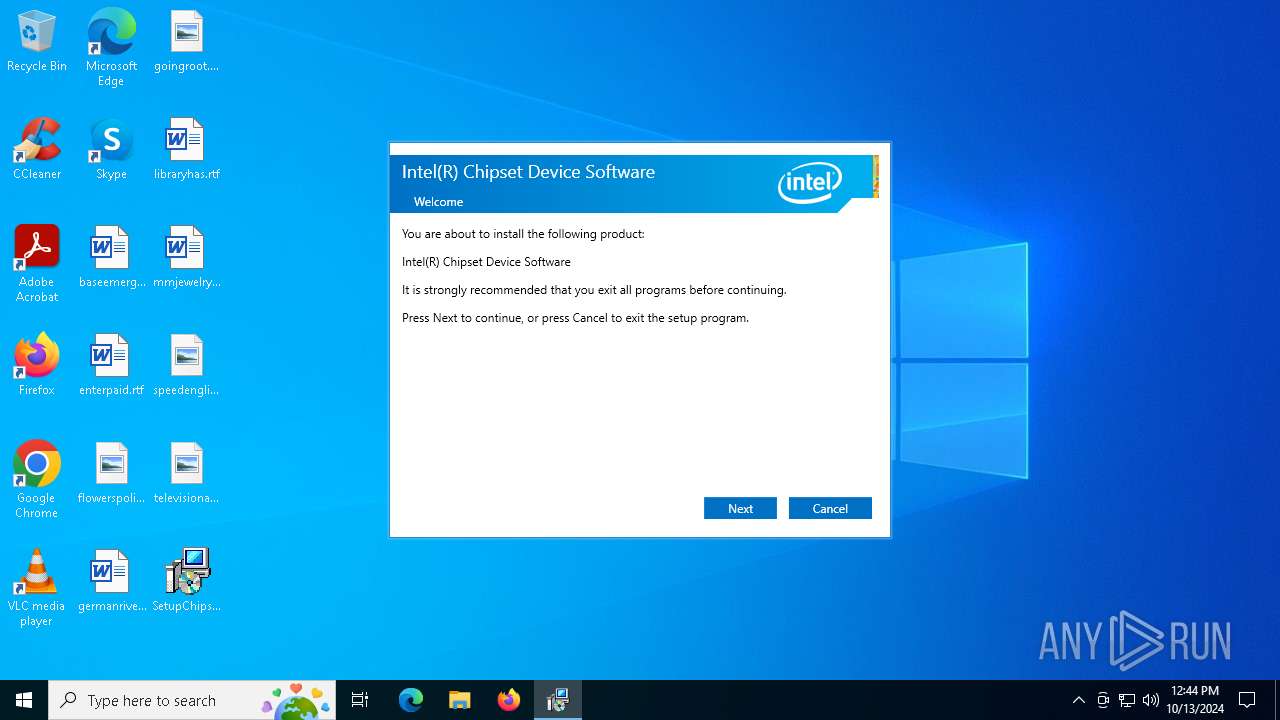
| File name: | SetupChipset.exe |
| Full analysis: | https://app.any.run/tasks/224b0eae-e050-44ba-8fba-ed0339fdcd53 |
| Verdict: | Malicious activity |
| Analysis date: | October 13, 2024, 12:44:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 26A024C29BE5DC2F9D508DE89D231595 |
| SHA1: | 3D61C29167EAC8C1A1073BFCA593A99C83FF1A5E |
| SHA256: | EA89F43B4A60CE57A3817DA7618BFEAE0D42177494D84DDDF083B7519AD468E4 |
| SSDEEP: | 98304:I1svXJG6gIS6/BfJtJBvVgwOVssnw+s7CuhOrSXNLf2mS8/h8DMfZab7yxOB8Wpi:LhTfr |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- SetupChipset.exe (PID: 6704)
- SetupChipset.exe (PID: 4072)
- SetupChipset.exe (PID: 4684)
- rundll32.exe (PID: 6336)
- rundll32.exe (PID: 3568)
The process creates files with name similar to system file names
- SetupChipset.exe (PID: 4072)
Searches for installed software
- SetupChipset.exe (PID: 4072)
Starts itself from another location
- SetupChipset.exe (PID: 4072)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 1700)
INFO
Checks supported languages
- SetupChipset.exe (PID: 6704)
- SetupChipset.exe (PID: 4072)
Create files in a temporary directory
- SetupChipset.exe (PID: 6704)
- SetupChipset.exe (PID: 4072)
Reads the machine GUID from the registry
- SetupChipset.exe (PID: 4072)
Reads the computer name
- SetupChipset.exe (PID: 4072)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4476)
Application launched itself
- msiexec.exe (PID: 4476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:22 22:14:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 314368 |
| InitializedDataSize: | 164352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x302e5 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
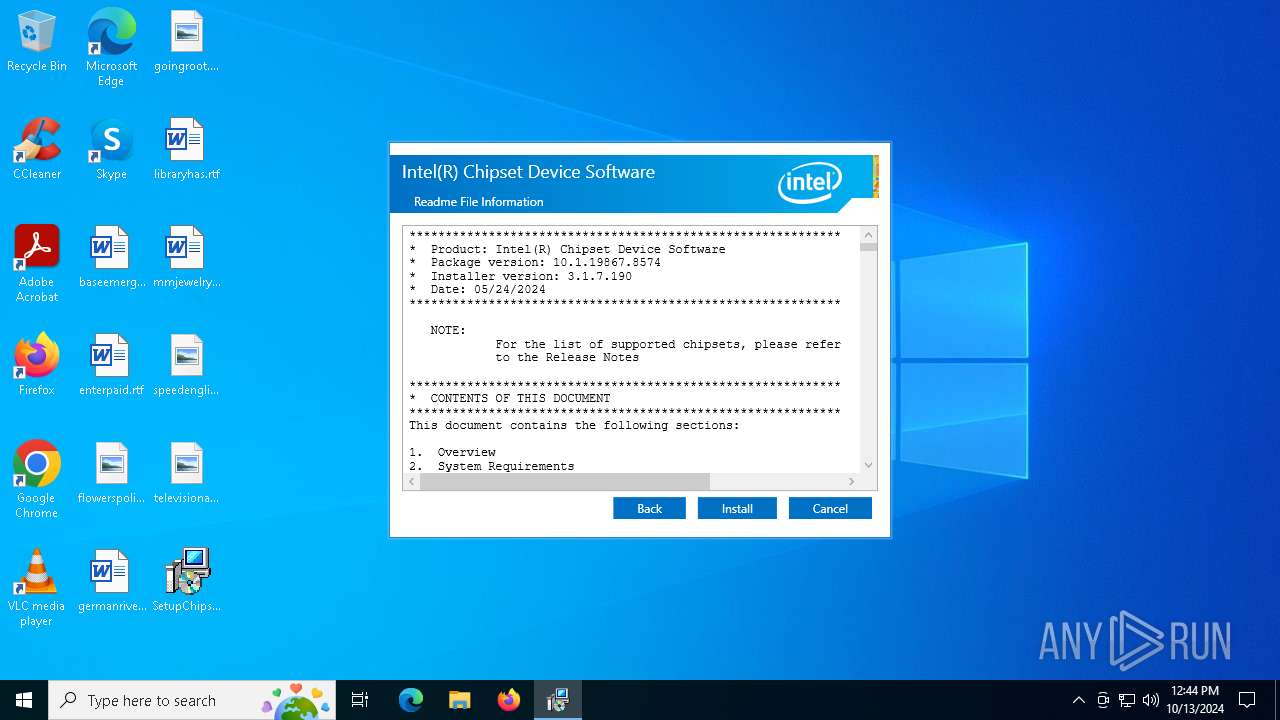
| FileVersionNumber: | 10.1.19867.8574 |
| ProductVersionNumber: | 10.1.19867.8574 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Intel(R) Corporation |
| FileDescription: | Intel(R) Chipset Device Software |
| FileVersion: | 10.1.19867.8574 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Intel(R) Corporation. All rights reserved. |
| OriginalFileName: | SetupChipset.exe |
| ProductName: | Intel(R) Chipset Device Software |
| ProductVersion: | 10.1.19867.8574 |
Total processes
135
Monitored processes
7
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1700 | C:\Windows\System32\MsiExec.exe -Embedding F1B024964C4A794BC7764E7813986758 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3568 | rundll32.exe "C:\WINDOWS\Installer\MSI49F0.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_608781 8 ChipsetWiX.CustomAction!Intel.Deployment.ChipsetWiX.CustomActions.PrepareInstall | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4072 | "C:\Users\admin\AppData\Local\Temp\{7D241721-1D12-42F5-AE83-C9BB9052B919}\.cr\SetupChipset.exe" -burn.clean.room="C:\Users\admin\Desktop\SetupChipset.exe" -burn.filehandle.attached=596 -burn.filehandle.self=572 | C:\Users\admin\AppData\Local\Temp\{7D241721-1D12-42F5-AE83-C9BB9052B919}\.cr\SetupChipset.exe | SetupChipset.exe | ||||||||||||
User: admin Company: Intel(R) Corporation Integrity Level: MEDIUM Description: Intel(R) Chipset Device Software Exit code: 20004 Version: 10.1.19867.8574 Modules
| |||||||||||||||
| 4476 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4684 | "C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.be\SetupChipset.exe" -q -burn.elevated BurnPipe.{33E26EF3-49DA-4702-80BB-9AB910661C5E} {7C2E8CC1-8FA5-4606-B672-EEDF27BFB606} 4072 | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.be\SetupChipset.exe | SetupChipset.exe | ||||||||||||
User: admin Company: Intel(R) Corporation Integrity Level: HIGH Description: Intel(R) Chipset Device Software Exit code: 20004 Version: 10.1.19867.8574 Modules
| |||||||||||||||
| 6336 | rundll32.exe "C:\WINDOWS\Installer\MSI48D5.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_608546 2 ChipsetWiX.CustomAction!Intel.Deployment.ChipsetWiX.CustomActions.SetTargetPath | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6704 | "C:\Users\admin\Desktop\SetupChipset.exe" | C:\Users\admin\Desktop\SetupChipset.exe | explorer.exe | ||||||||||||
User: admin Company: Intel(R) Corporation Integrity Level: MEDIUM Description: Intel(R) Chipset Device Software Exit code: 20004 Version: 10.1.19867.8574 Modules
| |||||||||||||||
Total events
8 090
Read events
8 038
Write events
36
Delete events
16
Modification events
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\ProgramData\Package Cache\{794e9c5a-0300-4591-8d51-5fca6934efd1}\SetupChipset.exe | |||
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {D8CA2E7A-5763-4161-82B8-F870F2BD4F2F} | |||
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | BundleVersion |
Value: 10.1.19867.8574 | |||
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | VersionMajor |
Value: 10 | |||
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | VersionMinor |
Value: 1 | |||
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | BundleProviderKey |
Value: {794e9c5a-0300-4591-8d51-5fca6934efd1} | |||
| (PID) Process: | (4684) SetupChipset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{794e9c5a-0300-4591-8d51-5fca6934efd1} |
| Operation: | write | Name: | BundleTag |
Value: | |||
Executable files
91
Suspicious files
160
Text files
36
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4072 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.ba\Bootstrapper.dll | executable | |
MD5:145141B289FFF841F9CD315F1C5F33CC | SHA256:3EBC16013A2C89E1AA3051CBCD1B0DB6E67A80D2090CE9DDC6376D381B48DB59 | |||
| 4072 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.ba\mbapreq.wxl | xml | |
MD5:4D2C8D10C5DCCA6B938B71C8F02CA8A8 | SHA256:C63DE5F309502F9272402587A6BE22624D1BC2FEACD1BD33FB11E44CD6614B96 | |||
| 4072 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.ba\1044\mbapreq.wxl | xml | |
MD5:5454F724C9CDAB8172678A1CC7057220 | SHA256:41545AC1247B61C3C3E2A7E4659D9FAD2BCCA8347C69F2EB7B9D0CF5FC31E113 | |||
| 4072 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.ba\mbahost.dll | executable | |
MD5:E3471734DF4345B4EC9F60333A96982B | SHA256:D728E7449243BC7099890BADB6FAE3F2B082A80D9C950E498051F89A65D48687 | |||
| 4072 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.ba\1060\mbapreq.wxl | xml | |
MD5:5836F0C655BDD97093F68AAF69AB2BAB | SHA256:C015247D022BDC108B4FFCAE89CB55D1E313034D7E6EED18744C1BB55F108F8C | |||
| 6704 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{7D241721-1D12-42F5-AE83-C9BB9052B919}\.cr\SetupChipset.exe | executable | |
MD5:6C477CFE8DC046592BF3AEB23F51BF5D | SHA256:ECF22C99FD8748F660B1F511D851DE6B390B06DFF2E4100D23DEBCEDDF5D61D3 | |||
| 4072 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.ba\1043\mbapreq.wxl | xml | |
MD5:67F28BCDB3BA6774CD66AA198B06FF38 | SHA256:226B778604236931B4AE45F6F272586C884A11517444A34BF45CD5CAE49BE62E | |||
| 4072 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.ba\Intel.Tools.dll | executable | |
MD5:6E79D40E7CEB7376455D796D0F2BA7E2 | SHA256:C475E6D4712978DBB4A9D3F926885181178923C17759EB9002551829F07BFB23 | |||
| 4072 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.ba\BootstrapperCore.dll | executable | |
MD5:E808F606E54D6F823B9D22F56E8982FC | SHA256:CF2AE76D1DA5AF70A72259E7E51DAE62C715BC32239DAF5DA6B1BDE122BCDAB6 | |||
| 4072 | SetupChipset.exe | C:\Users\admin\AppData\Local\Temp\{C325DD71-124C-4FA4-A9BC-6AE9B24243EC}\.ba\1032\mbapreq.wxl | xml | |
MD5:074D5921AF07E6126049CB45814246ED | SHA256:B8E90E20EDF110AAAAEA54FBC8533872831777BE5589E380CFDD17E1F93147B5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
22
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1764 | RUXIMICS.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4476 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEEXO0uQQ2KuFiIzKgfWL62E%3D | US | binary | 637 b | whitelisted |
4476 | msiexec.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | binary | 1.42 Kb | whitelisted |
4476 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | US | binary | 765 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1764 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1764 | RUXIMICS.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |