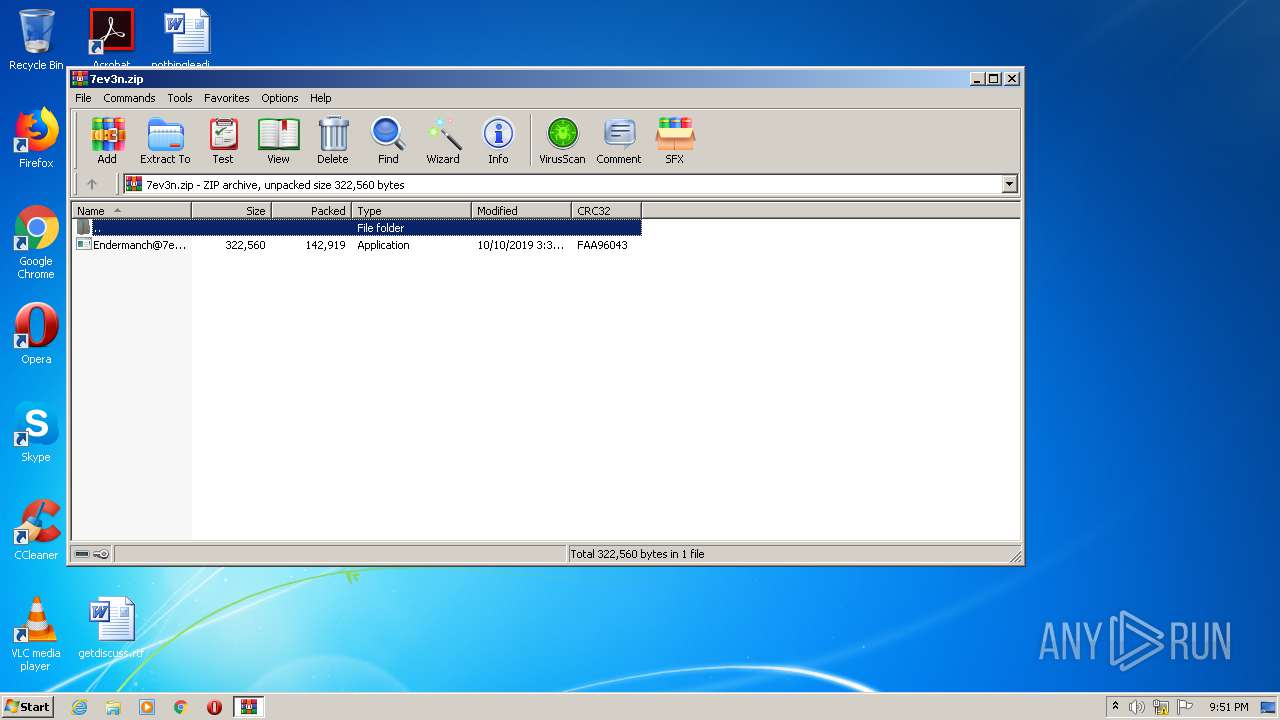
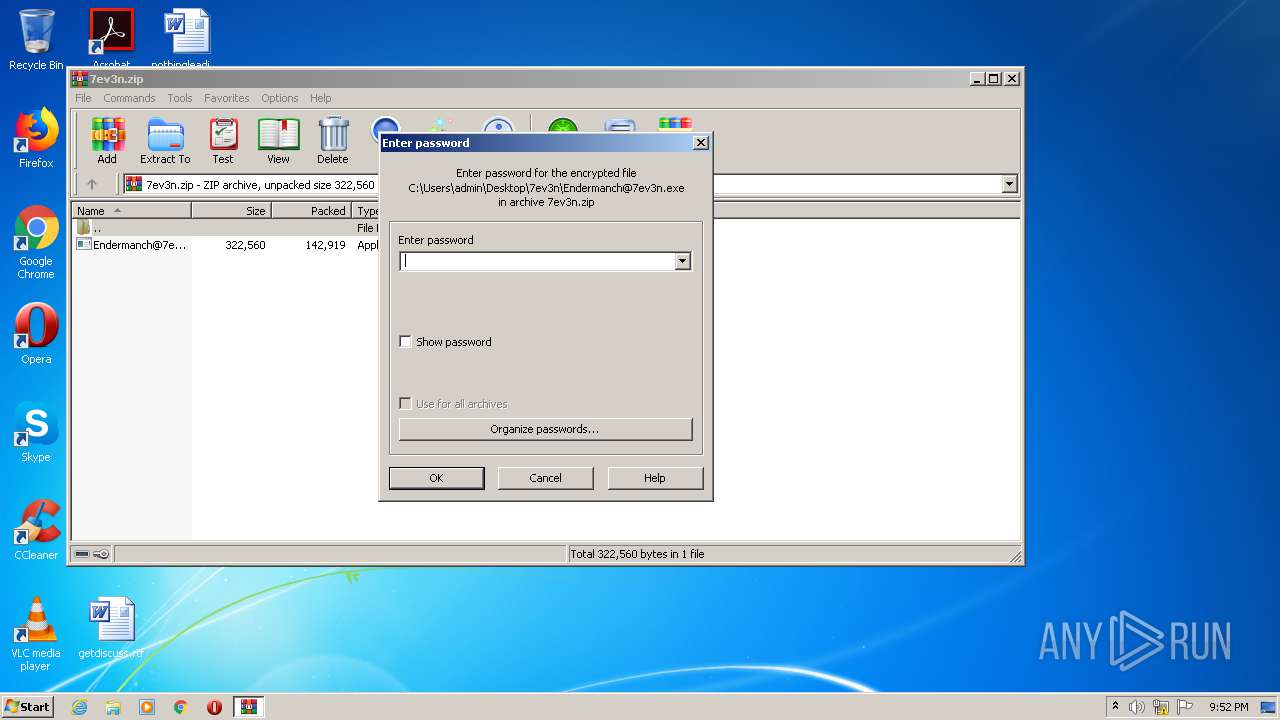
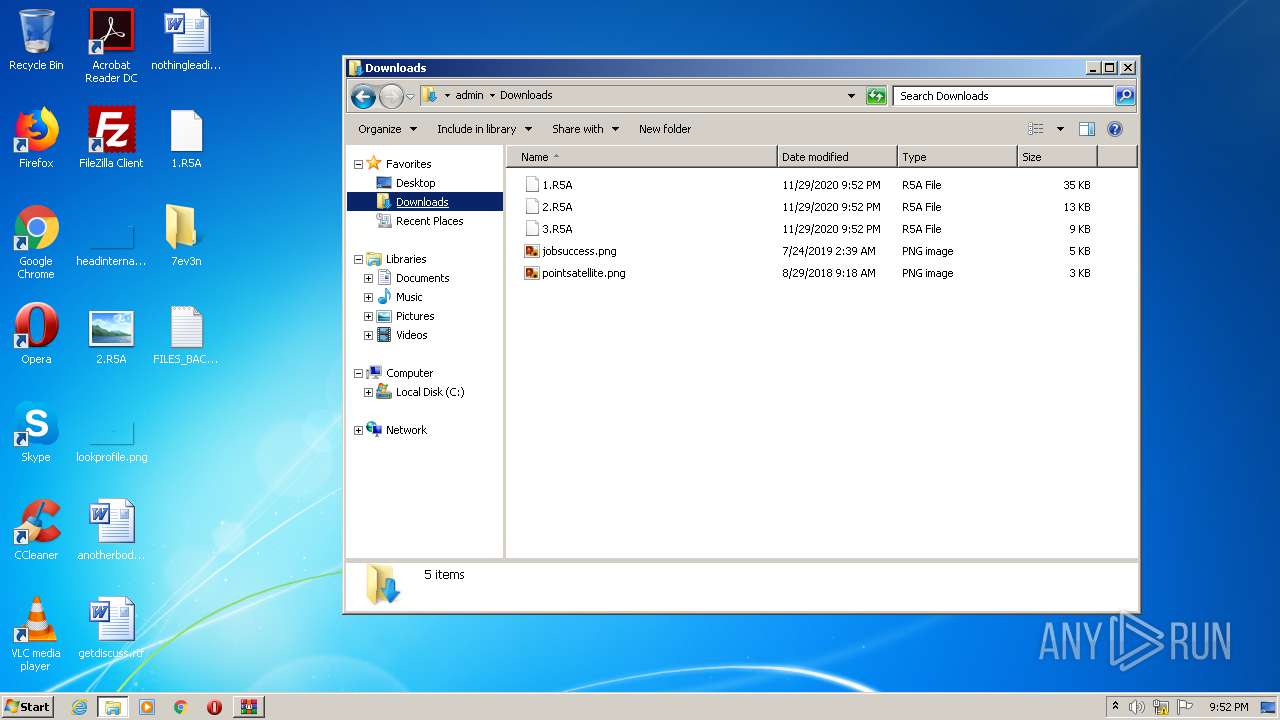
| download: | 7ev3n.zip |
| Full analysis: | https://app.any.run/tasks/cca6e283-8890-40ee-811c-a266f29d954a |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 21:50:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C6F3D62C4FB57212172D358231E027BC |
| SHA1: | 11276D7A49093A51F04667975E718BB15BC1289B |
| SHA256: | EA60123EC363610C8CFCD0AD5F0AB2832934AF69A3C715020A09E6D907691D4C |
| SSDEEP: | 3072:4JB/Rmo5VYvT/dQVB3gUm1lnjhvBzXL0x2vkRFd+OqpzdyG6osCvS8LS7:CF5VYDmVBhm1lnjhvBrLqHDydyLCqd |
MALICIOUS
Application was dropped or rewritten from another process
- Endermanch@7ev3n.exe (PID: 1088)
- system.exe (PID: 1892)
- uac.exe (PID: 3500)
- winsat.exe (PID: 2960)
- winsat.exe (PID: 3332)
- system.exe (PID: 3884)
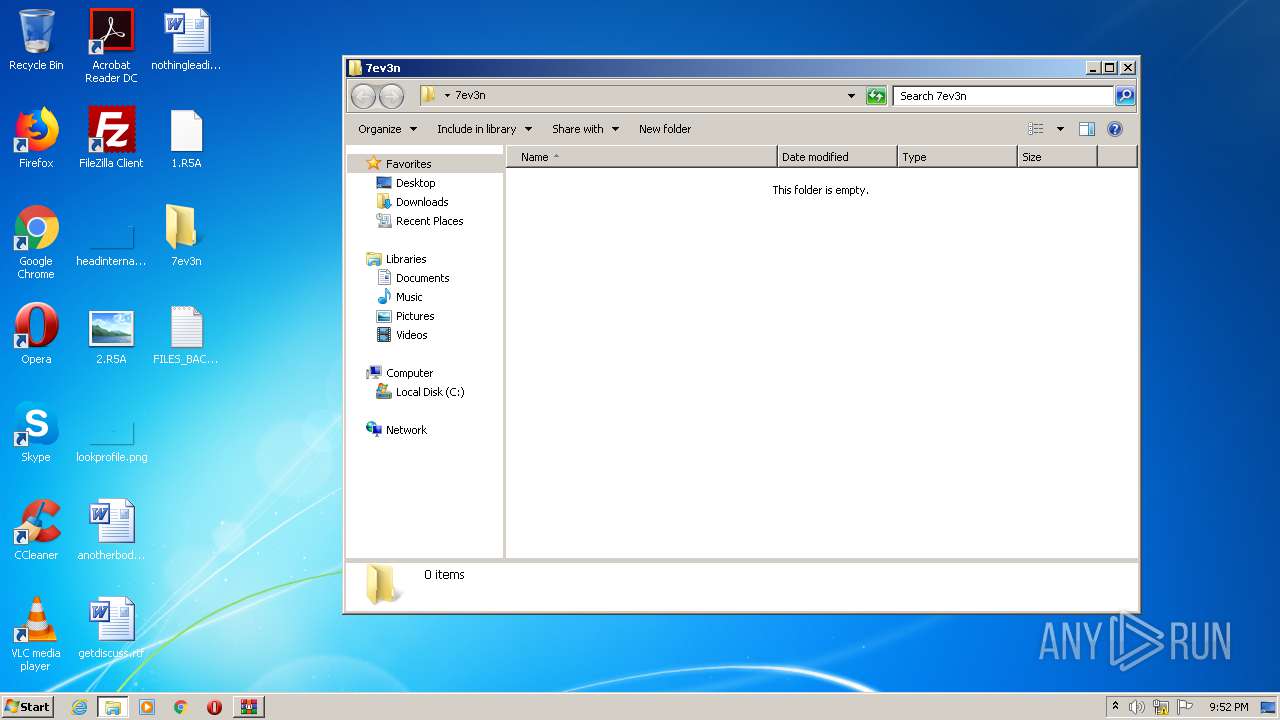
Drops executable file immediately after starts
- Endermanch@7ev3n.exe (PID: 1088)
- system.exe (PID: 1892)
- uac.exe (PID: 3500)
- wusa.exe (PID: 3296)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1188)
Loads dropped or rewritten executable
- winsat.exe (PID: 3332)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 3580)
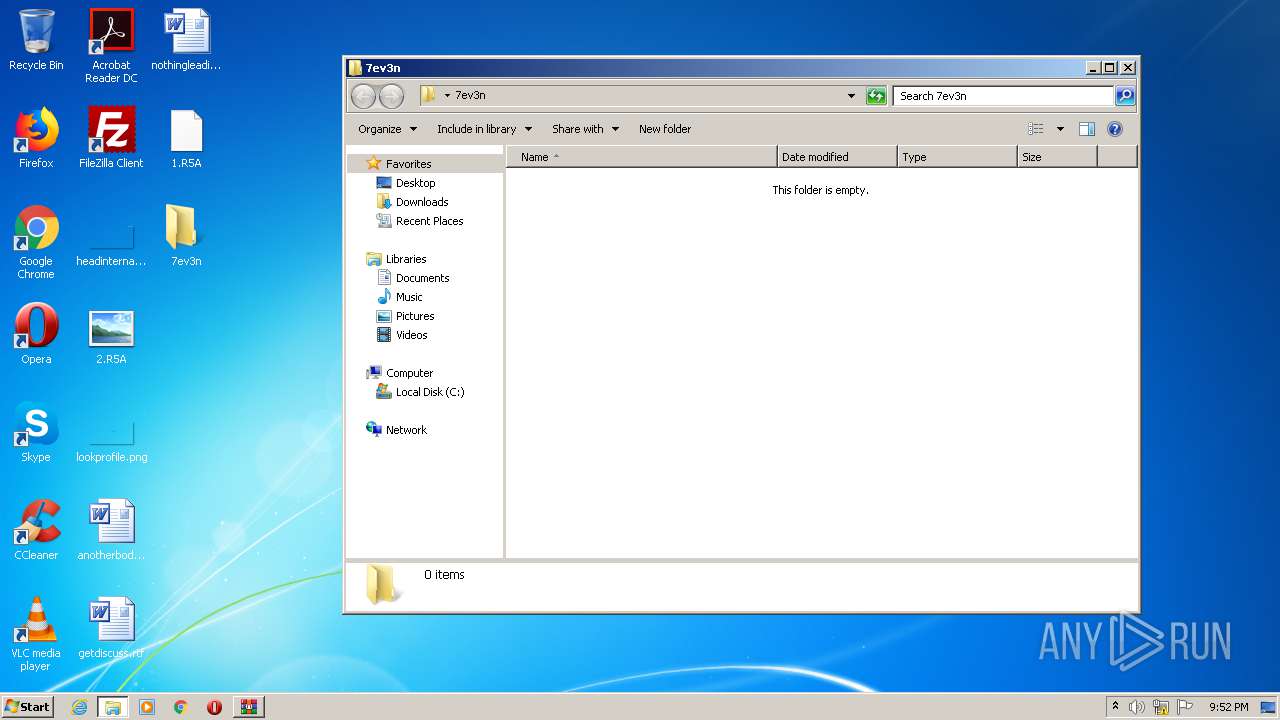
Changes the login/logoff helper path in the registry
- reg.exe (PID: 1020)
Changes the autorun value in the registry
- reg.exe (PID: 2924)
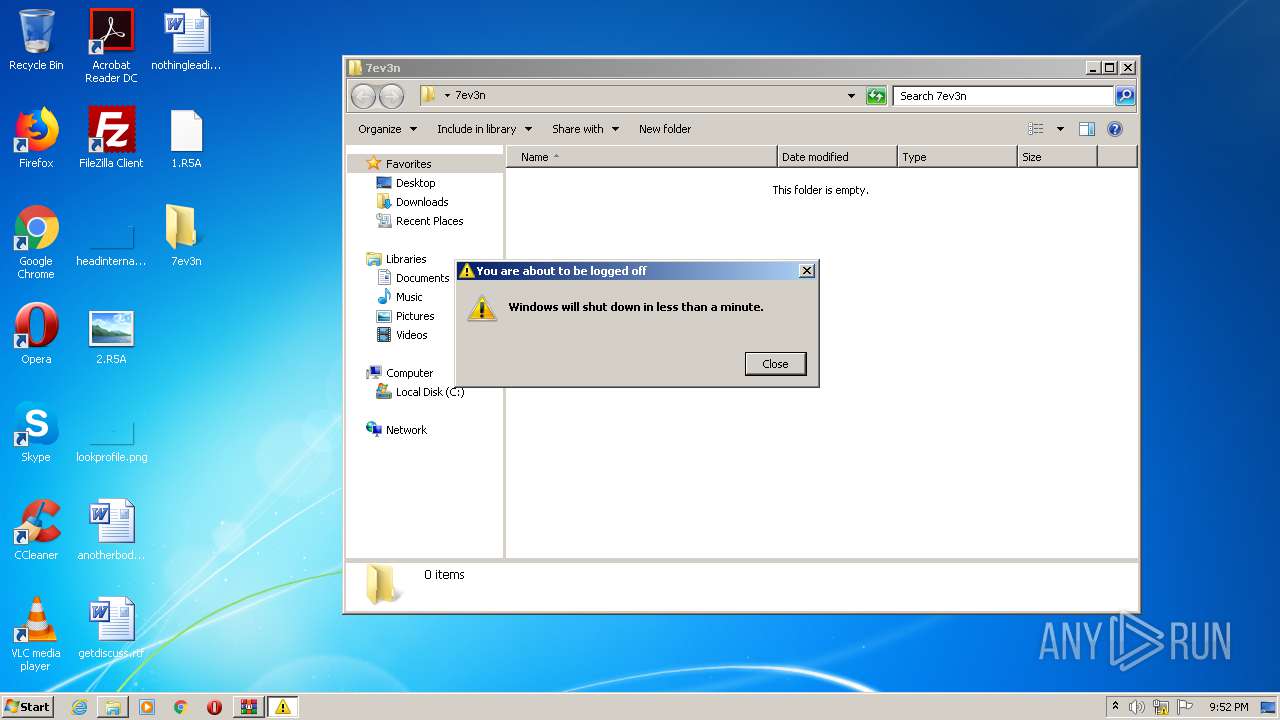
UAC/LUA settings modification
- reg.exe (PID: 2116)
SUSPICIOUS
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1908)
- Endermanch@7ev3n.exe (PID: 1088)
- uac.exe (PID: 3500)
- wusa.exe (PID: 3296)
Executable content was dropped or overwritten
- Endermanch@7ev3n.exe (PID: 1088)
- WinRAR.exe (PID: 1908)
- system.exe (PID: 1892)
- uac.exe (PID: 3500)
- wusa.exe (PID: 3296)
Starts itself from another location
- Endermanch@7ev3n.exe (PID: 1088)
Starts CMD.EXE for commands execution
- system.exe (PID: 1892)
- uac.exe (PID: 3500)
- system.exe (PID: 3884)
Creates files in the Windows directory
- wusa.exe (PID: 3296)
Removes files from Windows directory
- wusa.exe (PID: 3296)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3844)
- cmd.exe (PID: 1716)
- cmd.exe (PID: 2344)
- cmd.exe (PID: 1016)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 2504)
- cmd.exe (PID: 3272)
INFO
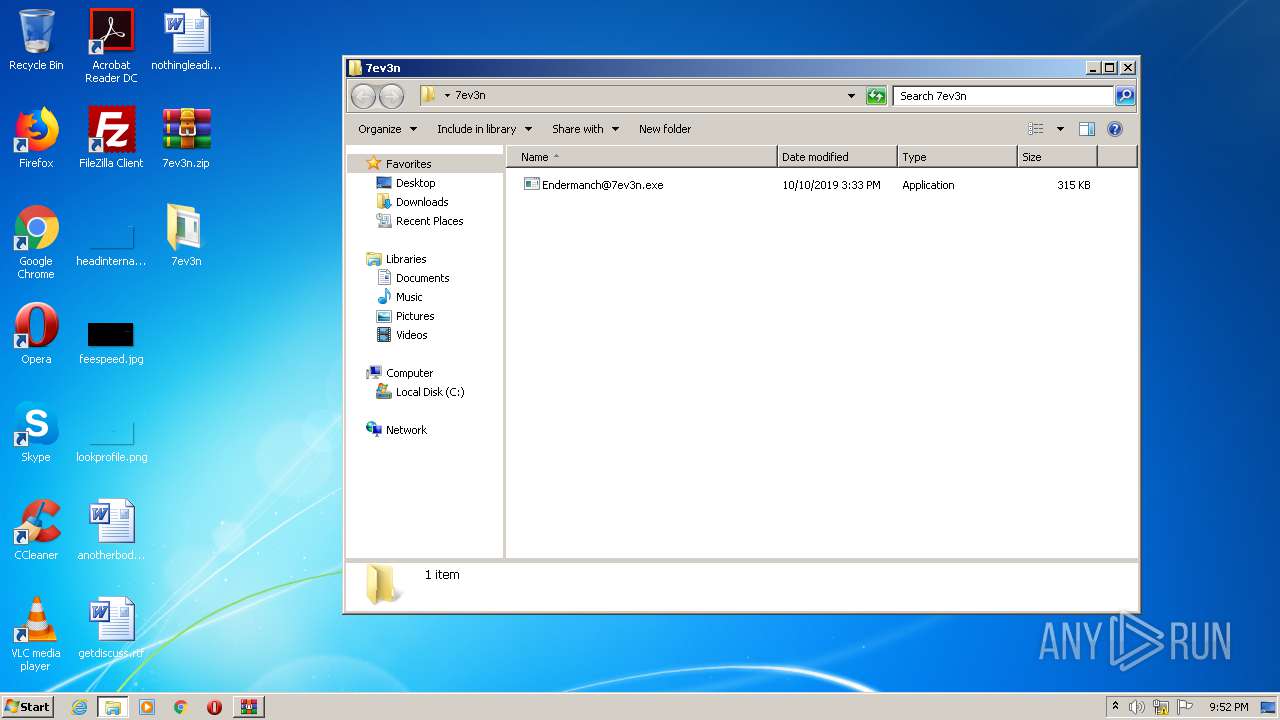
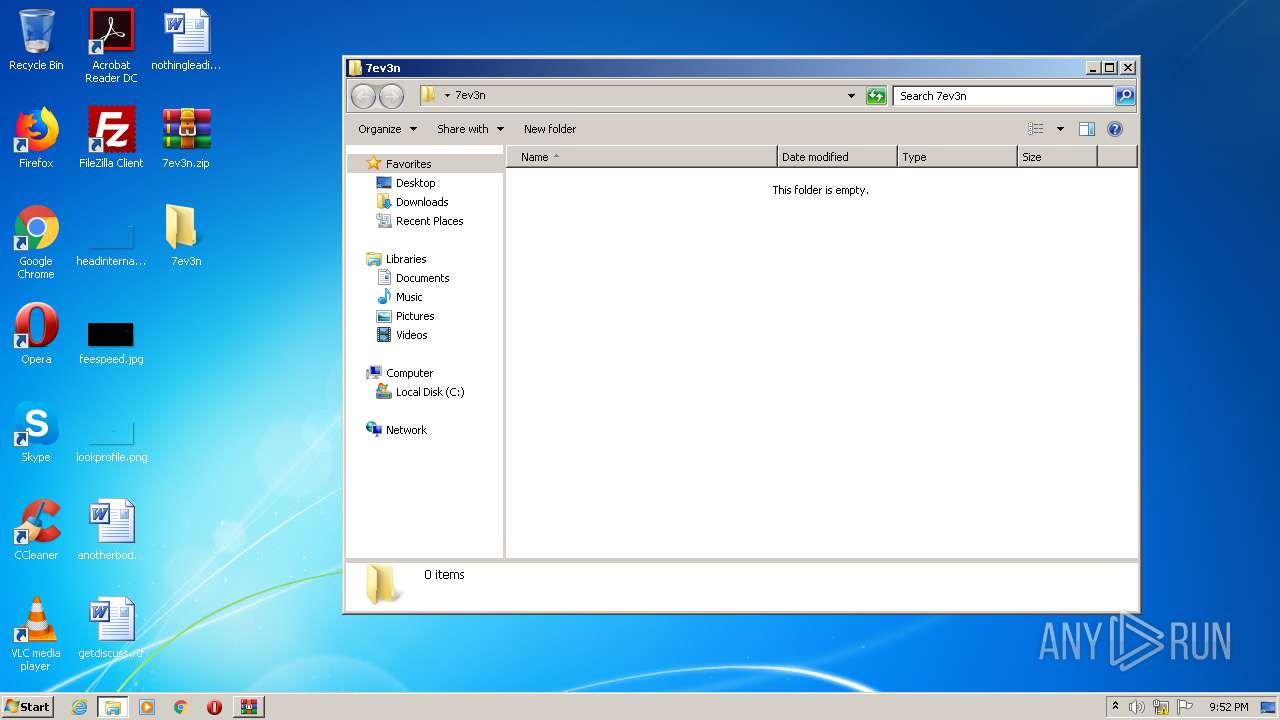
Manual execution by user
- Endermanch@7ev3n.exe (PID: 1088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:10 17:33:20 |
| ZipCRC: | 0xfaa96043 |
| ZipCompressedSize: | 142919 |
| ZipUncompressedSize: | 322560 |
| ZipFileName: | Endermanch@7ev3n.exe |
Total processes
93
Monitored processes
32
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | C:\windows\system32\cmd.exe /c REG ADD "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Keyboard Layout" /v "Scancode Map" /t REG_BINARY /d "00000000000000001700000000003800000038e000005be000005ce00000360000001d0000001de000000f000000010000001c0000003e0000003b00000044000000450000003d0000005de000000000" /f /reg:64 | C:\windows\system32\cmd.exe | — | system.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1020 | REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon" /v "Shell" /t REG_SZ /d "C:\Users\admin\AppData\Local\system.exe" /f /reg:64 | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Users\admin\Desktop\7ev3n\Endermanch@7ev3n.exe" | C:\Users\admin\Desktop\7ev3n\Endermanch@7ev3n.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1188 | C:\Windows\System32\SCHTASKS.exe /create /SC ONLOGON /TN uac /TR "C:\Users\admin\AppData\Local\bcd.bat" /RL HIGHEST /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1716 | C:\windows\system32\cmd.exe /c REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /v "System" /t REG_SZ /d "C:\Users\admin\AppData\Local\system.exe" /f /reg:64 | C:\windows\system32\cmd.exe | — | system.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1892 | "C:\Users\admin\AppData\Local\system.exe" | C:\Users\admin\AppData\Local\system.exe | Endermanch@7ev3n.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\7ev3n.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.60.0 Modules
| |||||||||||||||
| 1924 | REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion" /v "crypted" /t REG_SZ /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1952 | wusa C:\Users\admin\AppData\Local\Temp\ellocnak.msu /extract:C:\Windows\system32\sysprep | C:\Windows\system32\wusa.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2116 | REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "EnableLUA" /t REG_DWORD /d 0 /f /reg:64 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
587
Read events
527
Write events
59
Delete events
1
Modification events
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\7ev3n.zip | |||
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
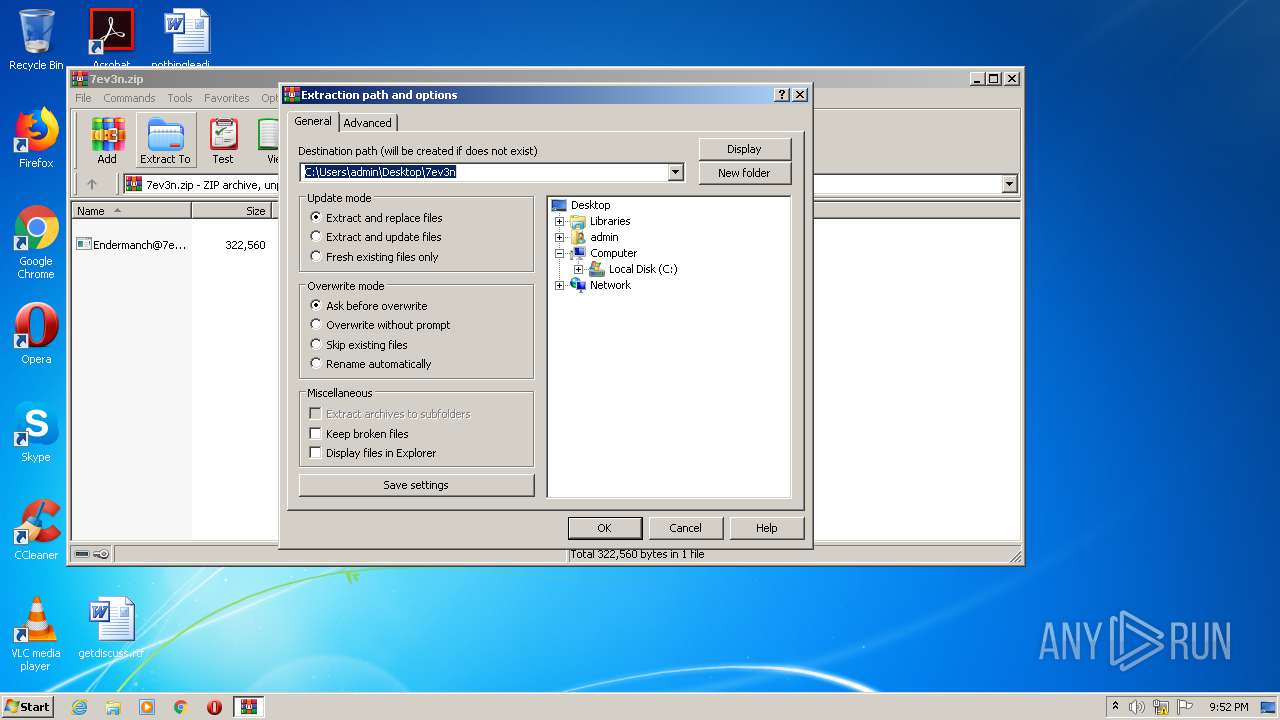
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\7ev3n | |||
| (PID) Process: | (1908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
8
Suspicious files
18
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1088 | Endermanch@7ev3n.exe | C:\Users\admin\AppData\Local\Temp\CabE023.tmp | — | |
MD5:— | SHA256:— | |||
| 1088 | Endermanch@7ev3n.exe | C:\Users\admin\AppData\Local\Temp\TarE024.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | uac.exe | C:\Users\admin\AppData\Local\Temp\emcE14C.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | uac.exe | C:\Users\admin\AppData\Local\Temp\emcE14D.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | uac.exe | C:\Users\admin\AppData\Local\Temp\emcE14E.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | uac.exe | C:\Users\admin\AppData\Local\Temp\emcE14F.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | uac.exe | C:\Users\admin\AppData\Local\Temp\emcE150.tmp | — | |
MD5:— | SHA256:— | |||
| 3296 | wusa.exe | C:\Windows\system32\sysprep\$dpx$.tmp\f0f86983dfea74418ecc81f58b0af9d0.tmp | — | |
MD5:— | SHA256:— | |||
| 3296 | wusa.exe | C:\Windows\system32\sysprep\$dpx$.tmp\56460aaf8c158f4eb6057ef1811390f0.tmp | — | |
MD5:— | SHA256:— | |||
| 3296 | wusa.exe | C:\Windows\Logs\DPX\setuperr.log | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1088 | Endermanch@7ev3n.exe | 104.16.54.3:443 | blockchain.info | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blockchain.info |
| shared |
jaster.in |
| malicious |
Threats
Process | Message |
|---|---|
uac.exe | [UCM] Dll dropped successfully |
winsat.exe | Akagi letter found |
winsat.exe | Akagi letter found |
winsat.exe | C:\Users\admin\AppData\Local\system.exe |