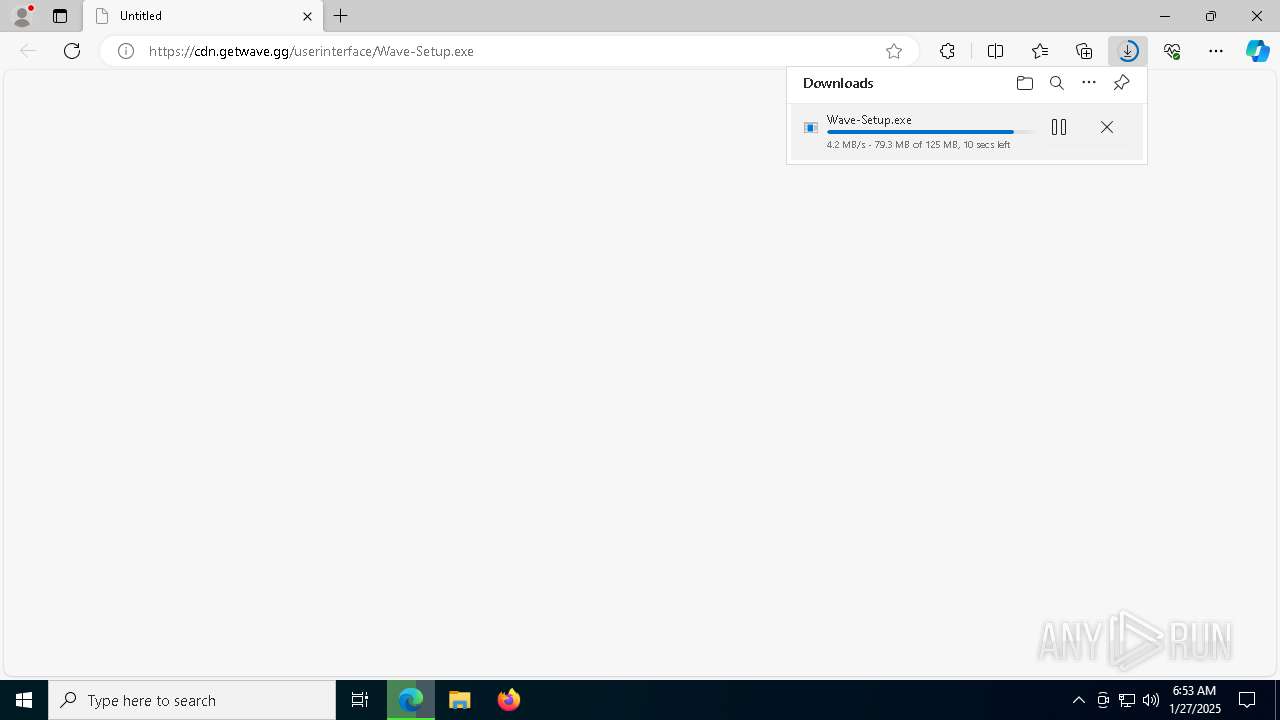
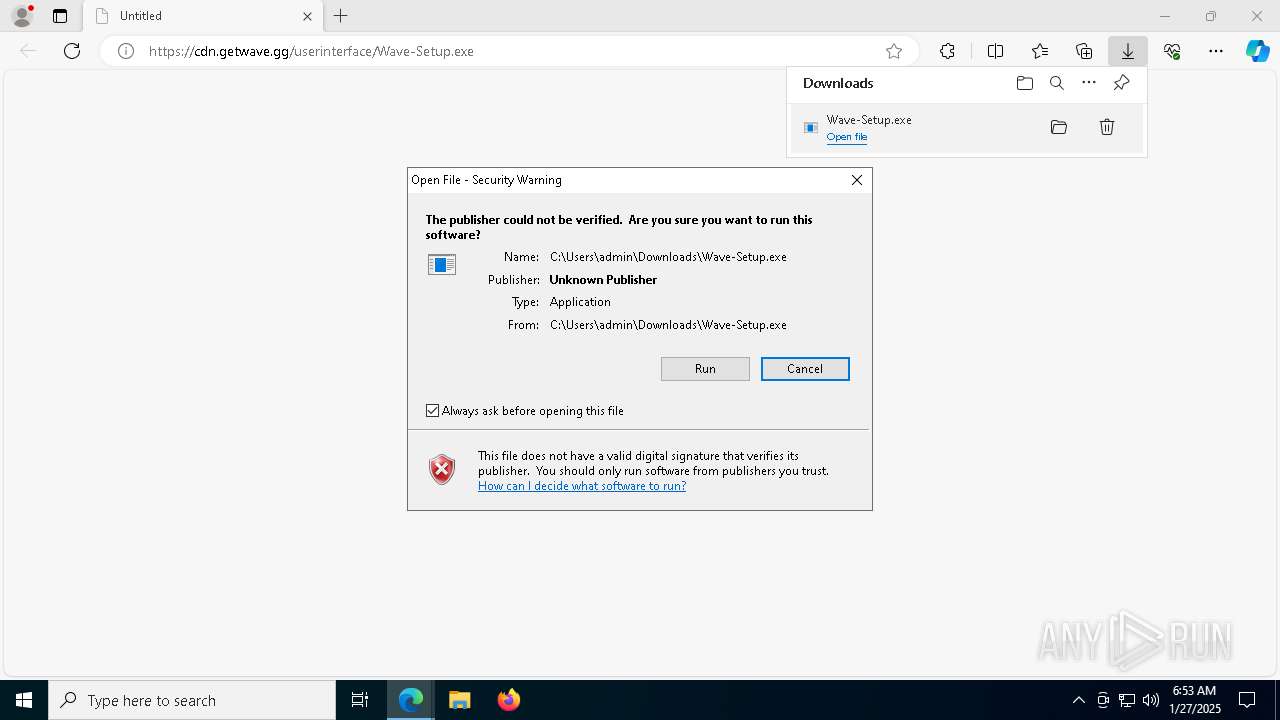
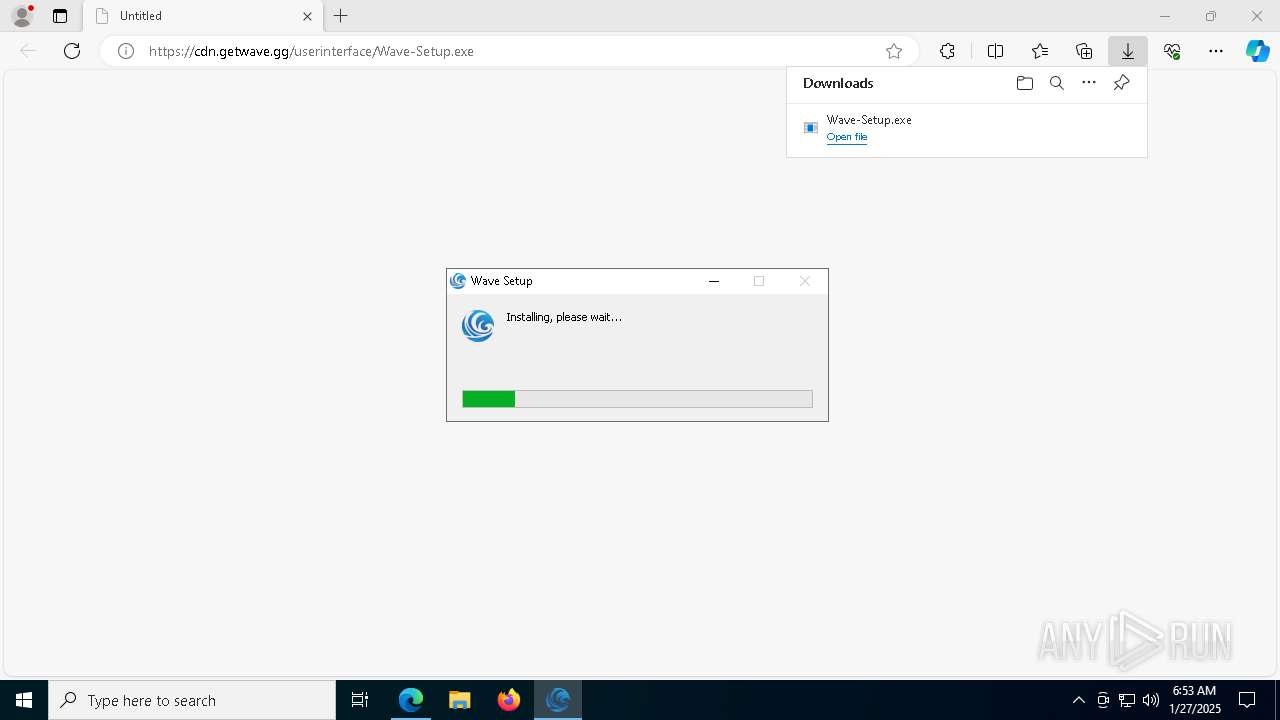
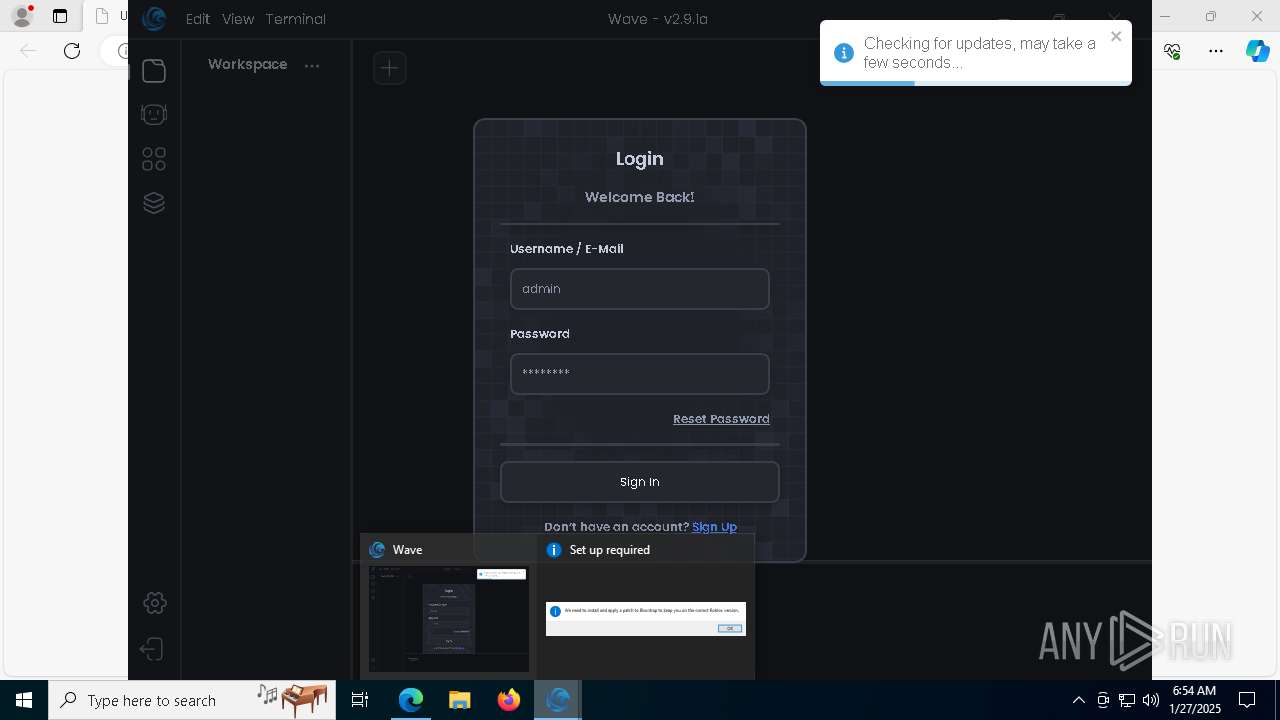
| URL: | https://cdn.getwave.gg/userinterface/Wave-Setup.exe |
| Full analysis: | https://app.any.run/tasks/c028391f-251d-44d0-a4a9-bbd2c234e099 |
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2025, 06:53:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 10CEF61E523BBA823A9DAFB8F5EEA131 |
| SHA1: | F97A25E6D50F0951696A9E3C7563C19055CBC406 |
| SHA256: | EA9D5EF013F58906C6D4F9251AB9C5EAAE62832C3851A785AFF283679F836C0A |
| SSDEEP: | 3:N8cbRSEM2JcvDEpaA:2cbR3MNDEpaA |
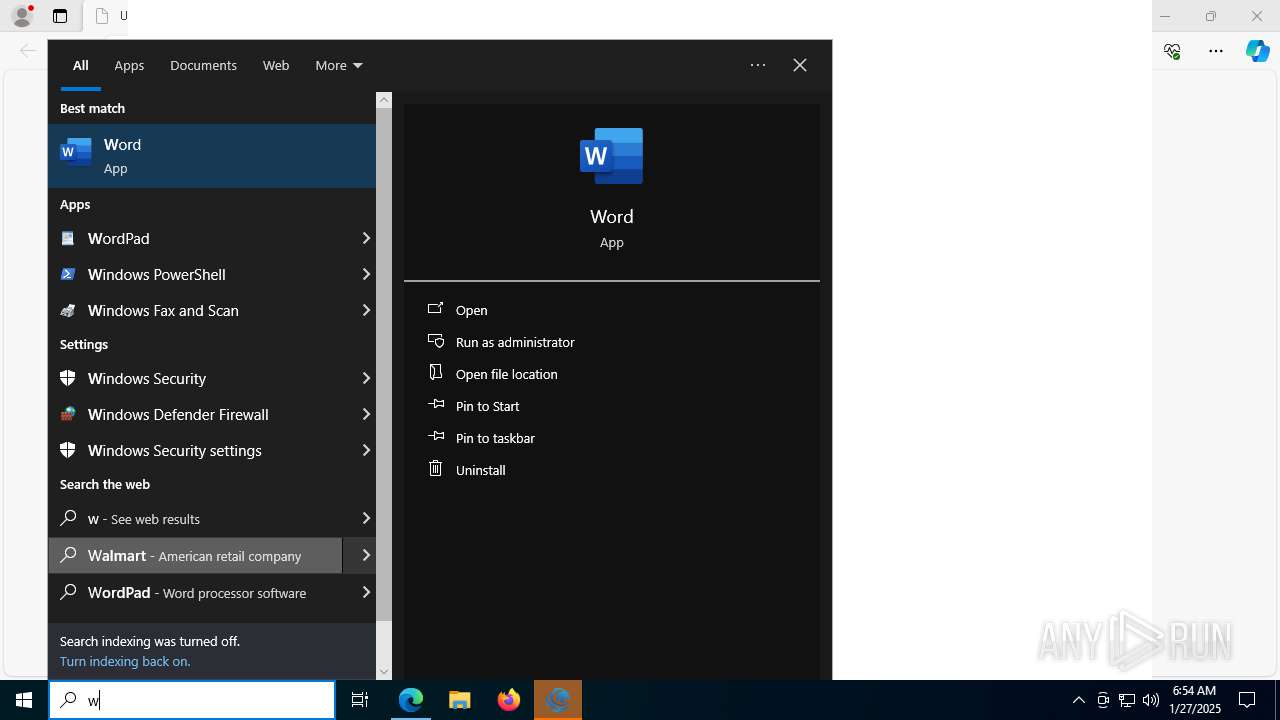
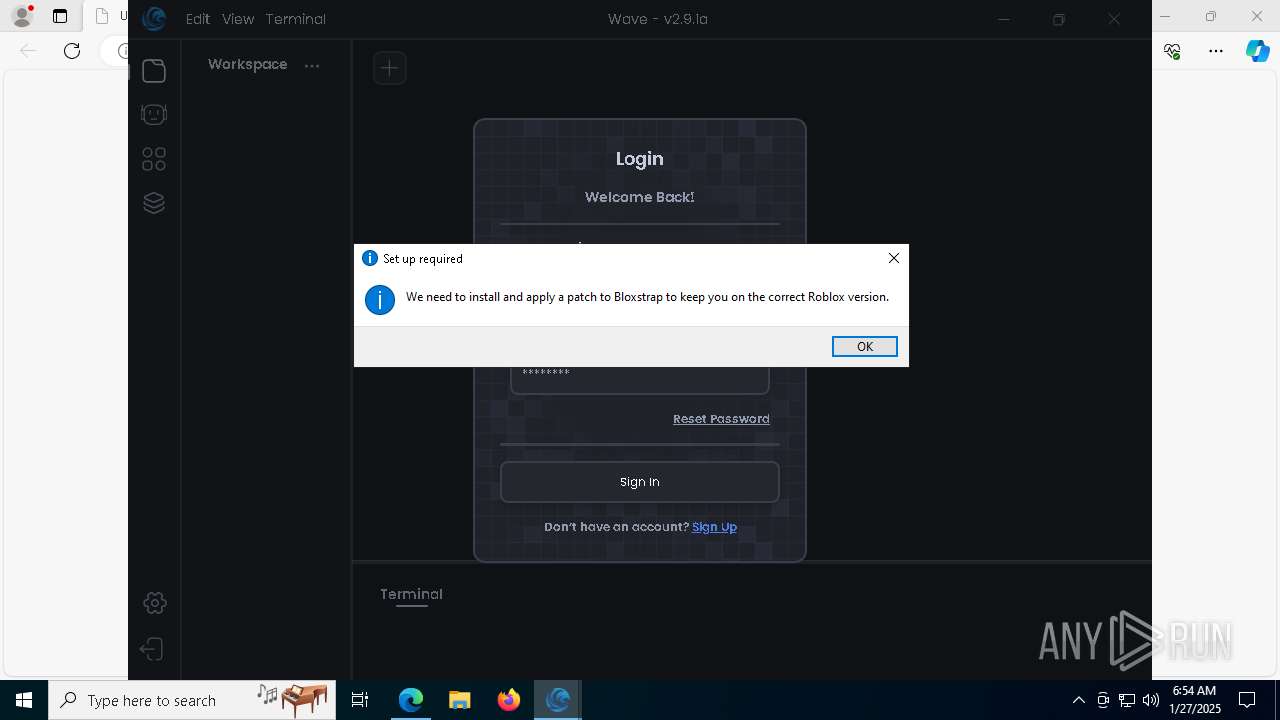
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 4244)
SUSPICIOUS
Executable content was dropped or overwritten
- Wave-Setup.exe (PID: 8036)
- Wave.exe (PID: 8068)
Malware-specific behavior (creating "System.dll" in Temp)
- Wave-Setup.exe (PID: 8036)
The process creates files with name similar to system file names
- Wave-Setup.exe (PID: 8036)
Starts CMD.EXE for commands execution
- Wave-Setup.exe (PID: 8036)
- Wave.exe (PID: 7740)
- powershell.exe (PID: 4244)
- Wave.exe (PID: 8068)
Get information on the list of running processes
- Wave-Setup.exe (PID: 8036)
- cmd.exe (PID: 7952)
Creates a software uninstall entry
- Wave-Setup.exe (PID: 8036)
Application launched itself
- Wave.exe (PID: 7740)
- Wave.exe (PID: 8068)
Executing commands from a ".bat" file
- Wave.exe (PID: 7740)
- powershell.exe (PID: 4244)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1616)
Starts process via Powershell
- powershell.exe (PID: 4244)
The executable file from the user directory is run by the CMD process
- Wave.exe (PID: 8068)
Starts application with an unusual extension
- cmd.exe (PID: 8064)
Detected use of alternative data streams (AltDS)
- wave-luau.exe (PID: 4536)
The process deletes folder without confirmation
- Wave.exe (PID: 7740)
Drops 7-zip archiver for unpacking
- Wave-Setup.exe (PID: 8036)
Reads security settings of Internet Explorer
- Wave-Setup.exe (PID: 8036)
Process drops legitimate windows executable
- Wave-Setup.exe (PID: 8036)
INFO
Checks supported languages
- identity_helper.exe (PID: 7716)
- Wave-Setup.exe (PID: 8036)
- Wave.exe (PID: 7740)
- Wave.exe (PID: 3524)
- Wave.exe (PID: 6084)
- Wave.exe (PID: 7028)
- Wave.exe (PID: 8068)
- Wave.exe (PID: 8000)
- wave-luau.exe (PID: 4536)
- Wave.exe (PID: 7032)
Reads the computer name
- identity_helper.exe (PID: 7716)
- Wave-Setup.exe (PID: 8036)
- Wave.exe (PID: 7740)
- Wave.exe (PID: 3524)
- Wave.exe (PID: 7032)
- Wave.exe (PID: 8068)
- Bloxstrap.exe (PID: 1448)
- Wave.exe (PID: 7028)
Reads Environment values
- identity_helper.exe (PID: 7716)
- Wave.exe (PID: 8068)
Creates files in the program directory
- Wave-Setup.exe (PID: 8036)
Executable content was dropped or overwritten
- msedge.exe (PID: 6288)
- msedge.exe (PID: 7812)
Create files in a temporary directory
- Wave-Setup.exe (PID: 8036)
- Wave.exe (PID: 7740)
- Wave.exe (PID: 8068)
The sample compiled with english language support
- Wave-Setup.exe (PID: 8036)
- msedge.exe (PID: 7812)
Application launched itself
- msedge.exe (PID: 6288)
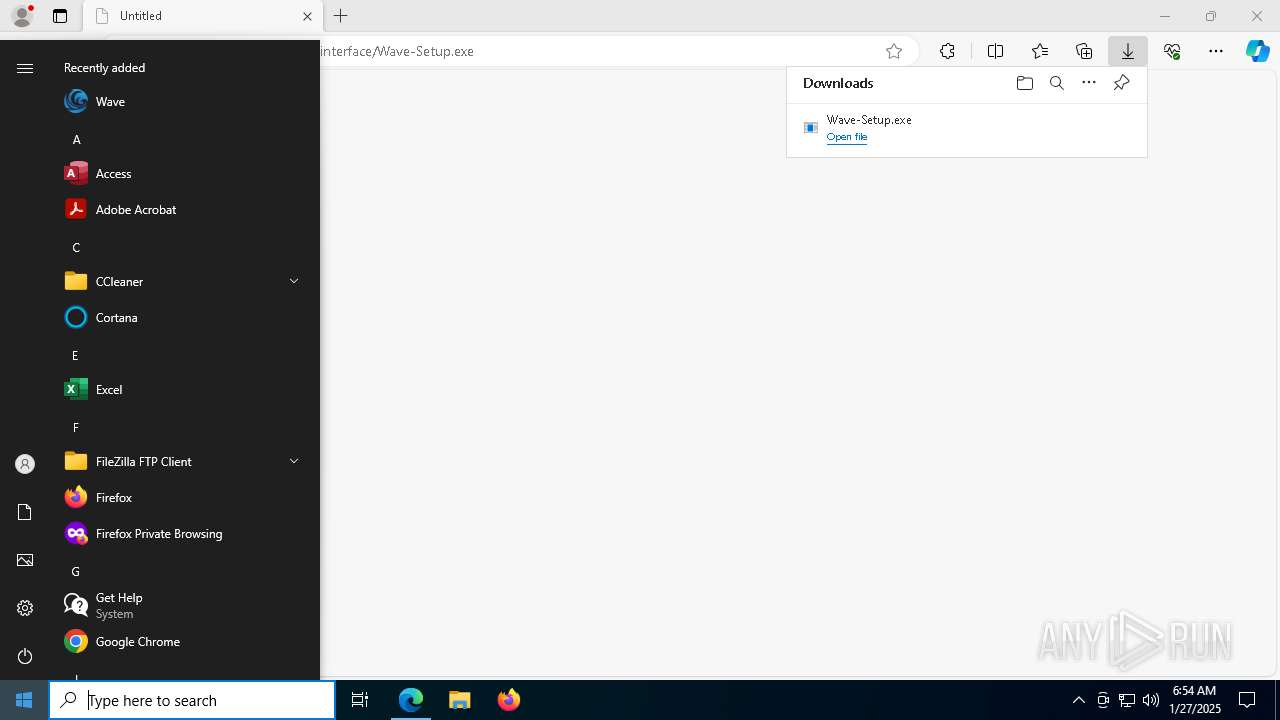
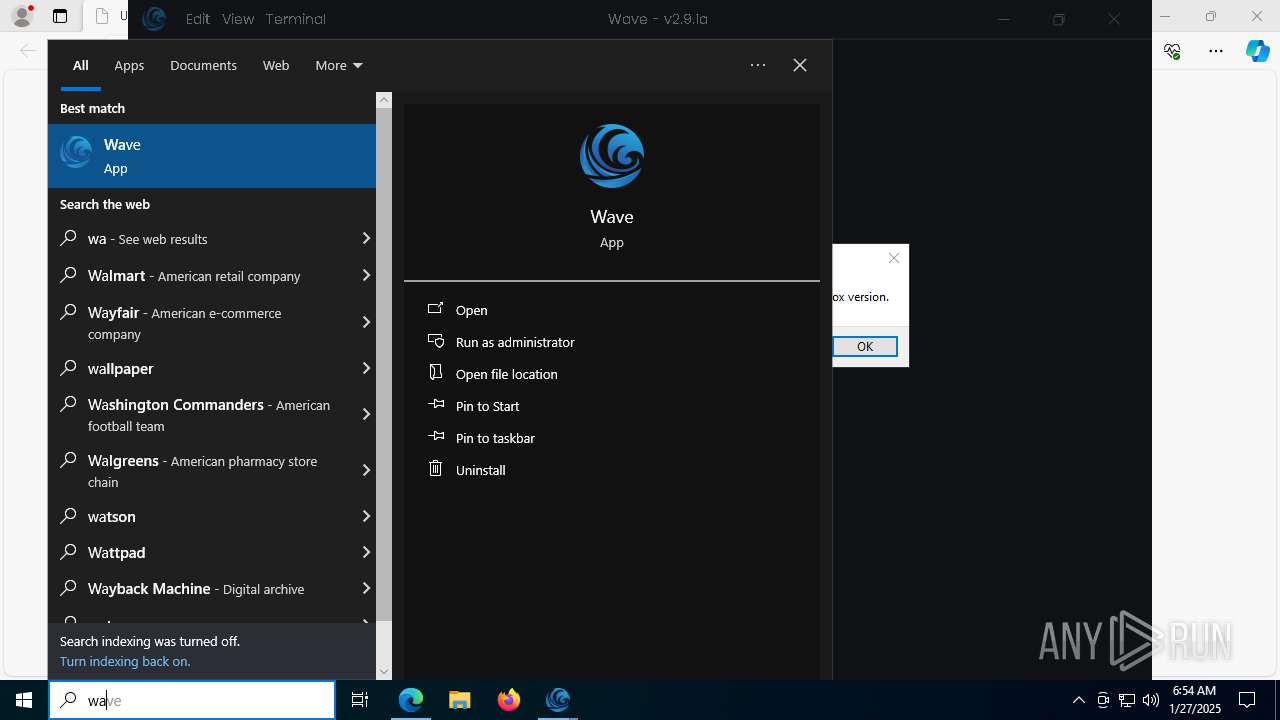
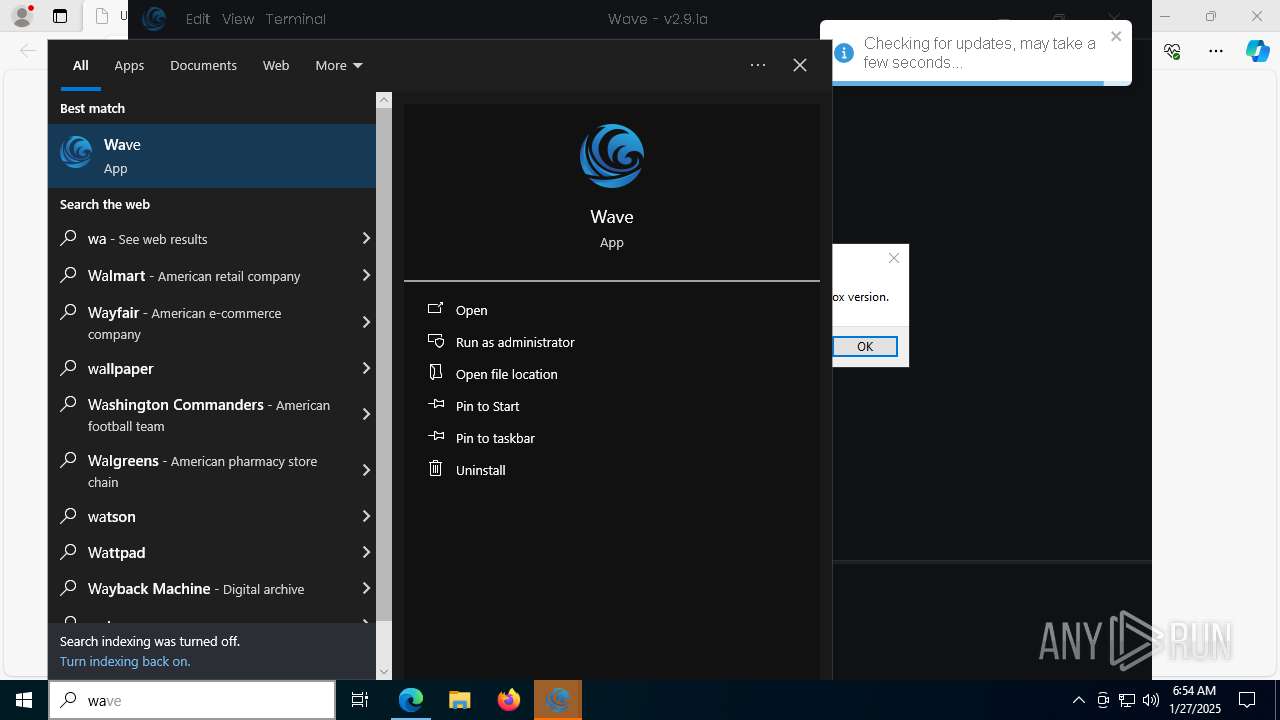
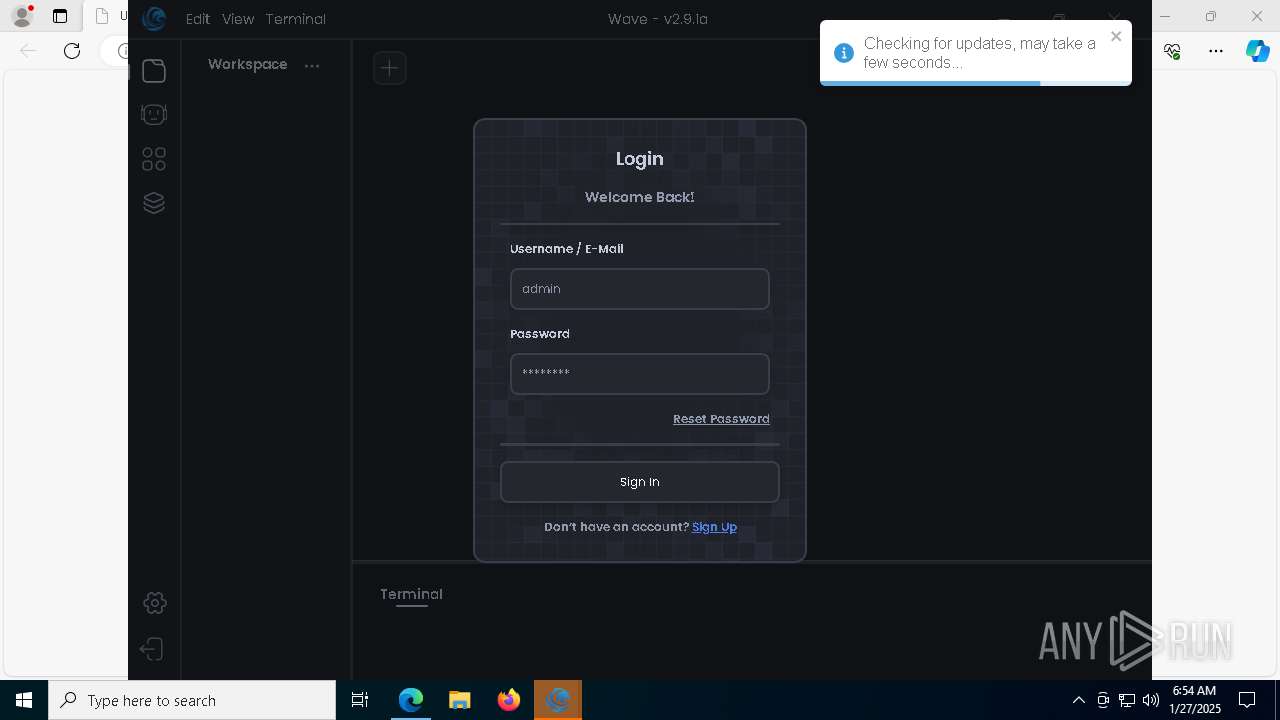
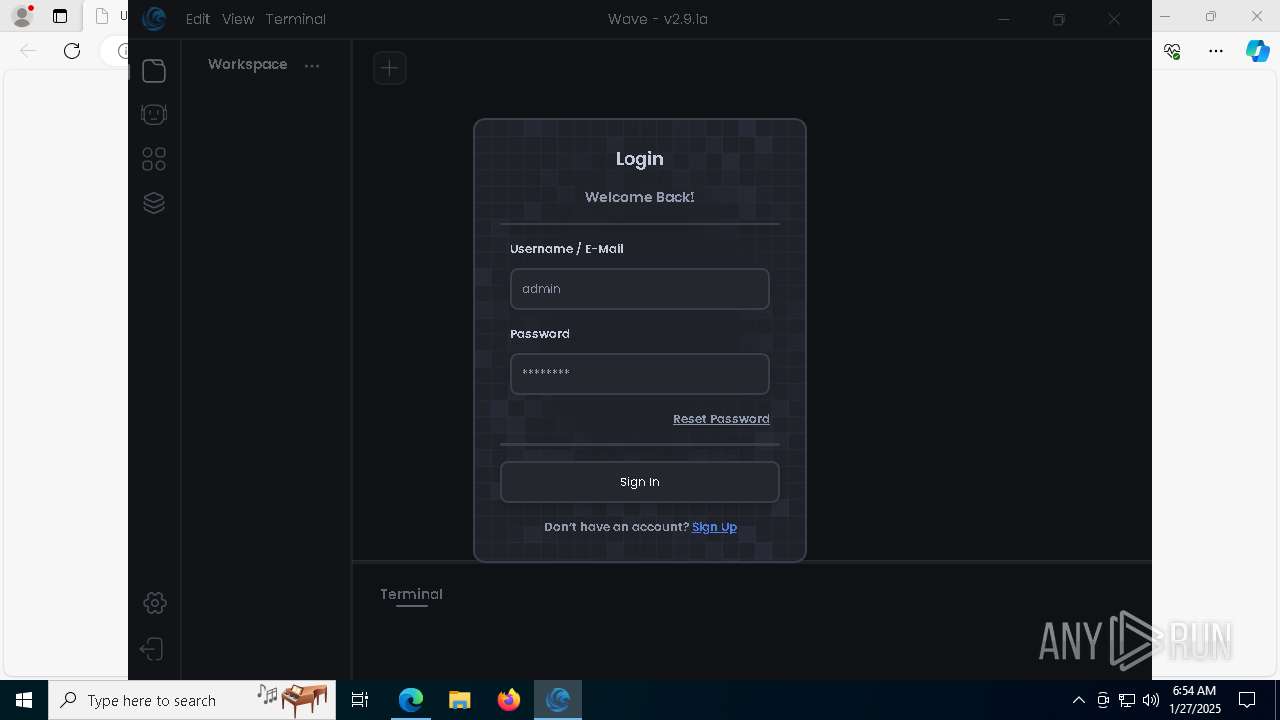
Manual execution by a user
- Wave.exe (PID: 7740)
Drops encrypted JS script (Microsoft Script Encoder)
- Wave.exe (PID: 7740)
- Wave.exe (PID: 8068)
Reads the machine GUID from the registry
- Wave.exe (PID: 7740)
- Wave.exe (PID: 8068)
Checks proxy server information
- Wave.exe (PID: 7740)
- Wave.exe (PID: 8068)
Changes the display of characters in the console
- cmd.exe (PID: 8064)
Reads product name
- Wave.exe (PID: 8068)
Process checks computer location settings
- Wave.exe (PID: 8068)
- Wave.exe (PID: 8000)
Creates files or folders in the user directory
- Wave.exe (PID: 7032)
- Wave.exe (PID: 8068)
- Wave.exe (PID: 7740)
- Wave-Setup.exe (PID: 8036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
71
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | fsutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=5340 --field-trial-handle=2368,i,2129648559514682192,17031473698149205368,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1380 | "C:\WINDOWS\system32\find.exe" "Wave.exe" | C:\Windows\SysWOW64\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
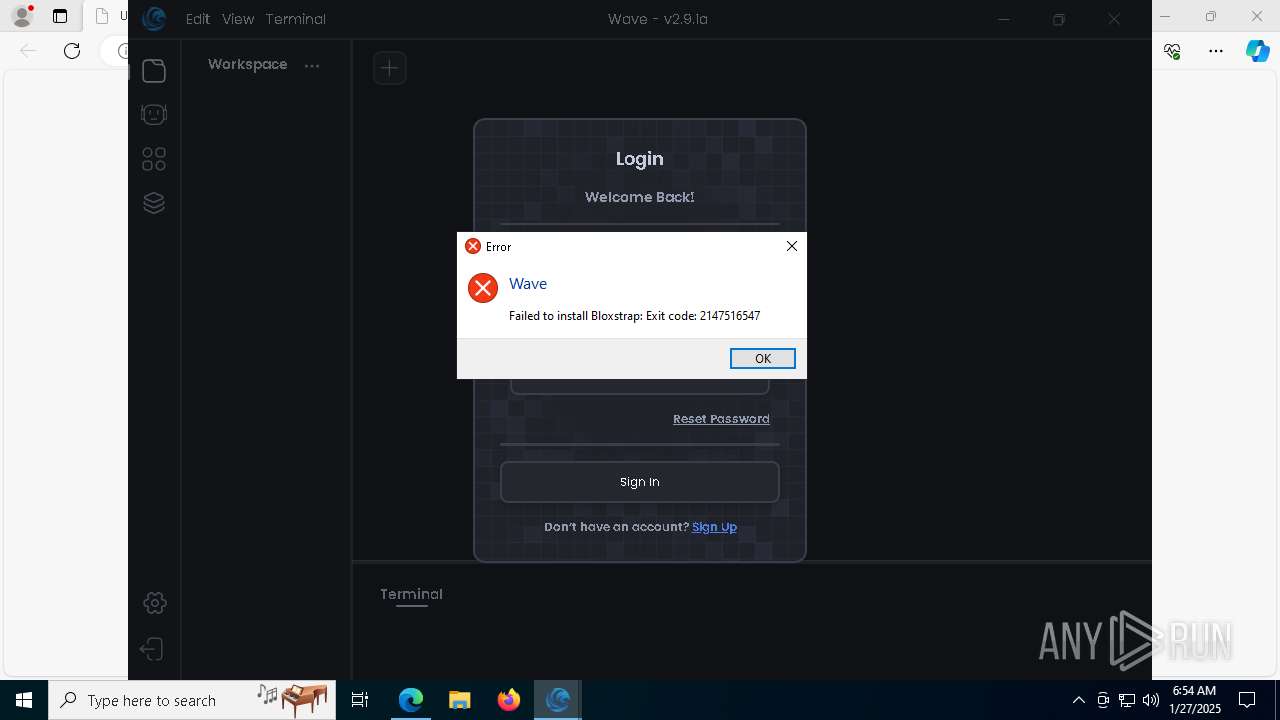
| 1448 | C:\Users\admin\AppData\Local\Programs\Wave\bin\Bloxstrap.exe | C:\Users\admin\AppData\Local\Programs\Wave\bin\Bloxstrap.exe | Wave.exe | ||||||||||||
User: admin Company: Bloxstrap Integrity Level: HIGH Description: Bloxstrap Exit code: 2147516547 Version: 4.2.1 Modules
| |||||||||||||||
| 1488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell.exe Start-Process -FilePath "'C:\Users\admin\AppData\Local\Temp\8e0ef7551ca4559d925a522bf4b5eb7c\execute.bat'" -WindowStyle hidden -Verb runAs" | C:\Windows\System32\cmd.exe | — | Wave.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1472 --field-trial-handle=2368,i,2129648559514682192,17031473698149205368,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --mojo-platform-channel-handle=7452 --field-trial-handle=2368,i,2129648559514682192,17031473698149205368,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3524 | "C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\Wave" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAEAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --field-trial-handle=1824,i,12173470554951942460,15961783672025283678,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=1804 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe | — | Wave.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: Wave Exit code: 0 Version: 0.4.0 Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cdn.getwave.gg/userinterface/Wave-Setup.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 017
Read events
14 955
Write events
44
Delete events
18
Modification events
| (PID) Process: | (3612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
41
Suspicious files
580
Text files
100
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135883.TMP | — | |
MD5:— | SHA256:— | |||
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135883.TMP | — | |
MD5:— | SHA256:— | |||
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135893.TMP | — | |
MD5:— | SHA256:— | |||
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135893.TMP | — | |
MD5:— | SHA256:— | |||
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1358a3.TMP | — | |
MD5:— | SHA256:— | |||
| 6288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
78
DNS requests
71
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6368 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2092 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738145189&P2=404&P3=2&P4=K6AQWun8zOiCXZP0XYvBp%2b6pINb1z1%2bpzSEmAclVCAvbzVhfMrFKqnT8btEMvR6h58CNXUgh9GV7B1cqgNHzow%3d%3d | unknown | — | — | whitelisted |
7668 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7668 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738145189&P2=404&P3=2&P4=K6AQWun8zOiCXZP0XYvBp%2b6pINb1z1%2bpzSEmAclVCAvbzVhfMrFKqnT8btEMvR6h58CNXUgh9GV7B1cqgNHzow%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2548 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6288 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6656 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
cdn.getwave.gg |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
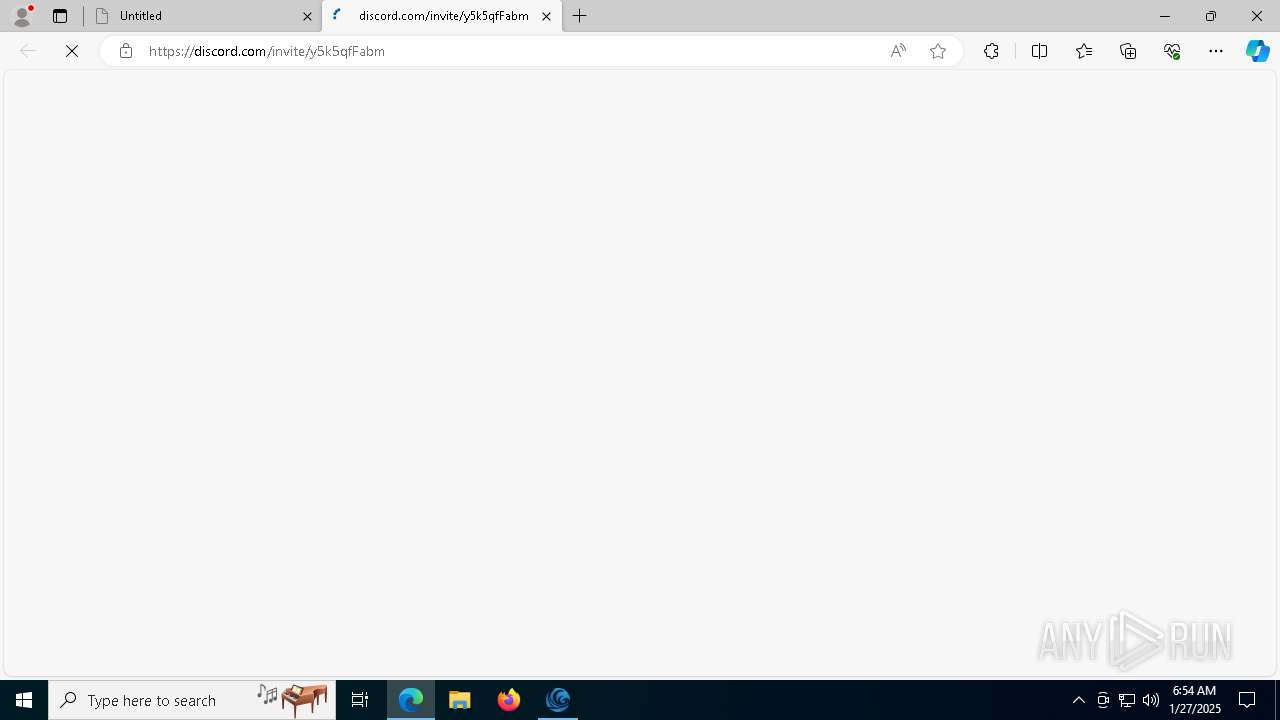
Threats
PID | Process | Class | Message |
|---|---|---|---|
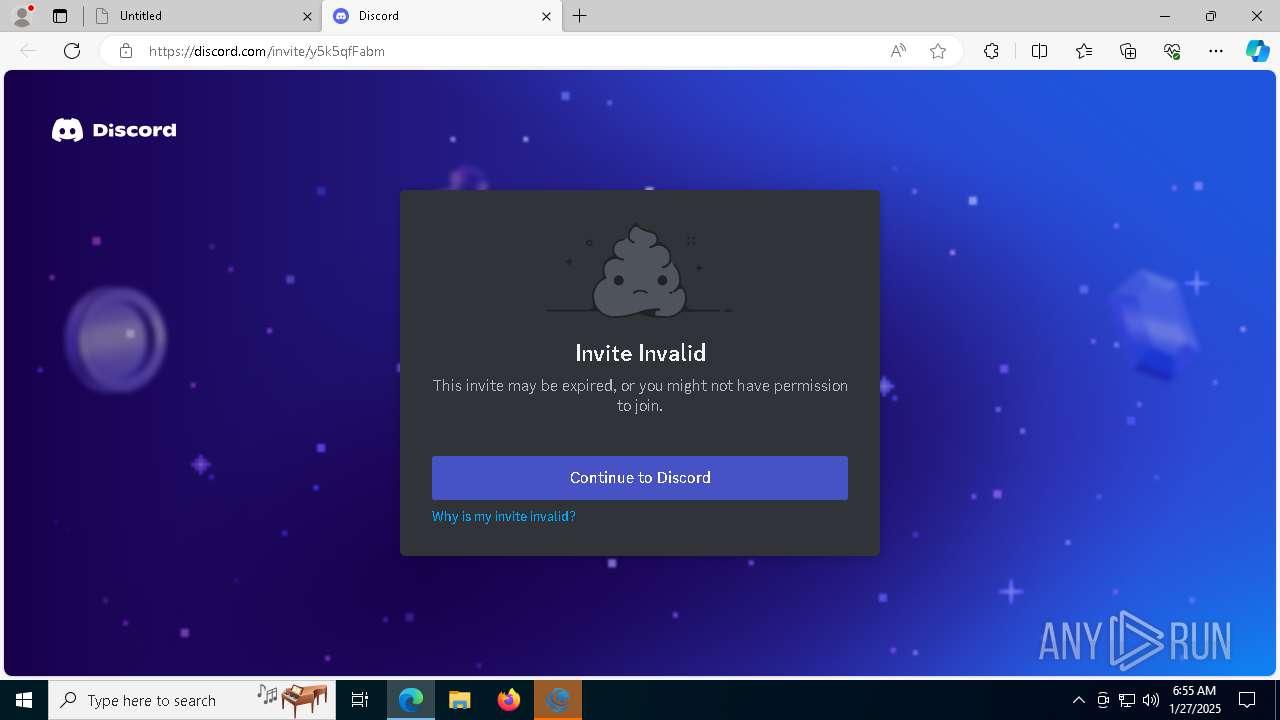
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6656 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
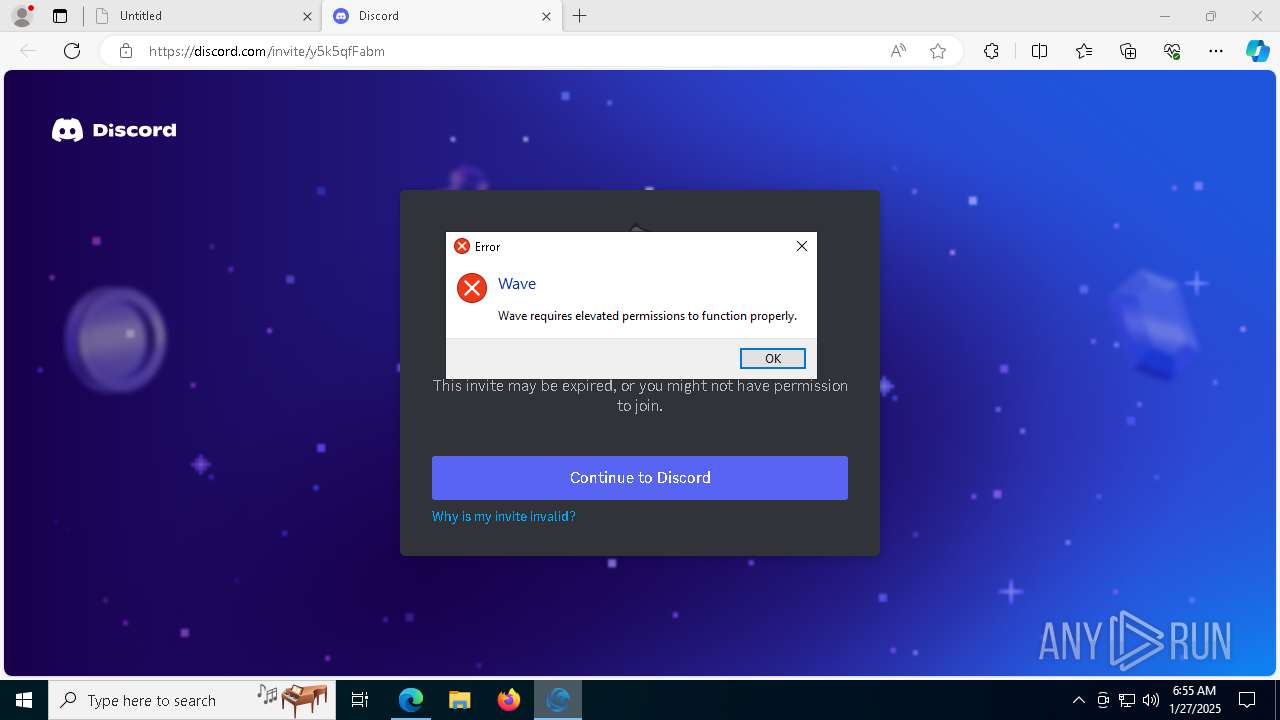
Process | Message |
|---|---|
Bloxstrap.exe | You must install .NET to run this application.
App: C:\Users\admin\AppData\Local\Programs\Wave\bin\Bloxstrap.exe
Architecture: x64
App host version: 6.0.35
.NET location: Not found
Learn about runtime installation:
https://aka.ms/dotnet/app-launch-failed
Download the .NET runtime:
https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win10-x64&apphost_version=6.0.35 |