| File name: | VCS antivirus.exe |
| Full analysis: | https://app.any.run/tasks/ceb8f18f-ce0b-4b14-9569-c17e0c12fdd7 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 04:11:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 3EEEFAA309C8B93EFE5E99ECF85EA227 |
| SHA1: | E0F6A44AB200A0A0A7959CCA664618B6B8E02797 |
| SHA256: | EA5D1E2D0DDCC874CBFE969D7BF49E58F980BCE01501F4E8A53107A0DACFF736 |
| SSDEEP: | 98304:Nv7i+tfi42kGJsXukTemIMpYftHfktEzafhOsE+XZ0FdD1yTK4qVcYGCh1GJIbj1:Nrn2QJpZf7AktijSem866s55cm |
MALICIOUS
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 5064)
SUSPICIOUS
Process drops python dynamic module
- VCS antivirus.exe (PID: 4688)
Executable content was dropped or overwritten
- VCS antivirus.exe (PID: 4688)
- VCS antivirus.exe (PID: 7020)
Process drops legitimate windows executable
- VCS antivirus.exe (PID: 4688)
The process drops C-runtime libraries
- VCS antivirus.exe (PID: 4688)
Application launched itself
- VCS antivirus.exe (PID: 4688)
Loads Python modules
- VCS antivirus.exe (PID: 7020)
Get information on the list of running processes
- VCS antivirus.exe (PID: 7020)
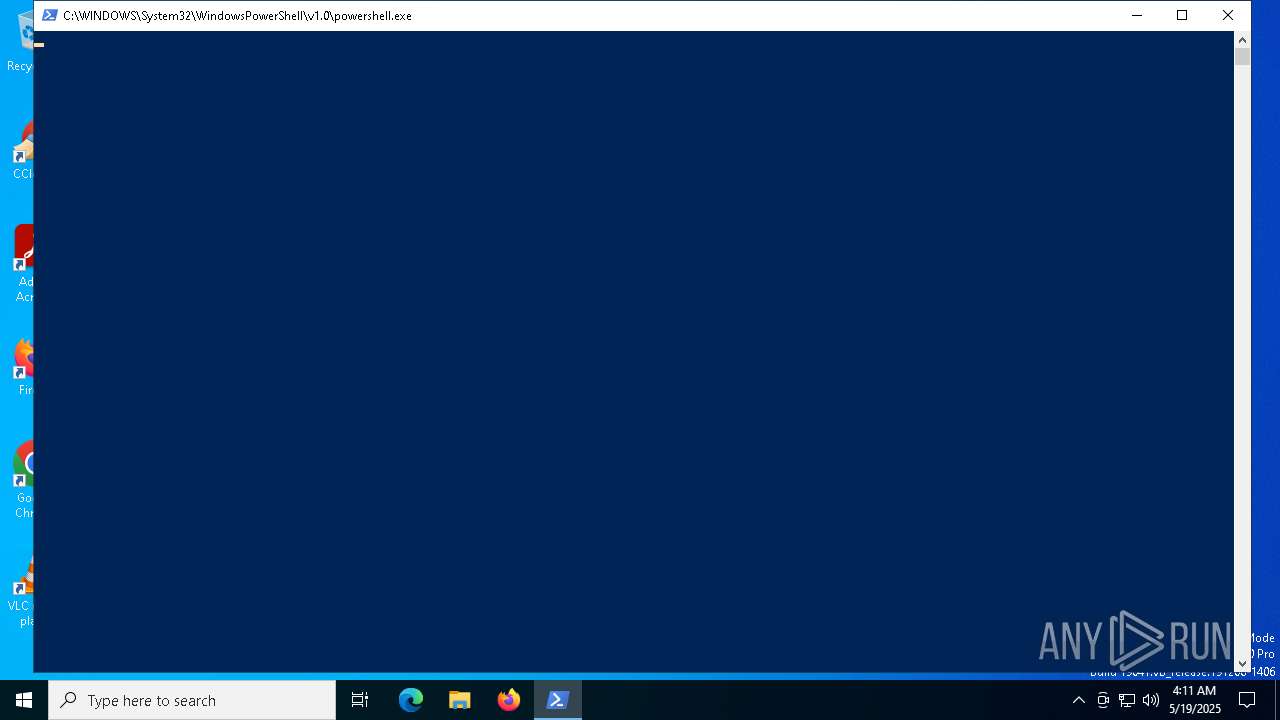
The process executes Powershell scripts
- VCS antivirus.exe (PID: 7020)
Starts POWERSHELL.EXE for commands execution
- VCS antivirus.exe (PID: 7020)
Creates file in the systems drive root
- powershell.exe (PID: 5064)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 5064)
There is functionality for taking screenshot (YARA)
- VCS antivirus.exe (PID: 4688)
- VCS antivirus.exe (PID: 7020)
Possible usage of Discord/Telegram API has been detected (YARA)
- VCS antivirus.exe (PID: 7020)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- VCS antivirus.exe (PID: 7020)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5064)
INFO
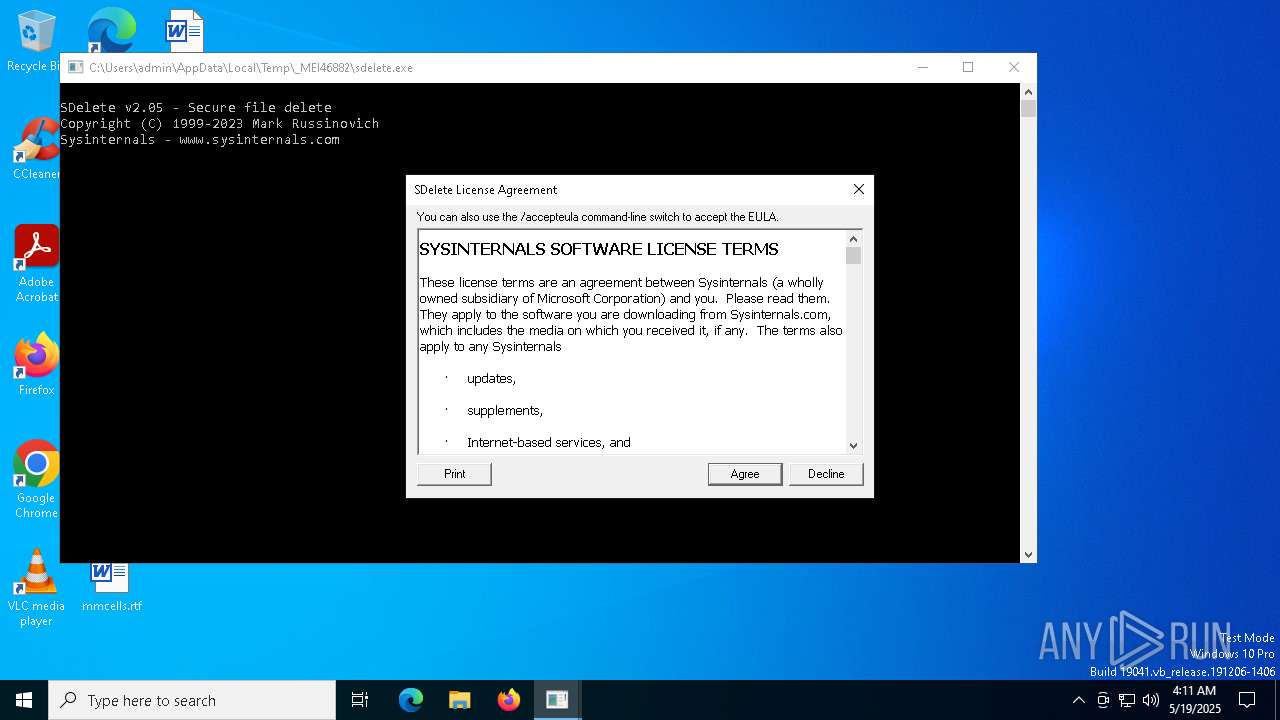
Checks supported languages
- VCS antivirus.exe (PID: 4688)
- VCS antivirus.exe (PID: 7020)
- sdelete.exe (PID: 2980)
Reads the computer name
- VCS antivirus.exe (PID: 4688)
- VCS antivirus.exe (PID: 7020)
- sdelete.exe (PID: 2980)
The sample compiled with english language support
- VCS antivirus.exe (PID: 4688)
- VCS antivirus.exe (PID: 7020)
Create files in a temporary directory
- VCS antivirus.exe (PID: 4688)
- VCS antivirus.exe (PID: 7020)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5064)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 5064)
PyInstaller has been detected (YARA)
- VCS antivirus.exe (PID: 4688)
- VCS antivirus.exe (PID: 7020)
Checks proxy server information
- VCS antivirus.exe (PID: 7020)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5064)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(7020) VCS antivirus.exe
Telegram-Tokens (1)7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0
Telegram-Info-Links
7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0
Get info about bothttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getMe
Get incoming updateshttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getUpdates
Get webhookhttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/deleteWebhook?drop_pending_updates=true
Telegram-Tokens (1)7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0
Telegram-Info-Links
7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0
Get info about bothttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getMe
Get incoming updateshttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getUpdates
Get webhookhttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0
End-PointsendMessage
Args
Telegram-Responses
oktrue
result
message_id573
from
id7457737016
is_bottrue
first_nametmqsuperbot_bot
usernametmqsuperbot_bot
chat
id1617506446
first_namepy
usernamepy0bf3c4t0r
typeprivate
date1747627877
textKey: Q1uFCmEC85EC4IAnaT1/mpVFbMMli4xyqfL/0HCQevs=
IV: JbaGgeB5IYdrJYNldeXP9w==
has_protected_contenttrue
Telegram-Responses
oktrue
result
message_id573
from
id7457737016
is_bottrue
first_nametmqsuperbot_bot
usernametmqsuperbot_bot
chat
id1617506446
first_namepy
usernamepy0bf3c4t0r
typeprivate
date1747627877
textKey: Q1uFCmEC85EC4IAnaT1/mpVFbMMli4xyqfL/0HCQevs=
IV: JbaGgeB5IYdrJYNldeXP9w==
has_protected_contenttrue
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:09:07 05:18:22+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.37 |
| CodeSize: | 171520 |
| InitializedDataSize: | 162304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc2f0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
135
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2980 | C:\Users\admin\AppData\Local\Temp\_MEI46882\sdelete.exe C:\Users\admin\AppData\Local\Temp\_MEI46882\ps.ps1 | C:\Users\admin\AppData\Local\Temp\_MEI46882\sdelete.exe | — | VCS antivirus.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sdelete.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4688 | "C:\Users\admin\AppData\Local\Temp\VCS antivirus.exe" | C:\Users\admin\AppData\Local\Temp\VCS antivirus.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5064 | powershell.exe -File C:\Users\admin\AppData\Local\Temp\_MEI46882\ps.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | VCS antivirus.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5164 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7020 | "C:\Users\admin\AppData\Local\Temp\VCS antivirus.exe" | C:\Users\admin\AppData\Local\Temp\VCS antivirus.exe | VCS antivirus.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
ims-api(PID) Process(7020) VCS antivirus.exe Telegram-Tokens (1)7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0 Telegram-Info-Links 7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0 Get info about bothttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getMe Get incoming updateshttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getUpdates Get webhookhttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getWebhookInfo Delete webhookhttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/deleteWebhook Drop incoming updateshttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/deleteWebhook?drop_pending_updates=true (PID) Process(7020) VCS antivirus.exe Telegram-Tokens (1)7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0 Telegram-Info-Links 7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0 Get info about bothttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getMe Get incoming updateshttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getUpdates Get webhookhttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/getWebhookInfo Delete webhookhttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/deleteWebhook Drop incoming updateshttps://api.telegram.org/bot7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0/deleteWebhook?drop_pending_updates=true Telegram-Requests Token7457737016:AAEvv7iDxEzpd9bxMmY9BBwZM0rE2e9Yef0 End-PointsendMessage Args Telegram-Responses oktrue result message_id573 from id7457737016 is_bottrue first_nametmqsuperbot_bot usernametmqsuperbot_bot chat id1617506446 first_namepy usernamepy0bf3c4t0r typeprivate date1747627877 textKey: Q1uFCmEC85EC4IAnaT1/mpVFbMMli4xyqfL/0HCQevs=
IV: JbaGgeB5IYdrJYNldeXP9w== has_protected_contenttrue (PID) Process(7020) VCS antivirus.exe Telegram-Responses oktrue result message_id573 from id7457737016 is_bottrue first_nametmqsuperbot_bot usernametmqsuperbot_bot chat id1617506446 first_namepy usernamepy0bf3c4t0r typeprivate date1747627877 textKey: Q1uFCmEC85EC4IAnaT1/mpVFbMMli4xyqfL/0HCQevs=
IV: JbaGgeB5IYdrJYNldeXP9w== has_protected_contenttrue | |||||||||||||||
Total events
4 800
Read events
4 800
Write events
0
Delete events
0
Modification events
Executable files
59
Suspicious files
3
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\_bz2.pyd | executable | |
MD5:37EACE4B806B32F829DE08DB3803B707 | SHA256:1BE51EF2B5ACBE490217AA1FF12618D24B95DF6136C6844714B9CA997B4C7F9B | |||
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\_cffi_backend.cp311-win_amd64.pyd | executable | |
MD5:210DEF84BB2C35115A2B2AC25E3FFD8F | SHA256:59767B0918859BEDDF28A7D66A50431411FFD940C32B3E8347E6D938B60FACDF | |||
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\_hashlib.pyd | executable | |
MD5:BA682DFCDD600A4BB43A51A0D696A64C | SHA256:2AD55E11BDDB5B65CDF6E9E126D82A3B64551F7AD9D4CBF74A1058FD7E5993BD | |||
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\_socket.pyd | executable | |
MD5:485D998A2DE412206F04FA028FE6BA90 | SHA256:8F9EDE5044643413C3B072CD31A565956498CA07CDD17FB6A04483D388FDAD76 | |||
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\_lzma.pyd | executable | |
MD5:3273720DDF2C5B75B072A1FB13476751 | SHA256:663F1087C2ED664C5995A3FFA64546D2E33A0FCE8A9121B48CC7C056B74A2948 | |||
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\_queue.pyd | executable | |
MD5:284FBC1B32F0282FC968045B922A4EE2 | SHA256:AC3B144D7D7C8EE39F29D8749C5A35C4314B5365198821605C883FD11807E766 | |||
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:E8B9D74BFD1F6D1CC1D99B24F44DA796 | SHA256:B1B3FD40AB437A43C8DB4994CCFFC7F88000CC8BB6E34A2BCBFF8E2464930C59 | |||
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\_ssl.pyd | executable | |
MD5:E5B1A076E9828985EA8EA07D22C6ABD0 | SHA256:591589DADC659D1AD4856D16CD25DC8E57EAA085BF68EB2929F8F93ABA69DB1B | |||
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:33BBECE432F8DA57F17BF2E396EBAA58 | SHA256:7CF0944901F7F7E0D0B9AD62753FC2FE380461B1CCE8CDC7E9C9867C980E3B0E | |||
| 4688 | VCS antivirus.exe | C:\Users\admin\AppData\Local\Temp\_MEI46882\VCRUNTIME140.dll | executable | |
MD5:BE8DBE2DC77EBE7F88F910C61AEC691A | SHA256:4D292623516F65C80482081E62D5DADB759DC16E851DE5DB24C3CBB57B87DB83 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
23
DNS requests
16
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4880 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4880 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7020 | VCS antivirus.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
7020 | VCS antivirus.exe | 13.107.253.45:443 | download.sysinternals.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
download.sysinternals.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.telegram.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7020 | VCS antivirus.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |