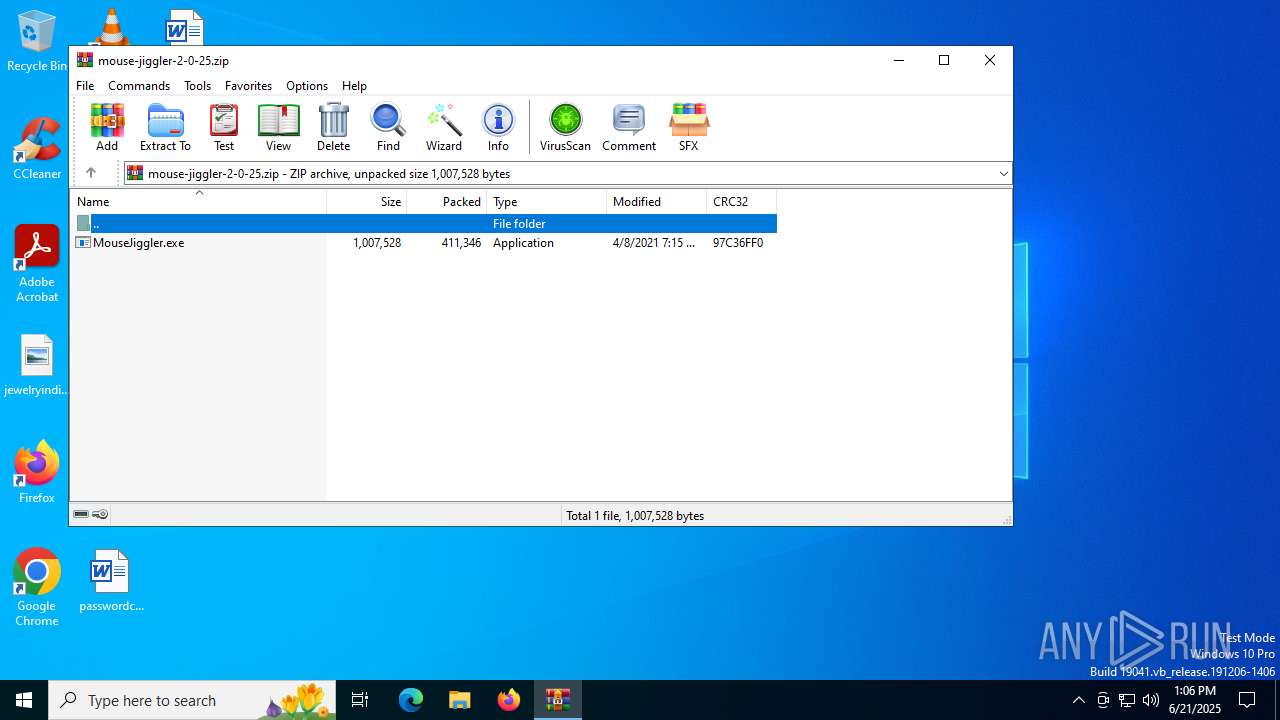
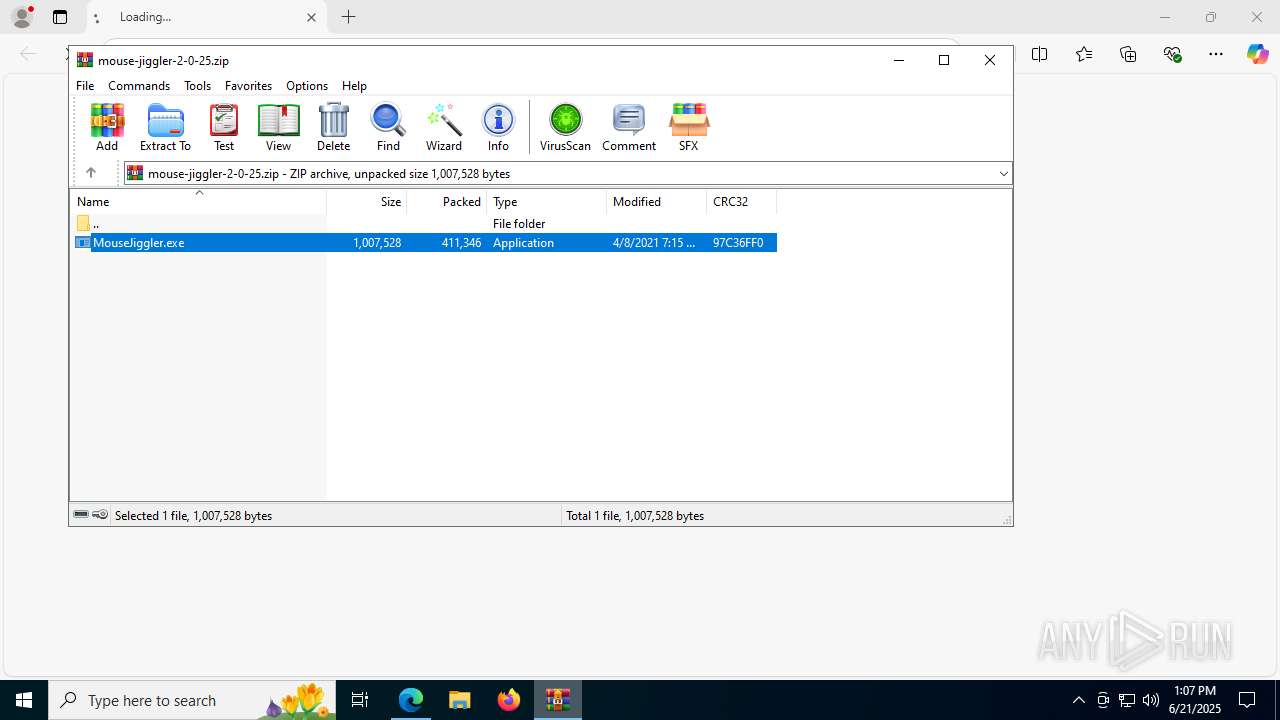
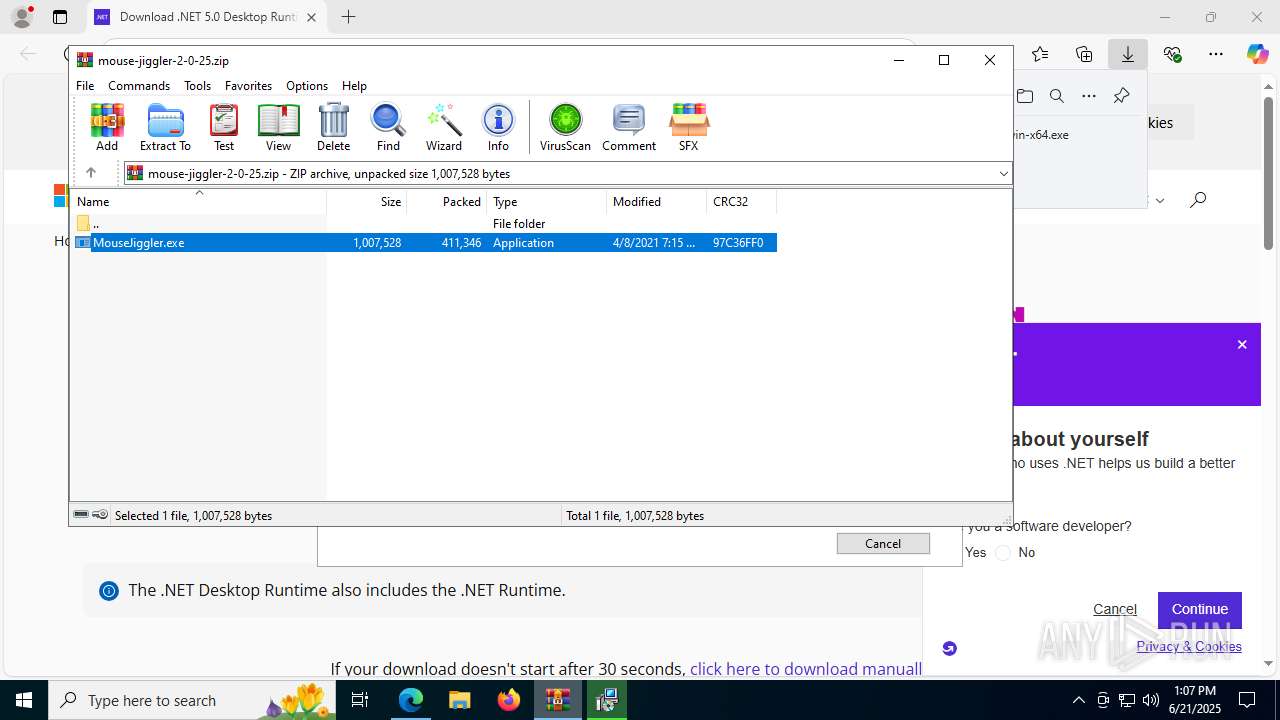
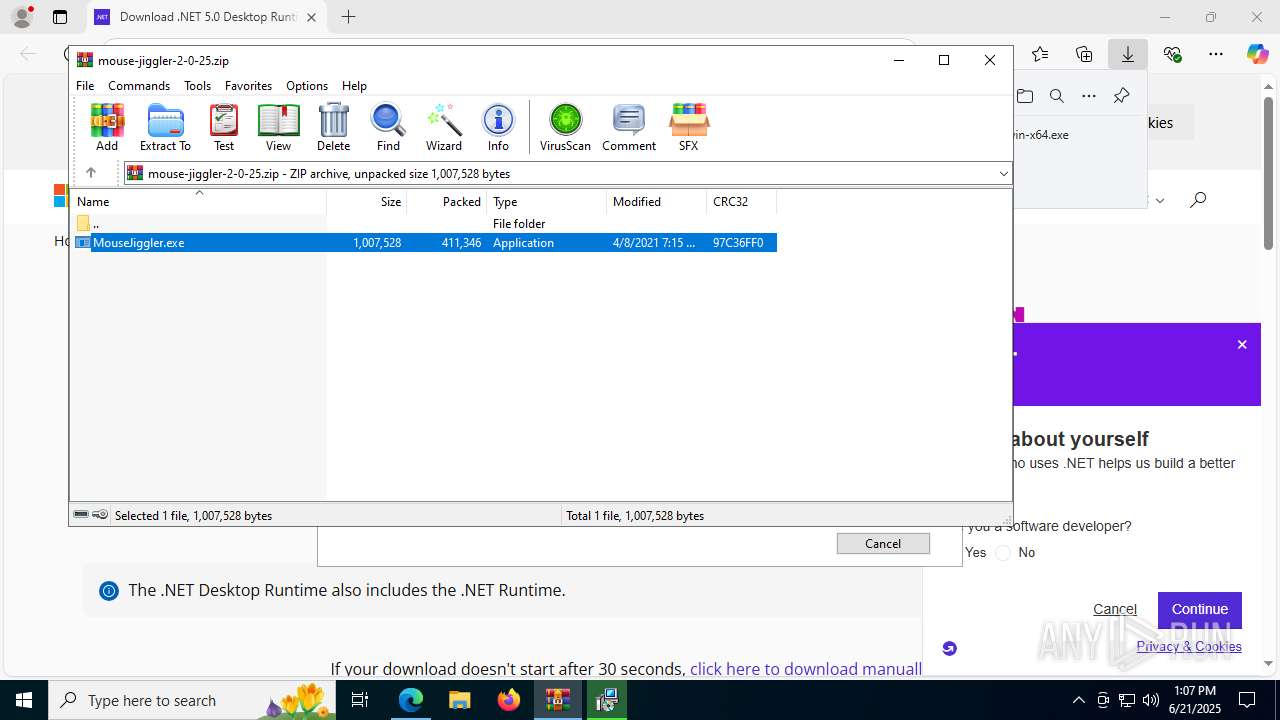
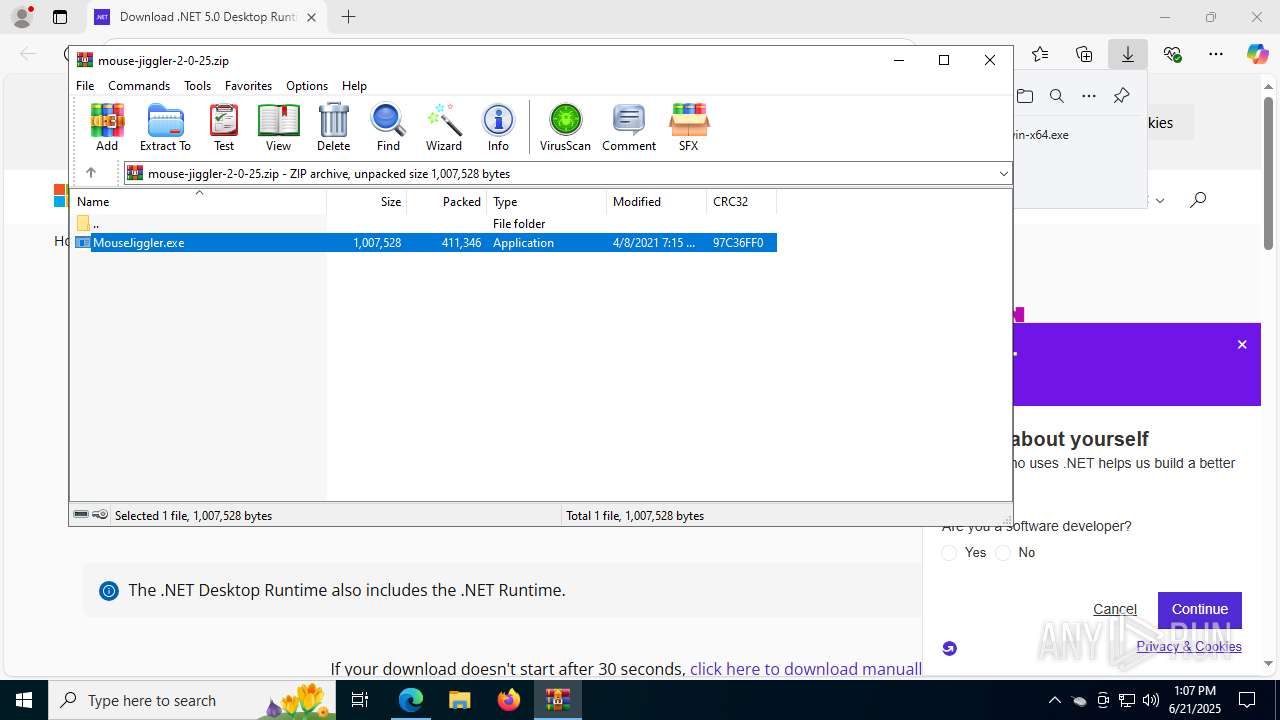
| File name: | mouse-jiggler-2-0-25.zip |
| Full analysis: | https://app.any.run/tasks/6a6e3761-132f-4b92-8539-9113feaf36be |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 13:06:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D10AA2403261677EDCB39FDC2B672F58 |
| SHA1: | 959BBD388DE785EA497B7E004206943215CCB9BC |
| SHA256: | EA61E59C58D8A80829C6AD565D292D716280D926E7BB1439CB0268A66264941C |
| SSDEEP: | 12288:ByY07+fnG6sNYCaZO/RSQyWWcYxUsMKMsY/:u+fN7CaY/0QyvzM66 |
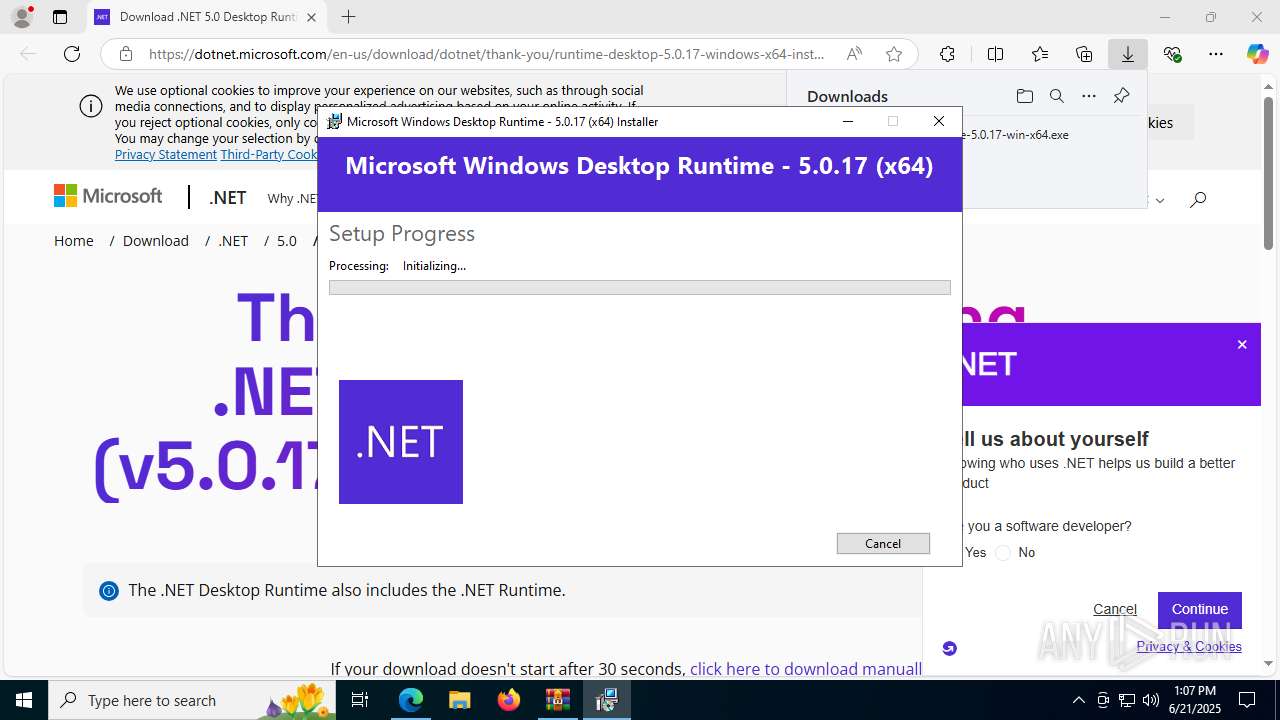
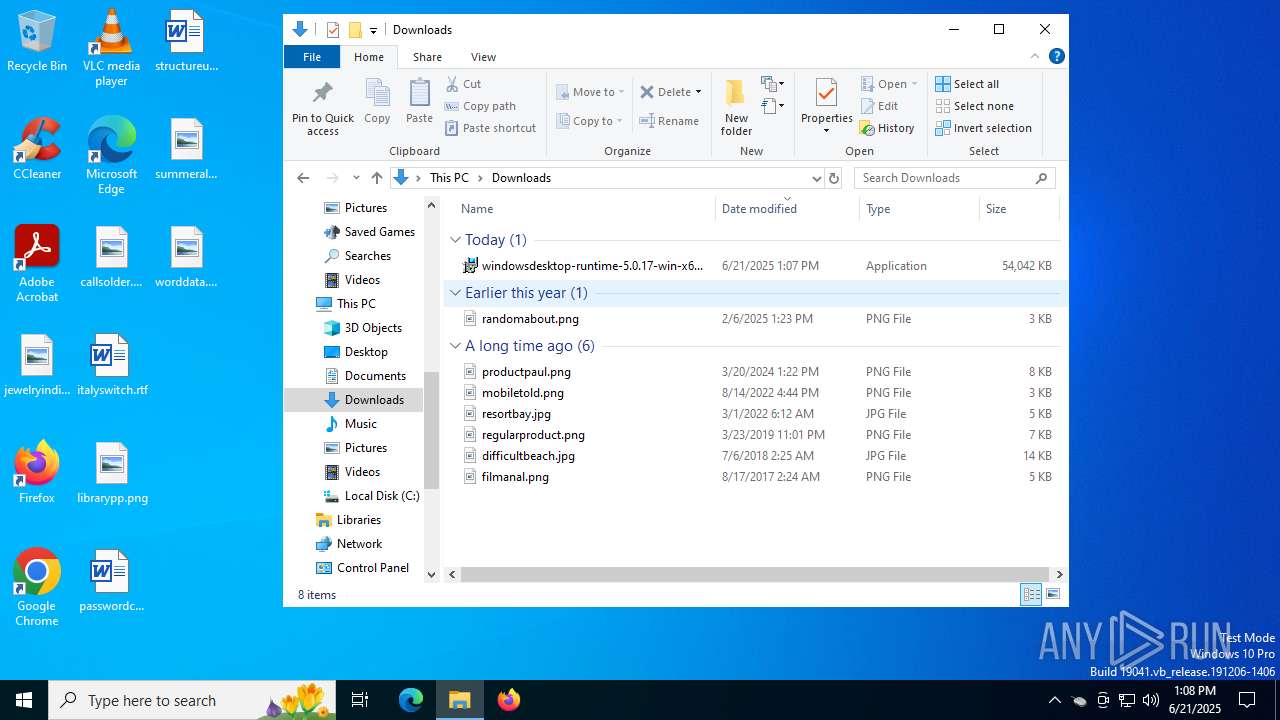
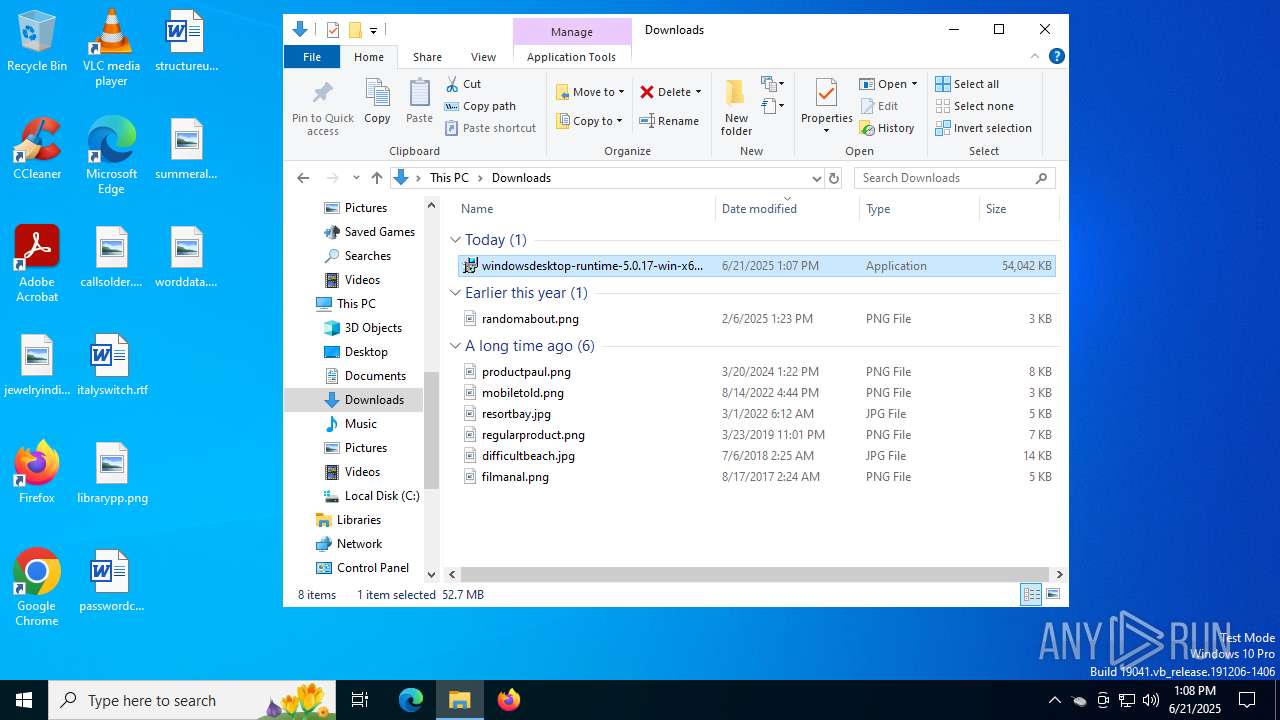
MALICIOUS
Generic archive extractor
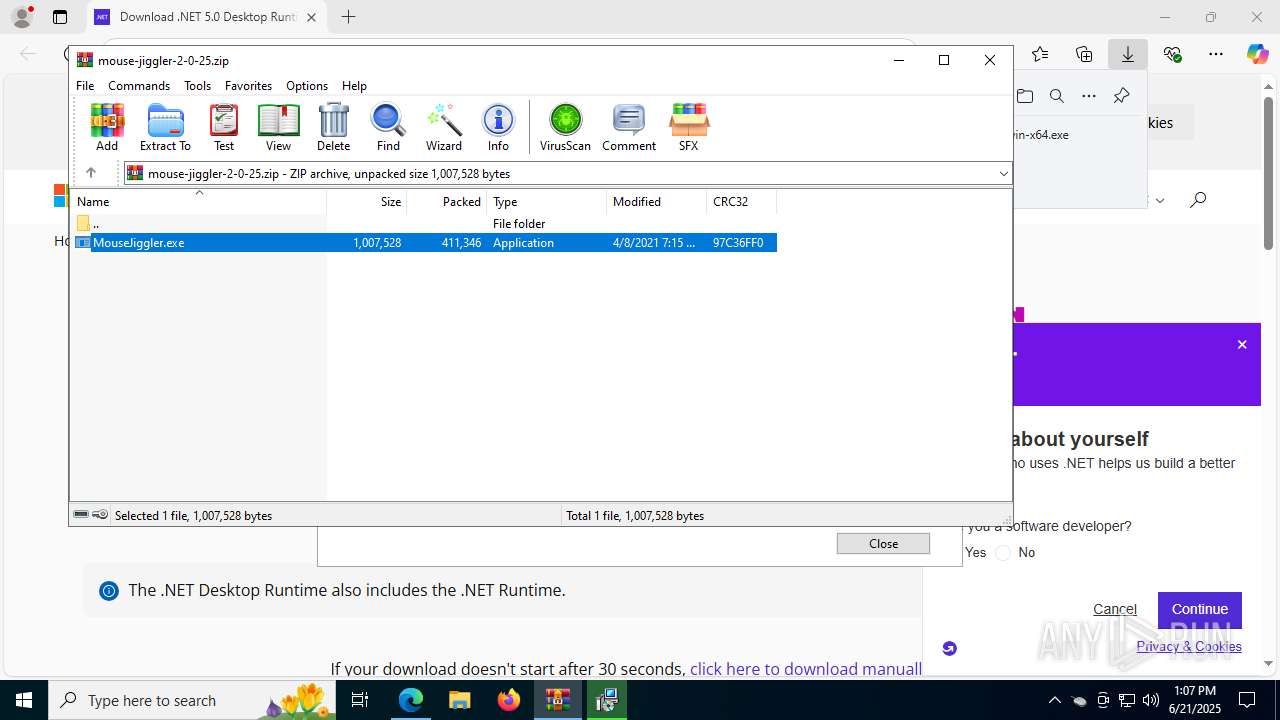
- WinRAR.exe (PID: 3752)
Changes the autorun value in the registry
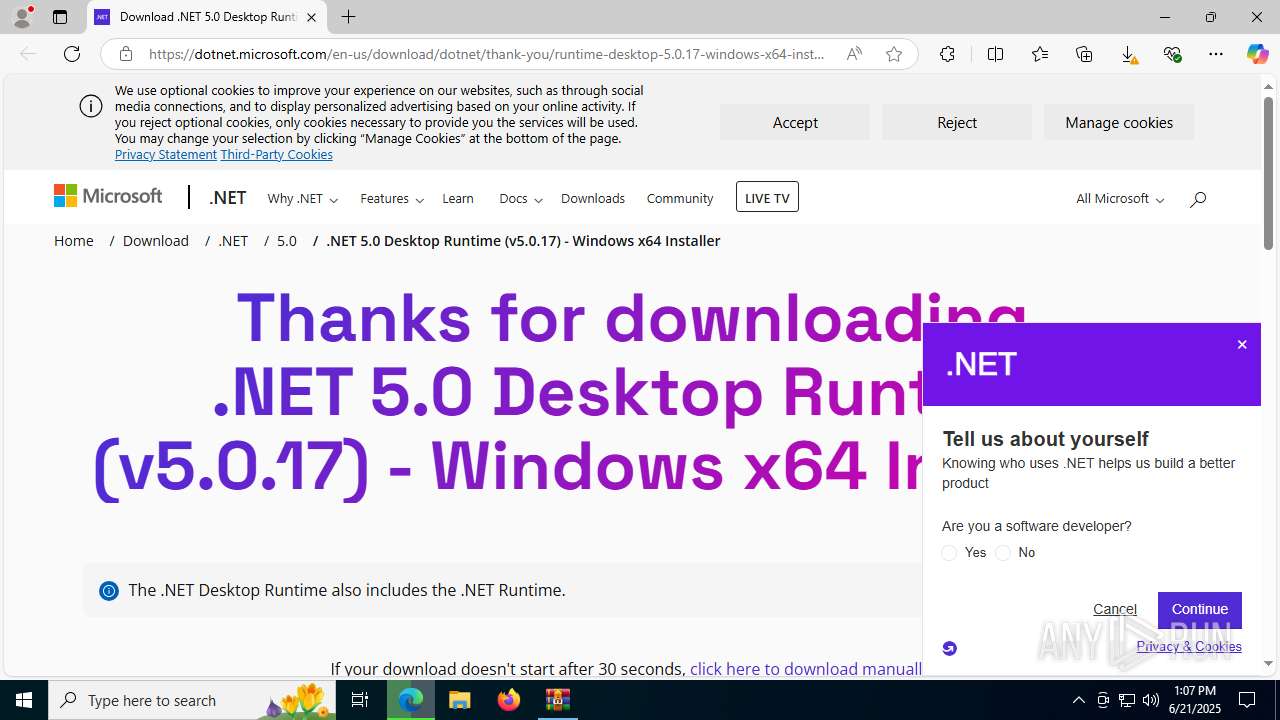
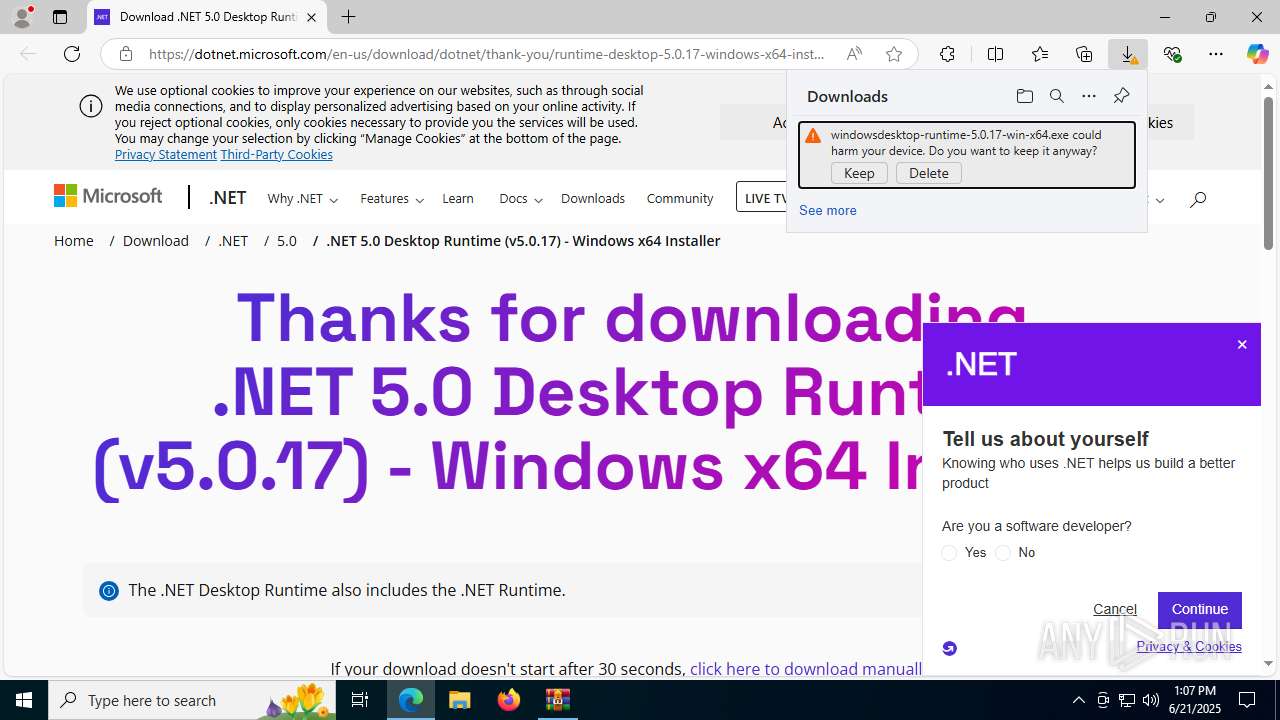
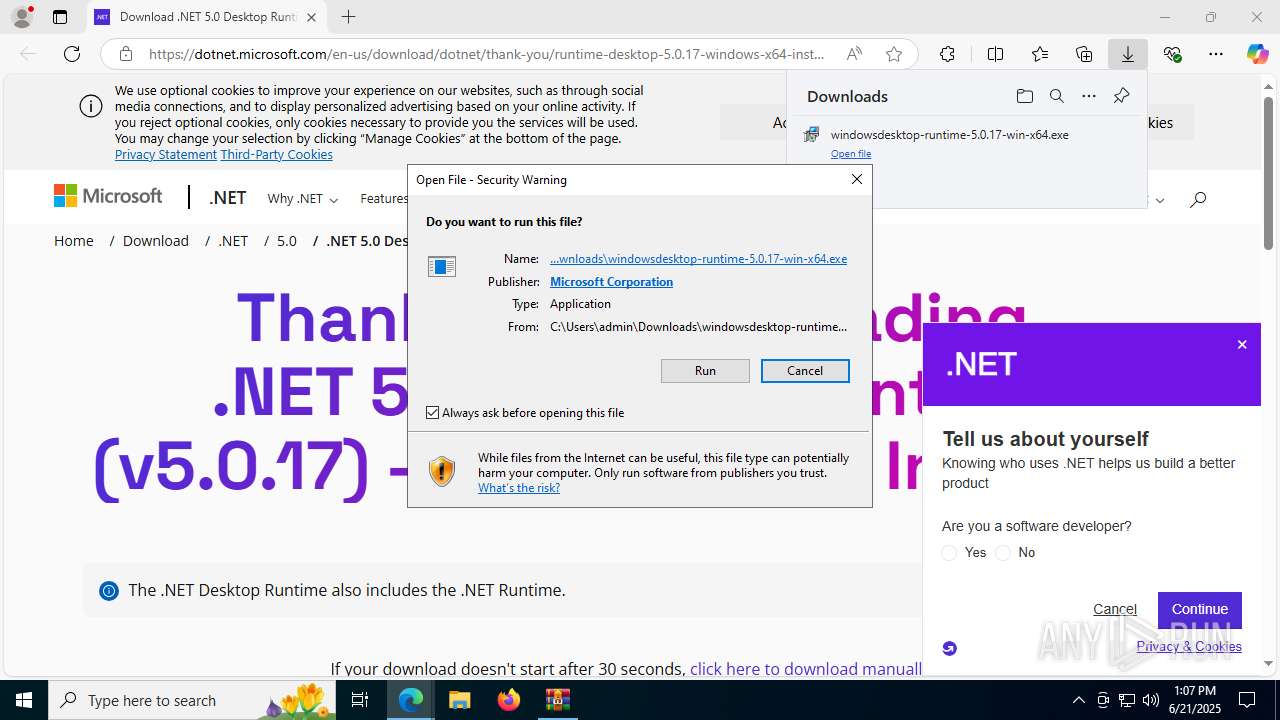
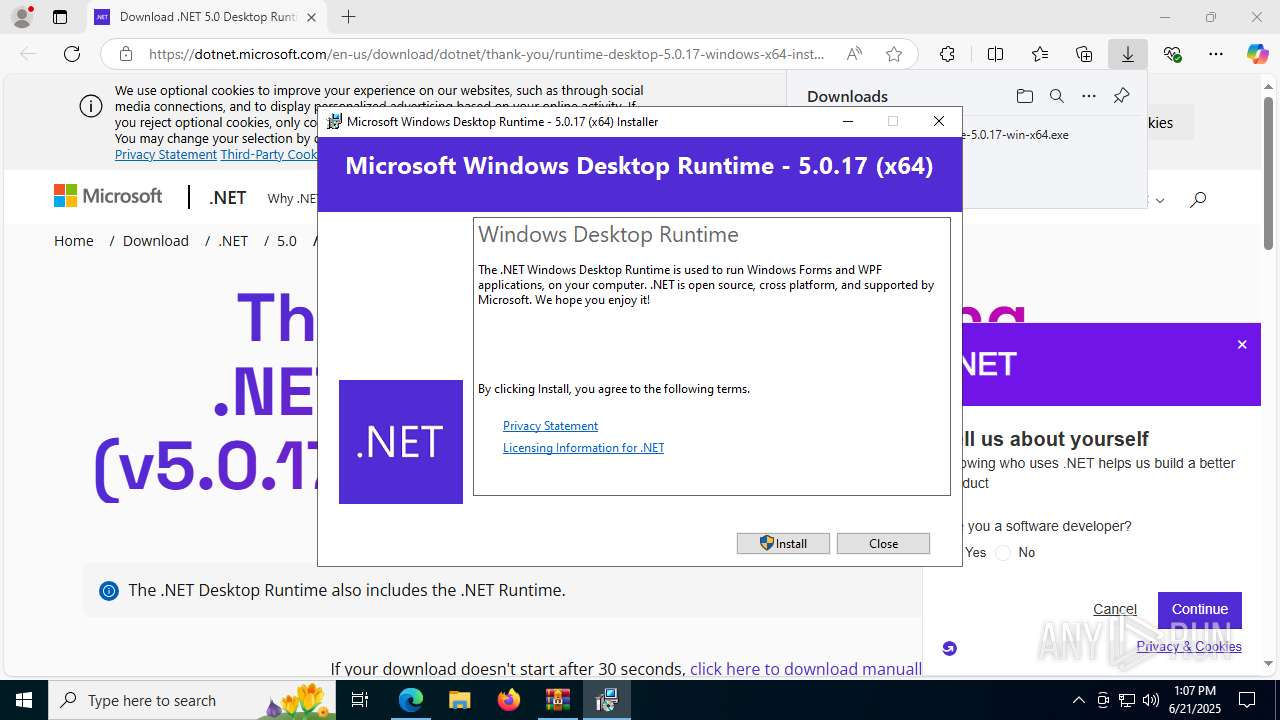
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
SUSPICIOUS
Reads security settings of Internet Explorer
- MouseJiggler.exe (PID: 4232)
- WinRAR.exe (PID: 3752)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
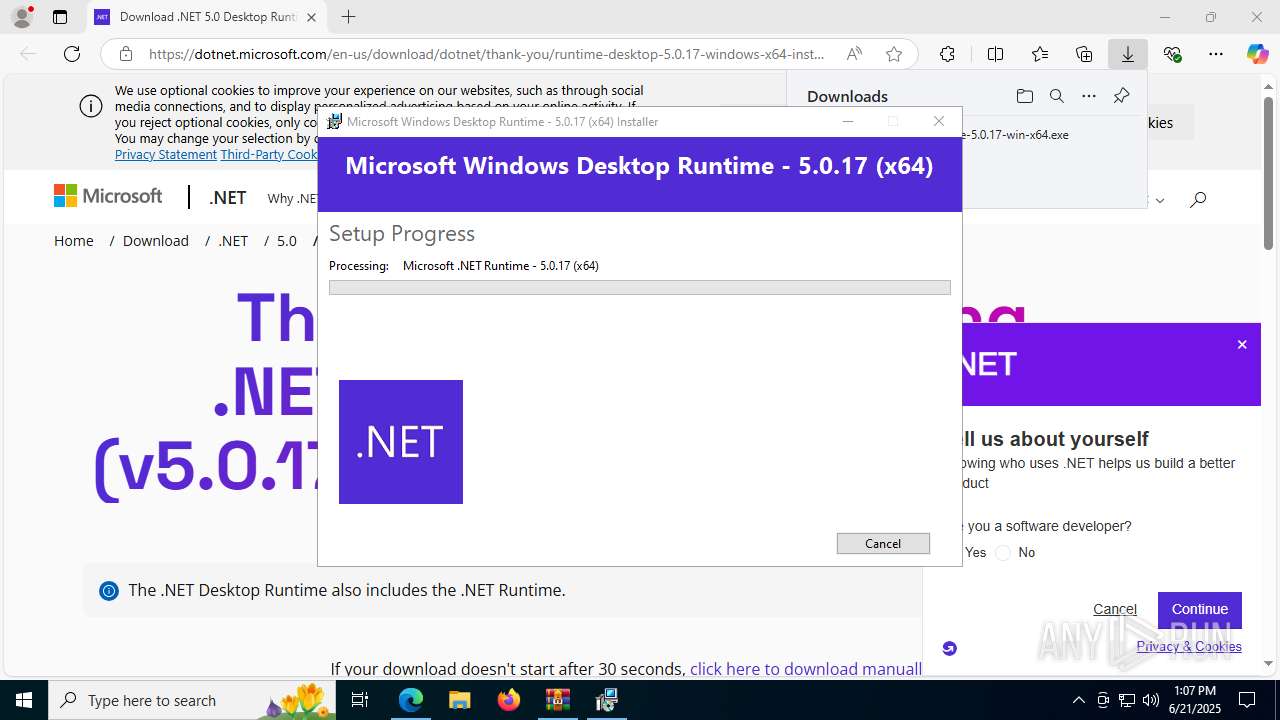
Executable content was dropped or overwritten
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 436)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
Process drops legitimate windows executable
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 436)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
- msiexec.exe (PID: 1712)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
Searches for installed software
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
Creates a software uninstall entry
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
Starts itself from another location
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
The process creates files with name similar to system file names
- msiexec.exe (PID: 1712)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1712)
The process drops C-runtime libraries
- msiexec.exe (PID: 1712)
INFO
Checks supported languages
- MouseJiggler.exe (PID: 4232)
- identity_helper.exe (PID: 7928)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 436)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
- msiexec.exe (PID: 1712)
- msiexec.exe (PID: 1472)
- msiexec.exe (PID: 7528)
- msiexec.exe (PID: 1872)
- msiexec.exe (PID: 2664)
- identity_helper.exe (PID: 2620)
- MouseJiggler.exe (PID: 7964)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3752)
- msedge.exe (PID: 3388)
- msiexec.exe (PID: 1712)
Reads the computer name
- MouseJiggler.exe (PID: 4232)
- identity_helper.exe (PID: 7928)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
- msiexec.exe (PID: 1712)
- msiexec.exe (PID: 1472)
- msiexec.exe (PID: 7528)
- msiexec.exe (PID: 2664)
- msiexec.exe (PID: 1872)
- identity_helper.exe (PID: 2620)
- MouseJiggler.exe (PID: 7964)
Application launched itself
- msedge.exe (PID: 3388)
- msedge.exe (PID: 6620)
Reads Environment values
- identity_helper.exe (PID: 7928)
- identity_helper.exe (PID: 2620)
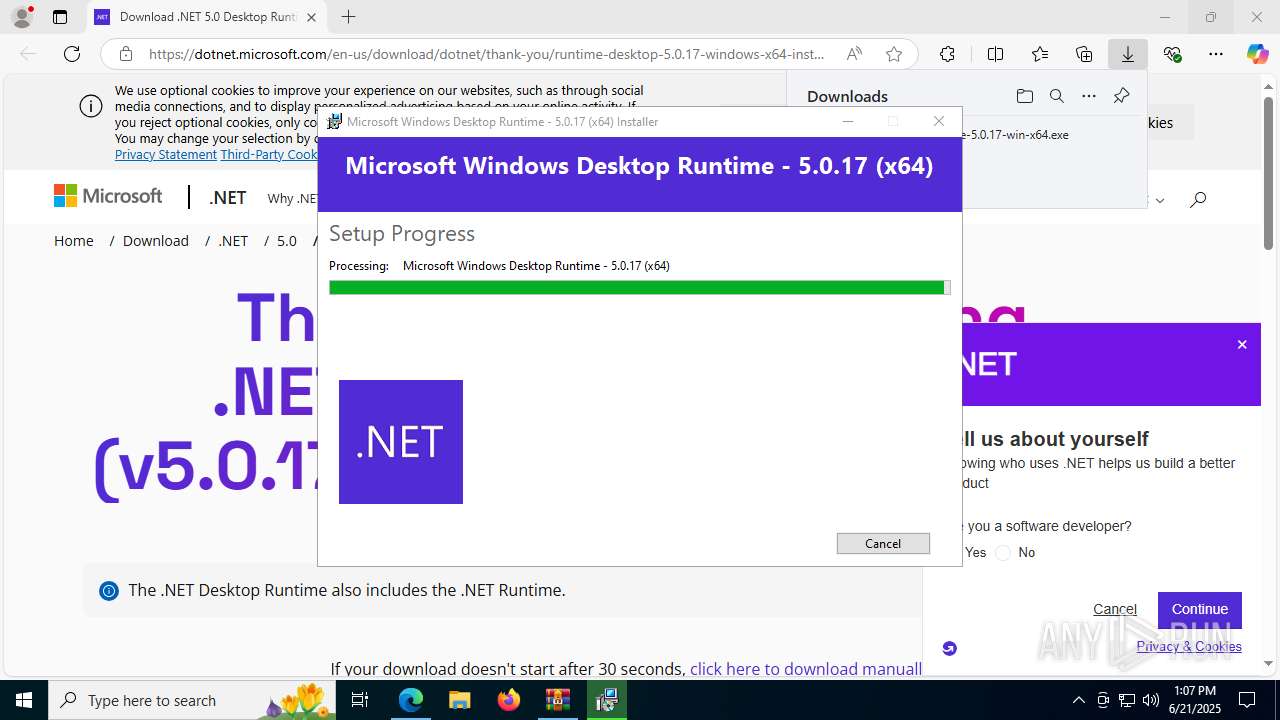
Create files in a temporary directory
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 436)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
- MouseJiggler.exe (PID: 7964)
The sample compiled with english language support
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 436)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
- msiexec.exe (PID: 1712)
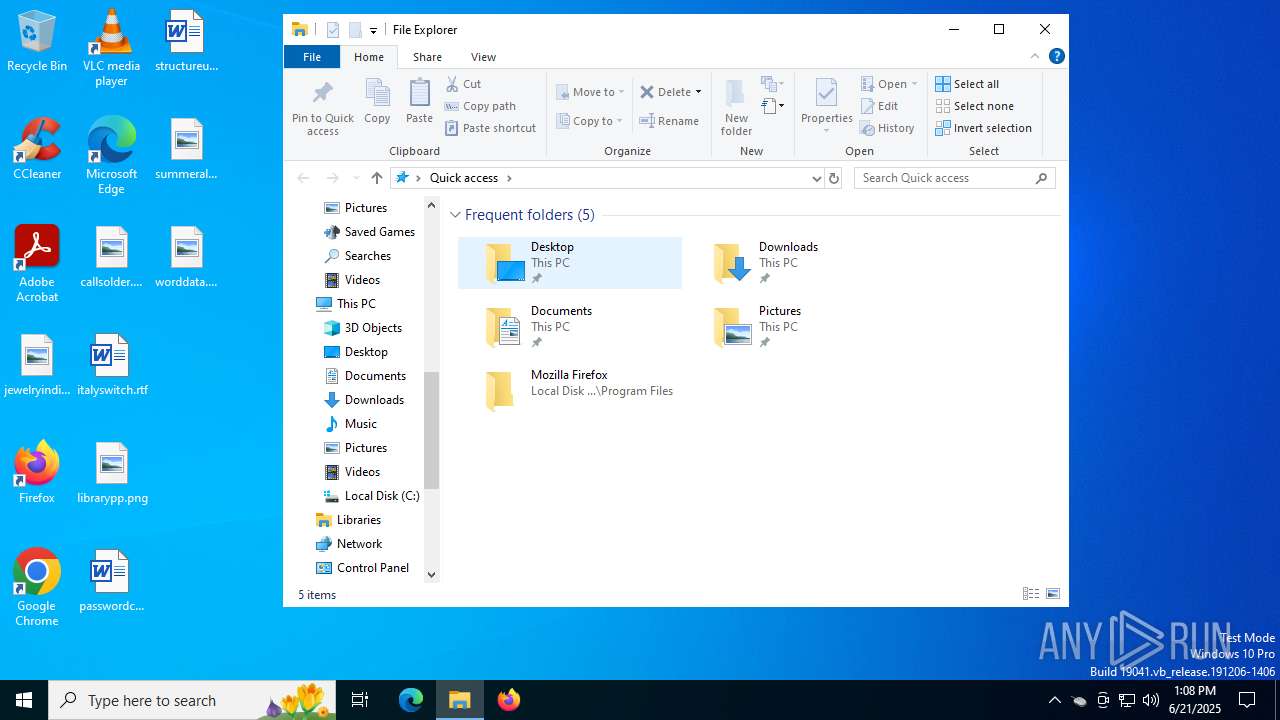
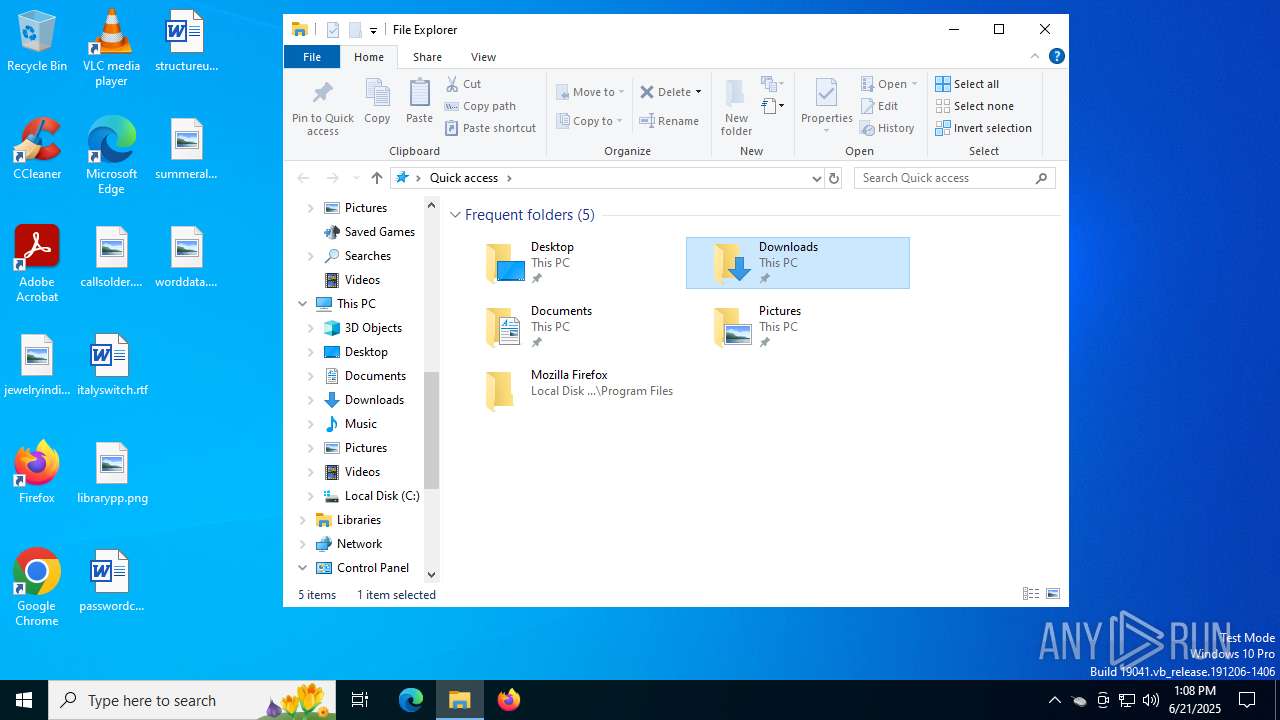
Creates files in the program directory
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
- MouseJiggler.exe (PID: 7964)
Process checks computer location settings
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 5008)
Launching a file from a Registry key
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
Reads the machine GUID from the registry
- windowsdesktop-runtime-5.0.17-win-x64.exe (PID: 7872)
- msiexec.exe (PID: 1712)
Reads the software policy settings
- msiexec.exe (PID: 1712)
Creates a software uninstall entry
- msiexec.exe (PID: 1712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
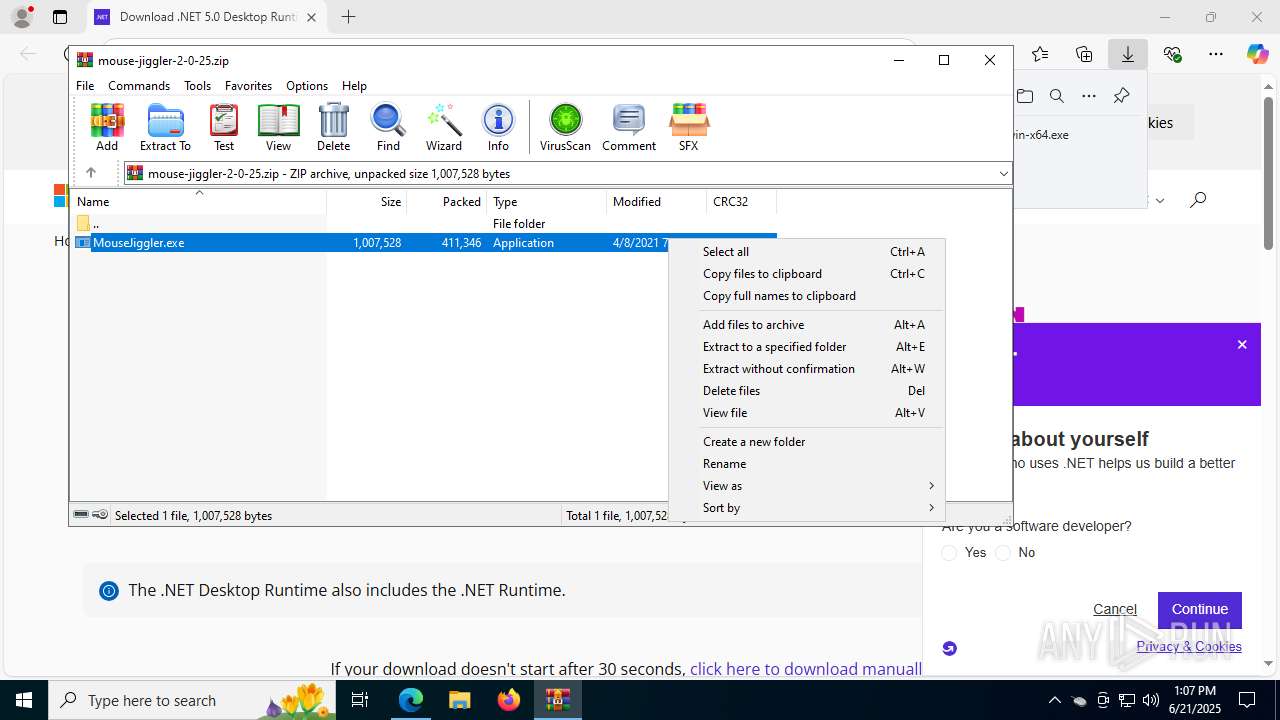
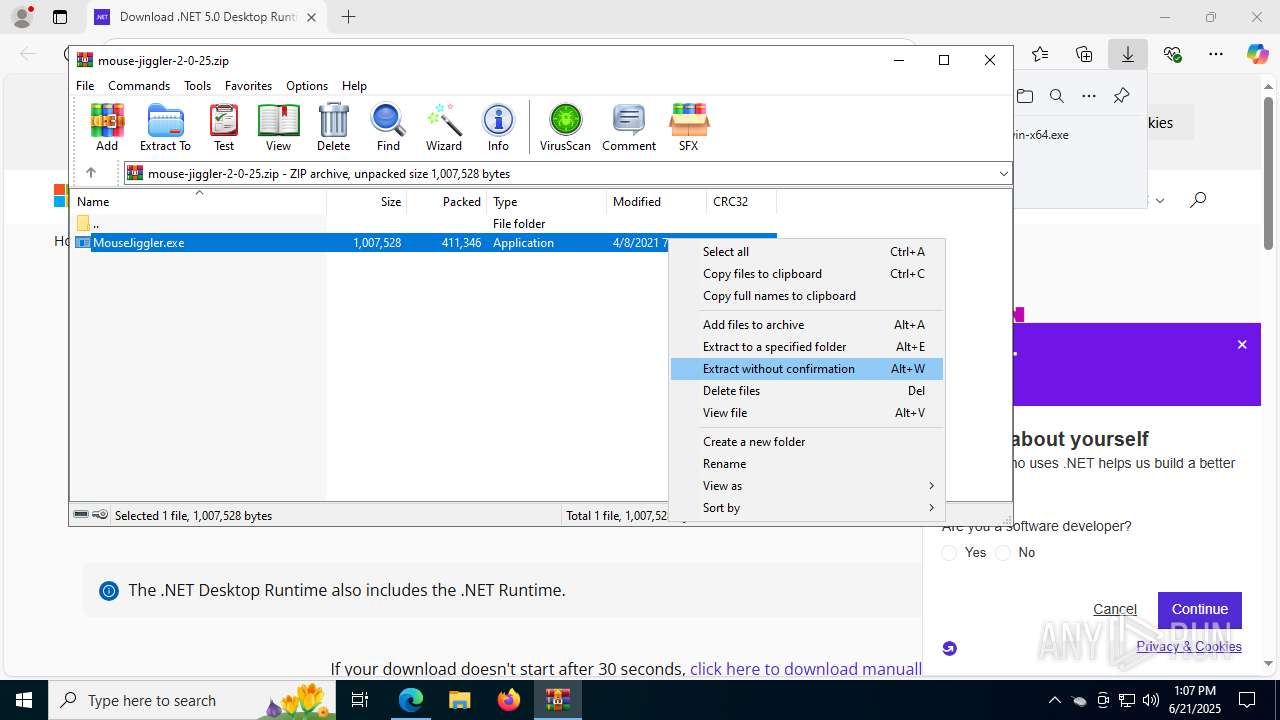
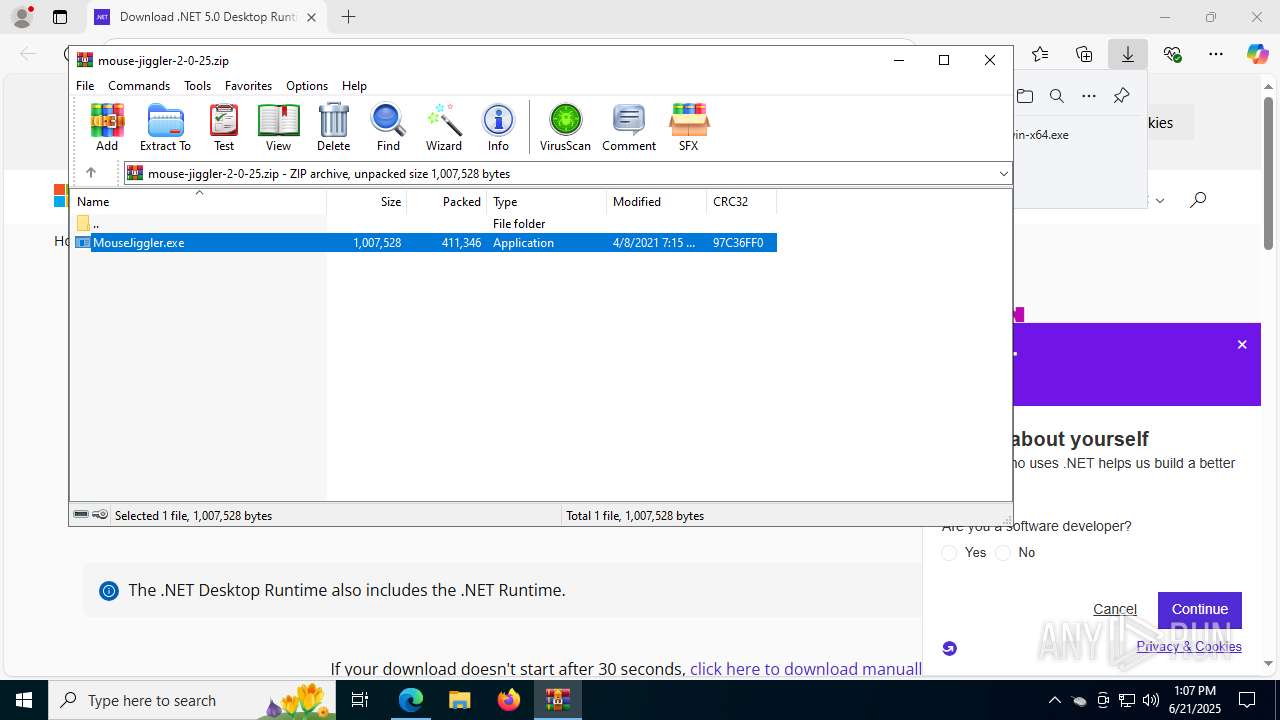
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:04:08 19:15:50 |
| ZipCRC: | 0x97c36ff0 |
| ZipCompressedSize: | 411346 |
| ZipUncompressedSize: | 1007528 |
| ZipFileName: | MouseJiggler.exe |
Total processes
188
Monitored processes
48
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
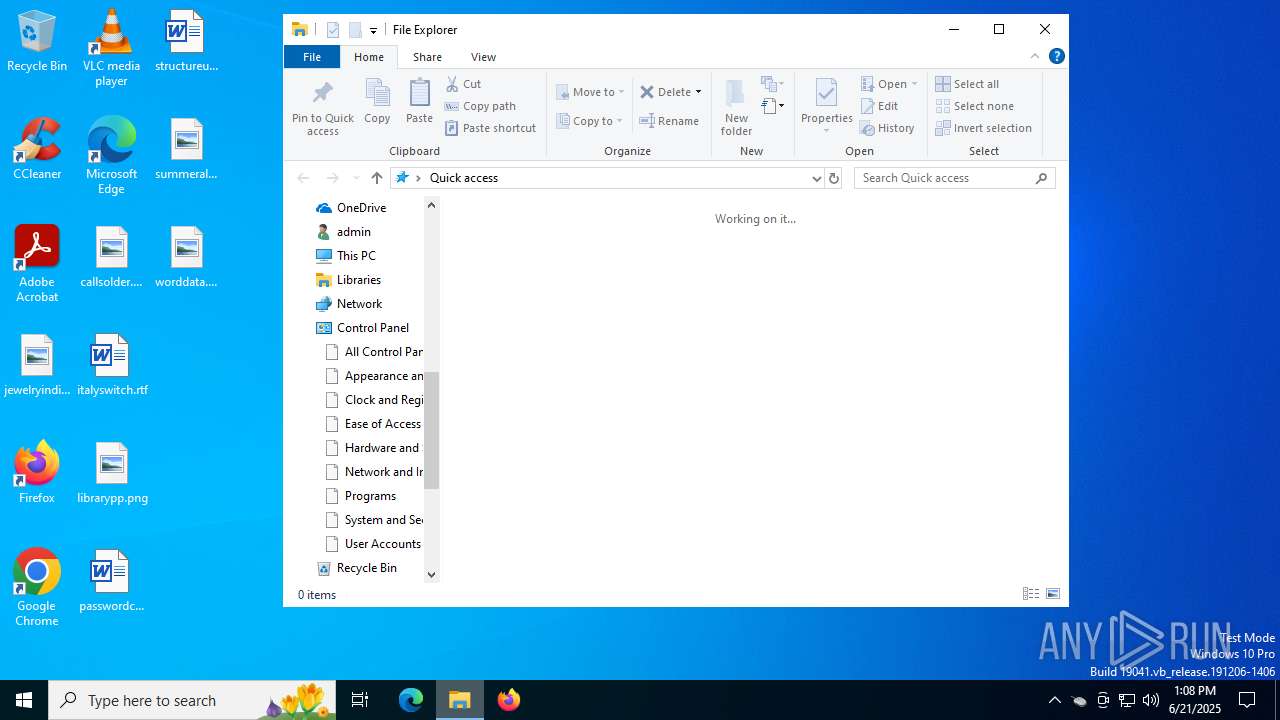
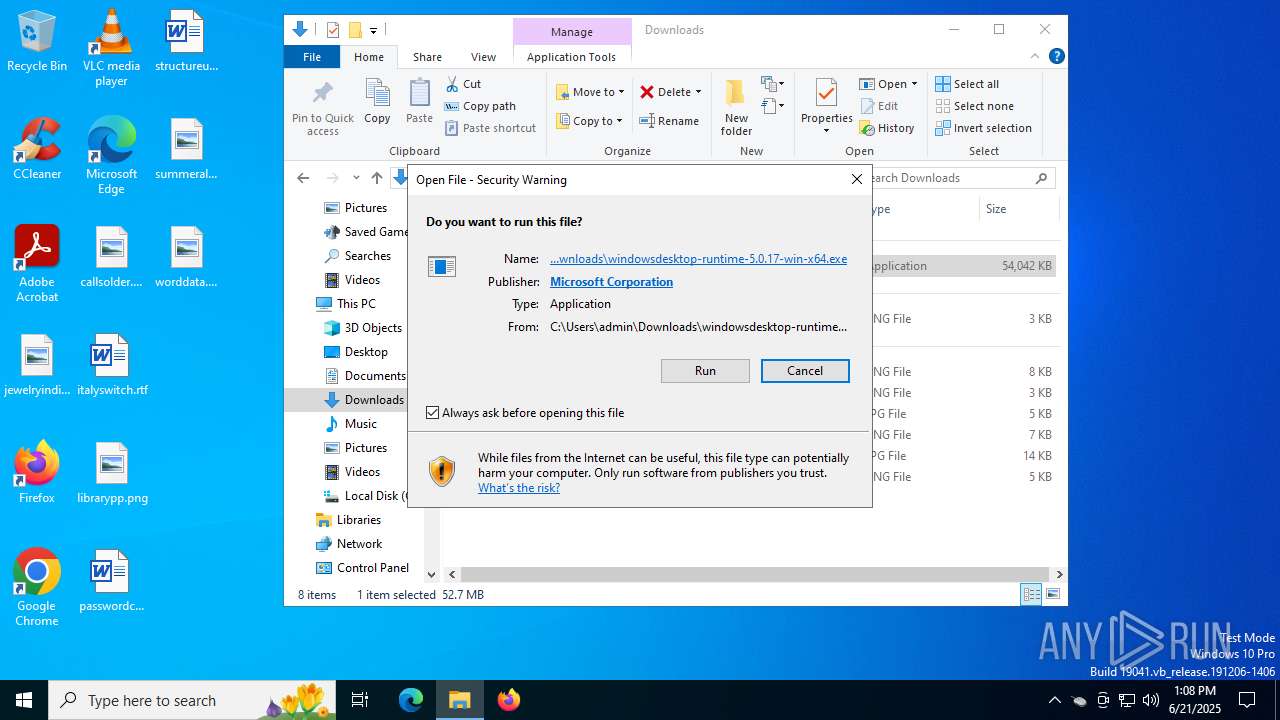
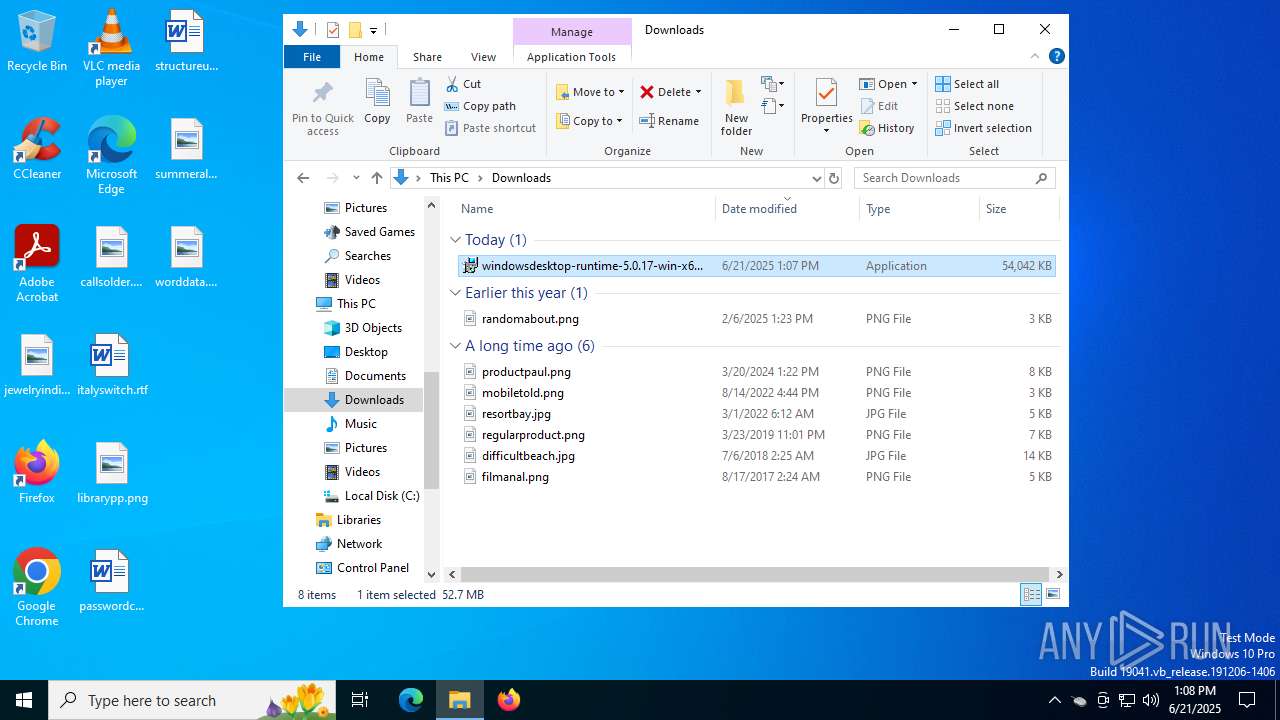
| 436 | "C:\Users\admin\Downloads\windowsdesktop-runtime-5.0.17-win-x64.exe" | C:\Users\admin\Downloads\windowsdesktop-runtime-5.0.17-win-x64.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Desktop Runtime - 5.0.17 (x64) Exit code: 0 Version: 5.0.17.31219 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2100,i,16720786357132396584,12308751542531329785,262144 --variations-seed-version --mojo-platform-channel-handle=2272 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1380 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4080,i,16720786357132396584,12308751542531329785,262144 --variations-seed-version --mojo-platform-channel-handle=4100 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3632,i,16720786357132396584,12308751542531329785,262144 --variations-seed-version --mojo-platform-channel-handle=3940 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1472 | C:\Windows\syswow64\MsiExec.exe -Embedding E45CA4995D47F73F74A1412C4519E060 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1872 | C:\Windows\syswow64\MsiExec.exe -Embedding ED4B968EA20C79846E7474A197DCA57B | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2368 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4792,i,13705767318870336888,9651696996479523475,262144 --variations-seed-version --mojo-platform-channel-handle=4848 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2620 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4792,i,13705767318870336888,9651696996479523475,262144 --variations-seed-version --mojo-platform-channel-handle=4848 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2664 | C:\Windows\syswow64\MsiExec.exe -Embedding A13B3D6D4C42045A1DD7CE42B3D19D5C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 572
Read events
24 570
Write events
957
Delete events
45
Modification events
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\mouse-jiggler-2-0-25.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
539
Suspicious files
217
Text files
96
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF178155.TMP | — | |
MD5:— | SHA256:— | |||
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF178155.TMP | — | |
MD5:— | SHA256:— | |||
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF178165.TMP | — | |
MD5:— | SHA256:— | |||
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF178165.TMP | — | |
MD5:— | SHA256:— | |||
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF178165.TMP | — | |
MD5:— | SHA256:— | |||
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1781a3.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
81
DNS requests
83
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3628 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:oMgAXmVaNiXmMm8bmwGA1NQztik_zuERF9-z4cau2-s&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2288 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3388 | msedge.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3388 | msedge.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
7840 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7840 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5908 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2288 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2288 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3628 | msedge.exe | 52.123.243.201:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
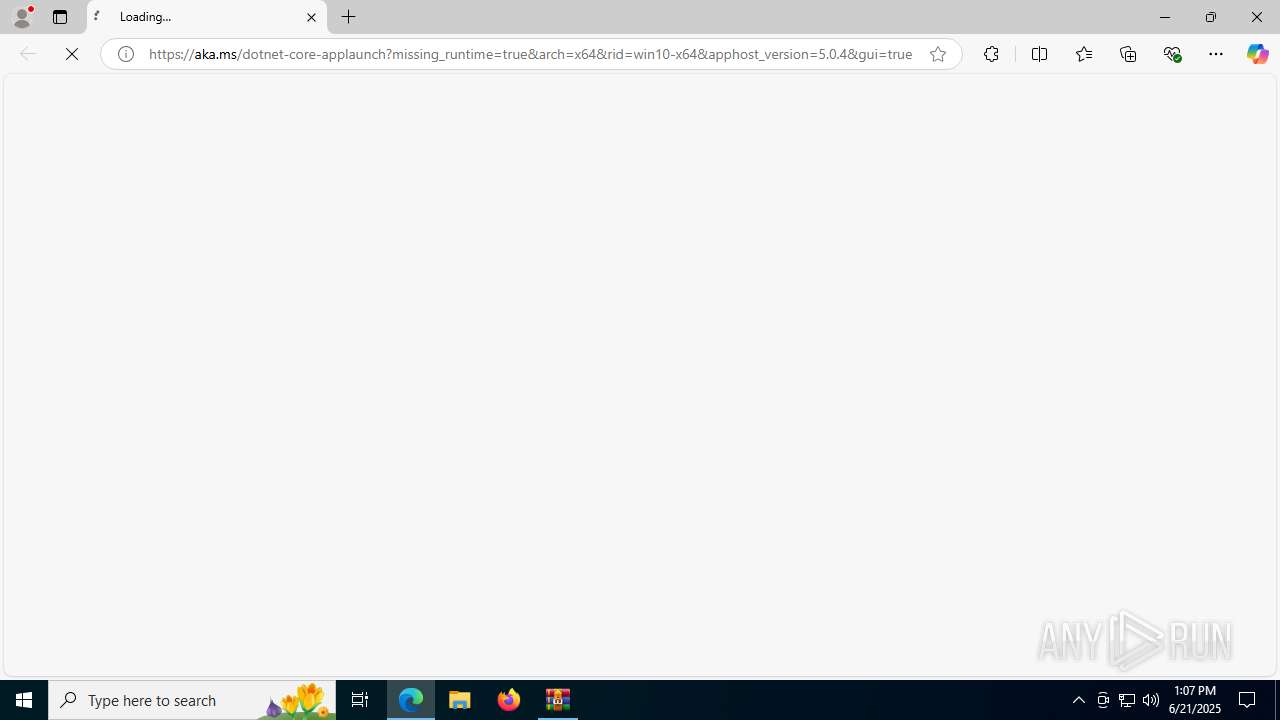
3628 | msedge.exe | 104.119.110.121:443 | aka.ms | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
aka.ms |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
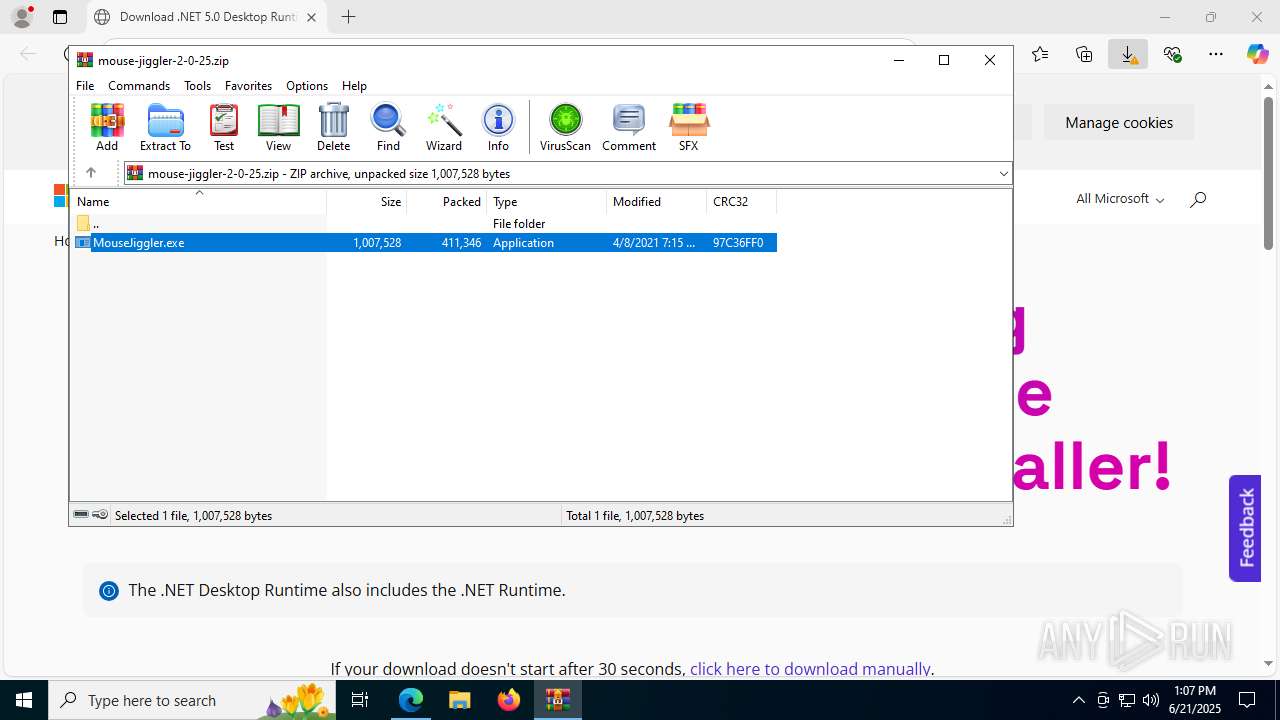
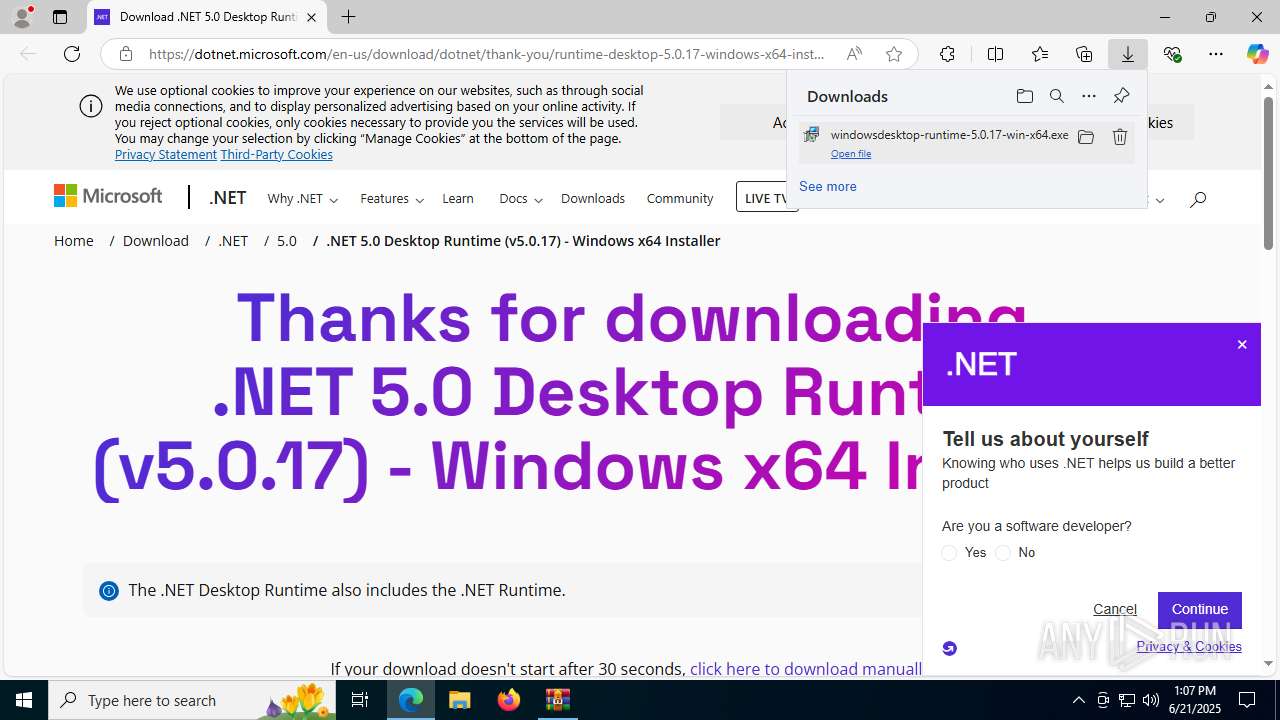
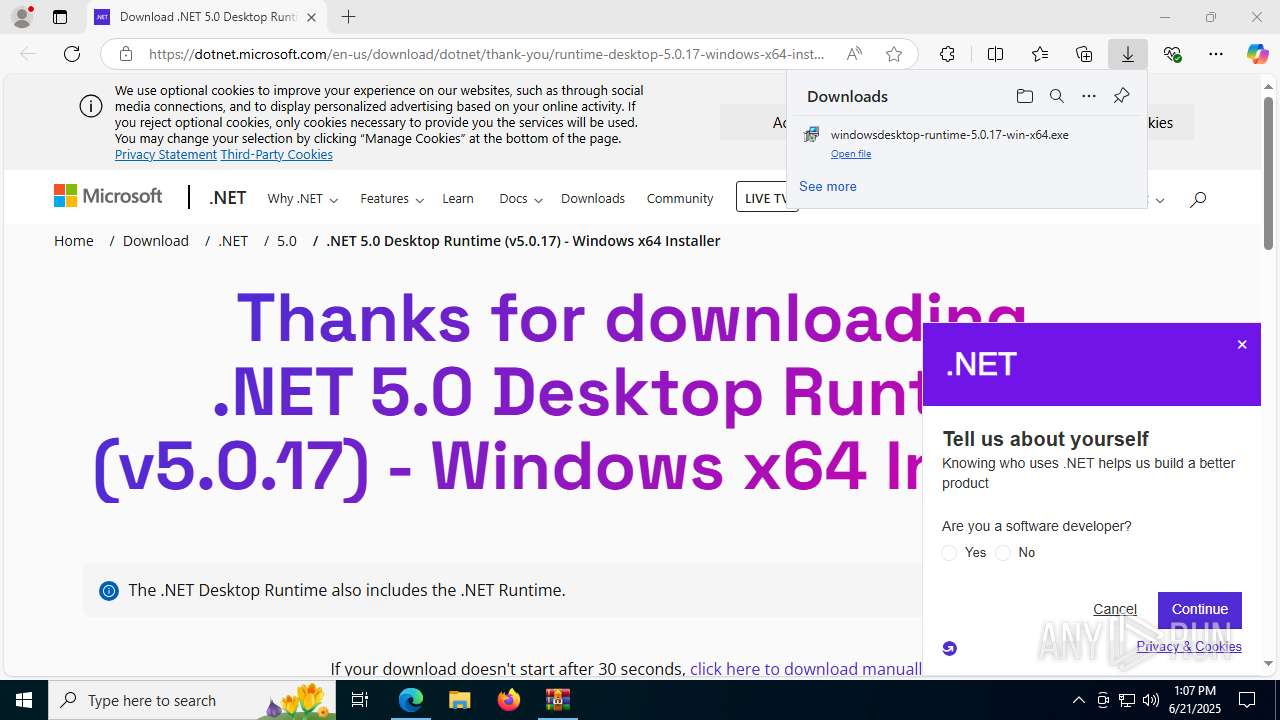
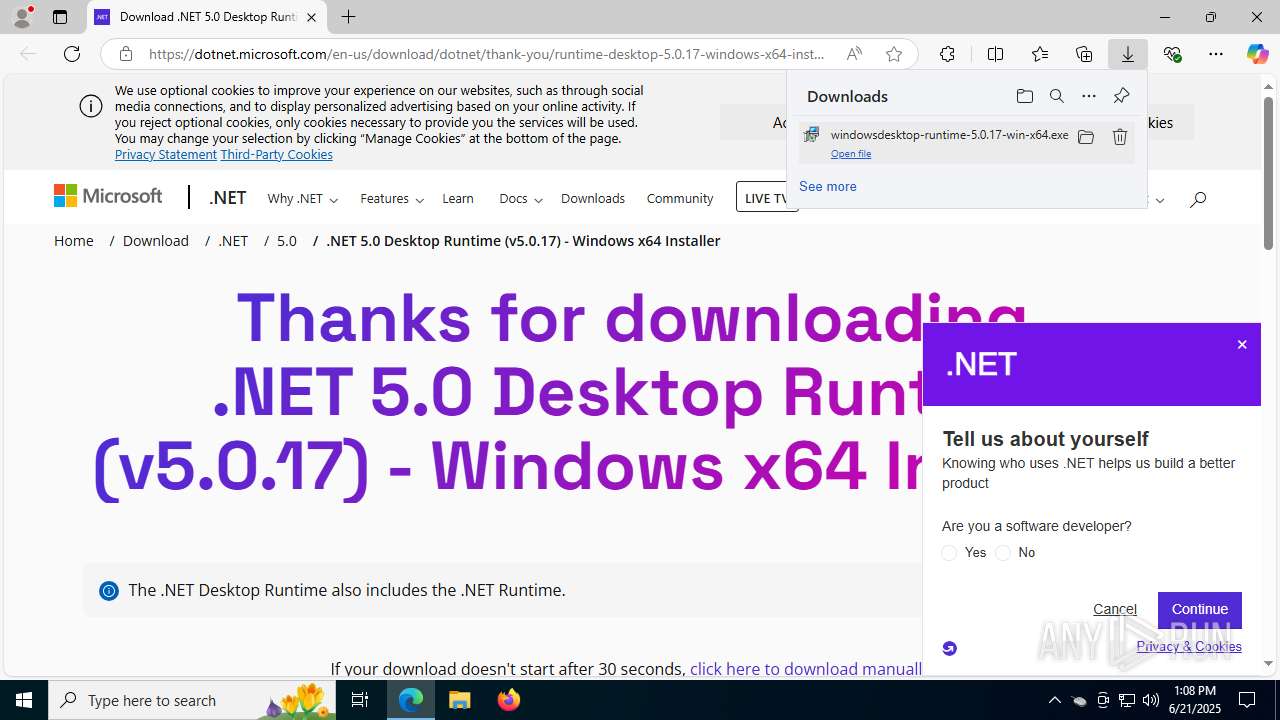
dotnet.microsoft.com |
| whitelisted |
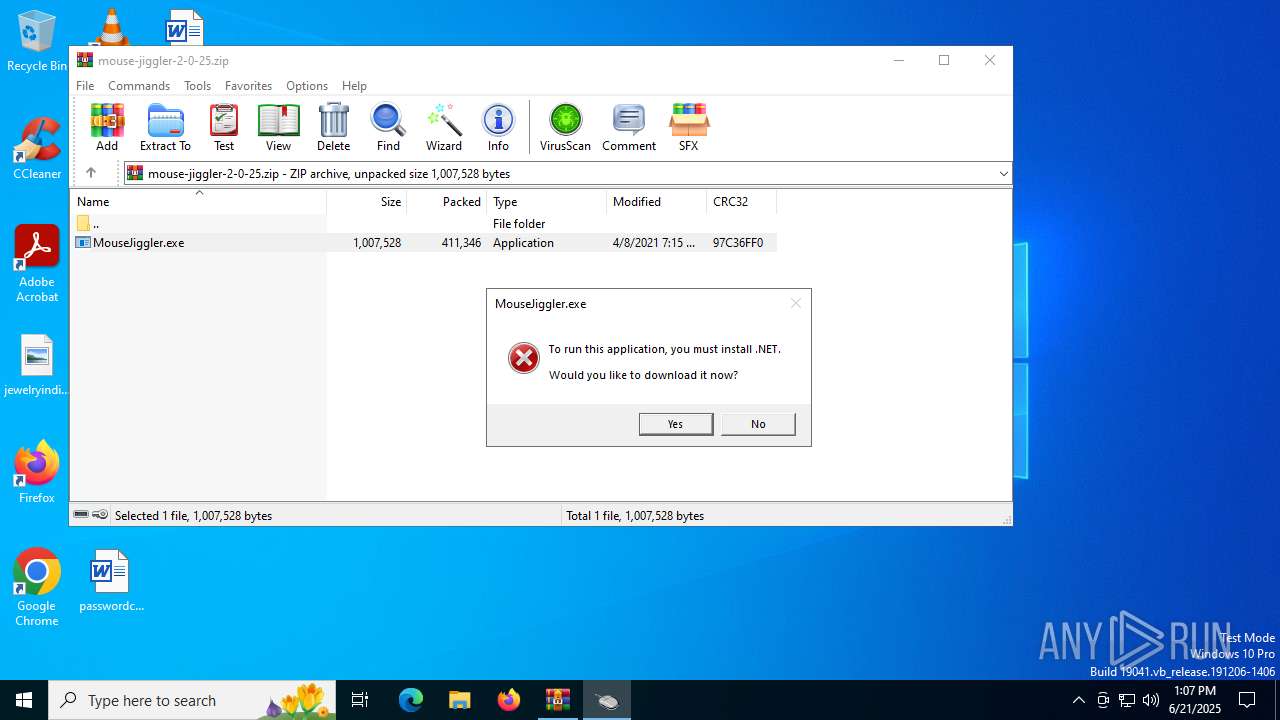
Threats
Process | Message |
|---|---|
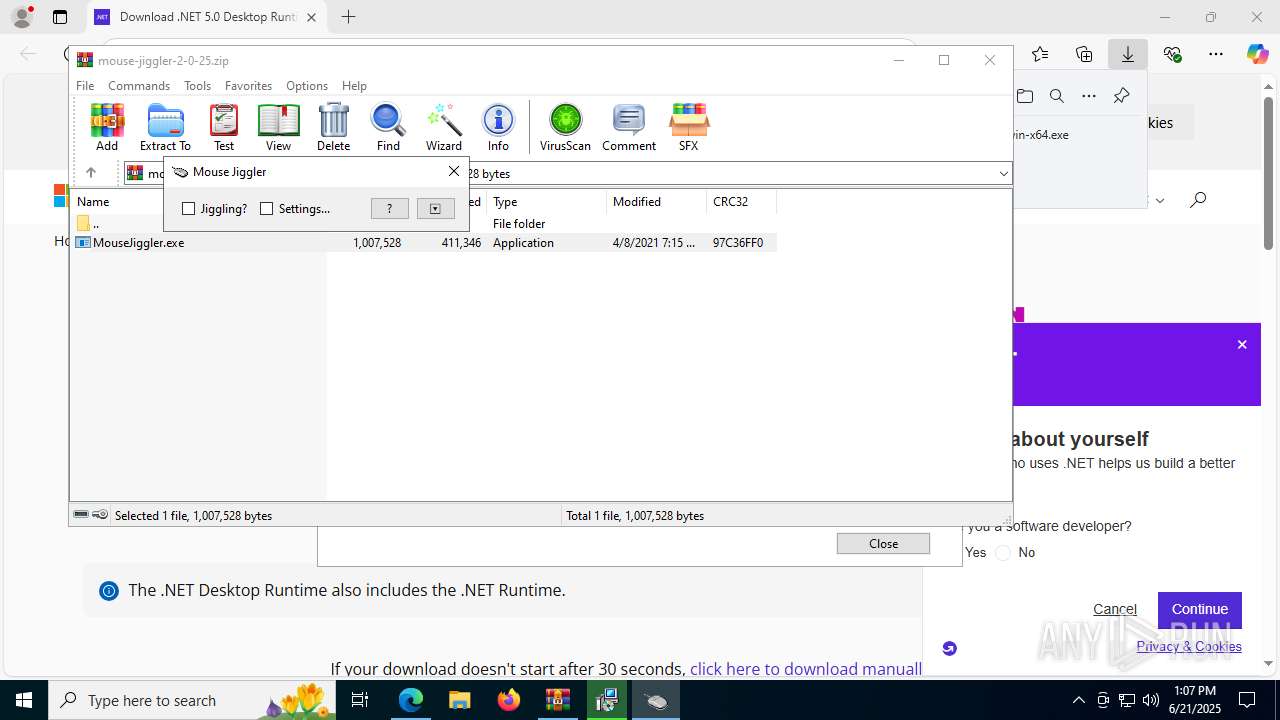
MouseJiggler.exe | A fatal error occurred. The required library hostfxr.dll could not be found.
If this is a self-contained application, that library should exist in [C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.3016\].
If this is a framework-dependent application, install the runtime in the global location [C:\Program Files\dotnet] or use the DOTNET_ROOT environment variable to specify the runtime location or register the runtime location in [HKLM\SOFTWARE\dotnet\Setup\InstalledVersions\x64\InstallLocation]. |
MouseJiggler.exe | The .NET runtime can be found at: |
MouseJiggler.exe | - https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win10-x64&apphost_version=5.0.4 |