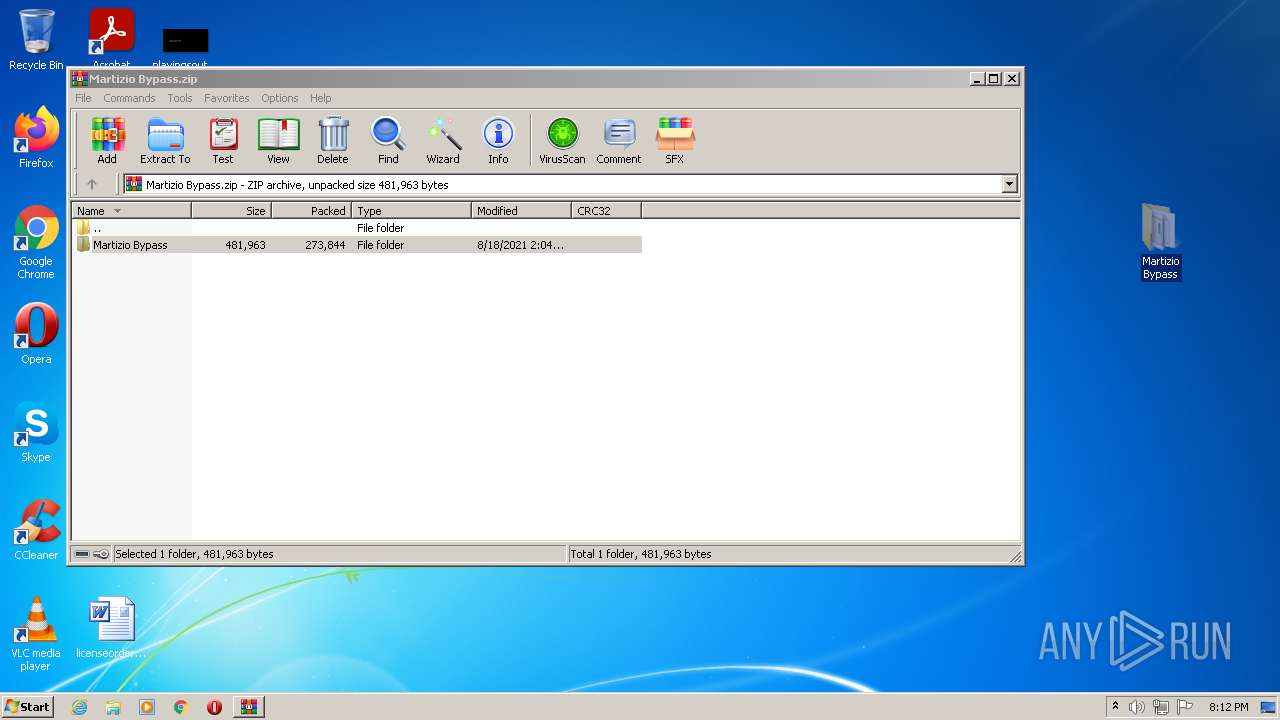
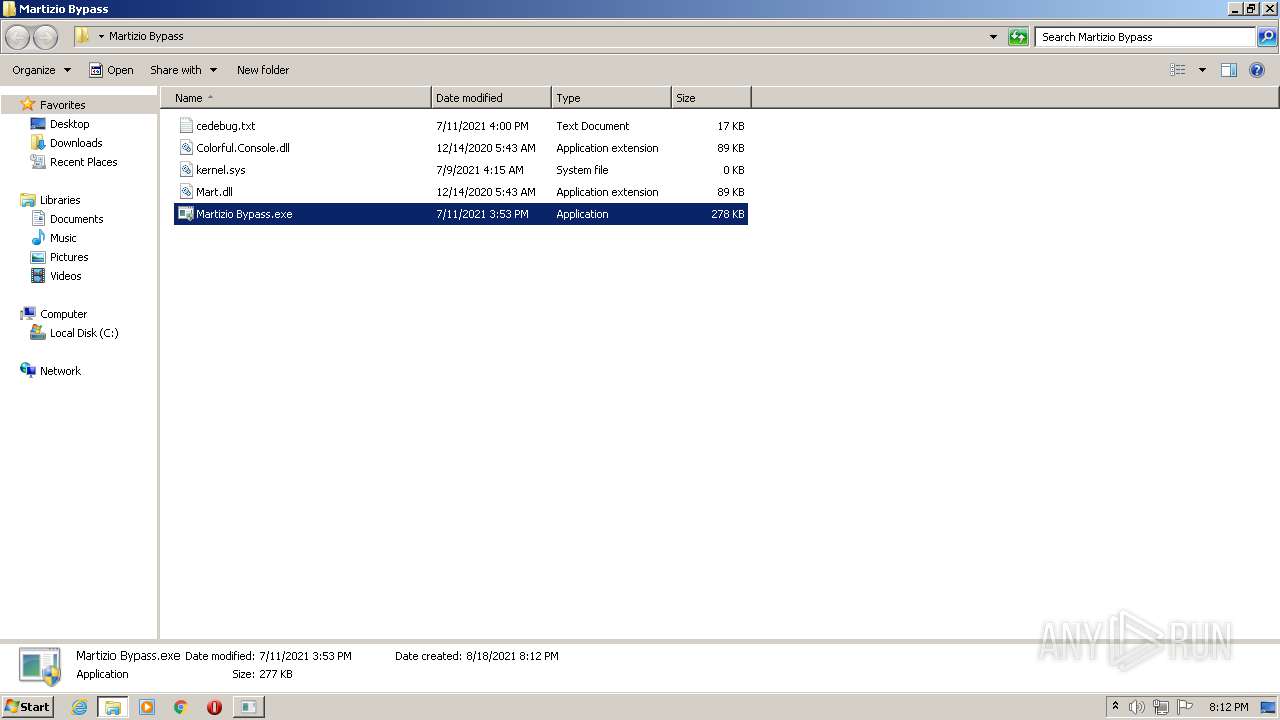
| File name: | Martizio Bypass.zip |
| Full analysis: | https://app.any.run/tasks/e3d811a4-9329-4b7f-9f20-7627faa46c4a |
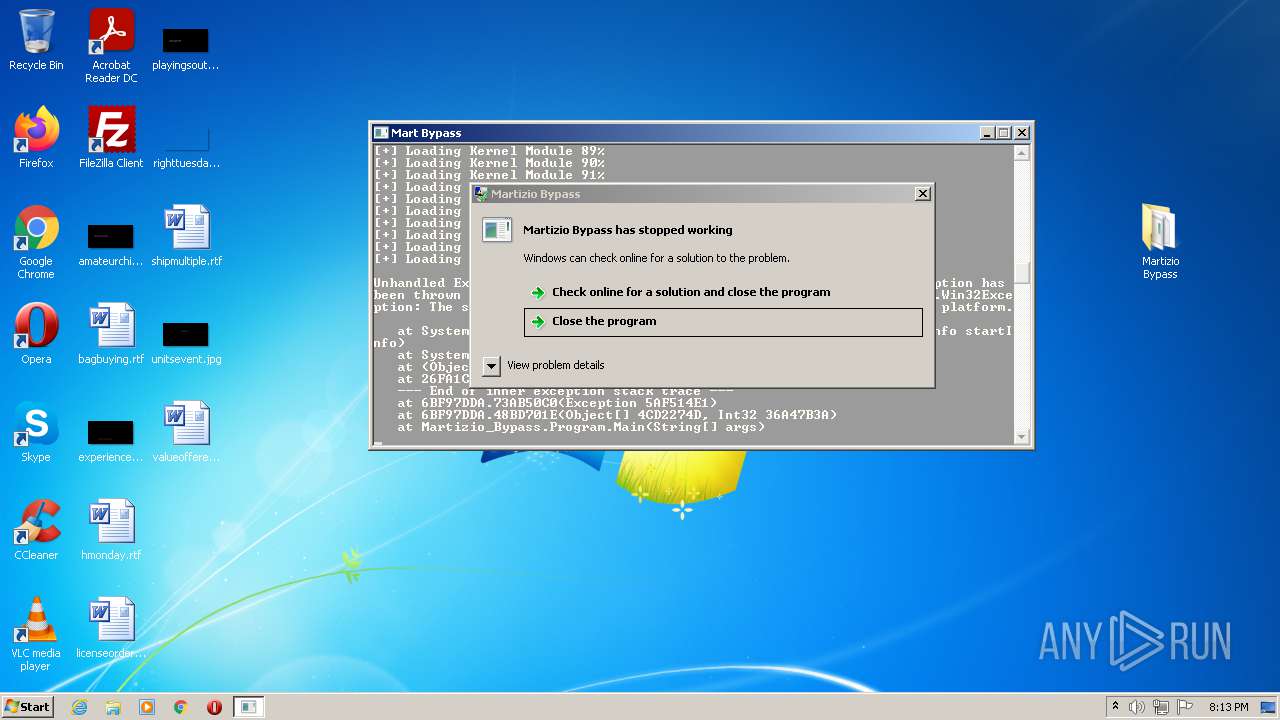
| Verdict: | Malicious activity |
| Analysis date: | August 18, 2021, 19:11:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 25705BA5146466AED21C646431E73BEC |
| SHA1: | 16FFFF16D46B3A08FE6B3AD6B693E4F0BCF676F7 |
| SHA256: | EA9224E5FE555EF323EA34D2F1378F011DF3194F3D6875F979AF16C993FE9ACE |
| SSDEEP: | 6144:j6/W3vdhTyH4f6r/UXlrzIEpK2XOuNWkqb8qZ/4BeVtCJNl:j6WvTO4fOKrzlpK2eVJ8qZBO |
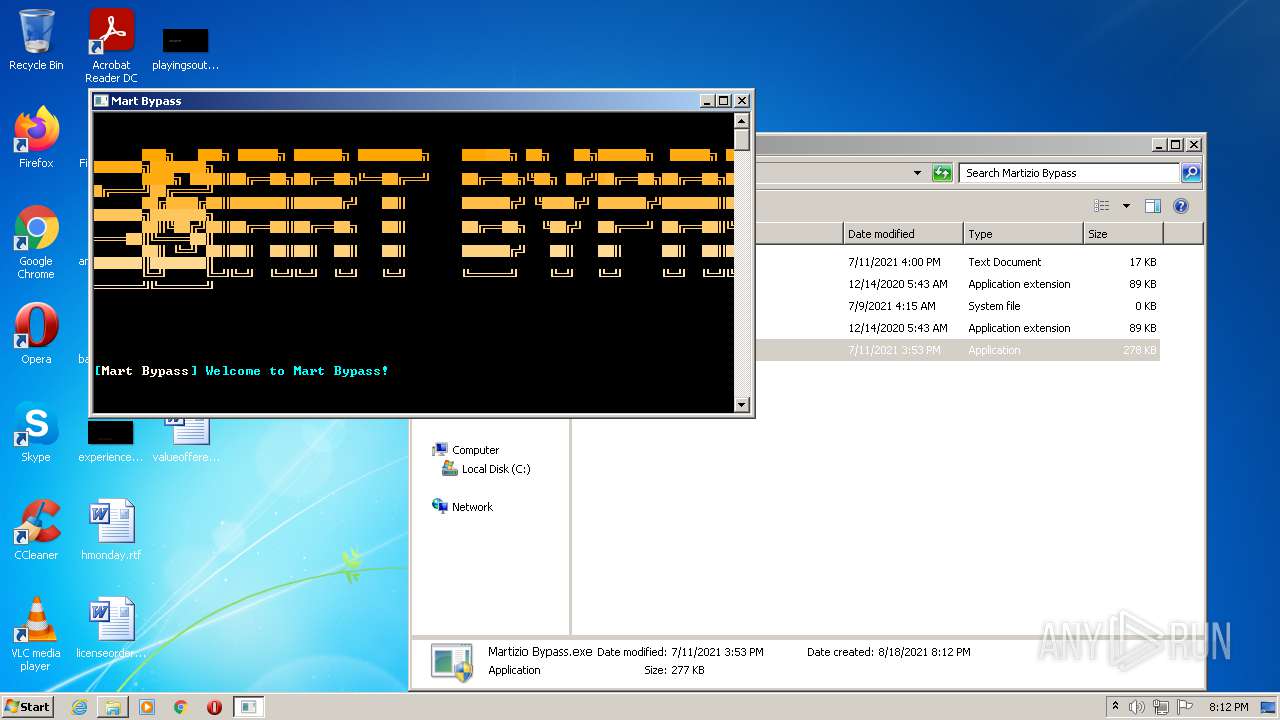
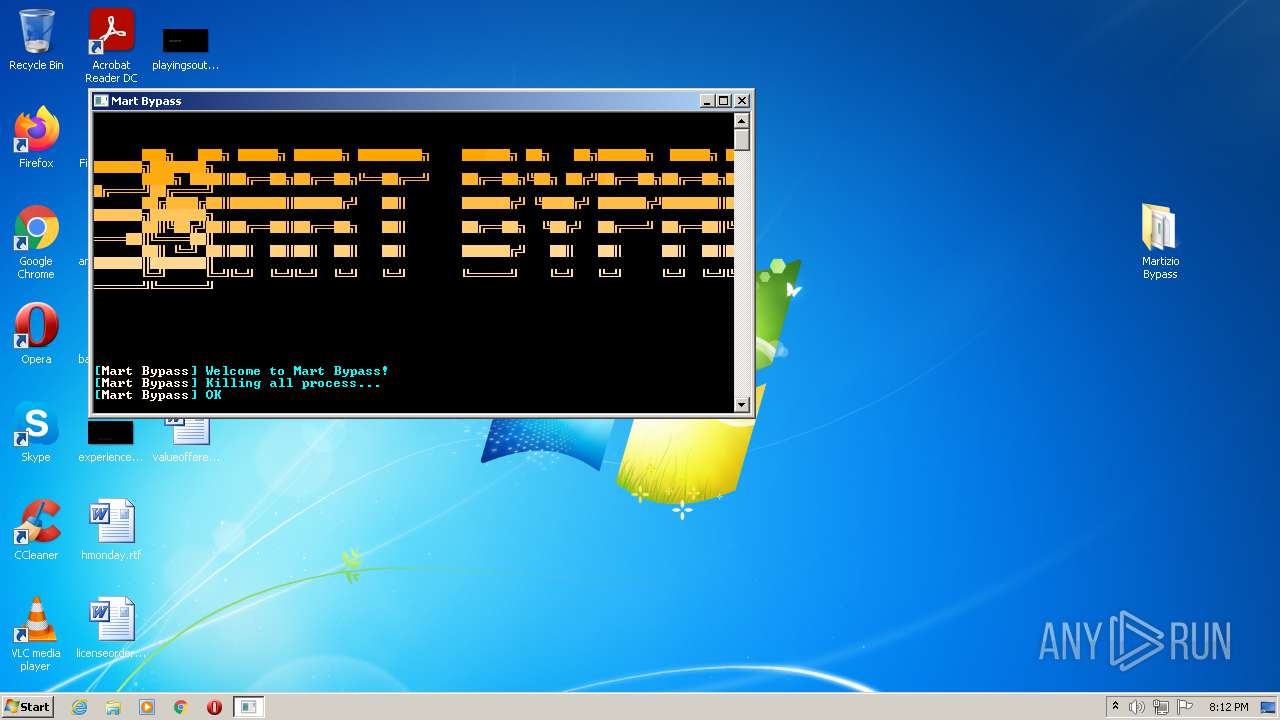
MALICIOUS
Application was dropped or rewritten from another process
- Martizio Bypass.exe (PID: 3600)
- Martizio Bypass.exe (PID: 1336)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2056)
- Martizio Bypass.exe (PID: 3600)
Changes settings of System certificates
- Martizio Bypass.exe (PID: 3600)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3276)
- Martizio Bypass.exe (PID: 3600)
Reads the computer name
- WinRAR.exe (PID: 3276)
- Martizio Bypass.exe (PID: 3600)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3276)
- Martizio Bypass.exe (PID: 3600)
Drops a file with too old compile date
- WinRAR.exe (PID: 3276)
- Martizio Bypass.exe (PID: 3600)
Reads default file associations for system extensions
- SearchProtocolHost.exe (PID: 2056)
- WinRAR.exe (PID: 3276)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3276)
- Martizio Bypass.exe (PID: 3600)
Reads Environment values
- Martizio Bypass.exe (PID: 3600)
Creates executable files which already exist in Windows
- Martizio Bypass.exe (PID: 3600)
Adds / modifies Windows certificates
- Martizio Bypass.exe (PID: 3600)
Creates files in the user directory
- Martizio Bypass.exe (PID: 3600)
INFO
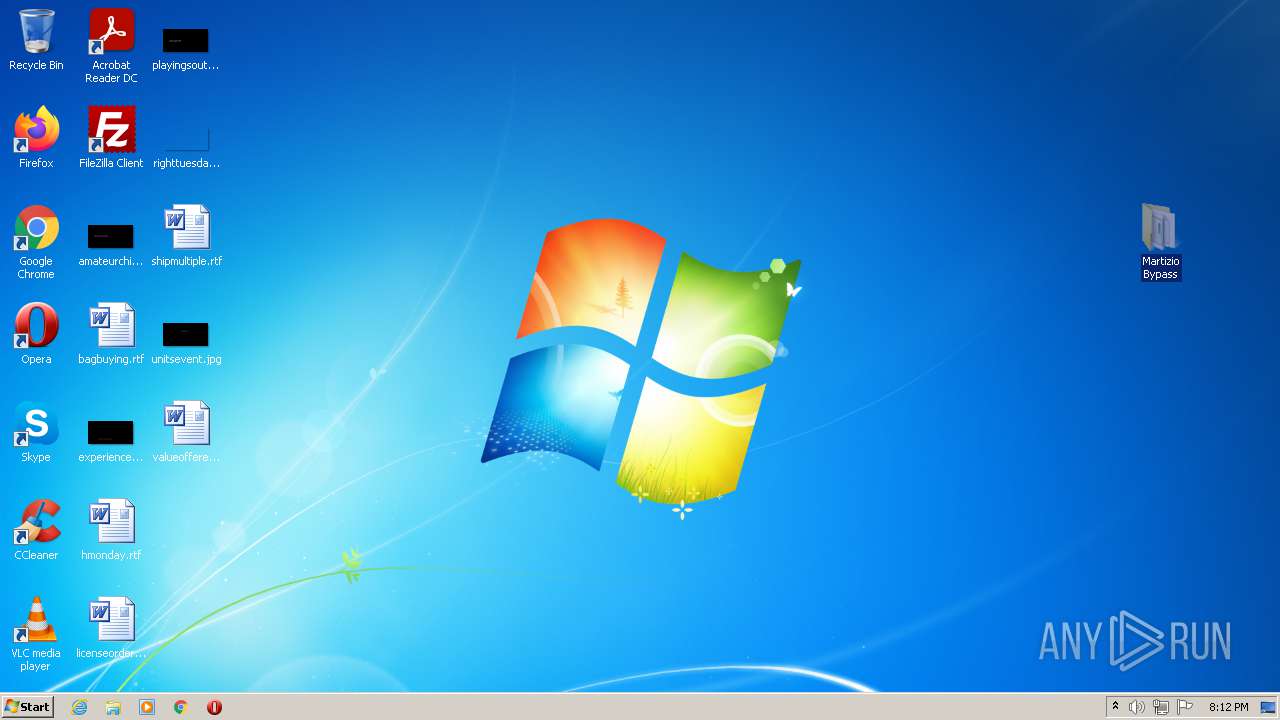
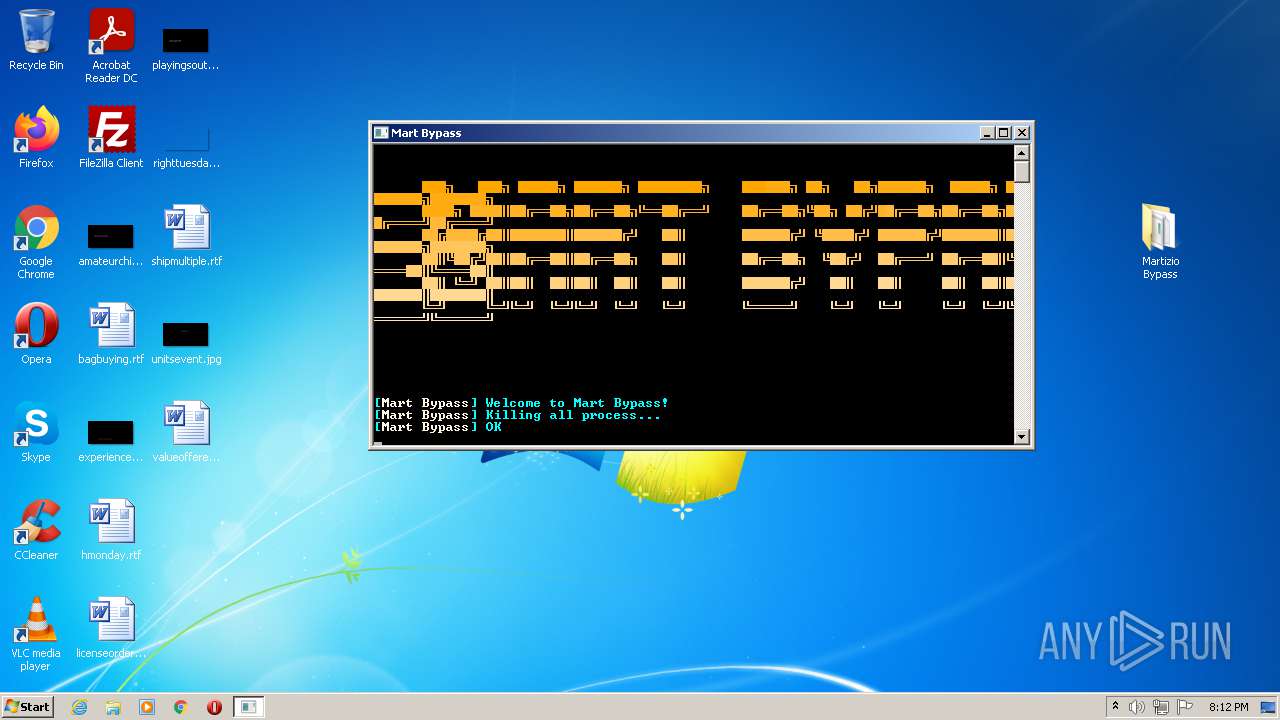
Manual execution by user
- Martizio Bypass.exe (PID: 1336)
- Martizio Bypass.exe (PID: 3600)
Reads settings of System Certificates
- Martizio Bypass.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
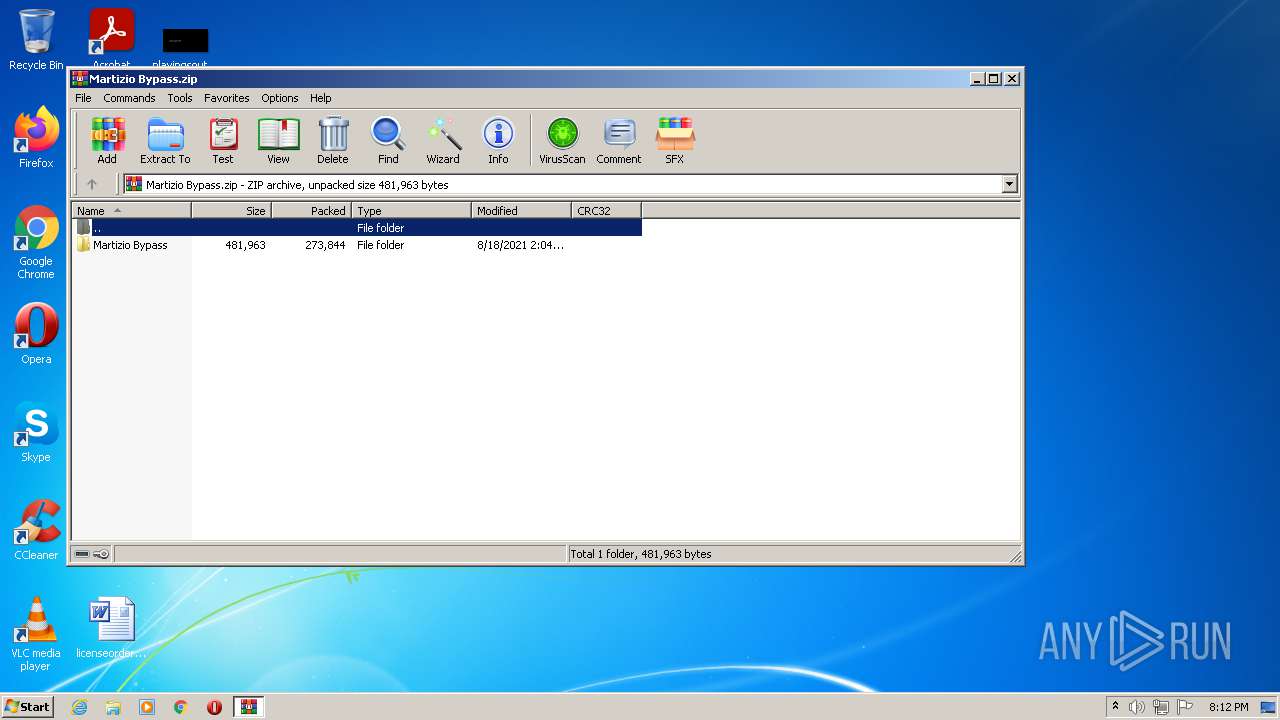
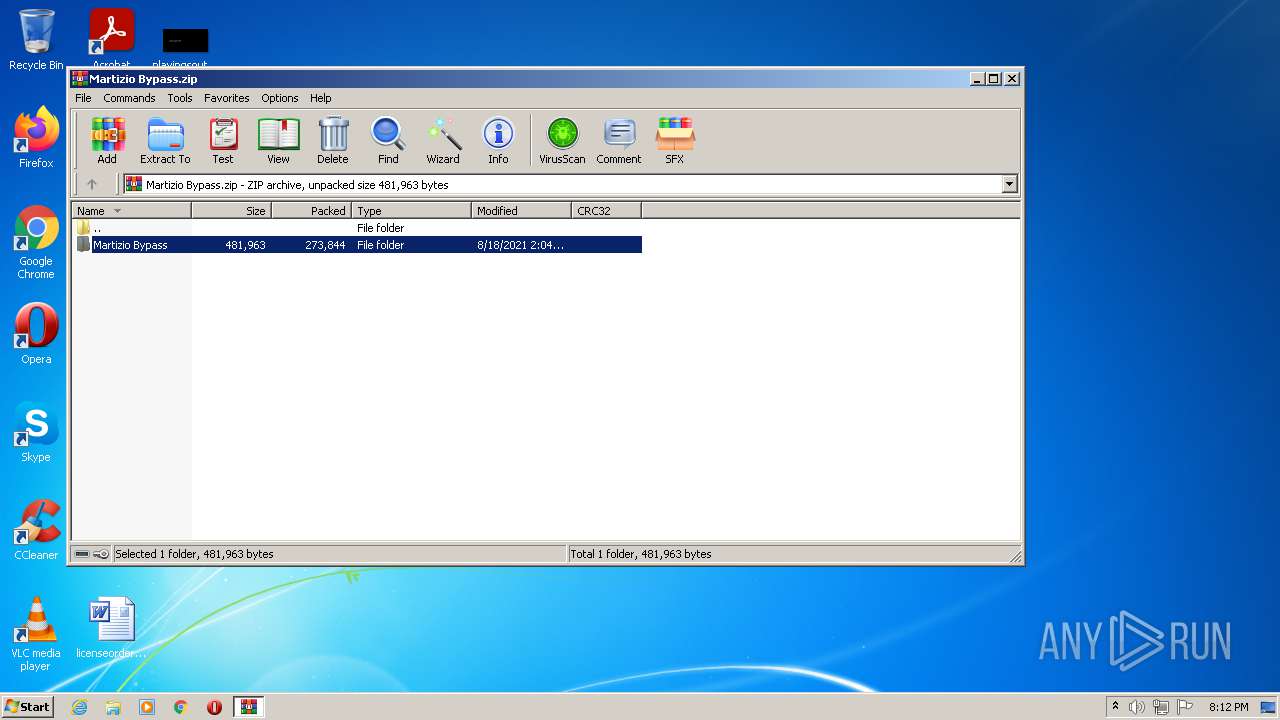
| ZipFileName: | Martizio Bypass/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2021:08:18 10:04:27 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
44
Monitored processes
4
Malicious processes
3
Suspicious processes
0
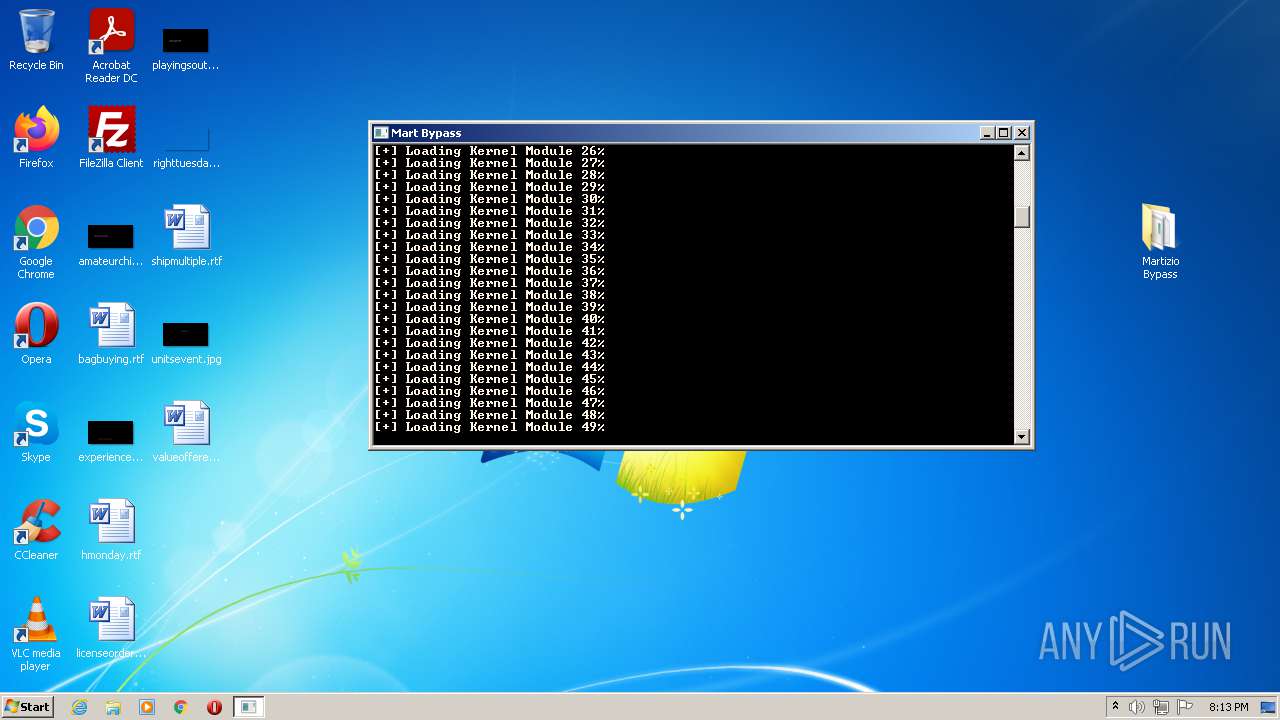
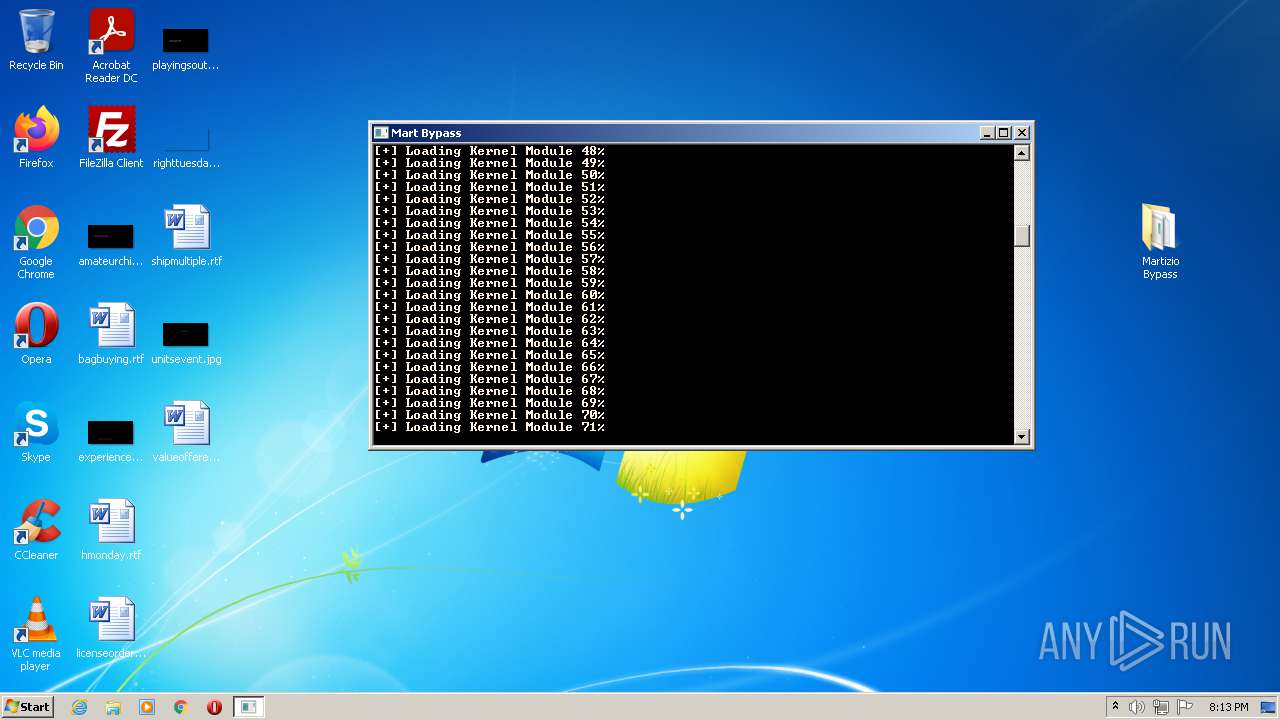
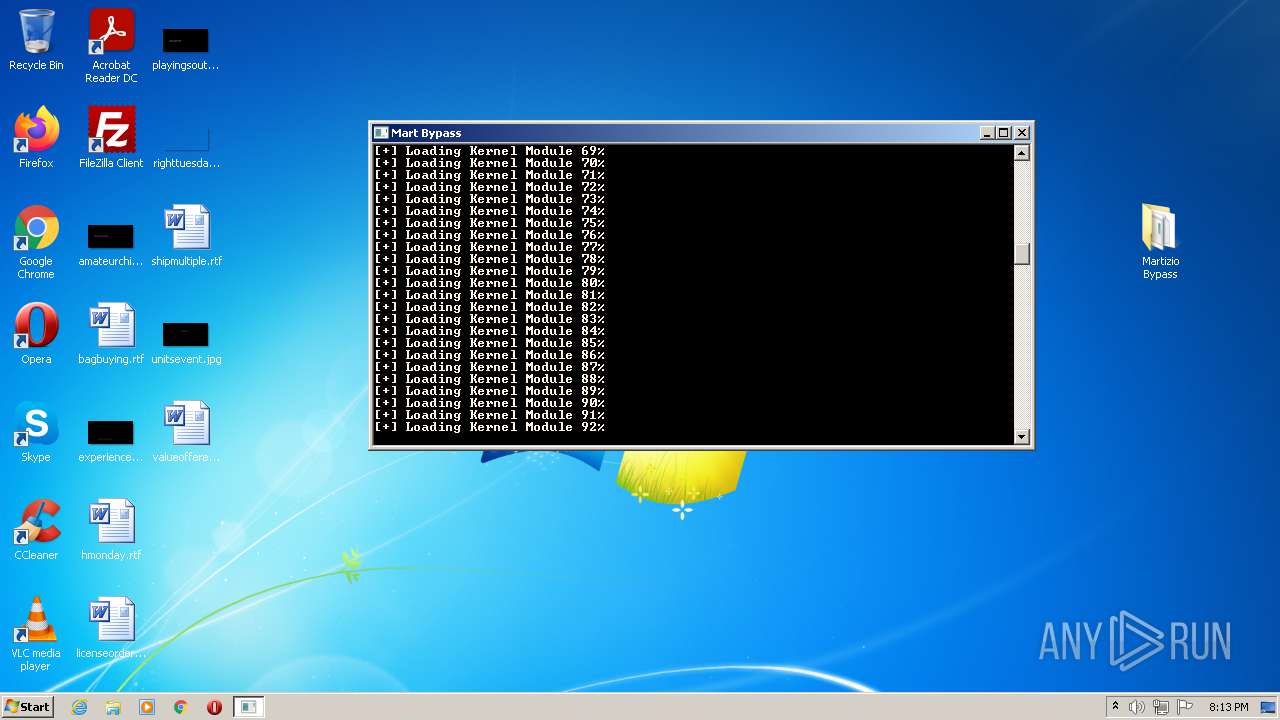
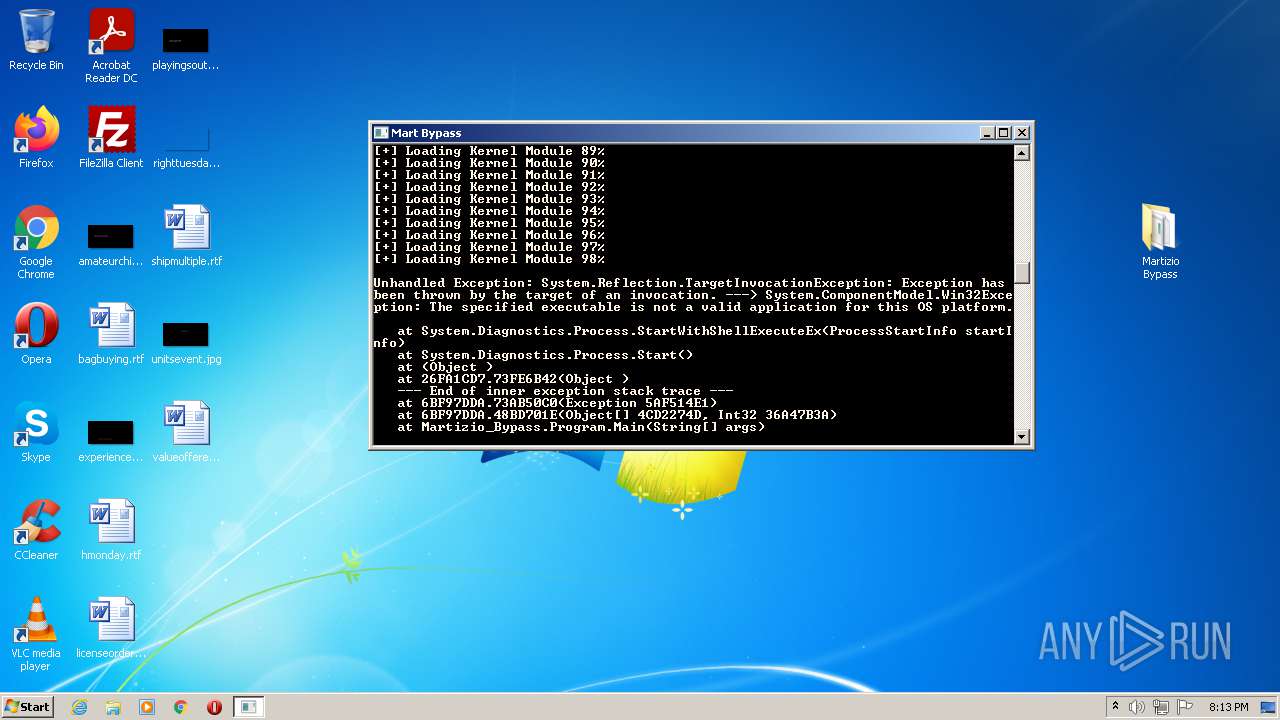
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
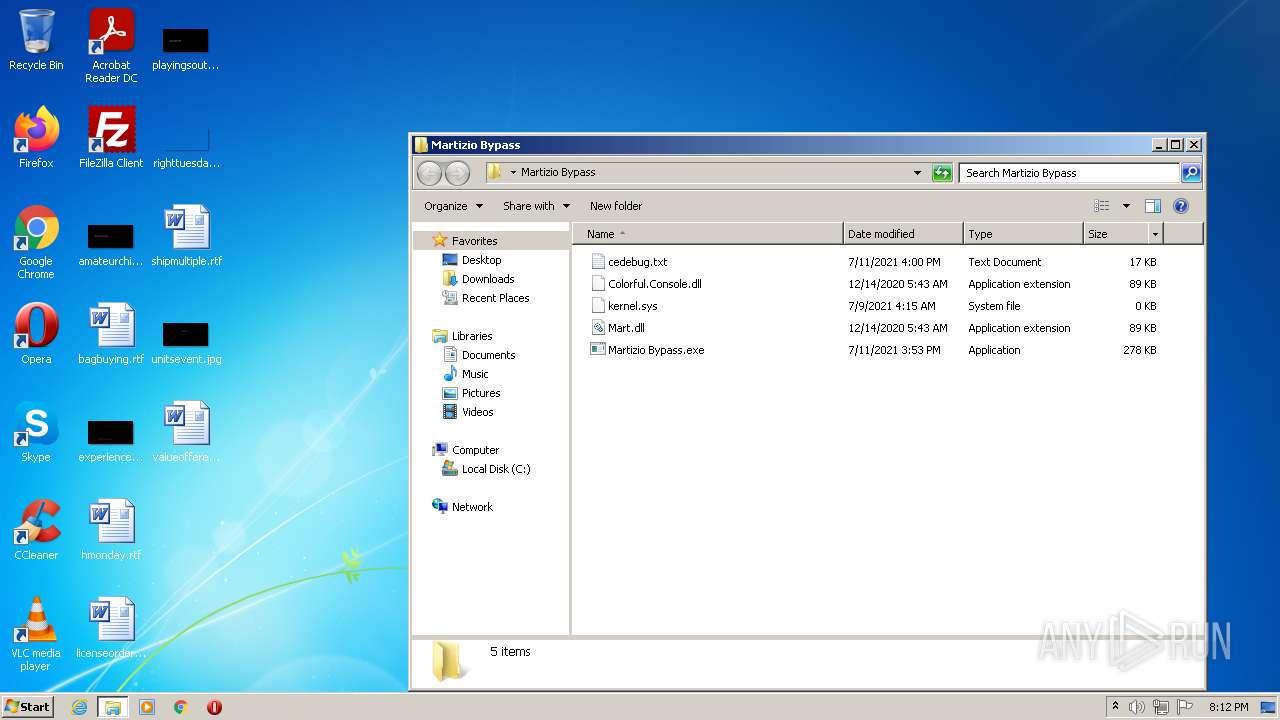
| 1336 | "C:\Users\admin\Desktop\Martizio Bypass\Martizio Bypass.exe" | C:\Users\admin\Desktop\Martizio Bypass\Martizio Bypass.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Martizio Bypass Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2056 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe9_ Global\UsGthrCtrlFltPipeMssGthrPipe9 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3276 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Martizio Bypass.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
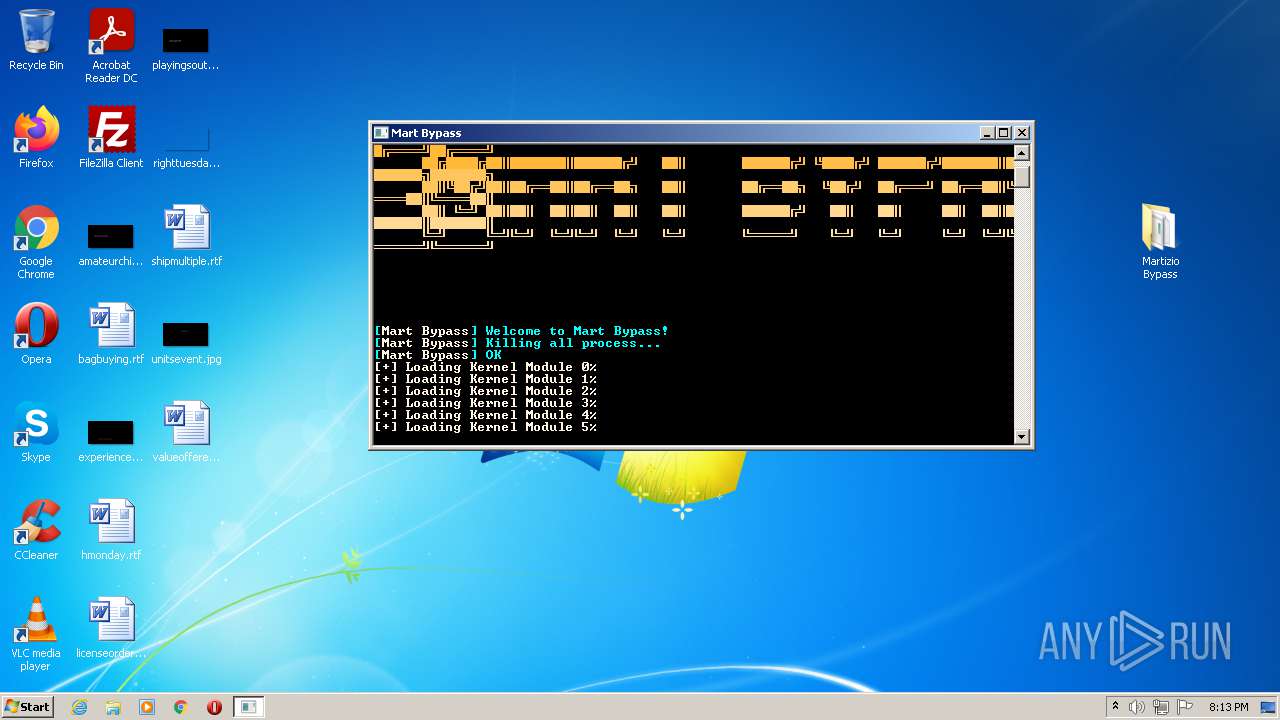
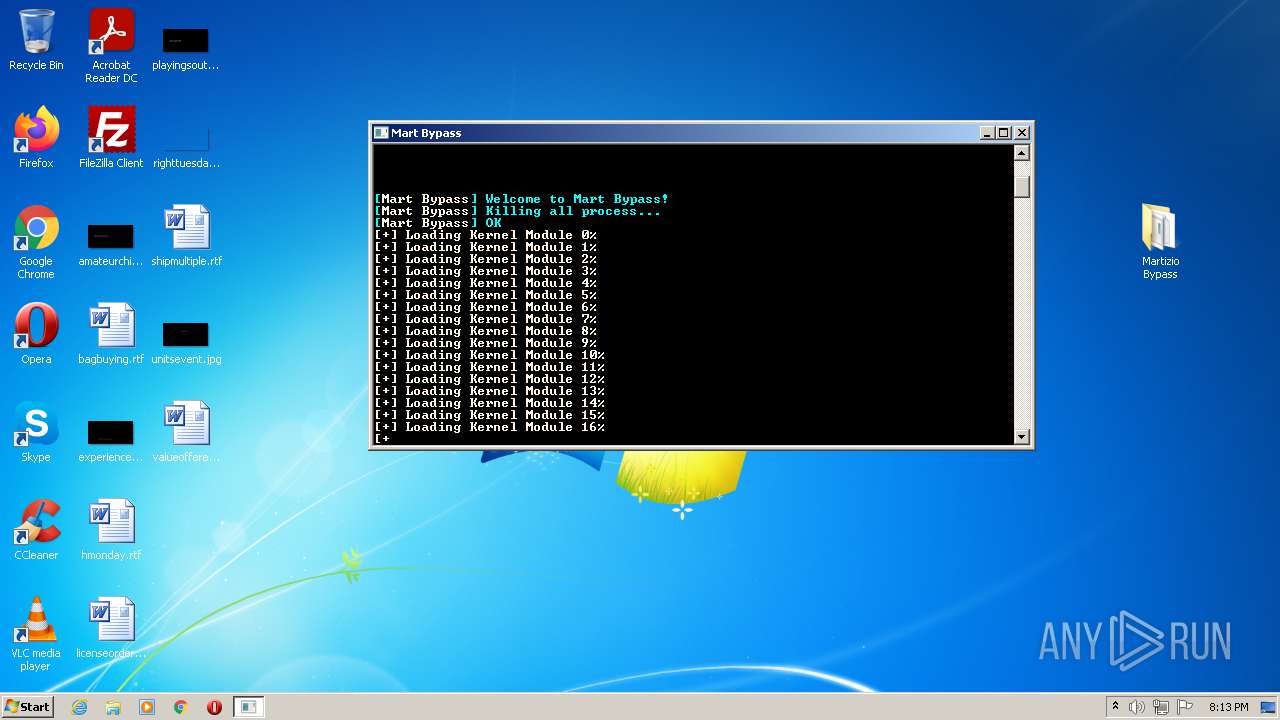
| 3600 | "C:\Users\admin\Desktop\Martizio Bypass\Martizio Bypass.exe" | C:\Users\admin\Desktop\Martizio Bypass\Martizio Bypass.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Martizio Bypass Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
5 658
Read events
5 601
Write events
57
Delete events
0
Modification events
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Martizio Bypass.zip | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (2056) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
61
Suspicious files
5
Text files
127
Unknown types
6
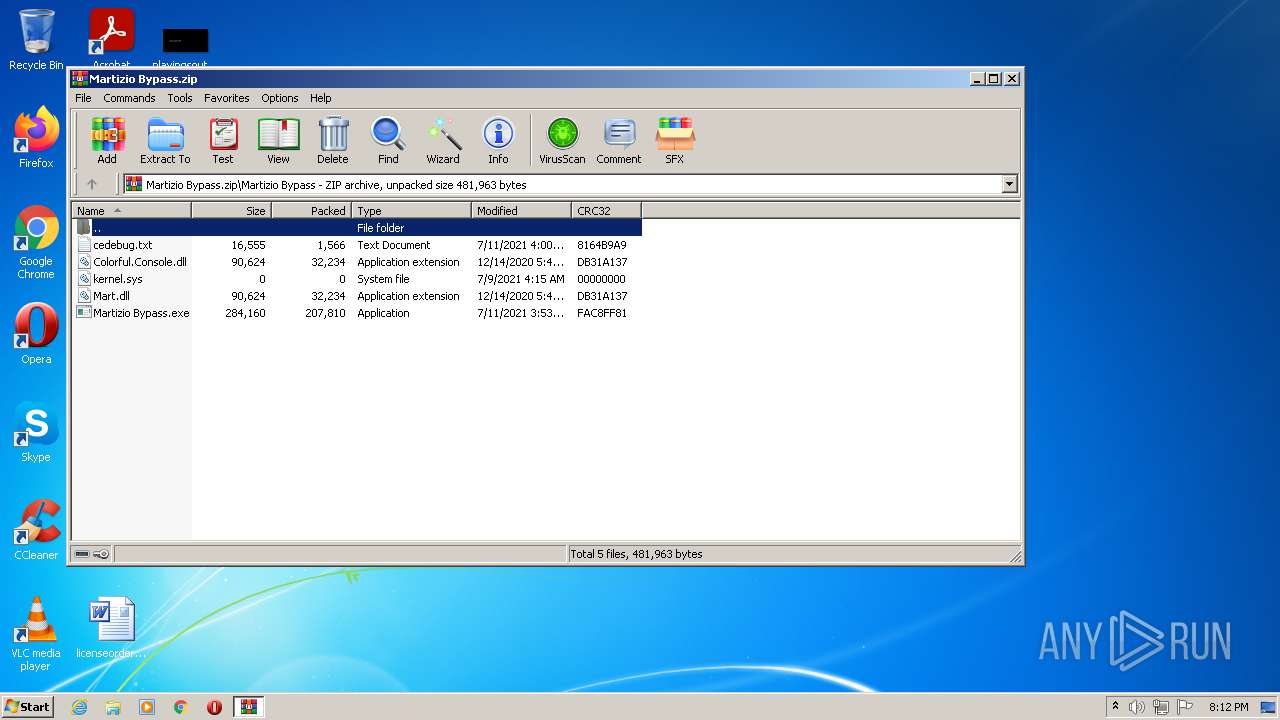
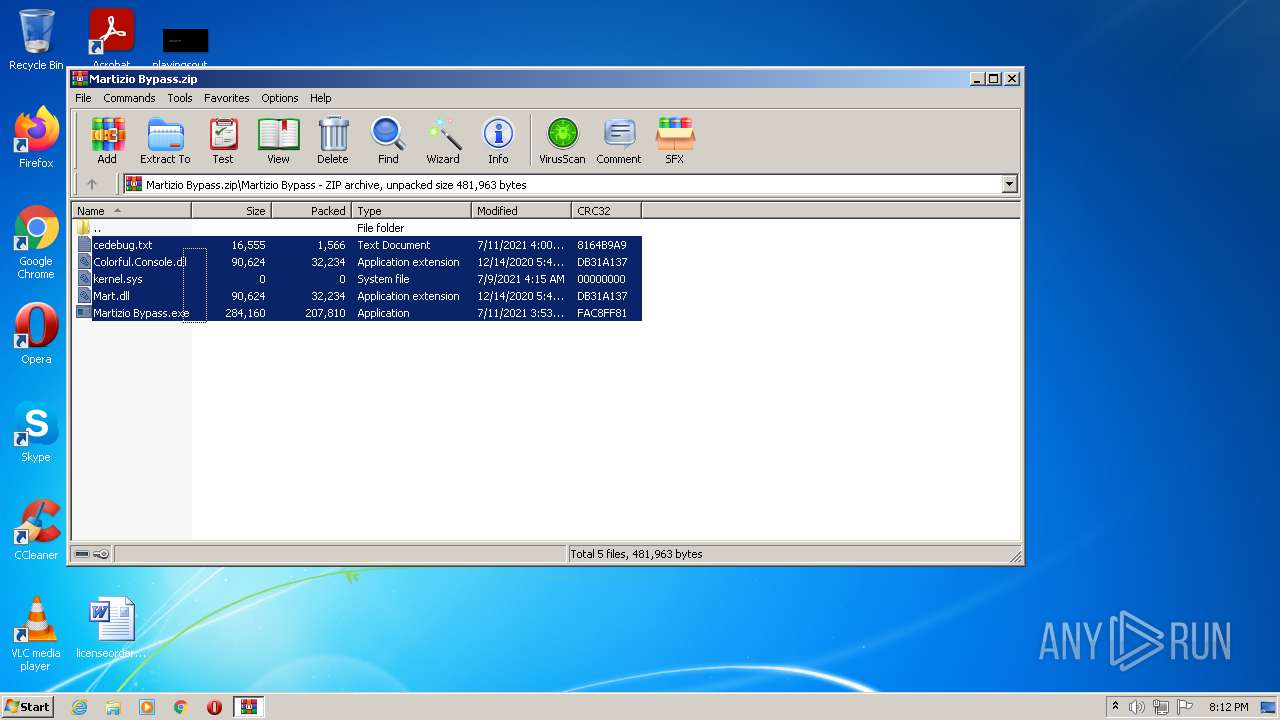
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3600 | Martizio Bypass.exe | C:\Users\admin\AppData\Roaming\Mart_Bypass\Temp\unpacked.zip | — | |
MD5:— | SHA256:— | |||
| 3276 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3276.11295\Martizio Bypass\Martizio Bypass.exe | executable | |
MD5:— | SHA256:— | |||
| 3276 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3276.11295\Martizio Bypass\cedebug.txt | text | |
MD5:— | SHA256:— | |||
| 3276 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3276.11295\Martizio Bypass\Mart.dll | executable | |
MD5:9F6CE7FF934FB2E786CED3516705EFAD | SHA256:59A3696950AC3525E31CDD26727DABD9FECD2E1BDC1C47C370D4B04420592436 | |||
| 3600 | Martizio Bypass.exe | C:\Users\admin\AppData\Roaming\Martizio_Bypass\autorun\ceshare\ceshare_permissions.lua | text | |
MD5:65C8D4EDDFE05267A72EAE3DDB2CF02A | SHA256:15B0C7682E5E8D2E2C2B8CB00C0C03B7DFA9439AC80C37F8E96A4F86652246F9 | |||
| 3600 | Martizio Bypass.exe | C:\Users\admin\AppData\Roaming\Martizio_Bypass\autorun\ceshare\ceshare_comments.lua | text | |
MD5:0D4D1B597712015EF1B0EC8ADC26495F | SHA256:89C8FCCC16D2AA0A3004DC1B477A5C1DCBBA539769B2A4558F7C7D9B9809B133 | |||
| 3600 | Martizio Bypass.exe | C:\Users\admin\AppData\Roaming\Martizio_Bypass\allochook-i386.dll | executable | |
MD5:6E808A8B417331EA7645B6A9FFA4B8FE | SHA256:B8DF41C3153C2A3212523099C71BC81AC97304DC886D8B4670A4F9A7AE6C3568 | |||
| 3600 | Martizio Bypass.exe | C:\Users\admin\AppData\Roaming\Martizio_Bypass\autorun\ceshare\ceshare_querycheats.lua | text | |
MD5:17AF0739B2F4B64373047E528F776B95 | SHA256:0F7424FF4F4D02B51C504C0C9A8A34B6F059C3FEA81C6B19E7AD0110478ABA26 | |||
| 3600 | Martizio Bypass.exe | C:\Users\admin\AppData\Roaming\Martizio_Bypass\autorun\ceshare\forms\BrowseCheats.FRM | xml | |
MD5:D4F5FE5A2F5FEEB3D97B2FDF4AE7E6BC | SHA256:9CB25C63AB41BE2BA3984DF20686DD27BF937E029EBFAA56EBE88BAC6DFC53B6 | |||
| 3600 | Martizio Bypass.exe | C:\Users\admin\AppData\Roaming\Martizio_Bypass\allochook-x86_64.dll | executable | |
MD5:BA991541C10506A7BD4A9DC6A7382E2E | SHA256:060F98F88F6280234578B06894C35136887DDD4C635C84A98E0297F5EF381870 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3600 | Martizio Bypass.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
3600 | Martizio Bypass.exe | 154.52.41.72:443 | api.blacklounge.xyz | Cogent Communications | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
api.blacklounge.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3600 | Martizio Bypass.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |