| File name: | PerfWatson2.exe |
| Full analysis: | https://app.any.run/tasks/d6b5b658-7352-475c-99db-a41562c5cbc2 |
| Verdict: | Malicious activity |
| Analysis date: | December 17, 2023, 20:19:26 |
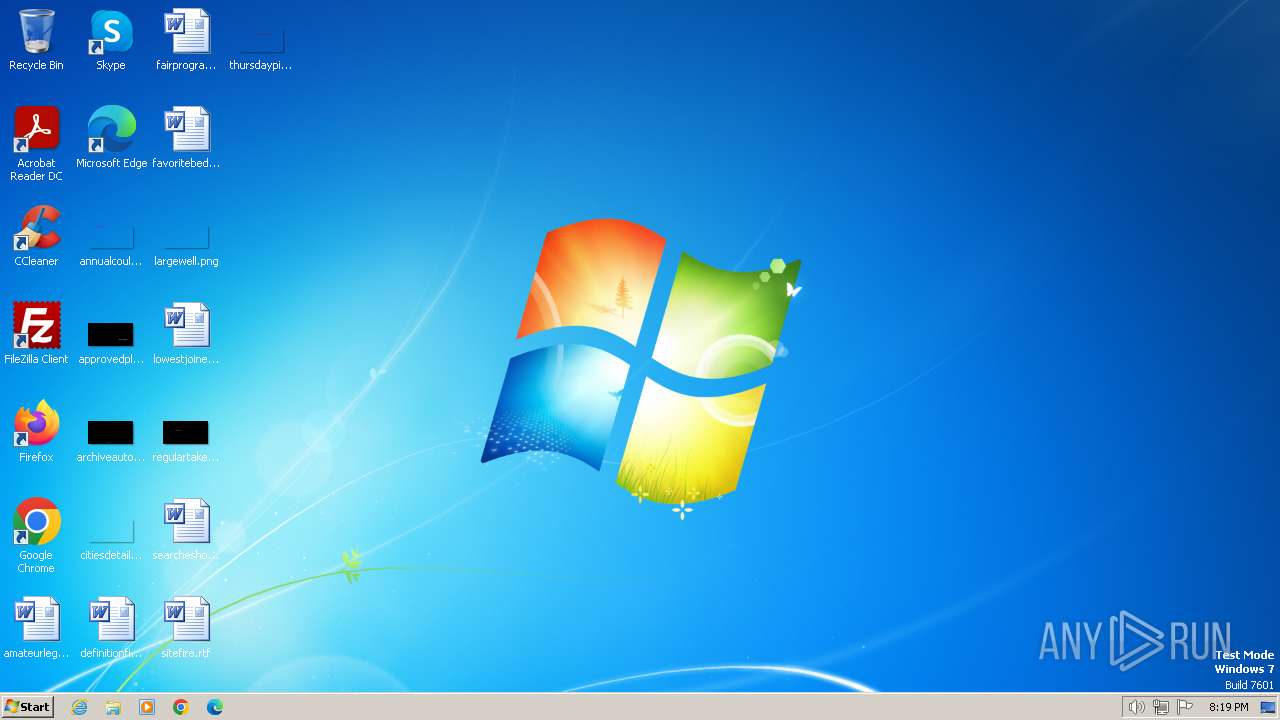
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 683C060CCCA9EE3A5DAD65946C8C9A88 |
| SHA1: | 35A18395CD290CF377FE665AEBDFB26E59869A5C |
| SHA256: | EA6F9411B4568ED828772CE578F40FF5B38715D067BDD76616D945F14462351A |
| SSDEEP: | 24576:ipJXCOkkO/MHqP0OF8u/N6HH6r8VDkiK:ipJX7kouFD8VIi |
MALICIOUS
Actions looks like stealing of personal data
- RegAsm.exe (PID: 2076)
SUSPICIOUS
Reads the Internet Settings
- PerfWatson2.exe (PID: 124)
- RegAsm.exe (PID: 2076)
Reads settings of System Certificates
- PerfWatson2.exe (PID: 124)
- RegAsm.exe (PID: 2076)
Starts POWERSHELL.EXE for commands execution
- RegAsm.exe (PID: 2076)
INFO
Reads the computer name
- RegAsm.exe (PID: 2076)
- PerfWatson2.exe (PID: 124)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 2076)
- PerfWatson2.exe (PID: 124)
Create files in a temporary directory
- PerfWatson2.exe (PID: 124)
- RegAsm.exe (PID: 2076)
Checks supported languages
- RegAsm.exe (PID: 2076)
- PerfWatson2.exe (PID: 124)
Reads Environment values
- PerfWatson2.exe (PID: 124)
- RegAsm.exe (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:17 18:16:44+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1810432 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1bbe46 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.0.0 |
| ProductVersionNumber: | 2.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | StackExchange.Profiling |
| CompanyName: | Stack Exchange |
| FileDescription: | StackExchange.Profiling |
| FileVersion: | 2.1.0.0 |
| InternalName: | b07a0 |
| LegalCopyright: | {5} |
| OriginalFileName: | b07a0 |
| ProductName: | {4} |
| ProductVersion: | 2.1.0.0 |
| AssemblyVersion: | 2.1.0.0 |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Temp\PerfWatson2.exe" | C:\Users\admin\AppData\Local\Temp\PerfWatson2.exe | explorer.exe | ||||||||||||
User: admin Company: Stack Exchange Integrity Level: MEDIUM Description: StackExchange.Profiling Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 1044 | "powershell.exe" Get-ItemPropertyValue -Path HKCU:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1972 | "powershell.exe" Get-ItemPropertyValue -Path HKLN:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
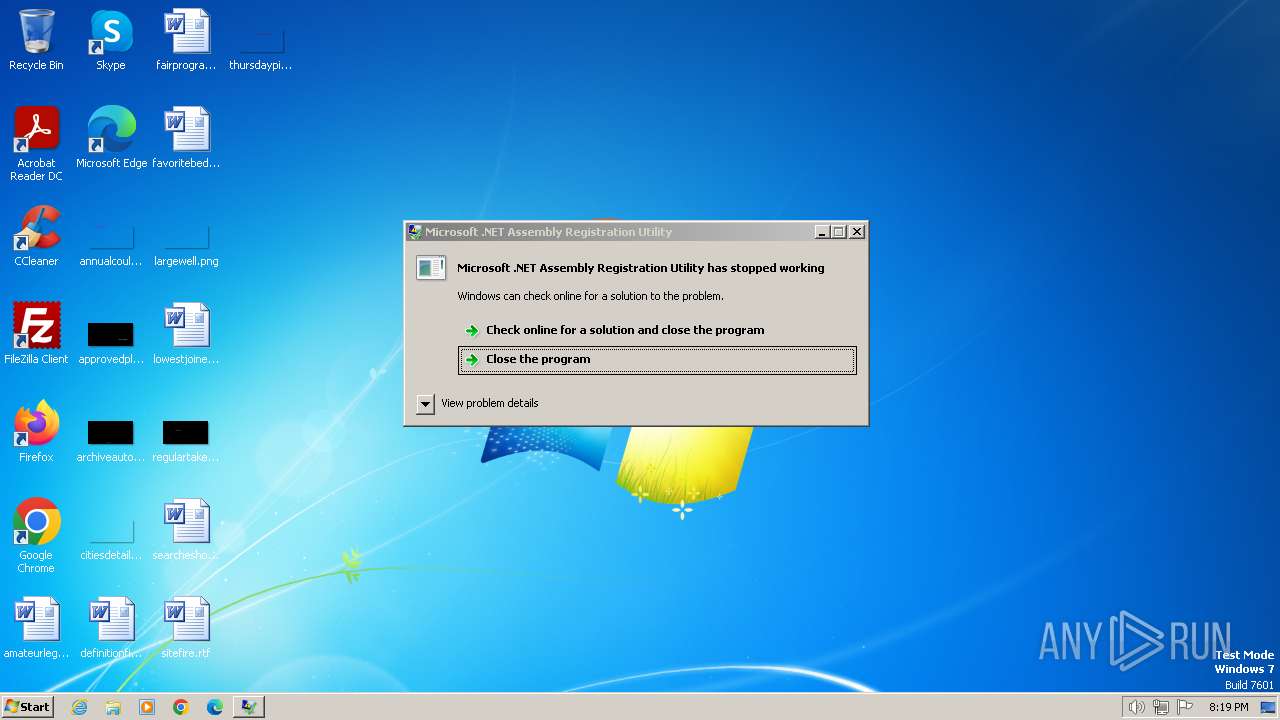
| 2076 | "C:\\Windows\\Microsoft.NET\\Framework\\v4.0.30319\\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | PerfWatson2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
9 725
Read events
9 697
Write events
28
Delete events
0
Modification events
| (PID) Process: | (124) PerfWatson2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2076) RegAsm.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
10
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 124 | PerfWatson2.exe | C:\Users\admin\AppData\Local\Temp\CabF916.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2076 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\9Uu3MtoQspOAHor | binary | |
MD5:6A80DD356027C9C7B333113E9B2AA028 | SHA256:7C236E441D371B0B85C2A5EAACC3E269214A06AA385835231DA163110C3F7FA4 | |||
| 124 | PerfWatson2.exe | C:\Users\admin\AppData\Local\Temp\TarF917.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 124 | PerfWatson2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 124 | PerfWatson2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:BDFC9A9160621DE0BD9DEC7DBEAC1472 | SHA256:E82347A44179D0DC8B984B4ACB4A1306E72B1E5924F1D3315738A59F65618F18 | |||
| 1044 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hppvzqy5.4ya.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
| 1044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\yagaahqu.eal.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
| 1972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\khzkmjsr.o44.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
| 1044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\m4r3nz0d.gle.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
124 | PerfWatson2.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?67c7103e6bf462aa | GB | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
124 | PerfWatson2.exe | 104.21.49.212:443 | artemis.community | CLOUDFLARENET | — | unknown |
124 | PerfWatson2.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2076 | RegAsm.exe | 142.250.74.195:443 | gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
artemis.community |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
gstatic.com |
| whitelisted |